When the marital infidelity website AshleyMadison.com learned in July 2015 that hackers were threatening to publish data stolen from 37 million users, the company’s then-CEO Noel Biderman was quick to point the finger at an unnamed former contractor. But as a new documentary series on Hulu reveals [SPOILER ALERT!], there was just one problem with that theory: Their top suspect had killed himself more than a year before the hackers began publishing stolen user data.
The new documentary, The Ashley Madison Affair, begins airing today on Hulu in the United States and on Disney+ in the United Kingdom. The series features interviews with security experts and journalists, Ashley Madison executives, victims of the breach and jilted spouses.
The series also touches on shocking new details unearthed by KrebsOnSecurity and Jeremy Bullock, a data scientist who worked with the show’s producers at the Warner Bros. production company Wall to Wall Media. Bullock had spent many hours poring over the hundreds of thousands of emails that the Ashley Madison hackers stole from Biderman and published online in 2015.
Wall to Wall reached out in July 2022 about collaborating with Bullock after KrebsOnSecurity published A Retrospective on the 2015 Ashley Madison Breach. That piece explored how Biderman — who is Jewish — had become the target of concerted harassment campaigns by anti-Semitic and far-right groups online in the months leading up to the hack.
Whoever hacked Ashley Madison had access to all employee emails, but they only released Biderman’s messages — three years worth. Apropos of my retrospective report, Bullock found that a great many messages in Biderman’s inbox were belligerent and anti-Semitic screeds from a former Ashley Madison employee named William Brewster Harrison.
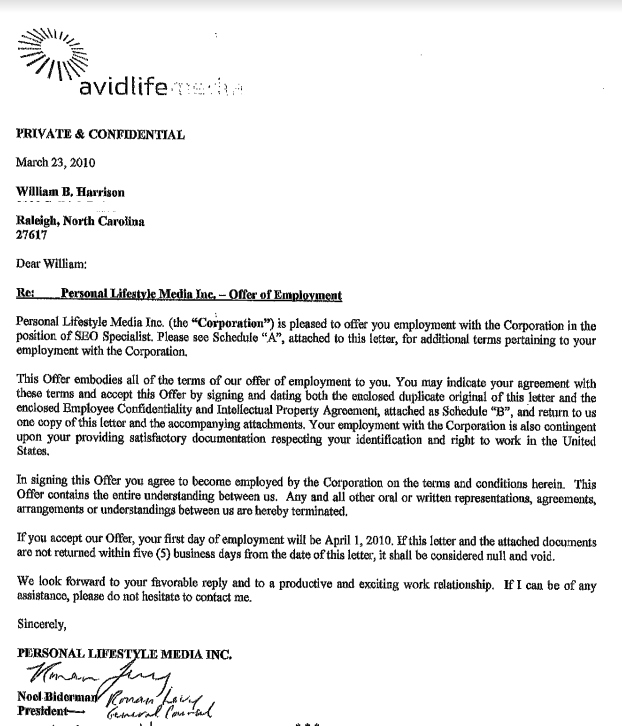
William Harrison’s employment contract with Ashley Madison parent Avid Life Media.
The messages show that Harrison was hired in March 2010 to help promote Ashley Madison online, but the messages also reveal Harrison was heavily involved in helping to create and cultivate phony female accounts on the service.
There is evidence to suggest that in 2010 Harrison was directed to harass the owner of Ashleymadisonsucks.com into closing the site or selling the domain to Ashley Madison.
Ashley Madison’s parent company — Toronto-based Avid Life Media — filed a trademark infringement complaint in 2010 that succeeded in revealing a man named Dennis Bradshaw as the owner. But after being informed that Bradshaw was not subject to Canadian trademark laws, Avid Life offered to buy AshleyMadisonSucks.com for $10,000.
When Bradshaw refused to sell the domain, he and his then-girlfriend were subject to an unrelenting campaign of online harassment and blackmail. It now appears those attacks were perpetrated by Harrison, who sent emails from different accounts at the free email service Vistomail pretending to be Bradshaw, his then-girlfriend and their friends.
[As the documentary points out, the domain AshleyMadisonSucks.com was eventually transferred to Ashley Madison, which then shrewdly used it for advertising and to help debunk theories about why its service was supposedly untrustworthy].
Harrison even went after Bradshaw’s lawyer and wife, listing them both on a website he created called Contact-a-CEO[.]com, which Harrison used to besmirch the name of major companies — including several past employers — all entities he believed had slighted him or his family in some way. The site also claimed to include the names, addresses and phone numbers of top CEOs.
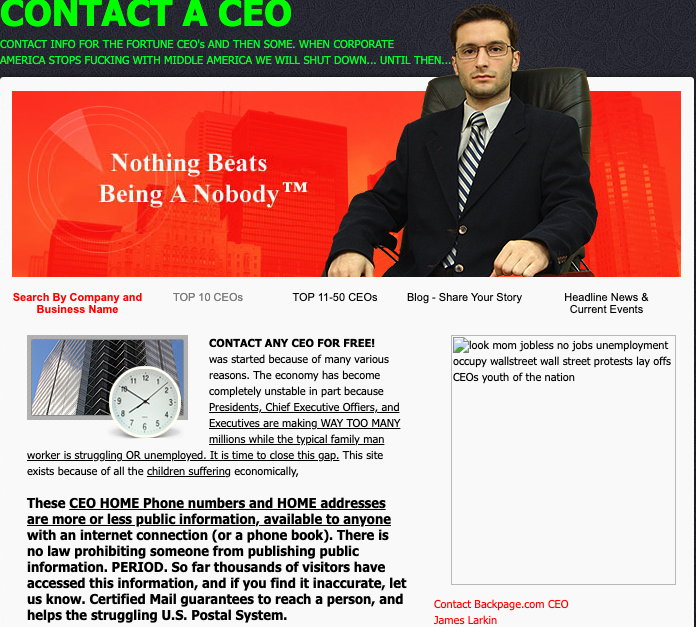
A cached copy of Harrison’s website, contact-the-ceo.com.
An exhaustive analysis of domains registered to the various Vistomail pseudonyms used by Harrison shows he also ran Bash-a-Business[.]com, which Harrison dedicated to “all those sorry ass corporate executives out there profiting from your hard work, organs, lives, ideas, intelligence, and wallets.” Copies of the site at archive.org show it was the work of someone calling themselves “The Chaos Creator.”
Will Harrison was terminated as an Ashley Madison employee in November 2011, and by early 2012 he’d turned his considerable harassment skills squarely against the company. Ashley Madison’s long-suspected army of fake female accounts came to the fore in August 2012 after the former sex worker turned activist and blogger Maggie McNeill published screenshots apparently taken from Ashley Madison’s internal systems suggesting that a large percentage of the female accounts on the service were computer-operated bots.
Ashley Madison’s executives understood that only a handful of employees at the time would have had access to the systems needed to produce the screenshots McNeill published online. In one exchange on Aug. 16, 2012, Ashley Madison’s director of IT was asked to produce a list of all company employees with all-powerful administrator access.
“Who or what is asdfdfsda@asdf.com?,” Biderman asked, after being sent a list of nine email addresses.
“It appears to be the email address Will used for his profiles,” the IT director replied.
“And his access was never shut off until today?,” asked the company’s general counsel Mike Dacks.
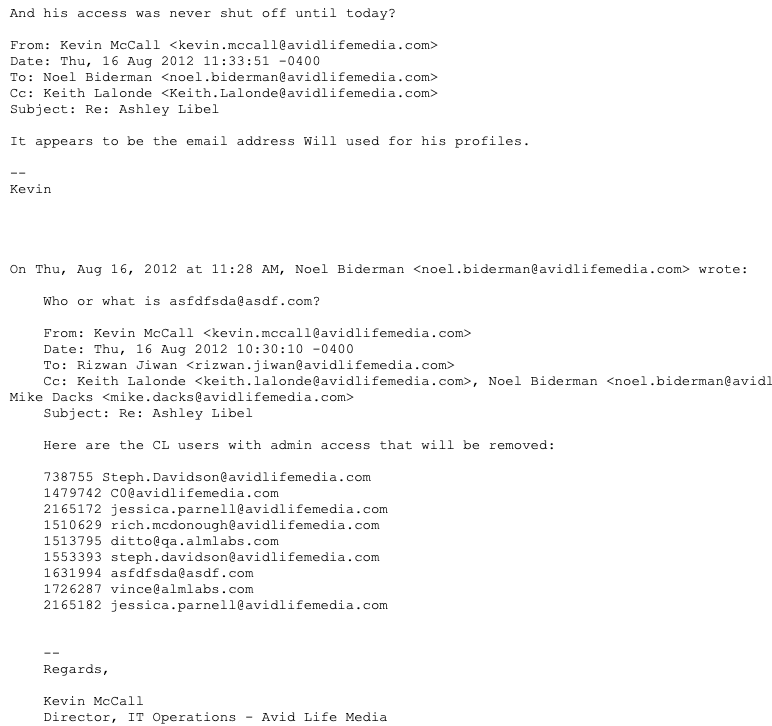
A Biderman email from 2012.
What prompted the data scientist Bullock to reach out were gobs of anti-Semitic diatribes from Harrison, who had taken to labeling Biderman and others “greedy Jew bastards.”
“So good luck, I’m sure we’ll talk again soon, but for now, Ive got better things in the oven,” Harrison wrote to Biderman after his employment contract with Ashley Madison was terminated. “Just remember I outsmarted you last time and I will outsmart and out maneuver you this time too, by keeping myself far far away from the action and just enjoying the sideline view, cheering for the opposition.”
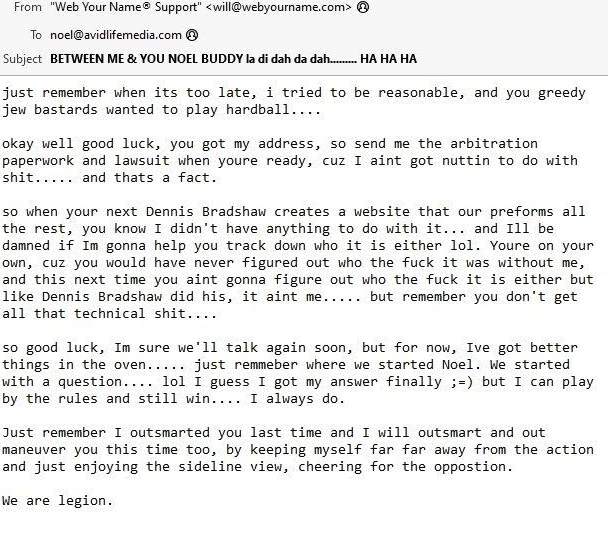
A 2012 email from William Harrison to former Ashley Madison CEO Noel Biderman.
Harrison signed his threatening missive with the salutation, “We are legion,” suggesting that whatever comeuppance he had in store for Ashley Madison would come from a variety of directions and anonymous hackers.
The leaked Biderman emails show that Harrison made good on his threats, and that in the months that followed Harrison began targeting Biderman and other Ashley Madison executives with menacing anonymous emails and spoofed phone calls laced with profanity and anti-Semitic language.
But on Mar. 5, 2014, Harrison committed suicide by shooting himself in the head with a handgun. This fact was apparently unknown to Biderman and other Ashley Madison executives more than a year later when their July 2015 hack was first revealed.
Does Harrison’s untimely suicide rule him out as a suspect in the 2015 hack? Who is The Chaos Creator, and what else transpired between Harrison and Ashley Madison prior to his death? We’ll explore these questions in Part II of this story, to be published early next week.
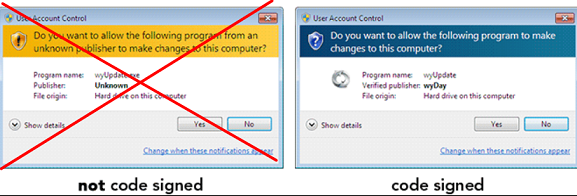
Code-signing certificates are supposed to help authenticate the identity of software publishers, and provide cryptographic assurance that a signed piece of software has not been altered or tampered with. Both of these qualities make stolen or ill-gotten code-signing certificates attractive to cybercriminal groups, who prize their ability to add stealth and longevity to malicious software. This post is a deep dive on “Megatraffer,” a veteran Russian hacker who has practically cornered the underground market for malware focused code-signing certificates since 2015.
A review of Megatraffer’s posts on Russian crime forums shows this user began peddling individual stolen code-signing certs in 2015 on the Russian-language forum Exploit, and soon expanded to selling certificates for cryptographically signing applications and files designed to run in Microsoft Windows, Java, Adobe AIR, Mac and Microsoft Office.
Megatraffer explained that malware purveyors need a certificate because many antivirus products will be far more interested in unsigned software, and because signed files downloaded from the Internet don’t tend to get blocked by security features built into modern web browsers. Additionally, newer versions of Microsoft Windows will complain with a bright yellow or red alert message if users try to install a program that is not signed.
“Why do I need a certificate?” Megatraffer asked rhetorically in their Jan. 2016 sales thread on Exploit. “Antivirus software trusts signed programs more. For some types of software, a digital signature is mandatory.”
At the time, Megatraffer was selling unique code-signing certificates for $700 apiece, and charging more than twice that amount ($1,900) for an “extended validation” or EV code-signing cert, which is supposed to only come with additional identity vetting of the certificate holder. According to Megatraffer, EV certificates were a “must-have” if you wanted to sign malicious software or hardware drivers that would reliably work in newer Windows operating systems.
Part of Megatraffer’s ad. Image: Ke-la.com.
Megatraffer has continued to offer their code-signing services across more than a half-dozen other Russian-language cybercrime forums, mostly in the form of sporadically available EV and non-EV code-signing certificates from major vendors like Thawte and Comodo.
More recently, it appears Megatraffer has been working with ransomware groups to help improve the stealth of their malware. Shortly after Russia invaded Ukraine in February 2022, someone leaked several years of internal chat logs from the Conti ransomware gang, and those logs show Megatraffer was working with the group to help code-sign their malware between July and October 2020.
According to cyber intelligence firm Intel 471, Megatraffer has been active on more than a half-dozen crime forums from September 2009 to the present day. And on most of these identities, Megatraffer has used the email address 774748@gmail.com. That same email address also is tied to two forum accounts for a user with the handle “O.R.Z.”
Constella Intelligence, a company that tracks exposed databases, finds that 774748@gmail.com was used in connection with just a handful of passwords, but most frequently the password “featar24“. Pivoting off of that password reveals a handful of email addresses, including akafitis@gmail.com.
Intel 471 shows akafitis@gmail.com was used to register another O.R.Z. user account — this one on Verified[.]ru in 2008. Prior to that, akafitis@gmail.com was used as the email address for the account “Fitis,” which was active on Exploit between September 2006 and May 2007. Constella found the password “featar24” also was used in conjunction with the email address spampage@yandex.ru, which is tied to yet another O.R.Z. account on Carder[.]su from 2008.
The email address akafitis@gmail.com was used to create a Livejournal blog profile named Fitis that has a large bear as its avatar. In November 2009, Fitis wrote, “I am the perfect criminal. My fingerprints change beyond recognition every few days. At least my laptop is sure of it.”
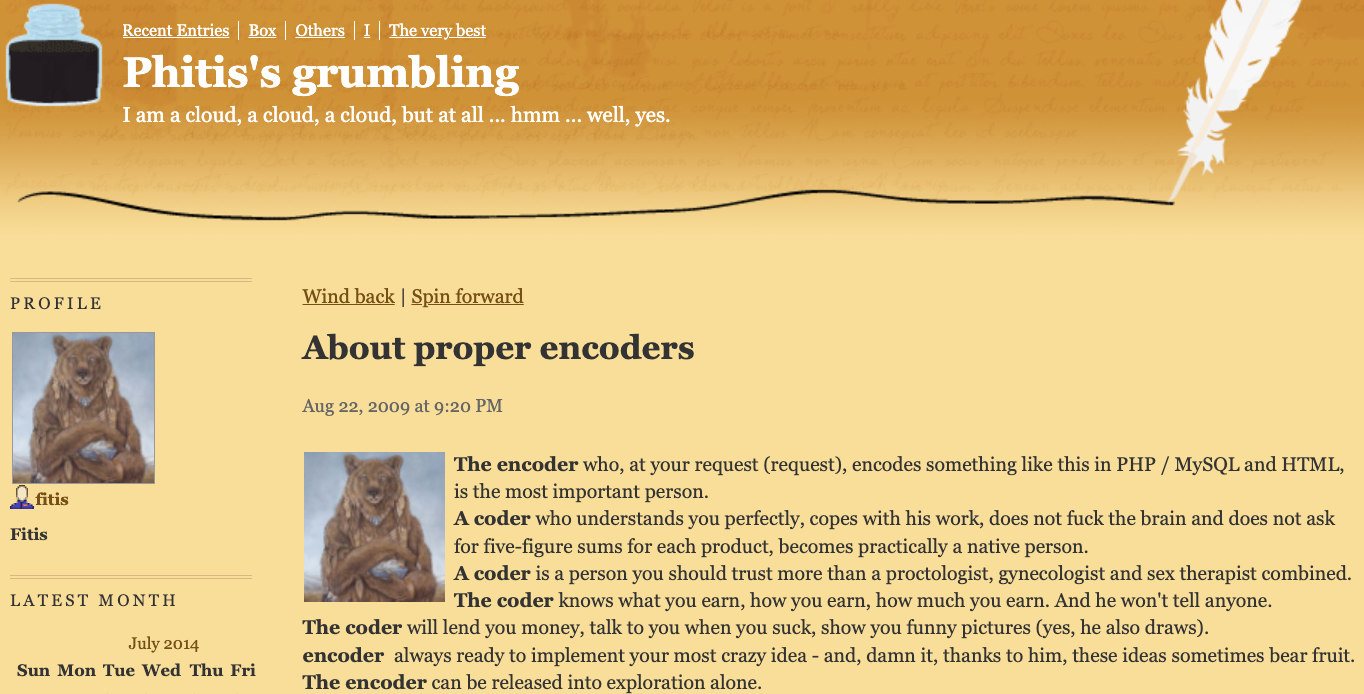
Fitis’s Livejournal account. Image: Archive.org.
Fitis’s real-life identity was exposed in 2010 after two of the biggest sponsors of pharmaceutical spam went to war with each other, and large volumes of internal documents, emails and chat records seized from both spam empires were leaked to this author. That protracted and public conflict formed the backdrop of my 2014 book — “Spam Nation: The Inside Story of Organized Cybercrime, from Global Epidemic to Your Front Door.”
One of the leaked documents included a Microsoft Excel spreadsheet containing the real names, addresses, phone numbers, emails, street addresses and WebMoney addresses for dozens of top earners in Spamit — at the time the most successful pharmaceutical spam affiliate program in the Russian hacking scene and one that employed most of the top Russian botmasters.
That document shows Fitis was one of Spamit’s most prolific recruiters, bringing more than 75 affiliates to the Spamit program over several years prior to its implosion in 2010 (and earning commissions on any future sales from all 75 affiliates).
The document also says Fitis got paid using a WebMoney account that was created when its owner presented a valid Russian passport for a Konstantin Evgenievich Fetisov, born Nov. 16, 1982 and residing in Moscow. Russian motor vehicle records show two different vehicles are registered to this person at the same Moscow address.
The most interesting domain name registered to the email address spampage@yahoo.com, fittingly enough, is fitis[.]ru, which DomainTools.com says was registered in 2005 to a Konstantin E. Fetisov from Moscow.
The Wayback Machine at archive.org has a handful of mostly blank pages indexed for fitis[.]ru in its early years, but for a brief period in 2007 it appears this website was inadvertently exposing all of its file directories to the Internet.
One of the exposed files — Glavmed.html — is a general invitation to the infamous Glavmed pharmacy affiliate program, a now-defunct scheme that paid tens of millions of dollars to affiliates who advertised online pill shops mainly by hacking websites and manipulating search engine results. Glavmed was operated by the same Russian cybercriminals who ran the Spamit program.
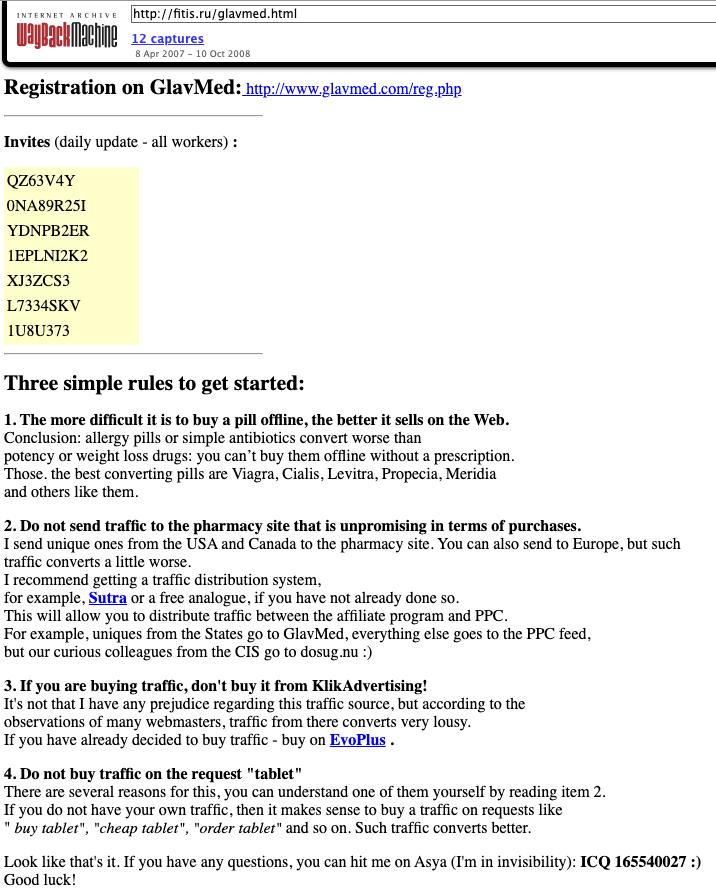
A Google translated ad circa 2007 recruiting for the pharmacy affiliate program Glavmed, which told interested applicants to contact the ICQ number used by Fitis, a.k.a. MegaTraffer. Image: Archive.org.
Archive.org shows the fitis[.]ru webpage with the Glavmed invitation was continuously updated with new invite codes. In their message to would-be Glavmed affiliates, the program administrator asked applicants to contact them at the ICQ number 165540027, which Intel 471 found was an instant messenger address previously used by Fitis on Exploit.
The exposed files in the archived version of fitis[.]ru include source code for malicious software, lists of compromised websites used for pharmacy spam, and a handful of what are apparently personal files and photos. Among the photos is a 2007 image labeled merely “fitis.jpg,” which shows a bespectacled, bearded young man with a ponytail standing next to what appears to be a newly-married couple at a wedding ceremony.
Mr. Fetisov did not respond to requests for comment.
As a veteran organizer of affiliate programs, Fitis did not waste much time building a new moneymaking collective after Spamit closed up shop. New York City-based cyber intelligence firm Flashpoint found that Megatraffer’s ICQ was the contact number for Himba[.]ru, a cost-per-acquisition (CPA) program launched in 2012 that paid handsomely for completed application forms tied to a variety of financial instruments, including consumer credit cards, insurance policies, and loans.
“Megatraffer’s entrenched presence on cybercrime forums strongly suggests that malicious means are used to source at least a portion of traffic delivered to HIMBA’s advertisers,” Flashpoint observed in a threat report on the actor.
Intel 471 finds that Himba was an active affiliate program until around May 2019, when it stopping paying its associates.

Fitis’s Himba affiliate program, circa February 2014. Image: Archive.org.
Flashpoint notes that in September 2015, Megatraffer posted a job ad on Exploit seeking experienced coders to work on browser plugins, installers and “loaders” — basically remote access trojans (RATs) that establish communication between the attacker and a compromised system.
“The actor specified that he is looking for full-time, onsite help either in his Moscow or Kiev locations,” Flashpoint wrote.
John Clifton Davies, a 60-year-old con man from the United Kingdom who fled the country in 2015 before being sentenced to 12 years in prison for fraud, has enjoyed a successful life abroad swindling technology startups by pretending to be a billionaire investor. Davies’ newest invention appears to be “CodesToYou,” which purports to be a “full cycle software development company” based in the U.K.

The scam artist John Bernard a.k.a. Alan John Mykailov (left) in a recent Zoom call, and a mugshot of John Clifton Davies from nearly a decade earlier.
Several articles here have delved into the history of John Bernard, the pseudonym used by a fake billionaire technology investor who tricked dozens of startups into giving him tens of millions of dollars.
John Bernard’s real name is John Clifton Davies, a convicted fraudster from the United Kingdom who is currently a fugitive from justice. For several years until reinventing himself again quite recently, Bernard pretended to be a billionaire Swiss investor who made his fortunes in the dot-com boom 20 years ago.
“The Private Office of John Bernard” let it be known to investment brokers that he had tens of millions of dollars to invest in tech startups, and he attracted a stream of new victims by offering extraordinarily generous finder’s fees to brokers who helped him secure new clients. But those brokers would eventually get stiffed because Bernard’s company would never consummate a deal.

John Bernard’s former website, where he pretended to be a billionaire tech investor.
Bernard would promise to invest millions in tech startups, and then insist that companies pay tens of thousands of dollars worth of due diligence fees up front. However, the due diligence company he insisted on using — another Swiss firm called The Inside Knowledge GmbH — also was secretly owned by Bernard, who would invariably pull out of the deal after receiving the due diligence money.
A variety of clues suggest Davies has recently adopted at least one other identity — Alan John Mykhailov — who is listed as chairman of a British concern called CodesToYou LTD, incorporated in May 2022. The CodesToYou website says the company employs talented coders in several countries, and that its programmers offer “your ultimate balance between speed, cost and quality.”
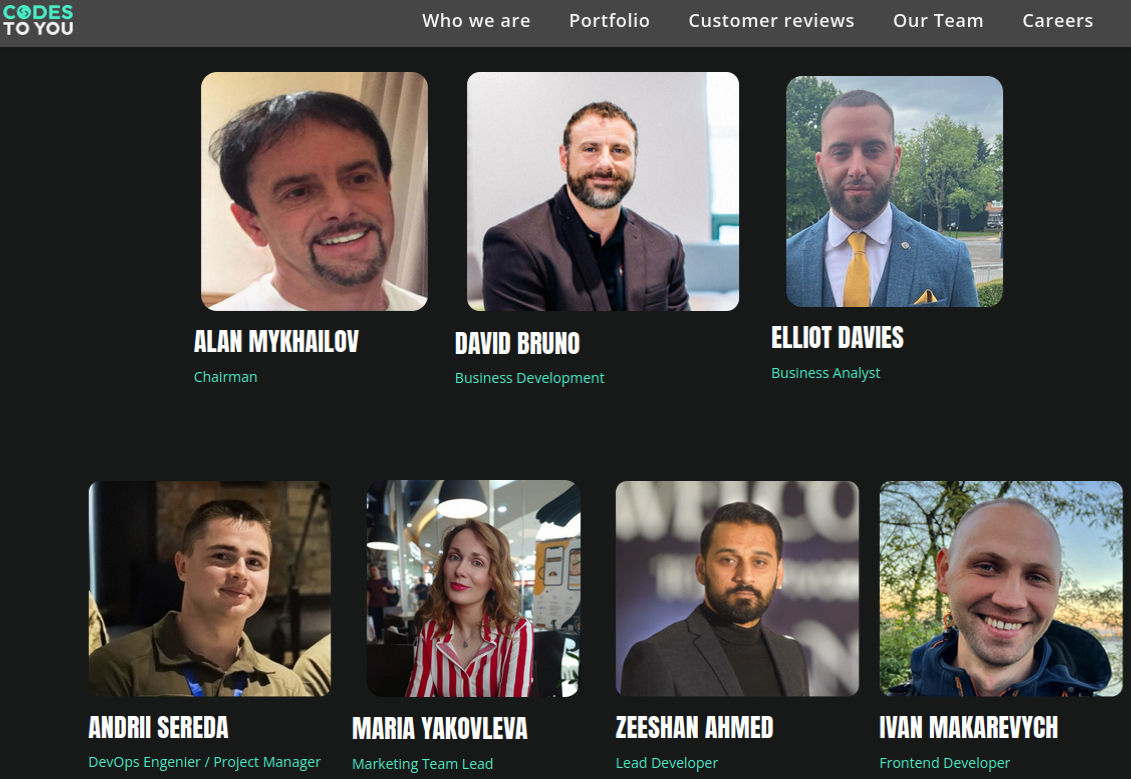
The team from CodesToYou.
In response to questions from KrebsOnSecurity, CodesToYou’s marketing manager — who gave their name only as “Zhena” — said the company was not affiliated with any John Bernard or John Clifton Davies, and maintained that CodesToYou is a legitimate enterprise.
But publicly available information about this company and its leadership suggests otherwise. Official incorporation documents from the U.K.’s Companies House represent that CodesToYou is headed by an Alan John Mykhailov, a British citizen born in March 1958.
Companies House says Mykhailov is an officer in three other companies, including one called Blackstone Corporate Alliance Ltd. According to the Swiss business tracking service business-monitor.ch, Blackstone Corporate Alliance Ltd. is currently the entity holding a decision-making role in John Bernard’s fake due diligence company — The Inside Knowledge GmbH — which is now in liquidation.
A screen shot of the stock photos and corporate-speak on John Bernard’s old website. Image: Archive.org
Also listed as a partner in Blackstone Corporate Alliance Limited is Igor Hubskyi (a.k.a. Igor Gubskyi), a Ukrainian man who was previously president of The Inside Knowledge GmbH.
The CodesToYou website says the company’s marketing team lead is Maria Yakovleva, and the photo of this employee matches the profile for the LinkedIn account name “Maria Y.” That same LinkedIn profile and photo previously listed Maria by a different first and last name — Mariya Kulikova; back then, Ms. Kulikova’s LinkedIn profile said she was an executive assistant in The Private Office of Mr. John Bernard.
Companies House lists Alan John Mykhailov as a current officer in two other companies, including Frisor Limited, and Ardelis Solutions Limited. A cached copy of the now-defunct Ardelis Solutions website says it was a private equity firm.
CodesToYou’s Maria also included Ardelis Solutions in the work history section of her LinkedIn resume. That is, until being contacted by this author on LinkedIn, after which Maria’s profile picture and any mention of Ardelis Solutions were deleted.
Listed as head of business development at CodesToYou is David Bruno, a Canadian man whose LinkedIn profile says he is founder of an organization called “World Privacy Resource.” As KrebsOnSecurity reported in 2020, Bruno was at the time promoting himself as the co-CEO of a company called SafeSwiss Secure Communication AG, and the founder of another tech startup called Secure Swiss Data.
Secure Swiss Data’s domain — secureswissdata.com — is a Swiss concern that sells encrypted email and data services. According to DomainTools.com, that website name was registered in 2015 by The Inside Knowledge GmbH. In February 2020, a press release announced that Secure Swiss Data was purchased in an “undisclosed multimillion buyout” by SafeSwiss Secure Communication AG.
A cached copy of the Ardelis Solutions website, which said it was a private equity firm and included similar stock images as John Bernard’s investment website.
When reached in 2020 and asked about his relationship to Mr. Bernard, Mr. Bruno said the two were business partners and that he couldn’t imagine that Mr. Bernard would be involved in anything improper. To this day Mr. Bruno is the only person I’ve spoken to who has had anything positive to say about Mr. Bernard.
Mr. Bruno did not respond to requests for comment this time around, but his LinkedIn profile no longer makes any mention of Secure Swiss Data or SafeSwiss — both companies he claimed to run for many years. Nor does it mention CodesToYou. However, Mr. Bruno’s former company SafeSwiss is listed as one of the six “portfolio” companies whose services are promoted on the CodesToYou website.
In mid-2021, Bruno announced he was running for public office in Ontario.
“The Kenora resident is no stranger to the government as he contributed to Canada’s new Digital Charter, Bill C-11, which is a new Cyber Security policy,” reported Drydennow.com, a news website that covers Northwestern Ontario. Drydennow says the next federal election is expected to be held on or before Oct. 16, 2023.
John Clifton Davies was convicted in 2015 of swindling businesses throughout the U.K. that were struggling financially and seeking to restructure their debt. For roughly six years, Davies ran a series of firms that pretended to offer insolvency services, but instead simply siphoned what little remaining money these companies had.
The very first entity mentioned in the technology portfolio advertised on the CodesToYou website is called “MySolve,” and it purports to offer a “multi-feature platform for insolvency practitioners.”
Mr. Davies’ fourth wife, Iryna Davies, is listed as a director of one of the insolvency consulting businesses in the U.K. that was part of John Davies’ 2015 fraud conviction. Prior to his trial for fraud, Davies served 16 months in jail before being cleared of murdering his third wife on their honeymoon in India: Colette Davies, 39, died after falling 80 feet from a viewing point at a steep gorge in the Himachal Pradesh region of India.
Mr. Davies was charged with murder and fraud after he attempted to collect GBP 132,000 in her life insurance payout, but British prosecutors ultimately conceded they did not have enough evidence to convict him.
The scams favored by Davies and his alter egos are smart because he never approaches investors directly; rather, investors are incentivized to put his portfolio in front of tech firms seeking financial backing. And all the best cons begin as an idea or possibility planted in the target’s mind.
It’s also a reliable scam because companies bilked by small-time investment schemes rarely pursue legal action, mainly because the legal fees involved can quickly surpass the losses. On top of that, many victims will likely be too ashamed to admit their duping. Victims who do press their case in court and win then face the daunting challenge of collecting damages from a slew of ephemeral shell corporations.
The latest Bernard victim to speak publicly — a Norwegian company hoping to build a fleet of environmentally friendly shipping vessels — is now embroiled in a lawsuit over a deal gone bad. As part of that scam, Bernard falsely claimed to have secured $100 million from six other wealthy investors, including the founder of Uber and the artist Abel Makkonen Tesfaye, better known as The Weeknd.
If you liked this story, check out my previous reporting on John Bernard/Davies:
Due Diligence That Money Can’t Buy
Who is Tech Investor John Bernard?
Promising Infusions of Cash, Fake Investor John Bernard Walked Away With $30 Million
Investment Scammer John Davies Reinvents Himself?
Fake Investor John Bernard Sinks Norwegian Green Shipping Dreams





















For many Aussies, identity theft was always something that happened to other people. People on TV, usually. But the recent spate of data breaches at Optus, Medibank and Energy Australia has made many of us pay far more attention than ever to one of the fastest growing crimes in our country.
According to the Department of Home Affairs, 1 in 4 Aussies will be the victim of identity theft over the course of their lives with an annual economic impact of more than $2 billion. And with the financial fallout from the recent data breaches only just starting to be counted, these statistics will no doubt increase dramatically next year.
Identity theft is when a cybercriminal gains access to your personal information to steal money or gain other benefits. Armed with your personal info, they can apply for real identity documents in your name but with another person’s photograph. This enables them to then apply for loans or benefits in your name, sign up for memberships or even apply for credit cards.
And it goes without saying that the financial and emotional fallout from identity theft can be huge. Since the Optus and Medibank hacking stories broke just a few months ago, there has been multiple stories of Aussie families who have had their identities stolen and who are in a world of pain. This Melbourne family who have had over $40,000 stolen from ATM withdrawals alone is just one example.
Your personal information is any piece of information or data that can confirm who you are or how to find you. It may be a single piece of information, or several pieces used together. It’s often referred to as personally identifiable information (PII). So, it includes your name, parents’ name, address, date of birth, phone numbers, email address, usernames/passwords or passphrases, bank account details, school or university attended, location check-ins even RSVPS for events.
Every time you register with a new shopping site or social media platform, you will be asked to share some personally identifiable information. However, what you share may be stolen or even misused – just think about the recent list of Australian companies who had their customers’ private information stolen by hackers. So that’s why you need to ensure you are only sharing your information with trusted online sites and take every possible step to protect your personal information online.
While there are no guarantees in life, there are steps you can take to ensure your online identity is as safe as possible. Here are my top 5 tips:
Multi-Factor Authentication (MFA) or 2 Factor Authentication (2FA) is a no-brainer because it makes a hacker’s life a lot harder. In short, it requires the user to provide two or more verification factors to gain access to an account or app. This might be a text, email or even a code generated by an authentication app. So, even if a hacker has your password and username, they still need that final piece of information before they can get their hands on your account!
Now this may take a bit of work to set up but using a unique and complex password on every account is one of the best things you can do to protect your online identity. And here’s the rationale – if you use the same password on all your accounts and your login details are stolen then hackers have access to all the accounts that are accessed with that password. Yikes!!! So, a unique password for each account is a great measure. I love using a password manager to make this process a little easier. Not only do they generate complex passwords, but they remember them too! All you need to do is remember your Master Password which needs to be extremely complex!!!
Updates are most commonly about addressing security weaknesses. And yes, I know they can be a pain but if you ignore them, you are essentially making it easier for hackers to find their way into your life via weak spots. And don’t forget to ensure your security software remains updated too!
I always recommend keeping a backup of all your important info in case something goes wrong. This should include all your photos, key documents and all your personally identifiable information. A hard drive works well but saving to the cloud is also a good option. I once dropped a hard drive and lost treasured family photos, so the cloud is my personal preference.
We all know knowledge is power so investing in top notch security and identity monitoring software will help keep you ahead of threats. McAfee+, McAfee’s new all in one privacy, identity and device protection solution is a fantastic way for Aussies to protect themselves online. It features identity monitoring and a password manager but also an unlimited VPN, a file shredder, protection score and parental controls. And the Rolls Royce version called McAfee+ Advanced, also offers subscribers additional identity protections including access to licensed restoration experts who can help you repair your identity and credit, in case you’re affected by a data breach. It also gives subscribers access to lost wallet protection which help you cancel and replace your ID, credit cards if they are lost or stolen.
Public, unsecured Wi-Fi can make life so much easier when you’re out and about but it’s also a tried and tested way for scammers to access your personal information. Unsecured Wi-Fi is free Wi-Fi that is available in public places such as libraries, cafes, or shopping centres. So, instead of using Wi-Fi, just use the data in your phone plan. Or alternatively invest in a Virtual Private Network (VPN) that cleverly encrypts everything you share on your device.
About 2 months ago, I embarked on a project to clean up my online life. I’m working through the list of sites I have accounts with and am closing those I no longer use, I’m also doing a huge password audit to ensure they are all unique to each site and are super complex, thanks to my password manager. Now, I’m not quite done yet, but things are in better shape than they were. Why not consider doing the same? With the holiday season fast approaching, why not dedicate a little of your poolside time to practicing a little cyber hygiene.
Till next time, keep those identities safe!
Alex
The post The Best Way To Protect Your Online Identity appeared first on McAfee Blog.
Millions of people likely just received an email or snail mail notice saying they’re eligible to claim a class action payment in connection with the 2017 megabreach at consumer credit bureau Equifax. Given the high volume of reader inquiries about this, it seemed worth pointing out that while this particular offer is legit (if paltry), scammers are likely to soon capitalize on public attention to the settlement money.
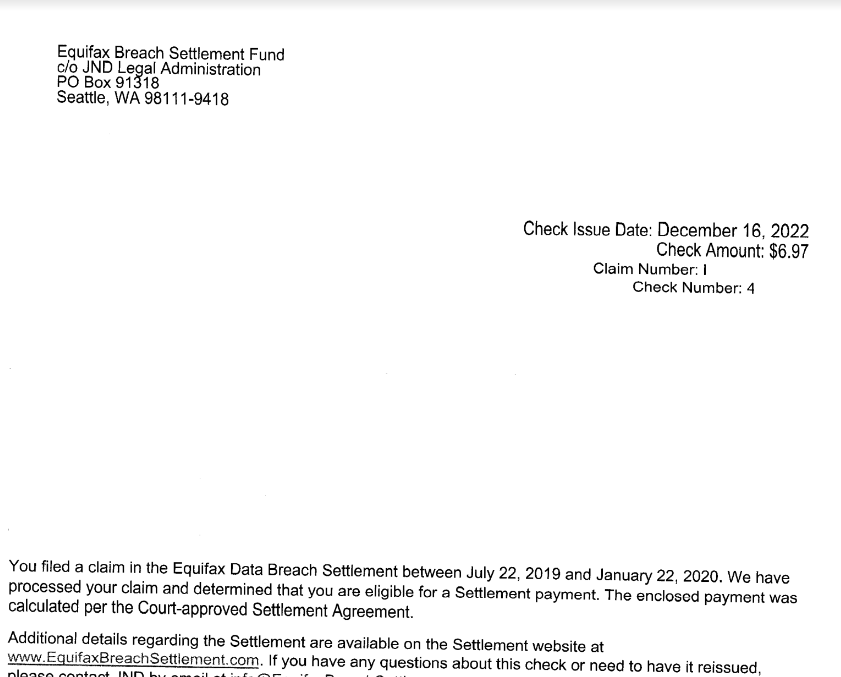
One reader’s copy of their Equifax Breach Settlement letter. They received a check for $6.97.
In 2017, Equifax disclosed a massive, extended data breach that led to the theft of Social Security Numbers, dates of birth, addresses and other personal information on nearly 150 million people. Following a public breach response perhaps best described as a giant dumpster fire, the big-three consumer credit reporting bureau was quickly hit with nearly two dozen class-action lawsuits.
In exchange for resolving all outstanding class action claims against it, Equifax in 2019 agreed to a settlement that includes up to $425 million to help people affected by the breach.
Affected consumers were eligible to apply for at least three years of credit monitoring via all three major bureaus simultaneously, including Equifax, Experian and TransUnion. Or, if you didn’t want to take advantage of the credit monitoring offers, you could opt for a cash payment of up to $125.
The settlement also offered reimbursement for the time you may have spent remedying identity theft or misuse of your personal information caused by the breach, or purchasing credit monitoring or credit reports. This was capped at 20 total hours at $25 per hour ($500), with total cash reimbursement payments not to exceed $20,000 per consumer.
Those who did file a claim probably started receiving emails or other communications earlier this year from the Equifax Breach Settlement Fund, which has been messaging class participants about methods of collecting their payments.
How much each recipient receives appears to vary quite a bit, but probably most people will have earned a payment on the smaller end of that $125 scale — like less than $10. Those who received higher amounts likely spent more time documenting actual losses and/or explaining how the breach affected them personally.
So far this week, KrebsOnSecurity has received at least 20 messages from readers seeking more information about these notices. Some readers shared copies of letters they got in the mail along with a paper check from the Equifax Breach Settlement Fund (see screenshot above).
Others said they got emails from the Equifax Breach Settlement domain that looked like an animated greeting card offering instructions on how to redeem a virtual prepaid card.
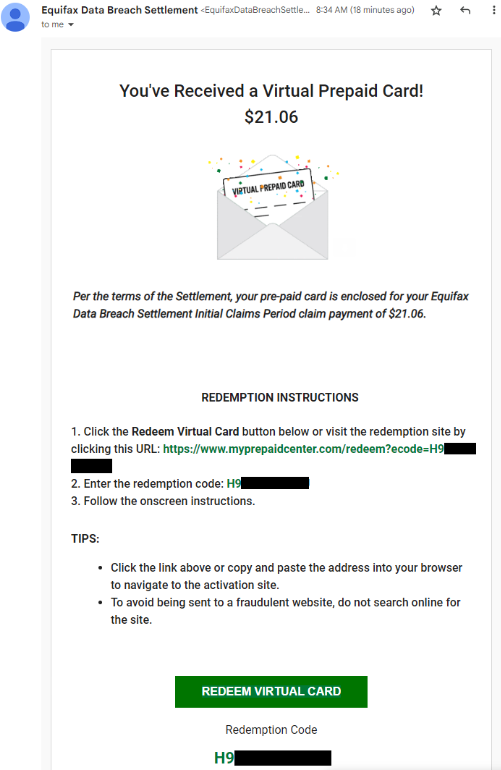
If you received one of these settlement emails and are wary about clicking the included links (good for you, by the way), copy the redemption code and paste it into the search box at myprepaidcenter.com/redeem. Successfully completing the card application requires accepting a prepaid MasterCard agreement (PDF).
The website for the settlement — equifaxbreachsettlement.com — also includes a lookup tool that lets visitors check whether they were affected by the breach; it requires your last name and the last six digits of your Social Security Number.
But be aware that phishers and other scammers are likely to take advantage of increased public awareness of the payouts to snooker people. Tim Helming, security evangelist at DomainTools.com, today flagged several new domains that mimic the name of the real Equifax Breach Settlement website and do not appear to be defensively registered by Equifax, including equifaxbreechsettlement[.]com, equifaxbreachsettlementbreach[.]com, and equifaxsettlements[.]co.
In February 2020, the U.S. Justice Department indicted four Chinese officers of the People’s Liberation Army (PLA) for perpetrating the 2017 Equifax hack. DOJ officials said the four men were responsible for carrying out the largest theft of sensitive personal information by state-sponsored hackers ever recorded.
Equifax surpassed Wall Street’s expectations in its most recent quarterly earnings: The company reported revenues of $1.24 billion for the quarter ending September 2022.
Of course, most of those earnings come from Equifax’s continued legal ability to buy and sell eye-popping amounts of financial and personal data on U.S. consumers. As one of the three major credit bureaus, Equifax collects and packages information about your credit, salary, and employment history. It tracks how many credit cards you have, how much money you owe, and how you pay your bills. Each company creates a credit report about you, and then sells this report to businesses who are deciding whether to give you credit.
Americans currently have no legal right to opt out of this data collection and trade. But you can and also should freeze your credit, which by the way can make your credit profile less profitable for companies like Equifax — because they make money every time some potential creditor wants a peek inside your financial life. Also, it’s probably a good idea to freeze the credit of your children and/or dependents as well. It’s free on both counts.

Our How I Got Here series spotlights the stories of McAfee team members who have successfully grown their careers. Read more about Brenda’s McAfee’s journey, what a day in the McAfee sales team is like, and what her superpower is.
When I started my professional career, I was in technology but one of the few women there at the time. A colleague encouraged me to join the Canadian Information Processing Society as a volunteer. I was just exploring, but it turned out to be a career-builder.
After some time, I joined the Society’s board – my first board appointment ever. Suddenly I was in a leadership position and people were looking to me to make decisions, especially the CIOs and other executives who were on the board with me. I embraced the opportunity, and the expectations they had of me shaped the professional I am today.
I knew about McAfee from some people who had already worked there and was intrigued by the premise of protecting families online. This was a chance to do what I loved at a bigger scale. And after my interviews, I knew it was the right move!
I am part of the North American Sales team that acquires customers through partnerships with big box retailers throughout North America. Together with our partners, we help customers see the value of McAfee.
In sales, you are constantly interacting with people. Each day is different: one moment I’m planning with partners on how to jointly protect their customers and families online. The next, I’m working will McAfee colleagues on sales strategies and business planning. My days are a steady mix of conference and video calls to collaborate, plan, and connect.
Every day, I get to work with so many great people. On top of that, we’re using our powers for good! Everyone, partners and colleagues alike, are all inspired by our ultimate mission: to protect people and their families. I keep going back to the people – but what a fabulous community of colleagues and partners we work with globally! I also love the birds-eye view I get across all McAfee’s business units. In order to make good on the promises we make to our partners, I collaborate every day with so many key stakeholders across our entire business.
And now that my children are adults, I’m finding more time for exercise, like Peloton or F45 cross fit. I’m also taking piano classes, and I just wrapped a one-night-a-week downhill skiing program with one of my daughters!
McAfee lets you be flexible in getting your job done and taking on other projects. I am so grateful that I can help others through activities such as WISE (the McAfee Women In Security community). It’s important to do something outside of your day job because it makes your world bigger.
I work with some really great women on the WISE board. We are so supportive of each other. Board work is outside of our normal day jobs and sometimes we want to do things we haven’t done before. We put our heads together to figure it out quickly, divide up the work, and get it done!
I’ve also been very fortunate to be able to meet with many customers, partners, and colleagues face-to-face. This has allowed me to learn and grow, not only in my career but also in the Diversity and Inclusion space. The more you know about someone, the better partner and ally you can be.
Over my career, I’ve built up my superpower: building relationships. I choose to be positive and empathetic, which helps me develop strong working relationships. I also keep in touch with people I’ve worked with over the years, whether they are peers, customers, or younger professionals I’ve mentored.
The post Know Your Superpower: Brenda’s McAfee Journey appeared first on McAfee Blog.

This time of year, the air not only gets chillier but a bit cheerier for everyone … including online scammers. Holiday scams are a quick way to make a buck, and cybercriminals employ several holiday-themed schemes to weasel money and personally identifiable information (PII) from gift givers.
Here are three common holiday scams to watch out for this year, plus a few tips to help you stay safe online.
Gift cards are a standby present for the people on your list who are difficult to buy for or for people you don’t know too well but want to get them a small something. Whether the gift card is worth $5 or $500, an online scammer can steal the entire value through two techniques: a brute force attack or phishing. Known as gift card cracking, cybercriminals can take wild guesses at gift card codes and cash in the value for themselves by methodically guessing strings of numbers and letters and crossing their fingers for a match. Cybercriminals will also employ phishing emails, texts or social media direct messages to trick people into divulging gift card information.
To avoid gift card cracking, encourage gift receivers to redeem their gift card quickly to shorten the amount of time a scammer has to guess the code correctly. Or, you could opt for a paper gift certificate from a small business that doesn’t require online redeeming at all. To avoid gift card phishing scams, do not engage with any type of correspondence that claims they can double the value of your gift card or claims that there’s a problem with it. Be instantly on alert if anyone asks for the activation code. If the gift card-issuing business really needs to replace your purchase, they’ll issue you a new code. They’ll never ask for your existing one.
Are you a procrastinator? Watch out for last-minute shopping scams that are targeted at people who leave their gift buying until deep in December. As with anything else, if it’s too good to be true, it probably is. Shopping scams often take the form of phishing emails where criminals impersonate a well-known merchant or shipping company.
While sales often have a quick timeline, don’t let that short timeline pressure you into making an impulsive decision. Phishers rely on people’s excitement or inattention to trick them into giving up their credit card or banking information. Phishing emails, when you take the time to inspect them, are usually easy to spot. The logos are often blurry, there are often typos and grammar mistakes, and the tone of the message will seem “off.” Either it will sound very formal and impersonalized or it will sound very informal and seem pushy.
To protect your finances during the holiday season, consider putting a lock on your credit. This is easy to do with McAfee credit lock. You can still use your credit card and shop as you normally would. A credit lock is useful because, in case a criminal gets ahold of your PII, they won’t be able to open lines of credit in your name. This protects your credit score, which is essential to keep in good standing if you hope to buy a house or take out a loan anytime soon.
Just because a “company” has an ad on Facebook or Instagram doesn’t mean that it’s a legitimate establishment. Before buying from an online store you’ve never heard of, do some background research on it and read customer reviews to make sure that it’s real and will deliver you a quality product.
Take note of the online store’s URL before entering it. (You can preview the link by hovering over it with your cursor.) If the URL is a string of letters and numbers, it could be a malware site in disguise. One way to alert you to suspicious sites is McAfee Web Protection. Web Protection color codes links to identify potential malware and phishing sites and alert you to steer clear.
Your mind is already drawn in a bunch of different directions this holiday season (cooking, traveling, shopping, wrapping, tidying) so give yourself a respite from worrying about the safety of your identity and finances. McAfee+ Ultimate includes a VPN, Web Protection, credit lock, antivirus and more to cover all your bases to keep your devices and your PII safe.
The post ‘Tis the Season for Holiday Scams appeared first on McAfee Blog.

Have you ever been browsing online and clicked a link or search result that took you to a site that triggers a “your connection is not private” or “your connection is not secure” error code? If you’re not too interested in that particular result, you may simply move on to another result option. But if you’re tempted to visit the site anyway, you should be sure you understand what the warning means, what the risks are, and how to bypass the error if you need to.
A “your connection is not private” error means that your browser cannot determine with certainty that a website has safe encryption protocols in place to protect your device and data. You can bump into this error on any device connected to the internet — computer, smartphone, or tablet.
So, what exactly is going on when you see the “this connection is not private” error?
For starters, it’s important to know that seeing the error is just a warning, and it does not mean any of your private information is compromised. A “your connection is not private” error means the website you were trying to visit does not have an up-to-date SSL (secure sockets layer) security certificate.
Website owners must maintain the licensing regularly to ensure the site encryption capabilities are up to date. If the website’s SSL certificate is outdated, it means the site owners have not kept their encryption licensing current, but it doesn’t necessarily mean they are up to no good. Even major websites like LinkedIn have had momentary lapses that would throw the error. LinkedIn mistakenly let their subdomain SSL certificates lapse.
In late 2021, a significant provider of SSL certificates, Let’s Encrypt, went out of business. When their root domain officially lapsed, it created issues for many domain names and SSL certificates owned by legitimate companies. The privacy error created problems for unwitting businesses, as many of their website visitors were rightfully concerned about site security.
While it does not always mean a website is unsafe to browse, it should not be ignored. A secure internet connection is critical to protecting yourself online. Many nefarious websites are dangerous to visit, and this SSL certificate error will protect you from walking into them unaware.
SSL certification standards have helped make the web a safer place to transact. It helps ensure online activities like paying bills online, ordering products, connecting to online banking, or keeping your private email accounts safe and secure. Online security continues to improve with a new Transport Layer Security (TLS) standard, which promises to be the successor protocol to SSL.
So be careful whenever visiting sites that trigger the “connection is not private” error, as those sites can potentially make your personal data less secure and make your devices vulnerable to viruses and malware.
Note: The “your connection is not private” error is Google Chrome‘s phrasing. Microsoft Edge or Mozilla Firefox users will instead see a “your connection is not secure” error as the warning message.
If you feel confident that a website or page is safe, despite the warning from your web browser, there are a few things you can do to troubleshoot the error.
Remember, you are taking your chances anytime you ignore an error. As we mentioned, you could leave yourself vulnerable to hackers after your passwords, personal information, and other risks.
Your data and private information are valuable to hackers, so they will continue to find new ways to try and procure it. Here are some ways to protect yourself and your data when browsing online.
As we continue to do more critical business online, we must also do our best to address the risks of the internet’s many conveniences.
A comprehensive cybersecurity tool like McAfee+ Ultimate can help protect you from online scams, identity theft, and phishing attempts, and ensure you always have a secure connection. McAfee helps keep your sensitive information out of the hands of hackers and can help you keep your digital data footprints lighter with personal data cleanup.
With McAfee’s experts on your side, you can enjoy everything the web offers with the confidence of total protection.
The post “This Connection Is Not Private” – What it Means and How to Protect Your Privacy appeared first on McAfee Blog.

Authored by: Christy Crimmins and Oliver Devane
Football (or Soccer as we call it in the U.S.) is the most popular sport in the world, with over 3.5 billion fans across the globe. On November 20th, the men’s World Cup kicks off (pun intended) in Qatar. This event, a tournament played by 32 national teams every four years, determines the sport’s world champion. It will also be one of the most-watched sporting events of at least the last four years (since the previous World Cup).
An event with this level of popularity and interest also attracts fraudsters and cyber criminals looking to capitalize on fans’ excitement. Here’s how to spot these scams and stay penalty-free during this year’s tournament.
Phishing is a tool that cybercriminals have used for years now. Most of us are familiar with the telltale signs—misspelled words, poor grammar, and a sender email whose email address makes no sense or whose phone number is unknown. But excitement and anticipation can cloud our judgment. What football fan wouldn’t be tempted to win a free trip to see their home team participate in the ultimate tournament? Cybercriminals are betting that this excitement will cloud fans’ judgment, leading them to click on nefarious links that ultimately download malware or steal personal information.
It’s important to realize that these messages can come via a variety of channels, including email, text messages, (also known as smishing) and other messaging channels like WhatsApp and Telegram. No matter what the source is, it’s essential to remain vigilant and pause to think before clicking links or giving out personal or banking information.
For more information on phishing and how to spot a phisher, see McAfee’s “What is Phishing?” blog.
According to ActionFraud, the UK’s national reporting center for fraud and cybercrime, thousands of people were victims of ticket fraud in 2019—and that’s just in the UK. Ticket fraud is when someone advertises tickets for sale, usually through a website or message board, collects the payment and then disappears, without the buyer ever receiving the ticket.
The World Cup is a prime (and lucrative) target for this type of scam, with fans willing to pay thousands of dollars to see their teams compete. Chances are most people have their tickets firmly in hand (or digital wallet) by now, but if you’re planning to try a last-minute trip, beware of this scam and make sure that you’re using a legitimate, reputable ticket broker. To be perfectly safe, stick with well-known ticket brokers and those who offer consumer protection. Also beware of sites that don’t accept debit or credit cards and only accept payment in the form of bitcoin or wire transfers such as the one on the fake ticket site below:
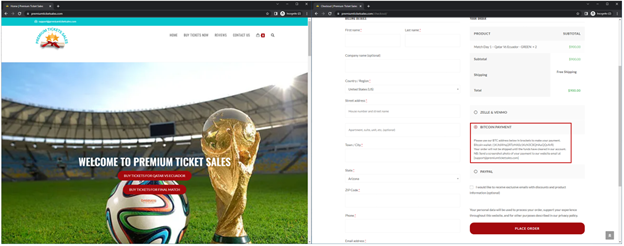
The red box on the right image shows that the ticket site accepts payment via Bitcoin.
Other red flags to look out for are websites that ask you to contact them to make payment and the only contact information is via WhatsApp.
Let’s be realistic—most of us are going to have to settle for watching the World Cup from the comfort of our own home, or the pub down the street. If you’re watching the tournament online, be sure that you’re using a legitimate streaming service. A quick Google of “FIFA World Cup 2022 Official Streaming” along with your country should get you the information you need to safely watch the event through official channels. The FIFA site itself is also a good source of information.
Illegal streaming sites usually contain deceptive ads and malware which can cause harm to your device.
In countries or regions where sports betting is legal, the 2022 World Cup is expected to drive an increase in activity. There’s no shortage of things to bet on, from a simple win/loss to the exact minute a goal will be scored by a particular player. Everything is subject to wager.
As with our previous examples, this increase in legitimate gambling brings with it an increase in deceptive activity. Online betting scams often start when users are directed to or search for gambling site and end up on a fraudulent one. After placing their bets and winning, users realize that while they may have “won” money, they are unable to withdraw it and are even sometimes asked to deposit even more money to make winnings available, and even then, they still won’t be. By the end of this process, the bettor has lost all their initial money (and then some, potentially) as well as any personal information they shared on the site.
Like other scams, users should be wary of sites that look hastily put together or are riddled with errors. Your best bet (yes, again, pun intended) is to look for an established online service that is approved by your government or region’s gaming commission. Finally, reading the fine print on incentives or bonuses is always a good idea. If something sounds too good to be true, it’s best to double-check.
For more on how you can bet online safely, and for details on how legalized online betting works in the U.S., check out our blog on the topic.
Using a free public Wi-Fi connection is risky. User data on these networks is unprotected, which makes it vulnerable to cyber criminals. Whether you’re traveling to Qatar for a match or watching the them with friends at your favorite pub, if you’re connecting to a public Wi-Fi connection, make sure you use a trusted VPN connection.
For more information on scams, visit our scam education page. Hopefully, with these tips, you’ll be able to enjoy and participate in some of the World Cup festivities, after all, fun is the goal!
The post Don’t Get Caught Offsides with These World Cup Scams appeared first on McAfee Blog.

Vernon has been our Manager of Technical Accounting for more than two years, but that doesn’t mean he’s busy with spreadsheets and numbers all day.
It’s been an amazing ride so far. My team touches on several areas of responsibility, including financial period closing, financial reporting, and accounting for complex transactions.
The most rewarding part of my role is definitely the variety and complexity – they really go hand-in-hand and I enjoy asking questions and figuring out the solutions, even when there is not always a textbook answer. I enjoy the challenge of working collectively with a team to find solutions by applying research and experience to a set of facts.
It’s also rewarding to be able to collaborate with auditors and other stakeholders who would be interested in the results.
My favorite thing about working at McAfee is the team. We have an amazing team. It’s full of really smart people. I’ve seen some companies try and find the best talent they can, but McAfee has just taken that to a whole different level. Everyone in their respective areas is really tuned in to the broader effort and we work well together. At McAfee, we enjoy both a high level of talent and collaborative effort. You don’t often find both in the same place.
I really believe that each person brings certain strengths to the table, and they should be able to exercise those strengths to develop and expand their capabilities. Once those natural roles are established, it’s best to trust them to determine how best to perform in their roles and collaborate with the team in achieving results that add value to the broader group.
First, expect the unexpected – consider each new experience an opportunity for personal growth.
Secondly, get involved in projects. If you have the opportunity to do something different or work with a cross-functional team, do it. It builds your own skill base, which opens the door for greater future opportunities and you get to meet people outside of your own department and develop relationships that may prove valuable over time.
The post For some, accounting is more than just spreadsheets! Vernon’s McAfee Journey appeared first on McAfee Blog.

*TW: Mentions Suicide
Our passion for protecting people doesn’t stop with online safety. We deeply care for our people, their families and friends, and our communities.
To recognize World Suicide Prevention on Sept. 10 and help normalize and encourage conversations about mental health year-round, we recently hosted a discussion with McAfee colleagues and suicide prevention activist and owner of The Jordan Legacy, Steve Phillip. During this session Steve discussed his own personal lived experience of suicide and what he’s learned since establishing The Jordan Legacy when it comes to creating an open and safe environment for all.
“I established The Jordan Legacy in 2020, following the suicide of my 34-year-old son, Jordan, in December 2019. It’s a registered not-for-profit Community Interest Company (CIC), whose mission is to raise awareness about suicide, open the conversation, help remove the stigma surrounding this topic and importantly, engage with communities and workplaces to discuss and identify practical solutions which will help prevent suicide.”
“#WSPD is important in highlighting the biggest killer of men and women under the age of 35. According to the W.H.O, we lose 700,000 people globally to suicide every year – that’s one person every 45 seconds. On average, each suicide will impact 135 other people. This means that more than 95 million people are impacted by suicide annually! And while #WSPD is an important day to highlight, it’s fundamental that we recognize that suicide awareness needs to happen 365 days a year.”
“There are several reasons why stigmas surrounding mental health and suicide exist. Generally, it’s due to a lack of understanding and people making assumptions – such as those with a mental health illness could be dangerous, unreliable or unemployable. Cultural backgrounds also play a part in creating stigma – certain cultures see mental illness and suicide as a taboo subject. The language used around mental health and suicide can also create stigma. In the UK, the act of attempting suicide was decriminalized in 1961 and yet the term ‘committed suicide’ is still frequently used, in the same way as commit murder or commit assault.”
“It’s important to ask people how they are with a genuine intent to listen to and understand their reply. Most people who are struggling with their mental health don’t necessarily want you to fix them, but they do want to feel that they’re being listened to. Ask open-ended questions, such as ‘tell me how are you really feeling?’, ‘explain to me how this is impacting on you?’, ‘describe to me, how this is making you feel?”
“We need to become a kinder and more compassionate society by recognizing that everyone can, at some point in their lives, struggle with poor mental health. Understanding this, would hopefully cause people to be less frustrated with others who don’t behave as they expect they might. We also need to check-in with family members, friends and colleagues more frequently and ask them ‘how are you really doing?”
“I am one of those individuals who probably works too hard and for too long! However, road cycling is a big escape for me and getting out in the fresh air in the countryside is a huge help. As is my part-time hobby of playing the drums – you can lose a lot of pent-up stress whilst playing along to Nirvana!! It’s so important that you make sure to look after yourself. So, my advice is to find out what works for you – whether that’s going for a walk, talking to a friend, speaking to a counsellor, joining a local group or seeing what resources are available to you through your company’s EAP. And remember most importantly to be kind to yourself.”
If you or someone you know is struggling, please call or text 988 to get support. And remember, you are not alone.
Together we can prevent suicide 
The post #WSPD Creating hope through action with The Jordan Legacy appeared first on McAfee Blog.

“Congratulations, you’re a winner!”
“Did you know this public figure is trying to make your life worse? Click here for what they don’t want you to know.”
“Save thousands today with just one click!”
Spam and bot accounts on social media are everywhere. You’ve likely encountered messages like these that attempt to get you to click on links or to stir your emotions in a frenzy. While bot accounts are usually more of an annoyance than anything, when they’re allowed to run rampant, they can quickly become dangerous to your personally identifiable information (PII) and create an emotionally charged mob mentality.
Here’s what you should know about bot accounts, including how to steer clear of menacing ones, plus a reminder to watch what you share on (and with) social media sites.
Bot accounts are software-automated accounts that try to blend in and act like a real user. They post updates and follow other users, though there isn’t a real person behind the account. A spam account is a type of bot account that attempts to gain financially from its automated posts. Everyday people should be wary of social media bot accounts because they can be used to disseminate false information or phishing scams.
One whistleblower of a social media giant recently divulged that the platform isn’t prioritizing deactivating bot accounts.1 This apathy sparks concerns about the company’s commitment to the security of its users. In the whistleblower’s same report, he stated that the social media site isn’t taking the necessary steps to protect itself from potential inside threats and it had fallen victim to at least 20 breaches in 2020 without reporting the incidents to the proper authorities.
Some bot accounts aren’t malicious (merely an annoying tactic by companies to spread the word about their business), but it’s best to give all of them a wide berth and never click on any links in their posts. Those links could direct to unsecured outside sites laden with malware or drop you in the middle of a phishing scheme.
You can often spot a malicious bot account by the tone of its messages. They’ll often try to inspire intense emotions, such as excitement, sadness, or rage, and attempt to get users to act or share the post. Do not engage with them, not even to argue their points. When you engage or share these posts with your network, it spreads false information and could dangerously manipulate public opinion.2
Here are a few ways you can take your cybersecurity into your own hands when you can’t be sure that social media sites are looking out for the safety of users’ information:
You can’t trust every company to look out for the safety of your personal information, but one organization you can trust is McAfee. McAfee Total Protection is a comprehensive identity and privacy protection solution for your digital life. Great social media habits go a long way toward keeping you safe online, and you can rest assured knowing that McAfee can fill in the gaps. McAfee Total Protection offers antivirus, identity monitoring, and security freeze in the case your information is leaked in a breach or a bot account gets ahold of key details.
Keep on sharing your life’s milestones with your closest friends and family online. The next time you update your status, flag any suspicious accounts you come across, so everyone can enjoy social media confidently!
1NBC News, “Twitter whistleblower alleges major security issues”
2Journal of Information Technology & Politics, “Harass, mislead & polarize: An analysis of Twitter political bots’ tactics in targeting the immigration debate before the 2018 U.S. midterm election”
The post Here’s How to Steer Clear of Bot Accounts on Social Media appeared first on McAfee Blog.

In this career-journey series, Internal Audit Manager Chris shares his recent journey joining the McAfee finance team and why he is always learning something new in his role.
I’m an Internal Audit Manager. Essentially, I work with my McAfee colleagues to understand the processes we follow and run tests to confirm everything is happening as it should.
Sometimes people find audits intimidating, but I do my best to reassure people that there are no hidden tricks and I respect their time. We’re just making sure things are going according to plan and we’re fulfilling our responsibilities.
In a typical day, I have three priorities: Dad, Work, Gym.
I’m normally up at 6 a.m. to cook breakfast for my son and myself, and then drop him off at school. His favorite is bacon and eggs! Since I work with people around the world, I catch up on emails and then review the day’s work and catch up with my team. From there, most of my day is spent in meetings with McAfee colleagues or external auditors.
Somewhere in the day I get in a one-hour workout. It’s tough to do sometimes, but I’d say I get to the gym 90% of the time. It’s a great reset for me: a time where I can focus on me and putting my body to the test.
And, of course, I pick up my son from school and have Dad Time! That’s really my day in repeat. It seems like the same thing but feels different every day. I’m always meeting new people and puzzling through different problems. Every day is a fresh challenge.
After interviewing with my future co-workers, I was excited to join the company. I thought, “Oh, this company is fun!” The culture seemed to be a place where not only do you get to come for work, but also have sense of community within it.
Also, it was a chance to work for a great boss. I knew she was a great boss because I worked for her before. She gives you the vision, then gives you the freedom to explore and get the work done. You really get to own your work. I appreciate that.
At McAfee, employees are a top priority. You’re not just a robot who has to work-work-work. It’s okay to have fun and take 10 minutes out to see how others are doing.
I like the way the company comes together to have contests and other fun activities. In Finance, we recently had a scavenger hunt with 70 people. It was great seeing the faces of people you’ve only talked to on the phone.
Another way we engage each other is with a recognition program called Bravo! You can write a letter to someone saying hey, I appreciate you. That makes you feel more valued as an employee.
I also like the quarterly updates we get from leaders. At other companies, I’ve seen that done once a year. It’s nice to hear from the CEO every quarter about what’s going on in the organization.
There are two parts that make my role so rewarding. The first is I enjoy interacting with people and have a passion for learning. In this job, you hear so many cool stories, and I’m exposed to so many different areas and processes in across the business. There’s always something new to learn. It makes every day different.
Secondly, at McAfee I’m part of the McAfee African Heritage Community (MAHC). We get together and talk about things we want to share with other Community members and the rest of McAfee. I’ve met people I never would run into otherwise. That’s important to me as someone who’s fairly new to McAfee plus having worked remote all this time. It’s very cool to be part of a company that supports having communities.
Honestly, my job is always outside my comfort zone. There’s always a new problem to be solved. But I like that. The way I see it, if you’re comfortable, you aren’t growing. You need to do something you haven’t done before to move to the next level.
As an auditor, I’m always helping others understand the audit process and how to provide solid information, so the audit goes well.
One of the most helpful skills I have developed during my career is communication. I need to establish a rapport quickly in my work so we can work well together. Everybody is different, right? Some are more direct, some are more indirect, and some people are more casual than others. You always need to adjust when you meet people. Good communication skills help prevent misunderstandings, which is especially important in a global company like McAfee with so many different cultures.

Embrace change! Change is just another way to grow, learn, and realize potential you didn’t know you had. Look at it as an opportunity. Raise your hand up when problems arise and take on that tough problem. The person who fixes the problem is the person everyone remembers.

The post Embrace change! Chris’s McAfee Journey appeared first on McAfee Blog.
Chief Information Officers and other technology decision makers continuously seek new and better ways to evaluate and manage their investments in innovation – especially the technologies that may create consequential decisions that impact human rights. As Artificial Intelligence (AI) becomes more prominent in vendor offerings, there is an increasing need to identify, manage, and mitigate the unique risks that AI-based technologies may bring.
Cisco is committed to maintaining a responsible, fair, and reflective approach to the governance, implementation, and use of AI technologies in our solutions. The Cisco Responsible AI initiative maximizes the potential benefits of AI while mitigating bias or inappropriate use of these technologies.
Gartner® Research recently published “Innovation Insight for Bias Detection/Mitigation, Explainable AI and Interpretable AI,” offering guidance on the best ways to incorporate AI-based solutions that facilitates “understanding, trust and performance accountability required by stakeholders.” This newsletter describes Cisco’s approach to Responsible AI governance and features this Gartner report.
At Cisco, we are committed to managing AI development in a way that augments our focus on security, privacy, and human rights. The Cisco Responsible AI initiative and framework governs the application of responsible AI controls in our product development lifecycle, how we manage incidents that arise, engage externally, and its use across Cisco’s solutions, services, and enterprise operations.
Our Responsible AI framework comprises:
We base our Responsible AI initiative on principles consistent with Cisco’s operating practices and directly applicable to the governance of AI innovation. These principles—Transparency, Fairness, Accountability, Privacy, Security, and Reliability—are used to upskill our development teams to map to controls in the Cisco Secure Development Lifecycle and embed Security by Design, Privacy by Design, and Human Rights by Design in our solutions. And our principle-based approach empowers customers to take part in a continuous feedback cycle that informs our development process.
We strive to meet the highest standards of these principles when developing, deploying, and operating AI-based solutions to respect human rights, encourage innovation, and serve Cisco’s purpose to power an inclusive future for all.
Check out Gartner recommendations for integrating AI into an organization’s data systems in this Newsletter and learn more about Cisco’s approach to Responsible Innovation by reading our introduction “Transparency Is Key: Introducing Cisco Responsible AI.”
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Earlier this month, the administrator of the cybercrime forum Breached received a cease-and-desist letter from a cybersecurity firm. The missive alleged that an auction on the site for data stolen from 10 million customers of Mexico’s second-largest bank was fake news and harming the bank’s reputation. The administrator responded to this empty threat by purchasing the stolen banking data and leaking it on the forum for everyone to download.
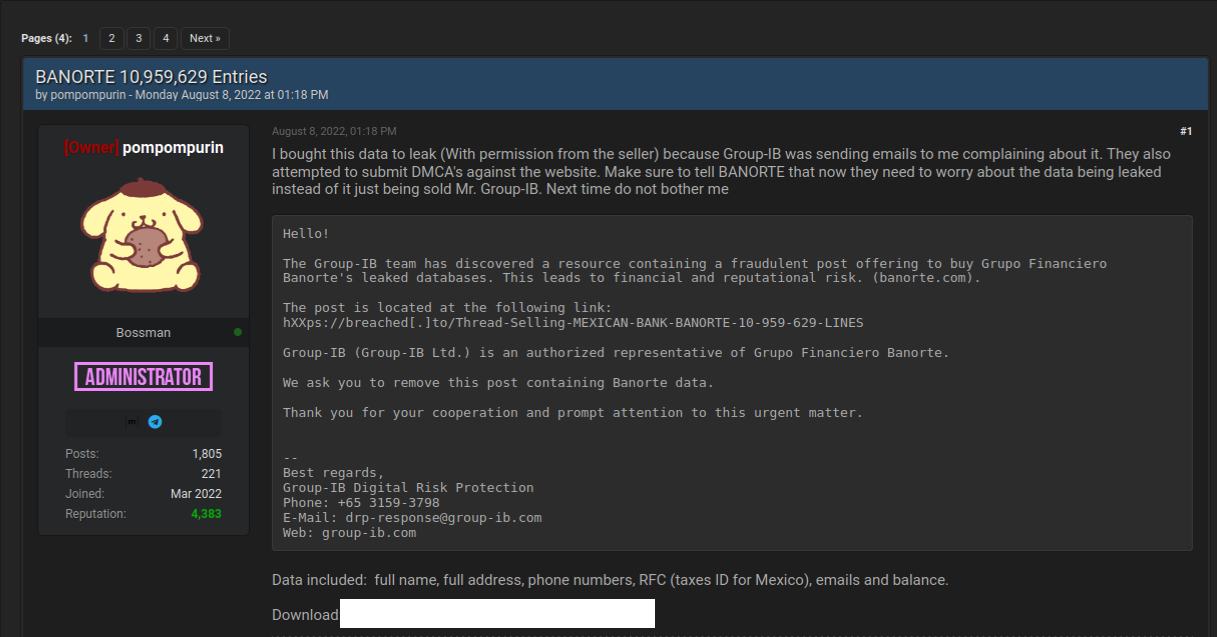
On August 3, 2022, someone using the alias “Holistic-K1ller” posted on Breached a thread selling data allegedly stolen from Grupo Financiero Banorte, Mexico’s second-biggest financial institution by total loans. Holistic-K1ller said the database included the full names, addresses, phone numbers, Mexican tax IDs (RFC), email addresses and balances on more than 10 million citizens.
There was no reason to believe Holistic-K1ller had fabricated their breach claim. This identity has been highly active on Breached and its predecessor RaidForums for more than two years, mostly selling databases from hacked Mexican entities. Last month, they sold customer information on 36 million customers of the Mexican phone company Telcel; in March, they sold 33,000 images of Mexican IDs — with the front picture and a selfie of each citizen. That same month, they also sold data on 1.4 million customers of Mexican lending platform Yotepresto.
But this history was either overlooked or ignored by Group-IB, the Singapore-based cybersecurity firm apparently hired by Banorte to help respond to the data breach.
“The Group-IB team has discovered a resource containing a fraudulent post offering to buy Grupo Financiero Banorte’s leaked databases,” reads a letter the Breach administrator said they received from Group-IB. “We ask you to remove this post containing Banorte data. Thank you for your cooperation and prompt attention to this urgent matter.”
The administrator of Breached is “Pompompurin,” the same individual who alerted this author in November 2021 to a glaring security hole in a U.S. Justice Department website that was used to spoof security alerts from the FBI. In a post to Breached on Aug. 8, Pompompurin said they bought the Banorte database from Holistic-K1ller’s sales thread because Group-IB was sending emails complaining about it.
“They also attempted to submit DMCA’s against the website,” Pompompurin wrote, referring to legal takedown requests under the Digital Millennium Copyright Act. “Make sure to tell Banorte that now they need to worry about the data being leaked instead of just being sold.”
Group-IB CEO Dmitriy Volkov said the company has seen some success in the past asking hackers to remove or take down certain information, but that making such requests is not a typical response for the security firm.
“It is not a common practice to send takedown notifications to such forums demanding that such content be removed,” Volkov said. “But these abuse letters are legally binding, which helps build a foundation for further steps taken by law enforcement agencies. Actions contrary to international rules in the regulated space of the Internet only lead to more severe crimes, which — as we know from the case of Raidforums — are successfully investigated and stopped by law enforcement.”
Banorte did not respond to requests for comment. But in a brief written statement picked up on Twitter, Banorte said there was no breach involving their infrastructure, and the data being sold is old.
“There has been no violation of our platforms and technological infrastructure,” Banorte said. “The set of information referred to is inaccurate and outdated, and does not put our users and customers at risk.”
That statement may be 100 percent true. Still, it is difficult to think of a better example of how not to do breach response. Banorte shrugging off this incident as a nothingburger is baffling: While it is almost certainly true that the bank balance information in the Banorte leak is now out of date, the rest of the information (tax IDs, phone numbers, email addresses) is harder to change.
“Is there one person from our community that think sending cease and desist letter to a hackers forum operator is a good idea?,” asked Ohad Zaidenberg, founder of CTI League, a volunteer emergency response community that emerged in 2020 to help fight COVID-19 related scams. “Who does it? Instead of helping, they pushed the organization from the hill.”
Kurt Seifried, director of IT for the CloudSecurityAlliance, was similarly perplexed by the response to the Banorte breach.
“If the data wasn’t real….did the bank think a cease and desist would result in the listing being removed?” Seifried wondered on Twitter. “I mean, isn’t selling breach data a worse crime usually than slander or libel? What was their thought process?”
A more typical response when a large bank suspects a breach is to approach the seller privately through an intermediary to ascertain if the information is valid and what it might cost to take it off the market. While it may seem odd to expect cybercriminals to make good on their claims to sell stolen data to only one party, removing sold stolen items from inventory is a fairly basic function of virtually all cybercriminal markets today (apart from perhaps sites that traffic in stolen identity data).
At a minimum, negotiating or simply engaging with a data seller can buy the victim organization additional time and clues with which to investigate the claim and ideally notify affected parties of a breach before the stolen data winds up online.
It is true that a large number of hacked databases put up for sale on the cybercrime underground are sold only after a small subset of in-the-know thieves have harvested all of the low-hanging fruit in the data — e.g., access to cryptocurrency accounts or user credentials that are recycled across multiple websites. And it’s certainly not unheard of for cybercriminals to go back on their word and re-sell or leak information that they have sold previously.
But companies in the throes of responding to a data security incident do themselves and customers no favors when they underestimate their adversaries, or try to intimidate cybercrooks with legal threats. Such responses generally accomplish nothing, except unnecessarily upping the stakes for everyone involved while displaying a dangerous naiveté about how the cybercrime underground works.
Update, Aug. 17, 10:32 a.m.: Thanks to a typo by this author, a request for comment sent to Group-IB was not delivered in advance of this story. The copy above has been updated to include a comment from Group-IB’s CEO.