More than five years after domain name registrars started redacting personal data from all public domain registration records, the non-profit organization overseeing the domain industry has introduced a centralized online service designed to make it easier for researchers, law enforcement and others to request the information directly from registrars.

In May 2018, the Internet Corporation for Assigned Names and Numbers (ICANN) — the nonprofit entity that manages the global domain name system — instructed all registrars to redact the customer’s name, address, phone number and email from WHOIS, the system for querying databases that store the registered users of domain names and blocks of Internet address ranges.
ICANN made the policy change in response to the General Data Protection Regulation (GDPR), a law enacted by the European Parliament that requires companies to gain affirmative consent for any personal information they collect on people within the European Union. In the meantime, registrars were to continue collecting the data but not publish it, and ICANN promised it would develop a system that facilitates access to this information.
At the end of November 2023, ICANN launched the Registration Data Request Service (RDRS), which is designed as a one-stop shop to submit registration data requests to participating registrars. This video from ICANN walks through how the system works.
Accredited registrars don’t have to participate, but ICANN is asking all registrars to join and says participants can opt out or stop using it at any time. ICANN contends that the use of a standardized request form makes it easier for the correct information and supporting documents to be provided to evaluate a request.
ICANN says the RDRS doesn’t guarantee access to requested registration data, and that all communication and data disclosure between the registrars and requestors takes place outside of the system. The service can’t be used to request WHOIS data tied to country-code top level domains (CCTLDs), such as those ending in .de (Germany) or .nz (New Zealand), for example.
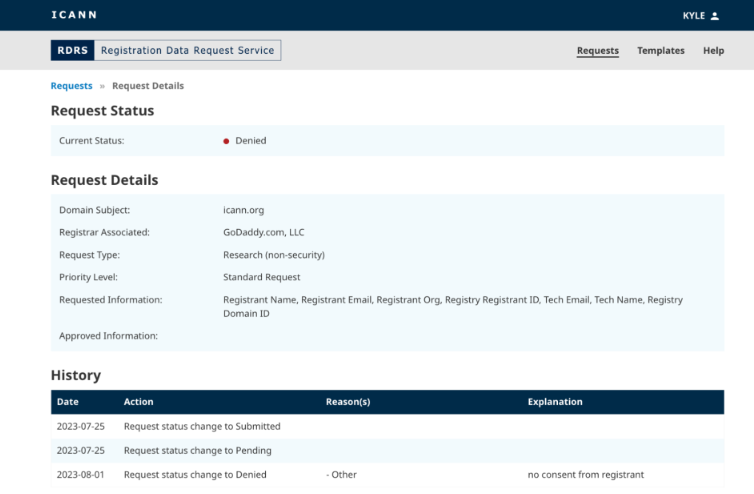
The RDRS portal.
As Catalin Cimpanu writes for Risky Business News, currently investigators can file legal requests or abuse reports with each individual registrar, but the idea behind the RDRS is to create a place where requests from “verified” parties can be honored faster and with a higher degree of trust.
The registrar community generally views public WHOIS data as a nuisance issue for their domain customers and an unwelcome cost-center. Privacy advocates maintain that cybercriminals don’t provide their real information in registration records anyway, and that requiring WHOIS data to be public simply causes domain registrants to be pestered by spammers, scammers and stalkers.
Meanwhile, security experts argue that even in cases where online abusers provide intentionally misleading or false information in WHOIS records, that information is still extremely useful in mapping the extent of their malware, phishing and scamming operations. What’s more, the overwhelming majority of phishing is performed with the help of compromised domains, and the primary method for cleaning up those compromises is using WHOIS data to contact the victim and/or their hosting provider.
Anyone looking for copious examples of both need only to search this Web site for the term “WHOIS,” which yields dozens of stories and investigations that simply would not have been possible without the data available in the global WHOIS records.
KrebsOnSecurity remains doubtful that participating registrars will be any more likely to share WHOIS data with researchers just because the request comes through ICANN. But I look forward to being wrong on this one, and will certainly mention it in my reporting if the RDRS proves useful.
Regardless of whether the RDRS succeeds or fails, there is another European law that takes effect in 2024 which is likely to place additional pressure on registrars to respond to legitimate WHOIS data requests. The new Network and Information Security Directive (NIS2), which EU member states have until October 2024 to implement, requires registrars to keep much more accurate WHOIS records, and to respond within as little as 24 hours to WHOIS data requests tied everything from phishing, malware and spam to copyright and brand enforcement.
One of the cybercrime underground’s more active sellers of Social Security numbers, background and credit reports has been pulling data from hacked accounts at the U.S. consumer data broker USinfoSearch, KrebsOnSecurity has learned.
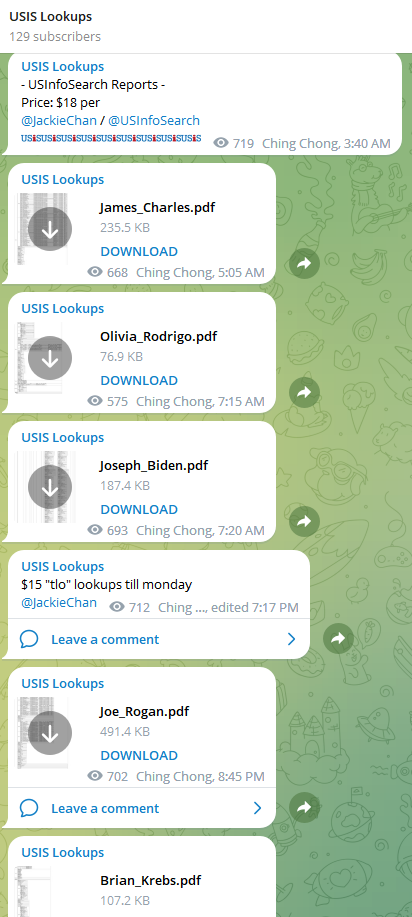 Since at least February 2023, a service advertised on Telegram called USiSLookups has operated an automated bot that allows anyone to look up the SSN or background report on virtually any American. For prices ranging from $8 to $40 and payable via virtual currency, the bot will return detailed consumer background reports automatically in just a few moments.
Since at least February 2023, a service advertised on Telegram called USiSLookups has operated an automated bot that allows anyone to look up the SSN or background report on virtually any American. For prices ranging from $8 to $40 and payable via virtual currency, the bot will return detailed consumer background reports automatically in just a few moments.
USiSLookups is the project of a cybercriminal who uses the nicknames JackieChan/USInfoSearch, and the Telegram channel for this service features a small number of sample background reports, including that of President Joe Biden, and podcaster Joe Rogan. The data in those reports includes the subject’s date of birth, address, previous addresses, previous phone numbers and employers, known relatives and associates, and driver’s license information.
JackieChan’s service abuses the name and trademarks of Columbus, OH based data broker USinfoSearch, whose website says it provides “identity and background information to assist with risk management, fraud prevention, identity and age verification, skip tracing, and more.”
“We specialize in non-FCRA data from numerous proprietary sources to deliver the information you need, when you need it,” the company’s website explains. “Our services include API-based access for those integrating data into their product or application, as well as bulk and batch processing of records to suit every client.”
As luck would have it, my report was also listed in the Telegram channel for this identity fraud service, presumably as a teaser for would-be customers. On October 19, 2023, KrebsOnSecurity shared a copy of this file with the real USinfoSearch, along with a request for information about the provenance of the data.
USinfoSearch said it would investigate the report, which appears to have been obtained on or before June 30, 2023. On Nov. 9, 2023, Scott Hostettler, general manager of USinfoSearch parent Martin Data LLC shared a written statement about their investigation that suggested the ID theft service was trying to pass off someone else’s consumer data as coming from USinfoSearch:
Regarding the Telegram incident, we understand the importance of protecting sensitive information and upholding the trust of our users is our top priority. Any allegation that we have provided data to criminals is in direct opposition to our fundamental principles and the protective measures we have established and continually monitor to prevent any unauthorized disclosure. Because Martin Data has a reputation for high-quality data, thieves may steal data from other sources and then disguise it as ours. While we implement appropriate safeguards to guarantee that our data is only accessible by those who are legally permitted, unauthorized parties will continue to try to access our data. Thankfully, the requirements needed to pass our credentialing process is tough even for established honest companies.
USinfoSearch’s statement did not address any questions put to the company, such as whether it requires multi-factor authentication for customer accounts, or whether my report had actually come from USinfoSearch’s systems.
After much badgering, on Nov. 21 Hostettler acknowledged that the USinfoSearch identity fraud service on Telegram was in fact pulling data from an account belonging to a vetted USinfoSearch client.
“I do know 100% that my company did not give access to the group who created the bots, but they did gain access to a client,” Hostettler said of the Telegram-based identity fraud service. “I apologize for any inconvenience this has caused.”
Hostettler said USinfoSearch heavily vets any new potential clients, and that all users are required to undergo a background check and provide certain documents. Even so, he said, several fraudsters each month present themselves as credible business owners or C-level executives during the credentialing process, completing the application and providing the necessary documentation to open a new account.
“The level of skill and craftsmanship demonstrated in the creation of these supporting documents is incredible,” Hostettler said. “The numerous licenses provided appear to be exact replicas of the original document. Fortunately, I’ve discovered several methods of verification that do not rely solely on those documents to catch the fraudsters.”
“These people are unrelenting, and they act without regard for the consequences,” Hostettler continued. “After I deny their access, they will contact us again within the week using the same credentials. In the past, I’ve notified both the individual whose identity is being used fraudulently and the local police. Both are hesitant to act because nothing can be done to the offender if they are not apprehended. That is where most attention is needed.”
JackieChan is most active on Telegram channels focused on “SIM swapping,” which involves bribing or tricking mobile phone company employees into redirecting a target’s phone number to a device the attackers control. SIM swapping allows crooks to temporarily intercept the target’s text messages and phone calls, including any links or one-time codes for authentication that are delivered via SMS.
Reached on Telegram, JackieChan said most of his clients hail from the criminal SIM swapping world, and that the bulk of his customers use his service via an application programming interface (API) that allows customers to integrate the lookup service with other web-based services, databases, or applications.
“Sim channels is where I get most of my customers,” JackieChan told KrebsOnSecurity. “I’m averaging around 100 lookups per day on the [Telegram] bot, and around 400 per day on the API.”
JackieChan claims his USinfoSearch bot on Telegram abuses stolen credentials needed to access an API used by the real USinfoSearch, and that his service was powered by USinfoSearch account credentials that were stolen by malicious software tied to a botnet that he claims to have operated for some time.
This is not the first time USinfoSearch has had trouble with identity thieves masquerading as legitimate customers. In 2013, KrebsOnSecurity broke the news that an identity fraud service in the underground called “SuperGet[.]info” was reselling access to personal and financial data on more than 200 million Americans that was obtained via the big-three credit bureau Experian.
The consumer data resold by Superget was not obtained directly from Experian, but rather via USinfoSearch. At the time, USinfoSearch had a contractual agreement with a California company named Court Ventures, whereby customers of Court Ventures had access to the USinfoSearch data, and vice versa.
When Court Ventures was purchased by Experian in 2012, the proprietor of SuperGet — a Vietnamese hacker named Hieu Minh Ngo who had impersonated an American private investigator — was grandfathered in as a client. The U.S. Secret Service agent who oversaw Ngo’s capture, extradition, prosecution and rehabilitation told KrebsOnSecurity he’s unaware of any other cybercriminal who has caused more material financial harm to more Americans than Ngo.
JackieChan also sells access to hacked email accounts belonging to law enforcement personnel in the United States and abroad. Hacked police department emails can come in handy for ID thieves trying to pose as law enforcement officials who wish to purchase consumer data from platforms like USinfoSearch. Hence, Mr. Hostettler’s ongoing battle with fraudsters seeking access to his company’s service.
These police credentials are mainly marketed to criminals seeking fraudulent “Emergency Data Requests,” wherein crooks use compromised government and police department email accounts to rapidly obtain customer account data from mobile providers, ISPs and social media companies.
Normally, these companies will require law enforcement officials to supply a subpoena before turning over customer or user records. But EDRs allow police to bypass that process by attesting that the information sought is related to an urgent matter of life and death, such as an impending suicide or terrorist attack.

In response to an alarming increase in the volume of fraudulent EDRs, many service providers have chosen to require all EDRs be processed through a service called Kodex, which seeks to filter EDRs based on the reputation of the law enforcement entity requesting the information, and other attributes of the requestor.
For example, if you want to send an EDR to Coinbase or Twilio, you’ll first need to have valid law enforcement credentials and create an account at the Kodex online portal at these companies. However, Kodex may still throttle or block any requests from any accounts if they set off certain red flags.
Within their own separate Kodex portals, Twilio can’t see requests submitted to Coinbase, or vice versa. But each can see if a law enforcement entity or individual tied to one of their own requests has ever submitted a request to a different Kodex client, and then drill down further into other data about the submitter, such as Internet address(es) used, and the age of the requestor’s email address.
In August, JackieChan was advertising a working Kodex account for sale on the cybercrime channels, including redacted screenshots of the Kodex account dashboard as proof of access.
Kodex co-founder Matt Donahue told KrebsOnSecurity his company immediately detected that the law enforcement email address used to create the Kodex account pictured in JackieChan’s ad was likely stolen from a police officer in India. One big tipoff, Donahue said, was that the person creating the account did so using an Internet address in Brazil.
“There’s a lot of friction we can put in the way for illegitimate actors,” Donahue said. “We don’t let people use VPNs. In this case we let them in to honeypot them, and that’s how they got that screenshot. But nothing was allowed to be transmitted out from that account.”
Massive amounts of data about you and your personal history are available from USinfoSearch and dozens of other data brokers that acquire and sell “non-FCRA” data — i.e., consumer data that cannot be used for the purposes of determining one’s eligibility for credit, insurance, or employment.
Anyone who works in or adjacent to law enforcement is eligible to apply for access to these data brokers, which often market themselves to police departments and to “skip tracers,” essentially bounty hunters hired to locate others in real life — often on behalf of debt collectors, process servers or a bail bondsman.
There are tens of thousands of police jurisdictions around the world — including roughly 18,000 in the United States alone. And the harsh reality is that all it takes for hackers to apply for access to data brokers (and abuse the EDR process) is illicit access to a single police email account.
The trouble is, compromised credentials to law enforcement email accounts show up for sale with alarming frequency on the Telegram channels where JackieChan and their many clients reside. Indeed, Donahue said Kodex so far this year has identified attempted fake EDRs coming from compromised email accounts for police departments in India, Italy, Thailand and Turkey.