The U.S. Federal Communications Commission (FCC) today levied fines totaling nearly $200 million against the four major carriers — including AT&T, Sprint, T-Mobile and Verizon — for illegally sharing access to customers’ location information without consent.
![]()
The fines mark the culmination of a more than four-year investigation into the actions of the major carriers. In February 2020, the FCC put all four wireless providers on notice that their practices of sharing access to customer location data were likely violating the law.
The FCC said it found the carriers each sold access to its customers’ location information to ‘aggregators,’ who then resold access to the information to third-party location-based service providers.
“In doing so, each carrier attempted to offload its obligations to obtain customer consent onto downstream recipients of location information, which in many instances meant that no valid customer consent was obtained,” an FCC statement on the action reads. “This initial failure was compounded when, after becoming aware that their safeguards were ineffective, the carriers continued to sell access to location information without taking reasonable measures to protect it from unauthorized access.”
The FCC’s findings against AT&T, for example, show that AT&T sold customer location data directly or indirectly to at least 88 third-party entities. The FCC found Verizon sold access to customer location data (indirectly or directly) to 67 third-party entities. Location data for Sprint customers found its way to 86 third-party entities, and to 75 third-parties in the case of T-Mobile customers.
The commission said it took action after Sen. Ron Wyden (D-Ore.) sent a letter to the FCC detailing how a company called Securus Technologies had been selling location data on customers of virtually any major mobile provider to law enforcement officials.
That same month, KrebsOnSecurity broke the news that LocationSmart — a data aggregation firm working with the major wireless carriers — had a free, unsecured demo of its service online that anyone could abuse to find the near-exact location of virtually any mobile phone in North America.
The carriers promised to “wind down” location data sharing agreements with third-party companies. But in 2019, reporting at Vice.com showed that little had changed, detailing how reporters were able to locate a test phone after paying $300 to a bounty hunter who simply bought the data through a little-known third-party service.
Sen. Wyden said no one who signed up for a cell plan thought they were giving permission for their phone company to sell a detailed record of their movements to anyone with a credit card.
“I applaud the FCC for following through on my investigation and holding these companies accountable for putting customers’ lives and privacy at risk,” Wyden said in a statement today.
The FCC fined Sprint and T-Mobile $12 million and $80 million respectively. AT&T was fined more than $57 million, while Verizon received a $47 million penalty. Still, these fines represent a tiny fraction of each carrier’s annual revenues. For example, $47 million is less than one percent of Verizon’s total wireless service revenue in 2023, which was nearly $77 billion.
The fine amounts vary because they were calculated based in part on the number of days that the carriers continued sharing customer location data after being notified that doing so was illegal (the agency also considered the number of active third-party location data sharing agreements). The FCC notes that AT&T and Verizon each took more than 320 days from the publication of the Times story to wind down their data sharing agreements; T-Mobile took 275 days; Sprint kept sharing customer location data for 386 days.
Update, 6:25 p.m. ET: Clarified that the FCC launched its investigation at the request of Sen. Wyden.
It’s not unusual for the data brokers behind people-search websites to use pseudonyms in their day-to-day lives (you would, too). Some of these personal data purveyors even try to reinvent their online identities in a bid to hide their conflicts of interest. But it’s not every day you run across a US-focused people-search network based in China whose principal owners all appear to be completely fabricated identities.
Responding to a reader inquiry concerning the trustworthiness of a site called TruePeopleSearch[.]net, KrebsOnSecurity began poking around. The site offers to sell reports containing photos, police records, background checks, civil judgments, contact information “and much more!” According to LinkedIn and numerous profiles on websites that accept paid article submissions, the founder of TruePeopleSearch is Marilyn Gaskell from Phoenix, Ariz.
The saucy yet studious LinkedIn profile for Marilyn Gaskell.
Ms. Gaskell has been quoted in multiple “articles” about random subjects, such as this article at HRDailyAdvisor about the pros and cons of joining a company-led fantasy football team.
“Marilyn Gaskell, founder of TruePeopleSearch, agrees that not everyone in the office is likely to be a football fan and might feel intimidated by joining a company league or left out if they don’t join; however, her company looked for ways to make the activity more inclusive,” this paid story notes.
Also quoted in this article is Sally Stevens, who is cited as HR Manager at FastPeopleSearch[.]io.
Sally Stevens, the phantom HR Manager for FastPeopleSearch.
“Fantasy football provides one way for employees to set aside work matters for some time and have fun,” Stevens contributed. “Employees can set a special league for themselves and regularly check and compare their scores against one another.”
Imagine that: Two different people-search companies mentioned in the same story about fantasy football. What are the odds?
Both TruePeopleSearch and FastPeopleSearch allow users to search for reports by first and last name, but proceeding to order a report prompts the visitor to purchase the file from one of several established people-finder services, including BeenVerified, Intelius, and Spokeo.
DomainTools.com shows that both TruePeopleSearch and FastPeopleSearch appeared around 2020 and were registered through Alibaba Cloud, in Beijing, China. No other information is available about these domains in their registration records, although both domains appear to use email servers based in China.
Sally Stevens’ LinkedIn profile photo is identical to a stock image titled “beautiful girl” from Adobe.com. Ms. Stevens is also quoted in a paid blog post at ecogreenequipment.com, as is Alina Clark, co-founder and marketing director of CocoDoc, an online service for editing and managing PDF documents.
The profile photo for Alina Clark is a stock photo appearing on more than 100 websites.
Scouring multiple image search sites reveals Ms. Clark’s profile photo on LinkedIn is another stock image that is currently on more than 100 different websites, including Adobe.com. Cocodoc[.]com was registered in June 2020 via Alibaba Cloud Beijing in China.
The same Alina Clark and photo materialized in a paid article at the website Ceoblognation, which in 2021 included her at #11 in a piece called “30 Entrepreneurs Describe The Big Hairy Audacious Goals (BHAGs) for Their Business.” It’s also worth noting that Ms. Clark is currently listed as a “former Forbes Council member” at the media outlet Forbes.com.
Entrepreneur #6 is Stephen Curry, who is quoted as CEO of CocoSign[.]com, a website that claims to offer an “easier, quicker, safer eSignature solution for small and medium-sized businesses.” Incidentally, the same photo for Stephen Curry #6 is also used in this “article” for #22 Jake Smith, who is named as the owner of a different company.
Stephen Curry, aka Jake Smith, aka no such person.
Mr. Curry’s LinkedIn profile shows a young man seated at a table in front of a laptop, but an online image search shows this is another stock photo. Cocosign[.]com was registered in June 2020 via Alibaba Cloud Beijing. No ownership details are available in the domain registration records.
Listed at #13 in that 30 Entrepreneurs article is Eden Cheng, who is cited as co-founder of PeopleFinderFree[.]com. KrebsOnSecurity could not find a LinkedIn profile for Ms. Cheng, but a search on her profile image from that Entrepreneurs article shows the same photo for sale at Shutterstock and other stock photo sites.
DomainTools says PeopleFinderFree was registered through Alibaba Cloud, Beijing. Attempts to purchase reports through PeopleFinderFree produce a notice saying the full report is only available via Spokeo.com.
Lynda Fairly is Entrepreneur #24, and she is quoted as co-founder of Numlooker[.]com, a domain registered in April 2021 through Alibaba in China. Searches for people on Numlooker forward visitors to Spokeo.
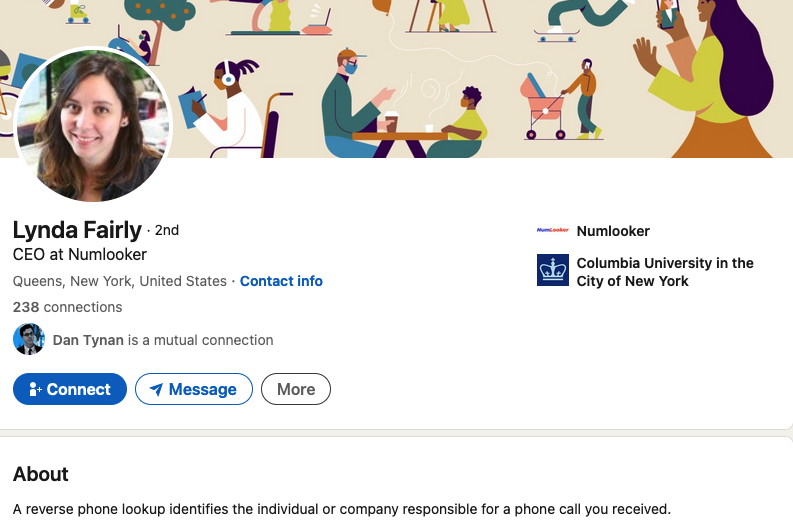
The photo next to Ms. Fairly’s quote in Entrepreneurs matches that of a LinkedIn profile for Lynda Fairly. But a search on that photo shows this same portrait has been used by many other identities and names, including a woman from the United Kingdom who’s a cancer survivor and mother of five; a licensed marriage and family therapist in Canada; a software security engineer at Quora; a journalist on Twitter/X; and a marketing expert in Canada.
Cocofinder[.]com is a people-search service that launched in Sept. 2019, through Alibaba in China. Cocofinder lists its market officer as Harriet Chan, but Ms. Chan’s LinkedIn profile is just as sparse on work history as the other people-search owners mentioned already. An image search online shows that outside of LinkedIn, the profile photo for Ms. Chan has only ever appeared in articles at pay-to-play media sites, like this one from outbackteambuilding.com.
Perhaps because Cocodoc and Cocosign both sell software services, they are actually tied to a physical presence in the real world — in Singapore (15 Scotts Rd. #03-12 15, Singapore). But it’s difficult to discern much from this address alone.
Who’s behind all this people-search chicanery? A January 2024 review of various people-search services at the website techjury.com states that Cocofinder is a wholly-owned subsidiary of a Chinese company called Shenzhen Duiyun Technology Co.
“Though it only finds results from the United States, users can choose between four main search methods,” Techjury explains. Those include people search, phone, address and email lookup. This claim is supported by a Reddit post from three years ago, wherein the Reddit user “ProtectionAdvanced” named the same Chinese company.
Is Shenzhen Duiyun Technology Co. responsible for all these phony profiles? How many more fake companies and profiles are connected to this scheme? KrebsOnSecurity found other examples that didn’t appear directly tied to other fake executives listed here, but which nevertheless are registered through Alibaba and seek to drive traffic to Spokeo and other data brokers. For example, there’s the winsome Daniela Sawyer, founder of FindPeopleFast[.]net, whose profile is flogged in paid stories at entrepreneur.org.
Google currently turns up nothing else for in a search for Shenzhen Duiyun Technology Co. Please feel free to sound off in the comments if you have any more information about this entity, such as how to contact it. Or reach out directly at krebsonsecurity @ gmail.com.
A mind map highlighting the key points of research in this story. Click to enlarge. Image: KrebsOnSecurity.com
It appears the purpose of this network is to conceal the location of people in China who are seeking to generate affiliate commissions when someone visits one of their sites and purchases a people-search report at Spokeo, for example. And it is clear that Spokeo and others have created incentives wherein anyone can effectively white-label their reports, and thereby make money brokering access to peoples’ personal information.
Spokeo’s Wikipedia page says the company was founded in 2006 by four graduates from Stanford University. Spokeo co-founder and current CEO Harrison Tang has not yet responded to requests for comment.
Intelius is owned by San Diego based PeopleConnect Inc., which also owns Classmates.com, USSearch, TruthFinder and Instant Checkmate. PeopleConnect Inc. in turn is owned by H.I.G. Capital, a $60 billion private equity firm. Requests for comment were sent to H.I.G. Capital. This story will be updated if they respond.
BeenVerified is owned by a New York City based holding company called The Lifetime Value Co., a marketing and advertising firm whose brands include PeopleLooker, NeighborWho, Ownerly, PeopleSmart, NumberGuru, and Bumper, a car history site.
Ross Cohen, chief operating officer at The Lifetime Value Co., said it’s likely the network of suspicious people-finder sites was set up by an affiliate. Cohen said Lifetime Value would investigate to determine if this particular affiliate was driving them any sign-ups.
All of the above people-search services operate similarly. When you find the person you’re looking for, you are put through a lengthy (often 10-20 minute) series of splash screens that require you to agree that these reports won’t be used for employment screening or in evaluating new tenant applications. Still more prompts ask if you are okay with seeing “potentially shocking” details about the subject of the report, including arrest histories and photos.
Only at the end of this process does the site disclose that viewing the report in question requires signing up for a monthly subscription, which is typically priced around $35. Exactly how and from where these major people-search websites are getting their consumer data — and customers — will be the subject of further reporting here.
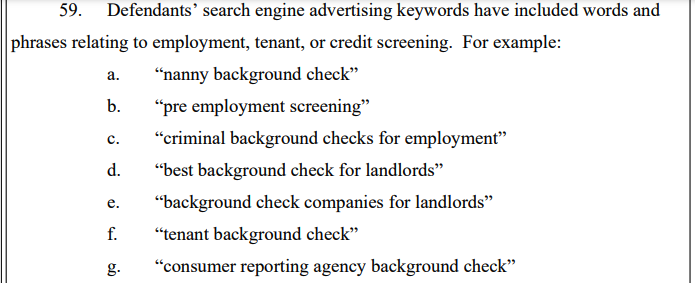
The main reason these various people-search sites require you to affirm that you won’t use their reports for hiring or vetting potential tenants is that selling reports for those purposes would classify these firms as consumer reporting agencies (CRAs) and expose them to regulations under the Fair Credit Reporting Act (FCRA).
These data brokers do not want to be treated as CRAs, and for this reason their people search reports typically don’t include detailed credit histories, financial information, or full Social Security Numbers (Radaris reports include the first six digits of one’s SSN).
But in September 2023, the U.S. Federal Trade Commission found that TruthFinder and Instant Checkmate were trying to have it both ways. The FTC levied a $5.8 million penalty against the companies for allegedly acting as CRAs because they assembled and compiled information on consumers into background reports that were marketed and sold for employment and tenant screening purposes.
The FTC also found TruthFinder and Instant Checkmate deceived users about background report accuracy. The FTC alleges these companies made millions from their monthly subscriptions using push notifications and marketing emails that claimed that the subject of a background report had a criminal or arrest record, when the record was merely a traffic ticket.
The FTC said both companies deceived customers by providing “Remove” and “Flag as Inaccurate” buttons that did not work as advertised. Rather, the “Remove” button removed the disputed information only from the report as displayed to that customer; however, the same item of information remained visible to other customers who searched for the same person.
The FTC also said that when a customer flagged an item in the background report as inaccurate, the companies never took any steps to investigate those claims, to modify the reports, or to flag to other customers that the information had been disputed.
There are a growing number of online reputation management companies that offer to help customers remove their personal information from people-search sites and data broker databases. There are, no doubt, plenty of honest and well-meaning companies operating in this space, but it has been my experience that a great many people involved in that industry have a background in marketing or advertising — not privacy.
Also, some so-called data privacy companies may be wolves in sheep’s clothing. On March 14, KrebsOnSecurity published an abundance of evidence indicating that the CEO and founder of the data privacy company OneRep.com was responsible for launching dozens of people-search services over the years.
Finally, some of the more popular people-search websites are notorious for ignoring requests from consumers seeking to remove their information, regardless of which reputation or removal service you use. Some force you to create an account and provide more information before you can remove your data. Even then, the information you worked hard to remove may simply reappear a few months later.
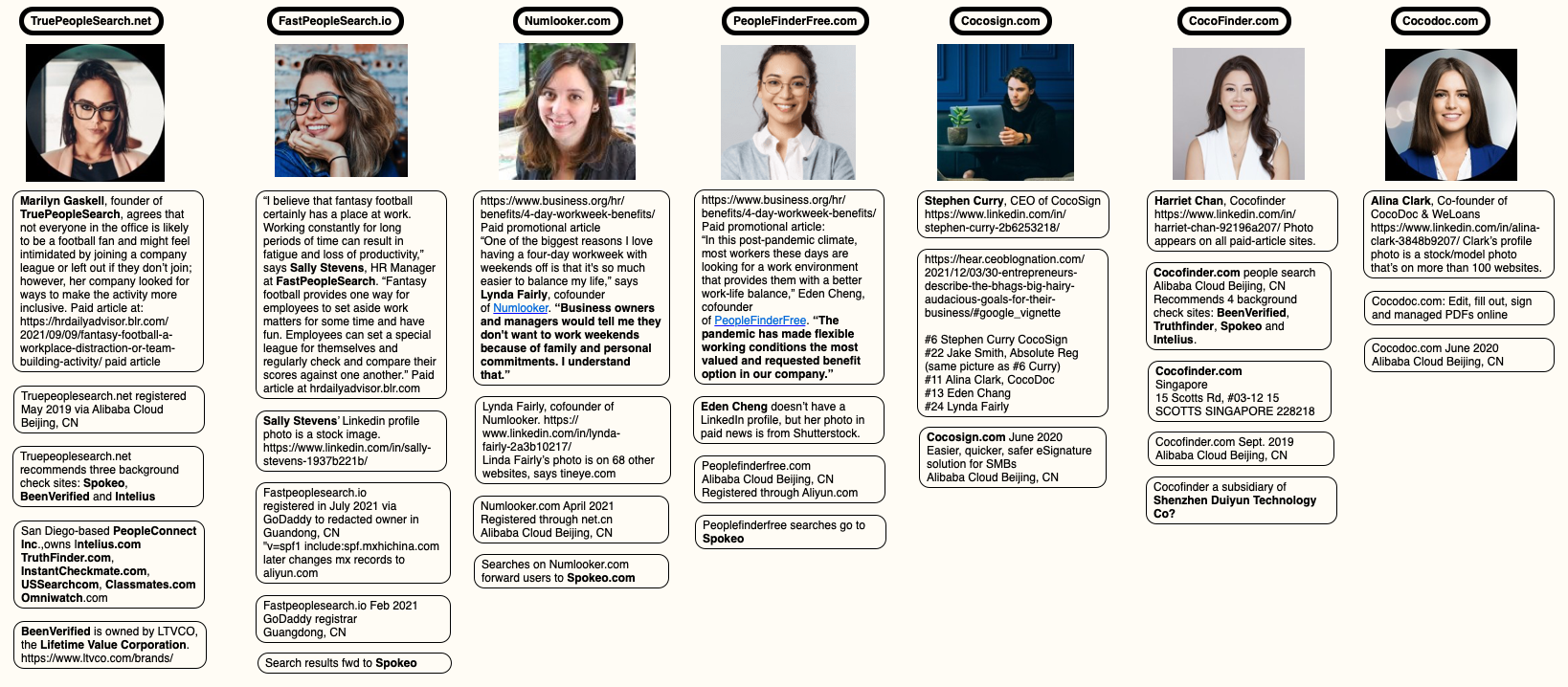
This aptly describes countless complaints lodged against the data broker and people search giant Radaris. On March 8, KrebsOnSecurity profiled the co-founders of Radaris, two Russian brothers in Massachusetts who also operate multiple Russian-language dating services and affiliate programs.
The truth is that these people-search companies will continue to thrive unless and until Congress begins to realize it’s time for some consumer privacy and data protection laws that are relevant to life in the 21st century. Duke University adjunct professor Justin Sherman says virtually all state privacy laws exempt records that might be considered “public” or “government” documents, including voting registries, property filings, marriage certificates, motor vehicle records, criminal records, court documents, death records, professional licenses, bankruptcy filings, and more.
“Consumer privacy laws in California, Colorado, Connecticut, Delaware, Indiana, Iowa, Montana, Oregon, Tennessee, Texas, Utah, and Virginia all contain highly similar or completely identical carve-outs for ‘publicly available information’ or government records,” Sherman said.
If you live in the United States, the data broker Radaris likely knows a great deal about you, and they are happy to sell what they know to anyone. But how much do we know about Radaris? Publicly available data indicates that in addition to running a dizzying array of people-search websites, the co-founders of Radaris operate multiple Russian-language dating services and affiliate programs. It also appears many of their businesses have ties to a California marketing firm that works with a Russian state-run media conglomerate currently sanctioned by the U.S. government.
Formed in 2009, Radaris is a vast people-search network for finding data on individuals, properties, phone numbers, businesses and addresses. Search for any American’s name in Google and the chances are excellent that a listing for them at Radaris.com will show up prominently in the results.
Radaris reports typically bundle a substantial amount of data scraped from public and court documents, including any current or previous addresses and phone numbers, known email addresses and registered domain names. The reports also list address and phone records for the target’s known relatives and associates. Such information could be useful if you were trying to determine the maiden name of someone’s mother, or successfully answer a range of other knowledge-based authentication questions.
Currently, consumer reports advertised for sale at Radaris.com are being fulfilled by a different people-search company called TruthFinder. But Radaris also operates a number of other people-search properties — like Centeda.com — that sell consumer reports directly and behave almost identically to TruthFinder: That is, reel the visitor in with promises of detailed background reports on people, and then charge a $34.99 monthly subscription fee just to view the results.
The Better Business Bureau (BBB) assigns Radaris a rating of “F” for consistently ignoring consumers seeking to have their information removed from Radaris’ various online properties. Of the 159 complaints detailed there in the last year, several were from people who had used third-party identity protection services to have their information removed from Radaris, only to receive a notice a few months later that their Radaris record had been restored.
What’s more, Radaris’ automated process for requesting the removal of your information requires signing up for an account, potentially providing more information about yourself that the company didn’t already have (see screenshot above).
Radaris has not responded to requests for comment.
Radaris, TruthFinder and others like them all force users to agree that their reports will not be used to evaluate someone’s eligibility for credit, or a new apartment or job. This language is so prominent in people-search reports because selling reports for those purposes would classify these firms as consumer reporting agencies (CRAs) and expose them to regulations under the Fair Credit Reporting Act (FCRA).
These data brokers do not want to be treated as CRAs, and for this reason their people search reports typically do not include detailed credit histories, financial information, or full Social Security Numbers (Radaris reports include the first six digits of one’s SSN).
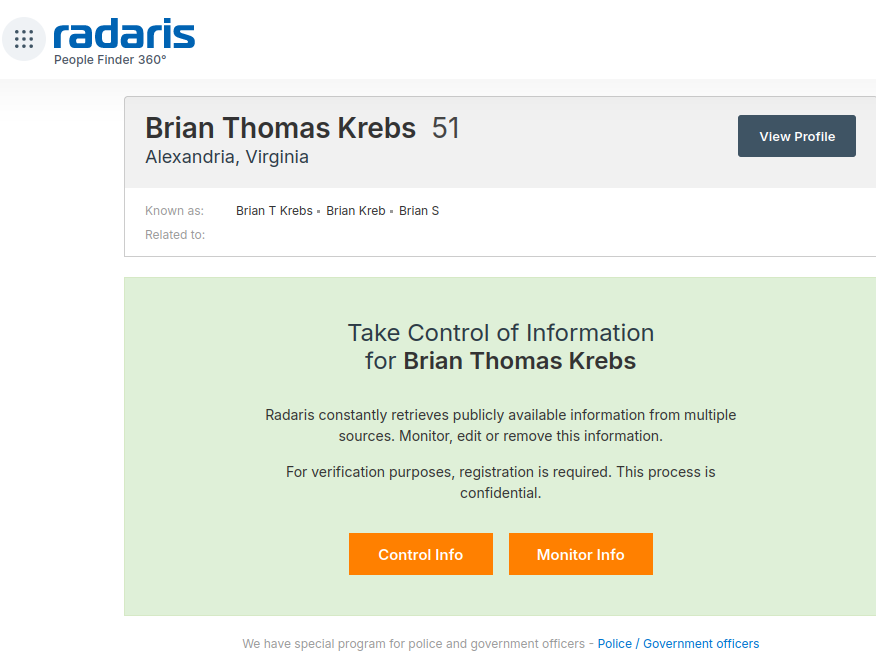
But in September 2023, the U.S. Federal Trade Commission found that TruthFinder and another people-search service Instant Checkmate were trying to have it both ways. The FTC levied a $5.8 million penalty against the companies for allegedly acting as CRAs because they assembled and compiled information on consumers into background reports that were marketed and sold for employment and tenant screening purposes.
An excerpt from the FTC’s complaint against TruthFinder and Instant Checkmate.
The FTC also found TruthFinder and Instant Checkmate deceived users about background report accuracy. The FTC alleges these companies made millions from their monthly subscriptions using push notifications and marketing emails that claimed that the subject of a background report had a criminal or arrest record, when the record was merely a traffic ticket.
“All the while, the companies touted the accuracy of their reports in online ads and other promotional materials, claiming that their reports contain “the MOST ACCURATE information available to the public,” the FTC noted. The FTC says, however, that all the information used in their background reports is obtained from third parties that expressly disclaim that the information is accurate, and that TruthFinder and Instant Checkmate take no steps to verify the accuracy of the information.
The FTC said both companies deceived customers by providing “Remove” and “Flag as Inaccurate” buttons that did not work as advertised. Rather, the “Remove” button removed the disputed information only from the report as displayed to that customer; however, the same item of information remained visible to other customers who searched for the same person.
The FTC also said that when a customer flagged an item in the background report as inaccurate, the companies never took any steps to investigate those claims, to modify the reports, or to flag to other customers that the information had been disputed.
According to Radaris’ profile at the investor website Pitchbook.com, the company’s founder and “co-chief executive officer” is a Massachusetts resident named Gary Norden, also known as Gary Nard.
An analysis of email addresses known to have been used by Mr. Norden shows he is a native Russian man whose real name is Igor Lybarsky (also spelled Lubarsky). Igor’s brother Dmitry, who goes by “Dan,” appears to be the other co-CEO of Radaris. Dmitry Lybarsky’s Facebook/Meta account says he was born in March 1963.

The Lybarsky brothers Dmitry or “Dan” (left) and Igor a.k.a. “Gary,” in an undated photo.
Indirectly or directly, the Lybarskys own multiple properties in both Sherborn and Wellesley, Mass. However, the Radaris website is operated by an offshore entity called Bitseller Expert Ltd, which is incorporated in Cyprus. Neither Lybarsky brother responded to requests for comment.
A review of the domain names registered by Gary Norden shows that beginning in the early 2000s, he and Dan built an e-commerce empire by marketing prepaid calling cards and VOIP services to Russian expatriates who are living in the United States and seeking an affordable way to stay in touch with loved ones back home.
In 2012, the main company in charge of providing those calling services — Wellesley Hills, Mass-based Unipoint Technology Inc. — was fined $179,000 by the U.S. Federal Communications Commission, which said Unipoint never applied for a license to provide international telecommunications services.
DomainTools.com shows the email address gnard@unipointtech.com is tied to 137 domains, including radaris.com. DomainTools also shows that the email addresses used by Gary Norden for more than two decades — epop@comby.com, gary@barksy.com and gary1@eprofit.com, among others — appear in WHOIS registration records for an entire fleet of people-search websites, including: centeda.com, virtory.com, clubset.com, kworld.com, newenglandfacts.com, and pub360.com.
Still more people-search platforms tied to Gary Norden– like publicreports.com and arrestfacts.com — currently funnel interested customers to third-party search companies, such as TruthFinder and PersonTrust.com.
The email addresses used by Gary Nard/Gary Norden are also connected to a slew of data broker websites that sell reports on businesses, real estate holdings, and professionals, including bizstanding.com, homemetry.com, trustoria.com, homeflock.com, rehold.com, difive.com and projectlab.com.
Domain records indicate that Gary and Dan for many years operated a now-defunct pay-per-click affiliate advertising network called affiliate.ru. That entity used domain name servers tied to the aforementioned domains comby.com and eprofit.com, as did radaris.ru.
A machine-translated version of Affiliate.ru, a Russian-language site that advertised hundreds of money making affiliate programs, including the Comfi.com prepaid calling card affiliate.
Comby.com used to be a Russian language social media network that looked a great deal like Facebook. The domain now forwards visitors to Privet.ru (“hello” in Russian), a dating site that claims to have 5 million users. Privet.ru says it belongs to a company called Dating Factory, which lists offices in Switzerland. Privet.ru uses the Gary Norden domain eprofit.com for its domain name servers.
Dating Factory’s website says it sells “powerful dating technology” to help customers create unique or niche dating websites. A review of the sample images available on the Dating Factory homepage suggests the term “dating” in this context refers to adult websites. Dating Factory also operates a community called FacebookOfSex, as well as the domain analslappers.com.
Email addresses for the Comby and Eprofit domains indicate Gary Norden operates an entity in Wellesley Hills, Mass. called RussianAmerican Holding Inc. (russianamerica.com). This organization is listed as the owner of the domain newyork.ru, which is a site dedicated to orienting newcomers from Russia to the Big Apple.
Newyork.ru’s terms of service refer to an international calling card company called ComFi Inc. (comfi.com) and list an address as PO Box 81362 Wellesley Hills, Ma. Other sites that include this address are russianamerica.com, russianboston.com, russianchicago.com, russianla.com, russiansanfran.com, russianmiami.com, russiancleveland.com and russianseattle.com (currently offline).
ComFi is tied to Comfibook.com, which was a search aggregator website that collected and published data from many online and offline sources, including phone directories, social networks, online photo albums, and public records.
The current website for russianamerica.com. Note the ad in the bottom left corner of this image for Channel One, a Russian state-owned media firm that is currently sanctioned by the U.S. government.
Many of the U.S. city-specific online properties apparently tied to Gary Norden include phone numbers on their contact pages for a pair of Russian media and advertising firms based in southern California. The phone number 323-874-8211 appears on the websites russianla.com, russiasanfran.com, and rosconcert.com, which sells tickets to theater events performed in Russian.
Historic domain registration records from DomainTools show rosconcert.com was registered in 2003 to Unipoint Technologies — the same company fined by the FCC for not having a license. Rosconcert.com also lists the phone number 818-377-2101.
A phone number just a few digits away — 323-874-8205 — appears as a point of contact on newyork.ru, russianmiami.com, russiancleveland.com, and russianchicago.com. A search in Google shows this 82xx number range — and the 818-377-2101 number — belong to two different entities at the same UPS Store mailbox in Tarzana, Calif: American Russian Media Inc. (armediacorp.com), and Lamedia.biz.
Armediacorp.com is the home of FACT Magazine, a glossy Russian-language publication put out jointly by the American-Russian Business Council, the Hollywood Chamber of Commerce, and the West Hollywood Chamber of Commerce.
Lamedia.biz says it is an international media organization with more than 25 years of experience within the Russian-speaking community on the West Coast. The site advertises FACT Magazine and the Russian state-owned media outlet Channel One. Clicking the Channel One link on the homepage shows Lamedia.biz offers to submit advertising spots that can be shown to Channel One viewers. The price for a basic ad is listed at $500.
In May 2022, the U.S. government levied financial sanctions against Channel One that bar US companies or citizens from doing business with the company.
The website of lamedia.biz offers to sell advertising on two Russian state-owned media firms currently sanctioned by the U.S. government.
In 2014, a group of people sued Radaris in a class-action lawsuit claiming the company’s practices violated the Fair Credit Reporting Act. Court records indicate the defendants never showed up in court to dispute the claims, and as a result the judge eventually awarded the plaintiffs a default judgement and ordered the company to pay $7.5 million.
But the plaintiffs in that civil case had a difficult time collecting on the court’s ruling. In response, the court ordered the radaris.com domain name (~9.4M monthly visitors) to be handed over to the plaintiffs.
However, in 2018 Radaris was able to reclaim their domain on a technicality. Attorneys for the company argued that their clients were never named as defendants in the original lawsuit, and so their domain could not legally be taken away from them in a civil judgment.
“Because our clients were never named as parties to the litigation, and were never served in the litigation, the taking of their property without due process is a violation of their rights,” Radaris’ attorneys argued.
In October 2023, an Illinois resident filed a class-action lawsuit against Radaris for allegedly using people’s names for commercial purposes, in violation of the Illinois Right of Publicity Act.
On Feb. 8, 2024, a company called Atlas Data Privacy Corp. sued Radaris LLC for allegedly violating “Daniel’s Law,” a statute that allows New Jersey law enforcement, government personnel, judges and their families to have their information completely removed from people-search services and commercial data brokers. Atlas has filed at least 140 similar Daniel’s Law complaints against data brokers recently.
Daniel’s Law was enacted in response to the death of 20-year-old Daniel Anderl, who was killed in a violent attack targeting a federal judge (his mother). In July 2020, a disgruntled attorney who had appeared before U.S. District Judge Esther Salas disguised himself as a Fedex driver, went to her home and shot and killed her son (the judge was unharmed and the assailant killed himself).
Earlier this month, The Record reported on Atlas Data Privacy’s lawsuit against LexisNexis Risk Data Management, in which the plaintiffs representing thousands of law enforcement personnel in New Jersey alleged that after they asked for their information to remain private, the data broker retaliated against them by freezing their credit and falsely reporting them as identity theft victims.
Another data broker sued by Atlas Data Privacy — pogodata.com — announced on Mar. 1 that it was likely shutting down because of the lawsuit.
“The matter is far from resolved but your response motivates us to try to bring back most of the names while preserving redaction of the 17,000 or so clients of the redaction company,” the company wrote. “While little consolation, we are not alone in the suit – the privacy company sued 140 property-data sites at the same time as PogoData.”
Atlas says their goal is convince more states to pass similar laws, and to extend those protections to other groups such as teachers, healthcare personnel and social workers. Meanwhile, media law experts say they’re concerned that enacting Daniel’s Law in other states would limit the ability of journalists to hold public officials accountable, and allow authorities to pursue criminals charges against media outlets that publish the same type of public and governments records that fuel the people-search industry.
There are some pending changes to the US legal and regulatory landscape that could soon reshape large swaths of the data broker industry. But experts say it is unlikely that any of these changes will affect people-search companies like Radaris.
On Feb. 28, 2024, the White House issued an executive order that directs the U.S. Department of Justice (DOJ) to create regulations that would prevent data brokers from selling or transferring abroad certain data types deemed too sensitive, including genomic and biometric data, geolocation and financial data, as well as other as-yet unspecified personal identifiers. The DOJ this week published a list of more than 100 questions it is seeking answers to regarding the data broker industry.
In August 2023, the Consumer Financial Protection Bureau (CFPB) announced it was undertaking new rulemaking related to data brokers.
Justin Sherman, an adjunct professor at Duke University, said neither the CFPB nor White House rulemaking will likely address people-search brokers because these companies typically get their information by scouring federal, state and local government records. Those government files include voting registries, property filings, marriage certificates, motor vehicle records, criminal records, court documents, death records, professional licenses, bankruptcy filings, and more.
“These dossiers contain everything from individuals’ names, addresses, and family information to data about finances, criminal justice system history, and home and vehicle purchases,” Sherman wrote in an October 2023 article for Lawfare. “People search websites’ business pitch boils down to the fact that they have done the work of compiling data, digitizing it, and linking it to specific people so that it can be searched online.”
Sherman said while there are ongoing debates about whether people search data brokers have legal responsibilities to the people about whom they gather and sell data, the sources of this information — public records — are completely carved out from every single state consumer privacy law.
“Consumer privacy laws in California, Colorado, Connecticut, Delaware, Indiana, Iowa, Montana, Oregon, Tennessee, Texas, Utah, and Virginia all contain highly similar or completely identical carve-outs for ‘publicly available information’ or government records,” Sherman wrote. “Tennessee’s consumer data privacy law, for example, stipulates that “personal information,” a cornerstone of the legislation, does not include ‘publicly available information,’ defined as:
“…information that is lawfully made available through federal, state, or local government records, or information that a business has a reasonable basis to believe is lawfully made available to the general public through widely distributed media, by the consumer, or by a person to whom the consumer has disclosed the information, unless the consumer has restricted the information to a specific audience.”
Sherman said this is the same language as the carve-out in the California privacy regime, which is often held up as the national leader in state privacy regulations. He said with a limited set of exceptions for survivors of stalking and domestic violence, even under California’s newly passed Delete Act — which creates a centralized mechanism for consumers to ask some third-party data brokers to delete their information — consumers across the board cannot exercise these rights when it comes to data scraped from property filings, marriage certificates, and public court documents, for example.
“With some very narrow exceptions, it’s either extremely difficult or impossible to compel these companies to remove your information from their sites,” Sherman told KrebsOnSecurity. “Even in states like California, every single consumer privacy law in the country completely exempts publicly available information.”
Below is a mind map that helped KrebsOnSecurity track relationships between and among the various organizations named in the story above:
Three Americans were charged this week with stealing more than $400 million in a November 2022 SIM-swapping attack. The U.S. government did not name the victim organization, but there is every indication that the money was stolen from the now-defunct cryptocurrency exchange FTX, which had just filed for bankruptcy on that same day.
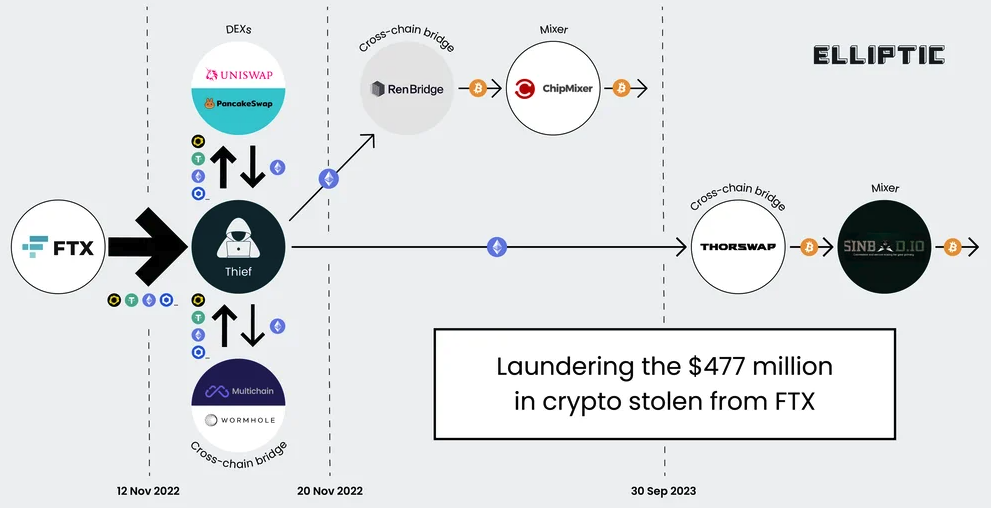
A graphic illustrating the flow of more than $400 million in cryptocurrencies stolen from FTX on Nov. 11-12, 2022. Image: Elliptic.co.
An indictment unsealed this week and first reported on by Ars Technica alleges that Chicago man Robert Powell, a.k.a. “R,” “R$” and “ElSwapo1,” was the ringleader of a SIM-swapping group called the “Powell SIM Swapping Crew.” Colorado resident Emily “Em” Hernandez allegedly helped the group gain access to victim devices in service of SIM-swapping attacks between March 2021 and April 2023. Indiana resident Carter Rohn, a.k.a. “Carti,” and “Punslayer,” allegedly assisted in compromising devices.
In a SIM-swapping attack, the crooks transfer the target’s phone number to a device they control, allowing them to intercept any text messages or phone calls sent to the victim, including one-time passcodes for authentication or password reset links sent via SMS.
The indictment states that the perpetrators in this heist stole the $400 million in cryptocurrencies on Nov. 11, 2022 after they SIM-swapped an AT&T customer by impersonating them at a retail store using a fake ID. However, the document refers to the victim in this case only by the name “Victim 1.”
Wired’s Andy Greenberg recently wrote about FTX’s all-night race to stop a $1 billion crypto heist that occurred on the evening of November 11:
“FTX’s staff had already endured one of the worst days in the company’s short life. What had recently been one of the world’s top cryptocurrency exchanges, valued at $32 billion only 10 months earlier, had just declared bankruptcy. Executives had, after an extended struggle, persuaded the company’s CEO, Sam Bankman-Fried, to hand over the reins to John Ray III, a new chief executive now tasked with shepherding the company through a nightmarish thicket of debts, many of which it seemed to have no means to pay.”
“FTX had, it seemed, hit rock bottom. Until someone—a thief or thieves who have yet to be identified—chose that particular moment to make things far worse. That Friday evening, exhausted FTX staffers began to see mysterious outflows of the company’s cryptocurrency, publicly captured on the Etherscan website that tracks the Ethereum blockchain, representing hundreds of millions of dollars worth of crypto being stolen in real time.”
The indictment says the $400 million was stolen over several hours between November 11 and 12, 2022. Tom Robinson, co-founder of the blockchain intelligence firm Elliptic, said the attackers in the FTX heist began to drain FTX wallets on the evening of Nov. 11, 2022 local time, and continuing until the 12th of November.
Robinson said Elliptic is not aware of any other crypto heists of that magnitude occurring on that date.
“We put the value of the cryptoassets stolen at $477 million,” Robinson said. “The FTX administrators have reported overall losses due to “unauthorized third-party transfers” of $413 million – the discrepancy is likely due to subsequent seizure and return of some of the stolen assets. Either way, it’s certainly over $400 million, and we are not aware of any other thefts from crypto exchanges on this scale, on this date.”
The SIM-swappers allegedly responsible for the $400 million crypto theft are all U.S. residents. But there are some indications they had help from organized cybercriminals based in Russia. In October 2023, Elliptic released a report that found the money stolen from FTX had been laundered through exchanges with ties to criminal groups based in Russia.
“A Russia-linked actor seems a stronger possibility,” Elliptic wrote. “Of the stolen assets that can be traced through ChipMixer, significant amounts are combined with funds from Russia-linked criminal groups, including ransomware gangs and darknet markets, before being sent to exchanges. This points to the involvement of a broker or other intermediary with a nexus in Russia.”
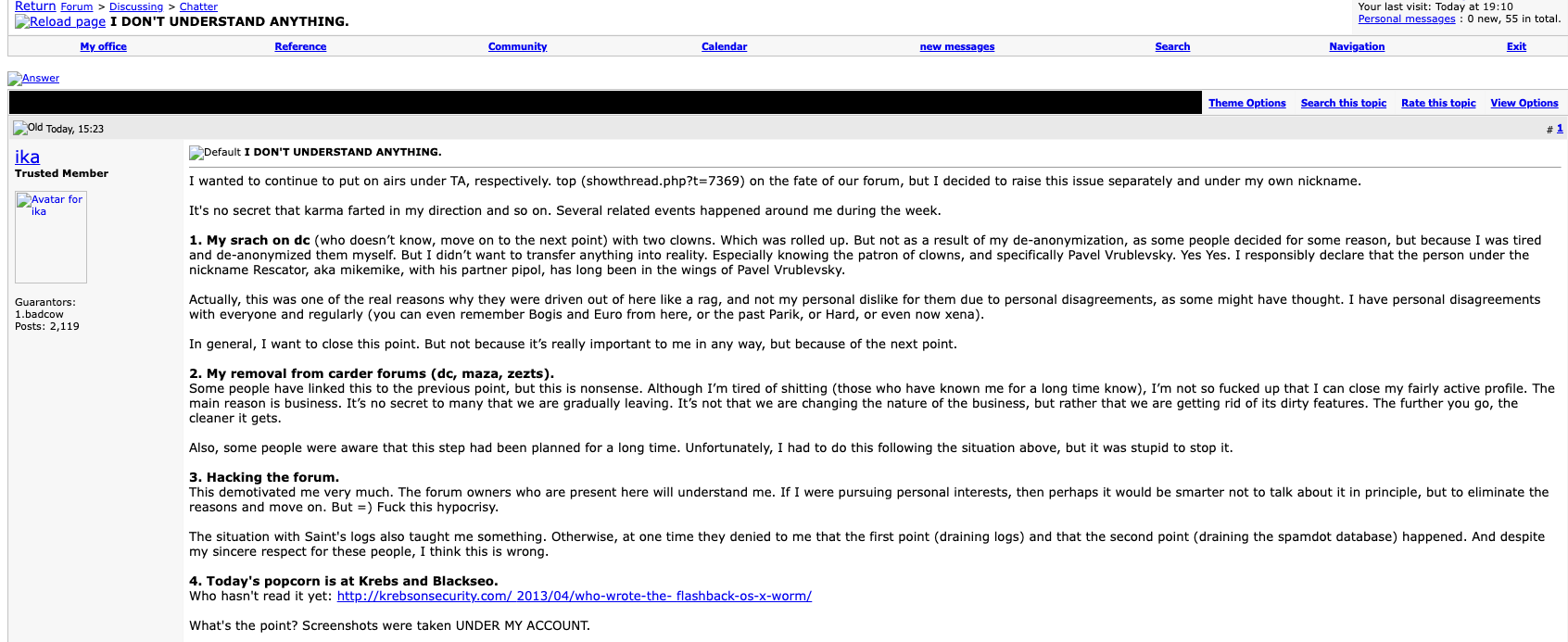
Nick Bax, director of analytics at the cryptocurrency wallet recovery firm Unciphered, said the flow of stolen FTX funds looks more like what his team has seen from groups based in Eastern Europe and Russian than anything they’ve witnessed from US-based SIM-swappers.
“I was a bit surprised by this development but it seems to be consistent with reports from CISA [the Cybersecurity and Infrastructure Security Agency] and others that “Scattered Spider” has worked with [ransomware] groups like ALPHV/BlackCat,” Bax said.
CISA’s alert on Scattered Spider says they are a cybercriminal group that targets large companies and their contracted information technology (IT) help desks.
“Scattered Spider threat actors, per trusted third parties, have typically engaged in data theft for extortion and have also been known to utilize BlackCat/ALPHV ransomware alongside their usual TTPs,” CISA said, referring to the group’s signature “Tactics, Techniques an Procedures.”
Nick Bax, posting on Twitter/X in Nov 2022 about his research on the $400 million FTX heist.
Earlier this week, KrebsOnSecurity published a story noting that a Florida man recently charged with being part of a SIM-swapping conspiracy is thought to be a key member of Scattered Spider, a hacking group also known as 0ktapus. That group has been blamed for a string of cyber intrusions at major U.S. technology companies during the summer of 2022.
Financial claims involving FTX’s bankruptcy proceedings are being handled by the financial and risk consulting giant Kroll. In August 2023, Kroll suffered its own breach after a Kroll employee was SIM-swapped. According to Kroll, the thieves stole user information for multiple cryptocurrency platforms that rely on Kroll services to handle bankruptcy proceedings.
KrebsOnSecurity sought comment for this story from Kroll, the FBI, the prosecuting attorneys, and Sullivan & Cromwell, the law firm handling the FTX bankruptcy. This story will be updated in the event any of them respond.
Attorneys for Mr. Powell said they do not know who Victim 1 is in the indictment, as the government hasn’t shared that information yet. Powell’s next court date is a detention hearing on Feb. 2, 2024.
Update, Feb. 3, 12:19 p.m. ET: The FBI declined a request to comment.
In 2020, the United States brought charges against four men accused of building a bulletproof hosting empire that once dominated the Russian cybercrime industry and supported multiple organized cybercrime groups. All four pleaded guilty to conspiracy and racketeering charges. But there is a fascinating and untold backstory behind the two Russian men involved, who co-ran the world’s top spam forum and worked closely with Russia’s most dangerous cybercriminals.
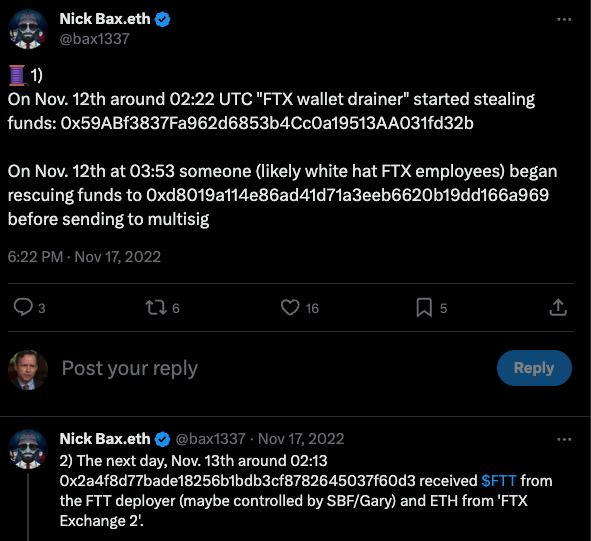
From January 2005 to April 2013, there were two primary administrators of the cybercrime forum Spamdot (a.k.a Spamit), an invite-only community for Russian-speaking people in the businesses of sending spam and building botnets of infected computers to relay said spam. The Spamdot admins went by the nicknames Icamis (a.k.a. Ika), and Salomon (a.k.a. Sal).
Spamdot forum administrator “Ika” a.k.a. “Icamis” responds to a message from “Tarelka,” the botmaster behind the Rustock botnet. Dmsell said: “I’m actually very glad that I switched to legal spam mailing,” prompting Tarelka and Ika to scoff.
As detailed in my 2014 book, Spam Nation, Spamdot was home to crooks controlling some of the world’s nastiest botnets, global malware contagions that went by exotic names like Rustock, Cutwail, Mega-D, Festi, Waledac, and Grum.
Icamis and Sal were in daily communications with these botmasters, via the Spamdot forum and private messages. Collectively in control over millions of spam-spewing zombies, those botmasters also continuously harvested passwords and other data from infected machines.
As we’ll see in a moment, Salomon is now behind bars, in part because he helped to rob dozens of small businesses in the United States using some of those same harvested passwords. He is currently housed in a federal prison in Michigan, serving the final stretch of a 60-month sentence.
But the identity and whereabouts of Icamis have remained a mystery to this author until recently. For years, security experts — and indeed, many top cybercriminals in the Spamit affiliate program — have expressed the belief that Sal and Icamis were likely the same person using two different identities. And there were many good reasons to support this conclusion.
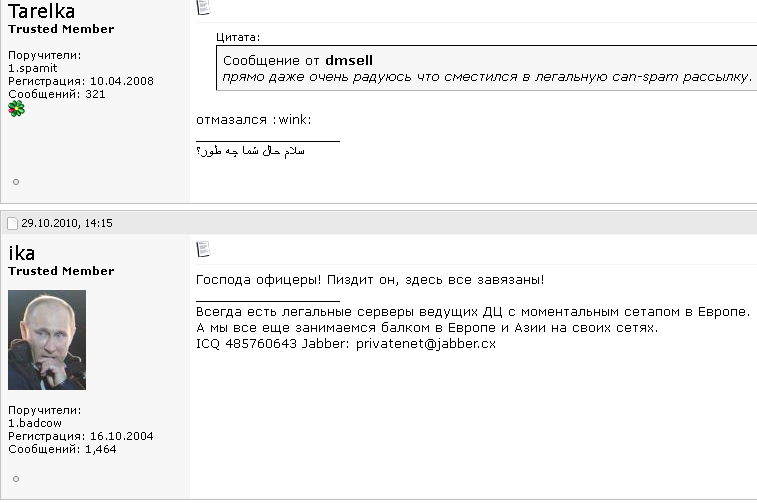
For example, in 2010 Spamdot and its spam affiliate program Spamit were hacked, and its user database shows Sal and Icamis often accessed the forum from the same Internet address — usually from Cherepovets, an industrial town situated approximately 230 miles north of Moscow. Also, it was common for Icamis to reply when Spamdot members communicated a request or complaint to Sal, and vice versa.
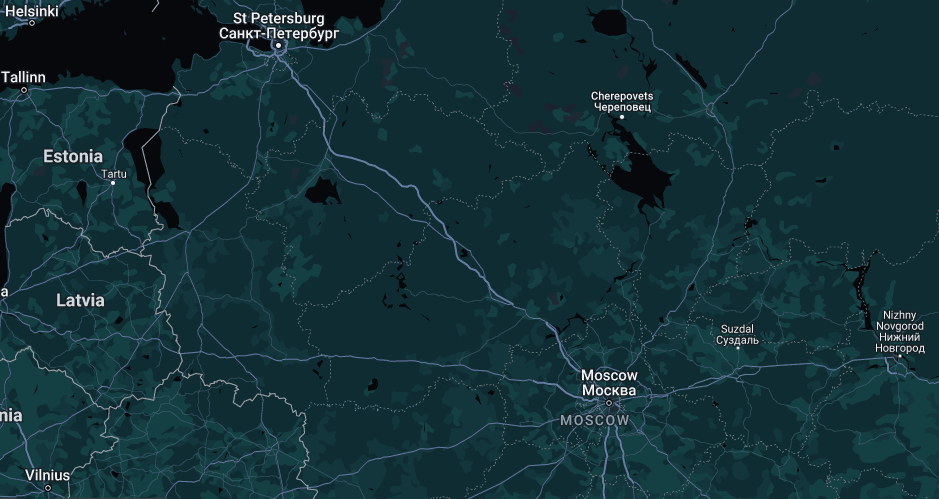
Image: maps.google.com
Still, other clues suggested Icamis and Sal were two separate individuals. For starters, they frequently changed the status on their instant messenger clients at different times. Also, they each privately discussed with others having attended different universities.
KrebsOnSecurity began researching Icamis’s real-life identity in 2012, but failed to revisit any of that research until recently. In December 2023, KrebsOnSecurity published new details about the identity of “Rescator,” a Russian cybercriminal who is thought to be closely connected to the 2013 data breach at Target.
That story mentioned Rescator’s real-life identity was exposed by Icamis in April 2013, as part of a lengthy farewell letter Ika wrote to Spamdot members wherein Ika said he was closing the forum and quitting the cybercrime business entirely.
To no one’s shock, Icamis didn’t quit the business: He simply became more quiet and circumspect about his work, which increasingly was focused on helping crime groups siphon funds from U.S. bank accounts. But the Rescator story was a reminder that 10 years worth of research on who Ika/Icamis is in real life had been completely set aside. This post is an attempt to remedy that omission.
The farewell post from Ika (aka Icamis), the administrator of both the BlackSEO forum and Pustota, the successor forum to Spamit/Spamdot.
Icamis and Sal offered a comprehensive package of goods and services that any aspiring or accomplished spammer would need on a day-to-day basis: Virtually unlimited bulletproof domain registration and hosting services, as well as services that helped botmasters evade spam block lists generated by anti-spam groups like Spamhaus.org. Here’s snippet of Icamis’s ad on Spamdot from Aug. 2008, wherein he addresses forum members with the salutation, “Hello Gentlemen Scammers.”
We are glad to present you our services!
Many are already aware (and are our clients), but publicity is never superfluous.Domains.
– all major gtlds (com, net, org, info, biz)
– many interesting and uninteresting cctlds
– options for any topic
– processing of any quantities
– guarantees
– exceptionally low prices for domains for white and gray schemes (including any SEO and affiliate spam )
– control panel with balances and auto-registration
– all services under the Ikamis brand, proven over the years;)Servers.
– long-term partnerships with several [data centers] in several parts of the world for any topic
– your own data center (no longer in Russia ;)) for gray and white topics
– any configuration and any hardware
– your own IP networks (PI, not PA) and full legal support
– realtime backups to neutral sites
– guarantees and full responsibility for the services provided
– non-standard equipment on request
– our own admins to resolve any technical issues (services are free for clients)
– hosting (shared and vps) is also possibleNon-standard and related services.
– ssl certificates signed by geotrust and thawte
– old domains (any year, any quantity)
– beautiful domains (keyword, short, etc.)
– domains with indicators (any, for SEO, etc.)
– making unstable gtld domains stable
– interception and hijacking of custom domains (expensive)
– full domain posting via web.archive.org with restoration of native content (preliminary applications)
– any updates to our panels to suit your needs upon request (our own coders)All orders for the “Domains” sections and “Servers” are carried out during the day (depending on our workload).
For non-standard and related services, a preliminary application is required 30 days in advance (except for ssl certificates – within 24 hours).
Icamis and Sal frequently claimed that their service kept Spamhaus and other anti-spam groups several steps behind their operations. But it’s clear that those anti-spam operations had a real and painful impact on spam revenues, and Salomon was obsessed with striking back at anti-spam groups, particularly Spamhaus.
In 2007, Salomon collected more than $3,000 from botmasters affiliated with competing spam affiliate programs that wanted to see Spamhaus suffer, and the money was used to fund a week-long distributed denial-of-service (DDoS) attack against Spamhaus and its online infrastructure. But rather than divert their spam botnets from their normal activity and thereby decrease sales, the botmasters voted to create a new DDoS botnet by purchasing installations of DDoS malware on thousands of already-hacked PCs (at a rate of $25 per 1,000 installs).
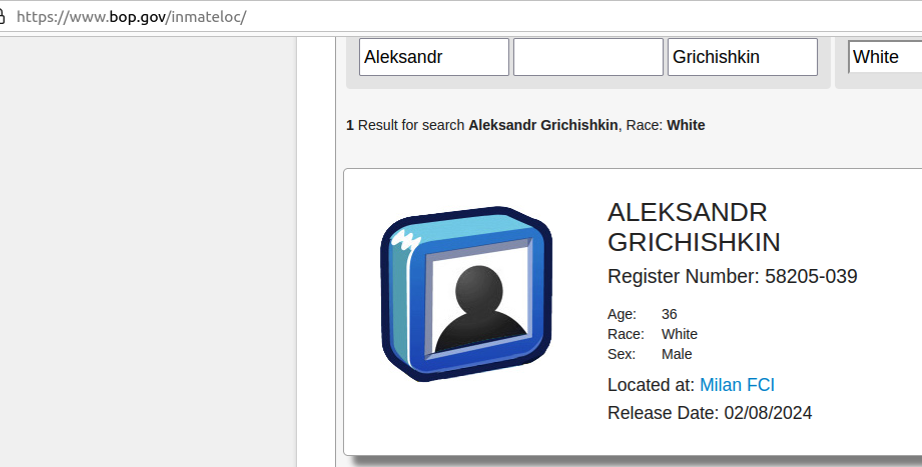
As an affiliate of Spamdot, Salomon used the email address ad1@safe-mail.net, and the password 19871987gr. The breach tracking service Constella Intelligence found the password 19871987gr was used by the email address grichishkin@gmail.com. Multiple accounts are registered to that email address under the name Alexander Valerievich Grichishkin, from Cherepovets.
In 2020, Grichishkin was arrested outside of Russia on a warrant for providing bulletproof hosting services to cybercriminal gangs. The U.S. government said Grichishkin and three others set up the infrastructure used by cybercriminals between 2009 to 2015 to distribute malware and attack financial institutions and victims throughout the United States.
Those clients included crooks using malware like Zeus, SpyEye, Citadel and the Blackhole exploit kit to build botnets and steal banking credentials.
“The Organization and its members helped their clients to access computers without authorization, steal financial information (including banking credentials), and initiate unauthorized wire transfers from victims’ financial accounts,” the government’s complaint stated.
Grichishkin pleaded guilty to conspiracy charges and was sentenced to four years in prison. He is 36 years old, has a wife and kids in Thailand, and is slated for release on February 8, 2024.
The identity of Icamis came into view when KrebsOnSecurity began focusing on clues that might connect Icamis to Cherepovets (Ika’s apparent hometown based on the Internet addresses he regularly used to access Spamdot).
Historic domain ownership records from DomainTools.com reveal that many of the email addresses and domains connected to Icamis invoke the name “Andrew Artz,” including icamis[.]ws, icamis[.]ru, and icamis[.]biz. Icamis promoted his services in 2003 — such as bulk-domains[.]info — using the email address icamis@4host.info. From one of his ads in 2005:
Domains For Projects Advertised By Spam
I can register bulletproof domains for sites and projects advertised by spam(of course they must be legal). I can not provide DNS for u, only domains. The price will be:
65$ for domain[if u will buy less than 5 domains]
50$ for domain[more than 5 domains]
45$ for domain[more than 10 domains]
These prices are for domains in the .net & .com zones.
If u want to order domains write me to: icamis@4host.info
In 2009, an “Andrew Artz” registered at the hosting service FirstVDS.com using the email address icamis@4host.info, with a notation saying the company name attached to the account was “WMPay.” Likewise, the bulletproof domain service icamis[.]ws was registered to an Andrew Artz.
The domain wmpay.ru is registered to the phonetically similar name “Andrew Hertz,” at andrew@wmpay.ru. A search on “icamis.ru” in Google brings up a 2003 post by him on a discussion forum designed by and for students of Amtek, a secondary school in Cherepovets (Icamis was commenting from an Internet address in Cherepovets).
The website amtek-foreva-narod.ru is still online, and it links to several yearbooks for Amtek graduates. It states that the yearbook for the Amtek class of 2004 is hosted at 41.wmpay[.]com.
The yearbook photos for the Amtek class of 2004 are not indexed in the Wayback Machine at archive.org, but the names and nicknames of 16 students remain. However, it appears that the entry for one student — the Wmpay[.]com site administrator — was removed at some point.
In 2004, the administrator of the Amtek discussion forum — a 2003 graduate who used the handle “Grand” — observed that there were three people named Andrey who graduated from Amtek in 2004, but one of them was conspicuously absent from the yearbook at wmpay[.]ru: Andrey Skvortsov.
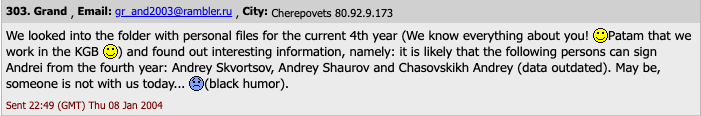
To bring this full circle, Icamis was Andrey Skvortsov, the other Russian man charged alongside Grichiskin (the two others who pleaded guilty to conspiracy charges were from Estonia and Lithuania). All of the defendants in that case pleaded guilty to conspiracy to engage in a Racketeer Influenced Corrupt Organization (RICO).
[Author’s note: No doubt government prosecutors had their own reasons for omitting the nicknames of the defendants in their press releases, but that information sure would have saved me a lot of time and effort].
Skvortsov was sentenced to time served, and presumably deported. His current whereabouts are unknown and he was not reachable for comment via his known contact addresses.
The government says Ika and Sal’s bulletproof hosting empire provided extensive support for a highly damaging cybercrime group known as the JabberZeus Crew, which worked closely with the author of the Zeus Trojan — Evgeniy Mikhailovich Bogachev — to develop a then-advanced strain of the Zeus malware that was designed to defeat one-time codes for authentication. Bogachev is a top Russian cybercriminal with a standing $3 million bounty on his head from the FBI.
The JabberZeus Crew stole money by constantly recruiting money mules, people in the United States and in Europe who could be enticed or tricked into forwarding money stolen from cybercrime victims. Interestingly, Icamis’s various email addresses are connected to websites for a vast network of phony technology companies that claimed they needed people with bank accounts to help pay their overseas employees.
Icamis used the email address tech@safe-mail.net on Spamdot, and this email address is tied to the registration records for multiple phony technology companies that were set up to recruit money mules.
One such site — sun-technology[.]net — advertised itself as a Hong Kong-based electronics firm that was looking for “honest, responsible and motivated people in UK, USA, AU and NZ to be Sales Representatives in your particular region and receive payments from our clients. Agent commission is 5 percent of total amount received to the personal bank account. You may use your existing bank account or open a new one for these purposes.”
In January 2010, KrebsOnSecurity broke the news that the JabberZeus crew had just used money mules to steal $500,000 from tiny Duanesburg Central School District in upstate New York. As part of his sentence, Skvortsov was ordered to pay $497,200 in restitution to the Duanesburg Central School District.
The JabberZeus Crew operated mainly out of the eastern Ukraine city of Donetsk, which was always pro-Russia and is now occupied by Russian forces. But when Russia invaded Ukraine in February 2022, the alleged leader of the notorious cybercrime gang — Vyacheslav Igoravich Andreev (a.ka. Penchukov) — fled his mandatory military service orders and was arrested in Geneva, Switzerland. He is currently in federal custody awaiting trial, and is slated to be arraigned in U.S. federal court tomorrow (Jan. 9, 2024). A copy of the indictment against Andreev is here (PDF).

Andreev, aka “Tank,” seen here performing as a DJ in Ukraine in an undated photo from social media.