As the majority of the global Covid fog finally started lifting in 2022, other events – and their associated risks – started to fill the headspace of C-level execs the world over. In my role, I regularly engage with CISOs in all kinds of sectors, representatives at industry bodies, and experts at analyst houses. This gives me an invaluable macroview not only of how the last 12 months have affected organizations and what CISOs are thinking about, but also how the upcoming year is shaping up.
Using this information, last year I wrote a blog summing up the nine top of mind issues I believed will most impact CISOs as we headed into 2022. Many of them still ring true now and will continue to do so, but some new concerns have risen up the agenda. Here are the topics that I think will be top of mind in 2023, and what CISOs can do to prepare.
One aspect that has come to the fore this year is the CISO’s position as ‘guardian of customers’ private data’ in the event of a breach, and their responsibilities over the level of disclosure they later provide. And here, we are not only talking about the legal duty to inform regulators, but the implicit moral duty to inform third parties, customers, etc. From my conversations this year, this whole area is getting CISOs thinking about their own personal liability more.
As a result of this, next year we could see CISOs tightening up the disclosure decision making process, focusing on quicker and greater clarity on breach impact, and even looking to include personal liability cover in cyber insurance contracts. CISOs will also likely be pushing more tabletop exercises with the executive leadership team to ask and answer questions around what is showed, to whom, and by whom.
Cyber insurance has become a newsworthy topic over the last 24 months, mainly due to the hardening of the market, as insurance products have become less profitable for underwriters and insurers’ costs have risen. But the topic will continue to be in focus as we move into 2023, with insurers demanding greater attribution – aka the science of identifying the perpetrator of a cybercrime by comparing the evidence gathered from an attack with evidence gathered from earlier attacks that have been attributed to known perpetrators to find similarities.
The need for greater attribution stems from the news that some insurers are announcing that they are not covering nation state attacks, including major marketplace for insurance and reinsurance, Lloyd’s – a topic I covered with colleague and co-author Martin Lee, in this blog earlier in the year.
Greater preparation and crystal-clear clarity of the extent to which attribution has taken place when negotiating contracts will be an essential element for CISOs going forward. For more practical advice on this topic, I also wrote a blog on some of the challenges and opportunities within the cyber liability insurance market back in June which you can read here.
Being a CISO has never been more complex. With more sophisticated attacks, scarcity of resources, the challenges of communicating effectively with the board, and more demanding regulatory drivers like the recently approved NIS2 in the EU, which includes a requirement to flag incidents that cause a significant financial implication or operational disruption to the service or to others within 24 hours.
With so much to consider, it is vital that CISOs have a clear understanding of the core elements of what they protect. Questions like ‘where is the data?’, ‘who is accessing it?’, ‘what applications is the organization using?’, ‘where and what is in the cloud?’ will continue to be asked, with an overarching need to make management of the security function more flexible and simpler for the user. This visibility will also inevitably help ease quicker decision making and less of an operational overhead when it comes to regulatory compliance, so the benefits of asking these questions are clear.
According to Forrester, the term Zero Trust was born in 2009. Since then, it has been used liberally by different cybersecurity vendors – with various degrees of accuracy. Zero Trust implementations, while being the most secure approach a firm can take, are long journeys that take multiple years for major enterprises to carry out, so it is vital that they start as they mean to go on. But it is clear from the interactions we have had that many CISOs still don’t know where to start, as we touched on in point #3.
However, that can be easier said than done in many cases, as the principles within Zero trust fundamentally turn traditional security methods on their head, from protecting from the outside in (guarding your company’s parameter from external threats) to protecting from in the inside out (guarding individual assets from all threats, both internal and external). This is particularly challenging for large enterprises with a multitude of different silos, stakeholders and business divisions to consider.
The key to success on a zero-trust journey is to set up the right governance mode with the relevant stakeholders and communicate all changes. It is also worth taking the opportunity to update their solutions via a tech refresh which has a multitude of benefits, as explained in our most recent Security Outcomes Study (volume 2).
For more on where to start check out our eBook which explores the five phases to achieving zero trust, and if you have already embarked on the journey, read our recently published Guide to Zero Trust Maturity to help you find quick wins along the way.
As with last year, ransomware continues to be the main tactical issue and concern facing CISOs. More specifically, the uncertainty around when and how an attack could be launched against the organization is a constant threat.
Increased regulation on the payment of ransomware and declaring payments is predicted, on top of the Cyber Incident Reporting for Critical Infrastructure Act of 2022 (CIRCIA), the Ransom Disclosure Act, but that doesn’t help alleviate ransomware worries, especially as this will again put the CISO in the firing line.
CISOs will continue to keep a focus on the core basics to prevent or limit the impact of an attack, and again have a closer look at how any ransomware payment may or may not be paid and who will authorize payment. For more on how executives can prepare for ransomware attacks, read this blog from Cisco Talos.
Traditionally CISOs have talked about the importance of improving security awareness which has resulted in the growth of those test phishing emails we all know and love so much. Joking aside, there is increased discussion now about the limited impact of this approach, including this in depth study from the computer science department of ETH Zurich.
The study, which was the largest both in terms of scale and length at time of publishing, revealed that ‘embedded training during simulated phishing exercises, as commonly deployed in the industry today, does not make employees more resilient to phishing, but instead it can have unexpected side effects that can make employees even more susceptible to phishing’.
For the most effective security awareness, culture is key. This means that everyone should see themselves as part of the security team, like the approach that has been taken when approaching the issue of safety in many high-risk industries. In 2023, CISOs will now be keen to bring about a change to a security culture by making security inclusive, looking to create security champions within the business unit, and finding new methods to communicate the security message.
Last year, we talked about preparing for the ‘great resignation’ and how to prevent staff leaving as WFH became a norm rather than an exception. In the past year, the conversations I have had have altered to focus on how to ensure recruitment and retention of key staff within the business by ensuring they work in an environment that supports their role.
Overly restrictive security practices, burdensome security with too many friction points, and limitations around what resources and tools can be used may deter the best talent from joining – or indeed staying – with an organization. And CISOs don’t need that extra worry of being the reason behind that kind of ‘brain drain’. So, security will need to focus on supporting the introduction of flexibility and the ease of user experience, such as passwordless or risk-based authentication.
Just when we thought it was safe to go back into the organization with MFA protecting us, along came methods of attack that rely on push-based authentication vulnerabilities including:
There has been a lot written about this kind of technique and how it works (including guidance from Duo) due to some recent high-profile cases. So, in the forthcoming year CISOs will look to update their solutions and introduce new ways to authenticate, along with increased communications to users on the topic.
This issue was highlighted again this year driven by regulations in different sectors such as the UK Telecoms (Security) Act which went live in the UK in November 2022 and the new EU regulation on digital operational resilience for financial services firms (DORA), which the European Parliament voted to adopt, also in November 2022. Both prompt greater focus on compliance, more reporting and understanding the dependency and interaction organizations have with the supply chain and other third parties.
CISOs will focus on obtaining reassurance from third parties as to their posture and will receive a lot of requests from others about where their organization stands, so it is crucial more robust insight into third parties is gained, documented, and communicated.
When writing this blog, and comparing it to last year’s, the 2023 top nine topics fit into three categories. Some themes make a reappearance, seem to repeat themselves such as the need to improve security’s interaction with users and the need to keep up to date with digital change. Others appear as almost incremental changes to current capabilities such as an adjusted approach to MFA to cope with push fatigue. But, perhaps one of the most striking differences to previous years is the new focus on the role of the CISO in the firing line and the personal impact that may have. We will of course continue to monitor all changes over the year and lend our viewpoint to give guidance. We wish you a secure and prosperous new year!
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
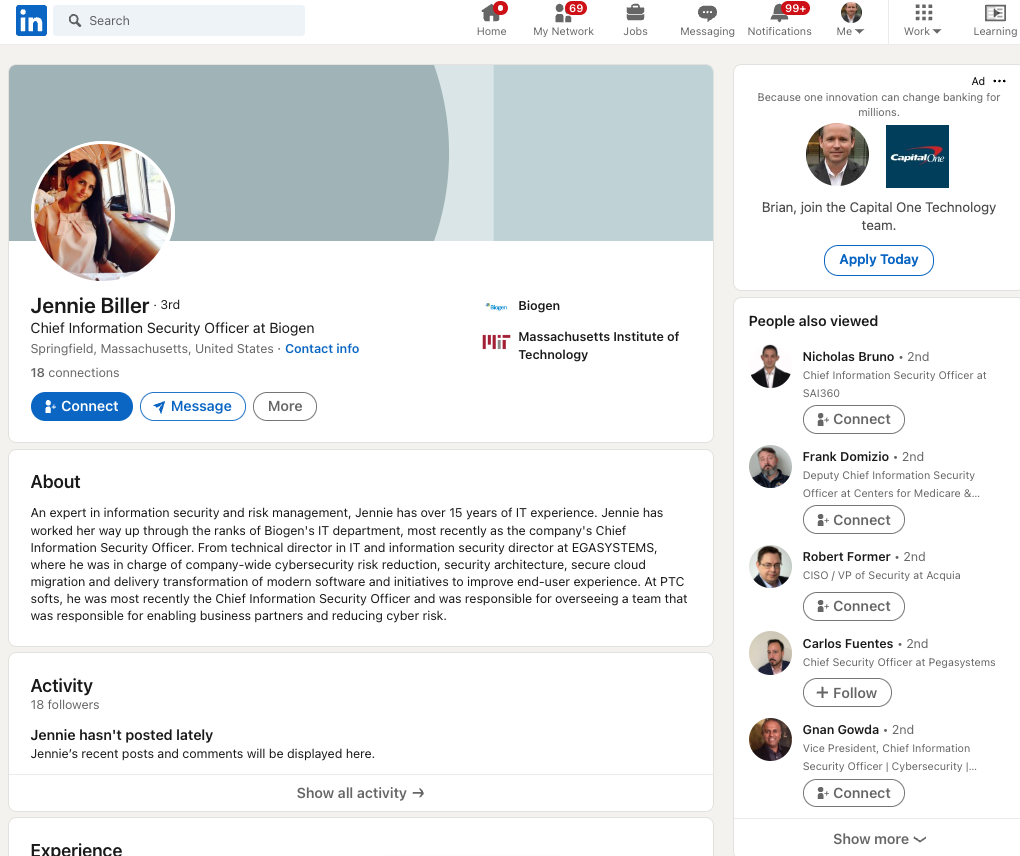
Someone has recently created a large number of fake LinkedIn profiles for Chief Information Security Officer (CISO) roles at some of the world’s largest corporations. It’s not clear who’s behind this network of fake CISOs or what their intentions may be. But the fabricated LinkedIn identities are confusing search engine results for CISO roles at major companies, and they are being indexed as gospel by various downstream data-scraping sources.
If one searches LinkedIn for the CISO of the energy giant Chevron, one might find the profile for a Victor Sites, who says he’s from Westerville, Ohio and is a graduate of Texas A&M University.
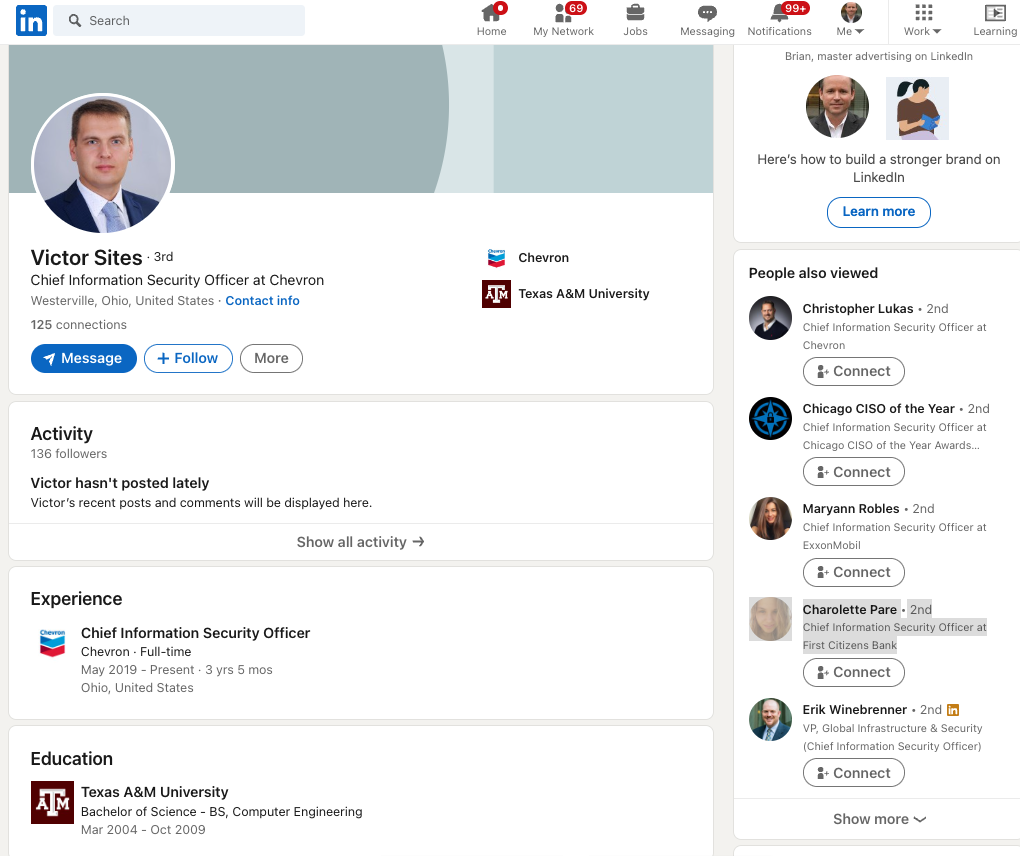
The LinkedIn profile for Victor Sites, who is most certainly NOT the CISO of Chevron.
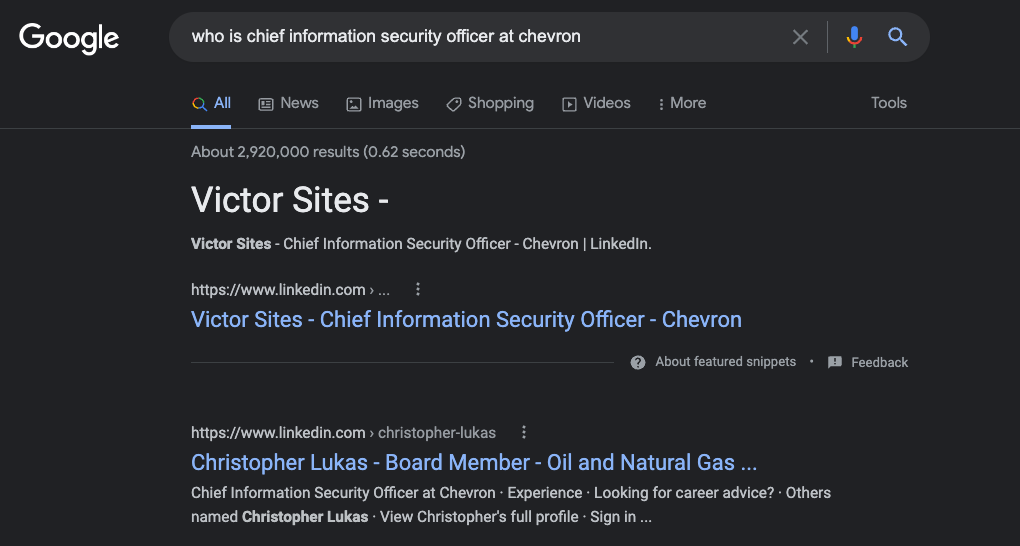
Of course, Sites is not the real CISO of Chevron. That role is currently occupied by Christopher Lukas of Danville, Calif. If you were confused at this point, you might ask Google who it thinks is the current Chief Information Security Officer of Chevron. When KrebsOnSecurity did that earlier this morning, the fake CISO profile was the very first search result returned (followed by the LinkedIn profile for the real Chevron CISO).
Helpfully, LinkedIn seems to be able to detect something in common about all these fake CISO profiles, because it suggested I view a number of them in the “People Also Viewed” column seen in the image above. There are two fake CISO profiles suggested there, including one for a Maryann Robles, who claims to be the CISO of another energy giant — ExxonMobil.
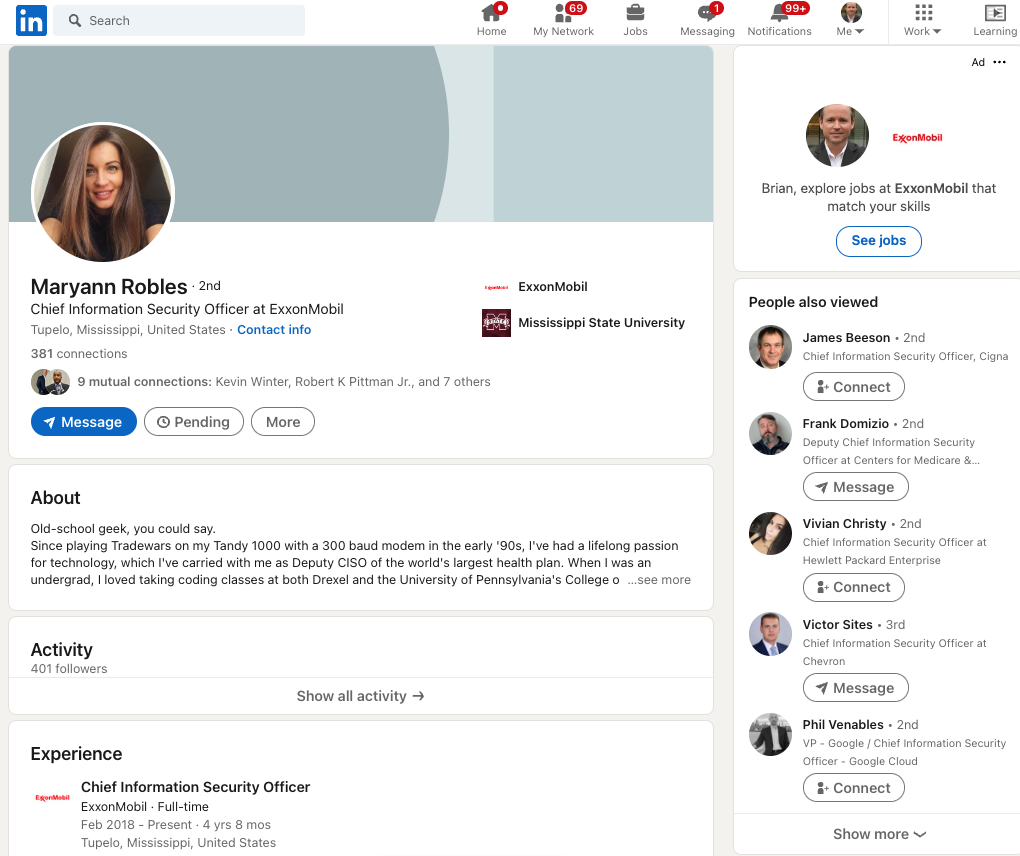
Maryann’s profile says she’s from Tupelo, Miss., and includes this detail about how she became a self-described “old-school geek.”
“Since playing Tradewars on my Tandy 1000 with a 300 baud modem in the early ’90s, I’ve had a lifelong passion for technology, which I’ve carried with me as Deputy CISO of the world’s largest health plan,” her profile reads.
However, this description appears to have been lifted from the profile for the real CISO at the Centers for Medicare & Medicaid Services in Baltimore, Md.
Interestingly, Maryann’s LinkedIn profile was accepted as truth by Cybercrime Magazine’s CISO 500 listing, which claims to maintain a list of the current CISOs at America’s largest companies:
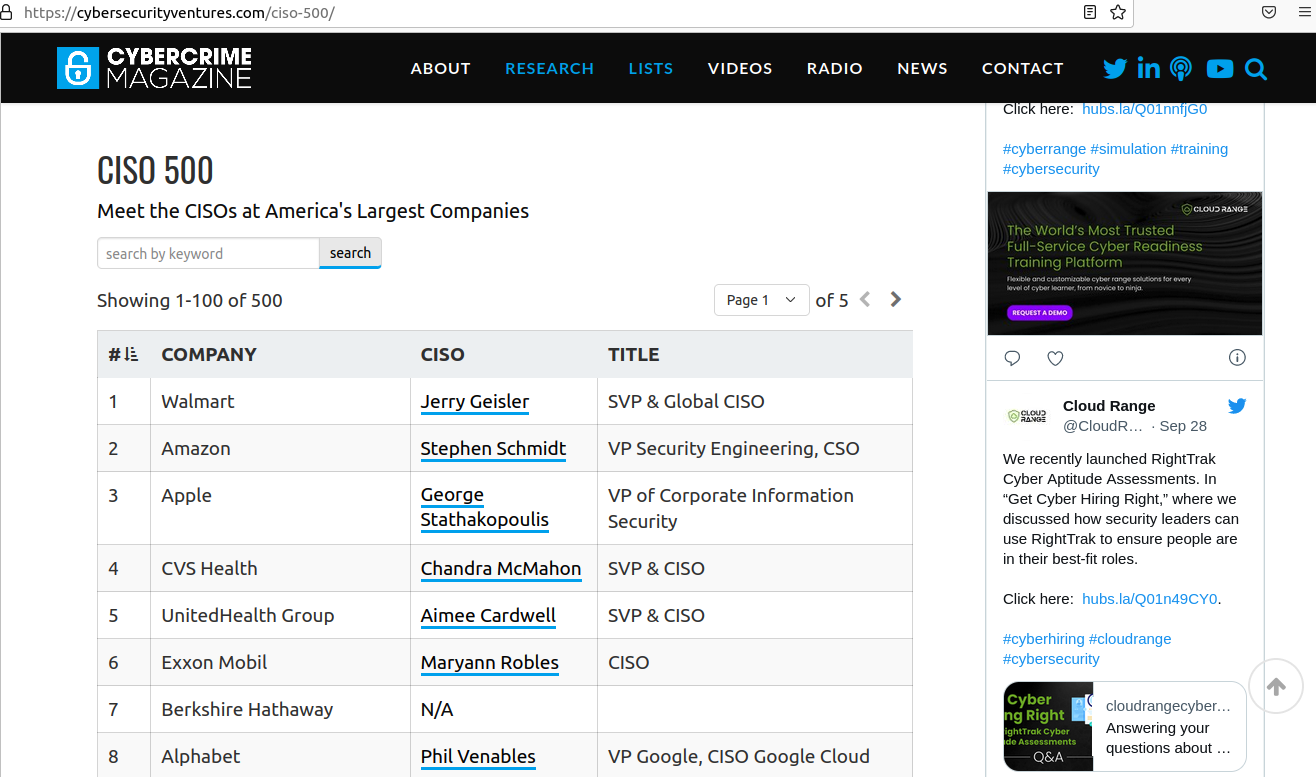
The fake CISO for ExxOnMobil was indexed in Cybercrime Magazine’s CISO 500.
Rich Mason, the former CISO at Fortune 500 firm Honeywell, began warning his colleagues on LinkedIn about the phony profiles earlier this week.
“It’s interesting the downstream sources that repeat LinkedIn bogus content as truth,” Mason said. “This is dangerous, Apollo.io, Signalhire, and Cybersecurity Ventures.”
Google wasn’t fooled by the phony LinkedIn profile for Jennie Biller, who claims to be CISO at biotechnology giant Biogen (the real Biogen CISO is Russell Koste). But Biller’s profile is worth mentioning because it shows how some of these phony profiles appear to be quite hastily assembled. Case in point: Biller’s name and profile photo suggest she is female, however the “About” description of her accomplishments uses male pronouns. Also, it might help that Jennie only has 18 connections on LinkedIn.
Again, we don’t know much about who or what is behind these profiles, but in August the security firm Mandiant (recently acquired by Google) told Bloomberg that hackers working for the North Korean government have been copying resumes and profiles from leading job listing platforms LinkedIn and Indeed, as part of an elaborate scheme to land jobs at cryptocurrency firms.
None of the profiles listed here responded to requests for comment (or to become a connection).
In a statement provided to KrebsOnSecurity, LinkedIn said its teams were actively working to take these fake accounts down.
“We do have strong human and automated systems in place, and we’re continually improving, as fake account activity becomes more sophisticated,” the statement reads. “In our transparency report we share how our teams plus automated systems are stopping the vast majority of fraudulent activity we detect in our community – around 96% of fake accounts and around 99.1% of spam and scam.”
LinkedIn could take one simple step that would make it far easier for people to make informed decisions about whether to trust a given profile: Add a “created on” date for every profile. Twitter does this, and it’s enormously helpful for filtering out a great deal of noise and unwanted communications.
The former CISO Mason said LinkedIn also could experiment with offering something akin to Twitter’s verified mark to users who chose to validate that they can respond to email at the domain associated with their stated current employer.
“If I saw that a LinkedIn profile had been domain-validated, then my confidence in that profile would go way up,” Mason said, noting that many of the fake profiles had hundreds of followers, including dozens of real CISOs. Maryann’s profile grew by a hundred connections in just the past few days, he said.
“If we have CISOs that are falling for this, what hopes do the masses have?” Mason said.
Mason said LinkedIn also needs a more streamlined process for allowing employers to remove phony employee accounts. He recently tried to get a phony profile removed from LinkedIn for someone who falsely claimed to have worked for his company.
“I shot a note to LinkedIn and said please remove this, and they said, well, we have to contact that person and arbitrate this,” he said. “They gave the guy two weeks and he didn’t respond, so they took it down. But that doesn’t scale, and there needs to be a mechanism where an employer can contact LinkedIn and have these fake profiles taken down in less than two weeks.”

Over the past three decades, we’ve had time at Trend Micro to observe the industry trends that have the biggest impact on our customers. And one of the big things we’ve seen is that threats move largely in tandem with changes to IT infrastructure. This matters today because most organizations are transforming the way they run and manage their infrastructure—a daunting task on its own.
But with digital transformation also comes an expanded corporate attack surface, driving security leaders to demand enhanced visibility, detection & response across the entire enterprise — this is not just about the endpoint.
Transforming business
Over the past five years, there has been a major shift in the way IT infrastructure is delivered, and with that shift, increasing complexity. A big part of this change has been the use of the cloud, reflected in Gartner’s prediction that the market will grow to over $266 billion in 2020. Organizations everywhere are leveraging the cloud and DevOps to rapidly deliver new and differentiated applications and services for their customers, partners and employees. And the use of containers and microservices across a multi-cloud and hybrid environment is increasingly common.
In addition to leveraging public cloud services like IaaS, organizations are also rapidly adopting SaaS applications like Office 365, and expanding their use of mobile and collaborative applications to support remote working. Some are even arguing that working patterns may never be the same again, following the changes forced on many employers by the Covid-19 pandemic.
Combine these changes with networks that continue to extend to include branch offices and add new areas to protect like operational technology including industrial systems, and we can certainly see that the challenges facing the modern enterprise look nothing like they did a few years ago.
Under fire, under pressure
All of these infrastructure changes make for a broader attack surface that the bad guys can take advantage of, and they’re doing so with an increasingly wide range of tools and techniques. In the cloud there is a new class of vulnerabilities introduced through a greater use of open source, containers, orchestration platforms, supply chain applications and more. For all organizations, the majority of threats still prey upon the user, arriving via email (over 90% of the 52.3 billion we blocked in 2019), and they’re no longer just basic phishing attempts. There’s been an uptick in fileless events designed to bypass traditional security filters (we blocked 1.4 million last year). And Business Email Compromise (BEC) and ransomware continue to evolve, the latter causing major outages across local government, healthcare and other vulnerable sectors.
Organizations are often left flat-footed because they don’t have the in-house skills to secure a rapidly evolving IT environment. Mistakes get made, and configuration errors can allow the hackers to sneak in.
Against this backdrop, CISOs need visibility, detection and response capabilities across the extended enterprise. But in too many cases, teams are struggling because they have:
|
|
Beyond the endpoint
While endpoint detection and response (EDR) has become a popular response to some of these problems over recent years, the reality is that cyber-attacks are rarely straightforward and limited to the endpoint (as noted in the email statistic above). Security teams actually need visibility, detection, and response across the entire IT environment, so they can better contextualize and deal with threats.
This is what Trend Micro XDR offers. It provides visibility across not just endpoints but also email, servers, cloud workloads and networks, applying AI and expert security analytics to correlate and identify potential threats. The result is fewer, higher fidelity alerts for stretched IT security teams to deal with. Recognizing the skills shortage reality, we also offer a managed XDR service that augments in-house SOC activities with the power of Trend Micro security experts.
Detection and response is too important to be limited to the endpoint. Today’s CISOs need visibility, detection, and response everywhere.
The post Why CISOs Are Demanding Detection and Response Everywhere appeared first on .

Variety is welcome in most walks of life, but not when it comes to the threat landscape. Yet that is unfortunately the reality facing modern cybersecurity professionals. As Trend Micro’s 2019 roundup report reveals, hackers have an unprecedented array of tools, techniques and procedures at their disposal today. With 52 billion unique threats detected by our filters alone, this is in danger of becoming an overwhelming challenge for many IT security departments.
In response, many CISOs are rightly re-examining how they approach threat defense. Rather than create potential security gaps and risk budget shortfalls through best-of-breed investments, they’re understanding that it may be better to consolidate on one provider that can do it all.
The state of play
Our report provides an alarming snapshot into a threat landscape characterized by volatility and chaos. Financially motivated cybercriminals collaborate and compete with each other on a daily basis to elicit profits from their victims. And there are plenty of those, thanks to increased investments in cloud and digital platforms that have broadened the corporate attack surface.
Three trends in the report stand out:
Ransomware is on the rise: Although the number of new families fell, the number of detected ransomware components jumped by 10% to top 61 million during the year. Attacks have been causing chaos across the US, particularly among under-funded public sector authorities and schools. The recent outage at Redcar council could be ominous for UK local authorities. As if service downtime wasn’t enough, several groups have also begun stealing sensitive data before they encrypt, and releasing it if victims don’t pay up — which will require organisations to evolve their threat defense strategies.
Phishing is evolving: As always, email-borne attacks accounted for the vast majority (91%) of threats we blocked last year, and increased 15% in volume from 2018. What does this mean? That phishing remains the number one vector for attacks on organisations. Although we noted an overall decline in total attempts to visit phishing sites, there were some spikes. Fraudsters appear to be targeting Office 365 in an attempt to bypass security filters: the number of unique phishing URLs that spoofed the Microsoft cloud platform soared by 100% from the previous year. BEC attacks, which the FBI has claimed cost more than any other cybercrime type last year, grew 5%.
The supply chain is exposed: At the same time, the digital supply chain has rapidly expanded in recent years, exposing more organisations to risk. This was particularly notable in the e-commerce space last year, as Magecart gangs managed to compromise an estimated two million sites. Many of these attacks focused on attacking supply chain partners, which provide JavaScript libraries to the victim sites. We also observed an increase in attacks focused on compromising DevOps tools and deployments, such as misconfigured versions of Docker Engine – Community and unsecured Docker hosts.
What happens now?
This is just the tip of the iceberg. We also detected a 189% brute force IoT logins, an increase in mobile malware, and much more. To regain the initiative in the face of such a wide-ranging set of threats, CISOs may find more value in taking a connected threat defence approach. This would consolidate protection onto a single provider across gateways, networks, servers and endpoints, with underlying threat intelligence optimizing defense at each layer.
Here’s a quick checklist of elements to consider:
|
|
To find out more, read Trend Micro’s 2019 roundup report here: https://www.trendmicro.com/vinfo/us/security/research-and-analysis/threat-reports/roundup/the-sprawling-reach-of-complex-threats.
The post Hackers Expand Their Repertoire as Trend Micro Blocks 52 Billion Threats in 2019 appeared first on .

We recently held a valuable conversation (and a great dinner) with about a dozen senior IT security leaders in Atlanta, Georgia. I was fortunate to attend and discuss what plagues them most.
Here are some of their concerns.
Many face considerable change in their business environments – one third of the companies called out the high pace of acquisitions as a source of risk.
Acquisitions draw down information security resources disproportionately. First, IT security must participate in the due diligence phase, prior to the actual acquisition. Under significant time pressure, and strictly bound by the terms of the governing NDA, the InfoSec team must verify the integrity of the target environment’s IT infrastructure. It must render a judgment on the trustworthiness of the underlying procedures, the competence of the support team, the appropriateness of funding and staffing, the effectiveness of policy and awareness training, the fitness of the security technology judged against the changing mission of the target firm, and the accessibility of crucial information. In regulated industries, the acquirer has to review past certifications, audit findings and recommendations, and earlier security events, including how they were handled, and how the organization effectively integrated lessons learned into its updated way of doing business. Some of the attendees reported an acquisition every six weeks over the past two years or more. This pace requires efficient process maturity and open communication among the team members, and ample trust.
Some CIOs reported the challenge of balancing the executive team’s need to know with the managerial desire to optimize team focus on critical initiatives. In the Boardroom and among the C-suite, IT remains a hot topic and IT security is a known vulnerability. This leads some organizations toward micromanaging the IT security team. As we all know, this inappropriate focus has two costs: first, it distracts the Board and the C-suite from their primary missions. Second, it distracts the people doing the job from their task. One effective tactic some adopted is the weekly – or even daily – newsletter. This document provides the status for ongoing projects, notes about top performers, assessment of newly discovered vulnerabilities, and pointers towards effective risk mitigation the leadership team can bring to their respective operational areas. When a Board member has a question for the team, the CISO can intercept it and post a response through the newsletter.
Many CISOs discussed their challenges with BYOD policies. Some mentioned concerns with GDPR impeding their ability to wipe corporate applications and information from employee-owned devices. It’s unclear how to balance that business requirement with privacy concerns for smart phones. With laptops, one approach is to limit corporate access through a locked-down virtual desktop image accessed through a secure VPN. An evil-minded employee could take a picture of the screen, but that attack works on a corporate laptop just as well.
BEC remains a concern, along with phishing attacks leading to possible ransomware infections. One approach is to ignore emails from new domains – those that are less than two months old. This would exclude email from nearly all attackers; anyone legitimately trying to reach an employee will try again in time.
The meeting was quite open and convivial. It was an honor to participate in the discussion, and I look forward to similar meetings in the future. My thanks to the participants!
What do you think? Let me know in the comments below, or message me @WilliamMalikTM!
The post What Worries CISOs Most In 2019 appeared first on .