
Authored by Dennis Pang
Online protection software. Antivirus. The two words get used interchangeably often enough. But sure enough, they’re different. And yet directly related when you take a closer look.
The term “antivirus” has been with us for decades now, dating back to the first software that was designed to prevent computers from getting malware—malicious code, like viruses, that would lock up computers, scramble data, or otherwise damage computers and the data on them. Prime examples of these early types of malware include 1999’s “Melissa” virus spreads by infected email attachments and the even more devastating “ILOVEYOU” virus that incurred billions in damages worldwide.
There’s a good reason why people default to the word “antivirus” so easily. Viruses have been on our collective minds for some time. And computer purchases have often been accompanied by the question, “Do you have antivirus for your computer?” By and large, the notion of antivirus has become pretty much engrained.
Yet look ahead to today and you can see how dramatically things have changed since those early days. We still need antivirus, that’s for sure. But it takes far more than that to live life safely online right now. And that’s where online protection software comes in.
Online protection software protects you. It includes antivirus, yet it further protects your identity and privacy in addition to your devices.
The way we use our computers, tablets, and phones nowadays shows the reason why we need such broad protection. We conduct so much of our lives online. We bank, we shop, we plan our finance online. We also run portions of our homes with smart devices and smart speakers. Increasingly, we track our health and wellness with connected devices too—like workouts on our phone and biometrics with consumer-grade and even medical-grade devices.
All of this creates data. Data about who we are, what we’re doing, when we’re doing it, how often, and where. That’s precious information. Private information. Personal information. And understandably, that needs to be protected.
Put simply, today’s threats have evolved. While viruses and malware remain a problem, today’s bad actors are out for the bigger games. Like stealing personal and financial info for identity theft. Moreover, organizations large and small collect data from your devices and the things you do on them, personal data that many share and sell for profit. Some of this data collection gets quite exacting, compiled from a broad range of public sources that can include records like bankruptcies, real estate sales, and birth records—plus private sources that can further include your shopping habits, the people you chat with, and what your daily travels look like based on location information captured from your smartphone.
If you find yourself surprised by this, you’re not alone. Tremendous volumes of data collection activity occur without people’s knowledge or consent.
Now as to why anyone would want any of that kind of data about you, consider the multi-billion-dollar industry of online data brokers. They compile thousands of data points from millions of people and put these vats of data up for sale to anyone who’ll buy them. That could be advertisers, potential employers, private investigators, and background checkers. And it could be bad actors as well who could use your own data to spam, harass, impersonate, or otherwise harm you.
Once, so many of these intrusions on our privacy and identity were difficult to spot, let alone prevent. For example, your personal info gets caught up in a data breach and winds up posted for sale on the dark web. How are you to know that before it’s too late and thief racks up umpteen charges on your debit card? Also, with dozens and dozens of data brokers out there, how do you track down which ones have information posted about you and then request to have it taken down? And what if online identity theft happens to you and you’re faced with the time and dollar costs it involves to set things right?
So just as online threats have evolved, so has online protection software. We go about so much of our day online, and online protection like our own McAfee+ helps you do it more privately and more safely. It’s quite comprehensive, and the various plans for McAfee+ include:
For certain, protections like these remain a primary focus of ours, because they protect you. And that’s who thieves and bad actors are really after—you, your information, your accounts, and even your identity. Expect us to continue to roll out more protections that look after you in this way and more.
So, while antivirus and online protection software are different, they work together. Antivirus provides strong device security, which complements the additional privacy and identity features included with online protection. That reflects how times have changed. Once it was enough to protect our devices from viruses and malware. Now we have to protect ourselves as well. Antivirus alone won’t do it, but antivirus as part of online protection will.
The post The Big Difference Between Online Protection Software and Antivirus appeared first on McAfee Blog.

Authored by Dennis Pang
What is antivirus? That’s a good question. What does it really protect? That’s an even better question.
Over the years, I’ve come to recognize that different people define antivirus differently. Some see it as way to keep hackers from crashing their computers. Others see it as a comprehensive set of protections. Neither definition is entirely on the money.
With this blog, I hope to give everyone a clear definition of what antivirus does well, along with what it doesn’t do at all. The fact is that antivirus is just one form of online protection. There are other forms of protection as well, and understanding antivirus’ role in your overall mix of online protection is an important part of staying safer online.
Antivirus software protects your devices against malware and viruses through a combination of prevention, detection, and removal.
For years, people have installed antivirus software on their computers. Today, it can also protect your smartphones and tablets as well. In fact, we recommend installing it on those devices as well because they’re connected, just like a computer—and any device that connects to the internet is a potential target for malware and viruses.
In short, if it’s connected, it must get protected.
One important distinction about antivirus is its name, a name that first came into use decades ago when viruses first appeared on the scene. (More on that in a bit.) However, antivirus protects you from more than viruses. It protects against malware too.
Malware is an umbrella term that covers all types of malicious software regardless of its design, intent, or how its delivered. Viruses are a subset of malicious software that infects devices and then replicates itself so that it can infect yet more devices.
So while we popularly refer to protection software as antivirus, it protects against far more than just viruses. It protects against malware overall.
Now here’s where some confusion may come in. Some antivirus apps are standalone. They offer malware protection and that’s it. Other antivirus apps are part of comprehensive online protection software, which can include several additional far-reaching features that can protect your privacy and your identity.
The reason why antivirus gets paired up with other apps for your privacy and identity is because antivirus alone doesn’t offer these kinds of protections. Yet when paired with things like a password manager, credit monitoring, identity theft coverage, and a VPN, to name a few, you can protect your devices—along with your privacy and identity. All the things you need to stay safer online.
In short, antivirus doesn’t cut it alone.
With that, let’s take a closer look at what malware and viruses really are—how they evolved, and what they look like today, along with how antivirus protects you against them.
Viruses have a long history. And depending on how you define what a virus is, the first one arguably took root in 1971—more than 50 years ago.
It was known as Creeper, and rather than being malicious in nature, it was designed to show how a self-replicating program could identify other connected devices on a network, transfer itself to them, and find yet more devices to repeat the process. Later, the same programmer who created a follow-on version of Creeper developed Reaper, a program that could remove the Creeper program. In a way, Reaper could be considered the first piece of antivirus software.
From there, it wasn’t until the 1980’s that malware started affecting the broader population, a time when computers became more commonplace in businesses and people’s homes.
At first, malware typically spread by infected floppy disks, much like the “Brain” virus in 1986. While recognized today as the first large-scale computer virus, its authors say they never intended it to work that way. Rather they say they created Brain as an anti-piracy measure to protect their proprietary software from theft. However, Brain got loose. It went beyond their software and affected computers worldwide. Although not malicious or destructive in nature, Brain most certainly put the industry, businesses, and consumers on notice.
Computer viruses became a thing.
Another piece of malware that got passed along via floppy disks was the “PC Cyborg” attack that targeted the medical research community in and around 1989. There the malware would lie in wait until the user rebooted their computer for the 90th time. And on that 90th boot, the user was presented with a digital ransom note like the one here:
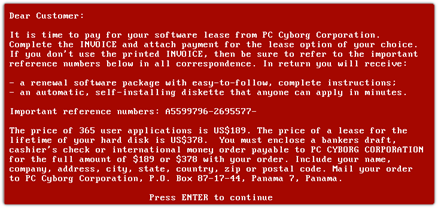
Along with that note, PC Cyborg encrypted the computer’s files, which would only get unencrypted if the victim paid a fee—making PC Cyborg the first widely recognized form of ransomware.
Shortly thereafter, the internet started connecting computers, which opened millions of doors for hackers as people went online. Among the most noteworthy was 1999’s “Melissa” virus, which spread by way of infected email attachments and overloaded hundreds of corporate and governmental email servers worldwide.
It was quickly followed in 2000 by what’s considered the among the most damaging malware to date—ILOVEYOU, which also spread by way of an attachment, this one posing as a love letter. Specifically, it was a self-replicating worm that installed itself on the victim’s computer where it destroyed some information and stole other information, then spread to other computers. One estimate puts the global cost of ILOVEYOU at $10 billion and further speculated that it infected 10% of the world’s internet-connected computers at the time.
With the advent of the internet, malware quickly established itself as a sad fact of connected life. Today, McAfee registers an average of 1.1 million new malicious programs and potentially unwanted apps (PUA) each day, which contributes to the millions and millions of malicious programs already in existence.
Apart from the sheer volume of malware out there today, another thing that distinguishes today’s malware from early malware attacks—they’re created largely for profit.
We can think of it this way:
Today’s malware is far more than an annoyance or headache. It can lead to follow-on attacks that target your finances, your identity, your privacy, or a mix of all three.
So with a million or so new threats coming online each day, and millions more out there already, how does antivirus protect you from malware? It blocks, detects, and removes malware. And it does so in a couple of ways:
However, as mentioned earlier, antivirus provides only one aspect of online protection today. While it protects your devices and the data that’s on them, your privacy and identity can come under attack as well. So while antivirus alone can protect you from malware, it can’t prevent other forms of online crime like identity theft, phishing attacks designed to steal personal information, or attacks on your accounts, to name a few of the many other types of threats out there.
Yet comprehensive online protection can.
Comprehensive online protection software like ours offers antivirus, along with specific services and features that protect your privacy and identity online as well. It gives you dozens of other features like identity theft coverage & restoration, personal data cleanup, security freezes, and an online protection score that shows you just how safe you are, along with suggestions that can make you safer still.
So while protecting your devices with antivirus is a great start, it’s only one part of staying safer online. Including privacy and identity protection rounds out your protection overall.
The post What is Antivirus and What Does It Really Protect? appeared first on McAfee Blog.

Have you ever been browsing online and clicked a link or search result that took you to a site that triggers a “your connection is not private” or “your connection is not secure” error code? If you’re not too interested in that particular result, you may simply move on to another result option. But if you’re tempted to visit the site anyway, you should be sure you understand what the warning means, what the risks are, and how to bypass the error if you need to.
A “your connection is not private” error means that your browser cannot determine with certainty that a website has safe encryption protocols in place to protect your device and data. You can bump into this error on any device connected to the internet — computer, smartphone, or tablet.
So, what exactly is going on when you see the “this connection is not private” error?
For starters, it’s important to know that seeing the error is just a warning, and it does not mean any of your private information is compromised. A “your connection is not private” error means the website you were trying to visit does not have an up-to-date SSL (secure sockets layer) security certificate.
Website owners must maintain the licensing regularly to ensure the site encryption capabilities are up to date. If the website’s SSL certificate is outdated, it means the site owners have not kept their encryption licensing current, but it doesn’t necessarily mean they are up to no good. Even major websites like LinkedIn have had momentary lapses that would throw the error. LinkedIn mistakenly let their subdomain SSL certificates lapse.
In late 2021, a significant provider of SSL certificates, Let’s Encrypt, went out of business. When their root domain officially lapsed, it created issues for many domain names and SSL certificates owned by legitimate companies. The privacy error created problems for unwitting businesses, as many of their website visitors were rightfully concerned about site security.
While it does not always mean a website is unsafe to browse, it should not be ignored. A secure internet connection is critical to protecting yourself online. Many nefarious websites are dangerous to visit, and this SSL certificate error will protect you from walking into them unaware.
SSL certification standards have helped make the web a safer place to transact. It helps ensure online activities like paying bills online, ordering products, connecting to online banking, or keeping your private email accounts safe and secure. Online security continues to improve with a new Transport Layer Security (TLS) standard, which promises to be the successor protocol to SSL.
So be careful whenever visiting sites that trigger the “connection is not private” error, as those sites can potentially make your personal data less secure and make your devices vulnerable to viruses and malware.
Note: The “your connection is not private” error is Google Chrome‘s phrasing. Microsoft Edge or Mozilla Firefox users will instead see a “your connection is not secure” error as the warning message.
If you feel confident that a website or page is safe, despite the warning from your web browser, there are a few things you can do to troubleshoot the error.
Remember, you are taking your chances anytime you ignore an error. As we mentioned, you could leave yourself vulnerable to hackers after your passwords, personal information, and other risks.
Your data and private information are valuable to hackers, so they will continue to find new ways to try and procure it. Here are some ways to protect yourself and your data when browsing online.
As we continue to do more critical business online, we must also do our best to address the risks of the internet’s many conveniences.
A comprehensive cybersecurity tool like McAfee+ Ultimate can help protect you from online scams, identity theft, and phishing attempts, and ensure you always have a secure connection. McAfee helps keep your sensitive information out of the hands of hackers and can help you keep your digital data footprints lighter with personal data cleanup.
With McAfee’s experts on your side, you can enjoy everything the web offers with the confidence of total protection.
The post “This Connection Is Not Private” – What it Means and How to Protect Your Privacy appeared first on McAfee Blog.

There’s no doubt that cyber bullying ranks towards the top of most parents ‘worry list’. As a mum of 4, I can tell you it always came in my top five, usually alongside driving, drugs, cigarettes and alcohol! But when McAfee research in May revealed that Aussie kids experience the 2nd highest rate of cyberbullying out of the 10 countries interviewed, my heart skipped a beat. Clearly cyberbullying is a big problem for Aussie kids. Bigger than I had previously thought. But many of us parents had so many more questions: what can it look like? where does it happen? and could my child be a perpetrator?
So, as an ally of connected families, McAfee set out to answer these questions so undertook more research through a detailed 10-country online questionnaire to 11,687 parents and their children in June. And the answers were quite revealing…
Before we get into the results, let’s clarify what cyberbullying means. There is often a lot of confusion because let’s be honest, different kids have different tolerances, standards and cultural lenses for what is and isn’t acceptable behaviour. The definition of cyberbullying used in McAfee’s report was based on the definition by StopBullying.Gov:
Cyberbullying is bullying that takes place over digital devices like cell phones, computers, and tablets. Cyberbullying can occur through SMS, Text, and apps, or online in social media, forums, or gaming where people can view, participate in, or share content. Cyberbullying includes sending, posting, or sharing negative, harmful, false, or mean content about someone else. It can include sharing personal or private information about someone else causing embarrassment or humiliation. Some cyberbullying crosses the line into unlawful or criminal behaviour.
McAfee’s definition was then expanded to include specific acts of cyberbullying, such as:
Along with other acts, including:
What Is The Most Common Form of Cyberbullying for Aussie Kids?
Even though racially motivated cyberbullying is on the rise, name-calling is the most common form of cyberbullying with 40% of kids globally reporting that they have been on the receiving end of it. Interestingly, in Australia, our kids receive this style of bullying more frequently, with 49% of Aussie kids affected.
Exclusion from group chats and conversations is the 2nd most commonly reported form of cyberbullying with 36% of kids globally experiencing it. In Australia, this is higher at 42%.
The spreading of false rumours rounds out the top three forms and was reported by 28% of children globally. Curiously, Aussie kids don’t seem to use this form just as commonly with just 24% affected. Japan stands out as the leader in this reported form of cyberbullying at 44% followed by Germany at 35% and India at 39%.
1 in 8 Aussie kids reports receiving extreme cyberbullying threats eg stalking, harassment and physical threats online. This is in line with the global average however in India and the US, more young people are affected with 1 in 5 reporting this behaviour.
It’s no surprise that the bulk of cyberbullying is happening on social media with 32% of kids affected globally. Group chats come in as the 2nd most commonplace with 24% of kids involved followed by online gaming being an issue for 22% of kids surveyed. 21% of kids experienced cyberbullying on websites and forums and 19% identified that they experienced cyberbullying via text messages.
Globally, Facebook is the social media site where cyberbullying is most likely to occur. 53% of children report witnessing it and 50% report experiencing it. This is followed by Instagram (40% witnessing and 30% experiencing), YouTube, TikTok and then Twitter.
Overall, Aussie kids appear to experience less cyberbullying on social media with just 47% witnessing it on Facebook and 37% experiencing it. Our kids also report lower levels on Instagram as well with 34% witnessing and 30% experiencing.
It appears that Snapchat is unfortunately where a lot of undesirable behaviour happens for our Aussie kids with 34% reporting that they have been affected on this platform – a huge 10% above the international average and the highest of any country included in the survey.
I’m sure it’s not a surprise to many parents that most cyberbullying comes from someone known to the victim. In fact, 57% of kids worldwide confirmed this with just 45% nominating that the cyberbullying they received had been initiated by a stranger. And Aussie kids’ experiences reflect the global norm with 56% expressing that they also knew the perpetrator but only 36% experienced cyberbullying from a stranger. Interestingly, only India, reported more cyberbullying at the hands of strangers (70%) than by someone the child knows (66%).
Globally, 81% of all children surveyed stated that they had never cyberbullied anyone while just 19% admitted that they had. But when questioned further, it became apparent that there may be some disconnect. In fact, when asked about specific cyberbullying behaviours, more than half of children worldwide (53%) admitted to committing one or more types of cyberbullying —perhaps indicating that their definition of cyberbullying differs from the clinically accepted definition. The most common acts that they admitted to included making a joke at someone else’s expense (22%), name-calling (18%) and excluding someone from a chat or conversation (15%).
It appears that our kids are calmer about the state of cyberbullying that their peers worldwide. Only 46% of our kids reported they were more concerned about being cyberbullied now than last year, compared to a 59% average worldwide. Aussie children said they are among the least concerned children in the world, alongside Canada at 44%, the U.K. at 43%, and Germany at 38%.
And Aussie parents also appear calmer than parents from other countries with only 61% nominating they were more concerned about their child being cyberbullied today versus last year, compared to the 72% international average. Australian parents also showed the least level of worry that their child may be a cyberbully. Only 41% said that they worried this was more likely this year than last, compared to 56% of parents elsewhere.
Now, this could be because the online learning and tech-heavy phase of the pandemic is, thankfully, over and we are not as focussed on technology-related issues. Or perhaps it’s because we really are a nation of ‘laid-back’ types! The jury is still out…
We all know that it’s impossible to fix a problem if you don’t truly understand it. So, while these statistics might be a little overwhelming, please soak them in. Appreciating the complexities of this problem and digesting how cyberbullying can look and impact our kids is essential. Now, as first-generation digital parents, it may take us a little longer to wrap our heads around it and that’s ok. The most important thing is that we commit to understanding the problem so that we are in the best position possible to support and guide our kids.
In my next blog post, I will be sharing more detailed strategies that will help you minimise the risk of your child becoming a victim of cyberbullying. I will also include advice on what to do if your child is affected by cyberbullying plus what to do if your child is in fact a cyberbully.
‘Till next time.
Stay Safe Online
Alex
The post How Cyberbullying Looks In Australia in 2022 appeared first on McAfee Blog.
It’s hard to imagine a world without cellphones. Whether it be a smartphone or a flip phone, these devices have truly shaped the late 20th century and will continue to do so for the foreseeable future. But while users have become accustomed to having almost everything they could ever want at fingertips length, cybercriminals were busy setting up shop. To trick unsuspecting users, cybercriminals have set up crafty mobile threats – some that users may not even be fully aware of. These sneaky cyberthreats include SMSishing, fake networks, malicious apps, and grayware, which have all grown in sophistication over time. This means users need to be equipped with the know-how to navigate the choppy waters that come with these smartphone-related cyberthreats. Let’s get started.
If you use email, then you are probably familiar with what phishing is. And while phishing is commonly executed through email and malicious links, there is a form of phishing that specifically targets mobile devices called SMSishing. This growing threat allows cybercriminals to utilize messaging apps to send unsuspecting users a SMSishing message. These messages serve one purpose – to obtain personal information, such as logins and financial information. With that information, cybercriminals could impersonate the user to access banking records or steal their identity.
While this threat was once a rarity, it’s rise in popularity is two-fold. The first aspect being that users have been educated to distrust email messages and the second being the rise in mobile phone usage throughout the world. Although this threat shows no sign of slowing down, there are ways to avoid a cybercriminal’s SMSishing hooks. Get started with these tips:
Public and free Wi-Fi is practically everywhere nowadays, with some destinations even having city-wide Wi-Fi set up. But that Wi-Fi users are connecting their mobile device to may not be the most secure, given cybercriminals can exploit weaknesses in these networks to intercept messages, login credentials, or other personal information. Beyond exploiting weaknesses, some cybercriminals take it a step further and create fake networks with generic names that trick unsuspecting users into connecting their devices. These networks are called “evil-twin” networks. For help in spotting these imposters, there are few tricks the savvy user can deploy to prevent an evil twin network from wreaking havoc on their mobile device:
Fake apps have become a rampant problem for Android and iPhone users alike. This is mainly in part due to malicious apps hiding in plain sight on legitimate sources, such as the Google Play Store and Apple’s App Store. After users download a faulty app, cybercriminals deploy malware that operates in the background of mobile devices which makes it difficult for users to realize anything is wrong. And while users think they’ve just downloaded another run-of-the-mill app, the malware is hard at work obtaining personal data.
In order to keep sensitive information out of the hands of cybercriminals, here are a few things users can look for when they need to determine whether an app is fact or fiction:
With so many types of malware out in the world, it’s hard to keep track of them all. But there is one in particular that mobile device users need to be keenly aware of called grayware. As a coverall term for software or code that sits between normal and malicious, grayware comes in many forms, such as adware, spyware or madware. While adware and spyware can sometimes operate simultaneously on infected computers, madware — or adware on mobile devices — infiltrates smartphones by hiding within rogue apps. Once a mobile device is infected with madware from a malicious app, ads can infiltrate almost every aspect on a user’s phone. Madware isn’t just annoying; it also is a security and privacy risk, as some threats will try to obtain users’ data. To avoid the annoyance, as well as the cybersecurity risks of grayware, users can prepare their devices with these cautionary steps:
The post Cybercrime’s Most Wanted: Four Mobile Threats that Might Surprise You appeared first on McAfee Blog.

Our phones store a lot of personal data, including contacts, social media account details, and bank account logins. We use our smartphones for everything under the sun, from work-related communication to online shopping.
However, like computer viruses, our phones can be vulnerable to malware. Viruses are a type of malware that replicate themselves and spread throughout the entire system. They can affect your phone’s performance or, worse, compromise your sensitive information so that hackers can benefit monetarily.
In this article, we give you a rundown of viruses that can infect your phone and how you can identify and eliminate them. We also provide some tips for protecting your phone from viruses in the first place.
iPhones and Android devices run on different operating systems. So, there are differences in the viruses that affect each type of mobile device and how resistant each operating system is to viruses.
Viruses have a harder time penetrating iOS because of its design (although iOS hacks can still happen). By restricting interactions between apps, Apple’s operating system limits the movement of an iPhone virus across the device. However, if you jailbreak your iPhone or iPad to unlock tweaks or install third-party apps, then the security restrictions set by Apple’s OS won’t work. This exposes iPhone users to vulnerabilities that cybercriminals can exploit.
While Android phones are also designed with cybersecurity in mind, their reliance on open-source code makes them an easier target for hackers. Android devices allow users to access third-party apps not available in the Google Play Store.
Cybercriminals today are sophisticated and can launch a variety of cyberattacks on your smartphone. Some viruses that can infect your phone include:
Smartphones and computers get viruses in a similar way. The most common include:
Now that you know how your phone could be the target of a virus, look out for these seven signs to determine if your device has been infected with malicious software.
Most pop-up ads don’t carry viruses but are only used as marketing tools. However, if you find yourself shutting pop-up ads more often than usual, it might indicate a virus on your phone.
Don’t open any apps in your library that you don’t remember installing. Instead, uninstall them immediately. These apps tend to carry malware that’s activated when the app is opened or used.
Your phone isn’t built to support malware. When you accidentally download apps that contain malware, the device has to work harder to continue functioning. In this case, your phone might be overheating.
If your contacts receive unsolicited scam emails or messages on social media from your account, especially those containing suspicious links, a virus may have accessed your contact list. It’s best to let all the recipients know that your phone has been hacked so that they don’t download any malware themselves or forward those links to anybody else.
An unusually slow-performing device is a hint of suspicious activity on your phone. The device may slow down because it needs to work harder to support the downloaded virus. Alternatively, unfamiliar apps might be taking up storage space and running background tasks, causing your phone to run slowly.
Be sure to follow up on charges on your credit card or transactions in your banking statements that you don’t recognize. It could be an unfamiliar app or malware making purchases through your account without your knowledge.
A sudden rise in your data usage or phone bill can be suspicious. A virus might be running background processes or using your internet connection to transfer data out of your device for malicious purposes.
An unusually quick battery drain may also cause concern. Your phone will be trying to meet the energy requirements of the virus, so this problem is likely to persist for as long as the virus is on the device.
You may have an inkling that a virus is housed inside your phone, but the only way to be sure is to check.
An easy way to do this is by downloading a trustworthy antivirus app. The McAfee Mobile Security app scans for threats regularly and blocks them in real time. It prevents suspicious apps from attaching themselves to your phone and secures any public connections you might be using.
If you detect a virus on your iPhone or Android device, there are several things you can do.
It’s never too late to start caring for your phone. Follow these tips to stay safe online and help reduce the risk of your phone getting a virus.
McAfee Mobile Security is committed to keeping your mobile phone secure, whether it’s an iPhone or Android device. In addition to regularly scanning your phone to track suspicious activity, our technology responds to threats in real time. Our comprehensive tools also secure your internet connections and let you browse peacefully. Using our app makes sure that your phone and data are protected at all times.
So, what are you waiting for? Download McAfee Mobile Security today!
The post 7 Signs Your Phone Has a Virus and What You Can Do appeared first on McAfee Blog.

If you’re the parent of a tween or teen, chances are they’re not the only ones going back to school. Their smartphones are going back too.
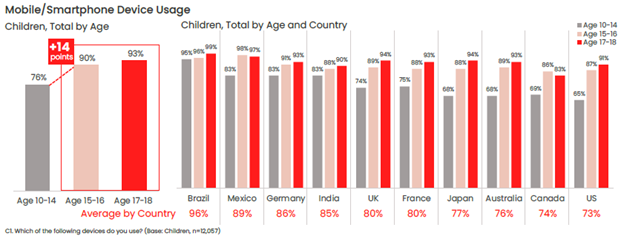
Our recent global research showed just how many tweens and teens use a smartphone. Plenty. Depending on the age band, that figure ranges anywhere from 76% to 93%, with some noteworthy variations between countries.
One of the top reasons parents give their child a phone is to stay in touch, so it likely follows that those phones will likely make their way into the classroom. Whether or not that’s the case for your child, back-to-school time is still a great time to help your child stay safer on their phone—and keep their phones safer too in the event of loss or theft.
Comprehensive online protection software can protect your phone in the same way that it protects your laptops and computers. Unfortunately, while many people use it on their laptops and computers, far fewer people use it on their phones—only about 42% of tweens and teens worldwide use it on their smartphones according to our most recent research.
Installing it can protect their privacy, keep them safe from attacks on public Wi-Fi, and automatically block unsafe websites and links, just to name a few things it can do. You can find our smartphone apps in both Google Play and the Apple App Store.
Updates do all kinds of great things for gaming, streaming, and chatting apps, such as adding more features and functionality over time. Updates do something else—they make those apps more secure. Hackers will hammer away at apps to find or create vulnerabilities, which can steal personal info or compromise the device itself. Updates will often include security improvements, in addition to performance improvements.
iPhones update apps automatically by default, yet you can learn how to turn them back on here if they’ve been set to manual updates. For Android phones, this article can help you set apps to auto-update if they aren’t set that way already.
Much the same goes for the operating system on smartphones too. Updates can bring more features and more security. iOS users can learn how to update their phones automatically in this article. Likewise, Android users can refer to this article about automatic updates for their phones.
Another finding from our latest global research is just how few people use a lock screen on their phones. Only 56% of parents said that they protect their smartphone with a password or passcode, and only 42% said they do the same for their child’s smartphone—a further 14% drop between parents and kids.
The issue here is clear. If an unlocked phone gets lost or stolen, all the information on it is an open book to a potential hacker, scammer, or thief. Enabling a lock screen if you haven’t already. It’s a simple feature found in both iOS and Android devices.
Preventing the actual theft of your phone is important too, as some hacks happen simply because a phone falls into the wrong hands. This is a good case for password or PIN protecting your phone, as well as turning on device tracking so that you can locate your phone or even wipe it remotely if you need to. Apple provides iOS users with a step-by-step guide for remotely wiping devices, and Google offers up a guide for Android users as well.
Strong, unique passwords offer another primary line of defense. Yet with all the accounts we have floating around, juggling dozens of strong and unique passwords can feel like a task—thus the temptation to use (and re-use) simpler passwords. Hackers love this because one password can be the key to several accounts. Instead, try a password manager that can create those passwords for you and safely store them as well. Comprehensive security software will include one, and McAfee also offers a free service with True Key.
Google Play and Apple’s App Store have measures in place to review and vet apps to help ensure that they are safe and secure. Third-party sites may not have that process in place. In fact, some third-party sites may intentionally host malicious apps as part of a broader scam. Granted, cybercriminals have found ways to work around Google and Apple’s review process, yet the chances of downloading a safe app from them are far greater than anywhere else. Furthermore, both Google and Apple are quick to remove malicious apps once discovered, making their stores that much safer.
One way that crooks can hack their way into your phone is via public Wi-Fi, such as at coffee shops, libraries, and other places on the go. These networks are public, meaning that your activities are exposed to others on the network—your banking, your password usage, all of it. One way to make a public network private is with a VPN, which can keep you and all you do protect from others on that Wi-Fi hotspot. Note that our VPN can turn on automatically for public Wi-Fi, protecting account credentials, search habits, and other activities online.
The same advice applies for these devices as well—strong online protection software, password management, VPN usage, and so on. What’s good for a smartphone is good for laptops and desktops too.
For laptops in particular, you can track these devices as well, just like a smartphone. The process differs from smartphones, yet it’s still quite straightforward. Windows and Mac users can enable the following settings—and you can click the links below for complete instructions from the source:
Putting these same protections in place on your laptops and desktops will help make your child, and your whole family, safer than before.
Note that on school-issued devices, your school district will likely have technology teams who manage them. As part of that, they typically have policies and restrictions in place to help keep them running safe and sound. If you have any questions about what kind of protections are in place on these school-issued devices, contact your school district.
While we’ve largely focused on protecting the phone itself, there’s also the importance of protecting the person who’s using it. In this case, your child—what they see, do, and experience on the internet. Device security is only part of the equation there.
Parents of tweens and teens know the concerns that come along with smartphone usage, ranging anywhere from cyberbullying, too much screen time, and simply wanting to know what their child is up to on their phone.
As you can imagine, each of these topics deserves its own treatment. The “Family Safety” section of our blog offers parents and their kids alike plenty of resources, and the list below can get you started on a few of the most pressing issues:
Without a doubt, while a child may get their first smartphone to “keep in touch,” that ownership blossoms into something far greater. And quite quickly. As they dive into the world of apps, social media, messaging, and gaming, take an interest, take it as an opportunity to spend time talking about their day and what it was like online.
By asking if they grabbed any cool pictures, what their favorite games are, and how their friends are when your child is texting them, questions like these can open a look into a world that would otherwise remain closed. This way, talking about the phone and what they’re doing on it becomes part of normal, everyday conversation. This can reap benefits down the road when your child encounters the inevitable bumps along the way, whether they’re dealing with a technical issue or something as difficult as cyberbullying or harassment. Talking about their life online on a regular basis may make them more apt to come forward when there’s a problem than they otherwise might.
In all, think of the smartphone as a fast pass into adulthood, thanks to how it puts the entirety of the internet right in your child’s hand. Protecting the device and the kid who’s using it will help ensure they get the absolute best out of all that potential.
The post Getting Your Kids Ready for School—And Their Smartphones Too appeared first on McAfee Blog.

McAfee announces a partnership that will grant new and existing Telstra customers easy access to McAfee’s leading security solutions to deliver holistic security and privacy protection through its integrated suite of services including Antivirus, Parental Controls, Identity Protection, Secure VPN and more, to protect and secure multiple devices including mobiles, PCs and laptops. The partnership brings added protection to Telstra’s millions of customers and their devices via McAfee’s intuitive and integrated consumer security platform
“A recent McAfee study found 27% of Australians surveyed reported attempted account theft and 23% had experienced financial account information leaks,” said Pedro Gutierrez, Senior Vice President of Global Sales and Operations at McAfee. “As the proliferation of life online accelerates, we are thrilled to be partnering with Telstra who are showing through this collaboration, a commitment to innovation and to their customers by investing in new infrastructure and technologies that safeguard their mobile and broadband subscribers.
McAfee’s integrated consumer security platform offers a wide array of mobile security solutions to protect customers’ privacy and identity while blocking viruses, malware, spyware, and ransomware attacks. This partnership allows Telstra’s customers to take advantage of these capabilities and protect themselves from additional threats including potential hacks, identity theft and broader gaps in online and mobile security so they can live life confidently online.
“In today’s increasingly connected world the risk of cyber threats continues to grow. To counter the risk, Telstra is committed to providing our customers with the safety and security features needed to protect them online,” said Matthew O’Brien, Cyber Security Executive and Group Owner at Telstra. “This partnership with McAfee helps drive our mission to build a safe and secure connected future where everyone can thrive, and further complements Telstra’s T25 ambition to extend our network leadership position by delivering greater value to our customers.”
To activate Device Security, Telstra customers can simply go in-store, online or to their MyTelstra app. The full suite of McAfee features supported include Antivirus/System Scan, Safe Browsing, Protection Center, Identity Protection, Password Manager, Parental Controls, Protection Score and Secure VPN. All eligible Telstra customers can try Device Security for three months on Telstra, then auto-roll onto $10/month after.
The post McAfee and Telstra Partner to Bring Privacy, Identity and Security to Australian Customers appeared first on McAfee Blog.

If your PC runs on Windows 10, you’re in very good company. The Microsoft operating system is the most widely used OS in the world. Many Windows 10 users have also been upgraded to Windows 11 through a rollout that began in 2021. Microsoft plans to complete the Windows update by mid-2022.
Unfortunately, its success as a widely used operating system makes Windows attractive to hackers. And if malicious software like malware can make a home in Windows, there are a lot of targets. So, this might raise the question of how best to protect your Windows 10 or 11 device.
Should you just use Windows Defender — Microsoft’s free version of antivirus software — or buy additional protection?
Read on to learn what Microsoft Defender covers and how additional virus protection can secure all of your connected devices.
For years, Microsoft has offered anti-malware protection, but the current version provides effective security against viruses. Windows Defender is a free antivirus tool that’s built into the Windows operating system.
While it’s considered one of the best free antivirus software programs, it doesn’t have any extra features that might come with paid security software. If you’re just looking for good antivirus software, though, Windows Defender can get the job done.
If you’re not using third-party antivirus protection, you’ll want to make sure that your Windows Defender antivirus coverage is working on your computer. Here’s how to check:
To make sure your Windows security is running, follow these steps:
With built-in coverage, you may wonder if you should invest in paid antivirus software. The answer is, of course, yes! It can be a good idea to get another antivirus solution because blocking malware and viruses should just be one part of your threat protection.
Today’s cybercriminals are using elaborate ruses to try to access your personal information, such as your bank and credit card numbers. And some of their scams might even target your devices with risky apps or links on social media.
As they always say, it’s better to be safe than sorry! Having another antivirus program can make sure you have real-time protection and access to the latest security features.
There are a lot of antivirus protection programs out there, but they aren’t all created equal. When looking for the best antivirus software for your needs, here are some things to consider for your devices running on Windows 10 or 11.
If you have a Windows PC, use an iPhone, and your tablet runs on Chrome, it helps to have an antivirus app that works across multiple operating systems. The good news is that McAfee Total Protection is compatible with Windows, Mac, iOS, and Android devices, so you can continue enjoying all of your different devices without losing protection.
For greater cybersecurity, antivirus software should defend against a variety of online threats like viruses, spyware, and ransomware. And that’s exactly what you get with McAfee Total Protection. Our antivirus software can also help you avoid phishing attacks, which are fake messages to trick you into providing information or clicking a malicious link. The software will give you a warning when it recognizes a risky link, website, or file.
Functionality is another thing you’ll want to consider when looking for antivirus software. If the program isn’t easy to use to begin with — especially if you want to easily manage multiple devices — what good will it do you?
But you don’t have to worry with McAfee Total Protection, which allows you to connect and manage all of your computers and mobile devices from one single dashboard.
To keep your devices free from online threats like malware, good antivirus software will scan your files for threats. McAfee Total Protection provides 24/7 protection with real-time, on-demand, and scheduled scanning of files and applications.
McAfee Total Protection was developed with an understanding of how cybercriminals operate. Scammers may use a variety of tactics to try to steal your personal information, so our all-in-one protection also includes:
Using Microsoft’s built-in antivirus software can protect your Windows devices from viruses and malware. But to really keep your network and all of your devices secure, it’s good to rely on comprehensive protection like McAfee Total Protection. With services like identity monitoring, safe browsing, and a secure VPN, you can enjoy the internet without worry.
The post Does Windows 10 or 11 Need Antivirus Software? appeared first on McAfee Blog.

Whether you think you might have a virus on your computer or devices, or just want to keep them running smoothly, it’s easy to do a virus scan. How to check for viruses depends on the software and device you have, so we’ll go through everything you need to know to run a scan effectively and keep your computers, phones and tablets in tip-top shape.
First, let’s cover a few of the telltale signs your device might have a virus. Is your computer or device acting sluggish or having a hard time booting up? Have you noticed missing files or a lack of storage space? Have you noticed emails or messages sent from your account that you did not write? Perhaps you’ve noticed changes to your browser homepage or settings? Or maybe, you’re seeing unexpected pop-up windows, or experiencing crashes and other program errors. These are all examples of signs that you may have a virus, but don’t get too worried yet, because many of these issues can be resolved with a virus scan.
Each antivirus program works a little differently, but in general the software will look for known malware that meets a specific set of characteristics. It may also look for variants of these known threats that have a similar code base. Some antivirus software even checks for suspicious behavior. If the software comes across a dangerous program or piece of code, it removes it. In some cases, a dangerous program can be replaced with a clean one from the manufacturer.
The process of checking for viruses depends on the device type and its operating system. Check out these tips to help you scan your computers, phones and tablets.
If you use Windows 10, go into “Settings” and look for the “Updates & Security” tab. From there you can locate a “Scan Now” button.
Of course, many people have invested in more robust antivirus software that has a high accuracy rate and causes less drain on their system resources, such as McAfee Total Protection. To learn how to run a virus scan using your particular antivirus software, search the software’s help menu or look online for instructions.
Mac computers don’t have a built-in antivirus program, so you will have to download security software to do a virus scan. There are some free antivirus applications available online, but we recommend investing in trusted software that can protect you from a variety of threats. Downloading free software and free online virus scans can be risky, since cybercriminals know that this is a good way to spread malware.
Whichever program you choose, follow their step-by-step instructions on how to perform a virus scan, either by searching under “help” or looking it up on their website.
Yes, you can get a virus on your phone or tablet, although they are less common than on computers. However, the wider category of mobile malware is on the rise and your device can get infected if you download a risky app, click on an attachment in a text message, visit a dangerous webpage, or connect to another device that has malware on it.
Fortunately, you can protect your devices with mobile security software. It doesn’t usually come installed, so you will have to download an application and follow the instructions.
Because the Android platform is an open operating system, there are a number of antivirus products for Android devices, that allows you to do a virus scan.
Apple devices are a little different because they have a closed operating system that doesn’t allow third parties to see their code. Although Apple has taken other security precautions to reduce malware risks, such as only allowing the installation of apps from Apple’s official app store, these measures aren’t the same as an antivirus program.
For more robust protection on your Apple devices, you can install mobile security software to protect the private data you have stored on your phone or tablet, such as contacts, photos and messages.
If safeguarding all your computers and devices individually sounds overwhelming, you can opt for a comprehensive security product that protects computers, smartphones and tablets from a central control center, making virus prevention a breeze.
New online threats emerge every day, putting our personal information, money and devices at risk. In the first quarter of 2019 alone McAfee detected 504 new threats per minute, as cybercriminals employed new tactics. That’s why it is essential to stay ahead of these threats by using security software that is constantly monitoring and checking for new known threats, while safeguarding all of your sensitive information. Virus scans are an essential part of this process when it comes to identifying and removing dangerous code.
Most antivirus products are regularly scanning your computer or device in the background, so you will only need to start a manual scan if you notice something suspicious, like crashes or excessive pop-ups. You can also program regular scans on your schedule.
Of course, the best protection is to avoid getting infected in the first place. Here are a few smart tips to sidestep viruses and other malware:
The post How To Do A Virus Scan appeared first on McAfee Blog.

The White House recently reissued a warning to American businesses in response to the unprecedented economic sanctions the U.S. has imposed on Russia for the Ukraine invasion, stating, “There is now evolving intelligence that Russia may be exploring options for potential cyberattacks.”
Along with this statement, the White House published a fact sheet outlining the new and ongoing steps the government is taking to protect its infrastructure and technologies, along with steps that private businesses can take to protect themselves from attacks as well.
Of course, any successful attack on government operations and the operations of private businesses could potentially affect households as well—such as in the case of data breaches where data or information is stolen from a system, often the personal data and information of individuals.
Word of potential attacks understandably leaves people feeling uncertain and may further leave them wondering if there’s anything they can do to protect themselves. With regards to data breaches and the cases of identity theft that typically follow, there are several steps people can take to keep safer online.
Let’s break down what a data breach looks like, how it can affect you, and what you can do in advance of a breach to protect yourself.
We’ve certainly seen data breaches make the news over the years, which are often (but not always) associated with malicious hackers or hacker organizations. A quick list of some of the largest and most impactful breaches we’ve seen in recent years:
Healthcare facilities have seen their data breached, along with the operations of popular restaurants. Small businesses find themselves in the crosshairs as well, with one report stating that 43% of data leaks target small businesses. Those may come by way of an attack on where those businesses store their records, a disgruntled employee, or by way of a compromised point-of-sale terminal in their store, office, or location.
What differs with the White House warning is who may end up being behind these potential attacks—a nation-state rather than what are financially motivated hackers or hacking groups. (Some research indicates that nearly 90% of breaches are about the money.) However, the result is the same. Your personal information winds up loose in the world and possibly in the hands of a bad actor.
The fact is that plenty of our information is out there on the internet, simply because we go about so much of our day online, whether that involves shopping, banking, getting results from our doctors, or simply hopping online to play a game once in a while.
Naturally, that means the data in any given breach will vary from service to service and platform to platform involved. Certainly, a gaming service will certainly have different information about you than your insurance company. Yet broadly speaking, there’s a broad range of information about you stored in various places, which could include:
As to what gets exposed and when you might find out about it, that can vary greatly as well. One industry research report found that 60% of breaches were discovered in just days from the initial attack while others could take months or even longer detect. Needless to say, the timeline can get rather stretched before word reaches you, which is a good reason to change your passwords regularly should any of them get swept up in a breach. (An outdated password does a hacker no good—more on that in a bit.)
The answer is plenty. In all, personal information like that listed above has a dollar value to it. In a way, your data and information are a kind of currency because they’re tied to everything from your bank accounts, investments, insurance payments—even tax returns and personal identification like driver’s licenses.
With this information in hand, a crook can commit several types of identity crimes—ranging from fraud to theft. In the case of fraud, that could include running up a bill on one of your credits cards or draining one of your bank accounts. In the case of theft, that could see crooks impersonate you so they can open new accounts or services in your name. Beyond that, they may attempt to claim your tax refund or potentially get an ID issued in your name as well.
Another possibility is that a hacker will simply sell that information on the dark marketplace, perhaps in large clumps or as individual pieces of information that go for a few dollars each. However it gets sold, these dark-market practices allow other fraudsters and thieves to take advantage of your identity for financial or another gain.
The succinct answer is to sign up for an identity protection service. It can monitor dozens of types of personal information and then alert you if any of them are possibly being misused, so you can address any issues right away before they become a potentially much bigger problem.
Further, pairing identity protection with online protection software can protect you even more. With an all-up view of your overall online security—how well you’re protecting yourself and your identity online—it can guide you through steps that can shore up your protection and make you safer still.
When a business, service, or organization falls victim to a breach, it doesn’t always mean that you’re automatically a victim too. Your information may not have been caught up in it. However, it’s best to act as if it was. With that, we strongly suggest you take these immediate steps.
Given the possibility that your password may be in the hands of a bad actor, change it right away. Strong, unique passwords offer one of your best defenses against hackers. Update them regularly as well. As mentioned above, this can protect you in the event a breach occurs and you don’t find out about it until well after it’s happened. You can spare yourself the upkeep that involves a password manager that can keep on top of it all for you. If your account offers two-factor authentication as part of the login process, make use of it as it adds another layer of security that makes hacking tougher.
If you spot unusual or unfamiliar charges or transactions in your account, bank, or debit card statements, follow up immediately. That could indicate improper use. In general, banks, credit card companies, and many businesses have countermeasures to deal with fraud, along with customer support teams that can help you file a claim if needed.
As outlined above, identity protection like ours can monitor a broad set of your personal information and provide you guidance for making it more secure, in addition to getting help from a professional recovery specialist.
For an even closer look at identity theft, we have two articles that can help guide the way if you think you’re a victim, each featuring a series of straightforward steps you can take to set matters right:
No matter how uncertain news of possible cyberattacks may any of us feel, you can take steps to set some of that uncertainty aside. An identity protection service is a strong first move against possible identity theft, as is pairing it with online protection software that keeps you safer online overall. Likewise, knowing the signs of possible identity theft and what you can do to address it right away offer further assurance still—like having the services of a professional recovery specialist to help.
In all, there’s no need to leave yourself wondering at the news from the White House. As an individual, you have it in your power to make yourself and your family safer than they are now.
The post White House Announces Possible Rise in Cyberattacks—What You Can Do to Stay Safe appeared first on McAfee Blog.

You may hear corporate cybersecurity experts hail the benefits of a VPN, or a virtual private network, to keep company information safe from ransomware attacks and cybercriminals seeking to steal valuable business secrets. It’s unlikely that everyday people, such as yourself, will be targeted by a ransomware scheme, so you may be puzzled about how a VPN can help someone like you be safer online. Luckily, with a VPN being very easy to install and use, you can indeed experience these three everyday benefits to keep your browsing activities safe from eavesdroppers seeking to profit from your online comings and goings.
The most widely known benefit of a VPN for daily use is to safeguard your device when it’s connected to a public Wi-Fi network. Coffee shops, libraries, hotels, transportation hubs, and other public places often provide courtesy internet service to visitors. Shifty characters often lurk on unprotected networks to lift personally identifiable information (PII) from people handling sensitive emails, making banking transactions, or shopping online. Public Wi-Fi eavesdroppers can lift credit card numbers, addresses, birthdays, and Social Insurance Numbers.
When you connect to public Wi-Fi that doesn’t have a lock icon, that’s a sign that you should toggle on your VPN. Also, even if you’re required to enter a password, be wary of any network you share with strangers.
A VPN can also hide your location data. How does this help you protect your browsing history? First, when you scramble your location, you’re likely to confuse ad networks trying to send you targeted ads. This will free your social media feeds and search engines from targeted ads that often are so accurate they seem like an invasion of privacy.
Second, hiding your location can protect you from cybercriminals looking to mine PII. VPNs make it impossible for criminals to discover your IP address. (The internet protocol address is what ties your device to a specific local network.) When they’re visible, criminals can trace IP addresses to reveal home addresses, full names, and phone numbers: all of which are key pieces of PII that, in the wrong hands, can jeopardize your identity.
While Canada and the European Union don’t allow ISPs (internet service providers) to even collect the browsing data of their customers, keep in mind that in some countries, like the U.S., ISPs can collect, store, share, and/or sell customer data. While advertisers are often the buyers of customer data, in the case of a breach, the more places your PII lives, the more likely it may be involved in a security incident. The goal is to limit the extent and number of places where your browsing history is stored.
VPNs can scramble your online movements to the point where not even ISPs can track it. Plus, when you log out, your device doesn’t keep a record of what you did while connected to the VPN. Incognito mode on your internet browser hides your IP address, but the websites you visit still collect cookies and store data about your online whereabouts, meaning that it’s not truly private browsing.
McAfee Safe Connect VPN encrypts your online activity to protect your data from prying eyes. With a premium paid plan, you can protect up to five devices at once with bank-grade Wi-Fi encryption. Feel more confident whenever you hop on the internet across all your connected devices with just one quick and easy step.
The post Why Everyone Needs a VPN appeared first on McAfee Blog.

Authored by Oliver Devane and Vallabh Chole
Notifications on Chrome and Edge, both desktop browsers, are commonplace, and malicious actors are increasingly abusing this feature. McAfee previously blogged about how to change desktop browser settings to stop malicious notifications. This blog focuses on Chrome notifications on Android mobile devices such as phones and tablets, and how McAfee Mobile Security protects users from malicious sites leveraging these notifications.
Most users are unaware of the source of these notifications. Permission is granted when a user clicks ‘Allow’ on a prompt within Android Chrome.
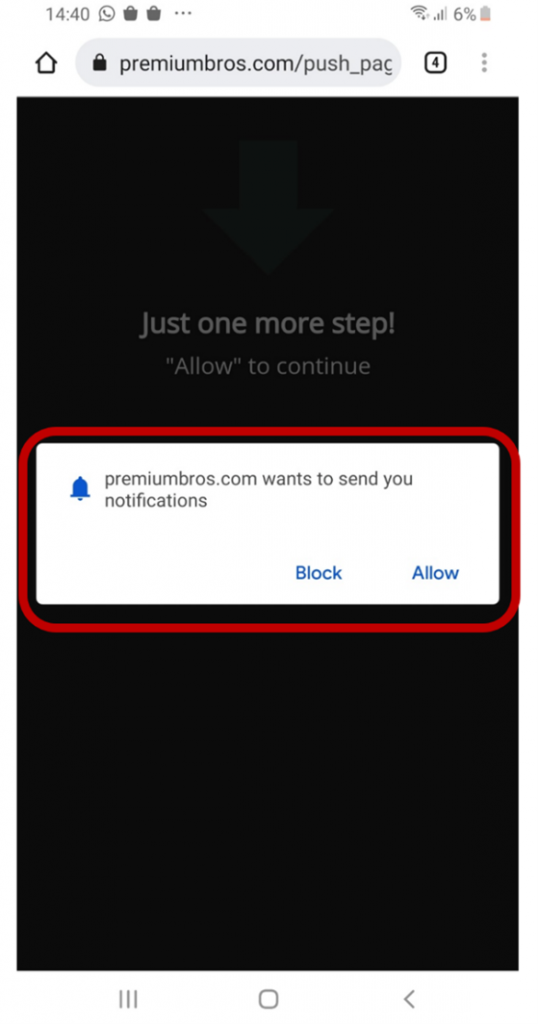
Many malicious websites use language and images like the one above that entice the user to click ‘Allow’ such as ‘Just one more step! Click “Allow” to continue. Once allow is clicked, the website is added to a site permissions list, which will enable it to send notifications.
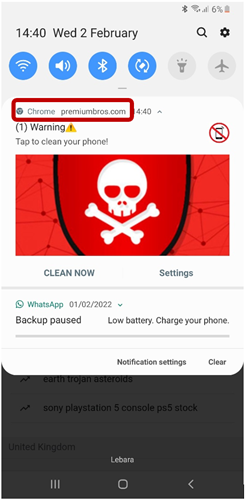
The notifications will look like a usual Android notification which you will be used to seeing such as you have a new WhatsApp message or email. To identify the source of the notification, we need to look for the application name which is like the one highlighted in the red box below.
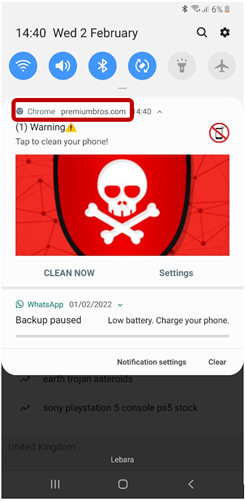
The image above shows the notification came from Chrome and it is from the website premiumbros[.]com. This is something you should pay attention to as it will be needed when you want to stop annoying notifications.
Some notifications like the ones in this blog are malicious as they attempt to trick users into believing that their mobile device is infected with a virus and some action is required. When the users click the notification, Chrome will load a website which will present them with a fake warning like the example below:
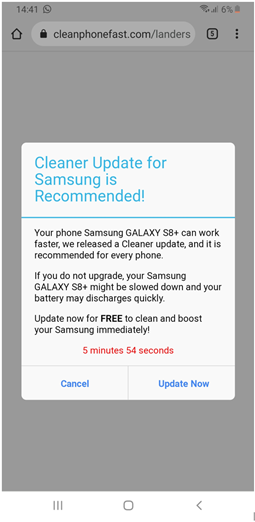
Clicking either Cancel or Update Now on the above website will result in the same behavior. The browser will redirect the user to a google play store app so that they can download and install it.
The malicious websites will flood your phone with several notifications. The screenshot below shows an example of this:
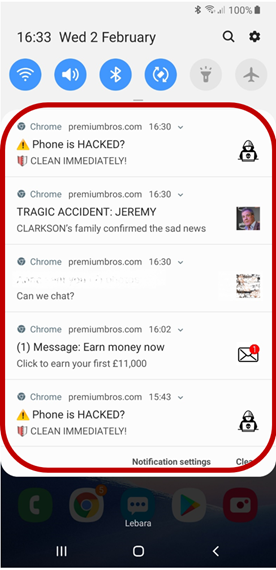
You may ask yourself, why do malicious actors try to get me to install a google play application? The people behind these scams receive a commission when these applications are installed on devices. They rely on deceptive tactics to trick users into installing them to maximize profits.
To remove a website’s notification permission, you need to change a Chrome setting.
1- Find out the name of the website which is sending these notifications. This can be done by looking at the notification and noting down the name of the website. If we use this blog as an example, it would be premiumbros[.]com
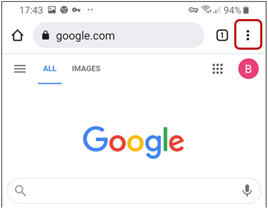
2- Open the Chrome browser app which can be found by performing the following search:
![]()
3- Click the three … on the top right hand of the application
4- Scroll down and click on settings
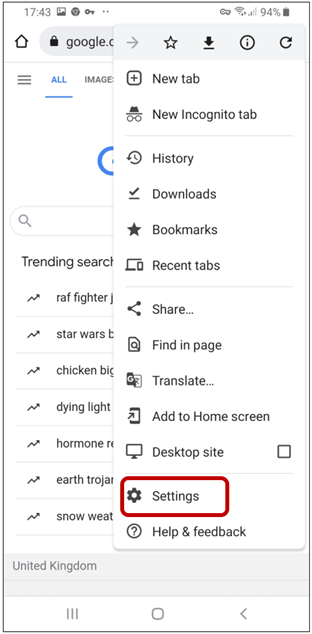
5- Click on Notifications
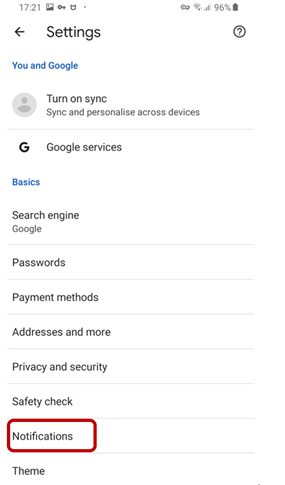
6- Scroll down until you find the website which you identified in step 1
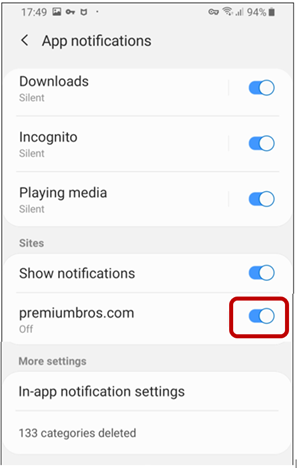
7- Pres the blue radio button so it turns grey
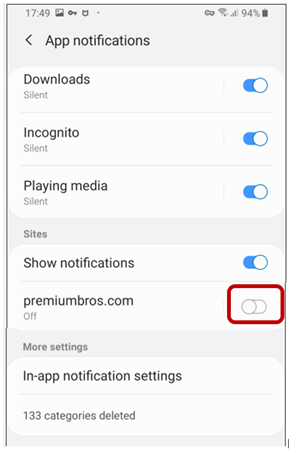
8- Notifications will now be disabled for that website. If you want to block multiple websites, click the radio button for them as well.
McAfee customers who have McAfee Mobile Security are protected against these malicious websites as long as they enable the ‘Safe Browsing’ feature within the application.
Upon trying to access a malicious website such as the one in the blog it will be blocked as shown in the image below:
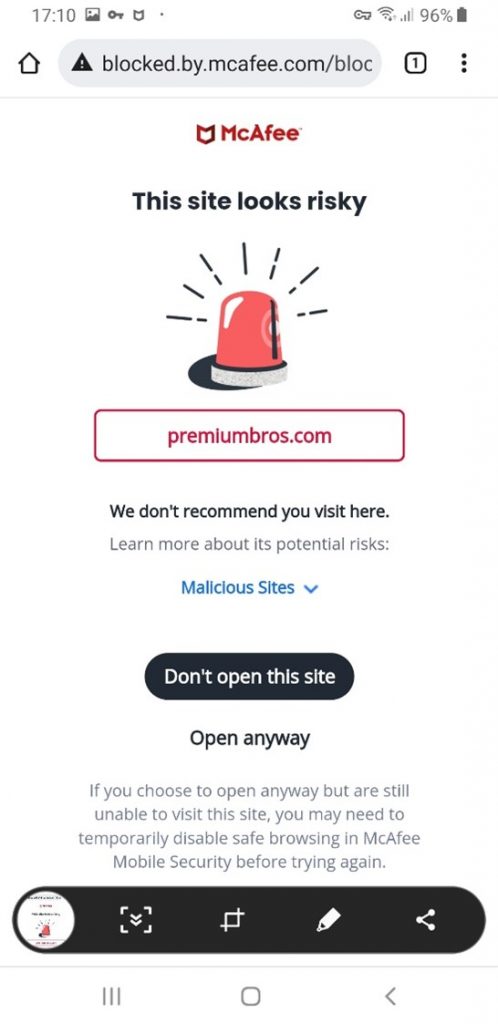
Please read this guide on enabling the Safe Browsing feature within the Mobile Security Application.
The post Why Am I Getting All These Notifications on my Phone? appeared first on McAfee Blog.

It’s a long-standing question. Can Apple Macs get viruses?
While Apple does go to great lengths to keep all its devices safe, this doesn’t mean your Mac is immune to all computer viruses. So what does Apple provide in terms of antivirus protection? Let’s take a look along with some signs that your Mac may be hacked and how you can protect yourself from further threats beyond viruses, like identity theft.
Whether hackers physically sneak it onto your device or by tricking you into installing it via a phony app, a sketchy website, or a phishing attack, viruses and malware can create problems for you in a few ways:
Some possible signs of hacking software on your Mac include:
Is your device operating more slowly, are web pages and apps harder to load, or does your battery never seem to keep a charge? These are all signs that you could have malware running in the background, zapping your device’s resources.
Like the performance issues above, malware or mining apps running in the background can burn extra computing power (and data). Aside from sapping performance, malware and mining apps can cause your computer to run hot or even overheat.
If you find apps you haven’t downloaded, along with messages and emails that you didn’t send, that’s a red flag. A hacker may have hijacked your computer to send messages or to spread malware to your contacts. Similarly, if you see spikes in your data usage, that could be a sign of a hack as well.
Malware can also be behind spammy pop-ups, changes to your home screen, or bookmarks to suspicious websites. In fact, if you see any configuration changes you didn’t personally make, this is another big clue that your computer may have been hacked.
Macs contain several built-in features that help protect them from viruses:
Similarly, all apps that wish to be sold on the Apple App Store must go through Apple’s App Review. While not strictly a review for malware, security matters are considered in the process. Per Apple, “We review all apps and app updates submitted to the App Store in an effort to determine whether they are reliable, perform as expected, respect user privacy, and are free of objectionable content.”
There are a couple reasons why Mac users may want to consider additional protection in addition to the antivirus protection that Mac provides out of the box:
In all, Macs are like any other connected device. They’re susceptible to threats and vulnerabilities as well. Looking more broadly, there’s the wider world of threats on the internet, such as phishing attacks, malicious links and downloads, prying eyes on public Wi-Fi, data breaches, identity theft, and so on. It’s for this reason Mac users may think about bolstering their defenses further with online protection software.
Staying safer online follows a simple recipe:
Reading between the lines, that recipe can take a bit of work. However, comprehensive online protection can take care of it for you. In particular, McAfee Total Protection includes an exclusive Protection Score, which checks to see how safe you are online, identifies gaps, and then offers personalized guidance, and helping you know exactly how safe you are.
An important part of this score is privacy and security, which is backed by a VPN that turns on automatically when you’re on an unsecure network and personal information monitoring to help protect you from identity theft—good examples that illustrate how staying safe online requires more than just antivirus.
So, Macs can get viruses and are subject to threats just like any other computer. While Macs have strong protections built into them, they may not offer the full breadth of protection you want, particularly in terms of online identity theft and the ability to protect you from the latest malware threats. Consider the threats you want to keep clear of and then take a look at your options that’ll help keep you safe.
The post Can Apple Macs get Viruses? appeared first on McAfee Blog.

Can thieves steal identities with only a name and address?
In short, the answer is “no.” Which is a good thing, as your name and address are in fact part of the public record. Anyone can get a hold of them. However, because they are public information, they are still tools that identity thieves can use.
If you think of your identity as a jigsaw puzzle, your name and address are the first two pieces that they can use to build a bigger picture and ultimately put your identity at risk.
With that, let’s look at some other key pieces of your identity that are associated with your name and address—and what you can do to protect them.
For starters, this information is so general that it is of little value in of itself to an identity thief. Yet a determined identity thief can do a bit of legwork and take a few extra steps to use them as a springboard for other scams.
For example, with your name and address a thief could:
There are volumes of public information that are readily available should someone want to add some more pieces to your identity jigsaw puzzle, such as:
In the U.S., the availability of such information will vary from state-to-state and different levels of government may have different regulations about what information gets filed—in addition to whether and how those reports are made public. Globally, different nations and regions will collect varying amounts of public information and have their own regulations in place as well. More broadly, though, many of these public databases are now online. Consequently, accessing them is easier than the days when getting a hold of that information required an in-person visit a library or public office.
Thieves can gain additional information about you from other online sources, such as data brokers. And data brokerage is a big business, a global economy estimated at $200 billion U.S. dollars a year. What fuels it? Personal information, representing thousands of data points on billions of people scraped from public records, social media, smartphone apps, shopper loyalty cards, third-party sources, and sometimes other data broker sites as well.
The above-the-board legal intent of data broker sites is to sell that information to advertisers so that they can create highly targeted campaigns based on people’s behaviors, travels, interests, and even political leanings. Others such as law enforcement officials, journalists, and others who are conducting background checks will use them too.
On the dark side, hackers, scammers, and thieves will buy this information as well, which they can use to commit identity theft and fraud. The thing is, data brokers will sell to anyone. They don’t discriminate.
Phishing attacks aren’t just for email, texts, and direct messages. In fact, thieves are turning to old tricks via old-fashioned physical mail. That includes sending phony offers or by impersonating officials of government institutions, all designed to trick you into giving up your personally identifiable information (PII).
What might that look like in your mailbox? They can take the form of bogus lottery prizes that request bank information for routing (non-existent) winnings. Another favorite of scammers are bogus tax notifications that demand immediate payment. In all, many can look quite convincing at first blush, yet there are ready ways you can spot them. In fact, many of the tips for avoiding these physical mail phishing attacks are the same for avoiding phishing attacks online, which we outline in detail here.
Recently, I’ve seen a few news stories like this where thieves reportedly abuse the change-of-address system with the U.S. Postal Service. Thieves will simply forward your mail to an address of their choosing, which can drop sensitive information like bank and credit card statements in their mailbox. From there, they could potentially have new checks sent to them or perhaps an additional credit card—both of which they can use to drain your accounts and run up your bills.
The Postal Service has mechanisms in place to prevent this, however. Among which, the Postal Service will send you a physical piece of mail to confirm the forwarding. So, if you ever receive mail from the Postal Service, open it and give it a close look. If you get such a notice and didn’t order the forwarding, visit your local post office to get things straightened out. Likewise, if it seems like you’re missing bills in the mail, that’s another good reason to follow up with your post office and the business in question to see if there have been any changes made in your mail forwarding.
So while your name and address are out there for practically all to see, they’re largely of little value to an identity thief on their own. But as mentioned above, they are key puzzle pieces to your overall identity. With enough of those other pieces in hand, that’s where an identity thief can cause trouble.
Other crucial pieces of your identity include:
Let’s start with the biggest one. This is the master key to your identity, as it is one of the most unique identifiers you have. As I covered in my earlier blog on Social Security fraud, a thief can unlock everything from credit history and credit line to tax refunds and medical care with your Social Security or tax ID number. In extreme cases, they can use it to impersonate you for employment, healthcare, and even in the event of an arrest.
You can protect your Social Security Number by keeping it locked in a safe place (rather than in your wallet) and by providing your number only when absolutely necessary. For more tips on keeping your number safe, drop by that blog on Social Security fraud I mentioned.
Thieves have figured out ways of getting around the fact that IDs like these include a photo. They may be able to modify or emulate these documents “well enough” to pull off certain types of fraud, particularly if the people requesting their bogus documents don’t review them with a critical eye.
Protecting yourself in this case means knowing where these documents are at any time. (With passports, you may want to store those securely like your Social Security or tax ID number.) Also be careful when you share this information, as the identifiers on these documents are highly unique. If you’re uncomfortable with sharing this information, you can ask if other forms of ID might work—or if this information is really needed at all. Also, take a moment to make copies of these documents and store them in a secure place. This can help you provide important info to the proper authorities if they’re lost or stolen.
With data breaches large and small making the news (and many more that do not), keeping a sharp eye on your accounts is a major part of identity theft prevention. We talk about this topic quite often, and it’s worth another mention because protecting these means protecting yourself from thieves who’re after direct access to your finances and more.
Secure your digital accounts for banking, credit cards, financials, and shopping by using strong, unique passwords for each of your accounts that you change every 60 days. Sound like a lot of work? Let a password manager do it for you, which you can find in comprehensive online protection software. By changing your strong passwords and keeping them unique can help prevent you from becoming a victim if your account information is part of a breach—by the time a crook attempts to use it, you may have changed it and made it out of date.
In addition to protecting the core forms of identity mentioned above, a few other good habits go a long way toward keeping your identity secure.
By protecting your devices, you protect what’s on them, like your personal information. Comprehensive online protection software can protect your identity in several ways, like creating and managing the strong, unique passwords we talked about and providing further services that monitor and protect your identity—in addition to digital shredders that can permanently remove sensitive documents (simply deleting them won’t do that alone.) Further, it can monitor your identity and monitor your credit, further protecting you from theft and fraud.
Identity theft where thieves dig through trash or go “dumpster diving” for literal scraps of personal info in bills and statements, has been an issue for some time. You can prevent it by shredding up any paper medical bills, tax documents, and checks once you’re through with them. Paper shredders are inexpensive, and let’s face it, kind of fun too. Also, if you’re traveling, have a trusted someone collects your mail or have the post office put a temporary hold on your mail. Thieves still poach mail from mailboxes too.
Getting statements online cuts the paper out of the equation and thus removes another thing that a thief can physically steal and possibly use against you. Whether you use electronic statements through your bank, credit card company, medical provider, or insurance company, use a secure password and a secure connection provided by a VPN. Both will make theft of your personal info far tougher on identity thieves.
A VPN is a Virtual Private Network, a service that protects your data and privacy online. It creates an encrypted tunnel to keep you more anonymous online by masking your IP address, device information, and the data you’re passing along that connection. In this way, it makes if far more difficult for advertisers, data brokers, and bad actors to skim your private information—in addition to shielding your information from crooks and snoops while you’re banking, shopping, or handling any kind of sensitive information online.
Give your statements a close look each time they come around. While many companies and institutions have fraud detection mechanisms in place, they don’t always catch every instance of fraud. Look out for strange purchases or charges and follow up with your bank or credit card company if you suspect fraud. Even the smallest charge could be a sign that something shady is afoot.
This is a powerful tool for spotting identity theft. And in many cases, it’s free to do so. In the U.S., the Fair Credit Reporting Act (FCRA) requires the major credit agencies to provide you with a free credit check at least once every 12 months. Canada provides this service, and the UK has options to receive free reports as well, along with several other nations. It’s a great idea to check your credit report, even if you don’t suspect a problem.
If the thought of your personal info being bought and sold puts you off, there’s something you can do about it. Our Personal Data Cleanup service can scan some of the riskiest data broker sites and show you which ones are selling your personal info. It also provides guidance on how you can remove your data from those sites, and with select products, it can even manage the removal for you.
While thieves need more than just your name and address to commit the overwhelming majority of fraud, your name and address are centerpieces of the larger jigsaw puzzle that is your overall identity.
And the interesting thing is your puzzle gets larger and larger as time goes on. With each new account you create and service that you sign into, that’s one more piece added to the puzzle. Thieves love getting their hands on any pieces they can because with enough of them in place they can try and pull a fast one in your name. By looking after each piece and knowing what your larger jigsaw puzzle looks like, you can help keep identity thieves out of your business and your life.
The post Can Thieves Steal Identities With Only a Name and Address? appeared first on McAfee Blog.

A good time to check if someone is using your identity is before it even happens.
One of identity theft’s several downsides is how people discover they’ve become a victim in the first place—by surprise. They go to rent an apartment, open a line of credit, or apply for financing, only to discover that their finances or reputation has taken a hit because of identity thief.
And those hits add up, particularly when you look at the dollars involved. In 2020, the Federal Trade Commission (FTC) reported $3.3 billion in financial losses from 4.7 million reported cases of fraud, a 45% increase over the year prior. Of those reports, identity theft was the leading fraud category, accounting for 29% of fraud incidents.
Plenty. Depending on the type and amount of information an identity thief gets their hands on, they can harm your finances and reputation in several ways, including:
Rather than ending up with a rude and potentially costly surprise of your own, you can get ahead of thieves by checking to see if someone is using your identity before it’s a problem or before it really takes root.
Major data breaches that expose personal information seem to hit the headlines with some regularity, not to mention the many, many more that don’t get national or international press coverage. Most recently we have the Neiman Marcus breach, where this major retailer alerted 4.6 million customers that “an unauthorized party obtained personal information associated with certain Neiman Marcus customers’ online accounts.”
And as it is with many such breaches, it took quite some time before the theft of information was discovered. Per Neiman Marcus, it’s believed that the breach occurred in May 2020 and only discovered in September of 2021. Potentially compromised information included:
Whether or not you have reason to suspect that your information got caught up in this recent large-scale breach, it serves as a good reminder that any time is the right time to check up on your identity. Acting now can save headaches, potentially big headaches, later.
Quite a bit of identity theft prevention begins with taking stock of the accounts and services you have in your name. This ranges anywhere from bank accounts to public utilities and from credit cards to loans, all of which contain varying degrees of personal information about you. With a sense of where your personal identity is being used, you can better look for instances where it’s being misused.
Ways you can spot for possible identity theft include:
If you stop receiving a bill that normally comes to you, such as a utility bill or for a department store credit card, that could be a sign that a thief has changed the mailing address and has potentially hijacked your identity.
This is rather straightforward, yet it reminds us how important it is to look at our statements closely. Charges that you didn’t ring up or that seem slightly higher than normal are a surefire sign that you should follow up with the bank or company involved and let them know of possible fraud.
In the U.S., you have annual access to free credit reports from the major credit reporting agencies. Not only will this give you a sense of your credit score, but it will also show the credit that’s open in your name, along with addresses associated with your identity. Spotting an account that you haven’t signed up for or seeing an address of a residence that you’re not renting are other common signs that your identity may have been compromised.
With the number of accounts many of us have these days, a credit monitoring service can help you stay on top of what’s happening in your name. Often offered through banks, credit unions, and even insurance providers, credit monitoring can alert you in several instances, including:
Overall, credit monitoring can act as another set of eyes for you and spot potential identity issues. Different services provide different levels of monitoring, so consider reviewing a few options to find the one that works best for you.
One like our own Identity Protection Service will monitor several types of personally identifiable information, alert you of potentially stolen personal info, and offer guided help to neutralize the threat—in addition to offering several preventative steps to help keep theft from happening in the first place. With this set up on your computers and smartphone you can stay in the know and address issues immediately.
Along with keeping an eye on what’s happening with your identity online and elsewhere, there are a few more things you can do to make it tougher for thieves to steal your identity.
Given all the banking and shopping we do on our computers and phones, installing and using comprehensive online protection software is a must these days. It puts several layers of security in place, such as creating complex passwords automatically, shielding credit card info from prying eyes, and protecting your privacy and data online by connecting with a VPN. In short, online protection software acts as a solid first line of defense.
As mentioned above, comprehensive online protection software often includes a password manager that can generate strong, unique passwords for each of your accounts and remember them for you. It’s extra protection that makes life a lot easier for you by managing all the accounts you’re juggling. Also, use MFA (multi-factor authentication) on the accounts that give you the option, which makes it harder for a thief to crack your accounts with a password alone.
Sensitive documents come in all forms. Top-of-the-line examples include things like tax returns, bank statements, and financial records. Yet there are also things like your phone and utility bills, statements from your doctor’s office, and offers that come to you via mail. Together, these things can contain personal information such as account numbers, your full Social Security Number, the last four digits of your Social Security Number (which can still be useful to thieves), and other information that may uniquely identify you. You’ll want to dispose of sensitive documents like these so that they can’t be harvested by hackers.
For physical documents, consider the low-cost investment of a paper shredder to help ensure they don’t fall into the wrong hands when you are done with them. (And let’s face it, they’re fun to use!) For digital documents, simply deleting a file is not enough – online protection software is a great resource that often includes a digital document shredder, designed to render the data practically unusable when you’re ready to trash the file.
Your Social Security Number is one of the most prized possessions a thief can run away with because it is so closely associated with you and things like your tax returns, employment, and so on. Keep it stored in a safe location rather than on your person or in your wallet. Likewise, be careful about giving out your SSN. While organizations like the IRS, your bank, and employer require it, there are other organizations who do not—but may ask for it anyway. (Doctor’s offices are a prime example.) If you get such a request, ask them what they intend to use it for and then ask if another form of identification will work instead.
Phishing attacks are one of the primary ways identity thieves steal personal information. Whether they come via a direct message, on social media, or through email, text, or phone calls, thieves use them to harvest your personal info by posing as a legitimate organization—such as in this recent IRS phishing scam. Phishing is a topic all unto itself, and you can check out this quick read to see how you can spot phishing scams and protect yourself from them.
Like any criminal, identity thieves do their dirtiest work in the shadows—quietly stealing money under your nose, or worse, as we outlined above. By shining a light on your identity and keeping regular track of what’s happening with it, you can spot unusual activity right away. Even the small stuff is important. A co-worker of mine once saw an incorrect address listed on his credit report. Turned out, that address was used to rack up several large charges at a retailer, which he was able to fix with the aid of the credit reporting agency and the retailer in question.
No doubt about it. Identity theft is indeed on the rise, and your best bet to avoid such a nasty surprise is to keep an eye on your digital identity the same way you keep an eye on your actual wallet.
The post How to Check if Someone is Using Your Identity appeared first on McAfee Blog.

You may have heard the news that more than 300,000 Android users unknowingly downloaded banking trojan apps from the Google Play Store, malicious apps which bypassed the store’s security detections to install malware.
This news comes from a security report that found these trojans cleverly posed as apps that people commonly search for, such as QR code scanners, fitness apps, and a bevy of other popular types of utilities. In fact, these phony apps contain trojans that are designed to steal banking information, harvest keystrokes as you enter account info, and even grab screenshots of what you’re doing on your phone.
The trick with this malware is that it only activates after it is installed, which may or may not be apparent to the user. For the malware to activate, it requires an extra step, such as an in-app update (not through the Play Store), which then downloads the payload of malware onto the phone. In many cases, the bogus apps force users to make this update once the app is downloaded.
So, while the apps that appeared in the Play Store may not have contained malware, they deliver the payload onto the user’s phone post-purchase from other servers, which is a reason why these malicious apps have not been readily flagged.
All of this is just one more way hackers have found to infect smartphones with malware.
It’s no wonder that they target smartphones. They’re loaded with personal info and photos, in addition to credentials for banking and payment apps, all of which are valuable to loot or hold for ransom. Add in other powerful smartphone features like cameras, microphones, and GPS, and a compromised phone may allow a hacker to:
All of that adds up to one thing—a great, big “no thanks!”
So how do these sorts of malicious apps work? By posing as legitimate apps, they can end up on your phone and gain broad, powerful permissions to files, photos, and functionality—or sneak in code that allows cybercriminals to gather personal info. As a result, that can lead to all kinds of headaches, ranging from a plague of popup ads to costly identity theft.
Here are a few recent examples of malicious apps in the news:
Again, “no thanks!” So, let’s see about steering clear of malicious apps like these.
The good news is that there are ways you can spot these imposters. Major app marketplaces like Google Play and Apple’s App Store do their part to keep their virtual shelves free of malware, as reported by Google and Apple themselves. Still, cybercriminals can find ways around these efforts. (That’s what they do, after all!) So, a little extra precaution on your part will help you stay safer. These steps can help:
Another way cyber criminals weasel their way into your device is by getting permissions to access things like your location, contacts, and photos—and they’ll use sketchy apps to do it. (Consider the long-running free flashlight app scams mentioned above that requested up to more than 70 different permissions, such as the right to record audio, video, and access contacts.) So, pay close attention to what permissions the app is requesting when you’re installing it. If it’s asking for way more than you bargained for, like a simple game wanting access to your camera or microphone, it may be a scam. Delete the app and find a legitimate one that doesn’t ask for invasive permissions like that.
Additionally, you can check to see what permissions an app may request before downloading the app. In Google Play, scroll down the app listing and find “About this app.” From there, click “App permissions,” which will provide you with an informative list. In the iOS App Store, scroll down to “App Privacy” and tap “See Details” for a similar list. If you’re curious about permissions for apps that are already on your phone, iPhone users can learn how to allow or revoke app permissions here, and Android can do the same here.
While some apps (like games) rely on downloadable content from within the app, look out for apps that prompt you for an immediate update directly from the app. For the most part, the app you download from the store should be the most recent version and not require an update. Likewise, update your phone through the app store, not the app itself, which can help you avoid malware-based attacks like these.
As with so many attacks, cybercriminals rely on people clicking links or tapping “download” without a second thought. Before you download, take time to do some quick research, which may uncover a few signs that the app is malicious. Check out the developer—have they published several other apps with many downloads and good reviews? A legit app typically has quite a few reviews, whereas malicious apps may have only a handful of (phony) five-star reviews. Lastly, look for typos and poor grammar in both the app description and screenshots. They could be a sign that a hacker slapped the app together and quickly deployed it.
Even better than combing through user reviews yourself is getting a recommendation from a trusted source, like a well-known publication or from app store editors. In this case, much of the vetting work has been done for you by an established reviewer. A quick online search like “best fitness apps” or “best apps for travelers” should turn up articles from legitimate sites that can suggest good options and describe them in detail before you download.
Unlike Google Play and Apple’s App Store, which have measures in place to review and vet apps to help ensure that they are safe and secure, third-party sites may not have that process in place. In fact, some third-party sites may intentionally host malicious apps as part of a broader scam. Granted, cybercriminals have found ways to work around Google and Apple’s review process, yet the chances of downloading a safe app from them are far greater than anywhere else. Furthermore, both Google and Apple are quick to remove malicious apps once discovered, making their stores that much safer.
With all that we do on our phones, it’s important to get security software installed on them, just like we do on our computers and laptops. Whether you go with comprehensive security software that protects all of your devices or pick up an app in Google Play or Apple’s iOS App Store, you’ll have malware, web, and device security that’ll help you stay safe on your phone.
Hand-in-hand with installing security software is keeping your phone’s operating system up to date. Updates can fix vulnerabilities that cybercriminals rely on to pull off their malware-based attacks—it’s another tried and true method of keeping yourself safe and your phone running in tip-top shape.
Here are a few more things you can do:
Lastly, you can always ask yourself, “Do I really need this app?” One way to avoid malicious mobile apps is to download fewer apps overall. If you’re unsure if that free game is on the up-and-up or if the offer for that productivity app sounds a little too good, skip it. Look for a better option or pass on the idea altogether. As said earlier, cybercriminals really rely on us clicking and downloading without thinking. Staying on guard against mobile malware will cost you a few moments of your time, which is minimal compared to the potential costs of a hacked phone.
The post Before You Download: Steer Clear of Malicious Android Apps appeared first on McAfee Blog.

Customers often ask us some version of this question. It’s a good question and in the past, there was no direct answer – only recommendations. For instance, we recommend online protection that goes beyond antivirus to include identity and privacy protection, as well as promoting safety best practices like using multi-factor authentication. We wondered if there was a simpler and easier way to advise customers how to better protect themselves.
A recent survey shows how important online security has become to consumers. We found that 74% of you have concerns about keeping your information private online. 57% want to be more in control of their personal info online. And, since the pandemic started, 47% of online consumers feel unsafe compared to 29%. Simply put, customers are more conscious of their safety online than ever before, and eager to play an active role in their protection.
It’s time for a new approach – meet the Protection Score.
If you’re thinking this looks like a credit, fitness, sleep, or any of the other scores we now use to visualize and quantify aspects of our life, you’re on the right track.
Your personalized Protection Score is a measure of your security online. The higher your score, the safer you are online. Your score will highlight any weaknesses in your security and help you fix them with easy step-by-step instructions. We’ll also let you know which features haven’t been setup so you can get the most out of your protection.
When we developed Protection Score the idea was to give customers a simple solution to better protect themselves and get the most from their subscription, including security tips to protect their identity, privacy, and devices, while also improving their online habits. We wanted it to be easy for anyone to:
Now that we’ve talked about Protection Score generally, let’s look at how it works in practice. Your score is based on a few things, including setting up your McAfee protection, strengthening your security with our safety recommendations, and ensuring your personal info is safely monitored with Identity Protection.
For example, if your information is exposed in a data breach your score may drop, but you can improve it by following our easy-to-follow remediation steps. Once you’ve completed those steps your score will go back up and you can be confident knowing you’re better protected online.
A perfect score does not mean you’re perfectly safe, but it does mean that you’re doing an excellent job of preventing and managing risks.
Your Protection Score is a great way to understand how safe you are at a glance. Additionally, improving your score ensures your life online is being protected by many of the safety features and benefits McAfee has to offer. For instance, the subscriber, John Smith, can see they’re fairly safe based on their score. However, it isn’t a perfect score and there are a few actions they could still take to improve it. In this case, adding their email and phone number to dark web monitoring – a crucial step in protecting their personally identifiable information online.

Protection Score can be easily accessed* from your browser of choice on any device so you can review our guidance and take steps to improve your score from wherever you are. McAfee’s Protection Score is a first for the cybersecurity industry, but we’re not stopping there. We’re going to continue to improve the feature by adding more personalization and accessibility so you can enjoy your life online knowing exactly how protected you are.
*Note that Protection Score is currently live in the US, Canada, Brazil, Australia, New Zealand, Japan, UK, Germany, France, Spain, and Italy.
The post Stay on top of your online security with our Protection Score appeared first on McAfee Blog.

For some, vanquishing aliens, building virtual amusement parks, and online battles royale are an excellent stress reliever. As we all know, over the past year there’s been plenty of stress to relieve and more spare time on our hands in which to revel in our hobbies. There was a 30% jump in online gaming traffic from the first to the second quarter of 2020.
Hackers are taking advantage of highly trafficked online gaming portals to make a profit on the dark web. The next time you log on to your virtual world of choice, consider these recent video game breaches and up your gamer security, which could include an antivirus for gaming.
Between 2019 and 2020, web attacks on gaming companies rocketed up 340%, according to Akamai. Hackers have targeted several high-profile gaming companies recently with various motives. First, game source code was stolen from Electronic Arts to sell on the dark web. Developers shopping the dark web use stolen source codes to reverse-engineer popular games or copy the code into their own game. Capcom and CD Projekt Red were hit by ransomware attacks only a few months apart from each other, one attack focused on company financial information and the other on source code.
“Titan Fall” and “Apex Legends” have both been hacked to the point where the former is unplayable, according to many gamers. To protest “Titanfall’s” developers’ inaction, gamers took to “Apex Legends,” altering in-game messages. The apparent ease with which hackers can walk into online gaming portals requires that game developers and gamers themselves pay more attention to their security.
Online PC gaming allows players to use real-world money to purchase valuable upgrades to their characters. These characters receive admiration from some fellow players. Others feel greed. Advanced characters can fetch a lot of money on the dark web, so some cybercriminals practice credential stuffing to force their way into player accounts and steal ownership. Credential stuffing is a type of brute force attack where hackers take informed guesses at username and password combinations. A strong password or passphrase is essential to keeping your account and investment safe from a dark web fate.
Based on the above recent hacks, it is clear that gaming companies host a trove of valuable information. Gamers trust these platforms with their payment information and with the safety of their gaming characters on which they spend thousands of hours and hundreds of dollars upgrading, making gaming a lucrative target for hackers.
Another way cybercriminals target gamers is through malware disguised as an advantage. Cheat software for online games is common as players strive to be the best out of thousands. Advantage seekers for “Call of Duty: Warzone” were targeted by a malware scam. The malware creators advertised the “cheat software” on YouTube with instructions on how to download it. The video received thousands of views and hundreds of comments, which made it look legitimate.
One of the steps in installing the “cheat software” was that users had to disable antivirus programs and firewalls. Users let the cybercriminals walk right into their device! From there, the device was infected by an aggressive type of fileless malware called a dropper. A dropper doesn’t download a malicious file onto the device; rather, it creates a direct pathway to deliver an additional payload, such as credential-stealing malware.
Competitive gaming is, well, competitive. So, if you invest a lot of real money into your characters, be especially vigilant and follow these five important tips to protect your online accounts.
It’s common for gamers to use variations of their real names and birthdates in their public-facing usernames. Don’t use your real name or birthdate in your username. Consider using a nickname or a combination of random numbers instead. Along this same vein, don’t reveal personal details about yourself (phone number, birthday, places you visit regularly) on chats or streams. Lurking cybercriminals can gather these personal details to impersonate you.
On some online PC games, you can join campaigns with gamers from all over the world. While the interconnectivity is great, carefully vet who you allow to follow your online profile. If a stranger sends a friend request out of the blue, be on alert. They could have nefarious motives, such as phishing for valuable personal data. It’s best to customize your privacy settings to make your profile invisible to strangers.
Developers spend a lot of time creating amazing games, so make sure you purchase games legally and play them as they are intended. Be especially wary of free downloads or pirated versions and cheat software, as they’re likely too good to be true. Instead, go for a challenge and have fun with the game as it’s written.
A virtual private network (VPN) scrambles your online data traffic, making it impossible for hackers to access your IP address and spy on your online browsing.
Gaming antivirus software not only makes your online gaming experience more secure, but it can boost your rig’s performance! McAfee Gamer Security detects threats through the cloud and optimizes resources to minimize frame drops.
The post 5 Online Gaming Tips to Stay Safe From Hackers appeared first on McAfee Blogs.

There’s a lot of misinformation about Virtual Private Networks, what they do, and the security benefits they offer. For this article, I’d like to do some myth-busting about how a VPN actually works and why you should use one.
A VPN is an app that you install on your device to help keep your personal data safe as you browse the internet
You may have heard that VPN apps live on your device and allow you to connect to the internet securely. What that means is, when you turn your VPN app on, your device makes a secure connection to a specialized computer that routes internet traffic, called a VPN server. You also may have heard that your connection is “wrapped in an encrypted tunnel” which means your device and the server share a secure connection so only you can see what you’re doing on the internet.
Every internet connection (like your cable modem) is assigned a unique set of numbers called an IP address, which is tied to information such as geographic location, ISP, etc. A VPN replaces your actual IP address to make it look like you’ve connected to the internet from a different location: the physical location of the VPN server, rather than your real location. This is just one reason why so many people use VPNs. This can be handy when you want to hide from advertising trackers or protect your search history.
To change your IP address, you simply open your VPN app, select the server location you’d like to connect to, and you’re done. You’re now browsing with a new IP address. If you’d like to make sure your IP has changed, open up a browser and search for “What’s my IP address” and click on one of the results.
When to use a VPN really depends on what you want it for. For example, 39% of users understand public Wi-Fi is unsafe but still do sensitive things, like banking or shopping on public WiFi, so using a VPN when you’re at the airport, or a café is a great use case.
As I mentioned before, a lot of people use a VPN for privacy reasons, like stopping advertisers from tracking them. Searches you perform, or websites you visit won’t be trackable, which means you’ll be able to surprise your spouse with a vacation you researched and planned on a computer you both use. Targeted ads could spoil things if your spouse is bombarded with ads for plane tickets and hotels while they browse.
A VPN protects your search history through the secure connection you share. When you search for a website, or type a URL into your navigation bar, your device sends something called a DNS request, which translates the website into the IP address of the web server; this is how your browser can find the website and serve its content to you. By encrypting your DNS requests, a VPN can hide your search habits and history from those that might use that info as part of building a profile of you. This type of info could be used in a wide variety of ways, from legitimately serving targeted ads to nefarious social engineering.
A VPN can protect your identity by blocking online trackers from following you around the internet. With your VPN on, trackers will think all of your browsing is coming from a different device in a different location. This throws off the profile advertisers try to build because they think you’re someone else.
Another way a VPN can protect your identity is by preventing some types of hacking. Stopping attacks on public WiFi where a bad actor tries to get between you and the website you’re visiting, is just one way VPNs can help. It’s called a Man-in-the-Middle attack, but that’s a subject for another article.
No, a VPN cannot make you anonymous. They help secure what you’re doing, but your ISP still knows when you’re using the internet. They just can’t see what you’re doing, what sites you visit, or how long you’ve been on a site.
Private browsing modes can help protect your privacy, but they’re useful if you share a device with other people and you don’t want them to see your search history. You can read all about the differences in the article I wrote a little while ago.
Apple’s Private Relay is currently in Beta and will be available with an iCloud+ subscription for Safari users on iOS and macOS soon. Private Relay is similar to a VPN in that it changes your IP address so websites you visit can’t tell exactly where you are.
When you turn Private Relay on, your device connects to a server that sends your browsing data to a second server, before it travels through the internet. The reason for the double hop is that first server gives you a new IP address, to make you harder to track, while the second server hides that information from the website you’re browsing. The first server only knows your original IP address, while the second server only knows what you’re browsing, but not your IP.
Private Relay only works with Safari on iOS and macOS. Even if you are using an Apple device, a VPN is still a good idea because it will protect the information that your device sends outside of Safari.
If you’re already a McAfee Total Protection subscriber, you have access to unlimited VPN usage. Protect your personal information, like your banking information and credit cards, from prying eyes with McAfee Total Protection’s Secure VPN. If you haven’t already signed up, now’s the perfect time. McAfee Total Protection provides security for all your devices, giving you peace of mind while you shop, bank, and browse online.
The post What is a VPN and Can it Hide My IP Address? appeared first on McAfee Blogs.

Small business owners are getting a special deal on their online protection through a partnership between McAfee and Visa. With new ways of working creating online opportunities and risks for small business owners, McAfee and Visa have come together to offer comprehensive protection for a changed business landscape.
Designed to help you minimize costs and unexpected interruptions to your business, McAfee® Security for Visa cardholders provides award-winning antivirus, ransomware, and malware protection for all your company devices including PCs, smartphones, and tablets on all major platforms. Visa Small Business cardholders automatically save up to 40% with a 24-month package and up to 60% with a 12-month offer.
Safety features include:
McAfee’s security savings bundle is also part of Visa’s commerce in a box initiative, which has launched in six U.S. cities (D.C., Detroit, Atlanta, Miami, Los Angeles and Chicago). This program features a curated selection of offers, discounts, and bundles from Visa’s Authorize.net and Visa partners designed to help small businesses with what they need to move their business forward digitally — from accepting digital payments and building an eCommerce site to marketing to their audience in new ways and providing online marketing tools to run and protect their business.
The post Small Businesses Save Up to 60% in McAfee and Visa Partnership appeared first on McAfee Blogs.

It’s a question I get several times a year from anxious parents, either via a direct message, an email or even in line at the grocery store. It goes something like this: “What’s the one thing you wish you’d done better when monitoring your kids’ technology?”
Both of my kids are now young adults, and together, we survived a handful of digital mishaps. So, I tend to have a few answers ready. I’ll go into one of those answers in this post, and here it is: I’d physically pick up their phone more often and ask questions about the apps I didn’t recognize.
And here’s why.
There are the apps on your child’s phone that are familiar. They are the easy ones. We know what color they are, what their graphic avatars look like — the little ghost on the yellow background, the little bird, the camera on the bright purple and orange background. We may have gone through the app together or even use one or two of the apps ourselves. There’s Snapchat, TikTok, Twitter, YouTube, WhatsApp, Kik, and Instagram, among others. There are the mainstay photo apps (VSCO, Facetune, PicsArt) and games (The Sims, Fortnite, Minecraft). We may not like all the apps, but we’ve likely talked about the risks and feel comfortable with how your kids use them. With general recognition, it’s easy to have a false sense of security about what apps our kids are using.
Then, there are the apps on your child’s phone you know nothing about — and there are plenty. Rather than dismiss your concern because you don’t understand the app or because you may not have the energy to start an argument, next time, think about pausing to take a closer look. If you have concerns, address them sooner rather than later.
Here are just a few of the non-mainstream apps that kids use that may not be on your radar but may need a second look. Note: Every app has the potential to be misused. The apps mentioned here are also used every day for connection, entertainment, and harmless fun. Here are just a few this author has had experience with, and others commonly documented in the media.
Quick Tip: It’s possible a child might bury an app inside a folder or behind other apps on their home screens, making it harder to find. By going into settings in either iOS (Settings > General > iPhone Storage) or Android (Google Play Store > Apps >All), you can usually get a quick view of all the apps that exist on a phone.
Almost every app has privacy gaps if settings and monitoring are neglected. However, apps such as Live.Me, Game Pigeon, and Zoomerang (among many others) may have loopholes when it comes to age verification, location tracking, and gaps in personal data security. These gaps can give potential predators access to kids and increases opportunities for cyberbullying.
Safe Family Tip: Sit down with your kids, go through any unfamiliar apps, and use parental controls to monitor all family device activity.
If a child wants to keep activity or content secret from a parent, they will likely find a way. Some of the apps kids use to hide games, photos, or texts are encryption apps (apps that scramble content to outside sources) such as WhatsApp, Proton VPN, ProtonMail, Telegram, and Signal. Other secrecy apps are called vault apps (apps that can be disguised, hidden, or locked), such as Calculator, Vault, HideItPro, App Locker, and Poof.
Safe Family Tip: If you find one of these apps on your child’s phone, stay calm. Kids want privacy, which is normal. However, if the content you see is risky, remind your child that no content is 100% private, even if it’s in a vault app. In addition, commit to the ongoing dialogue that strengthens trust and together, considers setting safety expectations for devices, which may include parental controls.
Some apps, especially dating-type apps, require users to allow geotagging to connect you with people in your area. Yubo, which is an app like Tinder, is one your kids may be using that requires location to use it. Live.Me is another geotagging app.
Safe Family Tip: Go over the reasons location apps (and dating apps) are dangerous with your child. Sharing their location and meeting In Real Life (IRL) has become the norm to many kids. Remind them of the risks of this kind of behavior and together, put new boundaries in place.
The web is full of sketchy, dark pockets kids can stumble into. They can hear about a community forum or app from a friend and be wowed simply because it’s different and edgy. While there are plenty of harmless conversations taking place on these apps, spaces such as Discord, Reddit, and Twitch have reportedly housed communities’ extreme ideologies that target vulnerable kids.
Safe Family Tip: Be aware of behavior changes. Talk with your kids about the wide range of ideals and agendas promoted online, how to think critically about conversations and content, and most importantly, how to spot these communities.
Anonymity online is problematic for a plethora of reasons. Apps such as Yolo, Tumblr, and Tellonym, Omegle, YikYak, Whisper, LMK, MeetMe, are just a few of those apps to look for. Many of these apps are chat apps used to eventually meet up with new friends in real life (IRL). However, when apps allow anonymous accounts, it’s almost impossible to trace inappropriate content, threats, or bullying incidents.
Safe Family Tip: Kids get excited about making friends and having new experiences— so much so, they can ignore potential consequences. Discuss issues that may arise (catfishing, sextortion, scams, bullying) when people hide behind anonymous names and profiles. If needed, give real examples from the news where these apps have been connected to tragic outcomes.
Several apps and online communities have been connected to violence, hate content, intolerance, and fanaticism. A few of these sites include 4Chan, 8Chan, AnyChan, Gab, SaidIt.Net, and 8Kun, among many others.
Safe Family Tip: Note any behavior changes in your child. Talk often about digital literacy and being a responsible publisher (and consumer) of media online.
Staying in step with your child’s latest and greatest app affinity isn’t easy, and every parent makes mistakes in how they approach the task. However, kids of all ages (no matter how tech-savvy they are) need boundaries, expectations, and consistent and honest dialogue when it comes to digital habits and staying safe online. If you don’t know where to start (or start over), one first step is to start today and commit to staying aware of the digital risks out there. In addition, make time to have regular, open conversations with your child about their favorite apps — the ones you know about and the ones you may not.
The post Potentially Malicious Apps Your Kids May Use appeared first on McAfee Blogs.

Personal devices and the information they carry are incredibly valuable to their owners. It is only natural to want to protect your device like a royal family fortifying a medieval castle. Unlike medieval castles that depended upon layers and layers of protection (moats, drawbridges, spiky gates, etc.), personal devices thrive on just one defense: a devoted guard called antivirus software.
Increasing your personal device’s security detail with more than one guard, or antivirus software is actually less effective than using a single, comprehensive option. Microsoft operating systems recognize the detriment of running two antivirus software programs simultaneously for real-time protection. Microsoft Windows automatically unregisters additional programs so they do not compete against each other. In theory, if you have a Microsoft device, you could run on-demand or scheduled scans from two different antivirus products without the operating system disabling one of them. But why invest in multiple software where one will do?
If you do not have a Microsoft device, here is what could happen to your device if you run more than one antivirus program at a time, and why you should consider investing in only one top-notch product.
Antivirus programs want to impress you. Each wants to be the one to catch a virus and present you with the culprit, like a cat with a mouse. When antivirus software captures a virus, it locks it in a secure place to neutralize it. If you have two programs running simultaneously, they could engage in a tussle over who gets to scan, report, and remove the virus. This added activity could cause your computer to crash or use up your device’s memory.
Antivirus software quietly monitors and collects information about how your system runs, which is similar to how viruses operate. One software could mark the other as suspicious because real-time protection software is lurking in the background. So, while one antivirus program is busy blowing the whistle on the other, malicious code could quietly slip by.
Additionally, users could be buried under a barrage of red flag notifications about each software reporting the other as suspicious. Some users become so distracted by the onslaught of notifications that they deactivate both programs or ignore notifications altogether, leaving the device vulnerable to real threats.
Running one antivirus software does not drain your battery, and it can actually make your device faster. However, two antivirus programs will not double your operating speed. In fact, it will make it run much slower and drain your battery in the process. With two programs running real-time protection constantly in the background, device performance is extremely compromised.
There is no reason to invest in two antivirus programs when one solid software will more than do the trick to protect your device. Here are some best practices to get the most out of your antivirus software:
One habit you should adopt is backing up your files regularly. You never know when malware could hit and corrupt your data. Add it to your weekly routine to sync with the cloud and back up your most important files to an external hard drive.
Whenever your software prompts you to install an update, do it! New cyber threats are evolving every day, and the best way to protect against them is to allow your software to stay as up-to-date as possible.
Always read your antivirus results reports. These reports let you know the suspicious suspects your software was busy rounding up. It will give you a good idea of the threats your devices face and perhaps the schemes that you unknowingly fell into, such as clicking on a link in a phishing email. This information can also help you improve your online safety habits.
Everyone needs strong antivirus. Yet antivirus alone isn’t enough to beat back today’s threats. Hackers, scammers, and thieves rely on far more tricks than viruses and malware to wage their attacks, and data breaches slip billions of personal and financial records into the hands of bad actors. You’ll want to pair antivirus with further protection that covers your privacy and identity as well.
For example the antivirus included with McAfee+ Ultimate can secure an unlimited number of household devices. Yet it offers far more than antivirus alone with our most comprehensive protection for your privacy, identity, and devices. The full list of features is long, yet you’ll get credit monitoring, dark web monitoring, removal of personal information from risky data broker sites, along with identity theft protection and restoration from a licensed expert if the unexpected happens. In all, it offers a single solution for antivirus, and far more that can protect you from the broad range of threats out there today.
The post Less Is More: Why One Antivirus Software Is All You Need appeared first on McAfee Blog.

Even as the internet kept us connected with family and friends during the pandemic, people remain understandably eager to reconnect in person as vaccines roll out and restrictions ease. In fact, people are making travel plans accordingly. Nearly two-thirds (64%) of people worldwide said that they’re planning to travel for leisure this year. And, as always, they’re bringing their devices with them.
These are a few of the top-line findings from our 2021 Consumer Security Mindset Report: Travel Edition, which garnered responses from more than 11,000 people aged 18 to 75 in eleven countries across North and South America, Europe, Asia, and the South Pacific. More broadly, this survey provides insight into people’s plans and preferences for travel and how they view online security while traveling—particularly after relying heavily on the internet at home during the pandemic for more than a year.
Indeed, people feel more connected by the internet today than they did prior to the onset of COVID-19 with a significant 76% of respondents stating as much. In light of that increasing reliance on the internet, 61% reported implementing more protection for their devices, connected homes, and online activities in general. This was particularly the case in nations like India (86%), Mexico (79%), and Brazil (68%). However, other nations trended much lower than the average, such as the UK (47%) and France (34%). In the U.S., that figure was lower than the international trend with roughly half of the people implementing more protection.

As called out earlier, people are taking the first steps toward leisure travel once again. Only 12% of people in the U.S said that they were planning on traveling internationally compared to a global average of 16%, while nations like Singapore (30%), the UK (25%), and Germany (24%) trending well above the average. In contrast, the outlook for domestic leisure travel appears exceptionally strong, particularly for respondents in Australia (88%), India (79%) and the U.S. (77%) who plan to travel as such.
The pandemic has shaped people’s views on where they’d like to stay, with 62% stating that their preference for lodging has changed this year. Well over one-third of respondents in the U.S., Australia, Indonesia, and Canada said that staying with family and friends as their preferred option. Globally speaking, hotel and motel accommodations topped the list at 41%. Vacation home rentals entered the mix as well with roughly 25% of respondents saying a rental was part of their plan.
Yet how have attitudes changed toward connecting to networks outside of the home, particularly after the past year saw the majority of people improve their security at home?
For a baseline, we found that 80% of respondents said that they’ve connected a device when visiting a home or place that is not their own. The devices they mentioned most include laptops, streaming devices, Bluetooth speakers, and gaming devices as well. To connect those devices, they’ll use the home network of the friend’s or rental home where they’re staying (48%) or the network provided by the hotel where they’re staying (48%). And while in-between places, public Wi-Fi remains a popular means of network connection at 50%, along with airport Wi-Fi (41%) plus transit Wi-Fi (31%). 
As to how secure people feel on those networks, the answer varies greatly. While people expect low risk or no risk at all on their home network (85%) or a friend’s home (73%), they’re far less apt to trust other networks. In general, they see Wi-Fi networks as most vulnerable to cyber threats than any other network or device at 68% and feel most at risk connecting to networks in hotels (25%) and rentals (21%).
Despite these findings, only 47% people said they take the same online security measures that they take at home when they’re on holiday or vacation. Similarly, just 52% of people check if the network they are joining is secure before they connect. Of that, 22% say they don’t check because they feel the network poses no threat and another 26% say that they simply don’t know how to check.
As travel becomes an actual possibility for people once again, it’s an opportunity to remember just how important security is outside the home. Whether people are at home or away, there will be banking to do, chances to shop online, and moments to stream a few shows while at the airport or on the road. Protecting laptops and mobile devices for travel become extra important when using public, airport, and public Wi-Fi, as those networks can expose people to more threats than their home networks.
With that, here are five things people can do to protect themselves and others while traveling:
The post Seeking Reconnection: Internet Usage and the Return to Travel appeared first on McAfee Blogs.

Google’s Android operating system has been a boon for the average consumer. No other operating system has given so much freedom to developers and hardware manufacturers to make quality devices at reasonable prices. The number of Android phones in the world is astounding. That success comes with a price, however.
A recent report from our own McAfee Mobile Research team has found malicious apps with hundreds of thousands of downloads in the Google Play store. This round of apps poses as simple wallpaper, camera filters, and picture editing, but they hide their nature till after they’ve been installed on your device.

Figure 1. Infected Apps on Google Play
On the bright side, Google Play performs a review for every app to ensure that they are legitimate, safe, and don’t contain malware before they’re allowed on the Play store. However, enterprising criminals regularly find ways to sneak malware past Google’s security checks.

Figure 2. Negative reviews on Google Play
When developers upload their apps to the Play store for approval, they have to send supporting documents that tell Google what the app is, what it does and what age group it’s intended for. By sending Google a “clean” version of their app, attackers can later get their malicious code into the store via a future update where it sits and waits for someone to download it. Once installed, the app contacts a remote server, controlled by the attackers, so it can download new parts of the app that Google has never seen. You can think of it as a malware add-on pack that installs itself on your device without you realizing it. By contacting their own server for the malware files, attackers sneak around Google security checks and can put anything they want on your device.
The current round of malware we’re seeing hijack your SMS messages so they can make purchases through your device, without your knowledge. Through a combination of hidden functionality and abuse of permissions like the ability to read notifications, that simple looking wallpaper app can send subscription requests and confirm them as if it were you. These apps will regularly run up large bills through purchasing subscriptions to premium rate services. The more troubling part is how they can read any message that you receive, possibly exposing your personal information to attackers.
To start, a comprehensive and cross-platform solution like McAfee Total Protection can help detect threats like malware and alerts you if your devices have been infected. I’d also like to share some tips our Research team has shared with me.
Before you hit that install button, take a good look at an app’s reviews. Do they look like they were written by real people? Do the account names of the reviewers make sense? Are people leaving real feedback, or are the majority of comments things like, “Works great. Loved it.” with no other information?
Scammers can easily generate fake reviews for an app to make it look like people are engaging with the developers. Look out for vague reviews that don’t mention the app or what it does, nothing but five-star reviews, and generic sounding account names like, “girl345834”. They’re probably bots, so be wary.
Search for the app developers’ company and see if they have a website. Having a website doesn’t guarantee an app is legitimate, but it’s another good indicator of how trustworthy a company’s app is. Through their website, you should be able to find out where their team is based, or at least some personal information about the company. If they’re hiding that information, or there’s no site at all, that might be a good sign to try a different app.
A lot of malicious apps offer features that your phone already provides, like a flashlight or photo viewer. Unless there’s a very specific reason why you need a separate app to do something your device already does, it’s not recommended to use a third-party app. Especially if it’s free.
App permissions must be clearly stated on the app’s page in order to get into the Google Play store. They’re found near the bottom of the page, along with developer information. Check the permissions every app asks for before you install it and ask yourself if they make sense. For example, a photo editor doesn’t need access to your contacts list, and wallpapers don’t need to have access to your location data. If the permissions don’t make sense for the type of app, steer clear.
Mobile devices are vulnerable to malware and viruses, just like your computer. By installing McAfee protection to your mobile device, you can secure your mobile data, protect your privacy, and even find lost devices.
Android is one of the most popular operating systems on the planet, which means the rewards for creating malware for Android devices are well worth it. It’s unlikely that Android malware is going away any time soon, so staying safe means being cautious with the things you install on your devices.
You can protect yourself by installing McAfee Total Protection on your mobile device and reading the permissions apps ask for when you install them. There’s no good reason for a wallpaper app to have SMS permissions, but that request should ring some alarm bells that something isn’t right and stop you from installing it.
The post Fraudulent Apps that Automatically Charge you Money Spotted in Google Play appeared first on McAfee Blogs.

Of all the pastimes that took off during the pandemic, it’s not surprising that online gaming was one of them. After all, gaming offers excitement, new experiences, and social interaction, all from the comfort of home. It’s no wonder then that the gaming industry saw a 20% increase in revenue in 2020, as new and previously-retired gamers returned to this pastime.
But while the gaming industry was finding a lot of new allies, the players themselves faced growing exposure to malware and threats. Our 2020 Mobile Threat Report found that gamers are being targeted with phishing attacks and malicious apps, aimed at stealing usernames and passwords. With this information, hackers could potentially steal hard-earned in-game collectibles, as well as real-world money and personal information. And PC gamers face similar threats, from viruses and spyware to network attacks that could potentially put their personal information and property at risk.
While 75% of gamers surveyed worry about their security while gaming in the future, some worry they’ll have to compromise performance to be protected. That’s why McAfee® Gamer Security offers robust protection to PC gamers with one of the lowest impacts on system performance in the industry.
To protect the growing number of gamers against increasing threats, we are offering one free year of McAfee Gamer Security for one gaming PC to multi-device McAfee ® Total Protection and McAfee® Live Safe users in the U.S. This powerful software was built from the ground up to address the challenges gamers face, with speedy performance, system optimization, uninterrupted gaming, and no pop-up apps.
users in the U.S. This powerful software was built from the ground up to address the challenges gamers face, with speedy performance, system optimization, uninterrupted gaming, and no pop-up apps.
But don’t just take it from me. This is what one of our users have to say: “I believe [McAfee Gamer Security] had a positive impact … because it increased the speed of my game as well as gave me peace of mind that I was protected during my gameplay.”
We know that gamers are some of the most tech-savvy and connected users out there, so it’s important that we meet them where they are by giving them the performance and security they need to play at full throttle. After all, many users are seeking stress relief through gaming, not the extra worry over their online security.
With McAfee Gamer Security we made security for players more fun, by including a gamer-centric interface that was inspired by familiar apps like game launchers — you can check the current status of your system and key resources that impact in-game performance, like GPU, CPU, and memory, as well as perform real-time optimization. And of course, we’ve also included monitoring for your all-important FPS (frames per second). You can even access past performance data to better understand your game-by-game trends.
Let’s keep the excitement of gaming while adding the extra confidence of knowing that your digital life is protected. Whether you are new to McAfee or already enjoying our personal protection, you can download McAfee Gamer Security for free in under one minute with a qualifying subscription! In our mission to provide users with personal protection, we are welcoming PC gamers with open arms.
The post PC Gamers (and Parents of Gamers) Rejoice! appeared first on McAfee Blogs.

Most of us have fond summer memories of hanging out with friends in a secret clubhouse. However, this isn’t that. While the word clubhouse stirs up instant feelings of belonging to a group of friends, the digital Clubhouse app, we’re referencing is a meeting hub for users over 18. Currently, still in its beta phase, Clubhouse is by invitation only. This exclusivity is also what makes it somewhat irresistible for tweens and teens looking for a new place to meet with friends.
Clubhouse is an all-audio social network; kind of like a podcast meets a group phone call. Guests may drop in and even speak if they raise their hand are unmuted by the speaker. Speakers create “rooms” each with different topics and invite people to join in on that discussion.
The app found its wings as a fun place to connect during the pandemic. Mom groups, business roundtables, staff meetings, political groups, think tanks, and hobbyists flocked to connect on the app and still do. The topics are plentiful and there’s always a conversation happening that you can access with a click.

Currently there aren’t any parental controls or privacy settings on Clubhouse. While the app states that there’s a minimum age requirement of 18, there isn’t an actual age-verification system. As with so many other apps, anyone under 18 can simply get an invite, fake their age, and either drop in on any of the conversations going on or start their own room.
Mature content. Topics on Clubhouse cover a wide range of topics both mainstream and fringe. So, if an underage user fills out their profile information and interests, they will automatically get invitations to several daily discussions, which may or may not be age appropriate. They can also explore and join any kind of group.
Bullying. Clubhouse discussions are uncensored. Therefore, it’s possible that a heated discussion, biased comments, or bullying can take place.
Misinformation. If you walked through a crowded mall, you might overhear a dozen different accounts about a news event, a person, or a topic. The same holds true for Clubhouse where commentary is the currency. Therefore, misinformation is likely (as is common with any other app).
Accounts can’t be locked. Another privacy gap on Clubhouse is that accounts can’t be set to private and rooms/conversations will remain open by default unless the host makes it private, which means anyone can drop in.
The celebrity hook. Clubhouse has attracted celebrities and social media influencers to its halls who host discussions. This is a big draw for kids who want to hear real-life conversations and just get a bit closer to their favorite celebrity. Again, content can be unpredictable in these rooms and potentially risky for underage users.
Why age restrictions matter. More and more, kids who ignore age restrictions on apps are wandering into trouble. Consider talking to your child about why age restrictions exist, the consequences if they are ignored, and some alternative apps that might be safer.
Why privacy matters. While Clubhouse has grown prolifically in a short time, which has caused some concern over data privacy. According to reports, Clubhouse asks users to share their contacts and has been accused of being “overly aggressive with its connection recommendations.” Also, it’s unclear how the app collects and leverages user data. As outlined by McAfee’s Advanced Threat Research Team last month, the security of user information and communication within Clubhouse has vulnerabilities that could be exploited. For these reasons, consider discussing the data “exchange” we often make when we jump on an exciting new app, why data matters, and why it’s important to understand what’s being collected and to use any and all privacy settings. According to its privacy policy, Clubhouse also “temporarily record the audio in a room when it is live.”
Why content matters. With so many images and ideas coming across our screens every day, holding fast to our content standards can be a challenge for families. Talk to kids about why age-appropriate conversations, topics, and friend groups matter online and what happens when you try to speed up that process. Discuss how content filters and parental controls work and consider them for your family.
The good news about Clubhouse (when it comes to young users) is that along with its rapid growth, the creators are reportedly responding to consumer safety demands and daily increasing in-app safety features for reporting harassment and abuse.
To stay updated on all things McAfee and on top of the latest consumer and mobile security threats, follow @McAfee_Home on Twitter, subscribe to our email, listen to our podcast Hackable?, and ‘Like’ us on Facebook.
The post Is the Clubhouse App a Safe Place for Kids to Hangout? appeared first on McAfee Blogs.

The number of new viruses grows every day. In fact, McAfee registers an average of 1.1 million new malicious programs and potentially unwanted apps (PUA) each day, which contributes to the millions and millions already in existence. While there is no way to know when or how cyberattacks will occur, it’s clear that antivirus software is one of the best ways to ensure you, and your devices, are safe.
Despite its proven strengths, some long-standing myths question the effectiveness of antivirus. To set the record straight, we’ve debunked five of the most common antivirus software myths, so you can rest assured that you are safely navigating the evolving cyber landscape.
We expect a lot from our devices—faster performance every time the latest model is released. As a result, many are reluctant to install apps or software that may jeopardize device performance, including antivirus software.
Many believe that antivirus software will slow down your devices. However, contrary to popular belief, quality antivirus software can improve device performance by using advanced optimizations. It’s this simple: antivirus software conducts regular system-wide scans to identify and prevent viruses and improve performance without compromising efficacy.
To run these scans, antivirus software requires system resources, which is where this myth originates. If you download or operate more than one antivirus program or download the wrong version for your system, then yes, your device will slow to a crawl. That is why it is essential to install one high-quality antivirus software that meets all your devices’ system requirements. Additionally, best-in-class antivirus software can be set to run during specific hours to avoid delays during the busiest times of your day.
The number of malware strains and potentially unwanted applications (PUA) increases every year. It is understandable why people might think that antivirus software cannot protect against them all.
However, antivirus software can provide extensive protection against the majority of malicious programs. It does so in two ways:
Taken together, a known list of threats paired with the unique capabilities of machine learning, data science, and AI for advanced threat detection enable antivirus software to protect against a wide range of existing and evolving threats.
Can you imagine grading your own driving test? You could omit the dreaded three-point turn and pass with flying colors, but the result wouldn’t be as accurate as that of an unbiased evaluator. This same concept applies to evaluating the efficacy of computer security.
It’s easy for a company to set up a test environment where they highlight all the excellent capabilities of their antivirus software and gloss over its shortcomings. It’s equally as easy for a company to commission a third-party to conduct a custom test painting the company in a good light. However, the results will not be as comprehensive or accurate as those from an independent third-party. Additionally, they also will not provide a comparative analysis with other company offerings to help users draw their own conclusions.
Independent third-party test results offer a more thorough evaluation of antivirus software. They also do a better job at evaluating security features. Furthermore, ISO-certified independent third parties lend transparency and credibility to the techniques used and ensure that evaluations align with industry standards.
There is a common belief that Apple products are protected against viruses because cybercriminals often target Windows and Android operating systems. However, Apple devices are just as vulnerable to viruses as any other computer or smartphone. Regardless of your device or operating system—macOS, iOS, Windows, or Android—if it connects to a network, it’s susceptible to viruses.
Windows and Android have long been the dominant operating systems for computers and smartphones. That’s why macOS and iOS have, up until recently, been the lesser focus for cybercriminals. The problem is that cybercriminals want to spread their viruses to the platforms with the largest customer base which just so happens to be Windows and Android. As Apple products continue to grow in popularity, cybercriminals will continue coming out with more viruses specifically targeting Macs, iPhones, and other iOS devices.
Antivirus software is not a guarantee of protection against all viruses. Some malware can and will slip through. This is where antivirus software’s ability to detect and remove malware comes in. Ours comes with a Virus Protection Pledge, which provides a 100% guarantee we’ll remove viruses on your devices, or we’ll give you your money back, all as part of your automatically renewable subscription.
However, viruses and malware are just one form of attack that hackers and bad actors will wage on their victims. They’ll also make attempts at identity theft or likewise try to invade your privacy—with the intent of stealing passwords, account information, and personal information, which could drain your debit cards, damage your credit, or otherwise impersonate you for their financial gain.
In this way, antivirus is just one form of protection. To truly stay safe as possible online, you need online protection software that looks after your identity and privacy as well. McAfee+ Ultimate offers our most comprehensive coverage, with
It is necessary to bust common myths about antivirus software to protect yourself and your family from cyberthreats. By educating yourself and selecting a best-in-class antivirus software that’s further bolstered by identity and privacy protection, you will be well on your way to implementing an effective protection strategy.
The post Myth-busting Antivirus Software Assumptions appeared first on McAfee Blog.

In the eyes of hackers, scammers, and thieves, your online privacy and identity look like a giant jigsaw puzzle. One that they don’t need every piece to solve. They only need a few bits to do their dirty work, which means protecting every piece you put out there—a sort of holistic view on your personal security. One that protects you, not just your devices.
Here’s what’s at stake: we create and share loads of personal information simply by going about our day online, where each bit of information makes up a piece of that giant jigsaw puzzle. Some pieces directly identify us, like our tax returns, bank account information, or driver’s licenses. Other pieces of information indirectly identify us, like the IP addresses assigned to our computers, tablets, and phones—or device ID numbers, location information, and browsing history. And bad actors only need a few key pieces to do you harm, such as committing identity crime in your name or selling your personal information on sketchy websites or the dark web.
While people show great concern about their personal information, who has it and what’s done with it, our research shows that 70% of people feel like they have little or no control over the data that’s collected about them. However, you have plenty of ways that you can indeed take control—ways that can prevent, detect, and correct attacks on your privacy and identity. That’s where holistic protection comes in.
You can think of holistic protection as layers of shields that protect you and the devices you use. It gives you three layers in all—a Prevention Layer, Detection Layer, and a Correction Layer.
A holistic and comprehensive security solution like McAfee+ combines those three layers in a way that protects your personal information and keep your identity private, showing you how it does it along the way, so you can see exactly how safe you are. Let’s take a quick look of some of the protections you’ll find in each layer …

In the Prevention Layer, you’ll see:
In the Detection Layer, you have …
In the Correction Layer, several other protections have your back …
These are just a few examples of the protections in each layer. And you’ll find our most comprehensive holistic protection in McAfee+ Ultimate, covering your privacy, identity, and devices.
While your online privacy and identity may look a jigsaw puzzle, protecting it shouldn’t be as complicated. With a holistic security solution for your personal protection, you can minimize your exposure with layers of security that do much of the work for you.
Antivirus on your PC is not enough. It has not been enough for many decades now. And this becomes more evident as we continue to spend more time online, with the average person spending 6 hours and 54 minutes online each day, leaving clouds of personal information in their wake.
While standalone apps like a password manager, a VPN app, and an identity solution from different vendors can be piecemealed together with your device security, these are difficult to keep track of and burdensome to maintain.
We have combined the important tools you need into a seamless and comprehensive experience because good security software is something that you use daily to feel safer online. This is why we are working on your behalf to redefine security, so you can enjoy your connected life with confidence.
The post True Security Requires a Holistic Approach appeared first on McAfee Blog.

Spooky season is among us, and ghosts and goblins aren’t the only things hiding in the shadows. Online threats are also lurking in the darkness, preparing to haunt devices and cause some hocus pocus for unsuspecting users. This Halloween season, researchers have found virtual zombies and witches among us – a new trojan that rises from the dead no matter how many times it’s deleted and malicious code that casts an evil spell to steal users’ credit card data.
Let’s unlock the mystery of these threats so you can avoid cyber-scares and continue to live your online life free from worry.
Just like zombies, malware can be a challenge to destroy. Oftentimes, it requires a user to completely wipe their device by backing up files, reinstalling the operating system, and starting from scratch. But what if this isn’t enough to stop the digital walking dead from wreaking havoc on your device?
Recently, a new type of Trojan has risen from the dead to haunt users no matter how many times it’s deleted. This zombie-like malware attaches itself to a user’s Windows 10 startup system, making it immune to system wipes since the malware can’t be found on the device’s hard drive. This stealthy malware hides on the device’s motherboard and creates a Trojan file that reinstalls the malware if the user tries to remove it. Once it sets itself up in the darkness, the malware scans for users’ private documents and sends them to an unknown host, leaving the user’s device in a ghoulish state.
A malware misfortune isn’t the only thing that users should beware of this Halloween. Cybercriminals have also managed to inject malicious code into a wireless provider’s web platform, casting an evil spell to steal users’ credit card data. The witches and warlocks allegedly responsible for casting this evil spell are part of a Magecart spin-off group that’s known for its phishing prowess. To pull off this attack, they plated a credit card skimmer onto the wireless provider’s checkout page. This allowed the hackers to exfiltrate users’ credit card data whenever they made a purchase – a spell that’s difficult to break.
While these threats might seem like just another Halloween trick, there are other forces at play. According to McAfee’s Quarterly Threats Report from July 2020, threats like malware phishing and trojans have proven opportunistic for cybercriminals as users spend more and more time online – whether it be working from home, distance learning, or connecting with friends and loved ones. In fact, McAfee Labs observed 375 threats per minute in Q1 2020 alone.
So, as hackers continue to adapt their techniques to take advantage of users spending more time online, it’s important that people educate themselves on emerging threats so they can take necessary precautions and live their digital lives free from worry.
Fortunately, there are a number of steps you can take to prevent these threats from haunting your digital life. Follow these tips to keep cybersecurity tricks at bay this spooky season:
Zombie malware is easily spread by phishing, which is when scammers try to trick you out of your private information or money. If you receive an email from an unknown user, it’s best to proceed with caution. Don’t click on any links or open any attachments in the email and delete the message altogether.
Look over your credit card accounts and bank statements often to check whether someone is fraudulently using your financial data – you can even sign up for transaction alerts that your bank or credit card company may provide. If you see any charges that you did not make, report it to the authorities immediately.
Add an extra layer of protection with a security solution like McAfee® Total Protection to help safeguard your digital life from malware and other threats. McAfee Total Protection also includes McAfee® WebAdvisor – web protection that enables users to sidestep attacks before they happen with clear warnings of risky websites, links, and files.
To stay updated on all things McAfee and on top of the latest consumer and mobile security threats, follow @McAfee_Home on Twitter, listen to our podcast Hackable?, and ‘Like’ us on Facebook.
The post Trick or Treat: Avoid These Spooky Threats This Halloween appeared first on McAfee Blogs.

During COVID-19, people stuck inside have scoured the internet for content to consume – often searching for free entertainment (movies, TV shows, and music) to avoid any extra costs. As these habits increase, so do the potential cyberthreats associated with free internet content – making our fourteenth Most Dangerous Celebrities study more relevant than ever.
To conduct our Most Dangerous Celebrities 2020 study, McAfee researched famous individuals to reveal which celebrities generate the most “dangerous” results – meaning those whose search results bring potentially malicious content to expose fans’ personal information.
Thanks to her recent starring roles, American actress Anna Kendrick has found herself at the top of McAfee’s 2020 Most Dangerous Celebrities list.
The Top Ten Most Dangerous Celebrities
You probably know Anna Kendrick from her popular roles in films like “Twilight,” Pitch Perfect,” and “A Simple Favor.” She also recently starred in the HBO Max series “Love Life,” as well as the 2020 children’s film “Trolls World Tour.” Kendrick is joined in the top ten list by fellow actresses Blake Lively (No. 3), Julia Roberts (No. 8), and Jason Derulo (No. 10). Also included in the top ten list are American singers Mariah Carey (No. 4), Justin Timberlake (No. 5), and Taylor Swift (No. 6). Rounding out the rest of the top ten are American rapper Sean (Diddy) Combs (No. 2), Kate McKinnon (No. 9), and late-night talk show host Jimmy Kimmel (No. 7).

Lights, Camera, Security
Many consumers don’t realize that simple internet searches of their favorite celebrities could potentially lead to malicious content, as cybercriminals often leverage these popular searches to entice fans to click on dangerous links. This year’s study emphasizes that consumers are increasingly searching for content, especially as they look for new forms of entertainment to stream amidst a global pandemic.
With a greater emphasis on streaming culture, consumers could potentially be led astray to malicious websites while looking for new shows and movies to watch. However, people must understand that torrent or pirated downloads can lead to an abundance of cyberthreats. If an unsuspecting user clicks on a malicious link while searching for their favorite celebrity film, their device could suddenly become plagued with adware or malware.
Whether you and your family are checking out your new favorite actress in her latest film or streaming a popular singer’s new album, it’s important to ensure that your searches aren’t potentially putting your online security at risk. Follow these tips so you can be a proactive fan while safeguarding your digital life:
Users looking for information on their favorite celebrities should be cautious and only click on links to reliable sources for downloads. The safest thing to do is to wait for official releases instead of visiting third-party websites that could contain malware.
When it comes to dangerous online behavior, using illegal streaming sites could wreak havoc on your device. Many illegal streaming sites are riddled with malware or adware disguised as pirated video files. Do yourself a favor and stream the show from a reputable source.
Safeguard yourself from cybercriminals with a comprehensive security solution like McAfee Total Protection. This can help protect you from malware, phishing attacks, and other threats.
Use a website reputation tool such as McAfee WebAdvisor, which alerts users when they are about to visit a malicious site.
Kids are fans of celebrities too, so ensure that limits are set for your child on their devices and use parental control software to help minimize exposure to potentially malicious or inappropriate websites.
To stay updated on all things McAfee and for more resources on staying secure from home, follow @McAfee_Home on Twitter, listen to our podcast Hackable?, and ‘Like’ us on Facebook.
The post Anna Kendrick Is McAfee’s Most Dangerous Celebrity 2020 appeared first on McAfee Blogs.

During COVID-19, people stuck inside have scoured the internet for content to consume – often searching for free entertainment (movies, TV shows, and music) to avoid any extra costs. As these habits increase, so do the potential cyberthreats associated with free internet content – making our fourteenth Most Dangerous Celebrities study more relevant than ever.
To conduct our Most Dangerous Celebrities 2020 study, McAfee researched famous individuals to reveal which celebrities generate the most “dangerous” results – meaning those whose search results bring potentially malicious content to expose fans’ personal information.
Known for his BAFTA-winning celebrity chat show and BBC radio show, the UK’s national treasure, Graham Norton, has found himself at the top of McAfee’s 2020 Most Dangerous Celebrities list.
Graham Norton is a household name thanks to his hugely popular talk show, The Graham Norton Show, which has seen him interview A-listers including Nicole Kidman, Hugh Grant and Helen Mirren. He is also known for his BBC radio show, as well as his inimitable Eurovision commentary. Not shy of celebrity friends, Norton is joined in the top ten list by fellow national treasures such as Ricky Gervais (No.2), and Idris Elba (No.7) and Mary Berry (no.10). Also included in the top ten list are British actor Tom Hardy (No.3) and Gavin and Stacey star, Ruth Jones (No.4). Rounding out the rest of the top ten are UK’s very own Mick Jagger (No.5), Aussie actress Margot Robbie (No.6) and models Kate Moss (No.8) and Bella Hadid (No.9).
Many consumers don’t realize that simple internet searches of their favorite celebrities could potentially lead to malicious content, as cybercriminals often leverage these popular searches to entice fans to click on dangerous links. This year’s study emphasizes that consumers are increasingly searching for content, especially as they look for new forms of entertainment to stream amidst a global pandemic.
With a greater emphasis on streaming culture, consumers could potentially be led astray to malicious websites while looking for celebrity gossip and new shows or movies to watch. For example, given Graham is strongly associated with malicious search terms, indicates that online criminals are using Britain’s love for celebrity gossip and the Eurovision for personal gain. If an unsuspecting user clicks on a malicious link while searching for their favorite celebrity film, their device could suddenly become plagued with adware or malware.
Whether you and your family are checking out your new favorite actress in her latest film or streaming a popular singer’s new album, it’s important to ensure that your searches aren’t potentially putting your online security at risk. Follow these tips so you can be a proactive fan while safeguarding your digital life:
Users looking for information on their favorite celebrities should be cautious and only click on links to reliable sources for downloads. The safest thing to do is to wait for official releases instead of visiting third-party websites that could contain malware.
Refrain from using illegal streaming sites
When it comes to dangerous online behavior, using illegal streaming sites could wreak havoc on your device. Many illegal streaming sites are riddled with malware or adware disguised as pirated video files. Do yourself a favor and stream the show from a reputable source.
Safeguard yourself from cybercriminals with a comprehensive security solution like McAfee Total Protection. This can help protect you from malware, phishing attacks, and other threats.
Use a website reputation tool such as McAfee WebAdvisor, which alerts users when they are about to visit a malicious site.
Kids are fans of celebrities too, so ensure that limits are set for your child on their devices and use parental control software to help minimize exposure to potentially malicious or inappropriate websites.
To stay updated on all things McAfee and for more resources on staying secure from home, follow @McAfee_Home on Twitter, listen to our podcast Hackable?, and ‘Like’ us on Facebook.
The post Check Out the McAfee Most Dangerous Celebrity 2020 appeared first on McAfee Blogs.

With millions of people continuing to work and study remotely, scammers have followed them home—generating an average of 375 new threats per minute so far this year. In response, our enhanced consumer portfolio directly addresses the new needs and new threats people face.
McAfee Labs found that these new threats via malicious apps, phishing campaigns malware, and more, according to its McAfee COVID-19 Threat Report: July 2020, which amounted to an estimated $130 million in total losses in the U.S. alone.
To help people stay safer and combat these threats, today we announced our latest consumer security portfolio. Our enriched products come with better user experiences such as a native Virtual Private Network (VPN), along with new features, including integrated Social Media and Tech Scam Protection—all of which are pressing security essentials today.
Specifically, our product lineup has been updated to include:
Scams involving tech support and product activation have continued to sneak into people’s inboxes and search results, which require a critical eye to spot. Here are some tips on how to identify these scams. We’re making it easier for people to stay safer with new features such as:
With jobs and things that simply need to get done “right now,” security can be an afterthought. Sometimes that desire for convenience has consequences, leading to situations where people’s devices, data, and personal information get compromised. In response, we’re doing our part to make security more intuitive so that people can get things done quickly and safely:
With people’s newfound reliance on the internet, we’ve made new advances that help them live their increasingly connected lives—looking after security and privacy even more comprehensively than before on security and the apps they use:
McAfee is on a journey to ensure security allows users to be as carefree as possible online, now that more time is spent on devices as consumers navigate a new normal of life from home. For more information on our consumer product lineup, visit https://www.mcafee.com/en-us/antivirus/mcafee-total-protection.html
To stay updated on all things McAfee and for more resources on staying secure from home, follow @McAfee_Home on Twitter, listen to our podcast Hackable?, and ‘Like’ us on Facebook.
The post Evolving Security Products for the new Realities of Living Life From Home appeared first on McAfee Blogs.

You get an email from bank0famerica@acc0unt.com claiming that they have found suspicious activity on your credit card statement and are requesting that you verify your financial information. What do you do? While you may be tempted to click on a link to immediately resolve the issue, this is likely the work of a cybercriminal. Phishing is a scam that tricks you into voluntarily providing important personal information. Protect yourself from phishing by reviewing some examples of phishing emails and learning more about this common online scam.
Phishing is a cybercrime that aims to steal your sensitive information. Scammers disguise themselves as major corporations or other trustworthy entities to trick you into willingly providing information like website login credentials or, even worse, your credit card number.
A phishing email or text (also known as SMiShing) is a fraudulent message made to look legitimate, and typically asks you to provide sensitive personal information in various ways. If you don’t look carefully at the emails or texts, however, you might not be able to tell the difference between a regular message and a phishing message. Scammers work hard to make phishing messages closely resemble emails and texts sent by trusted companies, which is why you need to be cautious when you open these messages and click the links they contain.
Phishing scammers often undo their own plans by making simple mistakes that are easy to spot once you know how to recognize them. Check for the following signs of phishing every time you open an email or text:
Even the biggest companies sometimes make minor errors in their communications. Phishing messages often contain grammatical errors, spelling mistakes, and other blatant errors that major corporations wouldn’t make. If you see multiple, glaring grammatical errors in an email or text that asks for your personal information, you might be a target of a phishing scam.
To enhance their edibility, phishing scammers often steal the logos of who they’re impersonating. In many cases, however, they don’t steal corporate logos correctly. The logo in a phishing email or text might have the wrong aspect ratio or low-resolution. If you have to squint to make out the logo in a message, the chances are that it’s phishing.
Phishing always centers around links that you’re supposed to click. Here are a few ways to check whether a link someone sent you is legitimate:
If the URL you discover doesn’t match up with the entity that supposedly sent you the message, you probably received a phishing email.
Phishing messages come in all shapes and sizes, but there are a few types of phishing emails and texts that are more common than others. Let’s review some examples of the most frequently sent phishing scams:
Some phishing emails appear to notify you that your bank temporarily suspended your account due to unusual activity. If you receive an account suspension email from a bank that you haven’t opened an account with, delete it immediately, and don’t look back. Suspended account phishing emails from banks you do business with, however, are harder to spot. Use the methods we listed above to check the email’s integrity, and if all else fails, contact your bank directly instead of opening any links within the email you received.
Two-factor authentication scam
Two-factor authentication (2FA) has become common, so you’re probably used to receiving emails that ask you to confirm your login information with six-digit numerical codes. Phishing scammers also know how standard 2FA has become, and they could take advantage of this service that’s supposed to protect your identity. If you receive an email asking you to log in to an account to confirm your identity, use the criteria we listed above to verify the message’s authenticity. Be especially wary if someone asks you to provide 2FA for an account you haven’t accessed for a while.
We all know how important tax season is. That’s what phishing scammers are counting on when they send you phony IRS refund emails. Be careful when an email informs you that you’ve received a windfall of cash and be especially dubious of emails that the IRS supposedly sent since this government agency only contacts taxpayers via snail mail. Tax refund phishing scams can do serious harm since they usually ask for your social security number as well as your bank account information.
Sometimes, cybercriminals will try to tick you by sending emails with fake order confirmations. These messages often contain “receipts” attached to the email or links claiming to contain more information on your order. However, criminals often use these attachments and links to spread malware to the victim’s device.
You need to be wary of phishing when you’re using your work email as well. One popular phishing scam involves emails designed to look like someone in the C-suite of your company sent them. They ask workers to wire funds to supposed clients, but this cash actually goes to scammers. Use the tips we listed above to spot these phony emails.
Often, hackers look for ways to update old schemes so that they go undetected by users already aware of certain cyberthreats. Such is the case with the latest phishing evasion technique, which detects virtual machines to fly under the radar. Cybersecurity firms often use headless devices or virtual machines (a computer file that behaves like an actual computer) to determine if a website is actually a phishing page. But now, some phishing kits contain JavaScript — a programming language that allows you to implement complex features on web pages — that checks whether a virtual machine is analyzing the page. If it detects any analysis attempts, the phishing kit will show a blank page instead of the phishing page, allowing the scam to evade detection. To help ensure that you don’t fall for the latest phishing scams, stay updated on the most recent phishing techniques so you can stay one step ahead of cybercriminals.
Never click links in suspicious emails. If you click a link you suspect a phishing scammer sent, the link will take you to a web page with a form where you can enter sensitive data such as your Social Security number, credit card information, or login credentials. Do not enter any data on this page.
If you accidentally enter data in a webpage linked to a suspicious email, perform a full malware scan on your device. Once the scan is complete, backup all of your files and change your passwords. Even if you only provided a phishing scammer with the data from one account, you may have also opened the door to other personal data, so it’s important to change all the passwords you use online in the wake of a suspected phishing attack.
Let’s wrap things up with some summarized tips on how to avoid phishing emails:
Phishing emails only work on the unaware. Now that you know how to spot phishing emails and what to do if you suspect scammers are targeting you, you’re far less likely to fall for these schemes. Remember to be careful with your personal information when you use the internet and err on the side of caution whenever anybody asks you to divulge sensitive details about your identity, finances, or login information.
To stay updated on all things McAfee and on top of the latest consumer and mobile security threats, follow @McAfee_Home on Twitter, subscribe to our email, listen to our podcast Hackable?, and ‘Like’ us on Facebook.
The post Phishing Email Examples: How to Recognize a Phishing Email appeared first on McAfee Blogs.