
As an avid internet surfer, you’ve most likely heard of cookies. No, we’re not talking about the ones filled with chocolate chips. We’re talking about the ones that allow you to log in to your favorite websites. Cookies may impact your online security, so check out these tips to manage them and keep your online accounts safe.
Ever wonder how a website saves the items you placed in your shopping cart last week, even though you closed the tab before making the purchase? This is made possible by cookies. According to the Federal Trade Commission, a cookie is information saved by your web browser. When you visit a website, the site may place a cookie on your web browser so it can recognize your device in the future. If you return to that site later, it can read that cookie to remember you from your last visit, keeping track of your activities over time.1
Cookies come in either the first-party or third-party variety. There’s no difference between the two in how they function, but rather in where and how you encountered them. First-party cookies belong to sites you visited first-hand in your browser. Third-party cookies, or “tracking cookies,” generally come from third-party advertising websites.
Although cookies generally function the same, there are technically two different types of cookies. Magic cookies refer to packets of information that are sent and received without changes. Historically, this would be used to log in to a computer database system, such as an internal business network. This concept predates the modern cookie we use today.
HTTP cookies are a repurposed version of the magic cookie built for internet browsing and managing online experiences. HTTP cookies help web developers give you more personalized, convenient website experiences. They allow sites to remember you, your website logins, and shopping carts so you can pick back up where you left off from your last visit. However, cybercriminals can manipulate HTTP cookies to spy on your online activity and steal your personal information.
Cookie hijacking (also known as session hijacking) is typically initiated when a cybercriminal sends you a fake login page. If you click the fake link, the thief can steal the cookie and capture anything you type while on the fraudulent website. Like a phishing attack, cookie hijacking allows a cybercriminal to steal personal information like usernames, passwords, and other important data held within the cookie. If you enter your information while on the fake website, the criminal can then put that cookie in their browser and impersonate you online. They may even change your credentials, locking you out of your account.
Sometimes, criminals initiate cookie hijacking attacks without a fake link. If you’re browsing on an unsecured, public Wi-Fi connection, hackers can easily steal your data that’s traveling through the connection. This can happen even if the site is secure and your username and password are encrypted.
Because the data in cookies doesn’t change, cookies themselves aren’t harmful. They can’t infect computers with viruses or malware. But if your cookies are hijacked as part of a cyberattack, a criminal could gain access to your browsing history and use cookies as the key to enter your locked accounts. For example, a hacker may steal your identity or confidential company information, purchase items in your online shopping carts, or loot your bank account.
Preventing cookie hijacking attacks can allow you to browse the internet with greater peace of mind. Follow these tips to not only safeguard your personal information but to also enhance your browsing experience:
Make it a habit to clear your cookie cache regularly to prevent cookie overload, which could slow your search speeds. Also, almost every browser has the option to enable/disable cookies on your computer. So if you don’t want them at all, your browser’s support section can walk you through how to disable them.
Although it’s convenient to not have to re-type your credentials into a website you frequently visit, autofill features could make it easier for a criminal to extract your data with cookie hijacking. Plus, autofill is risky if your physical device falls into the wrong hands. To browse more securely without having to constantly reenter your passwords, use a password manager like McAfee True Key. True Key makes it so you only have to remember one master password, and it encrypts the rest in a vault protected by one of the most secure encryption algorithms available.
Strong, unique passwords for each of your accounts, updated regularly, offer ample protection against hackers. Multi-factor authentication (MFA) adds yet another layer of security by double-checking your identity beyond your username and password, usually with a texted or emailed code. When your accounts offer MFA, always opt in.
Criminals can hijack your cookies if you’re browsing on an unsecured, public Wi-Fi connection. To prevent a criminal from swiping your data, use a virtual private network (VPN), a service that protects your data and privacy online. A VPN creates an encrypted tunnel that makes you anonymous by masking your IP address while connecting to public Wi-Fi hotspots. This is a great way to shield your information from online spies while you’re banking, shopping, or handling any kind of sensitive information online.
McAfee LiveSafe is an antivirus solution that protects your computer and mobile devices from suspicious web cookies by:
is an antivirus solution that protects your computer and mobile devices from suspicious web cookies by:
The post What Are Browser Cookies and How Do I Manage Them? appeared first on McAfee Blog.
Thread hijacking attacks. They happen when someone you know has their email account compromised, and you are suddenly dropped into an existing conversation between the sender and someone else. These missives draw on the recipient’s natural curiosity about being copied on a private discussion, which is modified to include a malicious link or attachment. Here’s the story of a thread hijacking attack in which a journalist was copied on a phishing email from the unwilling subject of a recent scoop.
In Sept. 2023, the Pennsylvania news outlet LancasterOnline.com published a story about Adam Kidan, a wealthy businessman with a criminal past who is a major donor to Republican causes and candidates, including Rep. Lloyd Smucker (R-Pa).
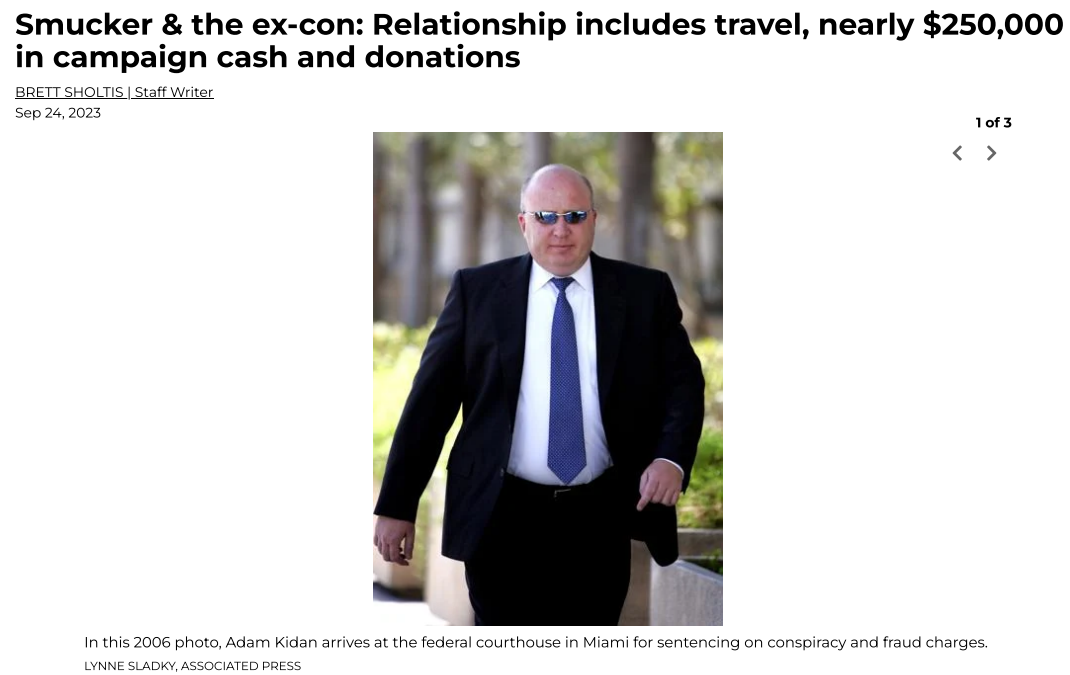
The LancasterOnline story about Adam Kidan.
Several months after that piece ran, the story’s author Brett Sholtis received two emails from Kidan, both of which contained attachments. One of the messages appeared to be a lengthy conversation between Kidan and a colleague, with the subject line, “Re: Successfully sent data.” The second missive was a more brief email from Kidan with the subject, “Acknowledge New Work Order,” and a message that read simply, “Please find the attached.”
Sholtis said he clicked the attachment in one of the messages, which then launched a web page that looked exactly like a Microsoft Office 365 login page. An analysis of the webpage reveals it would check any submitted credentials at the real Microsoft website, and return an error if the user entered bogus account information. A successful login would record the submitted credentials and forward the victim to the real Microsoft website.
But Sholtis said he didn’t enter his Outlook username and password. Instead, he forwarded the messages to LancasterOneline’s IT team, which quickly flagged them as phishing attempts.
LancasterOnline Executive Editor Tom Murse said the two phishing messages from Mr. Kidan raised eyebrows in the newsroom because Kidan had threatened to sue the news outlet multiple times over Sholtis’s story.
“We were just perplexed,” Murse said. “It seemed to be a phishing attempt but we were confused why it would come from a prominent businessman we’ve written about. Our initial response was confusion, but we didn’t know what else to do with it other than to send it to the FBI.”
The phishing lure attached to the thread hijacking email from Mr. Kidan.
In 2006, Kidan was sentenced to 70 months in federal prison after pleading guilty to defrauding lenders along with Jack Abramoff, the disgraced lobbyist whose corruption became a symbol of the excesses of Washington influence peddling. He was paroled in 2009, and in 2014 moved his family to a home in Lancaster County, Pa.
The FBI hasn’t responded to LancasterOnline’s tip. Messages sent by KrebsOnSecurity to Kidan’s emails addresses were returned as blocked. Messages left with Mr. Kidan’s company, Empire Workforce Solutions, went unreturned.
No doubt the FBI saw the messages from Kidan for what they likely were: The result of Mr. Kidan having his Microsoft Outlook account compromised and used to send malicious email to people in his contacts list.
Thread hijacking attacks are hardly new, but that is mainly true because many Internet users still don’t know how to identify them. The email security firm Proofpoint says it has tracked north of 90 million malicious messages in the last five years that leverage this attack method.
One key reason thread hijacking is so successful is that these attacks generally do not include the tell that exposes most phishing scams: A fabricated sense of urgency. A majority of phishing threats warn of negative consequences should you fail to act quickly — such as an account suspension or an unauthorized high-dollar charge going through.
In contrast, thread hijacking campaigns tend to patiently prey on the natural curiosity of the recipient.
Ryan Kalember, chief strategy officer at Proofpoint, said probably the most ubiquitous examples of thread hijacking are “CEO fraud” or “business email compromise” scams, wherein employees are tricked by an email from a senior executive into wiring millions of dollars to fraudsters overseas.
But Kalember said these low-tech attacks can nevertheless be quite effective because they tend to catch people off-guard.
“It works because you feel like you’re suddenly included in an important conversation,” Kalember said. “It just registers a lot differently when people start reading, because you think you’re observing a private conversation between two different people.”
Some thread hijacking attacks actually involve multiple threat actors who are actively conversing while copying — but not addressing — the recipient.
“We call these multi-persona phishing scams, and they’re often paired with thread hijacking,” Kalember said. “It’s basically a way to build a little more affinity than just copying people on an email. And the longer the conversation goes on, the higher their success rate seems to be because some people start replying to the thread [and participating] psycho-socially.”
The best advice to sidestep phishing scams is to avoid clicking on links or attachments that arrive unbidden in emails, text messages and other mediums. If you’re unsure whether the message is legitimate, take a deep breath and visit the site or service in question manually — ideally, using a browser bookmark so as to avoid potential typosquatting sites.