


Today, we released the latest issue of The Domain Name Industry Brief, which shows that the first quarter of 2023 closed with 354.0 million domain name registrations across all top-level domains (TLDs), an increase of 3.5 million domain name registrations, or 1.0%, compared to the fourth quarter of 2022.1,2 Domain name registrations also increased by 3.5 million, or 1.0%, year over year.1,2
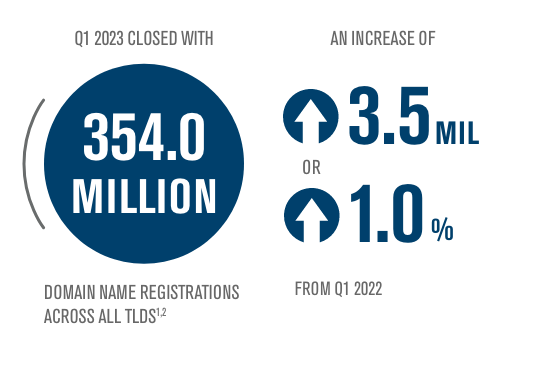
Check out the latest issue of The Domain Name Industry Brief to see domain name stats from the first quarter of 2023, including:
This issue of the Domain Name Industry Brief includes a correction to the March 2023 issue, which incorrectly reported the number of domain name registrations in the .eu ccTLD.2 This was the result of a one-time error in the .eu domain name registration data, provided by ZookNIC, which has since been resolved.
To see past issues of The Domain Name Industry Brief, please visit https://verisign.com/dnibarchives.
The post Verisign Domain Name Industry Brief: 354.0 Million Domain Name Registrations in the First Quarter of 2023 appeared first on Verisign Blog.
It’s not often that a zero-day vulnerability causes a network security vendor to urge customers to physically remove and decommission an entire line of affected hardware — as opposed to just applying software updates. But experts say that is exactly what transpired this week with Barracuda Networks, as the company struggled to combat a sprawling malware threat which appears to have undermined its email security appliances in such a fundamental way that they can no longer be safely updated with software fixes.

The Barracuda Email Security Gateway (ESG) 900 appliance.
Campbell, Calif. based Barracuda said it hired incident response firm Mandiant on May 18 after receiving reports about unusual traffic originating from its Email Security Gateway (ESG) devices, which are designed to sit at the edge of an organization’s network and scan all incoming and outgoing email for malware.
On May 19, Barracuda identified that the malicious traffic was taking advantage of a previously unknown vulnerability in its ESG appliances, and on May 20 the company pushed a patch for the flaw to all affected appliances (CVE-2023-2868).
In its security advisory, Barracuda said the vulnerability existed in the Barracuda software component responsible for screening attachments for malware. More alarmingly, the company said it appears attackers first started exploiting the flaw in October 2022.
But on June 6, Barracuda suddenly began urging its ESG customers to wholesale rip out and replace — not patch — affected appliances.
“Impacted ESG appliances must be immediately replaced regardless of patch version level,” the company’s advisory warned. “Barracuda’s recommendation at this time is full replacement of the impacted ESG.”
In a statement, Barracuda said it will be providing the replacement product to impacted customers at no cost, and that not all ESG appliances were compromised.
“No other Barracuda product, including our SaaS email solutions, were impacted by this vulnerability,” the company said. “If an ESG appliance is displaying a notification in the User Interface, the ESG appliance had indicators of compromise. If no notification is displayed, we have no reason to believe that the appliance has been compromised at this time.”
Nevertheless, the statement says that “out of an abundance of caution and in furtherance of our containment strategy, we recommend impacted customers replace their compromised appliance.”
“As of June 8, 2023, approximately 5% of active ESG appliances worldwide have shown any evidence of known indicators of compromise due to the vulnerability,” the statement continues. “Despite deployment of additional patches based on known IOCs, we continue to see evidence of ongoing malware activity on a subset of the compromised appliances. Therefore, we would like customers to replace any compromised appliance with a new unaffected device.”
Rapid7‘s Caitlin Condon called this remarkable turn of events “fairly stunning,” and said there appear to be roughly 11,000 vulnerable ESG devices still connected to the Internet worldwide.
“The pivot from patch to total replacement of affected devices is fairly stunning and implies the malware the threat actors deployed somehow achieves persistence at a low enough level that even wiping the device wouldn’t eradicate attacker access,” Condon wrote.
Barracuda said the malware was identified on a subset of appliances that allowed the attackers persistent backdoor access to the devices, and that evidence of data exfiltration was identified on some systems.
Rapid7 said it has seen no evidence that attackers are using the flaw to move laterally within victim networks. But that may be small consolation for Barracuda customers now coming to terms with the notion that foreign cyberspies probably have been hoovering up all their email for months.
Nicholas Weaver, a researcher at University of California, Berkeley’s International Computer Science Institute (ICSI), said it is likely that the malware was able to corrupt the underlying firmware that powers the ESG devices in some irreparable way.
“One of the goals of malware is to be hard to remove, and this suggests the malware compromised the firmware itself to make it really hard to remove and really stealthy,” Weaver said. “That’s not a ransomware actor, that’s a state actor. Why? Because a ransomware actor doesn’t care about that level of access. They don’t need it. If they’re going for data extortion, it’s more like a smash-and-grab. If they’re going for data ransoming, they’re encrypting the data itself — not the machines.”
In addition to replacing devices, Barracuda says ESG customers should also rotate any credentials connected to the appliance(s), and check for signs of compromise dating back to at least October 2022 using the network and endpoint indicators the company has released publicly.
Update, June 9, 11:55 a.m. ET: Barracuda has issued an updated statement about the incident, portions of which are now excerpted above.




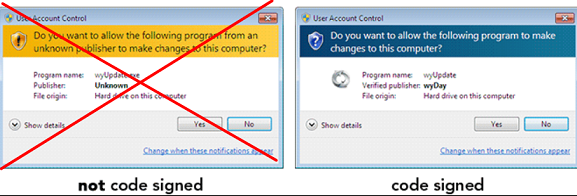
Code-signing certificates are supposed to help authenticate the identity of software publishers, and provide cryptographic assurance that a signed piece of software has not been altered or tampered with. Both of these qualities make stolen or ill-gotten code-signing certificates attractive to cybercriminal groups, who prize their ability to add stealth and longevity to malicious software. This post is a deep dive on “Megatraffer,” a veteran Russian hacker who has practically cornered the underground market for malware focused code-signing certificates since 2015.
A review of Megatraffer’s posts on Russian crime forums shows this user began peddling individual stolen code-signing certs in 2015 on the Russian-language forum Exploit, and soon expanded to selling certificates for cryptographically signing applications and files designed to run in Microsoft Windows, Java, Adobe AIR, Mac and Microsoft Office.
Megatraffer explained that malware purveyors need a certificate because many antivirus products will be far more interested in unsigned software, and because signed files downloaded from the Internet don’t tend to get blocked by security features built into modern web browsers. Additionally, newer versions of Microsoft Windows will complain with a bright yellow or red alert message if users try to install a program that is not signed.
“Why do I need a certificate?” Megatraffer asked rhetorically in their Jan. 2016 sales thread on Exploit. “Antivirus software trusts signed programs more. For some types of software, a digital signature is mandatory.”
At the time, Megatraffer was selling unique code-signing certificates for $700 apiece, and charging more than twice that amount ($1,900) for an “extended validation” or EV code-signing cert, which is supposed to only come with additional identity vetting of the certificate holder. According to Megatraffer, EV certificates were a “must-have” if you wanted to sign malicious software or hardware drivers that would reliably work in newer Windows operating systems.
Part of Megatraffer’s ad. Image: Ke-la.com.
Megatraffer has continued to offer their code-signing services across more than a half-dozen other Russian-language cybercrime forums, mostly in the form of sporadically available EV and non-EV code-signing certificates from major vendors like Thawte and Comodo.
More recently, it appears Megatraffer has been working with ransomware groups to help improve the stealth of their malware. Shortly after Russia invaded Ukraine in February 2022, someone leaked several years of internal chat logs from the Conti ransomware gang, and those logs show Megatraffer was working with the group to help code-sign their malware between July and October 2020.
According to cyber intelligence firm Intel 471, Megatraffer has been active on more than a half-dozen crime forums from September 2009 to the present day. And on most of these identities, Megatraffer has used the email address 774748@gmail.com. That same email address also is tied to two forum accounts for a user with the handle “O.R.Z.”
Constella Intelligence, a company that tracks exposed databases, finds that 774748@gmail.com was used in connection with just a handful of passwords, but most frequently the password “featar24“. Pivoting off of that password reveals a handful of email addresses, including akafitis@gmail.com.
Intel 471 shows akafitis@gmail.com was used to register another O.R.Z. user account — this one on Verified[.]ru in 2008. Prior to that, akafitis@gmail.com was used as the email address for the account “Fitis,” which was active on Exploit between September 2006 and May 2007. Constella found the password “featar24” also was used in conjunction with the email address spampage@yandex.ru, which is tied to yet another O.R.Z. account on Carder[.]su from 2008.
The email address akafitis@gmail.com was used to create a Livejournal blog profile named Fitis that has a large bear as its avatar. In November 2009, Fitis wrote, “I am the perfect criminal. My fingerprints change beyond recognition every few days. At least my laptop is sure of it.”
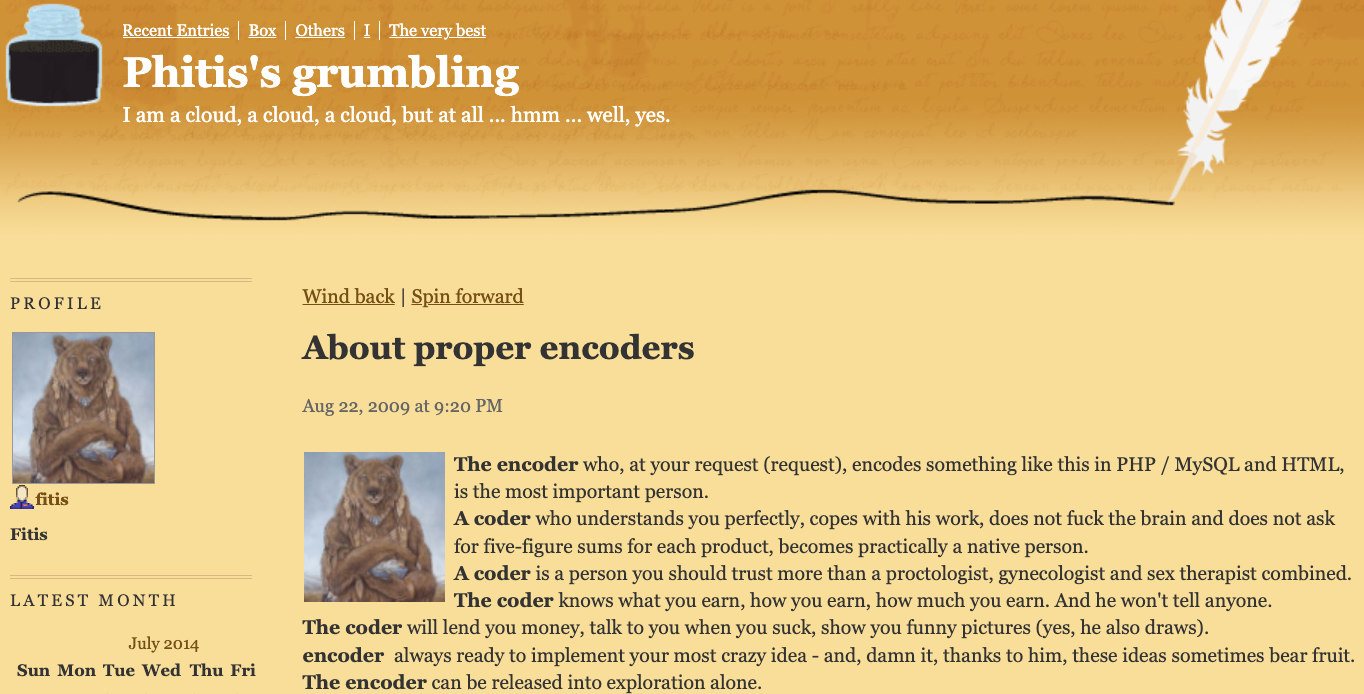
Fitis’s Livejournal account. Image: Archive.org.
Fitis’s real-life identity was exposed in 2010 after two of the biggest sponsors of pharmaceutical spam went to war with each other, and large volumes of internal documents, emails and chat records seized from both spam empires were leaked to this author. That protracted and public conflict formed the backdrop of my 2014 book — “Spam Nation: The Inside Story of Organized Cybercrime, from Global Epidemic to Your Front Door.”
One of the leaked documents included a Microsoft Excel spreadsheet containing the real names, addresses, phone numbers, emails, street addresses and WebMoney addresses for dozens of top earners in Spamit — at the time the most successful pharmaceutical spam affiliate program in the Russian hacking scene and one that employed most of the top Russian botmasters.
That document shows Fitis was one of Spamit’s most prolific recruiters, bringing more than 75 affiliates to the Spamit program over several years prior to its implosion in 2010 (and earning commissions on any future sales from all 75 affiliates).
The document also says Fitis got paid using a WebMoney account that was created when its owner presented a valid Russian passport for a Konstantin Evgenievich Fetisov, born Nov. 16, 1982 and residing in Moscow. Russian motor vehicle records show two different vehicles are registered to this person at the same Moscow address.
The most interesting domain name registered to the email address spampage@yahoo.com, fittingly enough, is fitis[.]ru, which DomainTools.com says was registered in 2005 to a Konstantin E. Fetisov from Moscow.
The Wayback Machine at archive.org has a handful of mostly blank pages indexed for fitis[.]ru in its early years, but for a brief period in 2007 it appears this website was inadvertently exposing all of its file directories to the Internet.
One of the exposed files — Glavmed.html — is a general invitation to the infamous Glavmed pharmacy affiliate program, a now-defunct scheme that paid tens of millions of dollars to affiliates who advertised online pill shops mainly by hacking websites and manipulating search engine results. Glavmed was operated by the same Russian cybercriminals who ran the Spamit program.
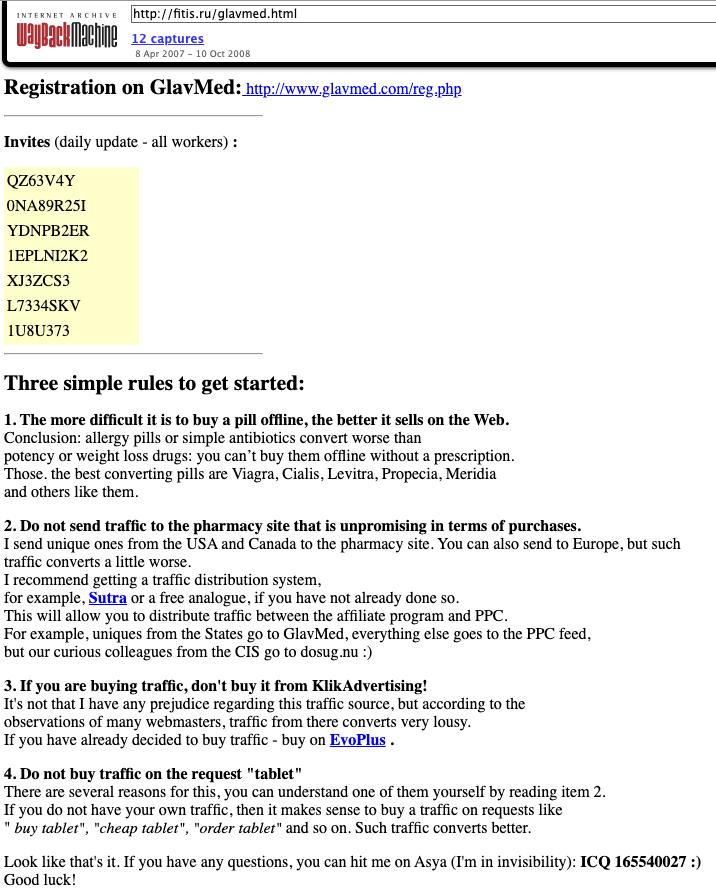
A Google translated ad circa 2007 recruiting for the pharmacy affiliate program Glavmed, which told interested applicants to contact the ICQ number used by Fitis, a.k.a. MegaTraffer. Image: Archive.org.
Archive.org shows the fitis[.]ru webpage with the Glavmed invitation was continuously updated with new invite codes. In their message to would-be Glavmed affiliates, the program administrator asked applicants to contact them at the ICQ number 165540027, which Intel 471 found was an instant messenger address previously used by Fitis on Exploit.
The exposed files in the archived version of fitis[.]ru include source code for malicious software, lists of compromised websites used for pharmacy spam, and a handful of what are apparently personal files and photos. Among the photos is a 2007 image labeled merely “fitis.jpg,” which shows a bespectacled, bearded young man with a ponytail standing next to what appears to be a newly-married couple at a wedding ceremony.
Mr. Fetisov did not respond to requests for comment.
As a veteran organizer of affiliate programs, Fitis did not waste much time building a new moneymaking collective after Spamit closed up shop. New York City-based cyber intelligence firm Flashpoint found that Megatraffer’s ICQ was the contact number for Himba[.]ru, a cost-per-acquisition (CPA) program launched in 2012 that paid handsomely for completed application forms tied to a variety of financial instruments, including consumer credit cards, insurance policies, and loans.
“Megatraffer’s entrenched presence on cybercrime forums strongly suggests that malicious means are used to source at least a portion of traffic delivered to HIMBA’s advertisers,” Flashpoint observed in a threat report on the actor.
Intel 471 finds that Himba was an active affiliate program until around May 2019, when it stopping paying its associates.

Fitis’s Himba affiliate program, circa February 2014. Image: Archive.org.
Flashpoint notes that in September 2015, Megatraffer posted a job ad on Exploit seeking experienced coders to work on browser plugins, installers and “loaders” — basically remote access trojans (RATs) that establish communication between the attacker and a compromised system.
“The actor specified that he is looking for full-time, onsite help either in his Moscow or Kiev locations,” Flashpoint wrote.
As APIs are a favorite target for threat actors, the challenge of securing the glue that holds various software elements together is taking on increasing urgency
The post All eyes on APIs: Top 3 API security risks and how to mitigate them appeared first on WeLiveSecurity
A number of Discord communities focused on cryptocurrency have been hacked this past month after their administrators were tricked into running malicious Javascript code disguised as a Web browser bookmark.
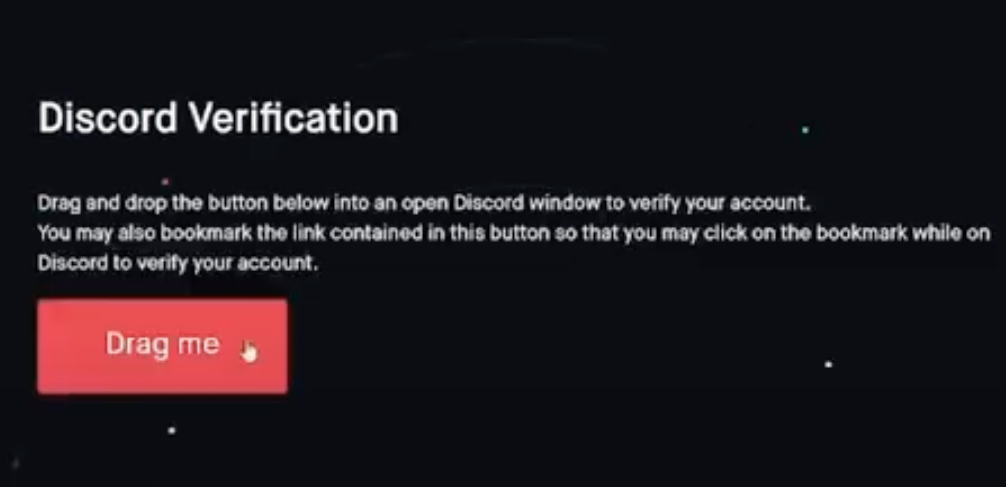
This attack involves malicious Javascript that is added to one’s browser by dragging a component from a web page to one’s browser bookmarks.
According to interviews with victims, several of the attacks began with an interview request from someone posing as a reporter for a crypto-focused news outlet online. Those who take the bait are sent a link to a Discord server that appears to be the official Discord of the crypto news site, where they are asked to complete a verification step to validate their identity.
As shown in this Youtube video, the verification process involves dragging a button from the phony crypto news Discord server to the bookmarks bar in one’s Web browser. From there, the visitor is instructed to go back to discord.com and then click the new bookmark to complete the verification process.
However, the bookmark is actually a clever snippet of Javascript that quietly grabs the user’s Discord token and sends it to the scammer’s website. The attacker then loads the stolen token into their own browser session and (usually late at night after the admins are asleep) posts an announcement in the targeted Discord about an exclusive “airdrop,” “NFT mint event” or some other potential money making opportunity for the Discord members.
The unsuspecting Discord members click the link provided by the compromised administrator account, and are asked to connect their crypto wallet to the scammer’s site, where it asks for unlimited spend approvals on their tokens, and subsequently drains the balance of any valuable accounts.
Meanwhile, anyone in the compromised Discord channel who notices the scam and replies is banned, and their messages are deleted by the compromised admin account.
Nicholas Scavuzzo is an associate at Ocean Protocol, which describes itself as an “open-source protocol that aims to allow businesses and individuals to exchange and monetize data and data-based services.” On May 22, an administrator for Ocean Protocol’s Discord server clicked a link in a direct message from a community member that prompted them to prove their identity by dragging a link to their bookmarks.
Scavuzzo, who is based in Maine, said the attackers waited until around midnight in his timezone time before using the administrator’s account to send out an unauthorized message about a new Ocean airdrop.
Scavuzzo said the administrator’s account was hijacked even though she had multi-factor authentication turned on.
“A CAPTCHA bot that allows Discord cookies to be accessed by the person hosting the CAPTCHA,” was how Scavuzzo described the attack. “I’ve seen all kinds of crypto scams, but I’ve never seen one like this.”
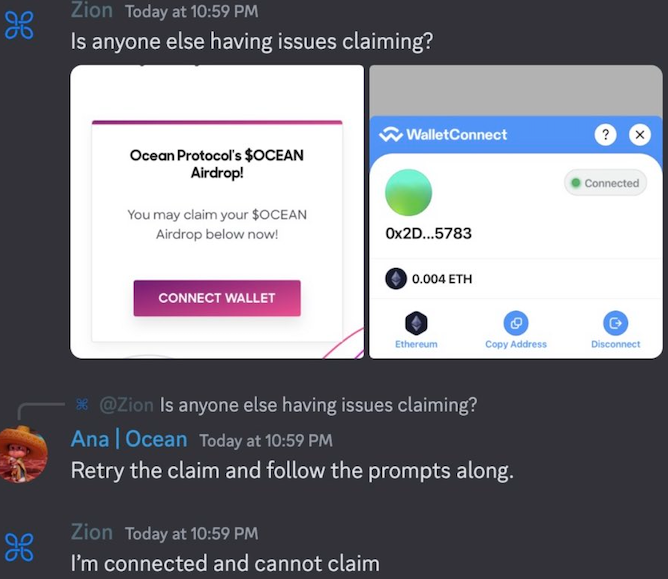
In this conversation, “Ana | Ocean” is a compromised Discord server administrator account promoting a phony airdrop.
Importantly, the stolen token only works for the attackers as long as its rightful owner doesn’t log out and back in, or else change their credentials.
Assuming the administrator can log in, that is. In Ocean’s case, one of the first things the intruders did once they swiped the administrator’s token was change the server’s access controls and remove all core Ocean team members from the server.
Fortunately for Ocean, Scavuzzo was able to reach the operator of the server that hosts the Discord channel, and have the channel’s settings reverted back to normal.
“Thankfully, we are a globally distributed team, so we have people awake at all hours,” Scavuzzo said, noting that Ocean is not aware of any Discord community members who fell for the phony airdrop offer, which was live for about 30 minutes. “This could have been a lot worse.”
On May 26, Aura Network reported on Twitter that its Discord server was compromised in a phishing attack that resulted in the deletion of Discord channels and the dissemination of fake Aura Network Airdrop Campaign links.
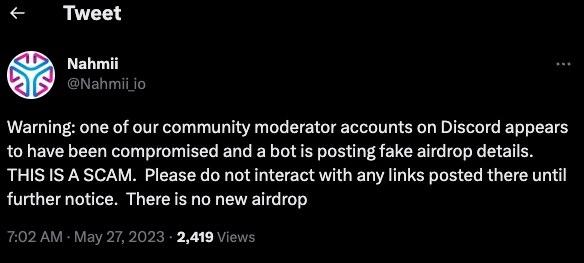
On May 27, Nahmii — a cryptocurrency technology based on the Ethereum blockchain — warned on Twitter that one of its community moderators on Discord was compromised and posting fake airdrop details.
On May 9, MetrixCoin reported that its Discord server was hacked, with fake airdrop details pushed to all users.
KrebsOnSecurity recently heard from a trusted source in the cybersecurity industry who dealt firsthand with one of these attacks and asked to remain anonymous.
“I do pro bono Discord security work for a few Discords, and I was approached by one of these fake journalists,” the source said. “I played along and got the link to their Discord, where they were pretending to be journalists from the Cryptonews website using several accounts.”
The source took note of all the Discord IDs of the admins of the fake Cryptonews Discord, so that he could ensure they were blocked from the Discords he helps to secure.
“Since I’ve been doing this for a while now, I’ve built up a substantial database of Discord users and messages, so often I can see these scammers’ history on Discord,” the source said.
In this case, he noticed a user with the “CEO” role in the fake Cryptonews Discord had been seen previously under another username — “Levatax.” Searching on that Discord ID and username revealed a young Turkish coder named Berk Yilmaz whose Github page linked to the very same Discord ID as the scammer CEO.
Reached via instant message on Telegram, Levatax said he’s had no involvement in such schemes, and that he hasn’t been on Discord since his Microsoft Outlook account was hacked months ago.
“The interesting thing [is] that I didn’t use Discord since few months or even social media because of the political status of Turkey,” Levatax explained, referring to the recent election in his country. “The only thing I confirm is losing my Outlook account which connected to my Discord, and I’m already in touch with Microsoft to recover it.”
The verification method used in the above scam involves a type of bookmark called a “bookmarklet” that stores Javascript code as a clickable link in the bookmarks bar at the top of one’s browser.
While bookmarklets can be useful and harmless, malicious Javascript that is executed in the browser by the user is especially dangerous. So please avoid adding (or dragging) any bookmarks or bookmarklets to your browser unless it was your idea in the first place.
The number of phishing websites tied to domain name registrar Freenom dropped precipitously in the months surrounding a recent lawsuit from social networking giant Meta, which alleged the free domain name provider has a long history of ignoring abuse complaints about phishing websites while monetizing traffic to those abusive domains.
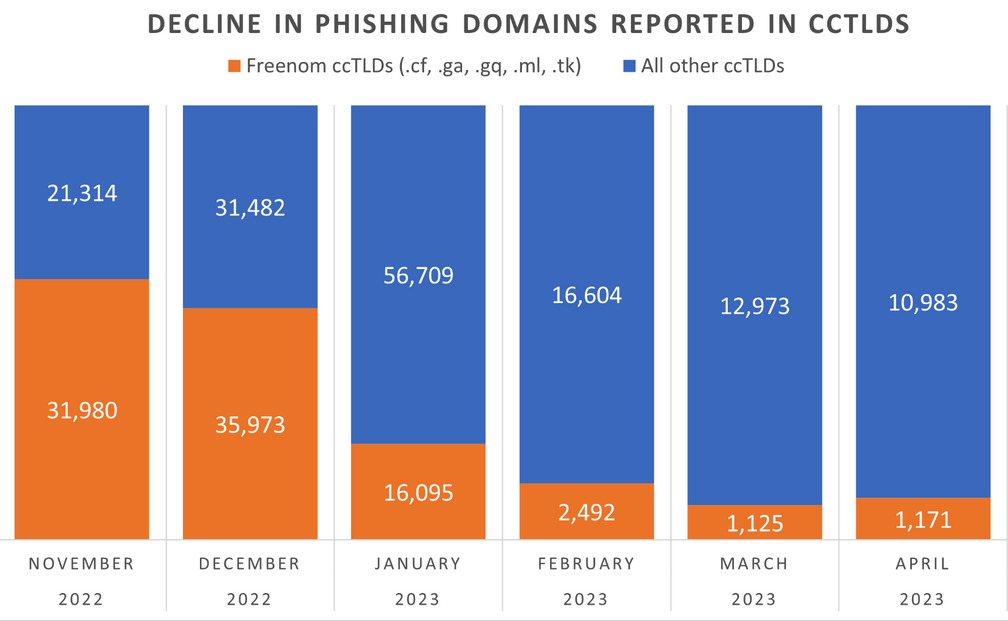
The volume of phishing websites registered through Freenom dropped considerably since the registrar was sued by Meta. Image: Interisle Consulting.
Freenom is the domain name registry service provider for five so-called “country code top level domains” (ccTLDs), including .cf for the Central African Republic; .ga for Gabon; .gq for Equatorial Guinea; .ml for Mali; and .tk for Tokelau.
Freenom has always waived the registration fees for domains in these country-code domains, but the registrar also reserves the right to take back free domains at any time, and to divert traffic to other sites — including adult websites. And there are countless reports from Freenom users who’ve seen free domains removed from their control and forwarded to other websites.
By the time Meta initially filed its lawsuit in December 2022, Freenom was the source of well more than half of all new phishing domains coming from country-code top-level domains. Meta initially asked a court to seal its case against Freenom, but that request was denied. Meta withdrew its December 2022 lawsuit and re-filed it in March 2023.
“The five ccTLDs to which Freenom provides its services are the TLDs of choice for cybercriminals because Freenom provides free domain name registration services and shields its customers’ identity, even after being presented with evidence that the domain names are being used for illegal purposes,” Meta’s complaint charged. “Even after receiving notices of infringement or phishing by its customers, Freenom continues to license new infringing domain names to those same customers.”
Meta pointed to research from Interisle Consulting Group, which discovered in 2021 and again last year that the five ccTLDs operated by Freenom made up half of the Top Ten TLDs most abused by phishers.
Interisle partner Dave Piscitello said something remarkable has happened in the months since the Meta lawsuit.
“We’ve observed a significant decline in phishing domains reported in the Freenom commercialized ccTLDs in months surrounding the lawsuit,” Piscitello wrote on Mastodon. “Responsible for over 60% of phishing domains reported in November 2022, Freenom’s percentage has dropped to under 15%.”
Interisle collects data from 12 major blocklists for spam, malware, and phishing, and it receives phishing-specific data from Spamhaus, Phishtank, OpenPhish and the APWG Ecrime Exchange. The company publishes historical data sets quarterly, both on malware and phishing.
Piscitello said it’s too soon to tell the full impact of the Freenom lawsuit, noting that Interisle’s sources of spam and phishing data all have different policies about when domains are removed from their block lists.
“One of the things we don’t have visibility into is how each of the blocklists determine to remove a URL from their lists,” he said. “Some of them time out [listed domains] after 14 days, some do it after 30, and some keep them forever.”
Freenom did not respond to requests for comment.
This is the second time in as many years that a lawsuit by Meta against a domain registrar has disrupted the phishing industry. In March 2020, Meta sued domain registrar giant Namecheap, alleging cybersquatting and trademark infringement.
The two parties settled the matter in April 2022. While the terms of that settlement have not been disclosed, new phishing domains registered through Namecheap declined more than 50 percent the following quarter, Interisle found.
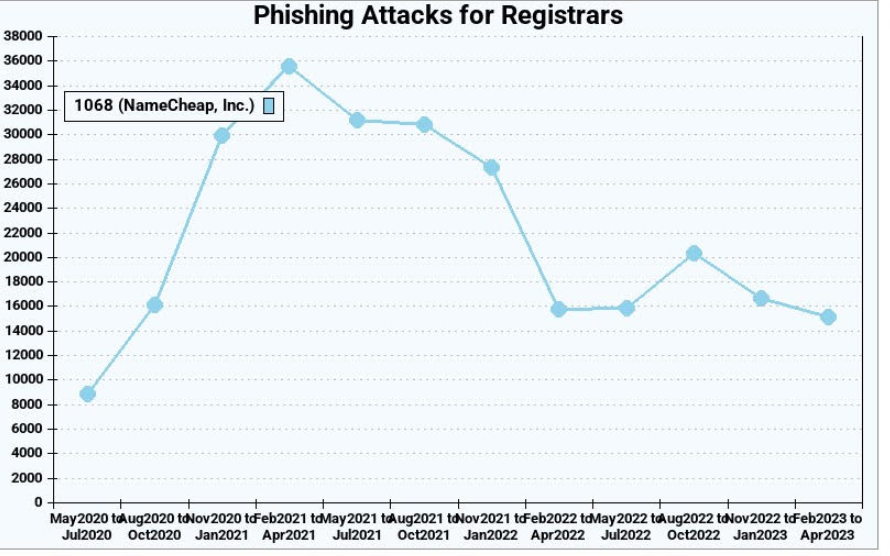
Phishing attacks using websites registered through Namecheap, before and after the registrar settled a lawsuit with Meta. Image: Interisle Consulting.
Unfortunately, the lawsuits have had little effect on the overall number of phishing attacks and phishing-related domains, which have steadily increased in volume over the years. Piscitello said the phishers tend to gravitate toward registrars that offer the least resistance and lowest price per domain. And with new top-level domains constantly being introduced, there is rarely a shortage of super low-priced domains.
“The abuse of a new top-level domain is largely the result of one registrar’s portfolio,” Piscitello told KrebsOnSecurity. “Alibaba or Namecheap or another registrar will run a promotion for a cheap domain, and then we’ll see flocking and migration of the phishers to that TLD. It’s like strip mining, where they’ll buy hundreds or thousands of domains, use those in a campaign, exhaust that TLD and then move on to another provider.”
Piscitello said despite the steep drop in phishing domains coming out of Freenom, the alternatives available to phishers are many. After all, there are more than 2,000 accredited domain registrars, not to mention dozens of services that let anyone set up a website for free without even owning a domain.
“There is no evidence that the trend line is even going to level off,” he said. “I think what the Meta lawsuit tells us is that litigation is like giving someone a standing eight count. It temporarily disrupts a process. And in that sense, litigation appears to be working.”
Social networks are constantly battling inauthentic bot accounts that send direct messages to users promoting scam cryptocurrency investment platforms. What follows is an interview with a Russian hacker responsible for a series of aggressive crypto spam campaigns that recently prompted several large Mastodon communities to temporarily halt new registrations. According to the hacker, their spam software has been in private use until the last few weeks, when it was released as open source code.

Renaud Chaput is a freelance programmer working on modernizing and scaling the Mastodon project infrastructure — including joinmastodon.org, mastodon.online, and mastodon.social. Chaput said that on May 4, 2023, someone unleashed a spam torrent targeting users on these Mastodon communities via “private mentions,” a kind of direct messaging on the platform.
The messages said recipients had earned an investment credit at a cryptocurrency trading platform called moonxtrade[.]com. Chaput said the spammers used more than 1,500 Internet addresses across 400 providers to register new accounts, which then followed popular accounts on Mastodon and sent private mentions to the followers of those accounts.
Since then, the same spammers have used this method to advertise more than 100 different crypto investment-themed domains. Chaput said that at one point this month the volume of bot accounts being registered for the crypto spam campaign started overwhelming the servers that handle new signups at Mastodon.social.
“We suddenly went from like three registrations per minute to 900 a minute,” Chaput said. “There was nothing in the Mastodon software to detect that activity, and the protocol is not designed to handle this.”

One of the crypto investment scam messages promoted in the spam campaigns on Mastodon this month.
Seeking to gain a temporary handle on the spam wave, Chaput said he briefly disabled new account registrations on mastodon.social and mastondon.online. Shortly after that, those same servers came under a sustained distributed denial-of-service (DDoS) attack.
Chaput said whoever was behind the DDoS was definitely not using point-and-click DDoS tools, like a booter or stresser service.
“This was three hours non-stop, 200,000 to 400,000 requests per second,” Chaput said of the DDoS. “At first, they were targeting one path, and when we blocked that they started to randomize things. Over three hours the attack evolved several times.”
Chaput says the spam waves have died down since they retrofitted mastodon.social with a CAPTCHA, those squiggly letter and number combinations designed to stymie automated account creation tools. But he’s worried that other Mastodon instances may not be as well-staffed and might be easy prey for these spammers.
“We don’t know if this is the work of one person, or if this is [related to] software or services being sold to others,” Chaput told KrebsOnSecurity. “We’re really impressed by the scale of it — using hundreds of domains and thousands of Microsoft email addresses.”
Chaput said a review of their logs indicates many of the newly registered Mastodon spam accounts were registered using the same 0auth credentials, and that a domain common to those credentials was quot[.]pw.
The domain quot[.]pw has been registered and abandoned by several parties since 2014, but the most recent registration data available through DomainTools.com shows it was registered in March 2020 to someone in Krasnodar, Russia with the email address edgard011012@gmail.com.
This email address is also connected to accounts on several Russian cybercrime forums, including “__edman__,” who had a history of selling “logs” — large amounts of data stolen from many bot-infected computers — as well as giving away access to hacked Internet of Things (IoT) devices.
In September 2018, a user by the name “ципа” (phonetically “Zipper” in Russian) registered on the Russian hacking forum Lolzteam using the edgard0111012@gmail.com address. In May 2020, Zipper told another Lolzteam member that quot[.]pw was their domain. That user advertised a service called “Quot Project” which said they could be hired to write programming scripts in Python and C++.
“I make Telegram bots and other rubbish cheaply,” reads one February 2020 sales thread from Zipper.
Clicking the “open chat in Telegram” button on Zipper’s Lolzteam profile page launched a Telegram instant message chat window where the user Quotpw responded almost immediately. Asked if they were aware their domain was being used to manage a spam botnet that was pelting Mastodon instances with crypto scam spam, Quotpw confirmed the spam was powered by their software.
“It was made for a limited circle of people,” Quotpw said, noting that they recently released the bot software as open source on GitHub.
Quotpw went on to say the spam botnet was powered by well more than the hundreds of IP addresses tracked by Chaput, and that these systems were mostly residential proxies. A residential proxy generally refers to a computer or mobile device running some type of software that enables the system to be used as a pass-through for Internet traffic from others.
Very often, this proxy software is installed surreptitiously, such as through a “Free VPN” service or mobile app. Residential proxies also can refer to households protected by compromised home routers running factory-default credentials or outdated firmware.
Quotpw maintains they have earned more than $2,000 sending roughly 100,000 private mentions to users of different Mastodon communities over the past few weeks. Quotpw said their conversion rate for the same bot-powered direct message spam on Twitter is usually much higher and more profitable, although they conceded that recent adjustments to Twitter’s anti-bot CAPTCHA have put a crimp in their Twitter earnings.
“My partners (I’m programmer) lost time and money while ArkoseLabs (funcaptcha) introduced new precautions on Twitter,” Quotpw wrote in a Telegram reply. “On Twitter, more spam and crypto scam.”
Asked whether they felt at all conflicted about spamming people with invitations to cryptocurrency scams, Quotpw said in their hometown “they pay more for such work than in ‘white’ jobs” — referring to legitimate programming jobs that don’t involve malware, botnets, spams and scams.
“Consider salaries in Russia,” Quotpw said. “Any spam is made for profit and brings illegal money to spammers.”
Shortly after edgard011012@gmail.com registered quot[.]pw, the WHOIS registration records for the domain were changed again, to msr-sergey2015@yandex.ru, and to a phone number in Austria: +43.6607003748.
Constella Intelligence, a company that tracks breached data, finds that the address msr-sergey2015@yandex.ru has been associated with accounts at the mobile app site aptoide.com (user: CoolappsforAndroid) and vimeworld.ru that were created from different Internet addresses in Vienna, Austria.
A search in Skype on that Austrian phone number shows it belongs to a Sergey Proshutinskiy who lists his location as Vienna, Austria. The very first result that comes up when one searches that unusual name in Google is a LinkedIn profile for a Sergey Proshutinskiy from Vienna, Austria.
Proshutinskiy’s LinkedIn profile says he is a Class of 2024 student at TGM, which is a state-owned, technical and engineering school in Austria. His resume also says he is a data science intern at Mondi Group, an Austrian manufacturer of sustainable packaging and paper.
Mr. Proshutinskiy did not respond to requests for comment.
Quotpw denied being Sergey, and said Sergey was a friend who registered the domain as a birthday present and favor last year.
“Initially, I bought it for 300 rubles,” Quotpw explained. “The extension cost 1300 rubles (expensive). I waited until it expired and forgot to buy it. After that, a friend (Sergey) bought [the] domain and transferred access rights to me.”
“He’s not even an information security specialist,” Quotpw said of Sergey. “My friends do not belong to this field. None of my friends are engaged in scams or other black [hat] activities.”
It may seem unlikely that someone would go to all this trouble to spam Mastodon users over several weeks using an impressive number of resources — all for just $2,000 in profit. But it is likely that whoever is actually running the various crypto scam platforms advertised by Quotpw’s spam messages pays handsomely for any investments generated by their spam.
According to the FBI, financial losses from cryptocurrency investment scams dwarfed losses for all other types of cybercrime in 2022, rising from $907 million in 2021 to $2.57 billion last year.
Update, May 25, 10:30 a.m.: Corrected attribution of the Austrian school TGM.

Countless smartphones seized in arrests and searches by police forces across the United States are being auctioned online without first having the data on them erased, a practice that can lead to crime victims being re-victimized, a new study found. In response, the largest online marketplace for items seized in U.S. law enforcement investigations says it now ensures that all phones sold through its platform will be data-wiped prior to auction.
Researchers at the University of Maryland last year purchased 228 smartphones sold “as-is” from PropertyRoom.com, which bills itself as the largest auction house for police departments in the United States. Of phones they won at auction (at an average of $18 per phone), the researchers found 49 had no PIN or passcode; they were able to guess an additional 11 of the PINs by using the top-40 most popular PIN or swipe patterns.
Phones may end up in police custody for any number of reasons — such as its owner was involved in identity theft — and in these cases the phone itself was used as a tool to commit the crime.
“We initially expected that police would never auction these phones, as they would enable the buyer to recommit the same crimes as the previous owner,” the researchers explained in a paper released this month. “Unfortunately, that expectation has proven false in practice.”
The researchers said while they could have employed more aggressive technological measures to work out more of the PINs for the remaining phones they bought, they concluded based on the sample that a great many of the devices they won at auction had probably not been data-wiped and were protected only by a PIN.
Beyond what you would expect from unwiped second hand phones — every text message, picture, email, browser history, location history, etc. — the 61 phones they were able to access also contained significant amounts of data pertaining to crime — including victims’ data — the researchers found.
Some readers may be wondering at this point, “Why should we care about what happens to a criminal’s phone?” First off, it’s not entirely clear how these phones ended up for sale on PropertyRoom.
“Some folks are like, ‘Yeah, whatever, these are criminal phones,’ but are they?” said Dave Levin, an assistant professor of computer science at University of Maryland.
“We started looking at state laws around what they’re supposed to do with lost or stolen property, and we found that most of it ends up going the same route as civil asset forfeiture,” Levin continued. “Meaning, if they can’t find out who owns something, it eventually becomes the property of the state and gets shipped out to these resellers.”
Also, the researchers found that many of the phones clearly had personal information on them regarding previous or intended targets of crime: A dozen of the phones had photographs of government-issued IDs. Three of those were on phones that apparently belonged to sex workers; their phones contained communications with clients.
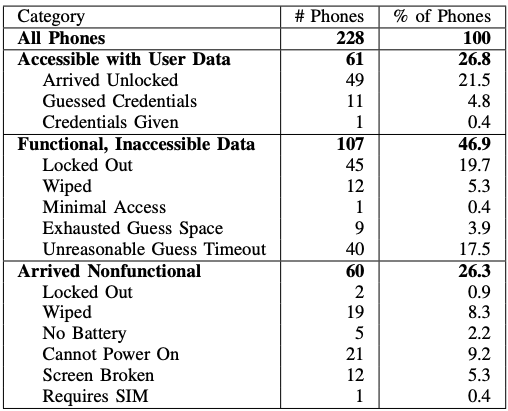
An overview of the phone functionality and data accessibility for phones purchased by the researchers.
One phone had full credit files for eight different people on it. On another device they found a screenshot including 11 stolen credit cards that were apparently purchased from an online carding shop. On yet another, the former owner had apparently been active in a Telegram group chat that sold tutorials on how to run identity theft scams.
The most interesting phone from the batches they bought at auction was one with a sticky note attached that included the device’s PIN and the notation “Gry Keyed,” no doubt a reference to the Graykey software that is often used by law enforcement agencies to brute-force a mobile device PIN.
“That one had the PIN on the back,” Levin said. “The message chain on that phone had 24 Experian and TransUnion credit histories”.
The University of Maryland team said they took care in their research not to further the victimization of people whose information was on the devices they purchased from PropertyRoom.com. That involved ensuring that none of the devices could connect to the Internet when powered on, and scanning all images on the devices against known hashes for child sexual abuse material.
It is common to find phones and other electronics for sale on auction platforms like eBay that have not been wiped of sensitive data, but in those cases eBay doesn’t possess the items being sold. In contrast, platforms like PropertyRoom obtain devices and resell them at auction directly.
PropertyRoom did not respond to multiple requests for comment. But the researchers said sometime in the past few months PropertyRoom began posting a notice stating that all mobile devices would be wiped of their data before being sold at auction.
“We informed them of our research in October 2022, and they responded that they would review our findings internally,” Levin said. “They stopped selling them for a while, but then it slowly came back, and then we made sure we won every auction. And all of the ones we got from that were indeed wiped, except there were four devices that had external SD [storage] cards in them that weren’t wiped.”
A copy of the University of Maryland study is here (PDF).





The U.S. Federal Bureau of Investigation (FBI) this week seized 13 domain names connected to “booter” services that let paying customers launch crippling distributed denial-of-service (DDoS) attacks. Ten of the domains are reincarnations of DDoS-for-hire services the FBI seized in December 2022, when it charged six U.S. men with computer crimes for allegedly operating booters.
Booter services are advertised through a variety of methods, including Dark Web forums, chat platforms and even youtube.com. They accept payment via PayPal, Google Wallet, and/or cryptocurrencies, and subscriptions can range in price from just a few dollars to several hundred per month. The services are generally priced according to the volume of traffic to be hurled at the target, the duration of each attack, and the number of concurrent attacks allowed.
The websites that saw their homepages replaced with seizure notices from the FBI this week include booter services like cyberstress[.]org and exoticbooter[.]com, which the feds say were used to launch millions of attacks against millions of victims.
“School districts, universities, financial institutions and government websites are among the victims who have been targeted in attacks launched by booter services,” federal prosecutors in Los Angeles said in a statement.
Purveyors of booters or “stressers” claim they are not responsible for how customers use their services, and that they aren’t breaking the law because — like most security tools — these services can be used for good or bad purposes. Most booter sites employ wordy “terms of use” agreements that require customers to agree they will only stress-test their own networks — and that they won’t use the service to attack others.
But the DOJ says these disclaimers usually ignore the fact that most booter services are heavily reliant on constantly scanning the Internet to commandeer misconfigured devices that are critical for maximizing the size and impact of DDoS attacks. What’s more, none of the services seized by the government required users to demonstrate that they own the Internet addresses being stress-tested, something a legitimate testing service would insist upon.
This is the third in a series of U.S. and international law enforcement actions targeting booter services. In December 2022, the feds seized four-dozen booter domains and charged six U.S. men with computer crimes related to their alleged ownership of the popular DDoS-for-hire services. In December 2018, the feds targeted 15 booter sites, and three booter store defendants who later pleaded guilty.
While the FBI’s repeated seizing of booter domains may seem like an endless game of virtual Whac-a-Mole, continuously taking these services offline imposes high enough costs for the operators that some of them will quit the business altogether, says Richard Clayton, director of Cambridge University’s Cybercrime Centre.
In 2020, Clayton and others published “Cybercrime is Mostly Boring,” an academic study on the quality and types of work needed to build, maintain and defend illicit enterprises that make up a large portion of the cybercrime-as-a-service market. The study found that operating a booter service effectively requires a mind-numbing amount of constant, tedious work that tends to produce high burnout rates for booter service operators — even when the service is operating efficiently and profitably.
For example, running an effective booter service requires a substantial amount of administrative work and maintenance, much of which involves constantly scanning for, commandeering and managing large collections of remote systems that can be used to amplify online attacks, Clayton said. On top of that, building brand recognition and customer loyalty takes time.
“If you’re running a booter and someone keeps taking your domain or hosting away, you have to then go through doing the same boring work all over again,” Clayton told KrebsOnSecurity. “One of the guys the FBI arrested in December [2022] spent six months moaning that he lost his servers, and could people please lend him some money to get it started again.”
In a statement released Wednesday, prosecutors in Los Angeles said four of the six men charged last year for running booter services have since pleaded guilty. However, at least one of the defendants from the 2022 booter bust-up — John M. Dobbs, 32, of Honolulu, HI — has pleaded not guilty and is signaling he intends to take his case to trial.

The FBI seizure notice that replaced the homepages of several booter services this week.
Dobbs is a computer science graduate student who for the past decade openly ran IPStresser[.]com, a popular and powerful attack-for-hire service that he registered with the state of Hawaii using his real name and address. Likewise, the domain was registered in Dobbs’s name and hometown in Pennsylvania. Prosecutors say Dobbs’ service attracted more than two million registered users, and was responsible for launching a staggering 30 million distinct DDoS attacks.
Many accused stresser site operators have pleaded guilty over the years after being hit with federal criminal charges. But the government’s core claim — that operating a booter site is a violation of U.S. computer crime laws — wasn’t properly tested in the courts until September 2021.
That was when a jury handed down a guilty verdict against Matthew Gatrel, a then 32-year-old St. Charles, Ill. man charged in the government’s first 2018 mass booter bust-up. Despite admitting to FBI agents that he ran two booter services (and turning over plenty of incriminating evidence in the process), Gatrel opted to take his case to trial, defended the entire time by court-appointed attorneys.
Gatrel was convicted on all three charges of violating the Computer Fraud and Abuse Act, including conspiracy to commit unauthorized impairment of a protected computer, conspiracy to commit wire fraud, and unauthorized impairment of a protected computer. He was sentenced to two years in prison.
A copy of the FBI’s booter seizure warrant is here (PDF). According to the DOJ, the defendants who pleaded guilty to operating booter sites include:
–Jeremiah Sam Evans Miller, aka “John The Dev,” 23, of San Antonio, Texas, who pleaded guilty on April 6 to conspiracy and violating the computer fraud and abuse act related to the operation of a booter service named RoyalStresser[.]com (formerly known as Supremesecurityteam[.]com);
–Angel Manuel Colon Jr., aka “Anonghost720” and “Anonghost1337,” 37, of Belleview, Florida, who pleaded guilty on February 13 to conspiracy and violating the computer fraud and abuse act related to the operation of a booter service named SecurityTeam[.]io;
–Shamar Shattock, 19, of Margate, Florida, who pleaded guilty on March 22 to conspiracy to violate the computer fraud and abuse act related to the operation of a booter service known as Astrostress[.]com;
–Cory Anthony Palmer, 23, of Lauderhill, Florida, who pleaded guilty on February 16 to conspiracy to violate the computer fraud and abuse act related to the operation of a booter service known as Booter[.]sx.
All four defendants are scheduled to be sentenced this summer.
The booter domains seized by the FBI this week include:
cyberstress[.]org
exoticbooter[.]com
layerstress[.]net
orbitalstress[.]xyz
redstresser[.]io
silentstress[.]wtf
sunstresser[.]net
silent[.]to
mythicalstress[.]net
dreams-stresser[.]org
stresserbest[.]io
stresserus[.]io
quantum-stress[.]org
The U.S. government this week put a $10 million bounty on a Russian man who for the past 18 years operated Try2Check, one of the cybercrime underground’s most trusted services for checking the validity of stolen credit card data. U.S. authorities say 43-year-old Denis Kulkov‘s card-checking service made him at least $18 million, which he used to buy a Ferrari, Land Rover, and other luxury items.

Denis Kulkov, a.k.a. “Nordex,” in his Ferrari. Image: USDOJ.
Launched in 2005, Try2Check soon was processing more than a million card-checking transactions per month — charging 20 cents per transaction. Cybercriminals turned to services like this after purchasing stolen credit card data from an underground shop, with an eye toward minimizing the number of cards that are inactive by the time they are put to criminal use.
Try2Check was so reliable that it eventually became the official card-checking service for some of the underground’s most bustling crime bazaars, including Vault Market, Unicc, and Joker’s Stash. Customers of these carding shops who chose to use the shop’s built-in (but a-la-carte) card checking service from Try2Check could expect automatic refunds on any cards that were found to be inactive or canceled at the time of purchase.
Many established stolen card shops will allow customers to request refunds on dead cards based on official reports from trusted third-party checking services. But in general, the bigger shops have steered customers toward using their own white-labeled version of the Try2Check service — primarily to help minimize disputes over canceled cards.
On Wednesday, May 3, Try2Check’s websites were replaced with a domain seizure notice from the U.S. Secret Service and U.S. Department of Justice, as prosecutors in the Eastern District of New York unsealed an indictment and search warrant naming Denis Gennadievich Kulkov of Samara, Russia as the proprietor.

Try2Check’s login pages have been replaced with a seizure notice from U.S. law enforcement.
At the same time, the U.S. Department of State issued a $10 million reward for information leading to the arrest or conviction of Kulkov. In November 2021, the State Department began offering up to to $10 million for the name or location of any key leaders of REvil, a major Russian ransomware gang.
As noted in the Secret Service’s criminal complaint (PDF), the Try2Check service was first advertised on the closely-guarded Russian cybercrime forum Mazafaka, by someone using the handle “KreenJo.” That handle used the same ICQ instant messenger account number (555724) as a Mazafaka denizen named “Nordex.”
In February 2005, Nordex posted to Mazafaka that he was in the market for hacked bank accounts, and offered 50 percent of the take. He asked interested partners to contact him at the ICQ number 228427661 or at the email address polkas@bk.ru. As the government noted in its search warrant, Nordex exchanged messages with forum users at the time identifying himself as a then-24-year-old “Denis” from Samara, RU.
In 2017, U.S. law enforcement seized the cryptocurrency exchange BTC-e, and the Secret Service said those records show that a Denis Kulkov from Samara supplied the username “Nordexin,” email address nordexin@ya.ru, and an address in Samara.
Investigators had already found Instagram accounts where Kulkov posted pictures of his Ferrari and his family. Authorities were able to identify that Kulkov had an iCloud account tied to the address nordexin@icloud.com, and upon subpoenaing that found passport photos of Kulkov, and well as more photos of his family and pricey cars.
Like many other top cybercriminals based in Russia or in countries with favorable relations to the Kremlin, the proprietor of Try2Check was not particularly difficult to link to a real-life identity. In Kulkov’s case, it no doubt was critical to U.S. investigators that they had access to a wealth of personal information tied to a cryptocurrency exchange Kulkov had used.
However, the link between Kulkov and Try2Check can be made — ironically — based on records that have been plundered by hackers and published online over the years — including Russian email services, Russian government records, and hacked cybercrime forums.

Kulkov posing with his passport, in a photo authorities obtained by subpoenaing his iCloud account.
According to cybersecurity firm Constella Intelligence, the address polkas@bk.ru was used to register an account with the username “Nordex” at bankir[.]com, a now defunct news website that was almost standard reading for Russian speakers interested in news about various Russian financial markets.
Nordex appears to have been a finance nerd. In his early days on the forums, Nordex posted several long threads on his views about the Russian stock market and mutual fund investments.
That Bankir account was registered from the Internet address 193.27.237.66 in Samara, Russia, and included Nordex’s date of birth as April 8, 1980, as well as their ICQ number (228427661).
Cyber intelligence firm Intel 471 found that Internet address also was used to register the account “Nordex” on the Russian hacking forum Exploit back in 2006.
Constella tracked another Bankir[.]com account created from that same Internet address under the username “Polkas.” This account had the same date of birth as Nordex, but a different email address: nordia@yandex.ru. This and other “nordia@” emails shared a password: “anna59.”
Nordia@yandex.ru shares several passwords with nordia@list.ru, which Constella says was used to create an account at a religious website for an Anna Kulikova from Samara. At the Russian home furnishing store Westwing.ru, Ms. Kulikova listed her full name as Anna Vnrhoturkina Kulikova, and her address as 29 Kommunistrecheskya St., Apt. 110.
A search on that address in Constella brings up a record for an Anna Denis Vnrhoturkina Kulkov, and the phone number 879608229389.
Russian vehicle registration records have also been hacked and leaked online over the years. Those records show that Anna’s Apt 110 address is tied to a Denis Gennadyvich Kulkov, born April 8, 1980.
The vehicle Kolkov registered in 2015 at that address was a 2010 Ferrari Italia, with the license plate number K022YB190. The phone number associated with this record — 79608229389 — is exactly like Anna’s, only minus the (mis?)leading “8”. That number also is tied to a now-defunct Facebook account, and to the email addresses nordexin@ya.ru and nordexin@icloud.com.
Kulkov’s Ferrari has been photographed numerous times over the years by Russian car aficionados, including this one with the driver’s face redacted by the photographer:

The Ferrari owned by Denis Kulkov, spotted in Moscow in 2016. Image: Migalki.net.
As the title of this story suggests, the hard part for Western law enforcement isn’t identifying the Russian cybercriminals who are major players in the scene. Rather, it’s finding creative ways to capture high-value suspects if and when they do leave the protection that Russia generally extends to domestic cybercriminals within its borders who do not also harm Russian companies or consumers, or interfere with state interests.
But Russia’s war against Ukraine has caused major fault lines to appear in the cybercrime underground: Cybercriminal syndicates that previously straddled Russia and Ukraine with ease were forced to reevaluate many comrades who were suddenly working for The Other Side.
Many cybercriminals who operated with impunity from Russia and Ukraine prior to the war chose to flee those countries following the invasion, presenting international law enforcement agencies with rare opportunities to catch most-wanted cybercrooks. One of those was Mark Sokolovsky, a 26-year-old Ukrainian man who operated the popular “Raccoon” malware-as-a-service offering; Sokolovsky was apprehended in March 2022 after fleeing Ukraine’s mandatory military service orders.
Also nabbed on the lam last year was Vyacheslav “Tank” Penchukov, a senior Ukrainian member of a transnational cybercrime group that stole tens of millions of dollars over nearly a decade from countless hacked businesses. Penchukov was arrested after leaving Ukraine to meet up with his wife in Switzerland.
A sprawling online company based in Georgia that has made tens of millions of dollars purporting to sell access to jobs at the United States Postal Service (USPS) has exposed its internal IT operations and database of nearly 900,000 customers. The leaked records indicate the network’s chief technology officer in Pakistan has been hacked for the past year, and that the entire operation was created by the principals of a Tennessee-based telemarketing firm that has promoted USPS employment websites since 2016.
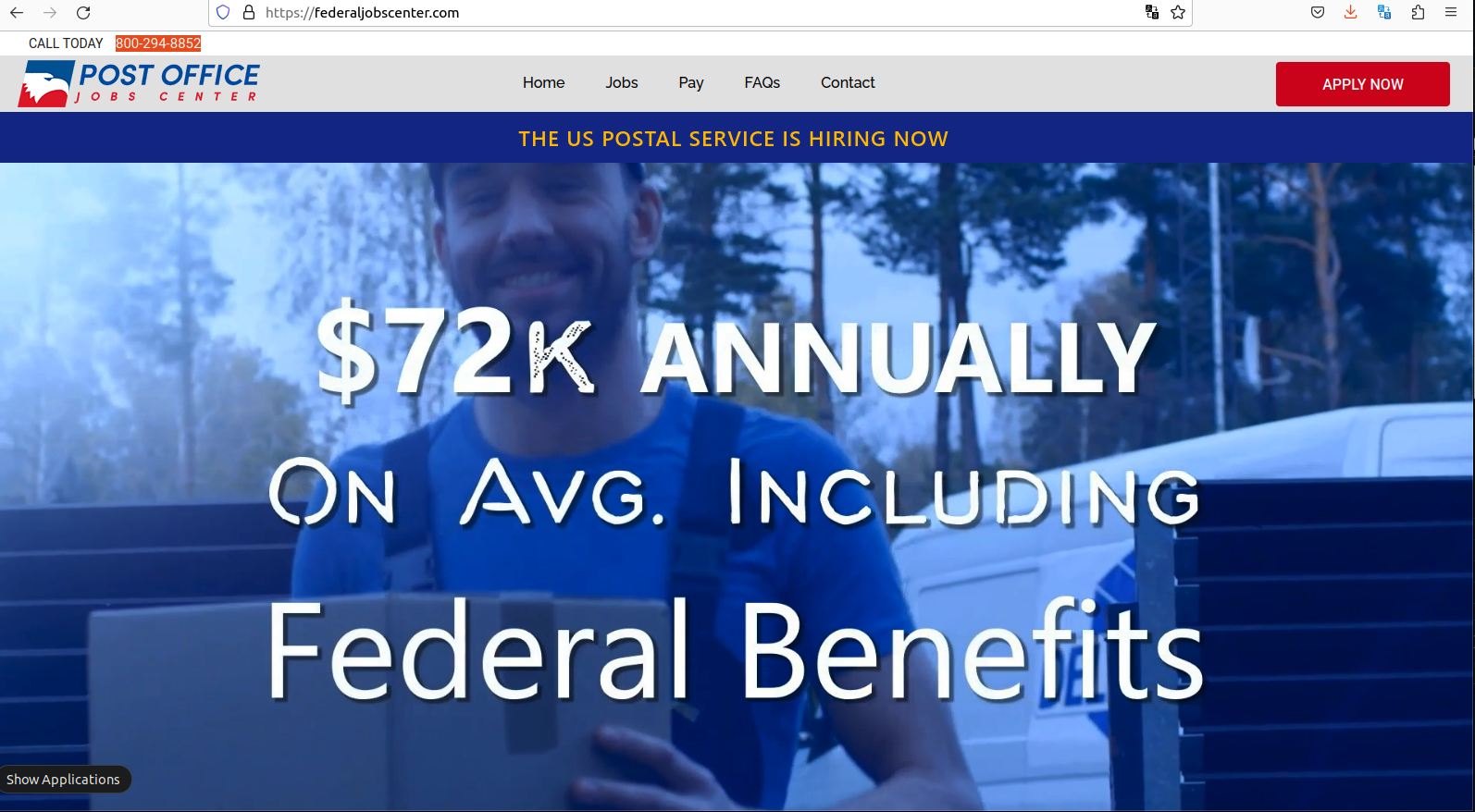
The website FederalJobsCenter promises to get you a job at the USPS in 30 days or your money back.
KrebsOnSecurity was recently contacted by a security researcher who said he found a huge tranche of full credit card records exposed online, and that at first glance the domain names involved appeared to be affiliated with the USPS.
Further investigation revealed a long-running international operation that has been emailing and text messaging people for years to sign up at a slew of websites that all promise they can help visitors secure employment at the USPS.
Sites like FederalJobsCenter[.]com also show up prominently in Google search results for USPS employment, and steer applicants toward making credit card “registration deposits” to ensure that one’s application for employment is reviewed. These sites also sell training, supposedly to help ace an interview with USPS human resources.
FederalJobsCenter’s website is full of content that makes it appear the site is affiliated with the USPS, although its “terms and conditions” state that it is not. Rather, the terms state that FederalJobsCenter is affiliated with an entity called US Job Services, which says it is based in Lawrenceville, Ga.
“US Job Services provides guidance, coaching, and live assistance to postal job candidates to help them perform better in each of the steps,” the website explains.
The site says applicants need to make a credit card deposit to register, and that this amount is refundable if the applicant is not offered a USPS job within 30 days after the interview process.
But a review of the public feedback on US Job Services and dozens of similar names connected to this entity over the years shows a pattern of activity: Applicants pay between $39.99 and $100 for USPS job coaching services, and receive little if anything in return. Some reported being charged the same amount monthly.
The U.S. Federal Trade Commission (FTC) has sued several times over the years to disrupt various schemes offering to help people get jobs at the Postal Service. Way back in 1998, the FTC and the USPS took action against several organizations that were selling test or interview preparation services for potential USPS employees.
“Companies promising jobs with the U.S. Postal Service are breaking federal law,” the joint USPS-FTC statement said.
In that 1998 case, the defendants behind the scheme were taking out classified ads in newspapers. Ditto for a case the FTC brought in 2005. By 2008, the USPS job exam preppers had shifted to advertising their schemes mostly online. And in 2013, the FTC won a nearly $5 million judgment against a Kentucky company purporting to offer such services.
Tim McKinlay authored a report last year at Affiliateunguru.com on whether the US Job Services website job-postal[.]com was legitimate or a scam. He concluded it was a scam based on several factors, including that the website listed multiple other names (suggesting it had recently switched names), and that he got nothing from the transaction with the job site.
“They openly admit they’re not affiliated with the US Postal Service, but claim to be experts in the field, and that, just by following the steps on their site, you easily pass the postal exams and get a job in no time,” McKinlay wrote. “But it’s really just a smoke and mirrors game. The site’s true purpose is to collect $46.95 from as many people as possible. And considering how popular this job is, they’re probably making a killing.”
KrebsOnSecurity was alerted to the data exposure by Patrick Barry, chief information officer at Charlotte, NC based Rebyc Security. Barry said he found that not only was US Job Services leaking its customer payment records in real-time and going back to 2016, but its website also leaked a log file from 2019 containing the site administrator’s contact information and credentials to the site’s back-end database.
Barry shared screenshots of that back-end database, which show the email address for the administrator of US Job Services is tab.webcoder@gmail.com. According to cyber intelligence platform Constella Intelligence, that email address is tied to the LinkedIn profile for a developer in Karachi, Pakistan named Muhammed Tabish Mirza.
A search on tab.webcoder@gmail.com at DomainTools.com reveals that email address was used to register several USPS-themed domains, including postal2017[.]com, postaljobscenter[.]com and usps-jobs[.]com.
Mr. Mirza declined to respond to questions, but the exposed database information was removed from the Internet almost immediately after KrebsOnSecurity shared the offending links.
A “Campaigns” tab on that web panel listed several advertising initiatives tied to US Job Services websites, with names like “walmart drip campaign,” “hiring activity due to virus,” “opt-in job alert SMS,” and “postal job opening.”
Another page on the US Job Services panel included a script for upselling people who call in response to email and text message solicitations, with an add-on program that normally sells for $1,200 but is being “practically given away” for a limited time, for just $49.
“There’s something else we have you can take advantage of that can help you make more money,” the script volunteers. “It’s an easy to use 12-month career development plan and program to follow that will result in you getting any job you want, not just at the post office….anywhere…and then getting promoted rapidly.”
It’s bad enough that US Job Services was leaking customer data: Constella Intelligence says the email address tied to Mr. Mirza shows up in more than a year’s worth of “bot logs” created by a malware infection from the Redline infostealer.
Constella reports that for roughly a year between 2021 and 2022, a Microsoft Windows device regularly used by Mr. Mirza and his colleagues was actively uploading all of the device’s usernames, passwords and authentication cookies to cybercriminals based in Russia.
The web-based backend for US Job Services lists more than 160 people under its “Users & Teams” tab. This page indicates that access to the consumer and payment data collected by US Job Services is currently granted to several other coders who work with Mr. Mirza in Pakistan, and to multiple executives, contractors and employees working for a call center in Murfreesboro, Tennessee.
The call center — which operates as Nextlevelsupportcenters[.]com and thenextlevelsupport[.]com — curiously has several key associates with a history of registering USPS jobs-related domain names.
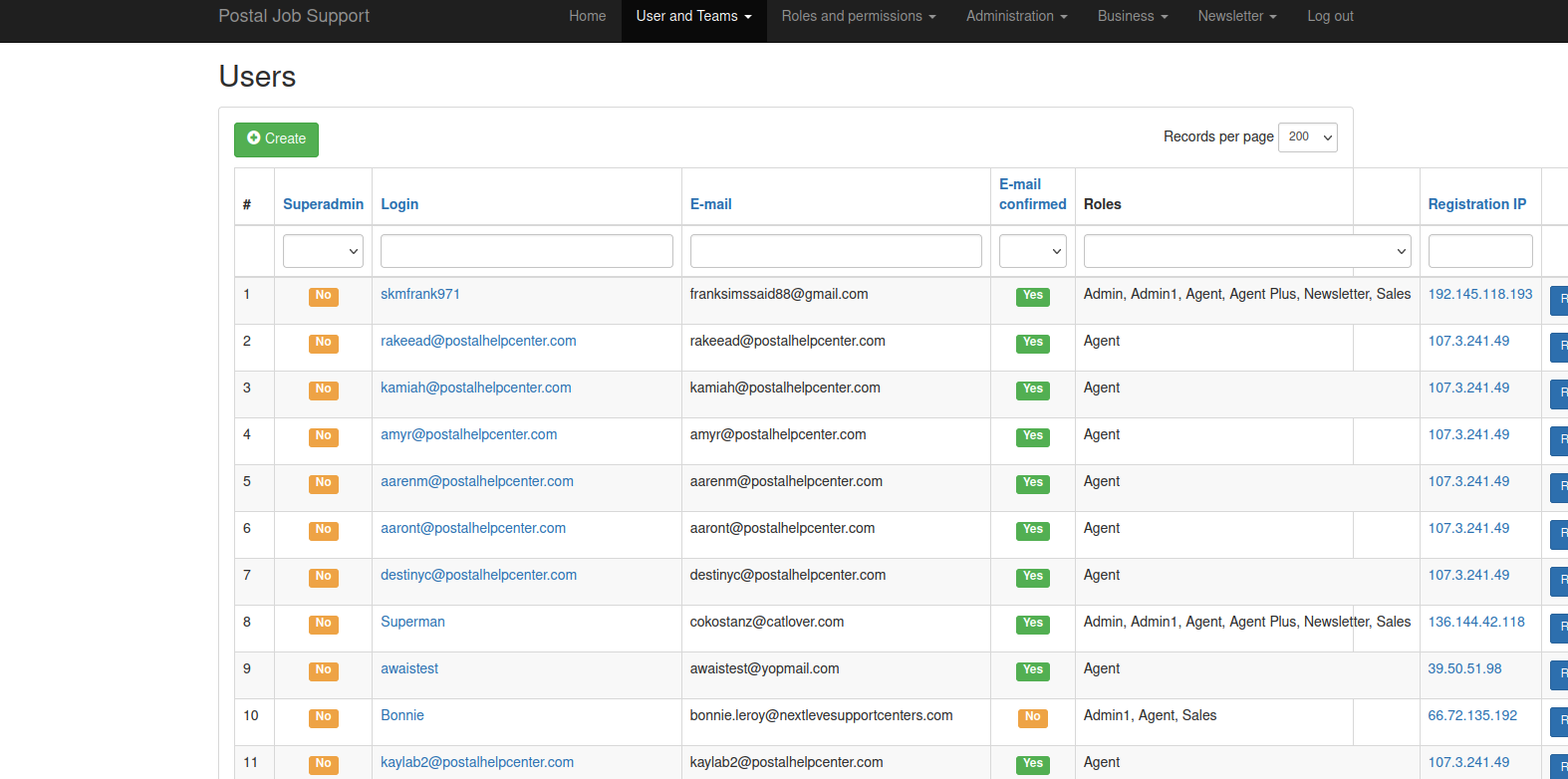
The US Job Services website has more than 160 users, including most of the employees at Next Level Support.
The website for NextLevelSupport says it was founded in 2017 by a Gary Plott, whose LinkedIn profile describes him as a seasoned telecommunications industry expert. The leaked backend database for US Job Services says Plott is a current administrator on the system, along with several other Nextlevel founders listed on the company’s site.
Reached via telephone, Plott initially said his company was merely a “white label” call center that multiple clients use to interact with customers, and that the content their call center is responsible for selling on behalf of US Job Services was not produced by NextLevelSupport.
“A few years ago, we started providing support for this postal product,” Plott said. “We didn’t develop the content but agreed we would support it.”
Interestingly, DomainTools says the Gmail address used by Plott in the US Jobs system was also used to register multiple USPS job-related domains, including postaljobssite[.]com, postalwebsite[.]com, usps-nlf[.]com, usps-nla[.]com.
Asked to reconcile this with his previous statement, Plott said he never did anything with those sites but acknowledged that his company did decide to focus on the US Postal jobs market from the very beginning.
Plott said his company never refuses to issue a money-back request from a customer, because doing so would result in costly chargebacks for NextLevel (and presumably for the many credit card merchant accounts apparently set up by Mr. Mirza).
“We’ve never been deceptive,” Plott said, noting that customers of the US Job Services product receive a digital download with tips on how to handle a USPS interview, as well as unlimited free telephone support if they need it.
“We’ve never told anyone we were the US Postal Service,” Plott continued. “We make sure people fully understand that they are not required to buy this product, but we think we can help you and we have testimonials from people we have helped. But ultimately you as the customer make that decision.”
An email address in the US Job Services teams page for another user — Stephanie Dayton — was used to register the domains postalhiringreview[.]com, and postalhiringreviewboard[.]org back in 2014. Reached for comment, Ms. Dayton said she has provided assistance to Next Level Support Centers with their training and advertising, but never in the capacity as an employee.
Perhaps the most central NextLevel associate who had access to US Job Services was Russell Ramage, a telemarketer from Warner Robins, Georgia. Ramage is listed in South Carolina incorporation records as the owner of a now-defunct call center service called Smart Logistics, a company whose name appears in the website registration records for several early and long-running US Job Services sites.

According to the state of Georgia, Russell Ramage was the registered agent of several USPS job-themed companies.
The leaked records show the email address used by Ramage also registered multiple USPS jobs-related domains, including postalhiringcenter[.]com, postalhiringreviews[.]com, postaljobs-email[.]com, and postaljobssupport1[.]com.
A review of business incorporation records in Georgia indicate Ramage was the registered agent for at least three USPS-related companies over the years, including Postal Career Placement LLC, Postal Job Services Inc., and Postal Operations Inc. All three companies were founded in 2015, and are now dissolved.
An obituary dated February 2023 says Russell Ramage recently passed away at the age of 41. No cause of death was stated, but the obituary goes on to say that Russ “Rusty” Ramage was “preceded in death by his mother, Anita Lord Ramage, pets, Raine and Nola and close friends, Nicole Reeves and Ryan Rawls.”
In 2014, then 33-year-old Ryan “Jootgater” Rawls of Alpharetta, Georgia pleaded guilty to conspiring to distribute controlled substances. Rawls also grew up in Warner Robins, and was one of eight suspects charged with operating a secret darknet narcotics ring called the Farmer’s Market, which federal prosecutors said trafficked in millions of dollars worth of controlled substances.
Reuters reported that an eighth suspect in that case had died by the time of Rawls’ 2014 guilty plea, although prosecutors declined to offer further details about that. According to his obituary, Ryan Christopher Rawls died at the age of 38 on Jan. 28, 2019.
In a comment on Ramage’s memorial wall, Stephanie Dayton said she began working with Ramage in 2006.
“Our friendship far surpassed a working one, we had a very close bond and became like brother and sister,” Dayton wrote. “I loved Russ deeply and he was like family. He was truly one of the best human beings I have ever known. He was kind and sweet and truly cared about others. Never met anyone like him. He will be truly missed. RIP brother.”
The FTC and USPS note that while applicants for many entry-level postal jobs are required to take a free postal exam, the tests are usually offered only every few years in any particular district, and there are no job placement guarantees based on score.
“If applicants pass the test by scoring at least 70 out of 100, they are placed on a register, ranked by their score,” the FTC explained. “When a position becomes open, the local post office looks to the applicable register for that geographic location and calls the top three applicants. The score is only one of many criteria taken into account for employment. The exams test general aptitude, something that cannot necessarily be increased by studying.”
The FTC says anyone interested in a job at the USPS should inquire at their local postal office, where applicants generally receive a free packet of information about required exams. More information about job opportunities at the postal service is available at the USPS’s careers website.
Michael Martel, spokesperson for the United States Postal Inspection Service, said in a written statement that the USPS has no affiliation with the websites or companies named in this story.
“To learn more about employment with USPS, visit USPS.com/careers,” Martel wrote. “If you are the victim of a crime online report it to the FBI’s Internet Crime Complaint Center (IC3) at www.ic3.gov. To report fraud committed through or toward the USPS, its employees, or customers, report it to the United States Postal Inspection Service (USPIS) at www.uspis.gov/report.”
According to the leaked back-end server for US Job Services, here is a list of the current sites selling this product:
usjobshelpcenter[.]com
usjobhelpcenter[.]com
job-postal[.]com
localpostalhiring[.]com
uspostalrecruitment[.]com
postalworkerjob[.]com
next-level-now[.]com
postalhiringcenters[.]com
postofficehiring[.]com
postaljobsplacement[.]com
postal-placement[.]com
postofficejobopenings[.]com
postalexamprep[.]com
postaljobssite[.]com
postalwebsite[.]com
postalcareerscenters[.]com
postal-hiring[.]com
postal-careers[.]com
postal-guide[.]com
postal-hiring-guide[.]com
postal-openings[.]com
postal-placement[.]com
postofficeplacements[.]com
postalplacementservices[.]com
postaljobs20[.]com
postal-jobs-placement[.]com
postaljobopenings[.]com
postalemployment[.]com
postaljobcenters[.]com
postalmilitarycareers[.]com
epostaljobs[.]com
postal-job-center[.]com
postalcareercenter[.]com
postalhiringcenters[.]com
postal-job-center[.]com
postalcareercenter[.]com
postalexamprep[.]com
postalplacementcenters[.]com
postalplacementservice[.]com
postalemploymentservices[.]com
uspostalhiring[.]com
A shocking number of organizations — including banks and healthcare providers — are leaking private and sensitive information from their public Salesforce Community websites, KrebsOnSecurity has learned. The data exposures all stem from a misconfiguration in Salesforce Community that allows an unauthenticated user to access records that should only be available after logging in.
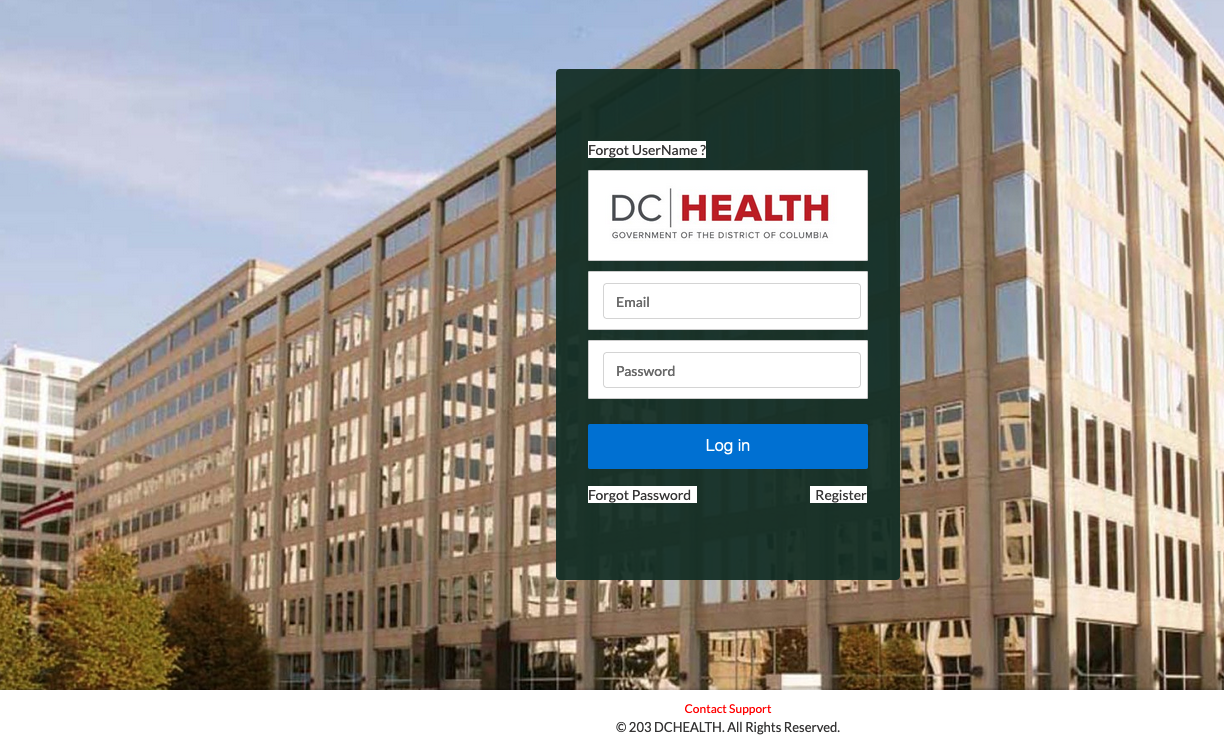
A researcher found DC Health had five Salesforce Community sites exposing data.
Salesforce Community is a widely-used cloud-based software product that makes it easy for organizations to quickly create websites. Customers can access a Salesforce Community website in two ways: Authenticated access (requiring login), and guest user access (no login required). The guest access feature allows unauthenticated users to view specific content and resources without needing to log in.
However, sometimes Salesforce administrators mistakenly grant guest users access to internal resources, which can cause unauthorized users to access an organization’s private information and lead to potential data leaks.
Until being contacted by this reporter on Monday, the state of Vermont had at least five separate Salesforce Community sites that allowed guest access to sensitive data, including a Pandemic Unemployment Assistance program that exposed the applicant’s full name, Social Security number, address, phone number, email, and bank account number.
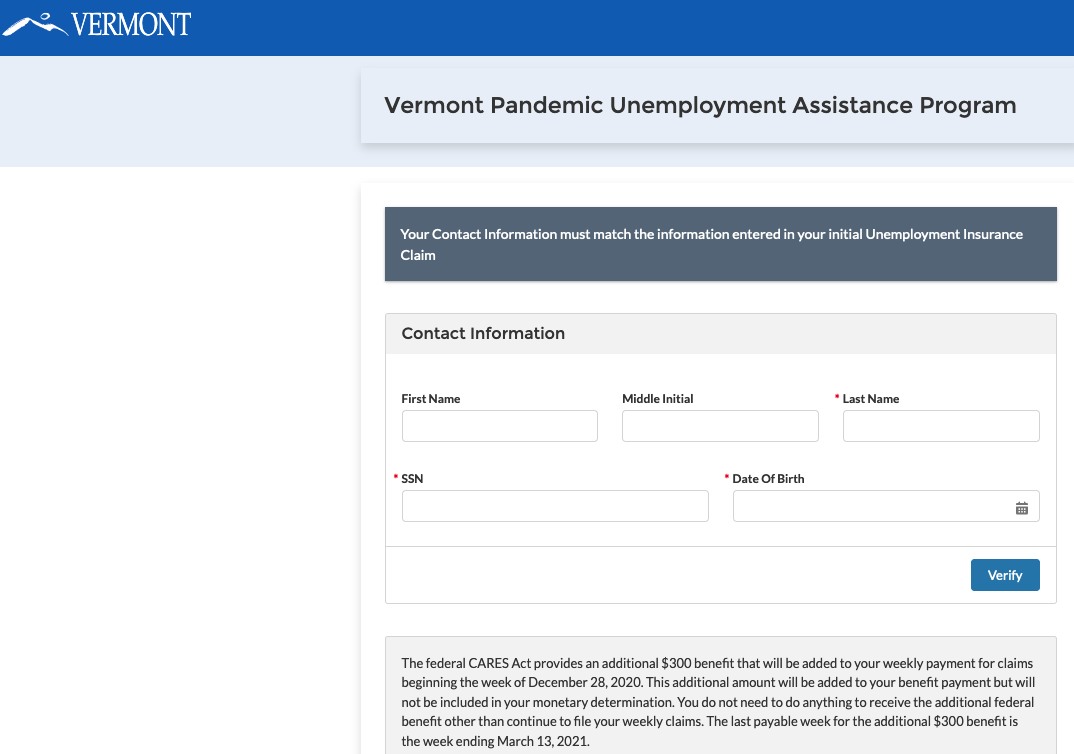
This misconfigured Salesforce Community site from the state of Vermont was leaking pandemic assistance loan application data, including names, SSNs, email address and bank account information.
Vermont’s Chief Information Security Officer Scott Carbee said his security teams have been conducting a full review of their Salesforce Community sites, and already found one additional Salesforce site operated by the state that was also misconfigured to allow guest access to sensitive information.
“My team is frustrated by the permissive nature of the platform,” Carbee said.
Carbee said the vulnerable sites were all created rapidly in response to the Coronavirus pandemic, and were not subjected to their normal security review process.
“During the pandemic, we were largely standing up tons of applications, and let’s just say a lot of them didn’t have the full benefit of our dev/ops process,” Carbee said. “In our case, we didn’t have any native Salesforce developers when we had to suddenly stand up all these sites.”
Earlier this week, KrebsOnSecurity notified Columbus, Ohio-based Huntington Bank that its recently acquired TCF Bank had a Salesforce Community website that was leaking documents related to commercial loans. The data fields in those loan applications included name, address, full Social Security number, title, federal ID, IP address, average monthly payroll, and loan amount.
Huntington Bank has disabled the leaky TCF Bank Salesforce website. Matthew Jennings, deputy chief information security officer at Huntington, said the company was still investigating how the misconfiguration occurred, how long it lasted, and how many records may have been exposed.
KrebsOnSecurity learned of the leaks from security researcher Charan Akiri, who said he wrote a program that identified hundreds of other organizations running misconfigured Salesforce pages. But Akiri said he’s been wary of probing too far, and has had difficulty getting responses from most of the organizations he has notified to date.
“In January and February 2023, I contacted government organizations and several companies, but I did not receive any response from these organizations,” Akiri said. “To address the issue further, I reached out to several CISOs on LinkedIn and Twitter. As a result, five companies eventually fixed the problem. Unfortunately, I did not receive any responses from government organizations.”
The problem Akiri has been trying to raise awareness about came to the fore in August 2021, when security researcher Aaron Costello published a blog post explaining how misconfigurations in Salesforce Community sites could be exploited to reveal sensitive data (Costello subsequently published a follow-up post detailing how to lock down Salesforce Community sites).
On Monday, KrebsOnSecurity used Akiri’s findings to notify Washington D.C. city administrators that at least five different public DC Health websites were leaking sensitive information. One DC Health Salesforce Community website designed for health professionals seeking to renew licenses with the city leaked documents that included the applicant’s full name, address, Social Security number, date of birth, license number and expiration, and more.
Akiri said he notified the Washington D.C. government in February about his findings, but received no response. Reached by KrebsOnSecurity, interim Chief Information Security Officer Mike Rupert initially said the District had hired a third party to investigate, and that the third party confirmed the District’s IT systems were not vulnerable to data loss from the reported Salesforce configuration issue.
But after being presented with a document including the Social Security number of a health professional in D.C. that was downloaded in real-time from the DC Health public Salesforce website, Rupert acknowledged his team had overlooked some configuration settings.
Washington, D.C. health administrators are still smarting from a data breach earlier this year at the health insurance exchange DC Health Link, which exposed personal information for more than 56,000 users, including many members of Congress.
That data later wound up for sale on a top cybercrime forum. The Associated Press reports that the DC Health Link breach was likewise the result of human error, and said an investigation revealed the cause was a DC Health Link server that was “misconfigured to allow access to the reports on the server without proper authentication.”
Salesforce says the data exposures are not the result of a vulnerability inherent to the Salesforce platform, but they can occur when customers’ access control permissions are misconfigured.
“As previously communicated to all Experience Site and Sites customers, we recommend utilizing the Guest User Access Report Package to assist in reviewing access control permissions for unauthenticated users,” reads a Salesforce advisory from Sept. 2022. “Additionally, we suggest reviewing the following Help article, Best Practices and Considerations When Configuring the Guest User Profile.”
In a written statement, Salesforce said it is actively focused on data security for organizations with guest users, and that it continues to release “robust tools and guidance for our customers,” including:
Control Which Users Experience Cloud Site Users Can See
Best Practices and Considerations When Configuring the Guest User Profile
“We’ve also continued to update our Guest User security policies, beginning with our Spring ‘21 release with more to come in Summer ‘23,” the statement reads. “Lastly, we continue to proactively communicate with customers to help them understand the capabilities available to them, and how they can best secure their instance of Salesforce to meet their security, contractual, and regulatory obligations.”
We learned some remarkable new details this week about the recent supply-chain attack on VoIP software provider 3CX. The lengthy, complex intrusion has all the makings of a cyberpunk spy novel: North Korean hackers using legions of fake executive accounts on LinkedIn to lure people into opening malware disguised as a job offer; malware targeting Mac and Linux users working at defense and cryptocurrency firms; and software supply-chain attacks nested within earlier supply chain attacks.
Researchers at ESET say this job offer from a phony HSBC recruiter on LinkedIn was North Korean malware masquerading as a PDF file.
In late March 2023, 3CX disclosed that its desktop applications for both Windows and macOS were compromised with malicious code that gave attackers the ability to download and run code on all machines where the app was installed. 3CX says it has more than 600,000 customers and 12 million users in a broad range of industries, including aerospace, healthcare and hospitality.
3CX hired incident response firm Mandiant, which released a report on Wednesday that said the compromise began in 2022 when a 3CX employee installed a malware-laced software package distributed via an earlier software supply chain compromise that began with a tampered installer for X_TRADER, a software package provided by Trading Technologies.
“This is the first time Mandiant has seen a software supply chain attack lead to another software supply chain attack,” reads the April 20 Mandiant report.
Mandiant found the earliest evidence of compromise uncovered within 3CX’s network was through the VPN using the employee’s corporate credentials, two days after the employee’s personal computer was compromised.
“Eventually, the threat actor was able to compromise both the Windows and macOS build environments,” 3CX said in an April 20 update on their blog.
Mandiant concluded that the 3CX attack was orchestrated by the North Korean state-sponsored hacking group known as Lazarus, a determination that was independently reached earlier by researchers at Kaspersky Lab and Elastic Security.
Mandiant found the compromised 3CX software would download malware that sought out new instructions by consulting encrypted icon files hosted on GitHub. The decrypted icon files revealed the location of the malware’s control server, which was then queried for a third stage of the malware compromise — a password stealing program dubbed ICONICSTEALER.
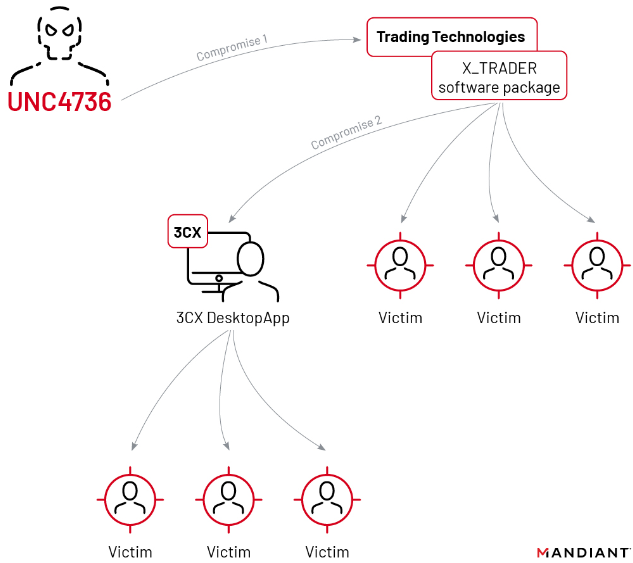
The double supply chain compromise that led to malware being pushed out to some 3CX customers. Image: Mandiant.
Meanwhile, the security firm ESET today published research showing remarkable similarities between the malware used in the 3CX supply chain attack and Linux-based malware that was recently deployed via fake job offers from phony executive profiles on LinkedIn. The researchers said this was the first time Lazarus had been spotted deploying malware aimed at Linux users.
As reported in a series last summer here, LinkedIn has been inundated this past year by fake executive profiles for people supposedly employed at a range of technology, defense, energy and financial companies. In many cases, the phony profiles spoofed chief information security officers at major corporations, and some attracted quite a few connections before their accounts were terminated.
Mandiant, Proofpoint and other experts say Lazarus has long used these bogus LinkedIn profiles to lure targets into opening a malware-laced document that is often disguised as a job offer. This ongoing North Korean espionage campaign using LinkedIn was first documented in August 2020 by ClearSky Security, which said the Lazarus group operates dozens of researchers and intelligence personnel to maintain the campaign globally.
Microsoft Corp., which owns LinkedIn, said in September 2022 that it had detected a wide range of social engineering campaigns using a proliferation of phony LinkedIn accounts. Microsoft said the accounts were used to impersonate recruiters at technology, defense and media companies, and to entice people into opening a malicious file. Microsoft found the attackers often disguised their malware as legitimate open-source software like Sumatra PDF and the SSH client Putty.
Microsoft attributed those attacks to North Korea’s Lazarus hacking group, although they’ve traditionally referred to this group as “ZINC“. That is, until earlier this month, when Redmond completely revamped the way it names threat groups; Microsoft now references ZINC as “Diamond Sleet.”
The ESET researchers said they found a new fake job lure tied to an ongoing Lazarus campaign on LinkedIn designed to compromise Linux operating systems. The malware was found inside of a document that offered an employment contract at the multinational bank HSBC.
“A few weeks ago, a native Linux payload was found on VirusTotal with an HSBC-themed PDF lure,” wrote ESET researchers Peter Kalnai and Marc-Etienne M.Leveille. “This completes Lazarus’s ability to target all major desktop operating systems. In this case, we were able to reconstruct the full chain, from the ZIP file that delivers a fake HSBC job offer as a decoy, up until the final payload.”
ESET said the malicious PDF file used in the scheme appeared to have a file extension of “.pdf,” but that this was a ruse. ESET discovered that the dot in the filename wasn’t a normal period but instead a Unicode character (U+2024) representing a “leader dot,” which is often used in tables of contents to connect section headings with the page numbers on which those sections begin.
“The use of the leader dot in the filename was probably an attempt to trick the file manager into treating the file as an executable instead of a PDF,” the researchers continued. “This could cause the file to run when double-clicked instead of opening it with a PDF viewer.”
ESET said anyone who opened the file would see a decoy PDF with a job offer from HSBC, but in the background the executable file would download additional malware payloads. The ESET team also found the malware was able to manipulate the program icon displayed by the malicious PDF, possibly because fiddling with the file extension could cause the user’s system to display a blank icon for the malware lure.
Kim Zetter, a veteran Wired.com reporter and now independent security journalist, interviewed Mandiant researchers who said they expect “many more victims” will be discovered among the customers of Trading Technologies and 3CX now that news of the compromised software programs is public.
“Mandiant informed Trading Technologies on April 11 that its X_Trader software had been compromised, but the software maker says it has not had time to investigate and verify Mandiant’s assertions,” Zetter wrote in her Zero Day newsletter on Substack. For now, it remains unclear whether the compromised X_Trader software was downloaded by people at other software firms.
If there’s a silver lining here, the X_Trader software had been decommissioned in April 2020 — two years before the hackers allegedly embedded malware in it.
“The company hadn’t released new versions of the software since that time and had stopped providing support for the product, making it a less-than-ideal vector for the North Korean hackers to infect customers,” Zetter wrote.