The Deepfake Nudes Crisis in Schools Is Much Worse Than You Thought






Emails claiming to be from Social Security are making the rounds right now.
They look official. They sound official. And they’re designed to get you to click before you think twice.
The Social Security Administration’s Office of Inspector General is warning about a spike in messages that claim your Social Security statement is ready to download. The goal is simple. Get you to click a link or open an attachment.
From there, things can go sideways fast.
Before interacting with anything like this, it’s worth pausing and running it through a tool like McAfee’s Scam Detector. This is exactly the kind of message it’s built to flag. Something that looks legitimate, but feels just slightly off.
The email mimics official government communication, using logos, formatting, and language that feels familiar. It might say your statement is ready, your account needs attention, or you need to review a document.
Once you click:
The biggest tell: Social Security does not send emails like this asking you to download statements or provide sensitive information.
And that, my friends, is scam number one in this week’s This Week in Scams.
Let’s get into what else is on our radar.
Healthcare data breaches don’t always make headlines the same way big tech breaches do, but they can be just as serious.
According to reporting from Fox News, CareCloud, a company that supports electronic health records for tens of thousands of providers, recently confirmed a security incident involving unauthorized access to one of its systems.
The access lasted several hours. And while it’s still unclear whether any data was taken, that uncertainty is exactly what makes situations like this risky.
Because even if you’ve never heard of the company, your doctor might use it.
Healthcare data is incredibly valuable. It can include:
Unlike a credit card, you can’t just cancel your medical history.
And when that kind of data is exposed or even potentially exposed, scammers often follow up with messages that feel highly specific and personal.
After incidents like this, scammers often move quickly:
These scams work because they’re timed perfectly and feel relevant.
This is another moment where Scam Detector can help flag suspicious links or messages before you engage, even when they reference real healthcare providers.
Scams today are layered.
A fake email leads to stolen credentials. A breach leads to targeted phishing. And those follow-ups are getting harder to spot.
McAfee+ Advanced gives you multiple layers working together so you are not left figuring it out after the damage is done:
Because the reality is, scams are designed to look legitimate. You shouldn’t have to figure it out on your own. We’re safer together.
We’ll be back next week with more scams making headlines.
The post Social Security Scam Emails and a Healthcare Data Breach: This Week in Scams appeared first on McAfee Blog.



We’re excited to share that McAfee’s Scam Detector has been named a finalist in the 2026 Webby Awards.
Recognized in the AI Experiences & Applications – Consumer Application category and named a Webby Honoree for Best Use of AI & Machine Learning, Scam Detector is being acknowledged for its effectiveness as an AI-driven consumer tool.
This recognition of Scam Detector validates something key in research findings. According to McAfee’s 2026 State of the Scamiverse report, Americans now spend 114 hours a year trying to decide what’s real and what’s fake online.
Scam Detector was built with this era of uncertainty in mind, designed to help people cut through confusion and identify scams as they appear. The Webby recognition reinforces to us that McAfee’s Scam Detector is doing exactly that.
The Webby Awards are presented by the International Academy of Digital Arts & Sciences and recognize excellence across the internet, including apps, software, AI, and digital experiences.
Each year, thousands of entries are evaluated, with finalists representing the top work in their category globally.
In addition to judged awards, the Webby Awards include a People’s Voice Award, which is decided by public vote.
Scam Detector is designed to help people identify scams where they’re most likely to happen, always ready to help you spot what’s real and what’s not when you least expect it.
It uses AI to analyze and flag suspicious:
Beyond detection, Scam Detector explains why something was flagged as risky. That transparency helps show how decisions are made, so people can quickly understand the risk and feel more confident trusting what’s flagged.
As scams become more personalized and harder to detect, this combination of automatic detection and clear guidance is critical to preventing financial loss and identity theft.
Scam Detector is eligible for the Webby People’s Voice Award, which is decided by public vote.
If you would like to support McAfee’s Scam Detector, you can vote here: https://vote.webbyawards.com/PublicVoting#/2026/ai/ai-experiences-applications/consumer-application
Voting is open through Thursday, April 16 at 11:59 pm PDT.
Winners will be announced on April 21, 2026.
And a big thank you to the McAfee teams who brought Scam Detector to life and who continuously improve how Scam Detector identifies new threats and adapts to the evolving world of AI-driven scams.
The post McAfee’s Scam Detector Named Webby Awards Finalist for AI Innovation appeared first on McAfee Blog.




Hackers linked to Russia’s military intelligence units are using known flaws in older Internet routers to mass harvest authentication tokens from Microsoft Office users, security experts warned today. The spying campaign allowed state-backed Russian hackers to quietly siphon authentication tokens from users on more than 18,000 networks without deploying any malicious software or code.
Microsoft said in a blog post today it identified more than 200 organizations and 5,000 consumer devices that were caught up in a stealthy but remarkably simple spying network built by a Russia-backed threat actor known as “Forest Blizzard.”

How targeted DNS requests were redirected at the router. Image: Black Lotus Labs.
Also known as APT28 and Fancy Bear, Forest Blizzard is attributed to the military intelligence units within Russia’s General Staff Main Intelligence Directorate (GRU). APT 28 famously compromised the Hillary Clinton campaign, the Democratic National Committee, and the Democratic Congressional Campaign Committee in 2016 in an attempt to interfere with the U.S. presidential election.
Researchers at Black Lotus Labs, a security division of the Internet backbone provider Lumen, found that at the peak of its activity in December 2025, Forest Blizzard’s surveillance dragnet ensnared more than 18,000 Internet routers that were mostly unsupported, end-of-life routers, or else far behind on security updates. A new report from Lumen says the hackers primarily targeted government agencies—including ministries of foreign affairs, law enforcement, and third-party email providers.
Black Lotus Security Engineer Ryan English said the GRU hackers did not need to install malware on the targeted routers, which were mainly older Mikrotik and TP-Link devices marketed to the Small Office/Home Office (SOHO) market. Instead, they used known vulnerabilities to modify the Domain Name System (DNS) settings of the routers to include DNS servers controlled by the hackers.
As the U.K.’s National Cyber Security Centre (NCSC) notes in a new advisory detailing how Russian cyber actors have been compromising routers, DNS is what allows individuals to reach websites by typing familiar addresses, instead of associated IP addresses. In a DNS hijacking attack, bad actors interfere with this process to covertly send users to malicious websites designed to steal login details or other sensitive information.
English said the routers attacked by Forest Blizzard were reconfigured to use DNS servers that pointed to a handful of virtual private servers controlled by the attackers. Importantly, the attackers could then propagate their malicious DNS settings to all users on the local network, and from that point forward intercept any OAuth authentication tokens transmitted by those users.
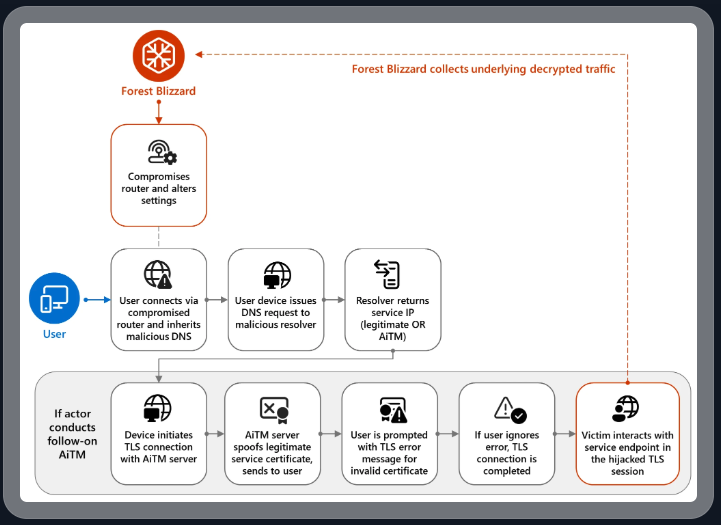
DNS hijacking through router compromise. Image: Microsoft.
Because those tokens are typically transmitted only after the user has successfully logged in and gone through multi-factor authentication, the attackers could gain direct access to victim accounts without ever having to phish each user’s credentials and/or one-time codes.
“Everyone is looking for some sophisticated malware to drop something on your mobile devices or something,” English said. “These guys didn’t use malware. They did this in an old-school, graybeard way that isn’t really sexy but it gets the job done.”
Microsoft refers to the Forest Blizzard activity as using DNS hijacking “to support post-compromise adversary-in-the-middle (AiTM) attacks on Transport Layer Security (TLS) connections against Microsoft Outlook on the web domains.” The software giant said while targeting SOHO devices isn’t a new tactic, this is the first time Microsoft has seen Forest Blizzard using “DNS hijacking at scale to support AiTM of TLS connections after exploiting edge devices.”
Black Lotus Labs engineer Danny Adamitis said it will be interesting to see how Forest Blizzard reacts to today’s flurry of attention to their espionage operation, noting that the group immediately switched up its tactics in response to a similar NCSC report (PDF) in August 2025. At the time, Forest Blizzard was using malware to control a far more targeted and smaller group of compromised routers. But Adamitis said the day after the NCSC report, the group quickly ditched the malware approach in favor of mass-altering the DNS settings on thousands of vulnerable routers.
“Before the last NCSC report came out they used this capability in very limited instances,” Adamitis told KrebsOnSecurity. “After the report was released they implemented the capability in a more systemic fashion and used it to target everything that was vulnerable.”
TP-Link was among the router makers facing a complete ban in the United States. But on March 23, the U.S. Federal Communications Commission (FCC) took a much broader approach, announcing it would no longer certify consumer-grade Internet routers that are produced outside of the United States.
The FCC warned that foreign-made routers had become an untenable national security threat, and that poorly-secured routers present “a severe cybersecurity risk that could be leveraged to immediately and severely disrupt U.S. critical infrastructure and directly harm U.S. persons.”
Experts have countered that few new consumer-grade routers would be available for purchase under this new FCC policy (besides maybe Musk’s Starlink satellite Internet routers, which are produced in Texas). The FCC says router makers can apply for a special “conditional approval” from the Department of War or Department of Homeland Security, and that the new policy does not affect any previously-purchased consumer-grade routers.

An elusive hacker who went by the handle “UNKN” and ran the early Russian ransomware groups GandCrab and REvil now has a name and a face. Authorities in Germany say 31-year-old Russian Daniil Maksimovich Shchukin headed both cybercrime gangs and helped carry out at least 130 acts of computer sabotage and extortion against victims across the country between 2019 and 2021.
Shchukin was named as UNKN (a.k.a. UNKNOWN) in an advisory published by the German Federal Criminal Police (the “Bundeskriminalamt” or BKA for short). The BKA said Shchukin and another Russian — 43-year-old Anatoly Sergeevitsch Kravchuk — extorted nearly $2 million euros across two dozen cyberattacks that caused more than 35 million euros in total economic damage.

Daniil Maksimovich SHCHUKIN, a.k.a. UNKN, and Anatoly Sergeevitsch Karvchuk, alleged leaders of the GandCrab and REvil ransomware groups.
Germany’s BKA said Shchukin acted as the head of one of the largest worldwide operating ransomware groups GandCrab and REvil, which pioneered the practice of double extortion — charging victims once for a key needed to unlock hacked systems, and a separate payment in exchange for a promise not to publish stolen data.
Shchukin’s name appeared in a Feb. 2023 filing (PDF) from the U.S. Justice Department seeking the seizure of various cryptocurrency accounts associated with proceeds from the REvil ransomware gang’s activities. The government said the digital wallet tied to Shchukin contained more than $317,000 in ill-gotten cryptocurrency.
The GandCrab ransomware affiliate program first surfaced in January 2018, and paid enterprising hackers huge shares of the profits just for hacking into user accounts at major corporations. The GandCrab team would then try to expand that access, often siphoning vast amounts of sensitive and internal documents in the process. The malware’s curators shipped five major revisions to the GandCrab code, each corresponding with sneaky new features and bug fixes aimed at thwarting the efforts of computer security firms to stymie the spread of the malware.
On May 31, 2019, the GandCrab team announced the group was shutting down after extorting more than $2 billion from victims. “We are a living proof that you can do evil and get off scot-free,” GandCrab’s farewell address famously quipped. “We have proved that one can make a lifetime of money in one year. We have proved that you can become number one by general admission, not in your own conceit.”
The REvil ransomware affiliate program materialized around the same as GandCrab’s demise, fronted by a user named UNKNOWN who announced on a Russian cybercrime forum that he’d deposited $1 million in the forum’s escrow to show he meant business. By this time, many cybersecurity experts had concluded REvil was little more than a reorganization of GandCrab.
UNKNOWN also gave an interview to Dmitry Smilyanets, a former malicious hacker hired by Recorded Future, wherein UNKNOWN described a rags-to-riches tale unencumbered by ethics and morals.
“As a child, I scrounged through the trash heaps and smoked cigarette butts,” UNKNOWN told Recorded Future. “I walked 10 km one way to the school. I wore the same clothes for six months. In my youth, in a communal apartment, I didn’t eat for two or even three days. Now I am a millionaire.”
As described in The Ransomware Hunting Team by Renee Dudley and Daniel Golden, UNKNOWN and REvil reinvested significant earnings into improving their success and mirroring practices of legitimate businesses. The authors wrote:
“Just as a real-world manufacturer might hire other companies to handle logistics or web design, ransomware developers increasingly outsourced tasks beyond their purview, focusing instead on improving the quality of their ransomware. The higher quality ransomware—which, in many cases, the Hunting Team could not break—resulted in more and higher pay-outs from victims. The monumental payments enabled gangs to reinvest in their enterprises. They hired more specialists, and their success accelerated.”
“Criminals raced to join the booming ransomware economy. Underworld ancillary service providers sprouted or pivoted from other criminal work to meet developers’ demand for customized support. Partnering with gangs like GandCrab, ‘cryptor’ providers ensured ransomware could not be detected by standard anti-malware scanners. ‘Initial access brokerages’ specialized in stealing credentials and finding vulnerabilities in target networks, selling that access to ransomware operators and affiliates. Bitcoin “tumblers” offered discounts to gangs that used them as a preferred vendor for laundering ransom payments. Some contractors were open to working with any gang, while others entered exclusive partnerships.”
REvil would evolve into a feared “big-game-hunting” machine capable of extracting hefty extortion payments from victims, largely going after organizations with more than $100 million in annual revenues and fat new cyber insurance policies that were known to pay out.
Over the July 4, 2021 weekend in the United States, REvil hacked into and extorted Kaseya, a company that handled IT operations for more than 1,500 businesses, nonprofits and government agencies. The FBI would later announce they’d infiltrated the ransomware group’s servers prior to the Kaseya hack but couldn’t tip their hand at the time. REvil never recovered from that core compromise, or from the FBI’s release of a free decryption key for REvil victims who couldn’t or didn’t pay.
Shchukin is from Krasnodar, Russia and is thought to reside there, the BKA said.
“Based on the investigations so far, it is assumed that the wanted person is abroad, presumably in Russia,” the BKA advised. “Travel behaviour cannot be ruled out.”
There is little that connects Shchukin to UNKNOWN’s various accounts on the Russian crime forums. But a review of the Russian crime forums indexed by the cyber intelligence firm Intel 471 shows there is plenty connecting Shchukin to a hacker identity called “Ger0in” who operated large botnets and sold “installs” — allowing other cybercriminals to rapidly deploy malware of their choice to thousands of PCs in one go. However, Ger0in was only active between 2010 and 2011, well before UNKNOWN’s appearance as the REvil front man.
A review of the mugshots released by the BKA at the image comparison site Pimeyes found a match on this birthday celebration from 2023, which features a young man named Daniel wearing the same fancy watch as in the BKA photos.
Update, April 6, 12:06 p.m. ET: A reader forwarded this English-dubbed audio recording from a ccc.de (37C3) conference talk in Germany from 2023 that previously outed Shchukin as the REvil leader (Shchuckin is mentioned at around 24:25).




A tax system breach in Oklahoma is putting highly sensitive personal information at risk. And unfortunately, this is exactly the kind of situation scammers love to exploit.
Hackers reportedly accessed W-2 and 1099 files through Oklahoma’s online tax portal, according to state officials, exposing the kind of information that can open the door to tax fraud, identity theft, and highly targeted phishing attempts.
Before the follow-up scams start rolling in, this is the kind of moment where layered protection matters. McAfee+ Advanced includes identity monitoring and data cleansup that can help alert you if your personal information starts circulating where it shouldn’t, and Scam Detector can flag suspicious messages if scammers try to use this breach as a hook.
According to a statement by the Oklahoma Tax Commission and reported by KOCO News 5, a local ABC affiliate, suspicious activity inside the state’s Oklahoma Taxpayer Access Point system was identified in December 2025. The agency says impacted individuals have been notified directly by mail, and complimentary credit monitoring and fraud assistance are being offered.
When W-2s, 1099s, Social Security numbers, and tax-related records are exposed, scammers can use that information to:
Either way, the goal is the same: use real information to make the next scam more believable.
The breach itself is real. But what often follows is a second wave of scams pretending to help.
That’s where people can get hit twice: once by the breach, and again by the scam that follows it.
First, don’t panic. Then:
And that, my friends, is scam number one in this week’s This Week in Scams.
Let’s get into what else is on our radar.
Scammers pretending to be federal agents are making the rounds across the country, and this one is built to make people panic fast.
Field offices, including Chicago and Houston, are warning the public about fraudsters posing as FBI agents in calls, texts, and emails. In some cases, the scammers claim you’re connected to an investigation. In others, they say you’re a victim of fraud and need to act immediately to protect yourself.
Sometimes they do not stop there. They may also pretend to be bank employees working alongside the FBI, all to make the story feel more convincing and get access to your money or personal information.

This scam plays on the same pressure tactics we’ve seen over and over again: authority, urgency, and confusion.
If someone claims to be a federal agent, many people freeze up and assume they need to cooperate immediately. That’s exactly what scammers are counting on.
The FBI has been clear about this: federal law enforcement will not ask you for money or sensitive personal information over the phone, by text, or by email.
If it feels dramatic, high-pressure, and just a little off, trust that instinct.
This is also exactly the kind of message McAfee’s Scam Detector is built to flag before you get pulled in.
McAfee+ Advanced gives you multiple layers working together so you are not left figuring it out after the damage is done:
This kind of layered protection is critical in cases like ghost student scams, where the first sign of fraud often comes after financial damage has already happened.
Safety tips to carry into next week
The reality is, scams are getting better at looking official.
You should not have to be an expert to spot them. That’s why McAfee is here to help. We’re Safer Together.
We’ll be back next week with more scams making headlines.
The post Oklahoma Tax Breach and FBI Impersonation Scam: This Week in Scams appeared first on McAfee Blog.
