


ESET researchers spot an updated version of the malware loader used in the Industroyer2 and CaddyWiper attacks
The post Sandworm uses a new version of ArguePatch to attack targets in Ukraine appeared first on WeLiveSecurity
Listen to Aryeh Goretsky, Martin Smolár, and Jean-Ian Boutin discuss what UEFI threats are capable of and what the ESPecter bootkit tells us about their evolution
The post ESET Research Podcast: UEFI in crosshairs of ESPecter bootkit appeared first on WeLiveSecurity
The U.S. Department of Justice (DOJ) recently revised its policy on charging violations of the Computer Fraud and Abuse Act (CFAA), a 1986 law that remains the primary statute by which federal prosecutors pursue cybercrime cases. The new guidelines state that prosecutors should avoid charging security researchers who operate in “good faith” when finding and reporting vulnerabilities. But legal experts continue to advise researchers to proceed with caution, noting the new guidelines can’t be used as a defense in court, nor are they any kind of shield against civil prosecution.
In a statement about the changes, Deputy Attorney General Lisa O. Monaco said the DOJ “has never been interested in prosecuting good-faith computer security research as a crime,” and that the new guidelines “promote cybersecurity by providing clarity for good-faith security researchers who root out vulnerabilities for the common good.”
What constitutes “good faith security research?” The DOJ’s new policy (PDF) borrows language from a Library of Congress rulemaking (PDF) on the Digital Millennium Copyright Act (DMCA), a similarly controversial law that criminalizes production and dissemination of technologies or services designed to circumvent measures that control access to copyrighted works. According to the government, good faith security research means:
“…accessing a computer solely for purposes of good-faith testing, investigation, and/or correction of a security flaw or vulnerability, where such activity is carried out in a manner designed to avoid any harm to individuals or the public, and where the information derived from the activity is used primarily to promote the security or safety of the class of devices, machines, or online services to which the accessed computer belongs, or those who use such devices, machines, or online services.”
“Security research not conducted in good faith — for example, for the purpose of discovering security holes in devices, machines, or services in order to extort the owners of such devices, machines, or services — might be called ‘research,’ but is not in good faith.”
The new DOJ policy comes in response to a Supreme Court ruling last year in Van Buren v. United States (PDF), a case involving a former police sergeant in Florida who was convicted of CFAA violations after a friend paid him to use police resources to look up information on a private citizen.
But in an opinion authored by Justice Amy Coney Barrett, the Supreme Court held that the CFAA does not apply to a person who obtains electronic information that they are otherwise authorized to access and then misuses that information.
Orin Kerr, a law professor at University of California, Berkeley, said the DOJ’s updated policy was expected given the Supreme Court ruling in the Van Buren case. Kerr noted that while the new policy says one measure of “good faith” involves researchers taking steps to prevent harm to third parties, what exactly those steps might constitute is another matter.
“The DOJ is making clear they’re not going to prosecute good faith security researchers, but be really careful before you rely on that,” Kerr said. “First, because you could still get sued [civilly, by the party to whom the vulnerability is being reported], but also the line as to what is legitimate security research and what isn’t is still murky.”
Kerr said the new policy also gives CFAA defendants no additional cause for action.
“A lawyer for the defendant can make the pitch that something is good faith security research, but it’s not enforceable,” Kerr said. “Meaning, if the DOJ does bring a CFAA charge, the defendant can’t move to dismiss it on the grounds that it’s good faith security research.”
Kerr added that he can’t think of a CFAA case where this policy would have made a substantive difference.
“I don’t think the DOJ is giving up much, but there’s a lot of hacking that could be covered under good faith security research that they’re saying they won’t prosecute, and it will be interesting to see what happens there,” he said.
The new policy also clarifies other types of potential CFAA violations that are not to be charged. Most of these include violations of a technology provider’s terms of service, and here the DOJ says “violating an access restriction contained in a term of service are not themselves sufficient to warrant federal criminal charges.” Some examples include:
-Embellishing an online dating profile contrary to the terms of service of the dating website;
-Creating fictional accounts on hiring, housing, or rental websites;
-Using a pseudonym on a social networking site that prohibits them;
-Checking sports scores or paying bills at work.
Kerr’s warning about the dangers that security researchers face from civil prosecution is well-founded. KrebsOnSecurity regularly hears from security researchers seeking advice on how to handle reporting a security vulnerability or data exposure. In most of these cases, the researcher isn’t worried that the government is going to come after them: It’s that they’re going to get sued by the company responsible for the security vulnerability or data leak.
Often these conversations center around the researcher’s desire to weigh the rewards of gaining recognition for their discoveries with the risk of being targeted with costly civil lawsuits. And almost just as often, the source of the researcher’s unease is that they recognize they might have taken their discovery just a tad too far.
Here’s a common example: A researcher finds a vulnerability in a website that allows them to individually retrieve every customer record in a database. But instead of simply polling a few records that could be used as a proof-of-concept and shared with the vulnerable website, the researcher decides to download every single file on the server.
Not infrequently, there is also concern because at some point the researcher suspected that their automated activities might have actually caused stability or uptime issues with certain services they were testing. Here, the researcher is usually concerned about approaching the vulnerable website or vendor because they worry their activities may already have been identified internally as some sort of external cyberattack.
What do I take away from these conversations? Some of the most trusted and feared security researchers in the industry today gained that esteem not by constantly taking things to extremes and skirting the law, but rather by publicly exercising restraint in the use of their powers and knowledge — and by being effective at communicating their findings in a way that maximizes the help and minimizes the potential harm.
If you believe you’ve discovered a security vulnerability or data exposure, try to consider first how you might defend your actions to the vulnerable website or vendor before embarking on any automated or semi-automated activity that the organization might reasonably misconstrue as a cyberattack. In other words, try as best you can to minimize the potential harm to the vulnerable site or vendor in question, and don’t go further than you need to prove your point.
Previously unknown macOS malware uses cloud storage as its C&C channel and to exfiltrate documents, keystrokes, and screen captures from compromised Macs
The post I see what you did there: A look at the CloudMensis macOS spyware appeared first on WeLiveSecurity
Listen to Cameron Camp, Juraj Jánošík, and Filip Mazán discuss the use of machine learning in cybersecurity, followed by Cameron’s insights into the security of medical devices
The post ESET Research Podcast: Hot security topics at RSA or mostly hype? appeared first on WeLiveSecurity



Focused mostly on Asia, this new cyberespionage group uses undocumented tools, including steganographically extracting PowerShell payloads from PNG files
The post Worok: The big picture appeared first on WeLiveSecurity
Misconfigured remote access services continue to give bad actors an easy access path to company networks – here’s how you can minimize your exposure to attacks misusing Remote Desktop Protocol
The post RDP on the radar: An up‑close view of evolving remote access threats appeared first on WeLiveSecurity
ESET researchers have uncovered another tool in the already extensive arsenal of the SparklingGoblin APT group: a Linux variant of the SideWalk backdoor
The post You never walk alone: The SideWalk backdoor gets a Linux variant appeared first on WeLiveSecurity
ESET researchers have discovered Lazarus attacks against targets in the Netherlands and Belgium that use spearphishing emails connected to fake job offers
The post Amazon‑themed campaigns of Lazarus in the Netherlands and Belgium appeared first on WeLiveSecurity
ESET researchers analyzed previously undocumented custom backdoors and cyberespionage tools deployed in Israel by the POLONIUM APT group
The post POLONIUM targets Israel with Creepy malware appeared first on WeLiveSecurity
APT-C-50’s Domestic Kitten campaign continues, targeting Iranian citizens with a new version of the FurBall malware masquerading as an Android translation app
The post Domestic Kitten campaign spying on Iranian citizens with new FurBall malware appeared first on WeLiveSecurity
Malicious apps used in this active campaign exfiltrate contacts, SMS messages, recorded phone calls, and even chat messages from apps such as Signal, Viber, and Telegram
The post Bahamut cybermercenary group targets Android users with fake VPN apps appeared first on WeLiveSecurity
ESET researchers uncover Dolphin, a sophisticated backdoor extending the arsenal of the ScarCruft APT group
The post Who’s swimming in South Korean waters? Meet ScarCruft’s Dolphin appeared first on WeLiveSecurity
ESET researchers analyzed a supply-chain attack abusing an Israeli software developer to deploy Fantasy, Agrius’s new wiper, with victims including the diamond industry
The post Fantasy – a new Agrius wiper deployed through a supply‑chain attack appeared first on WeLiveSecurity
ESET researchers discovered a spearphishing campaign targeting Japanese political entities a few weeks before the House of Councillors elections, and in the process uncovered a previously undescribed MirrorFace credential stealer
The post Unmasking MirrorFace: Operation LiberalFace targeting Japanese political entities appeared first on WeLiveSecurity
ESET researchers identified an active StrongPity campaign distributing a trojanized version of the Android Telegram app, presented as the Shagle app – a video-chat service that has no app version
The post StrongPity espionage campaign targeting Android users appeared first on WeLiveSecurity
ESET Research announces IPyIDA 2.0, a Python plugin integrating IPython and Jupyter Notebook into IDA
The post Introducing IPyIDA: A Python plugin for your reverse‑engineering toolkit appeared first on WeLiveSecurity
ESET researchers have identified a campaign using trojanized installers to deliver the FatalRAT malware, distributed via malicious websites linked in ads that appear in Google search results
The post These aren’t the apps you’re looking for: fake installers targeting Southeast and East Asia appeared first on WeLiveSecurity
The targeted region, and overlap in behavior and code, suggest the tool is used by the infamous North Korea-aligned APT group
The post WinorDLL64: A backdoor from the vast Lazarus arsenal? appeared first on WeLiveSecurity
And that’s just the tip of the iceberg when it comes to the trends that defined the cyberthreat landscape in the final four months of 2022.
The post ESET Research Podcast: Ransomware trashed data, Android threats soared in T3 2022 appeared first on WeLiveSecurity
The first in-the-wild UEFI bootkit bypassing UEFI Secure Boot on fully updated UEFI systems is now a reality
The post BlackLotus UEFI bootkit: Myth confirmed appeared first on WeLiveSecurity
ESET researchers tease apart MQsTTang, a new backdoor used by Mustang Panda, which communicates via the MQTT protocol
The post MQsTTang: Mustang Panda’s latest backdoor treads new ground with Qt and MQTT appeared first on WeLiveSecurity
ESET researchers analyze a cyberespionage campaign that distributes CapraRAT backdoors through trojanized and supposedly secure Android messaging apps – but also exfiltrates sensitive information
The post Love scam or espionage? Transparent Tribe lures Indian and Pakistani officials appeared first on WeLiveSecurity
ESET Research uncovered a campaign by APT group Tick against a data-loss prevention company in East Asia and found a previously unreported tool used by the group
The post The slow Tick‑ing time bomb: Tick APT group compromise of a DLP software developer in East Asia appeared first on WeLiveSecurity
ESET researchers analyzed Android and Windows clippers that can tamper with instant messages and use OCR to steal cryptocurrency funds
The post Not‑so‑private messaging: Trojanized WhatsApp and Telegram apps go after cryptocurrency wallets appeared first on WeLiveSecurity
ESET experts share their insights on the cyber-elements of the first year of the war in Ukraine and how a growing number of destructive malware variants tried to rip through critical Ukrainian systems
The post ESET Research Podcast: A year of fighting rockets, soldiers, and wipers in Ukraine appeared first on WeLiveSecurity
When decommissioning their old hardware, many companies 'throw the baby out with the bathwater'
The post Discarded, not destroyed: Old routers reveal corporate secrets appeared first on WeLiveSecurity
Similarities with newly discovered Linux malware used in Operation DreamJob corroborate the theory that the infamous North Korea-aligned group is behind the 3CX supply-chain attack
The post Linux malware strengthens links between Lazarus and the 3CX supply‑chain attack appeared first on WeLiveSecurity
ESET Research uncovers a campaign by the APT group known as Evasive Panda targeting an international NGO in China with malware delivered through updates of popular Chinese software
The post Evasive Panda APT group delivers malware via updates for popular Chinese software appeared first on WeLiveSecurity
ESET researchers discover AhRat – a new Android RAT based on AhMyth – that exfiltrates files and records audio
The post Android app breaking bad: From legitimate screen recording to file exfiltration within a year appeared first on WeLiveSecurity
ESET researchers reveal details about a prevalent cryptor, operating as a cryptor-as-a-service used by tens of malware families
The post Shedding light on AceCryptor and its operation appeared first on WeLiveSecurity
A curious case of a threat actor at the border between crimeware and cyberespionage
The post Asylum Ambuscade: crimeware or cyberespionage? appeared first on WeLiveSecurity
ESET researchers analyzed an updated version of Android GravityRAT spyware that steals WhatsApp backup files and can receive commands to delete files
The post Android GravityRAT goes after WhatsApp backups appeared first on WeLiveSecurity
A brief summary of what happened with Emotet since its comeback in November 2021
The post What’s up with Emotet? appeared first on WeLiveSecurity
A view of the H1 2023 threat landscape as seen by ESET telemetry and from the perspective of ESET threat detection and research experts
The post ESET Threat Report H1 2023 appeared first on WeLiveSecurity
A story of how an analysis of a supposed game cheat turned into the discovery of a powerful UEFI threat
The post ESET Research Podcast: Finding the mythical BlackLotus bootkit appeared first on WeLiveSecurity
In 2021, the exclusive Russian cybercrime forum Mazafaka was hacked. The leaked user database shows one of the forum’s founders was an attorney who advised Russia’s top hackers on the legal risks of their work, and what to do if they got caught. A review of this user’s hacker identities shows that during his time on the forums he served as an officer in the special forces of the GRU, the foreign military intelligence agency of the Russian Federation.
Launched in 2001 under the tagline “Network terrorism,” Mazafaka would evolve into one of the most guarded Russian-language cybercrime communities. The forum’s member roster included a Who’s Who of top Russian cybercriminals, and it featured sub-forums for a wide range of cybercrime specialities, including malware, spam, coding and identity theft.
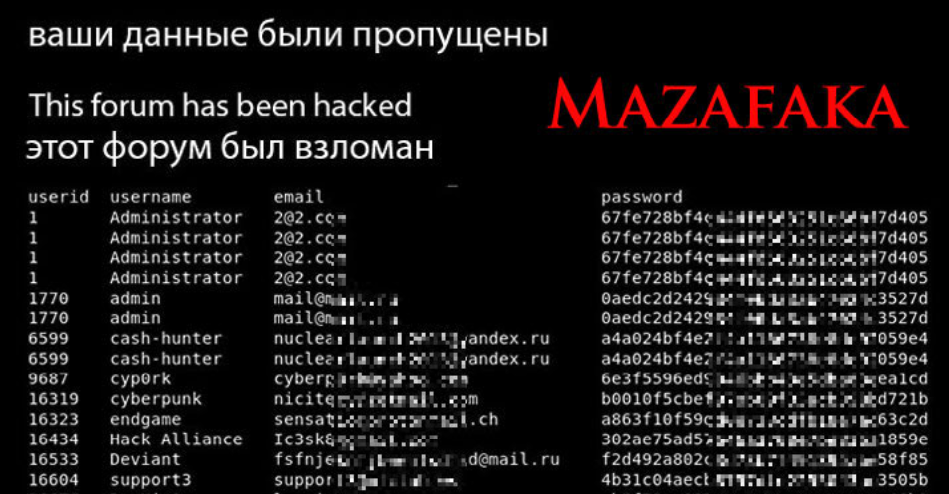
One representation of the leaked Mazafaka database.
In almost any database leak, the first accounts listed are usually the administrators and early core members. But the Mazafaka user information posted online was not a database file per se, and it was clearly edited, redacted and restructured by whoever released it. As a result, it can be difficult to tell which members are the earliest users.
The original Mazafaka is known to have been launched by a hacker using the nickname “Stalker.” However, the lowest numbered (non-admin) user ID in the Mazafaka database belongs to another individual who used the handle “Djamix,” and the email address djamix@mazafaka[.]ru.
From the forum’s inception until around 2008, Djamix was one of its most active and eloquent contributors. Djamix told forum members he was a lawyer, and nearly all of his posts included legal analyses of various public cases involving hackers arrested and charged with cybercrimes in Russia and abroad.
“Hiding with purely technical parameters will not help in a serious matter,” Djamix advised Maza members in September 2007. “In order to ESCAPE the law, you need to KNOW the law. This is the most important thing. Technical capabilities cannot overcome intelligence and cunning.”
Stalker himself credited Djamix with keeping Mazafaka online for so many years. In a retrospective post published to Livejournal in 2014 titled, “Mazafaka, from conception to the present day,” Stalker said Djamix had become a core member of the community.
“This guy is everywhere,” Stalker said of Djamix. “There’s not a thing on [Mazafaka] that he doesn’t take part in. For me, he is a stimulus-irritant and thanks to him, Maza is still alive. Our rallying force!”
Djamix told other forum denizens he was a licensed attorney who could be hired for remote or in-person consultations, and his posts on Mazafaka and other Russian boards show several hackers facing legal jeopardy likely took him up on this offer.
“I have the right to represent your interests in court,” Djamix said on the Russian-language cybercrime forum Verified in Jan. 2011. “Remotely (in the form of constant support and consultations), or in person – this is discussed separately. As well as the cost of my services.”
A search on djamix@mazafaka[.]ru at DomainTools.com reveals this address has been used to register at least 10 domain names since 2008. Those include several websites about life in and around Sochi, Russia, the site of the 2014 Winter Olympics, as well as a nearby coastal town called Adler. All of those sites say they were registered to an Aleksei Safronov from Sochi who also lists Adler as a hometown.
The breach tracking service Constella Intelligence finds that the phone number associated with those domains — +7.9676442212 — is tied to a Facebook account for an Aleksei Valerievich Safronov from Sochi. Mr. Safronov’s Facebook profile, which was last updated in October 2022, says his ICQ instant messenger number is 53765. This is the same ICQ number assigned to Djamix in the Mazafaka user database.
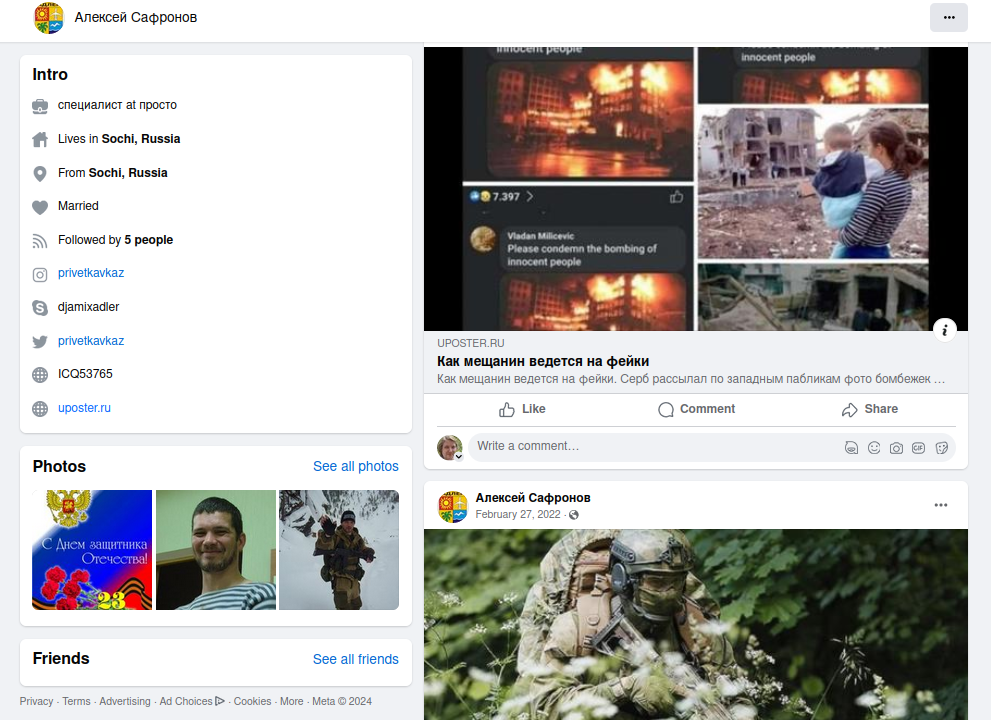
The Facebook account for Aleksey Safronov.
A “Djamix” account on the forum privetsochi[.]ru (“Hello Sochi”) says this user was born Oct. 2, 1970, and that his website is uposter[.]ru. This Russian language news site’s tagline is, “We Create Communication,” and it focuses heavily on news about Sochi, Adler, Russia and the war in Ukraine, with a strong pro-Kremlin bent.
Safronov’s Facebook profile also gives his Skype username as “Djamixadler,” and it includes dozens of photos of him dressed in military fatigues along with a regiment of soldiers deploying in fairly remote areas of Russia. Some of those photos date back to 2008.
In several of the images, we can see a patch on the arm of Safronov’s jacket that bears the logo of the Spetsnaz GRU, a special forces unit of the Russian military. According to a 2020 report from the Congressional Research Service, the GRU operates both as an intelligence agency — collecting human, cyber, and signals intelligence — and as a military organization responsible for battlefield reconnaissance and the operation of Russia’s Spetsnaz military commando units.

Mr. Safronov posted this image of himself on Facebook in 2016. The insignia of the GRU can be seen on his sleeve.
“In recent years, reports have linked the GRU to some of Russia’s most aggressive and public intelligence operations,” the CRS report explains. “Reportedly, the GRU played a key role in Russia’s occupation of Ukraine’s Crimea region and invasion of eastern Ukraine, the attempted assassination of former Russian intelligence officer Sergei Skripal in the United Kingdom, interference in the 2016 U.S. presidential elections, disinformation and propaganda operations, and some of the world’s most damaging cyberattacks.”
According to the Russia-focused investigative news outlet Meduza, in 2014 the Russian Defense Ministry created its “information-operation troops” for action in “cyber-confrontations with potential adversaries.”
“Later, sources in the Defense Ministry explained that these new troops were meant to ‘disrupt the potential adversary’s information networks,'” Meduza reported in 2018. “Recruiters reportedly went looking for ‘hackers who have had problems with the law.'”
Mr. Safronov did not respond to multiple requests for comment. A 2018 treatise written by Aleksei Valerievich Safronov titled “One Hundred Years of GRU Military Intelligence” explains the significance of the bat in the seal of the GRU.
“One way or another, the bat is an emblem that unites all active and retired intelligence officers; it is a symbol of unity and exclusivity,” Safronov wrote. “And, in general, it doesn’t matter who we’re talking about – a secret GRU agent somewhere in the army or a sniper in any of the special forces brigades. They all did and are doing one very important and responsible thing.”
It’s unclear what role Mr. Safronov plays or played in the GRU, but it seems likely the military intelligence agency would have exploited his considerable technical skills, knowledge and connections on the Russian cybercrime forums.
Searching on Safronov’s domain uposter[.]ru in Constella Intelligence reveals that this domain was used in 2022 to register an account at a popular Spanish-language discussion forum dedicated to helping applicants prepare for a career in the Guardia Civil, one of Spain’s two national police forces. Pivoting on that Russian IP in Constella shows three other accounts were created at the same Spanish user forum around the same date.
Mark Rasch is a former cybercrime prosecutor for the U.S. Department of Justice who now serves as chief legal officer for the New York cybersecurity firm Unit 221B. Rasch said there has always been a close relationship between the GRU and the Russian hacker community, noting that in the early 2000s the GRU was soliciting hackers with the skills necessary to hack US banks in order to procure funds to help finance Russia’s war in Chechnya.
“The guy is heavily hooked into the Russian cyber community, and that’s useful for intelligence services,” Rasch said. “He could have been infiltrating the community to monitor it for the GRU. Or he could just be a guy wearing a military uniform.”