A Canadian man who says he’s been falsely charged with orchestrating a complex e-commerce scam is seeking to clear his name. His case appears to involve “triangulation fraud,” which occurs when a consumer purchases something online — from a seller on Amazon or eBay, for example — but the seller doesn’t actually own the item for sale. Instead, the seller purchases the item from an online retailer using stolen payment card data. In this scam, the unwitting buyer pays the scammer and receives what they ordered, and very often the only party left to dispute the transaction is the owner of the stolen payment card.
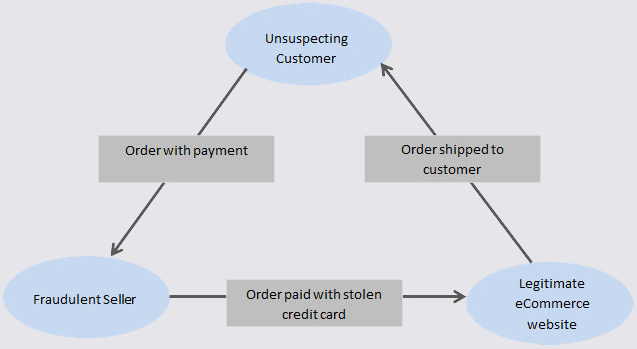
Triangulation fraud. Image: eBay Enterprise.
Timothy Barker, 56, was until recently a Band Manager at Duncan’s First Nation, a First Nation in northwestern Alberta, Canada. A Band Manager is responsible for overseeing the delivery of all Band programs, including community health services, education, housing, social assistance, and administration.
Barker told KrebsOnSecurity that during the week of March 31, 2023 he and the director of the Band’s daycare program discussed the need to purchase items for the community before the program’s budget expired for the year.
“There was a rush to purchase items on the Fiscal Year 2023 timeline as the year ended on March 31,” Barker recalled.
Barker said he bought seven “Step2 All Around Playtime Patio with Canopy” sets from a seller on Amazon.ca, using his payment card on file to pay nearly $2,000 for the items.
On the morning of April 7, Barker’s Facebook account received several nasty messages from an Ontario woman he’d never met. She demanded to know why he’d hacked her Walmart account and used it to buy things that were being shipped to his residence. Barker shared a follow-up message from the woman, who later apologized for losing her temper.
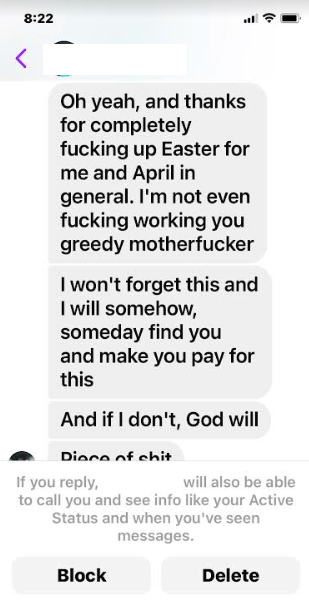
One of several messages from the Ontario woman whose Walmart account was used to purchase the goods that Barker ordered from Amazon.
“If this is not the person who did this to me, I’m sorry, I’m pissed,” the lady from Ontario said. “This order is being delivered April 14th to the address above. If not you, then someone who has the same name. Now I feel foolish.”
On April 12, 2023, before the Amazon purchases had even arrived at his home, Barker received a call from an investigator with the Royal Canadian Mounted Police (RCMP), who said Barker urgently needed to come down to the local RCMP office for an interview related to “an investigation.” Barker said the officer wouldn’t elaborate at the time on the nature of the investigation, and that he told the officer he was in Halifax for several days but could meet after his return home.
According to Barker, the investigator visited his home anyway the following day and began questioning his wife, asking about his whereabouts, his work, and when he might return home.
On April 14, six boxes arrived to partially fulfill his Amazon order; another box was delayed, and the Amazon.ca seller he’d purchased from said the remaining box was expected to ship the following week. Barker said he was confused because all six boxes came from Walmart instead of Amazon, and the shipping labels had his name and address on them but carried a contact phone number in Mexico.
Three days later, the investigator called again, demanding he submit to an interview.
“He then asked where my wife was and what her name is,” Barker said. “He wanted to know her itinerary for the day. I am now alarmed and frightened — this doesn’t feel right.”
Barker said he inquired with a local attorney about a consultation, but that the RCMP investigator showed up at his house before he could speak to the lawyer. The investigator began taking pictures of the boxes from his Amazon order.
“The [investigator] derisively asked why would anyone order so many play sets?” Barker said. “I started to give the very logical answer that we are helping families improve their children’s home life and learning for toddlers when he cut me off and gave the little speech about giving a statement after my arrest. He finally told me that he believes that I used someone’s credit card in Ontario to purchase the Walmart products.”
Eager to clear his name, Barker said he shared with the police copies of his credit card bills and purchase history at Amazon. But on April 21, the investigator called again to say he was coming to arrest Barker for theft.
“He said that if I was home at five o’clock then he would serve the papers at the house and it would go easy and I wouldn’t have to go to the station,” Barker recalled. “If I wasn’t home, then he would send a search team to locate me and drag me to the station. He said he would kick the door down if I didn’t answer my phone. He said he had every right to break our door down.”
Barker said he briefly conferred with an attorney about how to handle the arrest. Later that evening, the RCMP arrived with five squad cars and six officers.
“I asked if handcuffs were necessary – there is no danger of violence,” Barker said. “I was going to cooperate. His response was to turn me around and cuff me. He walked me outside and stood me beside the car for a full 4 or 5 minutes in full view of all the neighbors.”
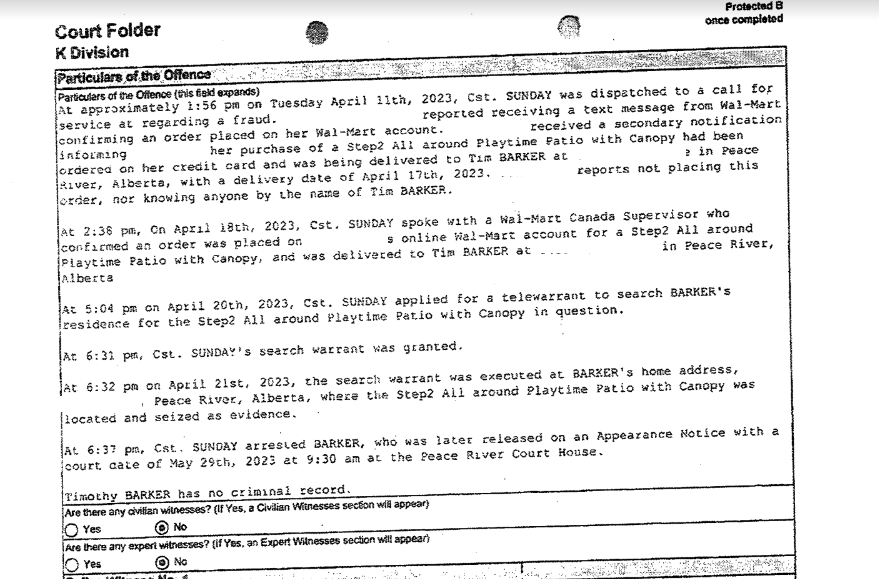
Barker believes he and the Ontario woman are both victims of triangulation fraud, and that someone likely hacked the Ontario woman’s Walmart account and added his name and address as a recipient.
But he says he has since lost his job as a result of the arrest, and now he can’t find new employment because he has a criminal record. Barker’s former employer — Duncan’s First Nation — did not respond to requests for comment.
“In Canada, a criminal record is not a record of conviction, it’s a record of charges and that’s why I can’t work now,” Barker said. “Potential employers never find out what the nature of it is, they just find out that I have a criminal arrest record.”
Barker said that right after his arrest, the RCMP called the Ontario woman and told her they’d solved the crime and arrested the perpetrator.
“They even told her my employer had put me on administrative leave,” he said. “Surely, they’re not allowed to do that.”
Contacted by KrebsOnSecurity, the woman whose Walmart account was used to fraudulently purchase the child play sets said she’s not convinced this was a case of triangulation fraud. She declined to elaborate on why she believed this, other than to say the police told her Barker was a bad guy.
“I don’t think triangulation fraud was used in this case,” she said. “My actual Walmart.ca account was hacked and an order was placed on my account, using my credit card. The only thing Mr. Barker did was to order the item to be delivered to his address in Alberta.”
Barker shared with this author all of the documentation he gave to the RCMP, including screenshots of his Amazon.ca account showing that the items in dispute were sold by a seller named “Adavio,” and that the merchant behind this name was based in Turkey.
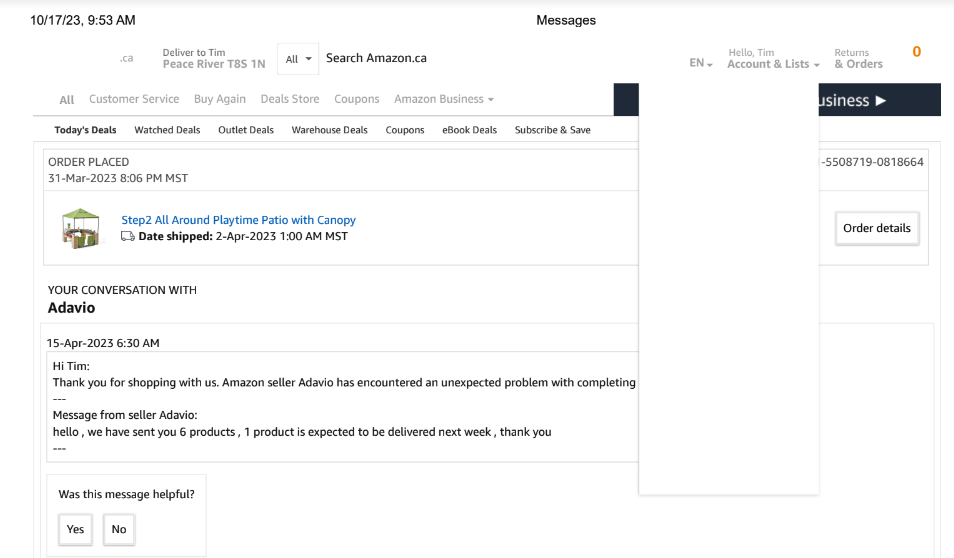
That Adavio account belongs to a young computer engineering student and “SEO expert” based in Adana, Turkey who did not respond to requests for comment.
Amazon.ca said it conducted an investigation and found that Mr. Barker never filed a complaint about the seller or transaction in question. The company noted that Adavio currently has a feedback rating of 4.5 stars out of 5.
“Amazon works hard to provide customers with a great experience and it’s our commitment to go above and beyond to make things right for customers,” Amazon.ca said in a written statement. “If a customer has an issue with an order, they may flag to Amazon through our Customer Service page.”
Barker said when he went to file a complaint with Amazon last year he could no longer find the Adavio account on the website, and that the site didn’t have a category for the type of complaint he wanted to file.
When he first approached KrebsOnSecurity about his plight last summer, Barker said he didn’t want any media attention to derail the chances of having his day in court, and confronting the RCMP investigator with evidence proving that he was being wrongfully prosecuted and maligned.
But a week before his court date arrived at the end of November 2023, prosecutors announced the charges against him would be stayed, meaning they had no immediate plans to prosecute the case further but that the investigation could still be reopened at some point in the future.
The RCMP declined to comment for this story, other than to confirm they had issued a stay of proceedings in the case.
Barker says the stay has left him in legal limbo — denying him the ability to clear his name, while giving the RCMP a free pass for a botched investigation. He says he has considered suing the investigating officer for defamation, but has been told by his attorney that the bar for success in such cases against the government is extremely high.
“I’m a 56-year-old law-abiding citizen, and I haven’t broken any laws,” Barker said, wondering aloud who would be stupid enough to use someone else’s credit card and have the stolen items shipped directly to their home.
“Their putting a stay on the proceedings without giving any evidence or explanation allows them to cover up bad police work,” he said. “It’s all so stupid.”
Triangulation fraud is hardly a new thing. KrebsOnSecurity first wrote about it from an e-commerce vendor’s perspective in 2015, but the scam predates that story by many years and is now a well-understood problem. The Canadian authorities should either let Mr. Barker have his day in court, or drop the charges altogether.
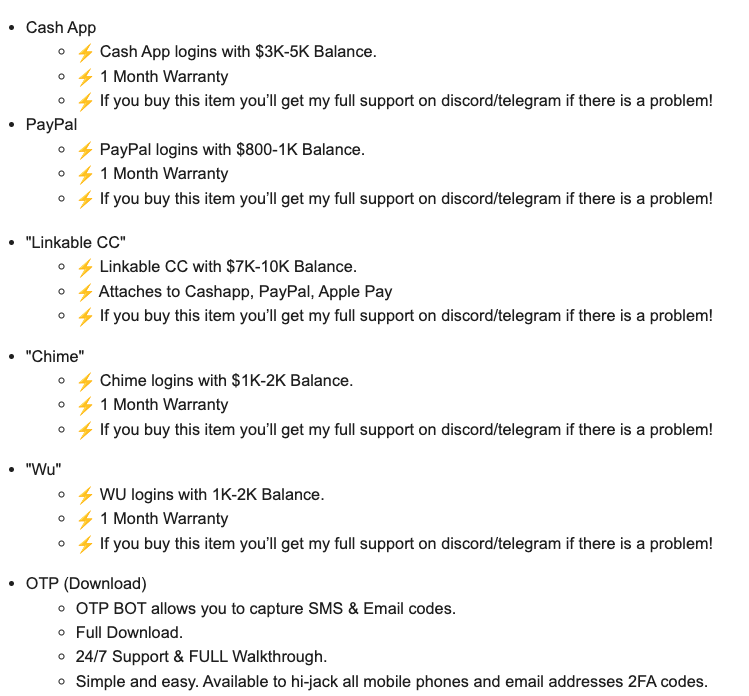
The rapper and social media personality Punchmade Dev is perhaps best known for his flashy videos singing the praises of a cybercrime lifestyle. With memorable hits such as “Internet Swiping” and “Million Dollar Criminal” earning millions of views, Punchmade has leveraged his considerable following to peddle tutorials on how to commit financial crimes online. But until recently, there wasn’t much to support a conclusion that Punchmade was actually doing the cybercrime things he promotes in his songs.

Images from Punchmade Dev’s Twitter/X account show him displaying bags of cash and wearing a functional diamond-crusted payment card skimmer.
Punchmade Dev’s most controversial mix — a rap called “Wire Fraud Tutorial” — was taken down by Youtube last summer for violating the site’s rules. Punchmade shared on social media that the video’s removal was prompted by YouTube receiving a legal process request from law enforcement officials.
The 24-year-old rapper told reporters he wasn’t instructing people how to conduct wire fraud, but instead informing his fans on how to avoid being victims of wire fraud. However, this is difficult to discern from listening to the song, which sounds very much like a step-by-step tutorial on how to commit wire fraud.
“Listen up, I’m finna show y’all how to hit a bank,” Wire Fraud Tutorial begins. “Just pay attention, this is a quick way to jug in any state. First you wanna get a bank log from a trusted site. Do your research because the information must be right.”
And even though we’re talking about an individual who regularly appears in videos wearing a half-million dollars worth of custom jewelry draped around his arm and neck (including the functional diamond-encrusted payment card skimming device pictured above), there’s never been much evidence that Punchmade was actually involved in committing cybercrimes himself. Even his most vocal critics acknowledged that the whole persona could just be savvy marketing.
That changed recently when Punchmade’s various video and social media accounts began promoting a new web shop that is selling stolen payment cards and identity data, as well as hacked financial accounts and software for producing counterfeit checks.
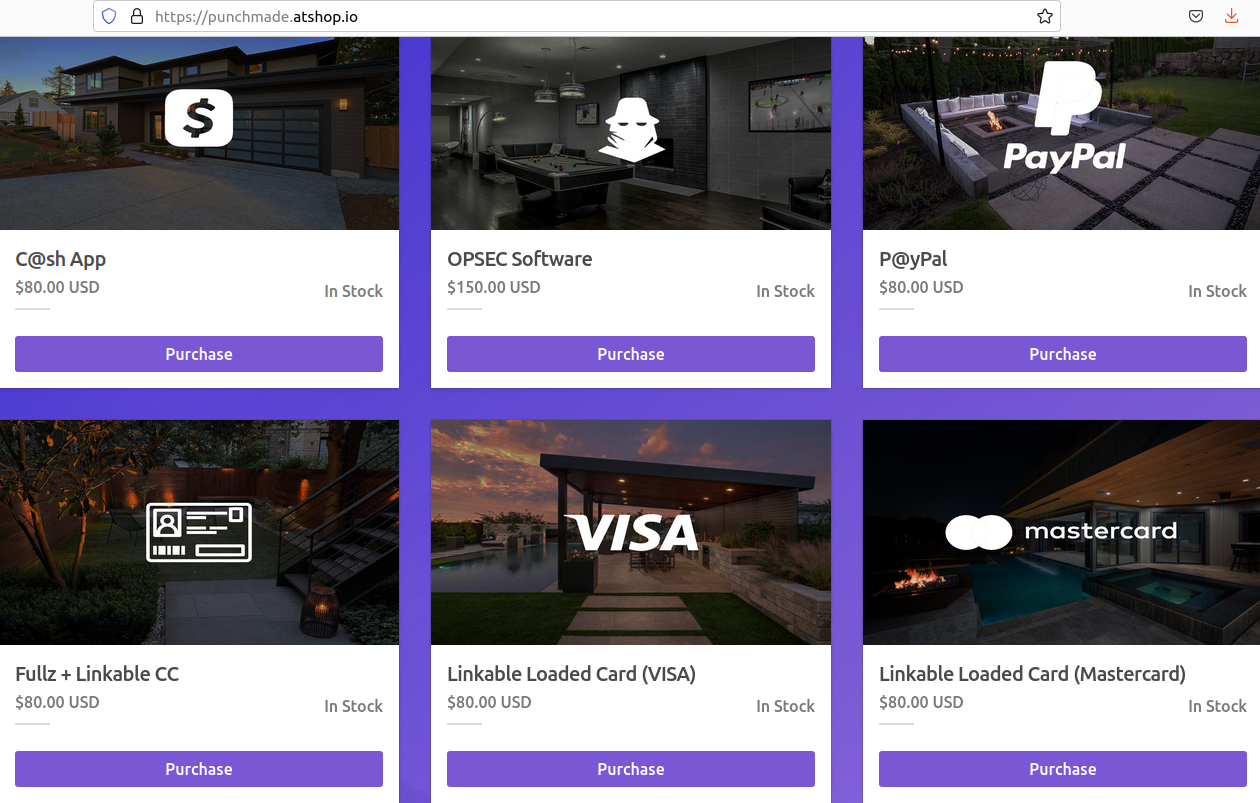
Punchmade Dev’s shop.
The official Punchmadedev account on Instagram links to many of the aforementioned rap videos and tutorials on cybercriming, as well as to Punchmadedev’s other profiles and websites. Among them is mainpage[.]me/punchmade, which includes the following information for “Punchmade Empire ®”
-212,961 subscribers
#1 source on Telegram
Contact: @whopunchmade
24/7 shop: https://punchmade[.]atshop[.]io
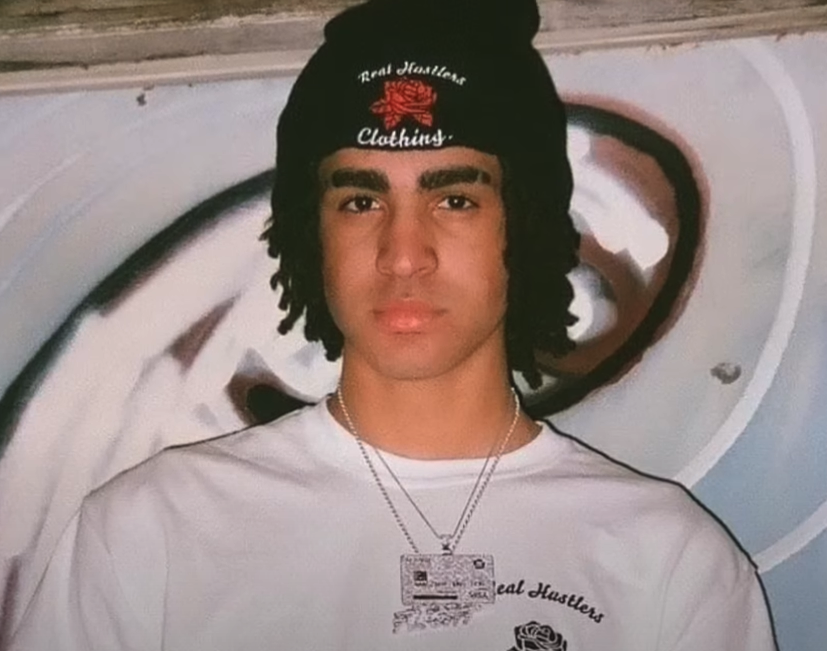
Visiting that @whopunchmade Telegram channel shows this user is promoting punchmade[.]atshop[.]io, which is currently selling hacked bank accounts and payment cards with high balances.
Clicking “purchase” on the C@sh App offering, for example, shows that for $80 the buyer will receive logins to Cash App accounts with balances between $3,000 and $5,000. “If you buy this item you’ll get my full support on discord/telegram if there is a problem!,” the site promises. Purchases can be made in cryptocurrencies, and checking out prompts one to continue payment at Coinbase.com.
Another item for sale, “Fullz + Linkable CC,” promises “ID Front + Back, SSN with 700+ Credit Score, and Linkable CC” or credit card. That also can be had for $80 in crypto.
Punchmade has fashioned his public persona around a collection of custom-made, diamond-covered necklaces that are as outlandish and gaudy as they are revelatory. My favorite shot from one of Punchmade’s videos features at least three of these monstrosities: One appears to be a boring old diamond and gold covered bitcoin, but the other two necklaces tell us something about where Punchmade is from:

Notice the University of Kentucky logo, and the Lexington, Ky skyline.
One of them includes the logo and mascot of the University of Kentucky. The other, an enormous diamond studded skyline, appears to have been designed based on the skyline in Lexington, Ky:

The “About” page on Punchmade Dev’s Spotify profile describes him as “an American artist, rapper, musician, producer, director, entrepreneur, actor and investor.” “Punchmade Dev is best known for his creative ways to use technology, video gaming, and social media to build a fan base,” the profile continues.
The profile explains that he launched his own record label in 2021 called Punchmade Records, where he produces his own instrumentals and edits his own music videos.
A search on companies that include the name “punchmade” at the website of the Kentucky Secretary of State brings up just one record: OBN Group LLC, in Lexington, Ky. This November 2021 record includes a Certificate of Assumed Name, which shows that Punchmade LLC is the assumed name of OBN Group LLC.
The president of OBN Group LLC is listed as Devon Turner. A search on the Secretary of State website for other businesses tied to Devon Turner reveals just one other record: A now-defunct entity called DevTakeFlightBeats Inc.
The breach tracking service Constella Intelligence finds that Devon Turner from Lexington, Ky. used the email address obndevpayments@gmail.com. A lookup on this email at DomainTools.com shows it was used to register the domain foreverpunchmade[.]com, which is registered to a Devon Turner in Lexington, Ky. A copy of this site at archive.org indicates it once sold Punchmade Dev-branded t-shirts and other merchandise.
Mr. Turner did not respond to multiple requests for comment.
Searching online for Devon Turner and “Punchmade” brings up a video from @brainjuiceofficial, a YouTube channel that focuses on social media celebrities. @Brainjuiceofficial says Turner was born in October 2000, the oldest child of a single mother of five whose husband was not in the picture.
Devon Turner, a.k.a. “Punchmade Dev,” in an undated photo.
The video says the six-foot five Turner played basketball, track and football in high school, but that he gradually became obsessed with playing the video game NBA 2K17 and building a following of people watching him play the game competitively online.
According to this brief documentary, Turner previously streamed his NBA 2K17 videos on a YouTube channel called DevTakeFlight, although he originally went by the nickname OBN Dev.
“Things may eventually catch up to Devon if he isn’t careful,” @Brainjuiceofficial observed, noting that Turner has been shot at before, and also robbed at an ATM while flexing a bunch of cash for a picture and wearing $500k in jewelry. “Although you have a lot of people that are into what you do, there are a lot of people waiting for you to slip up.”
A California man who lost $100,000 in a 2021 SIM-swapping attack is suing the unknown holder of a cryptocurrency wallet that harbors his stolen funds. The case is thought to be the first in which a federal court has recognized the use of information included in a bitcoin transaction — such as a link to a civil claim filed in federal court — as reasonably likely to provide notice of the lawsuit to the defendant. Experts say the development could make it easier for victims of crypto heists to recover stolen funds through the courts without having to wait years for law enforcement to take notice or help.

Ryan Dellone, a healthcare worker in Fresno, Calif., asserts that thieves stole his bitcoin on Dec. 14, 2021, by executing an unauthorized SIM-swap that involved an employee at his mobile phone provider who switched Dellone’s phone number over to a new device the attackers controlled.
Dellone says the crooks then used his phone number to break into his account at Coinbase and siphon roughly $100,000 worth of cryptocurrencies. Coinbase is also named as a defendant in the lawsuit, which alleges the company ignored multiple red flags, and that it should have detected and stopped the theft. Coinbase did not respond to requests for comment.
Working with experts who track the flow of funds stolen in cryptocurrency heists, Dellone’s lawyer Ethan Mora identified a bitcoin wallet that was the ultimate destination of his client’s stolen crypto. Mora says his client has since been made aware that the bitcoin address in question is embroiled in an ongoing federal investigation into a cryptocurrency theft ring.
Mora said it’s unclear if the bitcoin address that holds his client’s stolen money is being held by the government or by the anonymous hackers. Nevertheless, he is pursuing a novel legal strategy that allows his client to serve notice of the civil suit to that bitcoin address — and potentially win a default judgment to seize his client’s funds within — without knowing the identity of his attackers or anything about the account holder.
In a civil lawsuit seeking monetary damages, a default judgment is usually entered on behalf of the plaintiff if the defendant fails to respond to the complaint within a specified time. Assuming that the cybercriminals who stole the money don’t dispute Dellone’s claim, experts say the money could be seized by cryptocurrency exchanges if the thieves ever tried to move it or spend it.
The U.S. courts have generally held that if you’re going to sue someone, you have to provide some kind of meaningful and timely communication about that lawsuit to the defendant in a way that is reasonably likely to provide them notice.
Not so long ago, you had track down your defendant and hire someone to physically serve them with a copy of the court papers. But legal experts say the courts have evolved their thinking in recent years about what constitutes meaningful service, and now allow notification via email.
On Dec. 14, 2023, a federal judge in the Eastern District of California granted Dellone permission to serve notice of his lawsuit directly to the suspected hackers’ bitcoin address — using a short message that was attached to roughly $100 worth of bitcoin Mora sent to the address.
Bitcoin transactions are public record, and each transaction can be sent along with an optional short message. The message uses what’s known as an “OP RETURN,” or an instruction of the Bitcoin scripting language that allows users to attach metadata to a transaction — and thus save it on the blockchain.
In the $100 bitcoin transaction Mora sent to the disputed bitcoin address, the OP RETURN message read: “OSERVICE – SUMMONS, COMPLAINT U.S. Dist. E.D. Cal. LINK: t.ly/123cv01408_service,” which is a short link to a copy of the lawsuit hosted on Google Drive.
“The courts are adapting to the new style of service of process,” said Mark Rasch, a former federal prosecutor at the U.S. Department of Justice. “And that’s helpful and useful and necessary.”
Rasch said Mora’s strategy could force the government to divulge information about their case, or else explain to a judge why the plaintiff shouldn’t be able to recover their stolen funds without further delay. Rasch said it could be that Dellone’s stolen crypto was seized as part of a government asset forfeiture, but that either way there is no reason Uncle Sam should hold some cybercrime victims’ life savings indefinitely.
“The government doesn’t need the crypto as evidence, but in a forfeiture action the money goes to the government,” Rasch said. “But it was never the government’s money, and that doesn’t help the victim. The government should be providing information to the victims of cryptocurrency theft so that their attorneys can go get the money back themselves.”
Nick Bax is a security researcher who specializes in tracing the labyrinthine activity of criminals trying to use cryptocurrency exchanges and other financial instruments to launder the proceeds of cybercrime. Bax said Mora’s method could allow more victims to stake legitimate legal claims to their stolen funds.
“If you get a default judgment against a bitcoin address, for example, and then down the road that bitcoin gets sent to an exchange that complies with or abides by U.S. court orders, then it’s yours,” Bax said. “I’ve seen funds with a court order on them get frozen by the exchanges that decided it made sense to comply with orders from a U.S. federal court.”
Bax’s research was featured in a Sept. 2023 story here about how experts now believe it’s likely hackers are cracking open some of the password vaults stolen in the 2022 data breach at LastPass.
“I’ve talked to a lot victims who have had life-changing amounts of money being seized and would like that money back,” Bax said. “A big goal here is just making civil cases more efficient. Because then people can help themselves and they don’t need to rely solely on law enforcement with its limited resources. And that’s really the goal: To scale this and make it economically viable.”
While Dellone’s lawsuit may be the first time anyone has obtained approval from a federal judge to use bitcoin to notify another party of a civil action, the technique has been used in several recent unrelated cases involving other cryptocurrencies, including Ethereum and NFTs.
The law firm DLAPiper writes that in November 2022, the U.S. District Court for the Southern District of Florida “authorized service of a lawsuit seeking the recovery of stolen digital assets by way of a non-fungible token or NFT containing the text of the complaint and summons, as well as a hyperlink to a website created by the plaintiffs containing all pleadings and orders in the action.”
In approving Dellone’s request for service via bitcoin transaction, the judge overseeing the case cited a recent New York Superior Court ruling in a John Doe case brought by victims seeking to unmask the crooks behind a $1.3 million cyberheist.
In the New York case, the state trial court found it was acceptable for the plaintiffs to serve notice of the suit via cryptocurrency transactions because the defendants regularly used the Blockchain address to which the tokens were sent, and had recently done so. Also, the New York court found that because the account in question contained a significant sum of money, it was unlikely to be abandoned or forgotten.
“Thus the court inferred the defendants were likely to access the account in the future,” wrote Judge Helena M. March-Kuchta, for the Eastern District of California, summarizing the New York case. “Finally, the plaintiff had no alternative means of contacting these unknown defendants.”
Experts say regardless of the reason for a cryptocurrency theft or loss — whether it’s from a romance scam or a straight-up digital mugging — it’s important for victims to file an official report both with their local police and with the FBI’s Internet Crime Complaint Center (ic3.gov). The IC3 collects reports on cybercrime and sometimes bundles victim reports into cases for DOJ/FBI prosecutors and investigators.
The hard truth is that most victims will never see their stolen funds again. But sometimes federal investigators win minor victories and manage to seize or freeze crypto assets that are known to be associated with specific crimes and criminals. In those cases, the government will eventually make an effort to find, contact and in some cases remunerate known victims.
It might take many years for this process to unfold. But if and when they do make that effort, federal investigators are likely to focus their energies and attention responding to victims who staked a claim and can support it with documentation.
But have no illusions that any of this is likely to happen in a timeframe that is meaningful to victims in the short run. For example, in 2013 the U.S. government seized the assets of the virtual currency Liberty Reserve, massively disrupting a major vehicle for laundering the proceeds of cybercrime and other illegal activities.
When the government offered remuneration to Liberty Reserve account holders who wished to make a financial loss claim and supply supporting documentation, KrebsOnSecurity filed a claim. There wasn’t money much in my Liberty Reserve account; I simply wanted to know how long it would take for federal investigators to follow up on my claim, or indeed if they would at all.
In 2020 KrebsOnSecurity was contacted by an investigator with the U.S. Internal Revenue Service (IRS) who was seeking to discuss my claim. The investigator said they would have called sooner, but that it had taken that long for the IRS to gain legal access to the funds seized in the 2013 Liberty Reserve takedown.
In 2020, the United States brought charges against four men accused of building a bulletproof hosting empire that once dominated the Russian cybercrime industry and supported multiple organized cybercrime groups. All four pleaded guilty to conspiracy and racketeering charges. But there is a fascinating and untold backstory behind the two Russian men involved, who co-ran the world’s top spam forum and worked closely with Russia’s most dangerous cybercriminals.
From January 2005 to April 2013, there were two primary administrators of the cybercrime forum Spamdot (a.k.a Spamit), an invite-only community for Russian-speaking people in the businesses of sending spam and building botnets of infected computers to relay said spam. The Spamdot admins went by the nicknames Icamis (a.k.a. Ika), and Salomon (a.k.a. Sal).
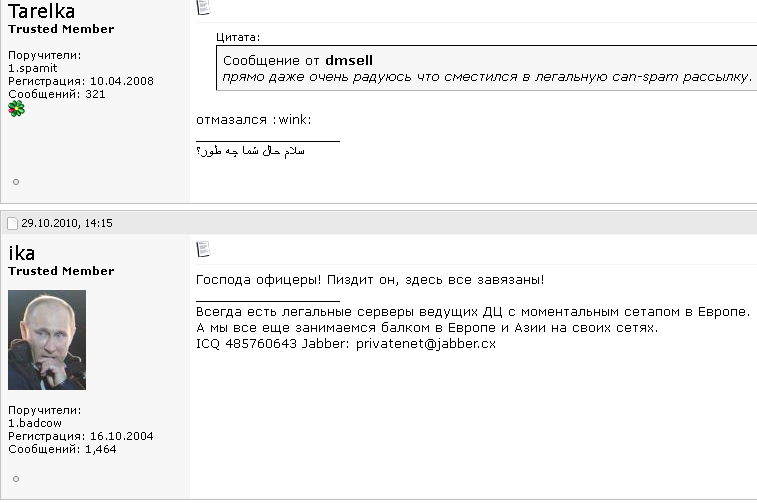
Spamdot forum administrator “Ika” a.k.a. “Icamis” responds to a message from “Tarelka,” the botmaster behind the Rustock botnet. Dmsell said: “I’m actually very glad that I switched to legal spam mailing,” prompting Tarelka and Ika to scoff.
As detailed in my 2014 book, Spam Nation, Spamdot was home to crooks controlling some of the world’s nastiest botnets, global malware contagions that went by exotic names like Rustock, Cutwail, Mega-D, Festi, Waledac, and Grum.
Icamis and Sal were in daily communications with these botmasters, via the Spamdot forum and private messages. Collectively in control over millions of spam-spewing zombies, those botmasters also continuously harvested passwords and other data from infected machines.
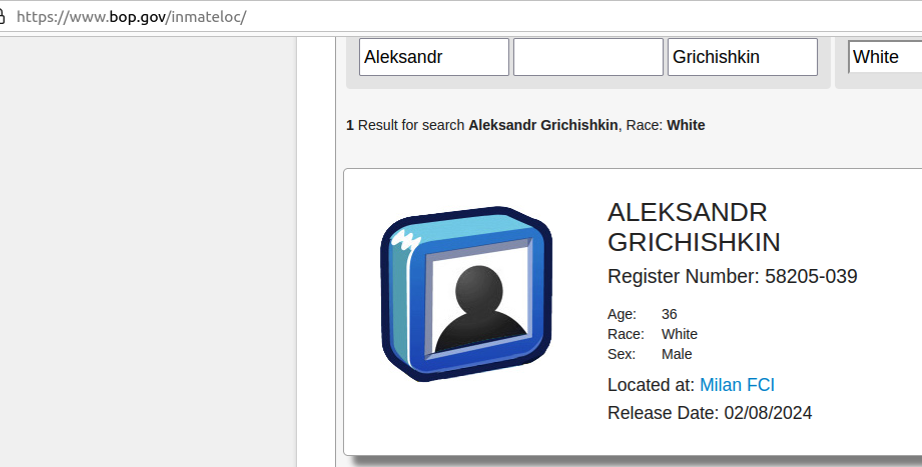
As we’ll see in a moment, Salomon is now behind bars, in part because he helped to rob dozens of small businesses in the United States using some of those same harvested passwords. He is currently housed in a federal prison in Michigan, serving the final stretch of a 60-month sentence.
But the identity and whereabouts of Icamis have remained a mystery to this author until recently. For years, security experts — and indeed, many top cybercriminals in the Spamit affiliate program — have expressed the belief that Sal and Icamis were likely the same person using two different identities. And there were many good reasons to support this conclusion.
For example, in 2010 Spamdot and its spam affiliate program Spamit were hacked, and its user database shows Sal and Icamis often accessed the forum from the same Internet address — usually from Cherepovets, an industrial town situated approximately 230 miles north of Moscow. Also, it was common for Icamis to reply when Spamdot members communicated a request or complaint to Sal, and vice versa.
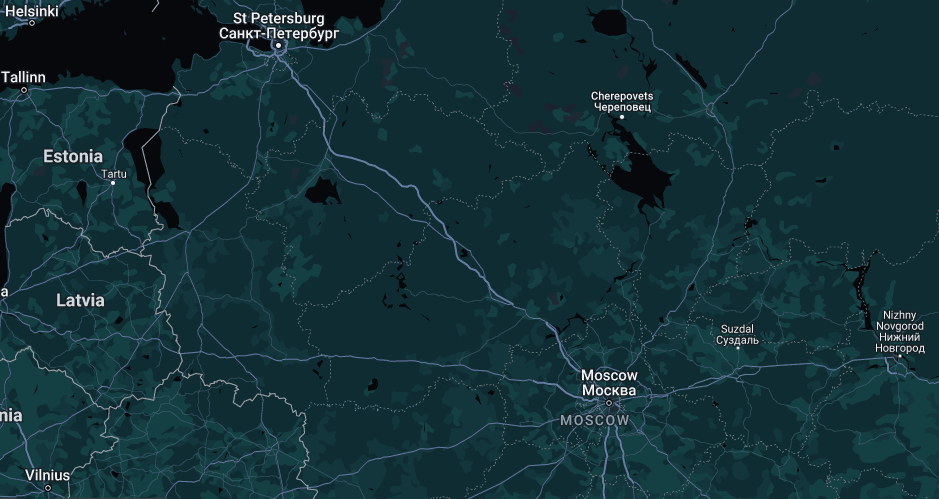
Image: maps.google.com
Still, other clues suggested Icamis and Sal were two separate individuals. For starters, they frequently changed the status on their instant messenger clients at different times. Also, they each privately discussed with others having attended different universities.
KrebsOnSecurity began researching Icamis’s real-life identity in 2012, but failed to revisit any of that research until recently. In December 2023, KrebsOnSecurity published new details about the identity of “Rescator,” a Russian cybercriminal who is thought to be closely connected to the 2013 data breach at Target.
That story mentioned Rescator’s real-life identity was exposed by Icamis in April 2013, as part of a lengthy farewell letter Ika wrote to Spamdot members wherein Ika said he was closing the forum and quitting the cybercrime business entirely.
To no one’s shock, Icamis didn’t quit the business: He simply became more quiet and circumspect about his work, which increasingly was focused on helping crime groups siphon funds from U.S. bank accounts. But the Rescator story was a reminder that 10 years worth of research on who Ika/Icamis is in real life had been completely set aside. This post is an attempt to remedy that omission.
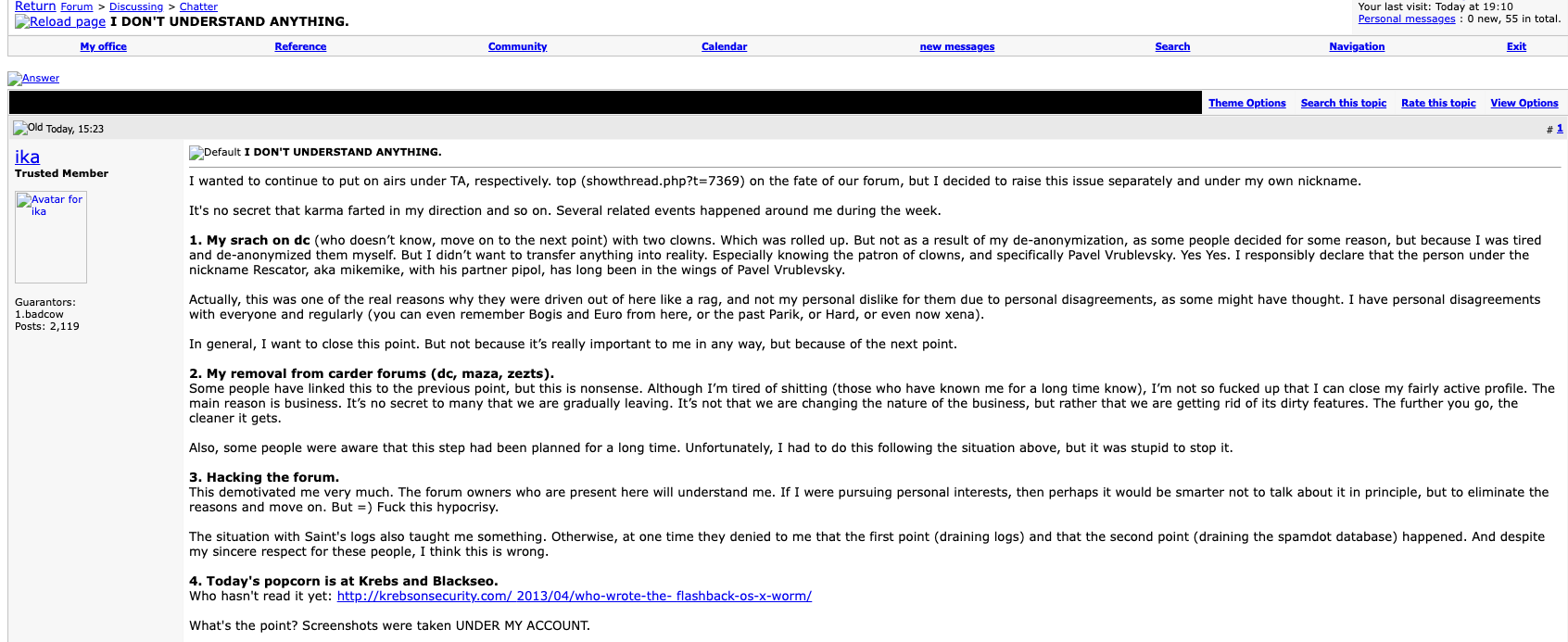
The farewell post from Ika (aka Icamis), the administrator of both the BlackSEO forum and Pustota, the successor forum to Spamit/Spamdot.
Icamis and Sal offered a comprehensive package of goods and services that any aspiring or accomplished spammer would need on a day-to-day basis: Virtually unlimited bulletproof domain registration and hosting services, as well as services that helped botmasters evade spam block lists generated by anti-spam groups like Spamhaus.org. Here’s snippet of Icamis’s ad on Spamdot from Aug. 2008, wherein he addresses forum members with the salutation, “Hello Gentlemen Scammers.”
We are glad to present you our services!
Many are already aware (and are our clients), but publicity is never superfluous.Domains.
– all major gtlds (com, net, org, info, biz)
– many interesting and uninteresting cctlds
– options for any topic
– processing of any quantities
– guarantees
– exceptionally low prices for domains for white and gray schemes (including any SEO and affiliate spam )
– control panel with balances and auto-registration
– all services under the Ikamis brand, proven over the years;)Servers.
– long-term partnerships with several [data centers] in several parts of the world for any topic
– your own data center (no longer in Russia ;)) for gray and white topics
– any configuration and any hardware
– your own IP networks (PI, not PA) and full legal support
– realtime backups to neutral sites
– guarantees and full responsibility for the services provided
– non-standard equipment on request
– our own admins to resolve any technical issues (services are free for clients)
– hosting (shared and vps) is also possibleNon-standard and related services.
– ssl certificates signed by geotrust and thawte
– old domains (any year, any quantity)
– beautiful domains (keyword, short, etc.)
– domains with indicators (any, for SEO, etc.)
– making unstable gtld domains stable
– interception and hijacking of custom domains (expensive)
– full domain posting via web.archive.org with restoration of native content (preliminary applications)
– any updates to our panels to suit your needs upon request (our own coders)All orders for the “Domains” sections and “Servers” are carried out during the day (depending on our workload).
For non-standard and related services, a preliminary application is required 30 days in advance (except for ssl certificates – within 24 hours).
Icamis and Sal frequently claimed that their service kept Spamhaus and other anti-spam groups several steps behind their operations. But it’s clear that those anti-spam operations had a real and painful impact on spam revenues, and Salomon was obsessed with striking back at anti-spam groups, particularly Spamhaus.
In 2007, Salomon collected more than $3,000 from botmasters affiliated with competing spam affiliate programs that wanted to see Spamhaus suffer, and the money was used to fund a week-long distributed denial-of-service (DDoS) attack against Spamhaus and its online infrastructure. But rather than divert their spam botnets from their normal activity and thereby decrease sales, the botmasters voted to create a new DDoS botnet by purchasing installations of DDoS malware on thousands of already-hacked PCs (at a rate of $25 per 1,000 installs).
As an affiliate of Spamdot, Salomon used the email address ad1@safe-mail.net, and the password 19871987gr. The breach tracking service Constella Intelligence found the password 19871987gr was used by the email address grichishkin@gmail.com. Multiple accounts are registered to that email address under the name Alexander Valerievich Grichishkin, from Cherepovets.
In 2020, Grichishkin was arrested outside of Russia on a warrant for providing bulletproof hosting services to cybercriminal gangs. The U.S. government said Grichishkin and three others set up the infrastructure used by cybercriminals between 2009 to 2015 to distribute malware and attack financial institutions and victims throughout the United States.
Those clients included crooks using malware like Zeus, SpyEye, Citadel and the Blackhole exploit kit to build botnets and steal banking credentials.
“The Organization and its members helped their clients to access computers without authorization, steal financial information (including banking credentials), and initiate unauthorized wire transfers from victims’ financial accounts,” the government’s complaint stated.
Grichishkin pleaded guilty to conspiracy charges and was sentenced to four years in prison. He is 36 years old, has a wife and kids in Thailand, and is slated for release on February 8, 2024.
The identity of Icamis came into view when KrebsOnSecurity began focusing on clues that might connect Icamis to Cherepovets (Ika’s apparent hometown based on the Internet addresses he regularly used to access Spamdot).
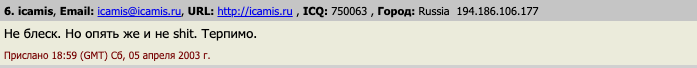
Historic domain ownership records from DomainTools.com reveal that many of the email addresses and domains connected to Icamis invoke the name “Andrew Artz,” including icamis[.]ws, icamis[.]ru, and icamis[.]biz. Icamis promoted his services in 2003 — such as bulk-domains[.]info — using the email address icamis@4host.info. From one of his ads in 2005:
Domains For Projects Advertised By Spam
I can register bulletproof domains for sites and projects advertised by spam(of course they must be legal). I can not provide DNS for u, only domains. The price will be:
65$ for domain[if u will buy less than 5 domains]
50$ for domain[more than 5 domains]
45$ for domain[more than 10 domains]
These prices are for domains in the .net & .com zones.
If u want to order domains write me to: icamis@4host.info
In 2009, an “Andrew Artz” registered at the hosting service FirstVDS.com using the email address icamis@4host.info, with a notation saying the company name attached to the account was “WMPay.” Likewise, the bulletproof domain service icamis[.]ws was registered to an Andrew Artz.
The domain wmpay.ru is registered to the phonetically similar name “Andrew Hertz,” at andrew@wmpay.ru. A search on “icamis.ru” in Google brings up a 2003 post by him on a discussion forum designed by and for students of Amtek, a secondary school in Cherepovets (Icamis was commenting from an Internet address in Cherepovets).
The website amtek-foreva-narod.ru is still online, and it links to several yearbooks for Amtek graduates. It states that the yearbook for the Amtek class of 2004 is hosted at 41.wmpay[.]com.
The yearbook photos for the Amtek class of 2004 are not indexed in the Wayback Machine at archive.org, but the names and nicknames of 16 students remain. However, it appears that the entry for one student — the Wmpay[.]com site administrator — was removed at some point.
In 2004, the administrator of the Amtek discussion forum — a 2003 graduate who used the handle “Grand” — observed that there were three people named Andrey who graduated from Amtek in 2004, but one of them was conspicuously absent from the yearbook at wmpay[.]ru: Andrey Skvortsov.
To bring this full circle, Icamis was Andrey Skvortsov, the other Russian man charged alongside Grichiskin (the two others who pleaded guilty to conspiracy charges were from Estonia and Lithuania). All of the defendants in that case pleaded guilty to conspiracy to engage in a Racketeer Influenced Corrupt Organization (RICO).
[Author’s note: No doubt government prosecutors had their own reasons for omitting the nicknames of the defendants in their press releases, but that information sure would have saved me a lot of time and effort].
Skvortsov was sentenced to time served, and presumably deported. His current whereabouts are unknown and he was not reachable for comment via his known contact addresses.
The government says Ika and Sal’s bulletproof hosting empire provided extensive support for a highly damaging cybercrime group known as the JabberZeus Crew, which worked closely with the author of the Zeus Trojan — Evgeniy Mikhailovich Bogachev — to develop a then-advanced strain of the Zeus malware that was designed to defeat one-time codes for authentication. Bogachev is a top Russian cybercriminal with a standing $3 million bounty on his head from the FBI.
The JabberZeus Crew stole money by constantly recruiting money mules, people in the United States and in Europe who could be enticed or tricked into forwarding money stolen from cybercrime victims. Interestingly, Icamis’s various email addresses are connected to websites for a vast network of phony technology companies that claimed they needed people with bank accounts to help pay their overseas employees.
Icamis used the email address tech@safe-mail.net on Spamdot, and this email address is tied to the registration records for multiple phony technology companies that were set up to recruit money mules.
One such site — sun-technology[.]net — advertised itself as a Hong Kong-based electronics firm that was looking for “honest, responsible and motivated people in UK, USA, AU and NZ to be Sales Representatives in your particular region and receive payments from our clients. Agent commission is 5 percent of total amount received to the personal bank account. You may use your existing bank account or open a new one for these purposes.”
In January 2010, KrebsOnSecurity broke the news that the JabberZeus crew had just used money mules to steal $500,000 from tiny Duanesburg Central School District in upstate New York. As part of his sentence, Skvortsov was ordered to pay $497,200 in restitution to the Duanesburg Central School District.
The JabberZeus Crew operated mainly out of the eastern Ukraine city of Donetsk, which was always pro-Russia and is now occupied by Russian forces. But when Russia invaded Ukraine in February 2022, the alleged leader of the notorious cybercrime gang — Vyacheslav Igoravich Andreev (a.ka. Penchukov) — fled his mandatory military service orders and was arrested in Geneva, Switzerland. He is currently in federal custody awaiting trial, and is slated to be arraigned in U.S. federal court tomorrow (Jan. 9, 2024). A copy of the indictment against Andreev is here (PDF).

Andreev, aka “Tank,” seen here performing as a DJ in Ukraine in an undated photo from social media.