The average time taken by global organizations to detect cyberattacks has dropped to its lowest-ever level of ten days, Mandiant revealed today.…
UnitedHealth Group, the parent of ransomware-struck Change Healthcare, delivered some very unwelcome news for customers today as it continues to recover from the massively expensive side and disruptive digital break-in.…
It's become somewhat cliché in cybersecurity reporting to speculate whether an organization will have the resources to "keep the lights on" after an attack. But the opposite turns out to be true with Leicester City Council following its March ransomware incident.…
Neighbourhood Watch (NW) groups across the UK can now rest easy knowing the developers behind a communications platform fixed a web app bug that leaked their data en masse.…
A misconfigured cloud server that used a North Korean IP address has led to the discovery that film production studios including the BBC, Amazon, and HBO Max could be inadvertently using workers from the hermit kingdom for animation projects.…

"More Data Breaches Than You Can Shake a Stick At". That seems like a reasonable summary and I suggest there are two main reasons for this observation. Firstly, there are simply loads of breaches happening and you know this already because, well, you read my stuff! Secondly, There are a couple of Twitter accounts in particular that are taking incidents that appear across a combination of a popular clear web hacking forum and various dark web ransomware websites and "raising them to the surface", so to speak. That is incidents that may have previously remained on the fringe are being regularly positioned in the spotlight where they have much greater visibility. The end result is greater awareness and a longer backlog of breaches to process than I've ever had before!

Russian spies are exploiting a years-old Windows print spooler vulnerability and using a custom tool called GooseEgg to elevate privileges and steal credentials across compromised networks, according to Microsoft Threat Intelligence.…
US lawmakers on Saturday reauthorized a contentious warrantless surveillance tool for another two years — and added a whole bunch of people and organizations to the list of those who can be compelled to spy for Uncle Sam.…
The head of counterintelligence for a division of the Russian Federal Security Service (FSB) was sentenced last week to nine years in a penal colony for accepting a USD $1.7 million bribe to ignore the activities of a prolific Russian cybercrime group that hacked thousands of e-commerce websites. The protection scheme was exposed in 2022 when Russian authorities arrested six members of the group, which sold millions of stolen payment cards at flashy online shops like Trump’s Dumps.

A now-defunct carding shop that sold stolen credit cards and invoked 45’s likeness and name.
As reported by The Record, a Russian court last week sentenced former FSB officer Grigory Tsaregorodtsev for taking a $1.7 million bribe from a cybercriminal group that was seeking a “roof,” a well-placed, corrupt law enforcement official who could be counted on to both disregard their illegal hacking activities and run interference with authorities in the event of their arrest.
Tsaregorodtsev was head of the counterintelligence department for a division of the FSB based in Perm, Russia. In February 2022, Russian authorities arrested six men in the Perm region accused of selling stolen payment card data. They also seized multiple carding shops run by the gang, including Ferum Shop, Sky-Fraud, and Trump’s Dumps, a popular fraud store that invoked the 45th president’s likeness and promised to “make credit card fraud great again.”
All of the domains seized in that raid were registered by an IT consulting company in Perm called Get-net LLC, which was owned in part by Artem Zaitsev — one of the six men arrested. Zaitsev reportedly was a well-known programmer whose company supplied services and leasing to the local FSB field office.
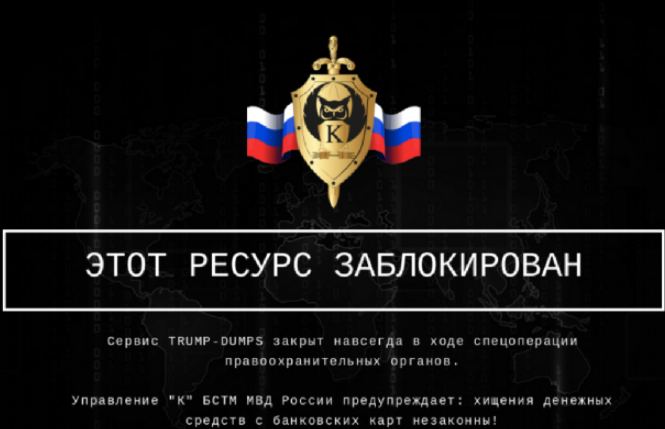
The message for Trump’s Dumps users left behind by Russian authorities that seized the domain in 2022.
Russian news sites report that Internal Affairs officials with the FSB grew suspicious when Tsaregorodtsev became a little too interested in the case following the hacking group’s arrests. The former FSB agent had reportedly assured the hackers he could have their case transferred and that they would soon be free.
But when that promised freedom didn’t materialize, four the of the defendants pulled the walls down on the scheme and brought down their own roof. The FSB arrested Tsaregorodtsev, and seized $154,000 in cash, 100 gold bars, real estate and expensive cars.
At Tsaregorodtsev’s trial, his lawyers argued that their client wasn’t guilty of bribery per se, but that he did admit to fraud because he was ultimately unable to fully perform the services for which he’d been hired.
The Russian news outlet Kommersant reports that all four of those who cooperated were released with probation or correctional labor. Zaitsev received a sentence of 3.5 years in prison, and defendant Alexander Kovalev got four years.
In 2017, KrebsOnSecurity profiled Trump’s Dumps, and found the contact address listed on the site was tied to an email address used to register more than a dozen domains that were made to look like legitimate Javascript calls many e-commerce sites routinely make to process transactions — such as “js-link[dot]su,” “js-stat[dot]su,” and “js-mod[dot]su.”
Searching on those malicious domains revealed a 2016 report from RiskIQ, which shows the domains featured prominently in a series of hacking campaigns against e-commerce websites. According to RiskIQ, the attacks targeted online stores running outdated and unpatched versions of shopping cart software from Magento, Powerfront and OpenCart.
Those shopping cart flaws allowed the crooks to install “web skimmers,” malicious Javascript used to steal credit card details and other information from payment forms on the checkout pages of vulnerable e-commerce sites. The stolen customer payment card details were then sold on sites like Trump’s Dumps and Sky-Fraud.
Yet another international cop shop has come out swinging against end-to-end encryption - this time it's Europol which is urging an end to implementation of the tech for fear police investigations will be hampered by protected DMs.…
Germany has arrested three citizens who allegedly tried to transfer military technology to China, a violation of the country's export rules.…
The Dutch Data Protection Authority (AP) has warned that government organizations should not use Facebook to communicate with the country's citizens unless they can guarantee the privacy of data.…
Fresh US legislation to force the sale of TikTok locally was passed in Washington over the weekend after an earlier version stalled in the Senate.…
Google's Privacy Sandbox, which aspires to provide privacy-preserving ad targeting and analytics, still isn't sufficiently private.…
Webinar On the face of it, there really isn't much of an upside for the current UK government after MPs described its response to attacks by cyber-espionage group APT31 as 'feeble, derisory and sadly insufficient.'…
Opinion It was a bold claim by the richest and most famous tech founder: bold, precise and wrong. Laughably so. Twenty years ago, Bill Gates promised to rid the world of spam by 2006. How's that worked out for you?…
Who, Me? It's Monday once again, dear reader, and you know what that means: another dive into the Who, Me? confessional, to share stories of IT gone wrong that Reg readers managed to pretend had gone right.…
BLACK HAT ASIA Researchers at US/Israeli infosec outfit SafeBreach last Friday discussed flaws in Microsoft and Kaspersky security products that can potentially allow the remote deletion of files. And, they asserted, the hole could remain exploitable – even after both vendors claim to have patched the problem.…
China last week reorganized its military to create an Information Support Force aimed at ensuring it can fight and win networked wars.…
Infosec In Brief In a cautionary tale that no one is immune from attack, the security org MITRE has admitted that it got pwned.…