
Finding someone who hasn’t heard of TikTok in 2022 would be quite the achievement. As one of the most popular social media platforms of the moment, it is not only being used by our tweens, teens and even grownups to connect but also as a crucial way to tell important stories amidst a backdrop of natural disasters and even war.
As parents, we know we need to keep up with the latest social media platforms but let’s be real – we don’t always have enough time. So, I’m going to do the hard work for you. Here’s my overview of TikTok – what it is, the risks, and most importantly, how you can help your kids (or yourself) stay safe while using it. You’re welcome!!
Tik Tok is a social media platform that can be downloaded on any smartphone via an app. Once you’ve signed up to the app and become a user, you can create and then share short videos of 15 seconds in length on any topic.
The app started life as Musical.ly, a super popular video streaming app that also allowed users to make funny 15-second videos, many of which focussed on lip-syncing. By mid-2017, the app had over 200 million registered users. In 2018, the app was taken over by Chinese company ByteDance and all of its users (and their content) were moved to TikTok.
According to Hootsuite, TikTok is the 6th most used social media platform in the world. As of late September 2021, TikTok had over a billion monthly users and as of August last year, it overtook Facebook to become the world’s most downloaded app. Facebook does, however, have more monthly users, reporting a massive 2.74 billion users as of August 2021.
It appears TikTok is used by females (57%) more than males (43%) however its user base is very diverse and cuts across all age categories – yes, even us parents! But brands hoping to reach younger female audiences are without a doubt using TikTok to showcase their wares. What is interesting is that although we all think that TikTok dominates the Gen Z market, research shows that it doesn’t rank as the top choice for younger users – in fact only 4.3% of users name it as their favorite platform. Users between 16 and 24 nominate Instagram as their top choice!
Unlike other social media platforms, there is no minimum age requirement when using TikTok. The company says that it adjusts a user’s privacy settings based on the birthday entered when setting up the account. If a user is under the age of 13, they will automatically be directed into the TikTok for Younger Users program which has additional privacy and safety protections. Of course, anyone can lie about their age, but TikTok has said publicly that it has moderators trained to predict when a user is suspected of being underage.
As you would know, there are risks associated with using all social media platforms and TikTok is no exception. However, in my opinion the majority of these can be managed with a combination of critical thinking, parental controls, and preparation – more about these later.
But let’s go worst-case scenario for one moment. Here are the potential risks that your child could encounter:
Unfortunately, it isn’t possible to keep our tweens and teens in a bubble – I know, so disappointing! So, the best and only option is to prepare them for challenges online and arm them with tools to navigate the tricky stuff. Here’s my advice on how to best help them manage TikTok:
Knowledge is power, my friends. So, download the app and have a play so you better understand it. Then, why not ask your experienced in-house ‘TikTokers’ to show you how it works. Use this as an opportunity to ask them what they do when they see something that concerns them, or how they would manage approaches from people they don’t know. Why not weave in reminders about the importance of online privacy and the permanence of their digital footprint? Commit to making these conversations regular.
Helping your kids become critical thinkers is, without doubt, one of the best ways of helping them prepare for life’s challenges – both online and offline. Being able to rigorously question ideas and assumptions rather than accepting them at face value is your kids’ golden ticket! So, if they are approached by friendly (but ill-intentioned) strangers online or sent a link to a super compelling offer online, they will have the ‘smarts’ to realise that all is not as it seems and to hit delete!
If the horse has already bolted and your tween or teen has been using TikTok for a while, then introducing boundaries might be tricky but don’t give up! TikTok has a Family Pairing feature which allows parents to link their TikTok account to their teen’s account so they can control the settings remotely. This might be a good option if your child is younger or just starting out on TikTok. This gives parents the power to turn on Restricted Mode, screen time limits, and also turn off the direct message option.
If your child has been using TikTok for some time and you want to pull things back, then why not work with them to set up their privacy and safety features. I find kids always respond best when you explain why you are doing something so assure them you are just wanting to keep them safe. TikTok has a long list of features you can enable that will make your offspring’s experience that much safer. From turning off downloads, filtering comments to introducing screen time limits, there is a great range of ways of making the TikTok experience much less risky. Check out the full list from TikTok here.
So, next time you hear your kids reference TikTok, don’t immediately feel a pang of guilt that you don’t really know what they are talking about. You’ve got this! Download the app, take a look around, read this post a few more times, and you’ll be fine! And remember, our kids don’t expect us to be experts straight away, or even at all. They just need to know that we’re interested in all parts of their life and respect just how important their digital life is to them.
You’ve got this!!
Take care all
Alex xx
The post A Parent’s Guide to TikTok appeared first on McAfee Blog.

Editor’s Note: This is the third in a series of articles about how we can help our elder parents get the most out of digital life—the ways we can help them look after their finances and health online, along with how they can use the internet to keep connected with friends and family, all safely and simply.
Now here’s a great topic. Spending more quality time with our folks, even if they’re far away. That’s the beauty of a family video chat. It’s a way to connect with more than voice. It’s a way to share moments together.
If your parents and the older loved ones in your family haven’t come around to the idea of video chats just yet, now’s a good time to give it a try. Video chats are far easier to enjoy than ever, and with a little initiative from you, the family can gather around a video chat rather quickly. In fact, there’s plenty you can do to get them started.
Clearly, a video chat is different than a phone call. Beyond the technological differences, it’s quite a different way of interacting. After all, there you are, face-to-face, talking over a device. And that may feel a little awkward, especially for our parents. They’ve lived lives where long-distance conversations meant using a phone that was anchored to the kitchen wall.
So aside from the technical considerations of video chats, there’s a degree of freedom that may leave our parents wondering what to do and how to act in this new medium. Just like when we first used video chat ourselves, questions come up … Where should I be looking on the screen … How should I hold the phone … Can everyone on this call see up my nose?
You can ease them in by taking the lead, welcoming them into the notion that your video chat can be much more than a phone call. More than simply talking, it’s a chance to create a shared space together.
A great example is this: a co-worker recently told me about his in-laws who were scouting out retirement communities to live in. Even though his in-laws lived 2,000 miles away, they all got to do a little house-hunting together. Using a smartphone, they took room-to-room tours of model homes together, got views of the tree-lined streets, checked out the pools and rec centers, and so on. A few weeks later, they shared another video call where his in-laws walked the family through their new place after they’d settled in. And all of it started with a simple request, “Hey, turn on FaceTime so we can take a look too!”
So, in a way, video chats truly are an opportunity to create moments together. It could be as simple as asking grandma to read a book to the kids, have mom and dad share what they’re having for a birthday dinner, or ask them to show how hard it’s snowing outside their home. Anything you can do to encourage a little free interaction of some sort may make a video chat feel far more comfortable. You can really relax and interact once you settle in and let the possibilities unfold.
In a way, a video call is much like dropping by the house for a visit. Placing a video call unannounced may catch mom in her curlers, so to speak. Or, as we’ve heard our parents say when they looked at a messy living room, we may catch them when “the house isn’t ready for guests.” In either case, scheduling a time for a video call gives everyone time to prepare. Whether it’s sprucing up your appearance or simply getting into the headspace for a face-to-face interaction, a designated time helps everyone get ready.
On your end, it’s an opportunity for you to prepare as well. Do the kids have some recent schoolwork or a project they’re proud of? Have them bring it for some show-and-tell. Doing some cooking lately and you just can’t seem to get the family secret BBQ sauce just right? Bring your folks into the kitchen for some cooking advice. Find an old treasure in storage? Break it out and flip through your old grade-school art scrapbook with them on the call. As you prepare, think about sharing and moments, some of the things you’d like to do together over a video call. That’ll make it all the more special.
As you know, there are plenty ways to hold a video call. There’s a good chance you’ve used several platforms and apps yourself already, whether with friends, work, or a mix of both. So when it comes to picking what’s best for your video call, the question to ask here is what’s your parent’s comfort level with technology.
If your parents are pretty comfortable with technology, you can share one of my earlier articles on video calls with them, which walks through the ins and outs of different apps and options. If they’re a little less savvy with technology, ideally they have a smartphone or tablet that they can use. Chances are, that device will have video calling built right in, such as Apple’s FaceTime or Google Duo on Android devices—both of which make video calls an easier “point and shoot” experience.
Even if you’re using different devices, you can still use apps like FaceTime between Androids and iPhones. It’s rather straightforward, as all it takes is for one party or other to click a link. Additionally, Google Duo is available as an app in Apple’s App Store, which makes it easy for everyone to get on one platform as needed.
If a smartphone or tablet isn’t in the picture, there are certainly options for laptops and computers, several you may also know well already. Of the free and relatively straightforward apps out there, you can choose from:
With a free account that can run through a browser window, you and your parents can enjoy a call without having to manually download an app.
This comes standard on Windows PCs and supports apps for all kinds of tablets and smartphones too. If you want to create a video chat without an account, you can simply visit this page and start an instant video chat with a click.
Free to anyone with a free Google Gmail account, you can use Google Meet just by clicking its icon from your Google apps menu or by visiting https://meet.google.com/. Like Zoom and Skype, it can run in the window of a browser, so there’s no app to manually download.
Of course, your folks will need a camera and microphone for their computer. If they don’t have one, there are plenty of moderately priced web cameras that include a microphone. I suggest getting one with a physical lens cap. That way they can protect privacy. Of course, they can always simply disconnect it when they’re not using it.
Setting up a laptop or computer for video calls may take a little bit of work. You can help your parents by walking them through the process with these articles:
Once you’re all set up, here are a few things that you and your parents can do to help keep your calls private and secure.
If your video chap app generates a link that others can click to join in, be sure to create a password that uninvited parties can’t join in as well. Also, don’t be shy about asking your family members to use a password on the calls they initiate. It’s pretty much standard practice nowadays.
Likewise, with any chat link that’s sent to you, be sure that link is legitimate. Confirm the link with the family member who sent it, particularly if you weren’t expecting one. (This is another good reason to schedule calls. Family members will be on the lookout for that link.)
Make sure that you’re using comprehensive online protection software that helps steer you clear of scam emails and links, along with browser protection that blocks links that could send you to sketchy websites. That way, if you do get sent a bogus invite link from a scammer, you’ll be protected.
Aside from giving you the latest features and functionality, updates also often include essential security improvements. Set your computer to update itself automatically and consider using security software that will scan for vulnerabilities and install updates automatically as needed.
An interesting closing note is that getting comfortable with video chat may open a world of other possibilities as well. Perhaps once they get online and see how video chats work, they’ll reach out to other friends and them get in on it too, creating more opportunities to reach out and spend time with others. In other words, you may really start something here by getting mom and dad on video chat.
Additionally, early research has shown that older adults who use regularly technologies like video chat have seen positive impacts in their long-term memory compared to those who just interacted over the phone or in person. Similarly, research has shown that the use of technology, in general, can enhance mental health for older adults as well.
With that, I hope you’ll give it a try with your parents and older loved ones. Meet the inevitable technical bumps in the road with a smile because this journey will be absolutely worth it. For all of you.
The post Helping Mom & Dad: Family Video Chats appeared first on McAfee Blog.

You may hear corporate cybersecurity experts hail the benefits of a VPN, or a virtual private network, to keep company information safe from ransomware attacks and cybercriminals seeking to steal valuable business secrets. It’s unlikely that everyday people, such as yourself, will be targeted by a ransomware scheme, so you may be puzzled about how a VPN can help someone like you be safer online. Luckily, with a VPN being very easy to install and use, you can indeed experience these three everyday benefits to keep your browsing activities safe from eavesdroppers seeking to profit from your online comings and goings.
The most widely known benefit of a VPN for daily use is to safeguard your device when it’s connected to a public Wi-Fi network. Coffee shops, libraries, hotels, transportation hubs, and other public places often provide courtesy internet service to visitors. Shifty characters often lurk on unprotected networks to lift personally identifiable information (PII) from people handling sensitive emails, making banking transactions, or shopping online. Public Wi-Fi eavesdroppers can lift credit card numbers, addresses, birthdays, and Social Insurance Numbers.
When you connect to public Wi-Fi that doesn’t have a lock icon, that’s a sign that you should toggle on your VPN. Also, even if you’re required to enter a password, be wary of any network you share with strangers.
A VPN can also hide your location data. How does this help you protect your browsing history? First, when you scramble your location, you’re likely to confuse ad networks trying to send you targeted ads. This will free your social media feeds and search engines from targeted ads that often are so accurate they seem like an invasion of privacy.
Second, hiding your location can protect you from cybercriminals looking to mine PII. VPNs make it impossible for criminals to discover your IP address. (The internet protocol address is what ties your device to a specific local network.) When they’re visible, criminals can trace IP addresses to reveal home addresses, full names, and phone numbers: all of which are key pieces of PII that, in the wrong hands, can jeopardize your identity.
While Canada and the European Union don’t allow ISPs (internet service providers) to even collect the browsing data of their customers, keep in mind that in some countries, like the U.S., ISPs can collect, store, share, and/or sell customer data. While advertisers are often the buyers of customer data, in the case of a breach, the more places your PII lives, the more likely it may be involved in a security incident. The goal is to limit the extent and number of places where your browsing history is stored.
VPNs can scramble your online movements to the point where not even ISPs can track it. Plus, when you log out, your device doesn’t keep a record of what you did while connected to the VPN. Incognito mode on your internet browser hides your IP address, but the websites you visit still collect cookies and store data about your online whereabouts, meaning that it’s not truly private browsing.
McAfee Safe Connect VPN encrypts your online activity to protect your data from prying eyes. With a premium paid plan, you can protect up to five devices at once with bank-grade Wi-Fi encryption. Feel more confident whenever you hop on the internet across all your connected devices with just one quick and easy step.
The post Why Everyone Needs a VPN appeared first on McAfee Blog.

Quick mental math challenge: How many Apple Watches can you buy with $118 billion dollars? If you guessed around 296 million watches congrats, you’re smarter than the writer of this blog! We had to use a calculator. The point is that’s the predicted size of the US wearable market by 2028 according to a recent report. That means for as much wearable tech as we have in our lives already, even more, is on the way.
If you own a piece of wearable tech it’s easy to understand why it’s so popular. After all, it can track our fitness, provide contextual help in daily life, and, in the case of hearing aids, even do cool things like sync with Bluetooth. As VR and AR gains a foothold who knows what other incredible tech might be headed our way by 2028? However wearable tech also comes with certain risks. The most prominent: cybercriminals potentially gaining access to your data.
The weakest link in the wearables space is your mobile phone, not the actual wearable device itself. That’s because wearables tend to link to your mobile device over a short-range wireless spectrum known as “Bluetooth.” This spectrum is used to send and receive data between your wearable device and your mobile. That makes your mobile a prime target for hackers.
Most commonly, hackers gain access to the data on your mobile through malware-laden apps. These apps are oftentimes designed to look like popular apps, but with enough differences that they don’t flag copyright suspicion.
Hackers can use these malicious apps to do a variety of things from making phone calls without your permission, sending and receiving texts, and extracting personal information—all potentially without your knowledge. They can also, with the help of your wearable, track your location through GPS and record any health issues you’ve entered into your wearable. The point is: once they have permissions to your mobile device, they have a lot of control and a lot of resources.
The hacker can then use this data to conduct varying forms of fraud. Need a special prescription from your doctor that happens to sell well on the black market? Well, so does the hacker. Going out for a jog in the morning? Good information for a burglar to know. These personal details just scratch the surface of information available for the taking on your mobile devices.
These types of threats aren’t limited to wearables, however. The Internet of Things—the phenomenon of devices connected to the Internet for analysis and optimization—encompasses all sorts of other electronic devices such as washing machines and refrigerators that can put your data at risk as well. But these life-changing devices can be secured through education and industry standards. Two things we’re working on day and night.
Of course, securing the weakest link in your wearables environment, your phone will go a long way towards keeping your data safe. But what happens when your computer, where you store backups of your smartphone, is compromised too? We’ve got you covered with McAfee LiveSafe service, our comprehensive security solution that provides protection for your entire online life.
service, our comprehensive security solution that provides protection for your entire online life.
The post The Wearable Future Is Hackable. Here’s What You Need To Know appeared first on McAfee Blog.

Have you ever been online and replied to a comment or post? Maybe it was on Reddit or on an influencer’s Instagram. Did other people reply to you, and were any of them unexpectedly hostile? When you’re online, a little hostility is sadly par for the course, but most people brush it off and move on to enjoy other aspects of life online. But what would you do if that unpleasant interaction went much farther than was reasonable? What if one day you discovered the most important parts of your identity had been maliciously and intentionally revealed online? Let’s talk about doxxing – what it is and how you can avoid becoming a victim of this kind of harassment.
Doxxing, derived from the hacker term “dropping docs”, is internet slang for revealing someone’s identity online for the purposes of harassing them. It usually goes way beyond simply revealing someone’s email address or name and may involve personal information like a home address or workplace, SSN, financial information, phone number, pictures, texts, IP address, and other important details. The tricky thing about doxxing is that aspects of it may not be a crime, depending on what you’ve made publicly available online. However, the context in which doxxing occurs is crucial. Often it’s the first step taken to incite more severe harassment. For instance, the doxxer may not plan on taking action against their target but instead hope that someone else does. When put up against a recent Pew Research report showing that 41% of U.S. web users experience harassment in some form, it’s clear that Doxxing is a dangerous trend online.
Doxxing is a problem that’s grown in scope simply because there’s so much more data about us being kept online. Third-party services, called data brokers, capture our account info, the sites we visit, how long we spent on them, and other kinds of metadata to create profiles they then resell to advertisers. If someone gets access to these troves of data, they can reveal extremely damaging information about an individual, or data that allows a person to be damaged. For instance, with a phone number and a current address, some criminals were able to call in SWAT teams on innocent individuals. Political dissidents are often doxxed by the governments their protesting against. And on a lighter note, the adult website Ashley Madison, which promotes extramarital affairs, had their members’ data leaked online, to the embarrassment of a few public figures.
The response should be very similar to the one you’d take if your wallet was stolen. Move fast, stem the loss, and begin remediation as soon as possible. Here are some broad steps that can be taken.
Of course, not being doxxed in the first place is the ultimate goal of a proactive online protection plan. Here’s what we recommend:
Identity theft protection services help protect your data, monitor your online accounts like emails, SSNs, and more. In addition to online monitoring, they should also offer insurance and even theft remediation if the worst should occur.
Before you tag your location, friends, or workplace in a photo think about who has access to this information. What’s gained or lost by sharing all that info? Also, security questions for your accounts should not use the name of your pet or your first-born child if you have posted those on Facebook.
Public Wi-Fi networks at coffee shops and airports may not be secure against hackers and snooping. That’s why we recommend using a VPN whenever you’re connected online. This powerful tool hides your activity and location whenever you’re online on an unsecured network.
Googling yourself is a great way to see if anyone is using your online identity in bad ways.
Social networks allow you to control who can see your data. Usually, with a few clicks, you can restrict what you show online to a great degree. For instance, makes your payments viewable to other users as a default, but can easily be changed to hide them from the public.
Using long, complex, unique passwords for every account is convenient and maybe the best way to prevent your information from being stolen. Yes, we said convenient because with a password manager you only need to remember one key to create and manage much longer ones for all your most important accounts.
The reality is that the more we live online, the more our identities will too. This does not mean we need to live a restricted life online. In fact, using comprehensive online protection, which features most of the tools above, we can remain free to enjoy life on our terms. Doxxing is something to be aware of, but with great protection, it’s far from anything we need to be worried about as we make the most of our lives online.
The post Doxxing, The Internet, and How You Can Lock Down Your Data appeared first on McAfee Blog.

There are very few guarantees in this world – but experiencing drama when you are a parent is a sure thing! And as a mum of 4, I’ve had my fair share. Whether it’s friendship issues, homework problems or just picking up the pieces after some bad choices – I feel like my job as a mother is most tested when I’m helping my boys navigate the tough stuff.
But after clocking up 25 years of parenting, I’ve learned one thing – when you’re in the thick of issues with your kids, being calm (even on the outside) is the best way of getting to the bottom of an issue, and helping them solve it.
Even though we may compartmentalize our lives into offline and online, our kids don’t. For them, it’s the same thing! They use their online life to set up their online activities. In fact, their online life is a critical element of their day-to-day lives. So, if a problem arises online – an embarrassing photo is shared or they make a wrong move – it can feel like their whole world is affected.
I don’t know how many times I’ve wanted to scream this from my lungs when my boys have found themselves in tricky online situations over the years. And I am sure I am not alone. When our kids come to us with an online issue, all we want to do is throw the router in the bin or cancel their phone plan. But, that, my friends, is the worst think you can do. If your kids think there is even a small chance you’ll remove their technology, then I promise you that they will never come to you with an online issue. They would much rather try and work it out themselves than threaten disconnection because their online world is their entire world.
Without a doubt, THE most important thing you can do for your kids is to guarantee that you will NOT scream, shout or disconnect them from their devices if they come to you with a problem. Even though you know it will be tough, promising them that you will remain calm will mean they are far more likely to seek your advice when things are tough. Of course, I am not suggesting that you don’t deal out punishments or introduce new rules as a result of the issue but remaining approachable is key.
Being a teenager in this digital era is completely different from the 70’s, 80’s and 90’s. So, while some of the issues your kids may experience may mirror yours, many will not. Thankfully, we didn’t have the constant pressure that social media can be when we were growing up. Some kids can rationalize the way social media works and not lose any sleep over it whereas others will find it much trickier to navigate.
So, take a minute to really understand their social media-dominated world. Many kids, understandably, struggle when comparing themselves to someone’s perfectly curated Instagram feed; feel lonely or ‘less than’ when discovering that their friends are all out (thanks to a shared pic online) but they weren’t invited; or, consumed by the number of likes their posts achieve. As the great Atticus Finch in ‘To Kill A Mockingbird’ said ‘You never really understand a person until you consider things from his point of view … until you climb into his skin and walk around in it.” So, try as hard as you can to understand how these pressures can affect their mindset.
When things are tricky and overwhelming, making a plan can help direct the angst and reduce the worry. Depending on the issue your child is having online, you may want to introduce some new rules around the time and place they can use their device. For example, if devices were not yet banned from the bedroom – this could be a good place to start. You could also insist devices are placed in a ‘charging zone’ on the kitchen bench overnight so their bedroom becomes a tech-free zone.
Additionally, if you are worried your child is experiencing concerning levels of anxiety or low mood as a result of the situation, you might want to include making an appointment with the counselor at school or an independent psychologist. Also, notifying the school may also be a helpful action point for the plan too – depending again on the nature of the issue.
If I’m being honest, being calm and chilled is probably not my natural state. I could blame it on genetics or maybe the amount of caffeine I consume but when it comes to my helping my boy with the tricky stuff, I dig deep. I channel my inner yogi and muster up all the patience and chilled vibes I can because it’s so worth it. Knowing my boys understand they can come to me about any problem – online or offline – means they know someone always has their back. And isn’t that our job as parents?
Till next time
Alex xx
The post Why Staying Calm May Be One Of The Best Ways Of Keeping Your Kids Safe Online appeared first on McAfee Blog.

There’s millions of dollars to be made in social media. For scammers.
New data from the U.S. Federal Trade Commission (FTC) suggests that Americans lost nearly three-quarters of a billion dollars to social media fraud in 2021, signaling that social media may be the most profitable method of scamming victims—marking an 18-fold increase over 2017.
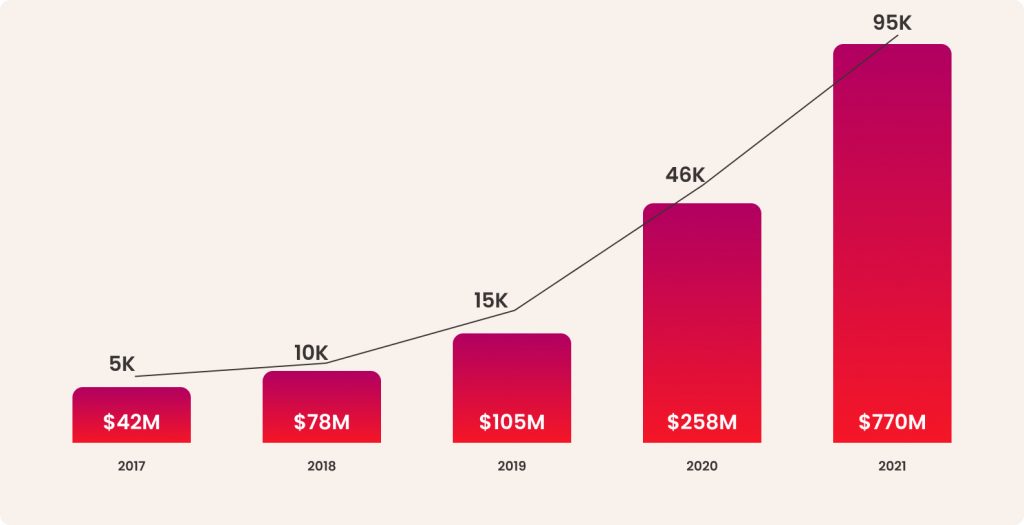
And that’s just cases of reported fraud.
Of the roughly 95,000 cases tallied in 2021, the actual number of reports and losses are arguably much higher because fraud victims infrequently report these crimes to the FTC or other agencies. Likewise, few take advantage of the FTC’s resources for recovering from fraud. Instead, they’ll share the sad news with family or friends if anyone at all.
Despite the rise of these online crimes, there are several things you can do to increase your awareness of social media fraud—what it looks like and how it’s pulled off—along with other ways you can prevent scammers from targeting you and the ones you care about.
Several types of social media fraud abound, yet the FTC reports that three types of scams prevail:
These often involve bogus sites that promote opportunities to mine or invest in cryptocurrencies. Rather than use these sites to trade in legitimate cryptocurrencies, scammers use these as a front to collect funds. The funds are never invested and never returned. Thanks to social media, scammers have a quick and easy way to drive victims to such bogus sites.
By starting up a chat through an unexpected friend request or a message that comes out of the blue, a scammer develops a budding romantic relationship with a victim—and eventually starts asking for money. Public social media profiles are particularly attractive to scammers because they’re loaded with information that scammers can use to win a victim’s confidence or heart.
Using ads on social media, scammers drive victims to phony online stores that will take people’s money but that don’t deliver the goods. They’re simply a way for scammers to harvest cash from unsuspecting shoppers. These sites may impersonate reputable brands and stores or they may sell bogus products altogether. Either way, victims pay and receive nothing in return.
Together, these three types of scams accounted for the overwhelming majority of losses and reports of social media fraud, which are broken down in detail as follows:
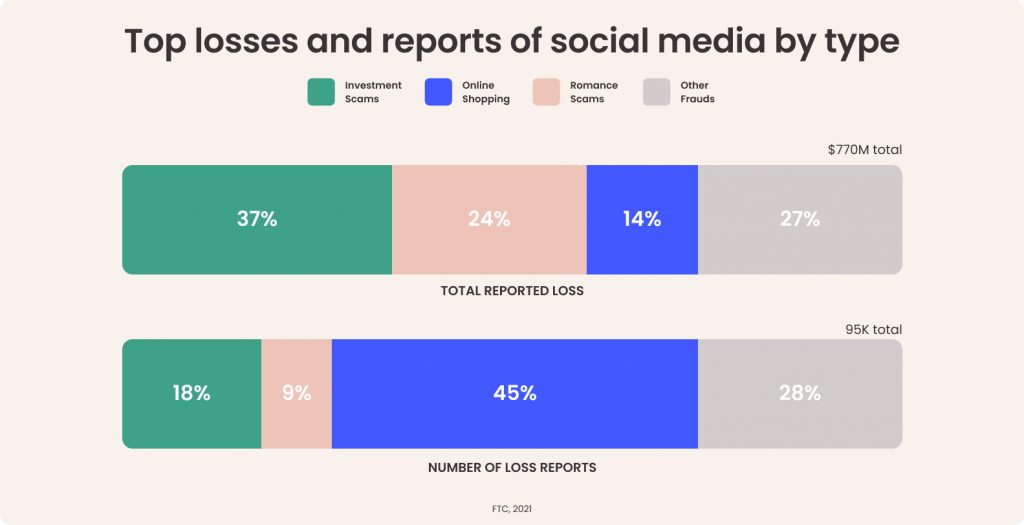
As illustrated, investment and romance scams may get reported less frequently, yet they are among the costliest scams going on social media. Meanwhile, online shopping scams on social media are far more common yet rake in fewer dollars overall.
For one, reach. Nearly half of the global population uses social media today. That translates into billions of people who can be made into potential victims. Secondly, social media provides the tools to reach those people through the otherwise legitimate services and features available to the people and businesses that use social media to connect.
In the case of investment and shopping scammers, the ad platforms are of particular use. For romance scammers, direct messaging and profile pages are potential avenues for fraud.
Scammers use the highly targeted ad platform that social media companies use to generate revenue. With millions of detailed user profiles in their data stores, social media companies put that data to work in their ad platforms allow businesses to create ads designed to reach specific age groups, hobbies and interests, past purchases, and so on. Just as easily, a scammer can use the same tools to cook up bogus ads for their bogus products, services, and sites at a relatively low cost.
For example, a scammer could target older females with an interest in investing. From there, the scammer could narrow down that target profile to those who live in areas of the country with a desired average income level, and who have shown interest in investment products before. The scammers would create an ad that takes them to phony website designed to entice that target group into purchasing a bogus product, service, or crypto. The FTC reports that the median loss for an online shopping scam in 2021 was $118, while online investment scams on social media racked up a median loss of $1,800 per victim. These stats make a strong case for sticking to reputable and established retailers and accredited financial services.
In the case of romance scammers on social media, the posts and personal profiles that form the heart of social media offer con artists a treasure trove. With a potential victim’s life a relatively open book, full of birthdays, events, interests, and activities for all to see, scammers have the hooks they need to form a phony romantic relationship online—or at least make the attempt at one.
For example, a scammer reaches out to a potential victim with a friend request. With the profile and posts this romance scammer has at hand, they can spin all manner of intriguing, yet utterly false tales designed to gain the victim’s trust. With that trust established, they can follow up with a similarly intriguing story about needing “a little help” to cover some “unexpected expenses,” often in the form of a gift card or reloadable debit card—sometimes stringing out a series of requests over time. According to the FTC, the median loss for this type of romance scam in 2021 was around $2,000 per victim.
People worldwide spend an average of 145 minutes a day on social media. And with users in the U.S. spending just over two hours on social media a day, that’s a great deal of potential exposure to scams.
Yet, whether you’re using Facebook, Instagram, TikTok, or whatnot, here are several things you can do that can help keep you safe and secure out there:
Passwords mark square one in your protection, with strong and unique passwords across all your accounts forming primary line of defense. Yet with all the accounts we have floating around, juggling dozens of strong and unique passwords can feel like a task—thus the temptation to use (and re-use) simpler passwords. Hackers love this because one password can be the key to several accounts. Instead, try a password manager that can create those passwords for you and safely store them as well. Comprehensive security software will include one.
Social media platforms like Facebook, Instagram, and others give you the option of making your profile and posts visible to friends only. Choosing this setting keeps the broader internet from seeing what you’re doing, saying, and posting, which can help protect your privacy and give a possible scammer much less material to work with.
Be critical of the invitations you receive. Out-and-out strangers could be more than just a stranger, they could be a fake account designed to gather information on users for purposes of fraud. There are plenty of fake accounts too. In fact, in Q3 of 2021 alone, Facebook took action on 1.8 billion fake accounts. Reject such requests.
We’re increasingly accustomed to the warnings about phishing emails, yet phishing attacks happen plenty on social media. The same rules apply. Don’t follow any links you get from strangers by way of instant or direct messages. And keep your personal information close. Don’t pass out your email, address, or other info as well. Even those so-called “quiz” posts and websites can be ruses designed to steal bits and pieces of personal info that can be used as the basis of an attack.
When you’re purchasing online, do some quick research on the company. How long have they been around? Have any complaints been recorded by your attorney general or local consumer protection agency? When you meet someone new, do a reverse image search on their profile pic to see where else it appears. Look up their name in search as well. If the results you find don’t match up with the person’s story, it may be a sign of a scam.
 Online protection software can protect you from clicking on malicious links while on social media while steering you clear of other threats like viruses, ransomware, and phishing attacks. It can look out for you as well, by protecting your privacy and monitoring your email, SSN, bank accounts, credit cards, and other personal information. With identity theft a rather commonplace occurrence today, security software is really a must. Additionally, our online protection software can also provide you with an online Protection Score that shows you just how safe you are. From there, it calls out any weak spots and then walks you through the steps to shore it up with personalized guidance.
Online protection software can protect you from clicking on malicious links while on social media while steering you clear of other threats like viruses, ransomware, and phishing attacks. It can look out for you as well, by protecting your privacy and monitoring your email, SSN, bank accounts, credit cards, and other personal information. With identity theft a rather commonplace occurrence today, security software is really a must. Additionally, our online protection software can also provide you with an online Protection Score that shows you just how safe you are. From there, it calls out any weak spots and then walks you through the steps to shore it up with personalized guidance.
It’s unfortunate seeing a resource we’ve come to know and love over the past years get taken advantage of this way. Yet taking the steps outlined above can go a long way to prevent it from happening to you or someone you love.
One important note is to strongly consider filing a report if you believe you’ve been a victim of a social media scam. While some of the scammers behind these crimes are small-time operators, there are larger, almost business-like operations that conduct these crimes on a broader and sometimes international scale. So whether filing a report will help you recover some or all your losses, it can provide information to businesses and agencies that can help keep it from happening to others.
For more on online theft and fraud, and how you can spot and report it, check out our article on the topic. Doing so may help you, and someone else as well.
The post The Gold Rush of Fraud: Why Scammers Have Flocked to Social Media appeared first on McAfee Blog.

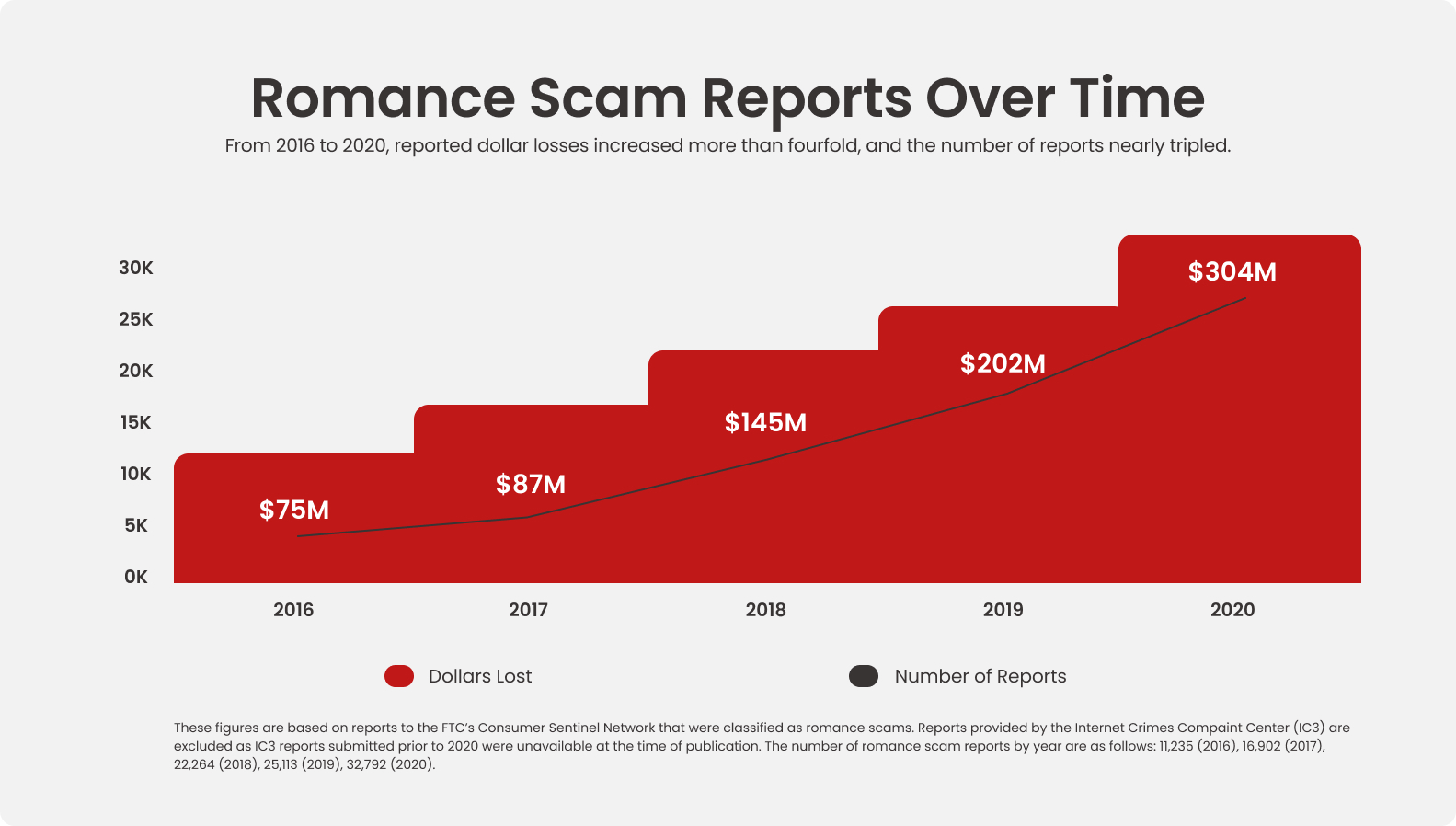
For years now, the popularity of online dating has been on the rise—and so have the number of online romance scams that leave people with broken hearts and empty wallets.
According to the U.S. Federal Trade Commission (FTC), the reported costs of online romance scams jumped 50% from 2019 to 2020, to the tune of $304 million. And that’s not entirely because 2020 was a pandemic year. From 2016 to 2020, the volume of reported cases tripled, while reported losses nearly quadrupled. Over that period, online romance scams are not only becoming more common, but they’re also becoming more costly.
Dating and romance scams aren’t limited to online dating apps and sites, they’ll happen on social media and in online games as well. However, the FTC reports that the scam usually starts the same way, typically through an unexpected friend request or a message that comes out of the blue.
With that initial introduction made, a chat begins, and a friendship (or more) blossoms from there. Along the way, the scammer will often rely on a mix of somewhat exotic yet believable storytelling to lure the victim in, often involving their job and where they’re working. Reports say that scammers will talk of being workers on an offshore oil rig, members of the military stationed overseas, doctors working with an international organization, or working in the sort of jobs that would prevent them from otherwise easily meeting up in person.
With the phony relationship established, the scammer starts asking for money. The FTC reports that they’ll ask for money for several bogus reasons, usually revolving around some sort of hardship where they need a “little help” so that they can pay:
The list goes on, yet that’s the general gist. Scammers often employ a story with an intriguing complication that seems just reasonable enough, one where the romance scammer makes it sound like they could really use the victim’s financial help.
People who have filed fraud reports say they’ve paid their scammer in a few typical ways.
One is by wiring money, often through a wire transfer company. The benefit of this route, for the scammer anyway, is that this is as good as forking over cash. Once it’s gone, it’s gone. The victim lacks the protections they have with other payment forms, such as a credit card that allows the holder to cancel or contest a charge.
Another way is through gift cards. Scammers of all stripes, not just romance scammers, like these because they effectively work like cash, whether it’s a gift card for a major online retailer or a chain of brick-and-mortar stores. Like a wire transfer, once that gift card is handed over, the money on it is highly difficult to recover, if at all.
One more common payment is through reloadable debit cards. A scammer may make an initial request for such a card and then make several follow-on requests to load it up again.
In all, a romance scammer will typically look for the easiest payment method that’s the most difficult to contest or reimburse, leaving the victim in a financial lurch once the scam ends.
When it comes to meeting new people online, the FTC suggests the following:
Scammers, although arguably heartless, are still human. They make mistakes. The stories they concoct are just that. Stories. They may jumble their details, get their times and dates all wrong, or simply get caught in an apparent lie. Also, keep in mind that some scammers may be working with several victims at once, which is yet another opportunity for them to get confused and slip up.
As mentioned above, some romance scammers troll social media and reach out through a direct message or friend request. With that, there are three things you can do to cut down your chances of getting caught up with a scammer:
Social media platforms like Facebook, Instagram, and others give you the option of making your profile and posts visible to friends only. Choosing this setting keeps the broader internet from seeing what you’re doing, saying, and posting, which can help protect your privacy and give a romance scammer less information to exploit.
Be critical of the invitations you receive. Out-and-out strangers could be more than a romance scammer, they could be a fake account designed to gather information on users for purposes of cybercrime, or they can be an account designed to spread false information. There are plenty of them too. In fact, in Q3 of 2021 alone, Facebook took action on 1.8 billion fake accounts. Reject such requests.
Security software can protect you from clicking on malicious links that a scammer may send you online, while also steering you clear of other threats like viruses, ransomware, and phishing attacks in general. It can look out for your personal information as well, by protecting your privacy and monitoring your email, SSN, bank accounts, credit cards, and other info that a scammer or identity thief may put to use. With identity theft a rather commonplace occurrence today, security software is really a must.
If you suspect that you’re being scammed, put an end to the relationship and report it, as difficult as that may feel.
Notify the FTC at ReportFraud.ftc.gov for support and next steps to help you recover financially as much as possible. Likewise, notify the social media site, app, or service where the scam occurred as well. In some cases, you may want to file a police report, which we cover in our broader article on identity theft and fraud.
If you sent funds via a gift card, the FTC suggests filing a claim with the company as soon as possible. They offer further advice on filing a claim here, along with a list of contact numbers for gift card brands that scammers commonly use.
Lastly, go easy on yourself. If you find yourself a victim of online dating or romance fraud, know that you won’t be the first or last person to be taken advantage of this way. By reporting your case, you in fact may help others from falling victim too.
The post Phony Valentines: Online Dating Scams and How to Spot Them appeared first on McAfee Blog.

When you logged on to your computer this morning, data privacy probably wasn’t the first thing you were thinking about. The same goes for when you opened your phone to catch up on social media and check emails, turned on your smart TV for a family movie night, or all the other ways we routinely use our connected devices in our everyday lives.
Although we live in an increasingly connected world, most of us give little thought to data privacy until after our personal information has been compromised. However, we can take proactive steps to help ourselves and our loved ones navigate this environment in a safe way. On January 28th – better known as Data Privacy Day – we have the perfect opportunity to own our privacy by taking the time to safeguard data. By making data privacy a priority, you and your family can enjoy the freedom of living your connected lives online knowing that your information is safe and sound.
Did you know that there is a difference between data security and data privacy? Although the two are intimately intertwined, there are various characteristics of each that make them different. National Today3 provides a useful analogy to define the two:
At this point, we already know not to share our passwords or PIN numbers with anyone. But what about the data that is collected by companies every time we sign up for an email newsletter or make an online account? Oftentimes, we trust these companies to guard the personal data they collect from us in exchange for the right to use their products and services. However, the personal information collected by companies today is not regarded as private by default, with a few exceptions. For this reason, it’s up to us to take our data privacy into our own hands.
Because we spend so much of our day online, plenty of our information is available on the internet. But what happens if one of your favorite online retailers experiences a data breach? This is the reality of the world we live in today, as data breaches have been on the rise and hackers are continuously finding clever, new ways to access our devices and information.
Thanks to the COVID-19 pandemic, we’ve become more reliant on technology than ever before. Whether it be for distance learning, online shopping, mobile banking, or remote work, we’ve all depended on our devices and the internet to stay connected. But with more time online comes more opportunities for cybercriminals to exploit. For example, with the massive increase in remote work since the onset of the pandemic, hackers have hijacked online meetings through a technique called ‘Zoombombing4.’ This occurred after the online conferencing company shared personal data with Facebook, Google, and LinkedIn. Additionally, the number of patient records breached in the healthcare industry jumped to 21.3 million in the second half of 2020 due to the increase in remote interactions between patients and their providers5.
When it comes to data breaches, any business is a potential target because practically every business is online in some way. When you put this in perspective, it’s important to consider what information is being held by the companies that you buy from. While a gaming service will likely have different information about you than your insurance company, you should remember that all data has value, and you should take steps to protect it like you would money.
Your browsing history and personal information are private, and we at McAfee want to keep it that way. By using McAfee Secure VPN, you can browse confidently knowing that your data is encrypted.
To further take control of your data privacy, monitor the health of your online protection with McAfee’s Protection Score. This tool provides simple steps to improve your security and allows you to know how safe you are online, which is the first step towards a safer, more confident connected life. Check your personal protection score here.
Here are a few more tips to keep you on top of your data privacy game:
1. Update your privacy and security settings. Begin with the websites and apps that you use the most. Check to see if your accounts are marked as private, or if they are open to the public. Also, look to see if your data is being leaked to third parties. You want to select the most secure settings available, while still being able to use these tools correctly.
2. Lock down your logins. Secure your logins by making sure that you are creating long and unique passphrases for all your accounts. Use multi-factor identification, when available.
3. Protect your family and friends. You can make a big difference by encouraging your loved ones to protect their online privacy. By helping others create solid safety habits as they build their digital footprints, it makes all of us more secure.
Follow the conversation this Data Privacy Day by following #PrivacyAware and #DataPrivacyDay on social media.
The post It’s Data Privacy Day: Here’s How to Stay Protected in 2022 appeared first on McAfee Blog.

Social media is part of our social fabric. So much so that nearly 50% of the global population are social media users to some degree or other. With all that sharing, conversing, and information passing between family and friends, social media can be a distinct digital extension of ourselves—making it important to know how you can protect your social media accounts from hacks and attacks.
Beyond the sheer number of people who’re on social media, there’s also the amount of time we spend on it. People worldwide spend an average of 145 minutes a day on social media. With users in the U.S. spending just over two hours on social media a day and users in the Philippines spending nearly four hours a day, that figure can vary widely. Yet it’s safe to say that a good portion of our day features time scrolling and thumbing through our social media feeds.
Given how much we enjoy and rely on social media, now’s a fine time to give your social media settings and habits a closer look so that you can get the most out of it with less fuss and worry. Whether you’re using Facebook, Instagram, TikTok, or whatnot, here are several things you can do that can help keep you safe and secure out there:
Passwords mark square one in your protection, with strong and unique passwords across all your accounts forming primary line of defense. Yet with all the accounts we have floating around, juggling dozens of strong and unique passwords can feel like a task—thus the temptation to use (and re-use) simpler passwords. Hackers love this because one password can be the key to several accounts. Instead, try a password manager that can create those passwords for you and safely store them as well. Comprehensive security software will include one.
Social media platforms like Facebook, Instagram, and others give you the option of making your profile and posts visible to friends only. Choosing this setting keeps the broader internet from seeing what you’re doing, saying, and posting, which can help protect your privacy.
Be critical of the invitations you receive. Out-and-out strangers could be more than just a stranger, they could be a fake account designed to gather information on users for purposes of cybercrime, or they can be an account designed to spread false information. There are plenty of them too. In fact, in Q3 of 2021 alone, Facebook took action on 1.8 billion fake accounts. Reject such requests.
Nothing says “there’s nobody at home right now” like that post of you on vacation or sharing your location while you’re out on the town. In effect, such posts announce your whereabouts to a broad audience of followers (even a global audience, if you’re not posting privately, as called out above). Consider sharing photos and stories of your adventures once you’ve returned.
It’s a famous saying for a reason. Whether your profile is set to private or if you are using an app with “disappearing” messages and posts (like Snapchat), what you post can indeed be saved and shared again. It’s as simple as taking a screenshot. If you don’t want it out there, forever or otherwise, simply don’t post it.
We’re increasingly accustomed to the warnings about phishing emails, yet phishing attacks happen plenty on social media. The same rules apply. Don’t follow any links you get from strangers by way of instant or direct messengers. And keep your personal information close. Don’t pass out your email, address, or other info as well. Even those so-called “quiz” posts and websites can be ruses designed to steal bits and pieces of personal info that can be used as the basis of an attack.
Sadly, social media can also be a place where people pull a fast one. Get-rich-quick schemes, romance cons, and all kinds of imposters can set up shop in ads, posts, and even direct messages—typically designed to separate you from your personal information, money, or both. This is an entire topic to itself, and you can learn plenty more about quizzes and other identity theft scams to avoid on social media.
Some platforms such as Facebook allow users to review posts that are tagged with their profile names. Check your account settings and give yourself the highest degree of control over how and where your tags are used by others. This will help keep you aware of where you’re being mentioned by others and in what way.
Security software can protect you from clicking on malicious links while on social media while steering you clear of other threats like viruses, ransomware, and phishing attacks. It can look out for you as well, by protecting your privacy and monitoring your email, SSN, bank accounts, credit cards, and other personal information. With identity theft a rather commonplace occurrence today, security software is really a must.

Now you can point to a number that shows you just how safe you are with our Protection Score. It’s an industry first, and it works by taking stock of your overall security and grading it on a scale of 0 to 1,000. From there, it calls out any weak spots and then walks you through the steps to shore it up with personalized guidance. This way, you’re always in the know about your security, privacy, and personal identity on social media and practically wherever else your travels take you online.
The post How to Protect Your Social Media Accounts appeared first on McAfee Blog.

We live online these days, sharing everything from vacation pictures to what we eat for breakfast on the internet. The internet is also useful for daily activities, like buying groceries or paying bills.
While it’s convenient to connect with people and complete tasks online, cybercriminals are eager to use the internet to steal financial or personal data for their personal gain — otherwise known as identity theft. This is a criminal act and can affect your credit score in a negative way and cost money to fix. It can also affect employment opportunities since some employers conduct a credit check on top of drug testing and a criminal history check. Identity theft victims may even experience an impact to their mental health as they work to resolve their case.
The good news is that being able to recognize the signs of identity theft means you can act quickly to intervene and minimize any effects in case it happens to you. You can also protect yourself by using preventive measures and engaging in smart online behavior. This article provides essential information about identity theft, giving you the tools you need to become an empowered internet user and live your best life online.
The internet is a great place to be, but identity thieves hope to catch you off-guard and seek access to your personal information for their benefit. This could include private details like your birth date, bank account information, Social Security number, home address, and more. With data like this, an individual can adopt your identity (or even create a fake identity using pieces of your personal profile) and apply for loans, credit cards, debit cards, and more.
You don’t have to be kept in the dark, though. There are several signs that your identity has been stolen, from a change in your credit score to receiving unfamiliar bills and debt collectors calling about unfamiliar new accounts. If you suspect that you’ve been affected by identity fraud, you can act fast to minimize what happens. Here’s what to do.
Start by contacting law enforcement to file a report. Your local police department can issue a formal report, which you may need to get your bank or other financial institution to reverse fraudulent charges. An official report assures the bank that you have been affected by identity fraud and it’s not a scam.
Before going to the police, gather all the relevant information about what happened. This could include the dates and times of fraudulent activity and any account numbers affected. Bringing copies of your bank statements can be useful. Also, make note of any suspicious activity that could be related. For example, was your debit card recently lost or your email hacked? The police will want to know.
You should also notify any businesses linked to your identity theft case. Depending on the type of identity theft, this could include banks, credit card companies, medical offices, health insurers, e-commerce stores, and more. For example, if someone used your credit card to make purchases on Amazon, alert the retailer.
Medical identity theft is another good example. In this case, a fraudster may assume your identity to gain access to health care services, such as medical checkups, prescription drugs, or pricey medical devices like wheelchairs. If someone uses your health insurance to get prescription drugs from a pharmacy, for instance, make sure to alert the pharmacy and your insurer.
The Federal Trade Commission (FTC) is a government body that protects consumer interests. You can report identity theft via their portal, IdentityTheft.gov. They’ll then use the details you provide to create a free recovery plan you can use to address the effects of identity theft, like contacting the major credit bureaus or alerting the Internal Revenue Service (IRS) fraud department. You can report your case online or by calling 1-877-438-4338.
A common consequence of identity theft is a dip in the victim’s credit score. For example, a cybercriminal may take out new lines of credit in the victim’s name, accrue credit card debt, and then not pay the balance. For this reason, contacting the credit monitoring bureaus is one of the most important steps to take in identity theft cases.
There are three main agencies: TransUnion, Equifax, and Experian. You can get a free credit report from each agency every 12 months via AnnualCreditReport.com. Check the report and note all fraudulent activity or false information and flag it with the relevant bureau’s fraud department. You should also initiate a fraud alert with each agency.
A fraud alert requires any creditors to verify your identity before opening a new line of credit. This adds an extra layer of security. An initial fraud alert lasts for 90 days. Once this expires, you can prolong your protection via an extended fraud alert, which will remain valid for seven years. You can notify one of the big three bureaus to set it up. They are then required to notify the other two bureaus.
A credit freeze is another smart move, which you can do through each of the three major credit bureaus. You can either call them or start the process online. This prevents people from accessing your credit report. Lenders, creditors, retailers, landlords, and others may want to see your credit as proof of financial stability. For example, if someone tries to open a phone contract under your name, the retailer may check the credit report. If there is a credit freeze in place, they won’t be able to view it and won’t issue the contract. If you need to allow someone access to your credit report, you can temporarily lift the freeze.
Identity theft is often linked with leaked or hacked passwords. Even if you aren’t sure whether your passwords have been compromised, it’s best to play it safe. Change passwords to any affected accounts. Make sure to use strong passwords with a mix of numbers, letters, and symbols. Further, if there’s a chance to activate two-factor authentication on your accounts, this can provide added protection going forward.
Ideally, you’ll never become the victim of identity theft, but things can happen. Cybercriminals work hard, but you can stay one step ahead by taking a few preventative measures. These include:
You can further protect yourself with antivirus software like McAfee’s Total Protection plan. This can help protect your devices against spyware and viruses. You can also enhance your network security with a firewall and virtual private network (VPN). A firewall controls traffic on your internet network based on predefined security parameters, while a VPN hides your IP address and other personal data.
Don’t let concerns about identity fraud keep you from enjoying all the conveniences and perks the internet offers. McAfee’s identity theft protection services can help you stay connected while keeping you safe. Tailor your package to your household’s needs to get the safeguards you want, like ID theft coverage, VPN, and 24/7 monitoring. Our Total Protection plan also comes with $1 million in identity theft coverage to cover qualifying losses and hands-on support to help you reclaim your identity.
With McAfee by your side, you can stay online confidently.
The post What to Do If Your Identity Has Been Stolen appeared first on McAfee Blog.

If there’s a particularly clear picture that’s developed over the past couple of years, it’s that our privacy and our personal identities are worth looking out for. With that, we have your back. And here’s why.
In the U.S., reported cases of identity theft continue to rise. In the first half of 2022, the Federal Trade Commission (FTC) reported more than 600,000 cases of identity theft, with more than 230,000 of those reported cases involving credit card theft.
And that’s just what’s been reported in the U.S. Far more crime goes unreported, and it is estimated that the cost of identity theft and fraud goes well into the billions of dollars.
Yet behind each stat is a person, a family, and a household that dealt with anything from a financial headache to a major life event no thanks to identity theft and fraud. Accordingly, we’re seeing to it that every person has the tools to prevent this from happening to them.
Here’s a little bit about our approach. We looked at some of the key areas where people’s private information can be vulnerable and rolled out a set of features and services that can help make you safer than before. They’re all part of McAfee+, our latest line of comprehensive online protection. Depending on your plan and location, the following offer protections that can look after you, your privacy, and your identity—along with your devices and the things on them too.
Unsecured networks can leave us vulnerable, like when we use public Wi-Fi. What’s at issue is that a cybercriminal can potentially capture your login credentials and other personal information as you use a public network in a hotel, airport, coffee shop, library, and so forth.
So, we made sure to include a Virtual Private Network (VPN) to keep your information protected from prying eyes. It does this easily by detecting when you’re on a public network and automatically turning on your VPN. The VPN then scrambles or encrypts, your data as it flows over the network. Unlike some VPNs that require advanced settings to shield your data, our app offers seamless security.
Given that data breaches large and small continue to occur with more regularity than any of us would like, always-on monitoring of your private information is key.
Whether one of your personal accounts is hacked–or worse–another website somehow gets ahold of your data and subsequently gets breached, your data may end up on the dark web. This is where cybercriminals buy and sell information.
To detect these dangerous leaks, we included dark web monitoring, which alerts you if your log-in credentials have been exposed. It can even provide you with a link to the site that uses those credentials when the information is available. This allows you to swiftly reset your passwords, mitigating the risk.
We’ll scan some of the riskiest data broker sites and show you which ones are selling your personal info. We’ll also provide guidance on how you can remove your data from those sites and with select products, we can even manage the removal for you.
Recovering from identity fraud or theft can be expensive. Not to mention time consuming. We’ll help relieve the burden with $1M coverage for lawyer fees, travel expenses, lost wages, and more.
Should the unfortunate happen to you, we have your back. In several ways. We offer licensed recovery experts who can work with you any time, around the clock, all year long. These pros can use a limited power of attorney to do the heavy lifting for identity recovery, taking all necessary steps to repair identity and credit.
Our all-new ransomware coverage is now available, ready to help just in case—all backed by expert advice to help you find the quickest and best possible path to recovery. In addition to eligibility for up to $25,000 in reimbursement due to ransomware losses, our team of experts can help you, determine the severity of a ransomware attack and learn what immediate action steps you can take.
Knowing your safe and staying that way just got far simpler. With a colorful view, you can see exactly what your Protection Score is at a glance, which compiles your overall levels of security, privacy, and identity theft protection. Better yet, if it spots gaps in your protection, it guides you through straightforward fixes that can make you safer than before.
It’s an industry first, and something we all deserve—the ability to clearly see exactly how secure you are and to quickly shore up your protection whenever it’s needed.
Everyone has credit, and everyone needs to protect it. McAfee’s Credit Monitoring does just that. Whether the suspicious change in your report is big or small, we can help you detect it—and take the right steps to correct it.
You can put proactive protection in place by stopping unauthorized access to existing credit card, bank, and utility accounts or from new ones being opened in your name. Security freezes stop companies from looking at your credit profile, which halts the application process for loans, credit cards, utilities, new bank accounts, and more. A security freeze won’t affect your credit score.
Also on our list, we wanted to make personal protection easy to use and available across all your compatible devices. So, whether you’re out with just your phone, or at home working at your PC, you have access to your protection, and can even pick up where you left off on a different device.
Ultimately, that’s what any of us want—to enjoy the internet with confidence, knowing that whatever it is we’re doing online is secure.
The way we use the internet continues to evolve. After all, it wasn’t long ago that the idea of using a phone to see who’s at the front door may have seemed a bit odd. Let alone having a little chat with the speaker on your kitchen counter. Yet that’s where we are today. And as the internet evolves, so will we. The protection we offer will cover your increasingly connected life in whatever shape that takes.
No question about it. We’re committed to protecting you, your privacy, your identity, and certainly your devices too—and making all of it simple.
Here’s to a happy and secure year!
The post Protecting Your Privacy This Year appeared first on McAfee Blog.

It happens with more regularity than any of us like to see. There’s either a headline in your news feed or an email from a website or service you have an account with—there’s been a data breach. So what do you do when you find out that you and your information may have been caught up in a data breach? While it can feel like things are out of your hands, there are actually several things you can do to protect yourself.
Let’s start with a look at what kind of information may be at stake and why crooks value that information so much (it’s more reasons than you may think).
The fact is that plenty of our information is out there on the internet, simply because we go about so much of our day online, whether that involves shopping, banking, getting results from our doctors, or simply hopping online to play a game once in a while.
Naturally, that means the data in any given breach will vary from service to service and platform to platform involved. Certainly, a gaming service will certainly have different information about you than your insurance company. Yet broadly speaking, there’s a broad range of information about you stored in various places, which could include:
As to what gets exposed and when you might find out about it, that can vary greatly as well. One industry research report found that 60% of breaches were discovered in just days from the initial attack while others could take months or even longer to detect. Needless to say, the timeline can get rather stretched before word reaches you, which is a good reason to change your passwords regularly should any of them get swept up in a breach. (An outdated password does a hacker no good—more on that in a bit.)
The answer is plenty. In all, personal information like that listed above has a dollar value to it. In a way, your data and information are a kind of currency because they’re tied to everything from your bank accounts, investments, insurance payments—even tax returns and personal identification like driver’s licenses.
With this information in hand, a crook can commit several types of identity crime—ranging from fraud to theft. In the case of fraud, that could include running up a bill on one of your credits cards or draining one of your bank accounts. In the case of theft, that could see crooks impersonate you so they can open new accounts or services in your name. Beyond that, they may attempt to claim your tax refund or potentially get ID issued in your name as well.
Another possibility is that a hacker will simply sell that information on the dark marketplace, perhaps in large clumps or as individual pieces of information that go for a few dollars each. However it gets sold, these dark-market practices allow other fraudsters and thieves to take advantage of your identity for financial or other gains.
Most breaches are financially motivated, with some researchers saying nearly 90% of breaches are about the money. However, we’ve also seen hackers simply dump stolen information out there for practically anyone to see. The motivations behind them vary, yet could involve anything from damaging the reputation of an organization to cases of revenge.
A list of big data breaches is a blog article of its own, yet here’s a quick list of some of the largest and most impactful breaches we’ve seen in recent years:
Needless to say, it’s not just the big companies that get hit. Healthcare facilities have seen their data breached, along with the operations of popular restaurants. Small businesses find themselves in the crosshairs as well, with one report stating that 43% of data leaks target small businesses. Those may come by way of an attack on where those businesses store their records, a disgruntled employee, or by way of a compromised point-of-sale terminal in their store, office, or location.
In short, when it comes to data breaches, practically any business is a potential target because practically every business is online in some form or fashion. Even if it’s by way of a simple point-of-sale machine.
When a business, service, or organization falls victim to a breach, it doesn’t always mean that you’re automatically a victim too. Your information may not have been caught up in it. However, it’s best to act as if it was. With that, we strongly suggest you take these immediate steps.
Given the possibility that your password may be in the hands of a hacker, change it right away. Strong, unique passwords offer one of your best defenses against hackers. Update them regularly as well. As mentioned above, this can protect you in the event a breach occurs and you don’t find out about it until well after it’s happened. You can spare yourself the upkeep that involves a password manager that can keep on top of it all for you. If your account offers two-factor authentication as part of the login process, make use of it as it adds another layer of security that makes hacking tougher.
If you spot unusual or unfamiliar charges or transactions in your account, bank, or debit card statements, follow up immediately. That could indicate improper use. In general, banks, credit card companies, and many businesses have countermeasures to deal with fraud, along with customer support teams that can help you file a claim if needed.
If you haven’t done so already, consider signing up for a service that can monitor dozens of types of personal information and then alert you if any of them are possibly being misused. Identity protection such as ours gives you the added benefit of a professional recovery specialist who can assist with restoring your affairs in the wake of fraud or theft, plus up to $1 million in insurance coverage.
Our advice is to take a deep breath and get to work. By acting quickly, you can potentially minimize and even prevent any damage that’s done. With that, we have two articles that can help guide the way if you think you’re the victim of identity theft, each featuring a series of straightforward steps you can take to set matters right:
Again, if you have any concerns. Take action. The first steps take only minutes. Even if the result is that you find out all’s well, you’ll have that assurance and you’ll have it rather quickly.
The post What to Do If You’re Caught Up in a Data Breach appeared first on McAfee Blog.

What’s the difference between identity fraud and identity theft? Well, it’s subtle, so much so that it’s easy to use them nearly interchangeably. While both can take a bite out of your wallet, they are different—and knowing the differences can help you know understand what’s at stake.
Let’s start with an overview and a few examples of each.
So there’s that subtle difference we mentioned. Identity fraud involves misuse of an existing account. Identity theft means the theft of your personal information, which is then used to impersonate you in some way, such as opening new accounts in your name.
Above and beyond those definitions and examples, a couple of real-life examples put the differences in perspective as well.
As for identity fraud, individual cases of fraud don’t always make the headlines, but that’s not to say you won’t hear about it a couple of different ways.
The first way may be news stories about data breaches, where hackers gain things like names, emails, and payment information from companies or organizations. (Chipotle, RobinHood, and T-Mobile being recent examples.) That info can then end up in the hands of a fraudster, who then accesses those accounts to drain funds or make purchases.
On a smaller scale, you may know someone who has had to get a new credit or debit card because theirs was compromised, perhaps by a breach or by mistakenly making a payment through an insecure website or by visiting a phony login page as part of a phishing attack. These can lead to fraud as well.
Identity theft took on new forms during the pandemic, such as was the case of a Rhode Island man charged with nearly half a million dollars in a pandemic unemployment fraud case. Authorities allege that the man-made 85 unemployment claims in 2020 using the identities of several other people.
Similarly, a Massachusetts man was sentenced for filing fraudulent claims for relief funds, as well as open store credit accounts using fake identities. Court proceedings alleged that the personal information used to commit this fraud came from several sources, including information stolen from a realty company that collected that information from potential renters.
Identity theft can stem from the workplace as well, such as the sentencing of a Maryland man who used stolen lists of personal information from his former employer. From there, he was found guilty of garnering more than a million dollars in funds from food assistance programs and fraudulent car loans.
Identity theft can run far deeper than these examples. Because it effectively allows someone else to pose as you, an identity thief can do more than drain your accounts. They can also claim health insurance benefits, file taxes in your name, or possibly purchase the property. Further, an identity thief can potentially get a job, driver’s license, or other forms of ID in your name, which could ruin your credit history, reputation, or even create a police record in your name.
So while both identity fraud and identity theft are certainly something you want to prevent, identity theft holds the potential to affect far-reaching aspects of your life—which marks a distinct difference between the two.
It usually starts with someone saying anything from, “That’s strange …” to “Oh, no!” There’ll be a strange charge on your credit card bill, a piece of mail from a bill collector, or a statement from an account you never opened—just to name a few things.
With that, I have a few recent blogs that help you spot all kinds of identity crime, along with advice to help keep it from happening to you in the first place:
While there are differences between identity fraud and identity theft, they do share a couple of things in common: you can take steps to prevent them, and you can take steps to limit their impact should you find yourself faced with one or the other.
The articles called out above will give you the details, yet staying safe begins with vigilance. Check on your accounts and credit reports regularly and really scrutinize what’s happening in them. Consider covering yourself with an —and act on anything that looks strange or outright fishy by reporting it to the company or institution in question.
The post What’s the Difference Between Identity Fraud and Identity Theft? appeared first on McAfee Blog.

Most of us use the internet every day, so we’re comfortable sharing a lot of information online. However, cybercriminals want us to get a bit too comfortable so they can take our personal or financial data and use it for their benefit. This is called identity theft, and it can cost people money and may dip their credit score.
Fortunately, you can help minimize what happens by knowing the signs of identity theft and taking fast action when you recognize them. Find out how below.
Being online comes with many benefits, but it can also come with some risks. Identity theft usually begins with the criminal accessing sensitive personal data, such as Social Security numbers, birth dates, home addresses, bank account information, and driver’s license details. The fraudster can then take this information to fake your identity, using it to take out credit cards, apply for loans, and more.
Here’s a quick look at some ways identity thieves can get their hands on your valuable data:
There are many ways thieves can get their hands on your data. Luckily, there are ways you can protect yourself against these methods. For example, you can protect your computer, tablet, or mobile device against hackers by equipping it with a strong password and safeguarding against phishing by adding a firewall and utilizing a virtual private network (VPN) like those offered by McAfee.
With some best practices, you can protect your data and help safeguard you and your family against identity theft. One way to continue living your best life online is to watch for potential warning signs of identity theft. This ensures you can take fast action and minimize the effects if you’re targeted. Here are some essential signs to look out for.
Financial identity theft is one of the most common types of identity theft, and credit cards are a popular target. The rise in online shopping has made credit card fraud even more common.
Your online banking portal or app should allow you to set up alerts to email, call, or text you about suspected fraudulent credit card charges. If you get an alert, someone may have taken your identity.
If you apply for a loan or line of credit and your application is denied, dig deeper. A rejection could indicate that your credit score is lower than you thought, possibly due to fraudulent activity. For example, someone may use your information to get new credit cards and not pay them off, leaving you responsible.
Changes in your credit score can indicate identity theft. For example, if someone takes out utility bills in your name and doesn’t pay them, your credit score may dip. Checking your credit report from each of the three major credit bureaus (Equifax, Experian, and TransUnion) can help pinpoint the problem.
The Federal Trade Commission (FTC) allows U.S. consumers to get a free credit report every 12 months. Just visit AnnualCreditReport.com to get a copy of yours from the credit reporting agencies. You can also pay for credit monitoring services to track your score.
Once identity thieves obtain enough data, including your name and address, they might be able to open new accounts and credit cards. When you check your credit report, keep an eye out for new accounts that you didn’t open. Another red flag is if you start getting bank statements or bills addressed to you for accounts you don’t recognize.
Companies are required to notify customers of data breaches that could impact them. For example, if you save your payment information and home address on a music streaming provider’s website and their database is hacked, identity thieves may get your data. Keep an eye out for notifications and read the news. The McAfee blog is another great resource for information on data breaches.
If debt collectors start calling, be cautious, especially if they’re referring to accounts you aren’t familiar with. Don’t provide personal information to any collection agencies that call, as this can be a potential phishing scam. However, it’s a good idea to follow up on these cases by checking your credit report for new accounts. You could be liable if someone opened accounts under your name and didn’t pay them.
Medical theft occurs when a fraudster imitates another person to get health care or supplies. For example, a person might use your identity to get prescription medication at a pharmacy. If you get unfamiliar medical bills, follow up. Incorrect medical records could impact your insurance premiums or interfere with your ability to get the care you need in the future.
This could be an indicator of synthetic identity theft. This occurs when a fraudster creates a fake identity using various people’s real information. For example, they may use your address and Social Security number and another person’s photo to create a fake persona that’s creditworthy. They can then take out credit cards in that fake person’s name.
If you receive a confirmation of an annual tax filing before you’ve filed, take note. Criminals may try to file a tax return for another person to access their tax refund. Alternatively, you may find that you’re unable to e-file your taxes, which can occur if someone else has already filed under your name.
No one wants their identity stolen, but it’s still good to be prepared if it does happen. If you notice the above red flags, here are some steps you may need to take:
You may also want to visit IdentityTheft.gov to report identity theft and find resources to help guide your recovery plan.
Worries about identity fraud shouldn’t prevent your household from enjoying the benefits of a connected world. McAfee’s identity theft protection services can help you enjoy everyday conveniences while keeping you safe. Packages can be tailored to your needs, including 24/7 monitoring, ID theft coverage, VPN services, and more. It’s guided online protection made easy.
The post 9 Ways to Determine If Your Identity Has Been Stolen appeared first on McAfee Blog.

Did you just get word that your personal information may have been caught up in a data breach? If so, you can take steps to protect yourself from harm should your info get into the hands of a scammer or thief.
How does that information get collected in the first place? We share personal information with companies for multiple reasons simply by going about our day—to pay for takeout at our favorite restaurant, to check into a hotel, or to collect rewards at the local coffee shop. Of course, we use our credit and debit cards too, sometimes as part of an online account that tracks our purchase history.
In other words, we leave trails of data practically wherever we go these days, and that data is of high value to hackers. Thus, all those breaches we read about.
Whether it’s a major breach that exposes millions of records or one of many other smaller-scale breaches like the thousands that have struck healthcare providers, each one serves as a reminder that data breaches happen regularly and that we could find ourselves affected. Depending on the breach and the kind of information you’ve shared with the business or organization in question, information stolen in a breach could include:
What do crooks do with that data? Several things. Apart from using it themselves, they may sell that data to other criminals. Either way, this can lead to illicit use of credit and debit cards, draining of bank accounts, claiming tax refunds or medical expenses in the names of the victims, or, in extreme cases, assuming the identity of others altogether.
In all, data is a kind of currency in of itself because it has the potential to unlock several aspects of victim’s life, each with its own monetary value. It’s no wonder that big breaches like these have made the news over the years, with some of the notables including:
As mentioned, these are big breaches with big companies that we likely more than recognize. Yet smaller and mid-sized businesses are targets as well, with some 43% of data breaches involving companies of that size. Likewise, restaurants and retailers have seen their Point-of-Sale (POS) terminals compromised, right on down to neighborhood restaurants.
When a company experiences a data breach, customers need to realize that this could impact their online safety. If your favorite coffee shop’s customer database gets leaked, there’s a chance that your personal or financial information was exposed. However, this doesn’t mean that your online safety is doomed. If you think you were affected by a breach, you can take several steps to protect yourself from the potential side effects.
One of the most effective ways to determine whether someone is fraudulently using one or more of your accounts is to check your statements. If you see any charges that you did not make, report them to your bank or credit card company immediately. They have processes in place to handle fraud. While you’re with them, see if they offer alerts for strange purchases, transactions, or withdrawals.
Our credit monitoring service can help you keep an eye on this. It monitors changes to your credit score, report, and accounts with timely notifications and guidance so you can take action to tackle identity theft.
Breached and stolen information often ends up in dark web marketplaces where hackers, scammers, and thieves purchase it to commit yet more crime. Once it was difficult to know if your information was caught up in such marketplaces, yet now an identity monitoring service can do the detective work for you.
Our service monitors the dark web for your personal info, including email, government IDs, credit card and bank account info, and more. This can help keep your personal info safe with early alerts that show you if your data is found on the dark web, an average of 10 months ahead of similar services. From there, you’ll get guidance that you can act on, which can help protect your info and accounts from theft.
If you suspect that your data might have been compromised, place a fraud alert on your credit. This not only ensures that any new or recent requests undergo scrutiny, but also allows you to have extra copies of your credit report so you can check for suspicious activity. You can place one fraud alert with any of the three major credit reporting agencies (Equifax, Experian, TransUnion) and they will notify the other two. A fraud alert typically lasts for a year, although there are options for extending it as well.
Freezing your credit will make it highly difficult for criminals to take out loans or open new accounts in your name, as a freeze halts all requests to pull your credit—even legitimate ones. In this way, it’s a far stronger measure than placing a fraud alert. Note that if you plan to take out a loan, open a new credit card, or other activity that will prompt a credit report, you’ll need to take extra steps to see that through while the freeze is in place. (The organization you’re working with can assist with the specifics.) Unlike the fraud alert, you’ll need to contact each major credit reporting agency to put one in place. Also, a freeze lasts as long as you have it in place. You’ll have to remove it yourself, again with each agency.
You can centrally manage this process with our security freeze service, which stops companies from looking at your credit profile, and thus halts the application process for loans, credit cards, utilities, new bank accounts, and more. A security freeze won’t affect your credit score.
Ensure that your passwords are strong and unique. Many people utilize the same password or variations of it across all their accounts. Therefore, be sure to diversify your passcodes to ensure hackers cannot obtain access to all your accounts at once, should one password be compromised. You can also employ a password manager to keep track of your credentials, such as the one you’ll find in comprehensive online protection software.
If the unfortunate happens to you, an identity theft coverage & restoration service can help you get back on your feet. Ours offers $1 million in coverage for lawyer fees, travel expenses, and stolen funds reimbursement. It further provides support from a licensed recovery expert who can take the needed steps to repair your identity and credit. In all, it helps you recover the costs of identity theft along with the time and money it takes to recover from it.
You can take this step any time, even if you haven’t been caught up in a data breach. The fact is that data broker companies collect and sell thousands of pieces of information on millions and millions of people worldwide, part of a global economy estimated at $200 billion U.S. dollars a year. And they’ll sell it to anyone—from advertisers for their campaigns, to scammers who will use it for spammy emails, texts, and calls, and to thieves who use that information for identity theft.
Yet you can clean it up. Our personal data cleanup service can scan some of the riskiest data broker sites and show you which ones are selling your personal info. It also provides guidance on how you can remove your data from those sites and, with select products, even manage the removal for you.
Comprehensive online protection software will offer you the tools and services listed above, along with further features that can protect you online. That includes a VPN to keep your time online more private from online data collection while protecting it from thieves who’re out to steal credit card and account information. It also includes web browsing protection that can warn you of sketchy websites and malicious downloads that look to steal your information. In all, it’s thorough protection for your devices, privacy, and identity. And in a time of data breaches, that kind of protection has become essential.
The post How to Protect Yourself From Identity Theft After a Data Breach appeared first on McAfee Blog.

We’re online more than ever, in large part because it allows us to take advantage of online conveniences like bill pay and booking appointments. But these many benefits might also leave us exposed to risks, like identity theft.
Identity theft is characterized by one person using another’s personal or financial data for their benefit. Cybercriminals may take information like a person’s name, birthday, Social Security number, driver’s license number, home address, and bank account information and use it for their benefit. A name and matching financial information, for instance, can be used to apply for credit cards or open new accounts.
The good news is that you can safeguard yourself and your family with some best practices — allowing you to enjoy your best life online and worry less about cybercriminals. Share these 10 tips with your family to help keep your entire household safe.
A good habit to get into is to password-protect your computer, tablet, and mobile devices through unique, strong passwords. These devices are home to some of your most sensitive information, including everything from emails to apps that connect to your bank accounts. So, if these devices fall into the wrong hands, a password makes it harder to access your personal data.
Take some time to come up with your passwords, though. It’s important to create strong passwords that hackers can’t guess. A strong password will include a mix of symbols, numbers, and letters. Steer clear of simple passwords like “123456” (it might seem obvious, but this is one of the most common passwords people use). Also, avoid including information that other people can guess, like your birthdate, home address, or name.
Don’t forget to use different passwords for different accounts. If you use the same password across multiple accounts, and a fraudster gains access to one account, they may access the others. Fortunately, McAfee’s identity protection services include a password manager, which can help secure your account credentials across multiple devices. This tool encrypts passwords, storing them safely and making it easy to keep track of them.
Identity thieves are skilled at leveraging new technologies. Phishing is one great example of this. Phishing involves criminals masquerading as trustworthy entities, such as government agencies or banks, and using this trusted position to get sensitive information. Phishing scams started with traditional mail. They’re now also done via phone, text, and email.
As a general rule of thumb, never give out any personal information when contacted by a business, bank, or another entity. Also, make sure your email spam filters detect phishing attempts. Never open emails from people you don’t know, and don’t download email attachments without knowing what they are. Some phishing emails include malware, which can infiltrate your device and access personal data. A McAfee Total Protection plan is an all-in-one protection solution that can help you detect and avoid malware.
Fraudulent websites may also use phishing techniques. A website may look similar to the legitimate website of a mortgage lender, bank, or credit card company but might be a fraudulent platform seeking to get information from consumers. Always verify that any website you visit is the legitimate website of the institution, and consider McAfee antivirus software, which offers a safe browsing solution.
When financial identity theft occurs, this can also impact financial institutions like banks and lenders. So, they’re eager to prevent fraud, as well. One way they do this is through fraud alerts. You can set up your online banking to issue fraud alerts — for example, via an email, text message, or phone call — if your bank suspects suspicious activity on your account.
In some cases, a bank will also freeze your account until you verify whether the activity is legitimate. This is a common tactic used to protect against credit card fraud. Geo-control is one example: If you live in the U.S., but a German IP address uses your credit card, your credit card provider will likely issue an alert. You can also set up alerts for certain transaction amounts or types.
Your credit report is one of the most powerful tools you have at your disposal for catching identity thieves and stopping them in their tracks. You’re entitled to a free credit report every 12 months via AnnualCreditReport.com, an initiative of the Federal Trade Commission (FTC). You can get a free copy of your report from each major credit bureau: Experian, Equifax, and TransUnion.
Review your report thoroughly, checking for inaccuracies. When credit monitoring, check your:
If you find any discrepancies, contact the appropriate credit reporting company. You should also contact the relevant financial institution and visit IdentityTheft.gov. You can report the suspected identity theft and find resources to help you recover.
Social media is great for connecting with others online, but it does open the door to some vulnerabilities. Be careful about what you post, and steer clear of sharing personal details like your home address, children’s names, pet’s names, or birthdays, which some people use as passwords. If a social media platform offers two-factor authentication, opt in.
Images are another touchy subject. Never post photos that include private data, like a picture of your passport or vaccine card. Consider what’s in the background of any photos — from your home (with a house number) to mail with your address. Finally, you may want to set your visibility to private on all social media accounts, limiting who can view them. And even if your account is private, you should still follow the above tips.
Some identity thieves get people’s personal information by dumpster diving. One solution? Invest in a paper shredder. You’ll be able to shred documents into tiny bits that are hard to piece together, making it that much harder for someone else to piece together any personal information they contain.
Here are some documents worth shredding:
If you’re not sure whether something needs to be shredded, go ahead and destroy it. It only takes seconds, and you’re better off safe than sorry.
Whether you use a computer, tablet, or mobile device for many of your online activities, like paying bills, these devices contain a lot of personal data. So, it’s good to protect them from hackers. Install antivirus software like McAfee’s to protect against viruses and spyware. It would be best if you also had a firewall, which is a network security system that controls the incoming and outgoing network traffic based on set security parameters.
To take your device security a step further, you may also want to invest in a virtual private network (VPN). This helps hide your online activity. It can safeguard against hackers on public networks but is also worth using at home. It hides details like browsing activity, personal data, and IP address from potential snoops. McAfee also offers VPN services.
While your computer, tablet, or mobile device may hold a great deal of personal data, you likely also have hard copies of sensitive documents worth protecting. Documents like your birth certificate, Social Security card, and passport contain valuable information that identity thieves can use for personal gain, so you want to make sure they’re kept in a safe space.
Don’t simply shove these documents into your desk drawer. It’s best to keep them in a locked, fireproof home safe with a secure code. To keep things organized, put each document in a protective plastic sleeve and put the sleeves in a binder. This can be useful if you have a large family and need to keep track of everyone’s data.
Sophisticated hackers don’t just target individuals. They may also try to infiltrate businesses, government agencies, higher education institutions, health care facilities, and any other organization that gathers sensitive consumer information. If an entity is subject to a data breach, they’re legally required to notify any consumers who may have been impacted.
However, it’s still good to inform yourself about potential breaches that may affect you. Larger-scale data security risks are usually reported in the media. We also post about data breaches on the McAfee blog. If an entity you do business with has been affected, change your passwords and the passwords of any related accounts immediately.
Knowing possible signs of identity theft can help you catch it early so that you can continue to enjoy your time online. Educate yourself and your family about these warning signs, ensuring everybody stays safe. Here are some possible indications identity thieves have targeted you:
The internet keeps all of us connected, but that’s why identity theft protection is important. With people increasingly connected, doing more, and sharing more online, cybercriminals can pinpoint weaknesses and take advantage. Hackers are ready to leverage your information for personal gain, and identity theft is no exception.
McAfee is here to help. McAfee’s identity protection services provide 24/7 monitoring of your email addresses and bank accounts, providing up to $1 million worth of ID theft coverage. You deserve to enjoy the comfort offered by the internet without stressing about identity theft. Implement the best practices above in your household so that you and your loved ones can stay connected with confidence.
The post 10 Ways to Protect Your Identity appeared first on McAfee Blog.

The internet provides plenty of fun and exciting opportunities for you and your family, from sharing on social media to online shopping. To help you enjoy every minute of it, though, it’s good to be aware of what less savory characters are up to.
And they sure have been busy. In fact, the U.S. Federal Trade Commission (FTC) received 2.1 million fraud reports in 2020. What is identity theft? Well, it’s the fraudulent use of another individual’s name and details for personal gain.
Those affected by identity fraud may see a dip in their finances and credit scores. They may also deal with anxiety around financial security going forward. However, while it’s important to be aware of the threat of identity theft, this shouldn’t be cause for alarm. There are plenty of tools and techniques that can help protect you and your family so you can continue to enjoy everything modern technology has to offer.
The first step in protecting yourself? Educate yourself. Understanding the different types of identity theft can help you safeguard yourself and your loved ones so that you can continue all your favorite online activities. Here we’ll define and explore the different types of identity theft to watch out for.
We’ve all probably heard of identity theft, but what is it? Identity theft is when someone uses another person’s financial or personal data, usually for monetary gain. This means a fraudster may take sensitive information like names, birthdates, Social Security numbers, driver’s license details, addresses, and bank account numbers or credit card numbers. They might then use this information to make purchases, open credit cards, and even use health insurance to get medical care.
A little knowledge can go a long way in stopping cybercriminals in their tracks — especially since they’re becoming more sophisticated and coming up with new schemes every day.
Here are five common types of identity theft to help you stay one step ahead of hackers.
Financial identity theft is when one person uses another’s personal data for financial benefit. This is the most common form of identity theft (including the credit card example described above). Financial identity theft can take multiple forms, including:
The good news is that it’s easy to protect yourself against financial identity theft by checking your bank accounts, credit card statements, and bills. If you see an unexplained charge, contact your credit card company or bank immediately to report it. Also, check your credit report for changes in your score. An unexplained decrease in your score could mean fraudulent activity. You can do this through AnnualCreditReport.com, where you can get a free credit report every 12 months from each of the three major credit bureaus.
Another idea is to place a one-year fraud alert on your credit reports to keep people from opening new accounts in your name. This encourages creditors and lenders to take extra precautions to verify your identity before granting any loans or credit increases. You can also place a security freeze on your credit report, which blocks others from accessing it to extend credit.
This might not seem like a real form of identity theft, but it happens. Medical identity theft is when a criminal poses as another person to obtain health care services. In fact, fraudsters may use your name and insurance information to:
This can result in you having bills for prescriptions, services, or devices you didn’t need, ask for, or even receive. Your health care and insurance records may even have these things added to them. An inaccurate medical record can make it harder for you to get the care you need in the future and even impact insurance coverage.
Fortunately, you can help minimize the risk of medical identity theft by regularly reviewing your medical claims. Contact your insurer if you see unfamiliar procedures, prescriptions, or services. You’ll also want to let your health care provider know so that they can ensure your medical files are correct. Finally, consider filing a complaint with the U.S. Department of Health and Human Services (HHS).
Criminal identity theft occurs when a person arrested by law enforcement uses someone else’s name instead of providing theirs. They might be able to pass this off by creating a fake ID or using a stolen ID, like your driver’s license, to show to the police. This type of fraud can be difficult to detect until the consequences are evident, like:
You can help protect yourself against criminal identity theft by safeguarding your ID. If your license or state-issued ID is lost or stolen, report it to the local Department of Motor Vehicles (DMV) and law enforcement. Also, limit the information you share online (and encourage family members to do the same). For example, if your teen got their first driver’s license and wants to share a pic of it on social media, explain why this isn’t a good idea.
As one of the fastest-growing types of financial crime in the U.S., synthetic identity theft involves creating fake identities using real people’s information. Fraudsters may use data like birthdates, addresses, and Social Security numbers from real people, blending them to create a fake profile. They can then use this persona to apply for loans or credit cards or commit other financial crimes. Kids and older adults tend to be vulnerable to this type of fraud since they rarely use their SSNs.
The most important thing about synthetic identity theft is knowing the signs and acting fast. Keep an eye out for any mail with your address on it but addressed to a different name and phone calls or mail about new credit accounts. You can further protect yourself by regularly checking your credit reports for unexplained changes and placing a security freeze on them.
There are also identity monitoring services available, which scan the internet, including the dark web, for breached Social Security numbers. If you suspect you or a loved one is the victim of synthetic identity theft, contact the relevant financial institutions to alert them.
We all want to protect our children from bad actors, especially when it comes to identity theft. Child identity theft involves using a minor’s information to commit financial fraud, like opening a new account or line of credit under the child’s name. The thief may even use the child’s identity to get a driver’s license, apply for government benefits, or buy a house. This is often easier than targeting an adult because most kids don’t have credit reports or financial accounts, making them a clean slate.
Unfortunately, child identity theft is often perpetrated within the family by a relative who has access to the child’s data like their birthdate and address. And many children don’t realize they’ve been targeted until they’re older — for example, when they try to take out a student loan. By this point, the issue may have been escalating for years. So, it’s important as a parent to be aware of child identity theft.
The best way to do this is to check whether your child has a credit report with any of the three big credit bureaus (TransUnion, Equifax, and Experian). If so, review the report and report any fraudulent activity. You can also place a freeze on your child’s credit report to help minimize the risk of future fraud.
No one wants to be left in the dark when it comes to identity theft, so knowing the signs can help you spot it and take action quickly. This can help stop fraud in its tracks, minimizing both immediate damage and long-term repercussions. Some warning signs that may indicate identity theft include:
You can also increase your odds of recognizing identity theft with tools like McAfee’s identity protection services. Our continual monitoring can keep tabs on over 60 types of personal information, which allows us to quickly identify security issues, alerting you to potential breaches so that you can fix them. We’ll also notify you up to 10 months sooner than similar services. By combining the best practices described above with a comprehensive identity protection service, you can worry less about identity theft and spend more time enjoying the internet.
The internet makes daily life easier in many ways. You can now learn, work, play, and shop online. You shouldn’t have to forego these conveniences because of the threat of identity theft.
McAfee’s identity theft protection services can help keep you and your loved ones safe. McAfee uses extensive monitoring and an early detection system to notify you of potential risks or breaches. You’ll also have access to 24/7 online security experts and up to $1 million of identity theft coverage. Get the peace of mind you need to continue using the internet with confidence.
The post 5 Common Types of Identity Theft appeared first on McAfee Blog.

Protecting your devices with antivirus is a great start, yet it’s only one part of staying safer online. With the way scammers and thieves target people today, you need to protect yourself too—specifically your identity and privacy.
Threats have evolved over the years. While hackers still wage malware attacks on computers, tablets, and smartphones, the devices aren’t the ultimate target. You are. The personal and private information created and kept on your devices have tremendous value because scammers and thieves can use it to steal your identity, open credit cards in your name, and commit all kinds of identity theft and fraud.
Yet just as using antivirus protection can keep you safer online, using privacy and identity protection will keep you far safer still. Let’s look at how all three can work in concert.
Privacy protection focuses on keeping your information from getting into the hands of advertisers, cybercriminals, and data brokers who want to use it for their benefit. To boost your online privacy, consider a few thoughtful additions to your daily browsing, email, and social media routine.
First, think carefully about your social media habits. Do you post everything about your day and childhood, pin your location, and share photos of documents that include your full name, birthday, or address? You may want to consider cutting back on what you broadcast on the internet, especially if your account is public for anyone to view.
Unfortunately, while your friends and family may love your status updates, cybercriminals love them more. After only minutes of snooping, cybercriminals can glean enough personal details about you to impersonate you or target a social engineering attempt at you. To keep your private information more private, limit what you share on social media, pare down your follower and friend lists to only the closest people, and if your social media account platform supports it set your account to private.
One more way to protect your privacy is to use a virtual private network (VPN). A VPN allows you to remain far more anonymous online by shielding your location and device information, along with the data passing along your connection—which includes things like your passwords, account information, and other sensitive info.
A VPN offers further protection when you’re logged on to a public network, like those in coffee shops, libraries, and transportation hubs. Cybercriminals often lurk on non-password-protected Wi-Fi networks and eavesdrop on people paying bills or online shopping to steal their credentials.
However, criminals aren’t the only ones who intrude on your privacy. Online data brokers collect thousands of data points on millions of people, then post bits of that information for anyone to see and offer far more detailed information for a price.
Who buys this information? More legitimate purposes include people conducting background checks, journalists, law enforcement, and, largely, advertisers. With such in-depth information, advertisers can target highly specific audiences with their ads, all based on personal information that can include shopping habits from customer loyalty cards, health data from fitness apps, and information scraped from public social media posts—just to name a few of the umpteen sources they draw from.
Yet data brokers won’t discriminate. They’ll sell to scammers and thieves as well, who can then use that personal information to help them commit identity fraud and theft.
However, you can do something about this. Personal data cleanup can scan some of the riskiest data broker sites and show you which ones are selling your personal info. It can also provide guidance on how you can remove your data from those sites and can even manage the removal for you. And because data brokers continually update their data, personal data cleanup will continue to monitor those sites and help you get your information removed should it crop up again.
In all, if you feel that your privacy shouldn’t be up for grabs, a personal data cleanup service can
Another form of protection focuses on keeping you safer from identity theft and fraud. Here, thieves will steal personal and account information to rack up charges on existing credit and debit cards, open entirely new accounts and lines of credit, or impersonating the victim themselves for employment, health insurance coverage, or to commit other crimes in someone else’s name.
A few forms of identity crime include:
This list provides just a few examples, yet in all its forms, identity crime can affect your finances, credit score, and ability to secure loans, a mortgage, or future credit cards.
One way to keep your identity secure is to guard your PII carefully. Never give out your Social Security Number unless it’s necessary—such for employment, opening bank and credit accounts, applying for public assistance, filing tax returns, or obtaining a driver’s license. While other businesses may ask you for your Social Security Number for identification purposes, you are not legally bound to provide it. You can ask to provide an alternate form. Also, never share it over email or text where it can be potentially intercepted.
Beyond your Social Security Number, you can take steps to protect the many other forms of personal information you have. An identity monitoring service can keep tabs on everything from email addresses to IDs and phone numbers for signs of breaches so you can take action to secure your accounts before they’re used for identity theft. Likewise, credit monitoring can watch for unusual credit activity that could be an indicator of identity theft as well.
Should the unfortunate occur, identity theft & recovery coverage like ours can help you get back on track in several ways. First, it provides $1 million in identity theft coverage that covers travel expenses, legal fees, and stolen funds reimbursement. Additionally, it provides the assistance of a licensed identity theft recovery pro who can help you repair your identity and credit.
The third form of protection involves our devices, like computers, tablets, and phones—protecting them from both physical and digital threats.
The first step you can take is to use a password, PIN, facial recognition, or other form of lock to keep your devices safer in the event of loss or theft. With this protection, your device is effectively an open book, providing a thief with access to all manner of personal information, accounts, and apps.
Taking this protection a step further is learning to remotely locate your devices and then lock or wipe them. Many laptops and mobile devices offer location tracking services to help find a lost device—and yet others allow the owner to remotely lock or even wipe the contents of that device if they fear it’s lost for good or fallen into the wrong hands.
It’s all rather straightforward, and device manufacturers have put up helpful web pages that can walk you through the process:
Another good step you can take is to back up your files, whether with an online cloud service, a physical external drive, or both. By storing your files in the cloud, you can recover them quickly if your device is stolen and you have to remotely wipe its contents. Storing them on an external drive also lets you recover your files if your device is stolen, however, you’ll want to keep it in a secure location so that it can’t be stolen as well. Options include a fireproof safe where you keep other valuables or even a safe deposit box. The drawback is that you will have to back up files manually and regularly whereas cloud backup is practically automatic when you’re connected to the internet.
Another component of device security is defending against malicious software. Viruses and malware can make their way onto your devices through several avenues, including sketchy websites, dishonest downloads, phishing schemes, and clicking on ads. The challenge is that several of these avenues can look rather legitimate at first glance. Sophisticated hackers, scammers, and thieves have learned how to make their bogus websites and search results look like the real thing. One way you can prevent making a bad click or downloading an attachment loaded with malware is to use web advisor software that can protect you while you browse.
And finally, yes, antivirus is a must now just as it’s ever been. When kept up to date with the latest updates, it can prevent malware from getting onto your devices—plus scan, detect, and delete viruses and malware from your devices should they make their way onto them.
The threats out there are many, and they go beyond threats to your devices. Hackers, scammers, and thieves are quite interested in you. Your accounts, your personal information, and anything they can grab to commit theft or fraud. Protecting yourself today calls for not only protecting your devices but your privacy and identity too.
Comprehensive online protection software like ours covers all three—privacy, identity, and devices. It includes the protections mentioned above, plus dozens of features more such as ransomware coverage, credit freezes, security locks, and an online protection score that shows you just how safe you are, along with suggestions that can make you safer still.
In all, it gives you far more control over your privacy and personal information, control that should rest in your hands, and not in the hands of data brokers, hackers, scammers, and thieves.
The post Privacy, Identity, and Device Protection: Why You Need to Invest in All Three appeared first on McAfee Blog.

Before you take the fun-looking quiz that popped up in your social media feed, think twice. The person holding the answers may be a hacker.
Where people go, hackers are sure to follow. So it’s no surprise hackers have set up shop on social media. This has been the case for years, yet now social media-based crime is on the rise. In 2019, total reported losses to this type of fraud reached $134 million. But reported losses hit $117 million in just the first six months of 2020, according to the U.S. Federal Trade Commission (FTC).
Among these losses are cases of identity theft, where criminals use social media to gather personal information and build profiles of potential victims they can target. Just as we discussed in our recent blog, “Can thieves steal identities with only a name and address?” these bits of information are important pieces in the larger jigsaw puzzle that is your overall identity.
Let’s uncover these scams these crooks use so that you can steer clear and stay safe.
“What’s your spooky Halloween name?” or “What’s your professional wrestler name?” You’ve probably seen a few of those and similar quizzes in your feed where you use the street you grew up on, your birthdate, your favorite song, and maybe the name of a beloved first pet to cook up a silly name or some other result. Of course, these are pieces of personal information, sometimes the answer to commonly used security questions by banks and other financial institutions. (Like, what was the model of your first car?) With this info in hand, a hacker could attempt to gain access to your accounts.
Similarly, scammers will also post surveys with the offer of a gift card to a popular retailer. All you have to do is fork over your personal info. Of course, there’s no gift card coming. Meanwhile, that scammer now has some choice pieces of personal info that they can potentially use against you.
How to avoid them: Simply put, don’t take those quizzes and surveys online.
The list here is long. These include posts and direct messages about phony relief funds, grants, and giveaways—along with bogus business opportunities that run the gamut from thinly-veiled pyramid schemes and gifting circles to mystery shopper jobs. What they all have in common is that they’re run by scammers who want your information, money or both. If this sounds familiar, like those old emails about transferring funds for a prince in some faraway nation, it is. Many of these scams simply made the jump from email to social media platforms.
How to avoid them: Research any offer, business opportunity, or organization that reaches out to you. A good trick is to do a search of the organization’s name plus the term “scam” or “review” or “complaint” to see if anything sketchy comes up.
If there’s one government official that scammers like use to put a scare in you, it’s the tax collector. These scammers will use social media messaging (and other mediums like emails, texts, and phone calls) to pose as an official that’s either demanding back taxes or offering a refund or credit—all of which are bogus and all of which involve you handing over your personal info, money, or both.
How to avoid them: Delete the message. In the U.S., the IRS and other government agencies will never reach out to you in this way or ask you for your personal information. Likewise, they won’t demand payment via wire transfer, gift cards, or cryptocurrency like bitcoin. Only scammers will.
These are far more targeted than the scams listed above, because they’re targeted and often rely upon specific information about you and your family. Thanks to social media, scammers can gain access to that info and use it against you. One example is the “grandkid scam” where a hacker impersonates a grandchild and asks a grandparent for money. Similarly, there are family emergency scams where a bad actor sends a message that a family member was in an accident or arrested and needs money quickly. In all, they rely on a phony story that often involves someone close to you who’s in need or in trouble.
How to avoid them: Take a deep breath and confirm the situation. Reach out to the person in question or another friend or family member to see if there really is a concern. Don’t jump to pay right away.
This is one of the most targeted attacks of all—the con artist who strikes up an online relationship to bilk a victim out of money. Found everywhere from social media sites to dating apps to online forums, this scam involves creating a phony profile and a phony story to go with it. From there, the scammer will communicate several times a day, perhaps talking about their exotic job in some exotic location. They’ll build trust along the way and eventually ask the victim to wire money or purchase gift cards.
How to avoid them: Bottom line, if someone you’ve never met in person asks you for money online, it’s a good bet that it’s a scam. Don’t do it.
Now with an idea of the bad actors are up to out there, here’s a quick rundown of things you can do to protect yourself further from the social media scams they’re trying to pull.
Above and beyond what we’ve covered so far, some online protection basics can keep you safer still. Comprehensive online protection software will help you create strong, unique passwords for all your accounts, help you keep from clicking links to malicious sites, and prevent you from downloading malware. Moreover, it can provide you with identity protection services like ours, which keep your personal info private with around-the-clock monitoring of your email addresses and bank accounts with up to $1M of ID theft insurance.
Together, with some good protection and a sharp eye, you can avoid those identity theft scams floating around on social media—and get back to enjoying time spent online with your true family and friends.
The post Quizzes and Other Identity Theft Schemes to Avoid on Social Media appeared first on McAfee Blog.

We all know the frustration. A new piece of tech isn’t working the way it should. Or maybe setting it up is simply turning into a royal pain. Grrr, right? Just make sure that when you go on the hunt for some help, you don’t let a tech support scam get the better of you.
Like so many scams out there, tech support scams play on people’s emotions. Specifically, the frustration you feel when things don’t work right. You want that problem fixed right now. So much so that you may not pay close enough attention to that tech support link you found in a search or came across in an ad. Tech support that looks legitimate but isn’t.
Tech support scams make good money for bad actors. In fact, the larger tech support scam operations organize and run themselves like a business, with call centers, marketing teams, finance groups, and so forth—and can rack up some serious profits to boot.
They make their money in several ways. Sometimes they’ll charge large fees to fix a non-existent problem. Other times, they’ll install information-stealing malware under the guise of software that’s supposed to correct an issue. In some cases, they’ll ask for remote access to your computer to perform a diagnosis but access your computer to steal information instead.
Fortunately, these scams are rather easy to spot. And avoid. If you know what to look for.
Let’s start with a quick overview of tech support scams. They tend to work in two primary ways.
This could be a phone call that comes from someone posing as a rep from “Microsoft” or “Apple.” The scammer on the other end of the line will tell you that there’s something wrong with your computer or device. Something urgently wrong. And then offers a bogus solution to the bogus problem, often at a high cost. Similarly, they may reach you by way of a pop-up ad. Again telling you that your computer or device is in need of urgent repair. These can find you a few different ways:
These are phony services and sites that pose as legitimate tech support but are anything but. They’ll place search ads, post other ads in social media, and so forth, ready for you to look up and get in touch with when you have a problem that you need fixed. Examples include:
While tech support scammers can and do prey on older computer users, they’re not the only ones. An apparent lack of computer savviness certainly makes older users an attractive target, yet it also seems that an apparent overconfidence in one’s savviness makes younger victims susceptible to tech support scams too. Turns out that the growing majority of victims worldwide are between 18 and 35 years old, a group that has known the internet for most, if not all, of their lives. That’s according to research from Microsoft’s Digital Crimes Unit, which found the 1 in 10 of people between the ages of 18 and 35 who encountered a tech support scam fell for it and lost money.
Whatever the age group, the U.S. Federal Trade Commission (FTC) says that the reported losses in the U.S. are into the millions, which of course does not account for the assumedly millions more that do not go reported.
Lastly, a good piece of general advice is to keep your devices and apps up to date. Regular updates often include security fixes and improvements that can help keep scammers and hackers at bay. You can set your devices and apps to download them automatically. And if you need to get an update or download it on your own, get it from the company’s official website. Stay away from third-party sites that may host malware.
This will provide protection if the scammer was able to access your account passwords in some form. While this can be a big task, it’s a vital one. A password manager that’s part of comprehensive online protection can make it much easier.
Delete files or apps that the software says is an issue. Do the same for other devices on your network too. Experienced and determined scammers can infect them as well simply by gaining access to one device on your network.
Contact your bank, credit card company, online payment platform, or wire transfer service immediately to reverse the charges. File a fraud complaint as well. The sooner you act, the better chance you have of recovering some or all your money. (Note that this is a good reason to use credit cards for online purchases, as they afford extra protection that debit cards and other payment services do not.)
In the U.S., you can contact https://www.ftc.gov/complaint, which reports the claim to thousands of law enforcement agencies. While they cannot resolve your individual issue, your report can help with broader investigations and build a case against scammers—which can make the internet safer for others. Their list of FAQs is particularly helpful too, answering important questions like “how do I get my money back?”
Here’s to holiday tech that works. And to quick fixes when things don’t go as planned. In all, if you find yourself staring down a technical issue, go straight to the source for help as we’ve outlined above. As you can see, scammers have burrowed themselves alongside otherwise legitimate ads, search results, and forums online, ready to take advantage of you when you need to get things working right.
Likewise, keep an eye and ear open for those scammers who’ll reach out to you, particularly this time of year when so many people are getting so many new devices. Realizing that legitimate tech support won’t call you out of the blue is a great place to start. In all, go with the pros you know—the ones you can reach at the companies you trust.
The post New tech for the holidays? Watch out for these tech support scams. appeared first on McAfee Blog.

Have you noticed that when parents gather, it doesn’t take long before the topic of kids and social media comes up. That’s because concern over screen time is a big deal, especially in this post-pandemic season. Parents want to know: How much is too much screen time? When should we step in? How do we reverse poor habits, and what will the lasting digital fallout of the lockdown be?
These conversations weigh heavy on parents for a good reason. According to a report from Common Sense Media, teens spend an average of seven hours and 22 minutes on their phones a day. Tweens (ages 8 to 12) spend four hours and 44 minutes daily. This is time outside of schoolwork.
Since the pandemic, another study claims that screen time for teens doubled to 7.7 hours a day—plus 5 to 7 daily hours of online learning, according to a study published in JAMA Pediatrics. In addition, according to the Journal of Affective Disorders Reports, children overall have been spending nearly triple the recommended amount of time on their screens.
The good news is that social media also became a powerful tool for kids during the pandemic. Social channels helped kids connect with peers and combat loneliness and other mental health challenges. Still, the poor habit of device dependence may have come with those benefits.
While the debate continues over social media’s impact on kids and the research methodology continues to evolve, we can hold on to one clear truth: Any activity in excess can cause kids harm. When it comes to social media, too much screen time may contribute to sleep deprivation, a lack of healthy, and poor academics. In addition, studies show that mental health can be impacted by exposure to hate speech, sexual content, cyberbullying, and comparing oneself to others both physically and financially.
As parents, we know when our family’s wellbeing is in jeopardy. We see it even if we fail to acknowledge it right away. Our kids might become compelled to check their phones. In fact, they panic when they can’t check their likes and comments every few minutes. We notice the red eyes and moodiness at the breakfast table caused by a late-night Tic Tock marathon. We sense a surge of anxiety in our kids when technology goes from entertaining to distressing.
Thankfully, it’s never too late to help your kids better understand the impact of their actions and revise digital habits.
In the bestselling book Atomic Habits, author James Clear says, “The task of breaking a bad habit is like uprooting a powerful oak within us.” He adds, “The task of building a good habit is like cultivating a delicate flower one day at a time.” Lasting change, says clear, needs to be enjoyable, not a punishment. If the goal is shaving a few hours off your child’s screen time, consider connecting time limits to an enjoyable activity such as making a meal together or creating an art space in your home for creative projects.
The data is in: The bright screens (and blue light emitted from devices( can cause permanent sleep cycle and brain/melatonin issues, which can have a cascading effect on physical and mental health. Turning off (or limiting the use of) electronic devices at least 15-30 minutes before going to bed may help prevent any adverse effects of technology and screen use on sleep. Consider investing in filtering software that comes with the time limits the whole family can all agree on. Do your research to ensure your family’s technology functions to empower, educate, and entertain.
Consider how your child uses their time before suggesting sweeping changes to your child’s screen time. Are they vegetating, or are they consciously engaged? Are they creating and learning? Are they engaging with others or stalking accounts and slipping into “comparison despair?” Are family and school responsibilities suffering? Is there a compulsion to post or thoughtfulness? All kids are different, and all online experiences vary. Encourage your child to take time to consider how they feel and what they think while they are using their technology.
One way to negotiate screen limits is to make sure your kids understand the impact of excess media. Balance includes tapping into the benefits of social media while also taking steps to protect the body’s need for physical activity, real-life relationships, goal-setting, creative activities, mindfulness, and self-reflection.
Helping kids manage and constantly revise their social media habits is a 24/7 endeavor from the minute they wake up to the minute they fall asleep. The biggest piece of that “management” plan and is keeping frequent, open, and honest communication a critical part of designing habits that encourage a healthy relationship with both peers and technology.
The post Does Your Child Have an Unhealthy Relationship with Social Media? appeared first on McAfee Blog.

I think it’s fair to say that come to next Australia Day, there needs to be a special award category for parents of young children who survived home learning during the lockdowns. Let’s be honest – it’s been brutal! So many parents had to juggle their own full-time work, running a household, AND supervising a day’s worth of learning for often, multiple children! Research from Macquarie University showed that many parents spent up to 14 hours a week in their role as home learning managers and 9/10 parents reported the experience as, quite understandably, stressful! As a mum of older teens and young adults – who are usually self-sufficient – I’m in awe!
But the good news is – things are on the improve! Our vaccine rates are amongst the best in the world, so lockdowns have been lifted and, drum roll… kids are back at school! I’ve always been a big fan of trying to find the silver lining of any situation and I think there are many we can take away from our COVID experience, particularly when it comes to digital parenting. I know of so many parents who have completely rethought their approach to managing kids and technology since the pandemic hit because of their home learning experience.
So, in the spirit of sharing and caring, I thought I’d round up some of the best ‘aha’ moments from parents who were forced to become expert home learning managers over multiple lockdowns. And make sure you take notes because there are some great learnings that we can apply to our digital parenting journey.
If you have never been ‘all in’ with your kids’ use of technology for both learning and socializing, then you need to get over this ASAP. Technology is the lifeblood of your kids’ lives. It’s how they connect, nurture friendships, and organize their social lives. I also recommend parents try to see technology through the eyes of their kids NOT just through our more ‘mature’ lens. It’s the best way of truly understanding just what a huge role it plays in their day-to-day lives. And don’t forget that technology is almost always used to set up in-person catchups! So, please don’t demonize it, it will only push your kids away.
I totally appreciate that many parents didn’t choose to be home learning ‘managers’ however many have shared with me how they now feel far more involved in their child’s life because of the experience. Seeing first-hand how your child’s day works, overhearing their conversations with teachers and peers (courtesy of Zoom), and being blown away by your offspring’s tech skills has given many parents incredible insight into their child.
I know of parents who have noticed learning issues and friendship problems all as a result of their home learning manager role! There’s nothing like being able to nip something in the bud before it becomes a big issue! So, stay involved and you’ll reap the rewards!
Confession – I have never been one of those parents who proactively organized park visits, bushwalks, and exercise regimes for my kids. But many of the parents who managed young children through a lockdown and resorted to becoming personal trainers reported that it paid dividends. So, now lockdowns are (hopefully!) history, don’t forget about the benefits of getting your kids to move. It’s hard to be on a screen when you are walking the dog, playing a game of family cricket, or bushwalking. I know it’s time-consuming but it’s so worth it!
As of 2 years ago, the average Aussie household had 17 internet-connected devices in tow so it’s no wonder keeping abreast of all the devices in your household feels like a full-time job! But with kids continuing to use their devices for both study and socializing, it’s essential that you give each device a ‘once over’ to minimize risks and prevent issues arising down the track.
Ensuring all their software is up to date is a great place to start. Also check that the default password has been changed and that there is some top-shelf security software installed to protect the device and, most importantly, its user! And while you are there, why not also ensure that each of their online accounts has its own distinct password? If you think they could manage a password manager, then it might be time to introduce them to one? Check out McAfee’s True Key – I couldn’t manage without it!
I think you’d be hard-pressed to find many parents keen to return to home learning. In fact, I think there may even be a revolt if we had to go back! But, knowing we have picked up some ‘nuggets of gold’ along the way makes it a little feel a little better! So, please embrace technology – it’s a fantastic way of connecting with your kids. But of course, keep your family’s usage in check and minimize the risks by giving each device a once-over.
Happy Digital Parenting!
Alex
The post What We’ve Learnt From Home Learning During Lockdown appeared first on McAfee Blog.

How do you connect online these days? I’ll give you an example from my own life: From my 15-year old son to my 80-year-old mother, not one of us leaves the house without our phone. And today, there isn’t a single thing you can’t do on your phone. It’s the minicomputer that goes where you go.
This trend in the way we connect is reflected in recent data too. In fact, we’ve found that the average consumer spends 6 hours and 55 min online per day, split between mobile (52%) and desktop (48%). Whether you’re a Boomer, Gen X, a Millennial, or Gen Z, the way you connect online is diverse and specific to you.
As for what we’re doing online? It’s just about everything. After all, we spend an average of 7 hours per day on connected devices and the pandemic has forced us to do even more online. The downside to this rapid change in the way we live is that we are opening ourselves up to more risk which leaves consumers feeling highly concerned about their ability to keep their personal info secure or private. We need new protection for this new normal.
What all these changes mean is that you’re able to have the same online experience regardless of where you are, what you’re doing, or what device you’re using. Your favorite streaming service is a great example – you can just as easily find a movie on a tablet as you can on your laptop. In fact, you can pause the movie you’re watching on that tablet and pick up where you left off on your laptop. Your experience with online security should offer the same convenience and familiarity. More importantly, online protection should give you a feeling of confidence however or wherever you choose to connect.
This means knowing your personal info is secure even when accessing an unsecured network, your browsing habits remain private, and you can take necessary actions should your information be compromised. To put it another way, YOU are what we’re focused on protecting and we do that by making sure everything you connect with is also secure.
A phone is the remote control for your life. From the palm of your hand, you’re able to shop, browse, stream, and create – everything you do online you can now do from your phone. So, it’s crucial that your phone be a major focus of our online protection. The new mobile app makes it easier to get robust protection for your identity, privacy, and phone. Let’s look at a few of the capabilities offered by the new mobile app.
Think about all the online accounts you’ve created in the past year. How many of them do you use regularly? Sometimes I think I have more food delivery apps on my phone than I do restaurants to use them on. Regardless of how often you use an account (or if you no longer use it at all!), any personal information (like emails, addresses, credit cards) added to it is available online and vulnerable to breaches. McAfee Security comes with identity protection, a feature that monitors your personal information and then notifies you when there’s a risk of your data being compromised. What this means is that if we detect that your data was stolen, you’ll be alerted an average of 10 months earlier than similar services, so you can act before your data is used illegally or shows up on the dark web.



Let’s say you’re about to use the free internet at your favorite café for a speedier connection. Time to flip on your virtual private network (VPN). Forget about digging through a sea of menus to find your VPN. The new mobile app offers a seamless VPN experience so you can keep your activity hidden on less-than-secure Wi-Fi. Or, better yet, you can set up a Secure VPN to automatically turn on for unsecured Wi-Fi networks. Whatever you choose, Secure VPN keeps your personal data and location private anywhere you go with unlimited data and bank-grade Wi-Fi encryption.



At the end of the day, phones are devices and they’re vulnerable to viruses, malware, and, increasingly, malicious apps. The new McAfee Mobile app offers an antivirus scan for Android phones and system scans to see if your passcode is strong enough and that your OS is up to date on iOS devices.
Most importantly, the app is part of McAfee’s total online protection, so the experience on your phone is the same as on your PC. It’s protection that goes where you go – at home on your PC, or on the go with your mobile.
If you’re an existing McAfee subscriber using McAfee Total Protection or McAfee LiveSafe, you can get the app right now. And, if you’ve already got the app installed, just make sure it’s up-to-date and you’ll be all set with the new look and features.
Interested in trying the app out? You can buy or get a free trial of McAfee Total Protection here and get started today.
The post Reimagining mobile security for the way we live our lives today, tomorrow, and beyond. appeared first on McAfee Blog.

With the holidays on the horizon, spirits are high—and it’s those same high spirits that hackers want to exploit. ‘Tis the season for clever social engineering attacks that play on your emotions, designed to trick you into giving up personal info or access to your accounts.
Social engineering attacks unfold much like a confidence scam. A crook takes advantage of someone’s trust, applies a little human psychology to further fool the victim, and then pulls off a theft. Online, a social engineering attack will likely involve a theft attempt of personal or account information that the crook can then use to make purchases, drain accounts, and so forth.
Not at all in the holiday spirit, right? Let’s take a look at some of their top tricks so that you can spot and avoid them.
As said, spirits can get high this time of year. There’s looking forward to gatherings with family and friends, the fun that comes along with hunting for that perfect gift, and the excitement of the holidays overall. And that’s what hackers count on—people getting caught up in the rush of the holidays, to the point where they may not look at emails, offers, shipping notices, and such with a critical eye. That’s how the scammers get their foot in the door.
Some of their favored tricks can look a little like this:
What are the holidays without that trendy “must-get” gift item, the one that’s seemingly out of stock no matter where you look? Scammers are keen on these items as well and will prop up phony ads and storefronts that pretend to sell those items but really don’t. Instead, they’re just a shady way for them to steal your debit or credit card information—or to lift a few bucks out of your pocket in return for nothing.
One way to keep from getting burned by one of these scams is to follow the old adage, “If it looks too good to be true, it probably is.” In this case, crooks are using feelings of scarcity and urgency to get you to bite. Here’s where you can take a moment before you click to do some research.
Answers to these questions can separate the good businesses from the bogus ones.
Like the above, crooks will create a sense of urgency about a hot holiday item or limited time offer. The twist comes when they request payment via a gift card rather than by credit or debit card or other legitimate online payment methods. This request is highly deliberate because gift cards are much like cash. Once the money on the card is spent, it’s gone, and these cards do not offer the same protections that come with other payment methods.
You can avoid this one easily. If anyone asks you to use a gift card as payment, it’s a scam. Gift cards are for gifts, not payment, says the Federal Trade Commission (FTC). If you come across such a scam, you can report it to the FTC as well.
Donating to a charity in someone else’s name is often a popular gift. Much the same, giving a donation to a worthy cause feels particularly good this time of year. Once again, scammers will take advantage of these good intentions by propping up phony charities designed to do nothing more than dupe you out of your money. Whether that’s a flat-out phony charity or one of the many other scam charities that have been known to pocket 90 cents of every dollar donated, this is the time of year to be on the lookout for both.
The advice here is much the same as the advice for avoiding phony businesses and retailers. Do your homework. The Better Business Bureau maintains a listing of charities that can help you make good donation choices. Also, your state government’s charity officials can help you separate good charities from bad—and even file a report if you suspect a scam is at play.
And once again, if a charity is asking for donations in the form of cash, gift cards, or wire transfer, just say no. That’s a surefire sign of a scam.
Scammers know you have packages in transit this holiday season, loaded with gifts that you’re eagerly tracking. Enter another classic scam—the phony shipping notice. The idea is that you already have so many packages on their way that you won’t think twice about opening an email with a “shipping notice” that comes in the form of an attachment. Of course, that attachment is a fake. And it’s loaded with malware.
Too bad for scammers, though. This is another one you can steer clear of rather easily. Don’t open such attachments. Shipping companies will almost certainly send along notices and invoices in the body of an email, not as an attachment. If you have a question, you can always visit the shipper’s website and look up your tracking info there. Likewise, follow up with the customer service department of the company that you purchased the item from in the first place.
While the holidays are a special time for scammers too, there are several things you can do to up the level of your protection now and year ‘round. A quick list includes:
No doubt, the holidays have a feel all to themselves, one which hackers and crooks want to take advantage of. They’ll craft their tricks accordingly and try to twist the good times that roll around at the end of the year into scams that capitalize on your good intentions. As you can see, it’s not too tough to spot them for what they are if you pause and take a moment to scrutinize those emails, offers, and sales. And that’s the thing with the holidays. We can all feel pinched for time at some point or other during this stretch. Look out for their pressure tactics and seemingly clever ways of using social engineering to rip you off. That way, you can spend the holidays focusing on what’s important—your friends and family.
The post Social Engineering: Tis the Season for Tricky Hackers appeared first on McAfee Blog.

How does that information get collected in the first place? We share personal information with companies for multiple reasons simply by going about our day—to pay for takeout at our favorite restaurant, to check into a hotel, or to collect rewards at the local coffee shop. Of course, we use our credit and debit cards too, sometimes as part of an online account that tracks our purchase history.
In other words, we leave trails of data practically wherever we go these days, and that data is of high value to hackers. Thus, all those breaches we read about.
Whether it’s a major breach that exposes millions of records or one of many other smaller-scale breaches like the thousands that have struck healthcare providers, each one serves as a reminder that data breaches happen regularly and that we could find ourselves affected. Depending on the breach and the kind of information you’ve shared with the business or organization in question, information stolen in a breach could include:
What do crooks do with that data? Several things. Apart from using it themselves, they may sell that data to other criminals. Either way, this can lead to illicit use of credit and debit cards, draining of bank accounts, claiming tax refunds or medical expenses in the names of the victims, or, in extreme cases, assuming the identity of others altogether.
In all, data is a kind of currency in of itself because it has the potential to unlock several aspects of victim’s life, each with its own monetary value. It’s no wonder that big breaches like these have made the news over the years, with some of the notables including:
Facebook – 2019: Two sets of data exposed the records of more than 530 million users, including phone numbers, account names, and Facebook IDs.
Marriott International (Starwood) – 2018: Half a million guests had names, email and physical mailing addresses, phone numbers, passport numbers, Starwood Preferred Guest account information, dates of birth, and other information about their stays exposed.
Equifax – 2017: Some 147 million records that included names, addresses, dates of birth, driver’s license numbers, and Social Security Numbers were exposed, along with a relatively small subset of 200,000 victims having their credit card information exposed as well.
As mentioned, these are big breaches with big companies that we likely more than recognize. Yet smaller and mid-sized businesses are targets as well, with some 43% of data breaches involving companies of that size. Likewise, restaurants and retailers have seen their Point-of-Sale (POS) terminals compromised, right on down to neighborhood restaurants.
When a company experiences a data breach, customers need to realize that this could impact their online safety. If your favorite coffee shop’s customer database gets leaked, there’s a chance that your personal or financial information was exposed. However, this doesn’t mean that your online safety is doomed. If you think you were affected by a breach, there are multiple steps you can take to help protect yourself from the potential side effects.
One of the most effective ways to determine whether someone is fraudulently using one or more of your accounts is to check your statements. If you see any charges that you did not make, report them to your bank or credit card company immediately. They have processes in place to handle fraud. While you’re with them, see if they offer alerts for strange purchases, transactions, or withdrawals.
File a police report and a Federal Trade Commission (FTC) Identity Theft Report. This will help in case someone uses your Social Security number to commit fraud, since it will provide a legal record of the theft. The FTC can also assist by guiding you through the identity theft recovery process as well. Their site offers a step-by-step recovery plan that you can follow and track your progress as you go.
If you suspect that your data might have been compromised, place a fraud alert on your credit. This not only ensures that any new or recent requests undergo scrutiny, but also allows you to have extra copies of your credit report so you can check for suspicious activity. You can place one fraud alert with any of the three major credit reporting agencies (Equifax, Experian, TransUnion) and they will notify the other two. A fraud alert typically lasts for a year, although there are options for extending it as well.
Freezing your credit will make it highly difficult for criminals to take out loans or open new accounts in your name, as a freeze halts all requests to pull your credit—even legitimate ones. In this way, it’s a far stronger measure than placing a fraud alert. Note that if you plan to take out a loan, open a new credit card, or other activity that will prompt a credit report, you’ll need to take extra steps to see that through while the freeze is in place. (The organization you’re working with can assist with the specifics.) Unlike the fraud alert, you’ll need to contact each major credit reporting agency to put one in place. Also, a freeze lasts as long as you have it in place. You’ll have to remove it yourself, again with each agency.
Ensure that your passwords are strong and unique. Many people utilize the same password or variations of it across all their accounts. Therefore, be sure to diversify your passcodes to ensure hackers cannot obtain access to all your accounts at once, should one password be compromised. You can also employ a password manager to keep track of your credentials, such as one you’ll find in comprehensive online protection software.
A solution such as this will help you to monitor your accounts and alert you of any suspicious activity. Specifically, our own Identity Protection Service will monitor several types of personally identifiable information, alert you of potentially stolen personal info, and offer guided help to neutralize the threat. Also, it can help you steer clear of some types of theft with preventative guidance that can help keep theft from happening in the first place. With this set up on your computers and smartphone you can stay in the know and address issues immediately.
To use your credit card safely online to make purchases, add both a VPN and password manager into your toolbox of security solutions. A VPN keeps your shopping experience private, while a password manager helps you keep track of and protect all your online accounts. Again, you’ll find a VPN as part of comprehensive online protection software.
The post Affected by a Data Breach? Here Are Security Steps You Should Take appeared first on McAfee Blogs.

You may have spotted the news last week that U.S. federal prosecutors brought charges against the former chief security officer of Uber. At issue was a breach that occurred in 2016, where prosecutors allege that he covered up a $100,000 payoff to the hackers responsible for the attack. The specific charges are obstructing justice and concealing a felony for the alleged cover-up.
While the breach itself is relatively old news and the company has since paid a $148 million settlement along with an agreement to regular audits of its privacy and security systems, this is a reminder that breaches happen. What’s more, it may be some time before you become aware of them, even in instances when companies move quickly, transparently, and in your best interest.
According to research we recently published, nearly three-quarters of all breaches have required public disclosure or have affected financial results, up five points from 2015. Additionally, industry studies show that it can take roughly nine month on average to identify and contain a breach. Yes, that’s more than nine months, and a lot can happen to your credit in that timeframe. Thus the onus is on us to be vigilant about our own credit.
Here’s a quick list of things you can do right now to keep on top of your credit—and that you can do on an ongoing basis as well, because that’s what it takes to keep tabs on your personal info today.
Closely monitor your online accounts: Whether it’s your credit card statements, banking statements, or your individual accounts for services like Uber, review them closely. If you see any suspicious activity, notify the institution or service and put a freeze on your account(s) as needed. Even a small charge can indicate a bigger problem, as that means your information is out there in the wild and could be used for bigger purchases down the pike. In the event you feel your Uber account has been compromised, you can contact them via their “I think my Uber account has been hacked” page.
Update your settings: That includes your privacy settings in addition to changing your password. As far as passwords go, strong and layered passwords are best, and never reuse your credentials across different platforms. Plus, update your passwords on a regular basis. That’ll further protect your data. Using a password manager will help you keep on top of it all, while also storing your passwords securely.
Enable two-factor authentication: While a strong and unique password is a good first line of defense, enabling app-based two-factor authentication across your accounts will help your cause by providing an added layer of security.
Check your credit: Depending on where you live, there are different credit reporting agencies that keep a centralized report of all your credit activities. For example, the major agencies in the U.S. are primarily Equifax, Experian, and TransUnion. Likewise in the U.S., the Fair Credit Reporting Act (FCRA) requires these agencies to provide you with a free credit check at least once every 12 months. It’s a relatively quick process, and you might be surprised what you find—anywhere to incorrect address information to bills falsely associated with your name. Get your free credit report here from the U.S. Federal Trade Commission (FTC). Other nations provide similar services, such as the free credit reports for UK customers.
Freeze your credit: Freezing your credit will make it impossible for criminals to take out loans or open up new accounts in your name. To do this effectively, you will need to freeze your credit at each of the three major credit-reporting agencies (Equifax, TransUnion, and Experian).
Consider using identity theft protection: A solution like McAfee Identify Theft Protection will help you to monitor your accounts and alert you of any suspicious activity in addition to the activities I’ve listed above. Additionally, you can use a comprehensive security solution such as McAfee Total Protection to help protect your devices and data from known vulnerabilities and emerging threats.
For all the technology we have at our fingertips, our best defense is our eyes. Keeping a lookout for fishy activity and following up with family members when unfamiliar charges show up on your accounts will help you keep your good name in good standing.
The thing is, we never know when the next data breach might hit and how long it may be until that information is discovered and finally disclosed to you. Staying on top of credit has always been important, but given all our apps, accounts, and overall exposure these days, it’s a must.
To stay updated on all things McAfee and for more resources on staying secure from home, follow @McAfee_Home on Twitter, listen to our podcast Hackable?, and ‘Like’ us on Facebook.
The post Uber Data Breach and How to Protect Your Info appeared first on McAfee Blog.

Can thieves steal identities with only a name and address?
In short, the answer is “no.” Which is a good thing, as your name and address are in fact part of the public record. Anyone can get a hold of them. However, because they are public information, they are still tools that identity thieves can use.
If you think of your identity as a jigsaw puzzle, your name and address are the first two pieces that they can use to build a bigger picture and ultimately put your identity at risk.
With that, let’s look at some other key pieces of your identity that are associated with your name and address—and what you can do to protect them.
For starters, this information is so general that it is of little value in of itself to an identity thief. Yet a determined identity thief can do a bit of legwork and take a few extra steps to use them as a springboard for other scams.
For example, with your name and address a thief could:
There are volumes of public information that are readily available should someone want to add some more pieces to your identity jigsaw puzzle, such as:
In the U.S., the availability of such information will vary from state-to-state and different levels of government may have different regulations about what information gets filed—in addition to whether and how those reports are made public. Globally, different nations and regions will collect varying amounts of public information and have their own regulations in place as well. More broadly, though, many of these public databases are now online. Consequently, accessing them is easier than the days when getting a hold of that information required an in-person visit a library or public office.
Thieves can gain additional information about you from other online sources, such as data brokers. And data brokerage is a big business, a global economy estimated at $200 billion U.S. dollars a year. What fuels it? Personal information, representing thousands of data points on billions of people scraped from public records, social media, smartphone apps, shopper loyalty cards, third-party sources, and sometimes other data broker sites as well.
The above-the-board legal intent of data broker sites is to sell that information to advertisers so that they can create highly targeted campaigns based on people’s behaviors, travels, interests, and even political leanings. Others such as law enforcement officials, journalists, and others who are conducting background checks will use them too.
On the dark side, hackers, scammers, and thieves will buy this information as well, which they can use to commit identity theft and fraud. The thing is, data brokers will sell to anyone. They don’t discriminate.
Phishing attacks aren’t just for email, texts, and direct messages. In fact, thieves are turning to old tricks via old-fashioned physical mail. That includes sending phony offers or by impersonating officials of government institutions, all designed to trick you into giving up your personally identifiable information (PII).
What might that look like in your mailbox? They can take the form of bogus lottery prizes that request bank information for routing (non-existent) winnings. Another favorite of scammers are bogus tax notifications that demand immediate payment. In all, many can look quite convincing at first blush, yet there are ready ways you can spot them. In fact, many of the tips for avoiding these physical mail phishing attacks are the same for avoiding phishing attacks online, which we outline in detail here.
Recently, I’ve seen a few news stories like this where thieves reportedly abuse the change-of-address system with the U.S. Postal Service. Thieves will simply forward your mail to an address of their choosing, which can drop sensitive information like bank and credit card statements in their mailbox. From there, they could potentially have new checks sent to them or perhaps an additional credit card—both of which they can use to drain your accounts and run up your bills.
The Postal Service has mechanisms in place to prevent this, however. Among which, the Postal Service will send you a physical piece of mail to confirm the forwarding. So, if you ever receive mail from the Postal Service, open it and give it a close look. If you get such a notice and didn’t order the forwarding, visit your local post office to get things straightened out. Likewise, if it seems like you’re missing bills in the mail, that’s another good reason to follow up with your post office and the business in question to see if there have been any changes made in your mail forwarding.
So while your name and address are out there for practically all to see, they’re largely of little value to an identity thief on their own. But as mentioned above, they are key puzzle pieces to your overall identity. With enough of those other pieces in hand, that’s where an identity thief can cause trouble.
Other crucial pieces of your identity include:
Let’s start with the biggest one. This is the master key to your identity, as it is one of the most unique identifiers you have. As I covered in my earlier blog on Social Security fraud, a thief can unlock everything from credit history and credit line to tax refunds and medical care with your Social Security or tax ID number. In extreme cases, they can use it to impersonate you for employment, healthcare, and even in the event of an arrest.
You can protect your Social Security Number by keeping it locked in a safe place (rather than in your wallet) and by providing your number only when absolutely necessary. For more tips on keeping your number safe, drop by that blog on Social Security fraud I mentioned.
Thieves have figured out ways of getting around the fact that IDs like these include a photo. They may be able to modify or emulate these documents “well enough” to pull off certain types of fraud, particularly if the people requesting their bogus documents don’t review them with a critical eye.
Protecting yourself in this case means knowing where these documents are at any time. (With passports, you may want to store those securely like your Social Security or tax ID number.) Also be careful when you share this information, as the identifiers on these documents are highly unique. If you’re uncomfortable with sharing this information, you can ask if other forms of ID might work—or if this information is really needed at all. Also, take a moment to make copies of these documents and store them in a secure place. This can help you provide important info to the proper authorities if they’re lost or stolen.
With data breaches large and small making the news (and many more that do not), keeping a sharp eye on your accounts is a major part of identity theft prevention. We talk about this topic quite often, and it’s worth another mention because protecting these means protecting yourself from thieves who’re after direct access to your finances and more.
Secure your digital accounts for banking, credit cards, financials, and shopping by using strong, unique passwords for each of your accounts that you change every 60 days. Sound like a lot of work? Let a password manager do it for you, which you can find in comprehensive online protection software. By changing your strong passwords and keeping them unique can help prevent you from becoming a victim if your account information is part of a breach—by the time a crook attempts to use it, you may have changed it and made it out of date.
In addition to protecting the core forms of identity mentioned above, a few other good habits go a long way toward keeping your identity secure.
By protecting your devices, you protect what’s on them, like your personal information. Comprehensive online protection software can protect your identity in several ways, like creating and managing the strong, unique passwords we talked about and providing further services that monitor and protect your identity—in addition to digital shredders that can permanently remove sensitive documents (simply deleting them won’t do that alone.) Further, it can monitor your identity and monitor your credit, further protecting you from theft and fraud.
Identity theft where thieves dig through trash or go “dumpster diving” for literal scraps of personal info in bills and statements, has been an issue for some time. You can prevent it by shredding up any paper medical bills, tax documents, and checks once you’re through with them. Paper shredders are inexpensive, and let’s face it, kind of fun too. Also, if you’re traveling, have a trusted someone collects your mail or have the post office put a temporary hold on your mail. Thieves still poach mail from mailboxes too.
Getting statements online cuts the paper out of the equation and thus removes another thing that a thief can physically steal and possibly use against you. Whether you use electronic statements through your bank, credit card company, medical provider, or insurance company, use a secure password and a secure connection provided by a VPN. Both will make theft of your personal info far tougher on identity thieves.
A VPN is a Virtual Private Network, a service that protects your data and privacy online. It creates an encrypted tunnel to keep you more anonymous online by masking your IP address, device information, and the data you’re passing along that connection. In this way, it makes if far more difficult for advertisers, data brokers, and bad actors to skim your private information—in addition to shielding your information from crooks and snoops while you’re banking, shopping, or handling any kind of sensitive information online.
Give your statements a close look each time they come around. While many companies and institutions have fraud detection mechanisms in place, they don’t always catch every instance of fraud. Look out for strange purchases or charges and follow up with your bank or credit card company if you suspect fraud. Even the smallest charge could be a sign that something shady is afoot.
This is a powerful tool for spotting identity theft. And in many cases, it’s free to do so. In the U.S., the Fair Credit Reporting Act (FCRA) requires the major credit agencies to provide you with a free credit check at least once every 12 months. Canada provides this service, and the UK has options to receive free reports as well, along with several other nations. It’s a great idea to check your credit report, even if you don’t suspect a problem.
If the thought of your personal info being bought and sold puts you off, there’s something you can do about it. Our Personal Data Cleanup service can scan some of the riskiest data broker sites and show you which ones are selling your personal info. It also provides guidance on how you can remove your data from those sites, and with select products, it can even manage the removal for you.
While thieves need more than just your name and address to commit the overwhelming majority of fraud, your name and address are centerpieces of the larger jigsaw puzzle that is your overall identity.
And the interesting thing is your puzzle gets larger and larger as time goes on. With each new account you create and service that you sign into, that’s one more piece added to the puzzle. Thieves love getting their hands on any pieces they can because with enough of them in place they can try and pull a fast one in your name. By looking after each piece and knowing what your larger jigsaw puzzle looks like, you can help keep identity thieves out of your business and your life.
The post Can Thieves Steal Identities With Only a Name and Address? appeared first on McAfee Blog.

Spyware is tricky. Some types notify users that they’re monitoring activity. Others function in stealth mode and use the information they collect for nefarious purposes. Spyware is a type of software that collects data about online users and reports it to a company or an individual. What just about everyone can agree on is that anonymous browsing is looking more and more appealing and is likely the way of the future.
Here’s more about the types of spyware, which types are legal, and how you can scrub your device and live more confidently online.
Here are a few types of spyware and facts about each:
Is it legal? Definitely not!
What is its purpose? Criminal
Keyloggers are the most intrusive of the spyware variations. It does exactly as its name suggests: It takes note of keyboard strokes, logs them, and reports to the owner of the nefarious software. Once the cybercriminal has digitally looked over your shoulder at your online activity, they make note of your passwords, walk into your online accounts, and pilfer your private personal information. They could use this information to gain entry to your online bank accounts or steal your identity.
Keyloggers are downloaded onto devices (cellphones, tablets, laptops, or desktop computers) without the user’s knowledge. Cybercriminals can hide them within email attachments or in malicious web pages. So, the best way to steer clear of keyloggers is to never download attachments you’re unsure about and don’t visit sites that seem unprofessional. One rule of thumb is to mostly stick to URLs that begin with https and include a lock icon. These sites are almost always secure.
To determine if your device is infected with a keylogger, check your system’s performance. Is your device running slowly? See if there are any spikes in activity or unknown programs running in the background. This could indicate that your device is hosting a malicious program.
Is it legal? Sometimes
What is its purpose? Advertising and criminal
Adware is categorized as a type of spyware. It tracks users’ online activity and spits out targeted pop-up advertisements. If you have the pop-up blocker enabled on your browser, you’ll likely be spared from the annoyance. Additionally, pop-ups can slow your device, so that’s another reason to turn on the pop-up blocking feature. Legitimate adware often asks users to opt into targeted ads.
Adware turns malicious (and illegal) when it contains malware. Sometimes cyber criminals hide malware within pop-ups. It’s easy to accidentally hit a link within a pop-up when you’re aiming quickly for the X to close it.
It’s easy to spot a device with an adware infestation. First, the number of pop-ups will be out of control. Also, the device will crash often, run very slowly, and have a short battery life. An antivirus program will likely be able to identify and remove the culprit. You can also check out your system monitor and end tasks that are draining your device’s power.
Is it legal? Yes
What is its purpose? Advertising
Cookies are delicious, especially to advertisers who use them to better target ads and make profits selling collected user data to third-party companies. Cookies are sometimes categorized as spyware, because they log the websites you visit and report them. You may notice the banners on websites that ask you to accept cookies.
Many users today are uneasy with sharing their online activity with strangers and advertisers. Sometimes the ads that pop up on your social media feed or in sidebars seem a little too targeted and it feels like someone is listening in to your conversations and attempting to make a profit from them.
How to Browse Free of Spyware
To scrub cybercriminals from your devices and confuse advertisers, consider the following steps you can easily add to your daily routine:
The post How to Live a Digital Life Free of Spyware appeared first on McAfee Blog.

You’re not the only one looking forward to the big holiday sales like Black Friday and Cyber Monday. Hackers are too. As people flock to retailers big and small in search of the best deals online, hackers have their shopping scams ready. Remember, McAfee frees you to live your connected life safe from threats like viruses, malware, phishing, and more. Download award-winning antivirus that protects your data and devices today.
One aspect of cybercrime that deserves a fair share of attention is the human element. Crooks have always played on our feelings, fears, and misplaced senses of trust. It’s no different online, particularly during the holidays. We all know it can be a stressful time and that we sometimes give into the pressure of finding that hard-to-get gift that’s so hot this year. Crooks know it too, and they’ll tailor their attacks accordingly as we get wrapped up in the rush of the season.
So while you already know how to spot a great deal, here are ways you and your family can spot online shopping scams so you can keep your finances safer this shopping season:
A common scam hackers use is introducing malware via email attachments, and during the holiday sale season, they’ll often send malware under the guise of offering emails and shipping notifications. Know that retailers and shipping companies won’t send things like offers, promo codes, and tracking numbers in attachments. They’ll clearly call those things out in the body of an email instead.
A classic scammer move is to “typosquat” phony email addresses and URLs that look awfully close to legitimate addresses of legitimate companies and retailers. They often appear in phishing emails and instead of leading you to a great deal, these can in fact link you to scam sites that can then lift your login credentials, payment info, or even funds should you try to place an order through them. You can avoid these sites by going to the retailer’s site directly. Be skeptical of any links you receive by email, text, or direct message—it’s best to go to the site yourself by manually typing in the legitimate address yourself and look for the deal there.
A related scammer trick that also uses typosquatting tactics is to set up sites that look like they could be run by a trusted retailer or brand but are not. These sits may tout a special offer, a great deal on a hot holiday item, or whatnot, yet such sites are one more way cybercriminals harvest personal and financial information. A common way for these sites to spread is by social media, email, and other messaging platforms. Again a “close to the real thing” URL is a telltale sign of a copycat, so visit retailers directly. Also, comprehensive online protection software can prevent your browser from loading suspicious sites and warn you of suspicious sites in your search results.
While the best of them can look practically professional and be tough to spot, one way to avoid counterfeit shopping apps is to go to the source. Hit the retailer’s website on your mobile browser and look for a link to the app from their website. Likewise, stick to the legitimate app stores such as Google Play and Apple’s App Store. Both have measures in place to prevent malicious apps from appearing in their stores. Some can sneak through before being detected though, so look for the publisher’s name in the description and ensure it is legitimate. On a fake app, the name may be close to the retailer you’re looking for, but not quite right. Other signs of a fake will include typos, poor grammar, and design that looks a bit off.
At the heart of holiday shopping is scarcity. Special offers for a limited time, popular holiday items that are tough to find, and just the general preciousness of time during the season to get things done, like shopping. Scammers love this time of year. During the holidays, they’ll play on that scarcity and crunch you’re under in their offers and messaging. Enter the “too good to be true” offer, typically set up on phony sites like the ones mentioned above. If the pricing, availability, or delivery time all look too good to be true, it may be a scam designed to harvest your personal info and accounts. Use caution here before you click. If you’re unsure about a product or retailer, read reviews from trusted websites to help see if it’s legitimate.
Apart from spotting scams, there are several things you can do to keep yourself safer while shopping this holiday season. In fact, they can keep you safer when you shop year ‘round as well. Looking for a last minute deal? Download McAfee online protection today.
This is a great one to start with. Secure websites begin their address with “https,” not just “http.” That extra “s” in stands for “secure,” which means that it uses a secure protocol for transmitting sensitive info like passwords, credit card numbers, and the like over the internet. It often appears as a little padlock icon in the address bar of your browser, so double-check for that. If you don’t see that it’s secure, it’s best to avoid making purchases on that website.
Specific to the U.S., the Fair Credit Billing Act offers the public protection against fraudulent charges on credit cards, where citizens can dispute charges over $50 for goods and services that were never delivered or otherwise billed incorrectly. Note that many credit card companies have their own policies that improve upon the Fair Credit Billing Act as well. However, debit cards aren’t afforded the same protection under the Act. Avoid using those while shopping online and use your credit card instead.
Another alternative is to set up a virtual credit card, which is a proxy for your actual credit card. With each purchase you make, that proxy changes, which then makes it much more difficult for hackers to exploit. You’ll want to research virtual credit cards further, as there are some possible cons that go along with the pros, such as in the case of returns where a retailer will want to use the same proxy to reimburse a purchase.
Using a complete suite of online protection software can offer layers of extra protection while you shop, such as web browser protection and a password manager. Browser protection can block malicious and suspicious links that could lead you down the road to malware or a financial scam. A password manager can create strong, unique passwords and store them securely as well, making it far more difficult for hackers to compromise your accounts. Identity theft protection takes your safety a step further by helping you secure your identity online and restore it should any of your personal info be found in the wrong hands.
Two-factor authentication is an extra layer of defense on top of your username and password. It adds in the use of a special one-time-use code to access your account, usually sent to you via email or to your phone by text or a phone call. In all, it combines something you know, like your password, with something you have, like your smartphone. Together, that makes it tougher for a crook to hack your account. If any of your accounts support two-factor authentication, the few extra seconds it takes to set up is more than worth the big boost in protection you’ll get.
Public Wi-Fi in coffee shops and other public locations can expose your private surfing to prying eyes because those networks are open to all. Using a virtual private network (VPN) encrypts your browsing, shopping, and other internet traffic, thus making it secure from attempts at intercepting your data on public Wi-Fi and harvesting information like your passwords and credit card numbers.
With all the passwords and accounts we keep, this is important. Checking your credit will uncover any inconsistencies or outright instances of fraud. From there, you can then take steps to straighten out any errors or bad charges that you find. In the U.S., you can run a free credit report once a year with the major credit reporting agencies.
So while you’re shopping online this year, take a deep breath before you dive in. Double-check those deals that may look almost too good to be true. Look closely at those links. And absolutely don’t click on those attachments that look like shipping notices or coupon deals. Hackers are counting on you to be in a bit of a hurry this time of year. Taking an extra moment to spot their tricks can go a long way toward keeping you and your finances safe. Remember, stay ahead of cyber criminals, get an extra layer of protection with McAfee this holiday season.
The post Spot Those Black Friday and Cyber Monday Shopping Scams appeared first on McAfee Blog.

If you pick up your teen’s phone on any given day, chances are the next stop you make will be Google. That’s because, if you’re like most parents, you’re beyond baffled by texting language kids use.
It’s okay, you are not alone if you feel out of the loop. As parents, we’re not invited to the party—and that’s okay. Slag belongs to the generation that coined it. And few of us are aching to use words like “sus” and “simp,” right? The goal of these updates isn’t to decode or invade. It’s digital parenting 101. The more we know about what’s going on in our child’s world, the better we can parent. It’s our job to know.
So once a year we do our best to decipher some of the more common terms you may hear or see your kids use. Keep in mind: Slang isn’t universal. It changes from city to city and culture to culture. Terms and meanings may vary. Many of the words are fun and harmless, while others are specifically meant to mask risky behavior. Remember, McAfee frees you to live your connected life safe from threats like viruses, malware, phishing, and more. Download award-winning antivirus that protects your data and devices today.
A real one. A person who is being authentic, genuine, trusted.
And I oop. A phrase used after a funny mistake or accident.
Awks. Short for awkward.
Baddie. Name for an independent female who is tough and beautiful.
Bands. Refers to bands around cash or a wealthy person. No doubt, the dude’s got bands.
Bet. A willingness to do something; means “yes” or “okay.”
Big yikes. When you see something, that is a huge embarrassment.
Booed up. To be in a romantic relationship.
Bop. A really good song. That song is such a bop!
Bread or Cheddar. Terms that refer to money.
Breadcrumbing. Sending flirtatious text messages to another person to get their attention but remain non-committal.
Bussin. Something is awesome. Her new hair color is bussin’.
Cake. When someone’s body looks good. The girl in my science class has cake.
Cancel. Reject or stop supporting a group or idea.
Cap. A term that means “lie” or “false.” He said we were a couple. Cap!
No cap. A phrase that means “no lie” or “for real” emphasizes telling the truth. I just saw him eat a bug. No cap!
CEO. A term used to describe something that you’re very good at, making you the CEO of it. I’m the CEO of being late to class.
Cheug. This term describes a person, idea, or situation that is outdated or inauthentic.
Clout. A term that relates to a person’s follower count, fame, or influencer status. Sometimes an expression for an extravagant way of living.
Chasing Clout. A term that describes a person who does and says things for the sole purpose of becoming more popular.
Curve. To reject someone romantically.
Cuffing. Wanting to date or cuff yourself to someone temporarily—at least until summer break.
Do it for the gram. A phrase that describes someone doing something for the sole purpose of posting online.
Drip. A term that describes someone’s style as sexy or cool. Zayne has some serious drip.
Facts. When you agree with someone.
Finsta. A second Instagram account used for sharing with a smaller circle of friends and followers.
Fish. Fishing for compliments.
Fit. Short for outfit.
Flex. To show off or show something off.
Get after it. Start with something with intensity.
Ghost. Suddenly stop all contact with someone online and in person.
Hundo P. Being 100% certain.
Hypebeast. A term that describes someone who cares too much about popular things rather than being self-aware and genuine.
I’m dead. Describes how you feel when something is hilarious.
I’m weak. Like, dead, describes how you feel when something is hilarious.
I can’t even. An expression used when you’ve had enough of someone or a situation.
Keep it 100. Stay true to yourself and stick to your values.
Lewk. Look.
Left on read. When someone does not respond to your text. He left me on read!
Lit. Cool or awesome.
Mood. A term used to express a relatable feeling or experience. Seeing that kid by himself kicking a can is such a mood.
Mutuals. People who follow and support one another on social media.
Oof. An expression used when something bad happens, and you don’t know how to respond.
Periodt. A term used to emphasize what you just said.
Purr. Expressing approval. I’ve got nothing but purr for my friends.
Receipts. Evidence to prove someone is either lying. Often in the form of screenshots, videos, or images.
Savage. A cool person or someone overly direct or candid.
Sketch. A sketchy or ominous situation, place, or person.
Skrrt. To leave quickly or get away from someone (the sound a car makes).
Ship. Short for relationship.
Simp. Used to describe a guy who is seen as being too attentive and submissive to a girl.
Sheesh. A term used to compliment someone when they look good or do something good.
Suh. A combination of “sup” and “huh” used as a greeting.
Sus. Short for suspect describing a situation, a person, or a claim. That guy is sus. Let’s get out of here.
Shawty. An attractive female. Sometimes a short, attractive female.
Sheee. An expression of disappointment, annoyance, or surprise.
Slaps. A term used when something is awesome. The DJ slaps.
Snatched. Describing a person or a thing that looks great. I’m jealous her makeup is so snatched.
Stan. A combination of “stalker” and “fan” refers to an overly obsessed fan of a celebrity.
Straight Fire or Fire. Describes something amazing. His new truck is straight fire.
Thumpin’. Word to describe someone going very. I didn’t even see him leave. He was thumpin’.
Vaguebooking. The act of posting vague Facebook or other social status updates for attention or as a cry for help. Wondering what the point of it all is anyway.
Whip. A word that means car. Have you seen his new whip?
Wig. When something has you so excited, your wig might come off; mind-blowing. The new Adele song!! WIIIIGGG!
Yeet. Throwing something out of rage. Also used as an exclamation for being excited.
NGL. Not Gonna Lie.
NMH. Nodding My Head; an expression of agreement.
NSA. No Strings Attached.
HWU. Hey, what’s up?
IYKWIM. If You Know What I Mean.
RLY. Really?
OG.Short for Original Gangster;a compliment for someone who is exceptional or authentic.
ORLY. Oh really?
SMH. Shaking My Head.
TFW. That Feeling When
TT2T. Too Tired to Talk.
L. Short for loose or loss.
V. Short for very.
W. Short for win. Their loss is our w.
WYA. Where are you at?
WYD. What are you doing?
YK. You’re Kidding.
YKTS. You Know the Score.
YKTV. You know the vibe.
Addy/Study Buddy. Terms used in place of the medication Adderal.
Break Green. A term that means to share marijuana with others.
Crashy. Combo of “crazy” and “trashy.”
Daddy. An attractive man, usually older, who conveys a sense of power and dominance.
Faded/Cooked. Terms used to describe being high on drugs.
Lit/Turnt Up. It can mean party or get drunk.
MOS/POS. Mom Over Shoulder; Parent Over Shoulder.
Kush/Flower/Gas. Terms used in place of marijuana.
Smash. To hook up for casual sex. Is he a smash or a pass?
Thirsty. Adjective for a person desperate for attention or sex.
Xan/Xans. Terms short for Xanax, a sedative used to treat anxiety. Also called xanny, beans, bars, and footballs.
ASL. Age/sex/location.
CD9. Can’t talk parents are here.
CU46. See You For Sex.
GALMA. Go Away Leave Me Alone.
GOMB. Get Off My Back.
GSW. Get Some Weed.
LMIRL. Let’s meet in Real Life.
KMS/KYS. Kill myself, Kill Yourself.
ONG. On God; a term that implies a person is serious enough to swear “on god.”
ONS. One Night Stand.
Spice or K2. Code for synthetic marijuana, which can be more harmful than actual cannabis.
URAL. You’re A Loser.
WWTP. Want to Trade Pics?
X or E. Letters that stand for ecstasy, otherwise known as “molly” or MDMA.
Zaddy. A well-dressed, attractive man of any age.
Zerg. A term that originated in the gaming community for gamers using the many against one strategy to win a game. A Zerg is a person who employs the same bullying tactics in real life. Stay away from him. He’s such a Zerg! Or Stay off that site. There’s too much zerging.
Protect your connected life today with McAfee Total Protection
*Content collected from various sources, including NetLingo.com, slangit.com, cyberdefinitions.com, UrbanDictionary.com, webopedia.com, and conversations on TikTok, Reddit, and YouTube.
The post Teen Slang and Texting Acronyms Parents Should Know appeared first on McAfee Blog.

The holidays are almost here! That means it’s time to start making your list and checking it twice. To help prepare you for this year’s holiday shopping spree, McAfee is providing you with the ultimate holiday shopping list for every Tech lover in your family. Here are the devices to keep on your radar this holiday shopping season and what you should use to protect them.
Know someone who enjoys vanquishing aliens, building virtual amusement parks, and online battle royale? There’s a good chance that you do, as online gaming traffic increased 30% from the first to the second quarter of 2020. For the gaming guru in your life, consider gifting them a top-of-the-line gaming laptop so, they don’t have to compromise portability for playability. If they prefer to play in the comfort of their own home, consider giving the gamer in your life a snazzy new gaming monitor. This will allow them to enjoy a crystal-clear resolution, rapid refresh rate, and size to bring their virtual world to life. And to truly immerse your gamer in a new realm, gift them a new gaming console so they can enjoy optimal speed and stellar game lineups.
When shopping for your gamer, consider how you can empower them to stay secure while they play. A security solution like McAfee Gamer Security not only delivers a faster, quieter, and safer experience, but it can also boost a rig’s performance. This antivirus software detects threats through the cloud and optimizes resources to minimize frame drops. Gamers can even customize which games to boost (or even add other apps they’d like to boost), which background services to pause, and more. This improves your gamer’s experience and also keeps them safe while they play.
Does your tech-savvy teen love to browse on the go? Or perhaps you have a college student who likes to bring their online studying and video streaming with them beyond the home. For the mobile mastermind in your family, gift them a new smartphone or tablet this holiday season. These devices will allow your loved ones to access all their favorite apps and surf the web anytime, anywhere.
With the World Wide Web constantly at their fingertips, enable your family members to surf the internet with confidence by employing the help of a safe browsing solution like McAfee WebAdvisor. This trusty companion, available for free and included in the McAfee Total Protection app for iOS and Android, helps keep users safe from threats like malware and phishing attempts. Web Advisor blocks malicious sites, scans downloads, and alerts the user if a known threat is detected. With comprehensive security on their side, your mobile user will be free to search, stream, and download on the go.
The number of smart households (households that contain connected technology and can interact with other IoT devices) in the U.S. is expected to grow to 77.05 million by 2025. That may not come as a surprise, since IoT devices have upped the convenience of tech users’ lives everywhere. Perhaps your spouse or parents love filling their home with the latest and greatest smart home gadgets. This holiday season, give them the gift of convenience with a smart TV, speaker, thermostat, kitchen appliances, a personal home assistant – the list of smart home devices goes on!
While these devices can provide greater efficiency to anyone’s life, it’s important to be aware of the potential risks that come with this level of interconnectivity. Many product designers treat security as an afterthought, rushing to get their smart devices to market and consequentially creating an easy access point for criminals to exploit. But fear not! A solution like McAfee Secure Home Platform can automatically secure connected devices through a router with McAfee protection. It can hide your IoT devices from hackers, giving you the confidence that you have a solid line of defense against online threats.
For the Fitness Fanatic
At the onset of the pandemic, people adjusted their workout routines to accommodate for gym closures and began to rely on other solutions to stay fit. In fact, many turned to IoT devices used for virtual fitness, including wearable fitness trackers and stationary machines equipped with digital interfaces. Sound like someone you know? Consider giving them a stylish new or upgraded smartwatch that allows them to track their daily step count, heart rate, and sleep patterns.
While these devices can be instrumental in tracking users’ activity levels, it’s important to remember that wearable gadgets collect valuable health and location data a criminal could exploit. To keep your fitness fanatic happy and healthy without sweating their security, encourage them to install software updates immediately. This will protect your loved one’s device from reported bugs, enhance functionality, and seal up any security loopholes.
As you plan your holiday shopping list this year, don’t forget about the gift that keeps on giving: the peace of mind that comes with having the right online security! With comprehensive solutions built to safeguard your loved one’s devices, personal data, and everything they do online, they can continue to live their digital lives with confidence.
The post The Ultimate Holiday Shopping Guide appeared first on McAfee Blog.

It’s safe to say that many Americans are obsessed with Squid Game. According to Business Insider, the Korean drama series has driven the newest engagers to a Netflix title of any Netflix series over the last three years. And while word-of-mouth buzz has played a big part in the show’s success, TV watchers aren’t the only ones taking note. Cybercriminals are also formulating ways to profit off the show’s popularity. According to the New York Post, a malicious app based on Squid Game was recently found on the Google Play Store, infecting users’ devices with malware.
The app in question, called “Squid Game Wallpaper 4K HD,” was one of the 200 Squid Game-related apps on the Google Play Store. This particular app masqueraded as a place to download cool Squid Game backgrounds for Android devices. However, once a user downloaded the app, it infected their smartphone with a strain of Joker malware. Joker malware is a type of billing fraud malware that usually disguises itself as a messenger, photo editor, camera, or in this case, wallpaper apps.
You may wonder how an app like this even ends up on a legitimate app purchasing store. In order to bypass Google Play’s app review process, Joker malware hides its malicious payload during the review process. This means that when the app is published in the Google Play Store, there’s no sign of malware. It’s only when a user installs the app that the malware downloads the malicious payload. Once the malware successfully installs itself, it secretly signs the user up for premium subscriptions, intercepts all their SMS messages, and can upload all their contacts to the malware operators.
The “Squid Game Wallpaper 4K HD” app received 5,000 downloads before it was removed from the Google Play Store. It’s likely that cybercriminals will continue to use the show’s popularity to exploit its fans and make a profit, whether that be through malicious apps disguised as a place where viewers can watch the show or fraudulent websites selling Squid Game merchandise. But fear not! There are steps you can take to help ensure that you steer clear of malware:
Unlike Google Play and Apple’s App Store, which have measures in place to review and vet apps to help ensure that they are safe, third-party sites may not have that process in place. In fact, some third-party sites may intentionally host malicious apps as part of a broader scam. However, cybercriminals have found ways to work around Google and Apple’s review process (such as with “Squid Game Wallpaper 4K HD”), but the chances of downloading a safe app from these stores are far greater than anywhere else. Additionally, Google and Apple are quick to remove malicious apps once discovered.
Before you download a new app, do some quick research. Check out the developer. Have they published several other apps with many downloads and good reviews? A legit app typically has several reviews, whereas malicious apps may have only a handful of fake five-star reviews. Lastly, look for typos and grammatical errors in both the app description and screenshots. They could be a sign that a hacker slapped the app together and quickly deployed it.
Certain types of malware strains operate stealthily behind the scenes, commandeering login credentials or banking information right under a user’s nose. Check your accounts every so often and if you notice any suspicious activity, report it and change your passwords. You can also use ID monitoring tools, which will notify you of uncharacteristic changes or actions.
Just like you secure your computers and laptops, it’s important to secure the minicomputer in your pocket—your smartphone! For the strongest protection, use comprehensive security software that shields your device from malware and risky websites, links, and files. With a few key steps, you can boost your confidence in the safety of your devices and personal information and enjoy your favorite binge-worthy shows to the fullest!
The post Squid Game App or Mobile Malware in Disguise? appeared first on McAfee Blog.

What do social media companies really know about you? It’s a fair question. And the quick answer is this: the more you use social media, the more those companies likely know.
The moment you examine the question more closely, the answer takes on greater depth. Consider how much we use social media for things other than connecting with friends. While that was the original intent behind social networks, the role of social media has since evolved into something far more expansive. We use it to get our news, stay up to date on when artists will drop a new release, and sometimes reach out for customer service on a company’s social media page. In some cases, we use our social media accounts to log into other sites and apps or we even make payments through social media.
Taken together, all of those likes, taps, clicks, links, and time spent reading or watching videos can add up and paint a detailed picture of who you are.
Why are they collecting all this information? Largely, it’s for two reasons:
1. To make improvements to their platform, by better understanding your behavior and ways you like to use their service.
2. To create an exacting user profile that advertisers can use for targeting ads that they think will interest you.
That’s the exchange in play here. You use the company’s social media service for free, and in return, they gain rights to gather specific information about you, which you consent to by agreeing to their terms of service.
Let’s get into the details of what social media companies may collect and know about you—along with ways you can limit the data and information they gather.
Different social media platforms have different user agreements that cover what types of information they collect and use. For starters, we’ll speak broadly about social media companies in general, and then we’ll weave in a few specific examples along the way. Generally, they may know:
We collect information about how you use our Products, such as the types of content you view or engage with; the features you use; the actions you take; the people or accounts you interact with; and the time, frequency and duration of your activities.
When you communicate with others by sending or receiving Direct Messages, we will store and process your communications and information related to them. This includes link scanning for malicious content, link shortening to http://t.co URLs, detection of spam, abuse and prohibited images, and use of reported issues. We also use information about whom you have communicated with and when (but not the content of those communications) to better understand the use of our services, to protect the safety and integrity of our platform, and to show more relevant content.
If you use our Products for purchases or other financial transactions (such as when you make a purchase in a game or make a donation), we collect information about the purchase or transaction. This includes payment information, such as your credit or debit card number and other card information; other account and authentication information; and billing, shipping and contact details.
By the way, none of this is secret. What I’ve listed here can be found by simply reading the terms of use posted by various social media companies. Note that these terms of use can and do change. Checking up on them regularly will help you understand what is being collected and how it may be used.
This nearly goes without saying, yet another layer of data and information collection comes by way of the pictures and updates you post. Per Instagram (as of October 2021):
We collect the content, communications and other information you provide when you use our Products, including when you sign up for an account, create or share content, and message or communicate with others. This can include information in or about the content you provide (like metadata), such as the location of a photo or the date a file was created.
Another consideration is how the content you interact with on other sites may be shared with social media companies in return. Some social media companies partner with other third parties to gather this data, which is used to round out your user profile in yet more detail. That information can include purchases you made, how often you visited that third party’s site, and so on.
In the case of Facebook, they refer to this as “Off-Facebook Activity.” In their words:
Off-Facebook activity includes information that businesses and organizations share with us about your interactions with them. Interactions are things like visiting their website or logging into their app with Facebook. Off-Facebook activity does not include customer lists that businesses use to show a unique group of customers relevant ads.
The good news here is that you can take control of the Off-Facebook Activity setting with a few clicks.
No doubt about it, the content you create and interact with, both on the social media sites and sometimes off of them as well, can generate information about you that’s collected by social media companies.
Short of deleting your accounts altogether, there are several things you can do to take control and limit the amount of information you share.
For example, you can visit your Facebook Settings, Instagram Settings, and Twitter Settings, which each gives you options for managing your information—or download it and even delete it from their platform outright if you wish. (Note that this will likely only delete data associated with your account. Content you posted or shared with other people on their accounts will remain.)
As noted above, this isn’t an absolute fix because social media companies can infer your location other ways. Yet taking this step gives them one less piece of exacting information about you.
Each platform will have its own settings and options, so give them a look. Here, you can determine which information advertisers are allowed to use to serve up ads to you, set rules for facial recognition, enable or disable location history, and much more. If possible, do this from your computer or laptop rather than your smartphone. Often, the account controls that you can access from a computer browser are far more comprehensive than the ones in a mobile app.
Using direct messaging on social media platforms may tell social media companies even more about you and who you interact with. When possible, think about using text messaging instead or other means of communication that aren’t tied to a social media company.
Some apps and sites will allow you to use your social media login instead of creating a new one. While convenient, this can provide the social media company with more information about you. Additionally, if your social media account is compromised, it could compromise the other accounts that are tied to it as well. Check your settings and look for “Apps and Websites” to see what’s connected to your social media account, what’s being shared, and how you can disable it.
Protection like ours will include a VPN, which anonymizes your online activity and thus may shield you from certain types of information collection, such as your location. Additionally, using online protection software is simply a good move because it can create and store strong, unique passwords for you, steer you clear of risky sites, protect your identity, and make your time online safer overall.
The very nature of social media is sharing and exchanging. That’s the draw it has—the way it keeps us connected to the people, pastimes, and things we care about. Yet that exchange runs deeper. In return for using these free services, social media companies collect information on us which they use to improve their platforms and generate revenue. It’s all there for you to see in the various terms of use associated with your social media accounts. In short, using social media means sharing information about yourself with social media companies.
Yet you can do several things to reduce the amount of information that social media companies know about you. By spending some time on the account and privacy settings for each of your social media accounts, you can determine what information you’re providing to them and get a much better sense of what social media companies know about you.
The post What Do Social Media Companies Know About You? appeared first on McAfee Blog.

In the hands of a thief, your Social Security Number is the master key to your identity.
With a Social Security Number (SSN), a thief can unlock everything from credit history and credit line to tax refunds and medical care. In extreme cases, thieves can use it to impersonate others. So, if you suspect your number is lost or stolen, it’s important to report identity theft to Social Security right away.
Part of what makes an SSN so powerful in identity theft is that there’s only one like it. Unlike a compromised credit card, you can’t hop on the phone and get a replacement. No question, the theft of your SSN has serious implications. If you suspect it, report it. So, let’s take a look at how it can happen and how you can report identity theft to Social Security if it does.
Yes. Sort of. The Social Security Administration can assign a new SSN in a limited number of cases. However, per the SSA, “When we assign a different Social Security number, we do not destroy the original number. We cross-refer the new number with the original number to make sure the person receives credit for all earnings under both numbers.”
In other words, your SSN is effectively forever, which means if it’s stolen, you’re still faced with clearing up any of the malicious activity associated with the theft potentially for quite some time. That’s yet another reason why the protection of your SSN deserves particular attention.
There are several ways an SSN can end up with a thief. Some involve physical theft, and others can take the digital route. To what extent are SSNs at risk? Notably, there was the Equifax breach of 2017, which exposed some 147 million SSNs. Yet just because an SSN has been potentially exposed does not mean that an identity crime has been committed with it.
So, let’s start with the basics: how do SSNs get stolen or exposed?
That’s quite the list. Broadly speaking, the examples above give good reasons for keeping your SSN as private and secure as possible. With that, it’s helpful to know that there are only a handful of situations where your SSN is required for legitimate purposes, which can help you can make decisions about how and when to give it out. The list of required cases is relatively short, such as:
You’ll notice that places like doctor’s offices and other businesses are not listed here, though they’ll often request an SSN for identification purposes. While there’s no law preventing them from asking you for that information, they may refuse to work with you if you do not provide that info. In such cases, ask what the SSN would be used for and if there is another form of identification that they can use instead. In all, your SSN is uniquely yours, so be extremely cautious in order to minimize its potential exposure to theft.
Let’s say you spot something unusual on your credit report or get a notification that someone has filed a tax return on your behalf without your knowledge. These are possible signs that your identity, if not your SSN, is in jeopardy, which means it’s time to act right away using the steps below:
File a police report and a Federal Trade Commission (FTC) Identity Theft Report. This will help in case someone uses your Social Security number to commit fraud, since it will provide a legal record of the theft. The FTC can also assist by guiding you through the identity theft recovery process as well. Their site really is an excellent resource.
Get in touch with the fraud department at each of the businesses where you suspect theft has taken place, let them know of your situation, and follow the steps they provide. With your police and FTC reports, you will already have a couple of vital pieces of information that can help you clear your name.
Check your Social Security account to see if someone has gotten a job and used your SSN for employment purposes. Reviewing earnings associated with your SSN can uncover fraudulent use. You can also contact the Social Security Fraud Hotline at (800) 269-0271 or reach out to your local SSA office for further, ongoing assistance. Likewise, contact the Internal Revenue Service at (800) 908-4490 to report the theft and help prevent someone from submitting a tax return in your name.
As we’ve talked about in some of my other blog posts, identity theft can be a long-term problem where follow-up instances of theft can crop up over time. However, there are a few steps you can take to minimize the damage and ensure it doesn’t happen again. I cover several of those steps in detail in this blog here, yet let’s take a look at a few of the top items as they relate to SSN theft:
By placing a fraud alert, you can make it harder for thieves to open accounts in your name. Place it with one of the three major credit bureaus (Experian, TransUnion, Equifax), and they will notify the other two. During the year-long fraud alert period, it will require businesses to verify your identity before issuing new credit in your name.
A full credit freeze is in place until you lift it and will prohibit creditors from pulling your credit report altogether. This can help stop thieves dead in their tracks since approving credit requires pulling a report. However, this applies to legitimate inquires, including any that you make, like opening a new loan or signing up for a credit card. If that’s the case, you’ll need to take extra steps as directed by the particular institution or lender. Unlike the fraud alert, you’ll need to notify each of the three major credit bureaus (Experian, TransUnion, Equifax) when you want the freeze lifted.
Once every 12 months, you can access a free credit report from Experian, TransUnion, and Equifax. (And as of this writing during the pandemic, this can be done for free on a weekly basis, which is great news.) Doing so will allow you to spot any future discrepancies and offer you options for correcting them.
Using a service to help protect your identity can monitor several types of personally identifiable information and alert you of potentially unauthorized use. Our own Identity Protection Service will do all this and more, like offering guided help to neutralize threats and prevent theft from happening again. You can set it up on your computers and smartphone to stay in the know, address issues immediately, and keep your identity secured.
Of all the forms of identity theft, the theft of a Social Security Number is certainly one of the most potentially painful because it can unlock so many vital aspects of your life. It’s uniquely you, even more than your name alone – at least in the eyes of creditors, banks, insurance companies, criminal records, etc. Your SSN calls for extra protection, and if you have any concerns that it may have been lost or stolen, don’t hesitate to spring into action.
The post How to Report Identity Theft to Social Security appeared first on McAfee Blog.

When it comes to identity theft, trust your gut when something doesn’t feel right. Follow up. What you’re seeing could be a problem.
A missing bill or a mysterious charge on your credit card could be the tip of an identity theft iceberg, one that can run deep if left unaddressed. Here, we’ll look at several signs of identity theft that likely need some investigation and the steps you can take to take charge of the situation.
Unfortunately, it can happen in several ways.
In the physical world, it can happen simply because you lost your wallet or debit card. However, there are also cases where someone gets your information by going through your mail or trash for bills and statements. In other more extreme cases, theft can happen by someone successfully registering a change of address form in your name (although the U.S. Postal Service has security measures in place that make this difficult).
In the digital world, that’s where the avenues of identity theft blow wide open. It could come by way of a data breach, a thief “skimming” credit card information from a point-of-sale terminal, or by a dedicated crook piecing together various bits of personal information that have been gathered from social media, phishing attacks, or malware designed to harvest information. Additionally, thieves may eavesdrop on public Wi-Fi and steal information from people who’re shopping or banking online without the security of a VPN.
Regardless of how crooks pull it off, identity theft is on the rise. According to the Federal Trade Commission (FTC), identity theft claims jumped up from roughly 650,000 claims in 2019 to nearly 1.4 million in 2020—practically double. Of the reported fraud cases where a dollar loss was reported, the FTC calls out the following top three contact methods for identity theft:
However, phone calls, texts, and email remain the most preferred contact methods that fraudsters use, even if they are less successful in creating dollar losses than malicious websites, ads, and social media.
Identity thieves leave a trail. With your identity in hand, they can charge things to one or more of your existing accounts—and if they have enough information about you, they can even create entirely new accounts in your name. Either way, once an identity thief strikes, you’re probably going to notice that something is wrong. Possible signs include:
As you can see, the signs of possible identity theft can run anywhere from, “Well, that’s strange …” to “OH NO!” However, the good news is that there are several ways to check if someone is using your identity before it becomes a problem – or before it becomes a big problem that gets out of hand.
The point is that if you suspect fraud, you need to act right away. With identity theft becoming increasingly commonplace, many businesses, banks, and organizations have fraud reporting mechanisms in place that can assist you should you have any concerns. With that in mind, here are some immediate steps you can take:
Whether you spot a curious charge on your bank statement or you discover what looks like a fraudulent account when you get your free credit report, let the bank or business involved know you suspect fraud. With a visit to their website, you can track down the appropriate number to call and get the investigation process started.
Some businesses will require you to file a local police report to acquire a case number to complete your claim. Even beyond a business making such a request, filing a report is still a good idea. Identity theft is still theft and reporting it provides an official record of the incident. Should your case of identity theft lead to someone impersonating you or committing a crime in your name, filing a police report right away can help clear your name down the road. Be sure to save any evidence you have, like statements or documents that are associated with the theft. They can help clean up your record as well.
The FTC’s identity theft website is a fantastic resource should you find yourself in need. Above and beyond simply reporting the theft, the FTC can provide you with a step-by-step recovery plan—and even walk you through the process if you create an account with them. Additionally, reporting theft to the FTC can prove helpful if debtors come knocking to collect on any bogus charges in your name. You can provide them with a copy of your FTC report and ask them to stop.
You can place a free one-year fraud alert with one of the major credit bureaus (Experian, TransUnion, Equifax), and they will notify the other two. A fraud alert will make it tougher for thieves to open accounts in your name, as it requires businesses to verify your identity before issuing new credit in your name.
A credit freeze goes a step further. As the name implies, a freeze prohibits creditors from pulling your credit report, which is needed to approve credit. Such a freeze is in place until you lift it, and it will also apply to legitimate queries as well. Thus, if you intend to get a loan or new credit card while a freeze is in place, you’ll likely need to take extra measures to see that through. Contact each of the major credit bureaus (Experian, TransUnion, Equifax) to put a freeze in place or lift it when you’re ready.
This can run the gamut from closing any false accounts that were set up in your name, removing bogus charges, and correcting information in your credit report such as phony addresses or contact information. With your FTC report, you can dispute these discrepancies and have the business correct the record. Be sure to ask for written confirmation and keep a record of all documents and conversations involved.
If you receive a notice from the IRS that someone used your identity to file a tax return in your name, follow the information provided by the IRS in the notice. From there, you can file an identity theft affidavit with the IRS. If the notice mentions that you were paid from an employer you don’t know, contact that employer as well and let them know of possible fraud—namely that someone has stolen your identity and that you don’t truly work for them.
Also, be aware that the IRS has specific guidelines as to how and when they will contact you. As a rule, they will most likely contact you via physical mail delivered by the U.S. Postal Service. (They won’t call or apply harassing pressure tactics—only scammers do that.) Identity-based tax scams are a topic all of their own, and for more on it, you can check out this article on tax scams and how to avoid them.
Another downside of identity theft is that it can mark the start of a long, drawn-out affair. One instance of theft can possibly lead to another, so even what may appear to be an isolated bad charge on your credit card calls for keeping an eye on your identity. Many of the tools you would use up to this point still apply, such as checking up on your credit reports, maintaining fraud alerts as needed, and reviewing your accounts closely.
With all the time we spend online as we bank, shop, and simply surf, we create and share all kinds of personal information—information that can get collected and even stolen. The good news is that you can prevent theft and fraud with online protection software, such as McAfee+ Ultimate.
With McAfee+ Ultimate you can:
In all, it’s our most comprehensive privacy, identity, and device protection plan, built for a time when we rely so heavily on the internet to go about our day, whether that’s work, play, or simply getting things done.
Realizing that you’ve become a victim of identity theft carries plenty of emotion with it, which is understandable—the thief has stolen a part of you to get at your money, information, and even reputation. Once that initial rush of anger and surprise has passed, it’s time to get clinical and get busy. Think like a detective who’s building – and closing – a case. That’s exactly what you’re doing. Follow the steps, document each one, and build up your case file as you need. Staying cool, organized, and ready with an answer for any questions you’ll face in the process of restoring your identity will help you see things through.
Once again, this is a good reminder that vigilance is the best defense against identity theft from happening in the first place. While there’s no absolute, sure-fire protection against it, there are several things you can do to lower the odds in your favor. And at the top of the list is keeping consistent tabs on what’s happening across your credit reports and accounts.
The post Top Signs of Identity Theft appeared first on McAfee Blog.

What was the first online service that you signed up for? Perhaps it was your middle school email address (“soccerloveR1450@hotmail.com” anyone?) or your very first Tumblr or Myspace account. Whatever it was, it’s likely that you haven’t used these accounts in years — but did you ever actually delete the account?
Over the past decade, you’ve likely collected various online accounts that you no longer use. But just because you stop using an account doesn’t mean that it doesn’t exist — and your data is likely still floating around on the World Wide Web. These old “zombie” accounts haunt your digital graveyard and are easy pickings for cybercriminals.
Today, most websites and apps either require or strongly encourage their visitors to create user accounts. Almost always, exchanging an email address for an exclusive offer seems a fair tradeoff. As a result, consumers quickly accumulate accounts, many of which they may not even remember creating.
According to Digital Guardian, 70% of consumers have more than 10 password-protected online accounts, and 30% have too many to keep track of. These accounts are comprised of free trials, stores that you no longer purchase from, one-time accounts that you create to buy something, gaming platforms, and apps that you only used a few times. While they may have once served a purpose, you no longer need them.
The problem with zombie accounts is that they contain credentials at risk of exposure. Say that you sign up for a free week trial of a meal kit delivery service. When creating your account, you include information like your email address, password, phone number, delivery address, and credit card information. Once your trial expires, you decide not to sign up for a membership, but your account information remains online. If the meal kit company is involved in a data breach, your personal data could be leaked and exploited by cybercriminals. And if you happen to reuse the same credentials across multiple accounts, a criminal could use credential stuffing techniques (where they use email and password combinations to hack into online profiles) to break into your other accounts.
So, how can you keep protect your online data and prevent a zombie account apocalypse? Follow these cybersecurity best practices to help keep your information secure:
Don’t remember which accounts you made and no longer use? No worries! If you browse with Google Chrome, check under chrome > settings > passwords. This will show all the accounts and passwords you’ve used and saved. Other browsers like Firefox and Safari have similar settings. If you use a password manager, this will also keep a record of your credentials. Once you’ve identified the online accounts you no longer used (or completely forgot you had), close the account for good! This may take some patience, as some websites require multiple steps to close an account. But it will be worth knowing that your information is safer from online exposure.
Having a strong, unique password for each of your online accounts helps protect them from credential stuffing. By using different passwords for your online accounts, you can take comfort in knowing that the majority of your data is secure if one of your accounts is vulnerable.
If you realize a company you buy from fell victim to a data breach, start investigating. A tool like McAfee Identity Protection Service can help you monitor multiple email addresses that allow you to see if you were impacted by a breach. If your credentials were potentially exposed, update them on the company’s website immediately.
Multifactor authentication is an online safety measure where more than one method of identity verification is needed to access the valuable information that lies within password-protected accounts. This can prevent a criminal from breaking into your online profile by providing an added layer of security.
McAfee Total Protection will help protect your personal information and privacy and provides identity restoration services and invaluable peace of mind. Ninety-two percent of Canadians are concerned about the protection of their privacy and 37% are extremely concerned, reports the Canadian Centre for Cybersecurity. All it takes is a few changes to your online habits and arming yourself with the right tools to feel secure about your online presence.
The post Don’t Let Old Accounts Haunt You: How to Maintain Your Digital Graveyard appeared first on McAfee Blog.

When you’re online, the world is at your fingertips. You can do amazing things like stream the latest movies while they’re still in theaters! Or you can enjoy the convenience of online shopping and avoiding the DMV by renewing your driver’s license remotely. This is possible because we’re able to communicate with these organizations through many different channels and we trust them. Unfortunately, many bad actors have taken advantage of this trust and the ease of communication to up their game when it comes to social engineering.
What is social engineering? One of the more famous examples of social engineering was the Nigerian Prince email scam. In this example, hackers relied on a novel, too-good-to-be-true story of a prince looking to transfer some of his fortune if only he could use your bank account number. The Nigerian Prince is a running joke these days, the internet version of “if you believe that, then I have a bridge to sell you,” but its original success made scammers realize they were onto something big.
Modern social engineering campaigns closely resemble communications from legitimate organizations. They’re carefully designed, may be grammatically correct, and appear in completely plausible scenarios. However, they’re all after the same thing – information to gain access to an organization or individual’s accounts.
Phishing is a type of social engineering that uses email or websites to convince people to give up their personal information, under the guise of a plausible reason. Instead of a Nigerian prince asking for a bank account number, an email posing as your bank may ask for you to confirm your account information. Often these emails are tied to circumstances that demand your attention and reflect a sense of urgency. Needless to say, many recent phishing scams have played into COVID-19 pandemic fears and economic concerns. Here are a few other scams related to phishing to watch out for:
First, does the message you’ve received contain any of the following:
If so, check for these tell-tale signs used by phishing scams
If the email you’re suspicious of has several of the above warning signs, chances are you’ve spotted a phishing email. Still not sure what we’re talking about? Check in your email’s spam and you’ll probably see some obvious examples of phishing right away. Spam doesn’t catch everything though, and the best phishing scams can be very difficult to separate from the legitimate emails. With that in mind, we’ve pulled together some safety precautions that will help keep you safer, from phishing emails.
The post Staying safer online from phishing and other attacks appeared first on McAfee Blog.

A good time to check if someone is using your identity is before it even happens.
One of identity theft’s several downsides is how people discover they’ve become a victim in the first place—by surprise. They go to rent an apartment, open a line of credit, or apply for financing, only to discover that their finances or reputation has taken a hit because of identity thief.
And those hits add up, particularly when you look at the dollars involved. In 2020, the Federal Trade Commission (FTC) reported $3.3 billion in financial losses from 4.7 million reported cases of fraud, a 45% increase over the year prior. Of those reports, identity theft was the leading fraud category, accounting for 29% of fraud incidents.
Plenty. Depending on the type and amount of information an identity thief gets their hands on, they can harm your finances and reputation in several ways, including:
Rather than ending up with a rude and potentially costly surprise of your own, you can get ahead of thieves by checking to see if someone is using your identity before it’s a problem or before it really takes root.
Major data breaches that expose personal information seem to hit the headlines with some regularity, not to mention the many, many more that don’t get national or international press coverage. Most recently we have the Neiman Marcus breach, where this major retailer alerted 4.6 million customers that “an unauthorized party obtained personal information associated with certain Neiman Marcus customers’ online accounts.”
And as it is with many such breaches, it took quite some time before the theft of information was discovered. Per Neiman Marcus, it’s believed that the breach occurred in May 2020 and only discovered in September of 2021. Potentially compromised information included:
Whether or not you have reason to suspect that your information got caught up in this recent large-scale breach, it serves as a good reminder that any time is the right time to check up on your identity. Acting now can save headaches, potentially big headaches, later.
Quite a bit of identity theft prevention begins with taking stock of the accounts and services you have in your name. This ranges anywhere from bank accounts to public utilities and from credit cards to loans, all of which contain varying degrees of personal information about you. With a sense of where your personal identity is being used, you can better look for instances where it’s being misused.
Ways you can spot for possible identity theft include:
If you stop receiving a bill that normally comes to you, such as a utility bill or for a department store credit card, that could be a sign that a thief has changed the mailing address and has potentially hijacked your identity.
This is rather straightforward, yet it reminds us how important it is to look at our statements closely. Charges that you didn’t ring up or that seem slightly higher than normal are a surefire sign that you should follow up with the bank or company involved and let them know of possible fraud.
In the U.S., you have annual access to free credit reports from the major credit reporting agencies. Not only will this give you a sense of your credit score, but it will also show the credit that’s open in your name, along with addresses associated with your identity. Spotting an account that you haven’t signed up for or seeing an address of a residence that you’re not renting are other common signs that your identity may have been compromised.
With the number of accounts many of us have these days, a credit monitoring service can help you stay on top of what’s happening in your name. Often offered through banks, credit unions, and even insurance providers, credit monitoring can alert you in several instances, including:
Overall, credit monitoring can act as another set of eyes for you and spot potential identity issues. Different services provide different levels of monitoring, so consider reviewing a few options to find the one that works best for you.
One like our own Identity Protection Service will monitor several types of personally identifiable information, alert you of potentially stolen personal info, and offer guided help to neutralize the threat—in addition to offering several preventative steps to help keep theft from happening in the first place. With this set up on your computers and smartphone you can stay in the know and address issues immediately.
Along with keeping an eye on what’s happening with your identity online and elsewhere, there are a few more things you can do to make it tougher for thieves to steal your identity.
Given all the banking and shopping we do on our computers and phones, installing and using comprehensive online protection software is a must these days. It puts several layers of security in place, such as creating complex passwords automatically, shielding credit card info from prying eyes, and protecting your privacy and data online by connecting with a VPN. In short, online protection software acts as a solid first line of defense.
As mentioned above, comprehensive online protection software often includes a password manager that can generate strong, unique passwords for each of your accounts and remember them for you. It’s extra protection that makes life a lot easier for you by managing all the accounts you’re juggling. Also, use MFA (multi-factor authentication) on the accounts that give you the option, which makes it harder for a thief to crack your accounts with a password alone.
Sensitive documents come in all forms. Top-of-the-line examples include things like tax returns, bank statements, and financial records. Yet there are also things like your phone and utility bills, statements from your doctor’s office, and offers that come to you via mail. Together, these things can contain personal information such as account numbers, your full Social Security Number, the last four digits of your Social Security Number (which can still be useful to thieves), and other information that may uniquely identify you. You’ll want to dispose of sensitive documents like these so that they can’t be harvested by hackers.
For physical documents, consider the low-cost investment of a paper shredder to help ensure they don’t fall into the wrong hands when you are done with them. (And let’s face it, they’re fun to use!) For digital documents, simply deleting a file is not enough – online protection software is a great resource that often includes a digital document shredder, designed to render the data practically unusable when you’re ready to trash the file.
Your Social Security Number is one of the most prized possessions a thief can run away with because it is so closely associated with you and things like your tax returns, employment, and so on. Keep it stored in a safe location rather than on your person or in your wallet. Likewise, be careful about giving out your SSN. While organizations like the IRS, your bank, and employer require it, there are other organizations who do not—but may ask for it anyway. (Doctor’s offices are a prime example.) If you get such a request, ask them what they intend to use it for and then ask if another form of identification will work instead.
Phishing attacks are one of the primary ways identity thieves steal personal information. Whether they come via a direct message, on social media, or through email, text, or phone calls, thieves use them to harvest your personal info by posing as a legitimate organization—such as in this recent IRS phishing scam. Phishing is a topic all unto itself, and you can check out this quick read to see how you can spot phishing scams and protect yourself from them.
Like any criminal, identity thieves do their dirtiest work in the shadows—quietly stealing money under your nose, or worse, as we outlined above. By shining a light on your identity and keeping regular track of what’s happening with it, you can spot unusual activity right away. Even the small stuff is important. A co-worker of mine once saw an incorrect address listed on his credit report. Turned out, that address was used to rack up several large charges at a retailer, which he was able to fix with the aid of the credit reporting agency and the retailer in question.
No doubt about it. Identity theft is indeed on the rise, and your best bet to avoid such a nasty surprise is to keep an eye on your digital identity the same way you keep an eye on your actual wallet.
The post How to Check if Someone is Using Your Identity appeared first on McAfee Blog.

When it comes to crime, what do people worry about most? Having their car stolen? A break-in while they’re not at home? Good answers, but not the top answer by a long shot. In this U.S.-based survey, hacker-related crime weighed in at 72%, with a home burglary at 35% and auto theft at 34%, indicating that people’s concerns about cybercrime are very much front and center.
The good news is that plenty of cybercrime can be prevented, or at least made less likely, provided you protect yourself online, much in the same way you take steps to protect your car or home. And that’s the focus of this year’s Cybersecurity Awareness Month. With the theme of “Do Your Part. #BeCyberSmart,” it reminds us of how we can take charge of our own safety—the ways we can look out for ourselves and others as we enjoy our time online.
Throughout October, we’re participating in Cybersecurity Month here on our blogs and across our social media channels, posting a host of ways that you can help keep cybercrooks away from your digital doorstep. Each week, we’ll tackle a different aspect of online protection:
Maybe it comes as no surprise to hear it, yet one recent study shows the average person spends nearly eight hours a day online. With that, we’re taking this week to focus on the family, how they spend their time online and how they can be safer when they do.
Whether they come by email, text, or DM, phishing attacks account for the most common types of reported cybercrime, according to the FBI Internet Crime Complaint Center. This week, we’ll show you how you can indeed fight the phish!
This sentiment sums up the best of the internet in so many ways. Getting out there, discovering, catching up with friends online. Our focus this week is helping you enjoy it all without any of the bad apples out there spoiling your fun.
We wrap it up with a look at some of the top priorities so everyone in the family can #BeCyberSmart—online banking, app scams, privacy, identity theft, and more—along with plenty of straightforward tips that can help you stay safer.
We hope our posts throughout Cybersecurity Awareness Month help you get a little sharper and feel a little safer so you can enjoy your time online, free from hassles or headaches. Look for more from us throughout October!
The post Cybersecurity Awareness Month: Taking Charge of Your Safety Online appeared first on McAfee Blog.

Customers often ask us some version of this question. It’s a good question and in the past, there was no direct answer – only recommendations. For instance, we recommend online protection that goes beyond antivirus to include identity and privacy protection, as well as promoting safety best practices like using multi-factor authentication. We wondered if there was a simpler and easier way to advise customers how to better protect themselves.
A recent survey shows how important online security has become to consumers. We found that 74% of you have concerns about keeping your information private online. 57% want to be more in control of their personal info online. And, since the pandemic started, 47% of online consumers feel unsafe compared to 29%. Simply put, customers are more conscious of their safety online than ever before, and eager to play an active role in their protection.
It’s time for a new approach – meet the Protection Score.
If you’re thinking this looks like a credit, fitness, sleep, or any of the other scores we now use to visualize and quantify aspects of our life, you’re on the right track.
Your personalized Protection Score is a measure of your security online. The higher your score, the safer you are online. Your score will highlight any weaknesses in your security and help you fix them with easy step-by-step instructions. We’ll also let you know which features haven’t been setup so you can get the most out of your protection.
When we developed Protection Score the idea was to give customers a simple solution to better protect themselves and get the most from their subscription, including security tips to protect their identity, privacy, and devices, while also improving their online habits. We wanted it to be easy for anyone to:
Now that we’ve talked about Protection Score generally, let’s look at how it works in practice. Your score is based on a few things, including setting up your McAfee protection, strengthening your security with our safety recommendations, and ensuring your personal info is safely monitored with Identity Protection.
For example, if your information is exposed in a data breach your score may drop, but you can improve it by following our easy-to-follow remediation steps. Once you’ve completed those steps your score will go back up and you can be confident knowing you’re better protected online.
A perfect score does not mean you’re perfectly safe, but it does mean that you’re doing an excellent job of preventing and managing risks.
Your Protection Score is a great way to understand how safe you are at a glance. Additionally, improving your score ensures your life online is being protected by many of the safety features and benefits McAfee has to offer. For instance, the subscriber, John Smith, can see they’re fairly safe based on their score. However, it isn’t a perfect score and there are a few actions they could still take to improve it. In this case, adding their email and phone number to dark web monitoring – a crucial step in protecting their personally identifiable information online.

Protection Score can be easily accessed* from your browser of choice on any device so you can review our guidance and take steps to improve your score from wherever you are. McAfee’s Protection Score is a first for the cybersecurity industry, but we’re not stopping there. We’re going to continue to improve the feature by adding more personalization and accessibility so you can enjoy your life online knowing exactly how protected you are.
*Note that Protection Score is currently live in the US, Canada, Brazil, Australia, New Zealand, Japan, UK, Germany, France, Spain, and Italy.
The post Stay on top of your online security with our Protection Score appeared first on McAfee Blog.

You open your laptop and see an email from a healthcare organization that you don’t recognize. The subject line reads “URGENT – PROOF OF VACCINATION NEEDED.” Impulsively, you open the email and click on the link. You’re redirected to a website that asks you to enter your name, date of birth, Social Security Number, and a photo of your vaccine card. Scrambling, you enter the information and click “Submit.”
As you continue to adapt your lifestyle to the ongoing public health precautions, it’s important to consider how these precautions can affect your digital health as well. According to the Washington Post, pandemic-related email scams are on the rise, especially with the delta variant surging. McAfee Labs’ April 2021 Threats Report found that COVID-19-themed cyber-attack detections increased 114% in Q3 and Q4 of 2020. Research also shows that COVID-19 phishing attempts in June 2021 increased 33%. With confusion around proof of vaccination and booster shots emerging, it’s likely that cybercriminals will take advantage.
As employers re-evaluate their return-to-office plans, some are requiring proof of vaccination or negative COVID-19 test results. This creates a new opportunity for cybercriminals to exploit. Researchers have uncovered phishing emails disguised as human resources departments asking recipients to submit personally identifiable information about their vaccination status. Many of these types of emails contain links to fake login pages. If the recipient proceeds with entering their credentials and personal data, cybercriminals can use the consumer’s data to conduct credential stuffing attacks and hack their online profiles. This could lead to credit card fraud, data extraction, wire transfers, identity theft, and more.
With various organizations contacting individuals about potential virus exposure, testing and vaccination information, and other public health news, it’s important to remember that some of these organizations may not be what they say they are. That email from the healthcare company you’ve never heard of? It’s probably a cybercriminal in disguise. Some hackers are impersonating public health and government organizations, sending phishing emails in the hopes of collecting users’ names, Social Security Numbers, birthdates, and other valuable data. Criminals tend to sell this information on the dark web, making a profit while the recipients’ online safety is put in jeopardy.
As more news and recommendations for dealing with the pandemic continues to emerge, it’s important that you stay vigilant when it comes to protecting your digital wellness. After all, it’s just as important as your physical wellness! In addition to staying updated on the latest COVID-19-related scams, follow these tips to keep yourself secure from online threats like phishing scams:
If you receive an email or text message from an organization that you’re unfamiliar with, do some sleuthing. Verify that the organization is legitimate. The same goes if you receive a message from an entity that you recognize. If your “HR department” or a “doctor’s office” contacts you and asks for personal information, reach out to them directly instead of replying directly or clicking on any links in the message. This can prevent you from interacting with a hacker in disguise.
Oftentimes, hackers will use a URL for their spoofed website that is just one character off from the legitimate site. Before clicking on any website from an email asking you to act, hover over the link with your cursor. This will allow you to preview the URL and identify any suspicious misspellings or grammatical errors before navigating to a potentially dangerous website.
Multi-factor authentication requires that users confirm a collection of things to verify their identity—usually something they have, and a factor unique to their physical being—such as a retina or fingerprint scan. This can prevent a cybercriminal from using credential-stuffing tactics (where they will use email and password combinations to hack into online profiles) to access your network or account if your login details were ever exposed during a data breach and sold on the dark web.
An identity theft alert service warns you about suspicious activity surrounding your personal information, allowing you to jump to action before irreparable damage is done. McAfee Total Protection not only keeps your devices safe from viruses but gives you the added peace of mind that your identity is secure, as well.
The post How Fraudsters Are Fooling Users With This Proof of Vaccination Phishing Scam appeared first on McAfee Blog.

Have you ever come across a website that just didn’t look quite right? Perhaps the company logo looked slightly misshapen, or the font seemed off-brand. Odds are, you landed on a phony version of a legitimate corporation’s website—a tried and true tactic relied on by many cybercriminals.
A fake login page is essentially a knock-off of a real login page used to trick people into entering their login credentials, which hackers can later use to break into online accounts. These websites mirror legitimate pages by using company logos, fonts, formatting, and overall templates. Depending on the attention to detail put in by the hackers behind the imposter website, it can be nearly impossible to distinguish from the real thing. Consequentially, fake login pages can be highly effective in their end goal: credential theft.
How do these pages get in front of a consumer in the first place? Typically, scammers will target unsuspecting recipients with phishing emails spoofing a trusted brand. These emails may state that the user needs to reset their password or entice them with a deal that sounds too good to be true. If the consumer clicks on the link in the email, they will be directed to the fake login page and asked to enter their username and password. Once they submit their information, cybercriminals can use the consumer’s data to conduct credential stuffing attacks and hack their online profiles. This could lead to credit card fraud, data extraction, wire transfers, identity theft, and more.
Scammers have recently targeted Canadians with attacks leveraging fake login pages to harvest personal data. For example, criminals preyed on employees who were expecting COVID-19 relief grants in the form of the CERB (Canada Emergency Response Benefit). These funds were sent via an electronic transfer from Interac, a legitimate Canadian interbank network. However, a phishing campaign spoofing Interac’s e-transfer service circulated emails claiming that the Canada Revenue Agency (CRA) made a CERB deposit of $1,957.50 CAD.
These emails directed recipients to a fake CRA login page, which then redirected to a phony Interac e-transfer site where users were asked to select their personal bank. From there, the recipient was asked to enter their username, card number, password, security questions and answers for their online banking profile, and other personally identifiable information—providing all the information a criminal would need to hack into the user’s bank account.
If you Google “fake login pages,” you will quickly find countless guides on how to create fake websites in seconds. Ethical concerns aside, this demonstrates just how common vector spoofed websites are for cyberattacks. While it has been easier to distinguish between real and fake login pages in the past, criminals are constantly updating their techniques to be more sophisticated, therefore making it more difficult for consumers to recognize their fraudulent schemes.
One reason why fake login pages are so effective is due to inattentional blindness, or failure to notice something that is completely visible because of a lack of attention. One of the most famous studies on inattentional blindness is the “invisible gorilla test.” In this study, participants watched a video of people dressed in black and white shirts passing basketballs. Participants were asked to count the number of times the team in white passed the ball:
Because participants were intently focused on counting the number of times the players in white passed the ball, more than 50% failed to notice the person in the gorilla costume walking through the game. If this is the first time you’ve seen this video, it’s likely that you didn’t notice the gorilla, the curtain changing color from red to gold, or the player in black leaving the game. Similarly, if you come across a well-forged login page and aren’t actively looking for signs of fraud, you could inherently miss a cybercriminal’s “invisible gorilla.” That’s why it’s crucial for even those with phishing training to practice caution when they come across a website asking them to take action or enter personal details.
The most important defense against steering clear of fake login pages is knowing how to recognize them. Follow these tips to help you decipher between a legitimate and a fake website:
Most fake login pages are circulated vis phishing messages. If you receive a suspicious message that asks for personal details, there are a few ways to determine if it was sent by a phisher aiming to steal your identity. Phishers often send messages with a tone of urgency, and they try to inspire extreme emotions such as excitement or fear. If an unsolicited email urges you to “act fast!” slow down and evaluate the situation.
Oftentimes, hackers will use a URL for their spoofed website that is just one character off from the legitimate site, such as using “www.rbcr0yalbank.com” versus “www.rbcroyalbank.com.” Before clicking on any website from an email asking you to act, hover over the link with your cursor. This will allow you to preview the URL and identify any suspicious misspellings or grammatical errors before navigating to a potentially dangerous website.
HTTPS, or Hypertext Transfer Protocol Secure, is a protocol that encrypts your interaction with a website. Typically, websites that begin with HTTPS and feature a padlock in the top left corner are considered safer. However, cybercriminals have more recently developed malware toolkits that leverage HTTPS to hide malware from detection by various security defenses. If the website is secured with HTTPS, ensure that this isn’t the only way you’re analyzing the page for online safety.
Multi-factor authentication requires that users confirm a collection of things to verify their identity—usually something they have, and a factor unique to their physical being—such as a retina or fingerprint scan. This can prevent a cybercriminal from using credential-stuffing tactics (where they will use email and password combinations to hack into online profiles) to access your network or account if your login details were ever exposed during a data breach.
An identity theft alert service warns you about suspicious activity surrounding your personal information, allowing you to jump to action before irreparable damage is done. McAfee Total Protection not only keeps your devices safe from viruses but gives you the added peace of mind that your identity is secure, as well.
The post How to Spot Fake Login Pages appeared first on McAfee Blog.

T-Mobile, the popular US mobile phone service provider, recently confirmed a data breach affecting 7.8 million current customers and 40 million records from past or prospective customers. The stolen data included customer names, dates of birth, social security numbers, and driver’s license information. Fortunately, subscriber credit card information and other financial details were not affected in the breach.
Even though financial data was spared in the breach, the types of information stolen, along with the vast volume of affected subscribers mean that all T-Mobile subscribers should take immediate action to secure their identities and accounts online.
This is the immediate step all affected subscribers should take.
As part of T-Mobile’s response, they are offering an identity protection service exclusively to all affected customers, free for two years. This identity protection service gives customers the ability to monitor personal info, including your SSN, bank account numbers, debit cards, email addresses, phone numbers, and more. If info is found on the dark web, customers will receive guidance to help secure online accounts. Should identity theft occur, the identity protection service includes fraud resolution support and identity theft insurance for peace of mind. The free 24 months of identity protection will be delivered directly by T-Mobile. The company is also encouraging customers to sign up for their Account Takeover Protection service.
One lesser-known type of data stolen in the breach was International Mobile Equipment Identity (IMEI) numbers, which allow individual devices to be identified on a mobile network. Access to IMEI numbers could enable SIM-swap attacks which make account takeovers possible. With an account takeover, two-factor authentication through text message becomes vulnerable, allowing hackers potential access to bank accounts, among others. App-based multi-factor authentication, using a solution like Google’s Authenticator, allows you to authenticate your identity from other devices, instead of having authentication tied to your mobile phone number.
T-Mobile will be contacting impacted customers directly. However, cybercriminals and scammers may also take advantage of this data breach to scam people using email. They will often pose as major corporations or other trustworthy entities to trick you into willingly providing information like website login credentials or, even worse, your credit card number. We’ve provided additional information here to help you to recognize legitimate emails.
In its simplest form, your digital identity is made up of a whole host of things that can be traced back to you and who you are. This includes email accounts, cell phone numbers, bank accounts, your tax ID, and more. Read our additional tips to protect your digital identity.
For regular updates and official news from T-Mobile, visit their Newsroom blog here.
The post T-Mobile’s data breach exposes the personal data of 40 million appeared first on McAfee Blog.

Over the past few years, food delivery apps have made it easy for people to get their favorite cuisines brought to their doorsteps. In 2020, consumers grew more accustomed to the convenience of ordering take-out when dining in at restaurants was no longer an option. But as we look ahead into 2022, this trend is here to stay. According to a new report by ResearchAndMarkets, the global online food delivery services market will grow from $115.07 billion in 2020 to $126.91 billion by the end of 2021.
To get the latest deals and news from their favorite restaurants, many consumers opt in to receiving marketing emails from the dining locations they frequent the most. One such restaurant is the popular fast-food chain Chipotle Mexican Grill, which has added 22.9 million consumers to its loyalty program since launching two years ago. But customers who signed up to receive emails from Chipotle may have more to consider than whether they choose queso or guacamole. According to Bleeping Computer, Chipotle’s email vendor Mailgun was recently breached, which allowed hackers to take over the company’s email marketing efforts and reach out to unsuspecting customers.
Let’s look at how this threat emerged and what consumers can do to help protect themselves from phishing and live a happy and safe digital life online.
Many restaurant chains like Chipotle utilize a third-party vendor to engage with customers who sign up to receive the latest updates. Chipotle uses Mailgun to help send, receive, and track its marketing emails. However, bad actors were able to hack into Chipotle’s Mailgun account, allowing them to send out phishing emails to recipients.
Under the guise of the Chipotle restaurant chain, cybercriminals reportedly sent out at least 120 malicious emails within a three-day period, luring Chipotle customers to malicious links. Most of the emails directed the unsuspecting users to credential-harvesting sites, impersonating services like a Microsoft 365 login page. Some messages even included malware attachments.
Although phishing is by no means a new cyberthreat, criminals have made it more difficult to spot scam messages with their increasingly sophisticated tactics. Most scammers disguise themselves as major corporations or other trustworthy entities to trick you into willingly providing information like your website login credentials or, even worse, your credit card number. But in Chipotle’s case, cybercriminals were able to hack into the company’s legitimate email marketing account, making it more difficult for consumers to spot the scam.
As a consumer, what can you do to sidestep these stealthy tactics and continue to enjoy your life online? Follow these tips to help safeguard your security:
While phishing has been around for years, cybercriminals continuously make these scams more sophisticated in the hopes of tricking even the most seasoned online experts. That’s why it’s important to stay up to date on the latest phishing techniques so you know what to look out for. Doing a quick search on recent phishing scams every once in a while will help you better spot these cyberthreats well before you find them in your inbox.
If you receive an email that appears to be from a business you subscribe to, but they are asking you for personal information, stop and think. Don’t click on anything or take any direct action from the message. Cybercriminals know that consumers tend to let their guard down when they think they are communicating with an entity that they trust, so play it safe and never assume anything. Instead, go straight to the organization’s website. This will prevent you from downloading dangerous content from phishing links or forking over money unnecessarily.
If someone sends you a message with a link, hover over the link without actually clicking on it. This will allow you to see a link preview. If the URL looks suspicious, don’t interact with it and delete the message altogether.
Use a security solution, like McAfee Total Protection, which can help protect devices against malware, phishing attacks, and other threats. It includes McAfee WebAdvisor, which can help identify malicious websites.
Now that you know how to spot phishing emails and what to do if you suspect scammers are targeting you, you’re far less likely to fall for these schemes. Remember to be careful with your personal information when you use the internet and err on the side of caution whenever anybody asks you to divulge sensitive details about your identity, finances, or login information – even if the message appears to be from a business you recognize.
The post Chipotle’s Marketing Account Hacked: Protect Yourself From Phishing Lures appeared first on McAfee Blog.

Smart speakers. Banking online. Location tracking. If you are a senior adult, there’s no doubt, the digital leaps and bounds you’re asked to consider each day can be daunting. If you are the child of a senior adult trying to make digital life more accessible, helping your parent consistently stay safe online can also be a challenge.
According to the most recent Pew study on the topic, senior adults continue to become more digitally connected, but adoption rates continue to trail younger users, and digital divides remain. The study also revealed that 77% of older adults needed assistance in learning how to use technology.
As a senior, it’s easy to feel intimidated and even try to avoid technology altogether as a safety plan. However, more healthcare, banking, and retailers become almost 100% digital, opting out of digital life is becoming impossible.
Still, there’s a way forward. As with any challenge, it’s best to begin one step at a time. First, put your stake in the ground by committing to increase your awareness and consistency in the digital realm. Doing so will help you reduce your fear about potential data breaches, malware attacks, or worse, falling prey to an online scam. Here are seven more ways to build upon your privacy path.
1. Consider another layer of protection. Parental controls and antivirus software cover every age and stage of a family’s digital life. Here’s why: 1) If you are a senior and love exploring online but hate bumping into inappropriate content, parental controls will help you keep the fun and block the junk 2) Filtering software also keeps your PC clean and protected from viruses and malware. 3) If you are a caregiver to a senior and notice your parent struggling with online shopping limits, keeping personal information private on social media, or even sharing fake news, parental controls can help by blocking tempting sites.
2. Update and store your passwords. Updating your passwords regularly is an online privacy gamechanger. The only problem? It’s tough to remember all those passwords, so who wants to risk changing them, right? Consider a password manager (find the software packages that have a password manager built-in). Your Password Manager (PM) stores then populates the username and password fields every time you log on to a favorite site or app. Better yet, it makes changing your password an easy task since you don’t need to do any remembering—your PM does it all for you.
3. Use 2-Factor Authentication (2FA). What in the world? 2FA sounds complicated! Don’t worry, it’s not. Opting for 2FA means that before logging onto your account, you will have one more step to verify it’s you logging on. When given this privacy option, take it. Commonly, the 2FA process is a code generated by a smartphone app—no biggie. If you want to try, go to your settings in your favorite apps, such as Google or Facebook, and turn on the 2FA option.
4. Install software updates immediately. Along with strong passwords, updating your software is a front-line defense against identity theft and fraud. Installing software updates (those pesky pop-up notices that are critical to your privacy) is essential in securing your IoT devices, PCs and phones, and the social media, banking, and healthcare portals connected to them.
5. Use a Virtual Private Network (VPN). If we could write this one tip down a hundred times without losing our readers, we surely would. Every senior adult needs a VPN for practical, powerful privacy protection and peace of mind. A VPN keeps credit card and personal info contained in a secure network and away from prying eyes.
6. Fight back with knowledge. Fraudulent emails connected to fraudulent websites can look very legitimate. A secure website will have an “HTTPS” in the browser’s address bar. The “s” stands for “secure.” If the web address or URL is just HTTP, it’s not a secure site. Still unsure? Read reviews of the site from other users before making a purchase. Never send cash, cashier’s check, or a personal check to any online vendor. If purchasing, always use a credit card in case there is a dispute. Stay up-to-date on scams that target seniors specifically. Lately, elder scams have been constructed around COVID, dating apps, tax returns, employment, and, of course, the common military catfish scams.
7. Have fun as you skill up. When trying to boost your digital skills, don’t forget about all the amazing instructional content at your fingertips. A quick search of YouTube will render easy-to-understand videos on how to do just about everything (including install security software, change your router password, secure the smart devices in your home, and how to adjust your privacy settings on any device).
Learning or building a new skill isn’t always easy, but if you stop to think about it, as a senior, you’ve gained so many skills over your lifetime (far more than your juniors). So, practically speaking, building up your tech skills is one is just one more task to ace. So, lean into the challenge, have fun learning, and don’t hesitate to ask for help if you need it.
The post 7 Savvy Ways Senior Adults Can Safeguard Digital Privacy appeared first on McAfee Blogs.

Picture this: you open your MacBook and see an email claiming to be from your favorite online store. In the email, there is an attachment with “important information regarding your recent purchase.” Out of curiosity, you open the attachment without checking the recipient’s email address. The next thing you know, your device is riddled with malware.
Unfortunately, this story is not far from reality. Contrary to popular belief, Apple computers can get viruses, and XLoader has Mac users in their sights.
Let’s break down XLoader’s ‘s origins and how this malware works.
Where Did XLoader Come From?
XLoader originated from FormBook, which has been active for at least five years and is among the most common types of malware. Designed as a malicious tool to steal credentials from different web browsers, collect screenshots, monitor and log keystrokes, and more, FormBook allowed criminals to spread online misfortune on a budget. Its developer, referred to as ng-Coder, charged $49, a relatively cheap price to use the malware, making it easily accessible to cybercriminals.
Although ng-Coder stopped selling FormBook in 2018, this did not stop cybercriminals from using it. Those who had bought the malware to host on their own servers continued to use it, and in turn, quickly noticed that FormBook had untapped potential. In February 2020, FormBook rebranded to XLoader. XLoader can now target Windows systems and macOS devices.
Typically, XLoader is spread via fraudulent emails that trick recipients into downloading a malicious file, such as a Microsoft Office document. Once the malware is on the person’s device, an attacker can eavesdrop on the user’s keystrokes and monitors. Once a criminal has collected enough valuable data, they can make fake accounts in the victim’s name, hack their online profiles, and even access their financial information.
According to recent data, Apple sold 20 million Mac and MacBook devices in 2020. With macOS’s growing popularity, it is no surprise that cybercriminals have set their sights on targeting Mac users. Check out these tips to safeguard your devices and online data from XLoader and similar hacks:
Hackers often use phishing emails or text messages to distribute and disguise their malicious code. Do not open suspicious or irrelevant messages, as this can result in malware infection. If the message claims to be from a business or someone you know, reach out to the source directly instead of responding to the message to confirm the sender’s legitimacy.
Hackers tend to hide malicious code behind the guise of fake websites. Before clicking on an unfamiliar hyperlink, hover over it with your cursor. This will show a preview of the web address. If something seems off (there are strange characters, misspellings, grammatical errors, etc.) do not click the link.
Use a solution like McAfee Total Protection, which can help protect devices against malware, phishing attacks, and other threats. It also includes McAfee WebAdvisor — a tool that identifies malicious websites.
Regardless of whether you use a PC or a Mac, it is important to realize that both systems are susceptible to cyberthreats that are constantly changing. Do your research on prevalent threats and software bugs to put you in a great position to protect your online safety.
XLoader is just the latest example of how the gap between the prevalence of PC versus macOS malware is steadily closing. To better anticipate what threats could be around the corner and how to best combat them, stay updated on all of the latest online safety trends and practice great security habits. This will not only help protect your devices and online accounts but also bring you greater peace of mind.
The post 3 Tips to Protect Yourself From XLoader Malware appeared first on McAfee Blogs.

There’s a lot of misinformation about Virtual Private Networks, what they do, and the security benefits they offer. For this article, I’d like to do some myth-busting about how a VPN actually works and why you should use one.
A VPN is an app that you install on your device to help keep your personal data safe as you browse the internet
You may have heard that VPN apps live on your device and allow you to connect to the internet securely. What that means is, when you turn your VPN app on, your device makes a secure connection to a specialized computer that routes internet traffic, called a VPN server. You also may have heard that your connection is “wrapped in an encrypted tunnel” which means your device and the server share a secure connection so only you can see what you’re doing on the internet.
Every internet connection (like your cable modem) is assigned a unique set of numbers called an IP address, which is tied to information such as geographic location, ISP, etc. A VPN replaces your actual IP address to make it look like you’ve connected to the internet from a different location: the physical location of the VPN server, rather than your real location. This is just one reason why so many people use VPNs. This can be handy when you want to hide from advertising trackers or protect your search history.
To change your IP address, you simply open your VPN app, select the server location you’d like to connect to, and you’re done. You’re now browsing with a new IP address. If you’d like to make sure your IP has changed, open up a browser and search for “What’s my IP address” and click on one of the results.
When to use a VPN really depends on what you want it for. For example, 39% of users understand public Wi-Fi is unsafe but still do sensitive things, like banking or shopping on public WiFi, so using a VPN when you’re at the airport, or a café is a great use case.
As I mentioned before, a lot of people use a VPN for privacy reasons, like stopping advertisers from tracking them. Searches you perform, or websites you visit won’t be trackable, which means you’ll be able to surprise your spouse with a vacation you researched and planned on a computer you both use. Targeted ads could spoil things if your spouse is bombarded with ads for plane tickets and hotels while they browse.
A VPN protects your search history through the secure connection you share. When you search for a website, or type a URL into your navigation bar, your device sends something called a DNS request, which translates the website into the IP address of the web server; this is how your browser can find the website and serve its content to you. By encrypting your DNS requests, a VPN can hide your search habits and history from those that might use that info as part of building a profile of you. This type of info could be used in a wide variety of ways, from legitimately serving targeted ads to nefarious social engineering.
A VPN can protect your identity by blocking online trackers from following you around the internet. With your VPN on, trackers will think all of your browsing is coming from a different device in a different location. This throws off the profile advertisers try to build because they think you’re someone else.
Another way a VPN can protect your identity is by preventing some types of hacking. Stopping attacks on public WiFi where a bad actor tries to get between you and the website you’re visiting, is just one way VPNs can help. It’s called a Man-in-the-Middle attack, but that’s a subject for another article.
No, a VPN cannot make you anonymous. They help secure what you’re doing, but your ISP still knows when you’re using the internet. They just can’t see what you’re doing, what sites you visit, or how long you’ve been on a site.
Private browsing modes can help protect your privacy, but they’re useful if you share a device with other people and you don’t want them to see your search history. You can read all about the differences in the article I wrote a little while ago.
Apple’s Private Relay is currently in Beta and will be available with an iCloud+ subscription for Safari users on iOS and macOS soon. Private Relay is similar to a VPN in that it changes your IP address so websites you visit can’t tell exactly where you are.
When you turn Private Relay on, your device connects to a server that sends your browsing data to a second server, before it travels through the internet. The reason for the double hop is that first server gives you a new IP address, to make you harder to track, while the second server hides that information from the website you’re browsing. The first server only knows your original IP address, while the second server only knows what you’re browsing, but not your IP.
Private Relay only works with Safari on iOS and macOS. Even if you are using an Apple device, a VPN is still a good idea because it will protect the information that your device sends outside of Safari.
If you’re already a McAfee Total Protection subscriber, you have access to unlimited VPN usage. Protect your personal information, like your banking information and credit cards, from prying eyes with McAfee Total Protection’s Secure VPN. If you haven’t already signed up, now’s the perfect time. McAfee Total Protection provides security for all your devices, giving you peace of mind while you shop, bank, and browse online.
The post What is a VPN and Can it Hide My IP Address? appeared first on McAfee Blogs.

How many rooms in your home contain a smart device? From Peloton bikes to showerheads with Bluetooth speakers, smart home technology is rapidly making its way into every room in every household. In fact, the number of smart households (those that contain smart home technology) in the U.S. is expected to grow to 77.05 million by 2025. But with new technology comes new challenges.
Many product designers rush to get their smart devices to market, treating security as an afterthought and consequentially creating an easy access point for criminals to exploit. Once a hacker taps in to a user’s home network, they could potentially gain access to all the devices connected to the network. And many consumers, amazed by the appliances’ efficiency, are unaware of the risks of interconnectivity. So, how can families prevent criminals from taking peeks into their home?
Let’s take a tour through an average smart home and uncover the security implications of the various devices in each room.
Believe it or not, the security risks of a smart home often apply before you even step foot inside the house. Approximately 21 million U.S. homes have professionally monitored security systems. However, these systems are not immune to hacks. One popular security camera system experienced a series of intrusions where hackers were able to communicate with residents, making inappropriate comments, taunting children, and even demanding a ransom payment for the hacker to leave the system. Some users of another security camera system experienced similar intrusions, with hackers playing vulgar music and cranking the homeowners’ heat up to 90 degrees.
Security cameras are just the beginning. Users control mowers, smart sprinklers, and other outdoor devices remotely with smartphone apps. Although they are meant to make consumers’ lives more convenient, outdoor devices with embedded computers could be at the greatest risk of attack, according to professor of computer science and cybersecurity expert, Dr. Zahid Anwar.
Outdoor devices like garage door openers, wireless doorbells, and smart sprinklers are more vulnerable because they may be easily accessible to someone driving down the street with a computer or other Wi-Fi transmitter. Outdoor smart devices can be used as entry points, allowing hackers to access the entire smart home network. To prevent a stranger from spying on your network, it’s important to check how these products store your data. If the device’s system stores your personal information and is connected to the main home network, there is a possibility that a breach of one device on the network could reveal your data to a hacker.
Once you step foot into a smart home, you’ll likely find a variety of devices adopted by residents for added convenience, including smart TVs, Wi-Fi routers, smart speakers, thermostats, lightbulbs, and personal home assistants — the list goes on! But the fact that these devices are connected to the internet opens the door for cybercriminals to make themselves at home. For example, the FBI issued warnings about the risks of smart TVs, noting that hackers could potentially gain access to an unsecured television and take control by changing channels, adjusting volume levels, and even showing inappropriate content to children.
Additionally, a recent study outlined multiple privacy concerns with a popular virtual assistant, ranging from misleading privacy policies to allowing third parties to change the code of their programs after receiving approval from the device’s parent company. Anupam Das, assistant professor of computer science at North Carolina State University, stated that third party software developers created many of the applications consumers interact with while using the virtual assistant. However, Das and their fellow researchers identified several flaws in the current vetting process that could allow those third parties to gain access to users’ personal information. The virtual assistant’s parent company does not verify the developer responsible for publishing the third-party program, so a cybercriminal could easily register under the name of a trusted developer and create a program that spreads malicious code. For these reasons, it is critical that consumers stay informed on potentially vulnerable entry points left open by device manufacturers so they can take action to better protect their smart home technology and their personal privacy.
Today, it is not so weird to talk to your refrigerator (well, maybe a little). Smart appliances are quickly making their way into consumers’ kitchens. You can control your blender or Instant Pot from your phone and use voice activation with various appliances, further blurring the lines between the physical and the digital. And while smart kitchen appliances empower you to do things like controlling your air fryer from an app and use voice activation to brew your coffee in the morning, living like a Jetson does come with potential security risks. In 2019, McAfee researchers discovered a vulnerability within a Mr. Coffee brand coffee maker that could allow a hacker to access the user’s home network. To prevent criminals from brewing up trouble in your home, ensure that you take measures to secure each of your devices and keep criminals from spying on your network.
For many people, the bedroom is more than just the place where they sleep at night — it is a relaxing sanctuary where they can unwind. It is no wonder that many people have adopted various gadgets to turn their sanctuaries into high-tech hubs for relaxation. Take a smart bed, for example. These mattresses incorporate biometric sensors to help you snooze better, and they connect to a smartphone app that tracks your sleep trends and health metrics. While this technology may provide insight on how you can sleep better, it is important to realize that these devices are collecting data and sending it back to the manufacturer. Often, consumers do not stop to research what specific data is being collected and how it is being used, placing a lot of trust in the device manufacturer to safeguard their private information. But what happens if the company suffers a data breach or ransomware attack? There is a chance that your data might fall into the hands of a hacker. To better protect your online security, understand that enjoying the convenience of connected IoT requires an assessment of where your information is being stored.
There is no denying that IoT devices have upped the convenience of tech users’ lives everywhere. But with these technological rewards comes added risk — cybersecurity risk, that is. The more connected devices you have in your home, the more opportunities criminals have to infiltrate your network and reach other data-rich devices. This can potentially put your private and financial information at risk, not to mention your privacy.
As our reliance on IoT and smart home technology grows, so will the need for users to step up their cybersecurity practices. Follow these tips to help protect your personal data and privacy while still enjoying all that your smart home gadgets have to offer:
1. Secure your Wi-Fi network
Out of the box, most Wi-Fi routers are either not secured or use a default password such as “admin,” making it easy for hackers to poke around and access devices that are connected to your router. To prevent cybercriminals from snooping on your network and the gadgets that are attached to it, secure your Wi-Fi network with a strong password.
A password or passphrase that is long, complex, and unique will discourage attempts to break into your accounts. Try creating a string that is at least 12 characters long, contains a combination of uppercase letters, lowercase letters, symbols, and numbers, and that is unique to each account.
Do your research before investing in a smart device. Ask yourself if the gadget is from a reputable manufacturer. Has the company had previous data breaches, or do they have an excellent reputation for providing secure products? Also, take note of the information your IoT device collects, how vendors use this information and what they release to other users or third parties.
Above all, understand what control you have over your privacy and information usage. It is a good sign if an IoT device allows you to opt-out of having your information collected or lets you access and delete the data it does collect.
In addition to the password/username combo, multi-factor authentication requires that users confirm a collection of things to verify their identity — usually something they have, and a factor unique to their physical being — such as a retina or fingerprint scan. This can prevent a cybercriminal from using credential-stuffing tactics (where they will use email and password combinations to hack into online profiles) to access your network or account if your login details were ever exposed during a data breach.
Stay on top of software updates from your device manufacturer. Available updates are not always advertised, so visit the manufacturer’s website regularly. Additionally, make sure to update mobile apps that pair with your IoT device. Adjust your settings to turn on automatic software updates, so you always have the latest security patches.
Your router is the central hub that connects all the devices in your home, so make sure that it’s secure. After you change the default password and name of your router, ensure that your network name does not give away your address, so hackers can’t locate it. Then check that your router is using an encryption method, like WPA2, which will keep your communications secure.
Additionally, consider setting up a “guest network” for your IoT devices. This is a second network on your router that allows you to keep your computers and smartphones separate from IoT devices. So, if a device is compromised, a hacker still cannot get all the valuable information that is saved on your computers. Check your router’s manual for instructions on how to set up a guest network.
You do not need to go it alone — employ the help of a security solution like McAfee Secure Home Platform, which provides smart security for your home network. By automatically protecting your connected devices through the router, you can feel confident that you have a solid line of defense against online threats.
McAfee Total Protection also includes a robust password management system that creates and saves strong passwords across all your accounts in one centralized location. It also includes home network security to protect your firewall and block hackers from accessing your home network. McAfee Total Protection includes a home network map that allows you to easily identify trusted devices on your network and flag potential intruders.
Recognize that every Wi-Fi connection, every Bluetooth connection, and every connection you make using a wireless connection is subject to hacking. This will help you better understand the risks associated with your smart home devices, and therefore will help you be more equipped to combat them. Remember: a secure home is the smartest home you can have!
The post How to Secure Your Smart Home: A Step-by-Step Guide appeared first on McAfee Blogs.

Over the past year and a half, workers everywhere have gotten used to working from home. They have adopted an entirely new work from home mindset and diverted their weekly commuting hours to other productive and more enjoyable pursuits. As parts of the world return to a “new normal,” another change is on the way: a gradual return to the office.
The hybrid working model is met with mixed reviews from employees and business security teams alike. For some employees, a clearer separation between work and home is a welcome change. CTV News reports 66% of Canadian respondents to an International Workplace Group poll say they are looking forward to splitting their working hours between the office and home.
For business security teams who are just catching their breath after the monumental shift to a remote workforce, they are now gearing up for the new online safety challenges posed by the hybrid work model. According to a VMware Canada Threat Report, 86% of security professionals agree that cyberattacks aimed at their organizations have become more sophisticated since the onset of the pandemic. Additionally, 91% of global respondents cite employees working from home as the cause of cyberattacks. Challenges of the hybrid workforce include the constant back-and-forth of company-issued devices, the lack of control over home office setups, and mixing personal and company devices with company and personal business respectively. For example, if you pay your bills or shop online using your work device, it opens several new avenues for a hacker to walk right onto the corporate network. When your guard is down even a little bit when you are off the clock, you could fall victim to e-skimmers, fake login pages, or phishing scams.
No matter how advanced your company’s threat detection system, hackers know where vulnerabilities lie and are on the hunt to exploit them. Check out these tips to ensure you are not the weak link in your organization.
A virtual private network (VPN) is a service that scrambles online browsing data, making it impossible for nefarious characters to decipher your activity. This is an excellent way to deter hackers from tracking your movements and picking up sensitive pieces of information.
VPNs are essential if you are working in a public area, sharing a wireless network with strangers, or using a Wi-Fi connection that is not password protected. Public Wi-Fi networks are notoriously easy pickings for hackers seeking entry into unsuspecting users’ devices. On the days where you are not in the office, make sure your wireless connection is secure.
While a VPN is an excellent tool, security measures and your accounts are vulnerable without a strong and private password or passphrase to protect them. The gigantic Colonial Pipeline hack is being blamed on a hacker gaining entry through an unused VPN that was not secured with multifactor authentication. Multifactor authentication is an online safety measure where more than one method of identity verification is needed to access the valuable information that lies within password-protected accounts.
Consider using a password manager to organize all your passwords and logins. Password managers remember each pairing so you don’t have to, plus most managers are secured with multifactor authentication. A password manager makes it easier to add variety to your passwords and prevents you from ever having to write them down.
Professionals who travel between their home and an office are likely transporting their devices back and forth, increasing the number of opportunities for devices to be forgotten at either location or in transit. As convenient as it may be, never use your personal device for official business. Even if you pride yourself on sound online safety habits, your company device likely has more defenses ingrained in its hardware than your personal devices.
With your personal devices, you should carefully vet everything you download. With your work-issued devices, this vetting process is even more important as company information is at stake. The Information and Privacy Commissioner of Ontario states that employees should never download applications to their work devices without permission from the IT team. Apps and programs often have security vulnerabilities that could open a gateway for hackers.
Zero Trust is a security philosophy that is exactly what it sounds like: trust no one. Businesses are employing Zero Trust models to greatly limit who has access to sensitive data sources. Adopt your own personal Zero Trust philosophy concerning your passwords, logins, and device access. This means never sharing passwords or log in details, especially over email, instant messenger, or over a video conference. Hackers commonly eavesdrop on all three mediums. Also, even your most trusted coworker could mishandle your passwords and login details, such as writing them down and leaving them in a public place.
A key aspect of the Zero Trust model is only granting employees access to platforms that are vital to their job. Sharing your logins with coworkers who may not be authorized for using that platform undermines all the hard work the IT team does to keep tabs on data access.
Every time you turn on the nightly news, another ransomware attack has hit another organization, each one bigger than the last. This heightened prevalence is a reflection on the wiliness of hackers, but also the number of security holes every company must plug.
There are several vulnerable points of entry in every company, and some of those vulnerabilities are heightened by the hybrid work model. Always heed the advice of your company’s IT team, and make sure to do your part to keep your devices and work information secure.
The post Hybrid Workplace Vulnerabilities: 4 Ways to Promote Online Safety appeared first on McAfee Blogs.

Equipping and guiding your digitally connected child is one of the toughest challenges you will face as a parent. As your child grows and changes, so too will their online activities. Friend groups, favorite apps, and online interests can shift from one month to the next, which is why parental controls can be a parent’s best friend.
According to a report from Common Sense Media, teens spend an average of seven hours and 22 minutes on their phones a day. Tweens (ages 8 to 12) spend four hours and 44 minutes daily. This is time outside of schoolwork.
That is a lot of time to stroll the streets of cyberspace for entertainment purposes, and it’s only increased since the pandemic.
Striking a balance between screen time and healthy device use is an always-evolving challenge. On the one hand, your child’s device is an essential channel connecting them to their self-identity, peer acceptance, and emotional well-being. On the other hand, that same device is also the door that can bring issues such as cyberbullying, predators, risky behavior, and self-image struggles into your child’s life.
Parental controls are tools that allow parents to set controls on their children’s internet use. Controls include content filters (inappropriate content), usage limits (time controls), and monitoring (tracking activity).
Many of the technology your family already owns or sites your kids visit have basic parental controls (i.e., built-in controls for android and iPhone and social networks such as YouTube). However, another level of parental control comes in software specifically engineered to filter, limit, and track digital activity. These consumer-designed parental controls offer families a higher, more powerful form of protection.
If you are like many parents who land on this blog, you’ve hit a rough patch. You have concerns about your child’s online activity but aren’t sure how to begin restoring balance. Rightly, you want to find the best parental control software and put digital safeguards in place.
Every family dynamic is different, as is every family’s approach to online monitoring. However, most parents can agree that when a negative influence begins to impact the family’s emotional and physical health, exploring new solutions can help get you back on track.
Depending on your child’s age, you may need to consider parental controls if:
1. They don’t respond when you talk to them
If your child is increasingly engrossed in their phone and it’s causing communication issues in your family, you may want to consider software that includes time limits. Connecting with your child during device-free time can improve communication.
2. They’ve started ignoring homework and family responsibilities
There are a lot of reasons grades can plummet, or interests can fade. However, if your child is spending more and more time online, limiting or monitoring what goes on in that time can help restore emotional balance and self-discipline to meet responsibilities.
3. Their browser history shows access to risky content
Innocent online searches can lead to not so innocent results or children may go looking for content simply because they’re curious. Parental controls automatically block age-inappropriate sites and filter websites, apps, and web searches.
4. They won’t give you their device without a fight
If the phone has become the center of your child’s world at the cost of parental respect and family rules, they may be engaged in inappropriate behavior online, connecting with the wrong friends, or struggling with tech balance. With the proper parental controls, a parent can block risky content, view daily activity, and set healthy time limits.
5. They’re losing interest in family outings and other non-digital activities
Poor habits form quietly over time. If your child has dramatically changed their focus in the past three to six months, consider zooming in on why. It may not be technology use, but you may consider an additional layer of protection if it is.
6. They go into another room to respond to a text
While everyone deserves privacy, if constantly sneaking away to communicate with a friend is your child’s new norm, you may consider making some screen time adjustments.
7. They are exhausted
Unbeknownst to parents, kids might be exchanging sleep for screen time. Parental controls can help you nip this unhealthy habit. Setting time limits can help kids experience deeper sleep, better moods, more focus, and more energy.
8. They overshare online
If you browse through your child’s social media and notice their profiles are public instead of private, or if your child tends to overshare personal information, parental controls can help you monitor future activity.
Ideally, we’d all prefer to live in a world where we didn’t need parental controls at all. Unfortunately, that is neither a present nor future reality. So, we recalibrate, keep learning, and keep adding to our parenting skills. As always, we believe the first go-to digital safety tool is investing in consistent open and honest conversation with your child. And the second tool? Yup, reach for the parental controls. While you may hear some hemming and hawing from your kids at first, the peace of mind you gain from having parental controls in place will be worth it.
The post 8 Signs It May Be Time for Parental Controls appeared first on McAfee Blog.

People in their 20s and 30s are losing it online. And by it, I mean money—thanks to digital identity theft.
In its simplest form, your digital identity is made up of a whole host of things that can be traced back to you and who you are. That can range anywhere from photos you post online to online shopping accounts, email accounts to telephone numbers, and bank accounts to your tax ID.
In this way, your digital identity is like dozens upon dozens of puzzle pieces made up of different accounts, ID numbers, and so forth. When put together, they create a picture of you. And that’s why those little puzzle pieces of your identity are such attractive targets for hackers. If they get the right combination of them, you can end up a victim of theft or fraud.
Here’s what’s happening: people in their 20s and 30s were twice as likely than people 40 and over to report losing money while shopping online. That’s according to recent figures from the U.S. Federal Trade Commission (FTC), which also found that people in their 20s to 30s are far more likely to report losing money to fraud. What’s more, they’re also 77% more likely than older people to lose it by way of an email scam.
And it’s no surprise younger adults get targeted this way. They’re far more likely than any other age group to use mobile apps for peer-to-peer payments, transfer money between accounts, deposit checks, and pay bills. In short, there’s a lot of money flowing through the palms of their hands thanks to their phones, as well as their computers.
Protecting yourself from hackers and fraud means protecting your digital identity. And that can feel like a pretty huge task given all the information your digital identity includes. It can be done, though, especially if you think about your identity like a puzzle. A piece here, another piece there, can complete the picture (or complete it just enough) to give a hacker what they need to separate you from your money. Thus, the way to stay safe is to keep those puzzle pieces out of other people’s hands.
It’s actually not that tough. With a few new habits and a couple of apps to help you out, you can protect yourself from the headaches and flat-out pain of fraud. Here’s a list of straightforward things that you can get started on right away:
1. Start with the basics—security software
Protect yourself by protecting your stuff. Installing and using security software on your computers and phones can prevent all kinds of attacks and make you safer while you surf, bank, and shop online. I should emphasize it again—protect your phone. Only about half of people protect their phones even though they use it to hail rides, order food, send money to friends, and more. Going unprotected on your phone means you’re sending all that money on the internet in a way that’s far, far less safe than if you use online protection.
2. Create strong passwords
You hear this one all the time and for good reason—strong, unique passwords offer one of your best defenses against hackers. Never re-use them (or slight alterations of them) across the different platforms and services you use. Don’t forget to update them on the regular (that means at least every 60 days)! While that sounds like a lot of work, a password manager can keep on top of it all for you. And if your platform or service offers the use of two-factor authentication, definitely make use of that. It’s a further layer of security that makes hacking tougher for crooks.
3. Keep up to date with your updates
Updates have a way of popping up on our phones and computers nearly every day, resist the urge to put them off until later. Aside from making improvements, updates often include important security fixes. So, when you get an alert for your operating system or app on your devices, go ahead and update. Think of it as adding another line of defense from hackers who are looking to exploit old flaws in your apps.
4. Think twice when you share
Social media is one place hackers go to harvest personal information because people sometimes have a way of sharing more than they should. With info like your birthday, the name of your first school, your mother’s maiden name, or even the make of your first car, they can answer common security questions that could hack into your accounts. Crank up the privacy settings on your accounts so only friends and family can see your posts—and realize the best defense here is not to post any possibly sensitive info in the first place. Also, steer clear of those “quizzes” that sometimes pop up in your social feeds. Those are other ways that hackers try to gain bits of info that can put your identity at risk.
5. Shred it
Even though so many of us have gone paperless with our bills, identity theft by digging through the trash, or “dumpster diving,” is still a thing. Things like medical bills, tax documents, and checks still might make their way to your mailbox. You’ll want to dispose of them properly when you’re through with them. First, invest in paper shredder. Once you’ve online deposited that check or paid that odd bill, shred it so that any personal or account info on there can’t be read (and can be recycled securely). Second, if you’re heading out of town for a bit, have a friend collect your mail or have the post office put a temporary hold on your mail. That’ll prevent thieves from lifting personal info right from your mailbox while you’re away.
6. Check your credit
Even if you don’t think there’s a problem, go ahead and check your credit. The thing is, someone could be charging things against your name without you even knowing it. Depending on where you live, different credit reporting agencies keep tabs on people’s credit. In the U.S., the big ones are Equifax, Experian, and TransUnion. Also in the U.S., the Fair Credit Reporting Act (FCRA) requires these agencies to provide you with a free credit check at least once every 12 months. Canada, the UK, and other nations likewise offer ways to get a free credit report. Run down your options—you may be surprised by what you find.
As I just mentioned, the quickest way to get sense of what’s happening with your identity is to check your credit. Identity theft goes beyond money. Crooks will steal identities to rent apartments, access medical services, and even get jobs. Things like that can show up on a credit report, such as when an unknown address shows up in a list of your current and former residences or when a company you’ve never worked for shows up as an employer. If you spot anything strange, track it down right away. Many businesses have fraud departments with procedures in place that can help you clear your name if you find a charge or service wrongfully billed under your name.
Other signs are far more obvious. You may find collection agencies calling or even see tax notices appearing in your mailbox (yikes). Clearly, cases like those are telltale signs that something is really wrong. In that case, report it right away:
Likewise, many nations offer similar government services. A quick search will point you in the right direction.
Another step you can take is to ask each credit bureau to freeze your credit, which prevents crooks from using your personal information to open new lines of credit or accounts in your name. Fraud alerts offer another line of protection for you as well, and you can learn more about fraud alerts here.
With so many bits and pieces of information making up your digital identity, a broader way of keeping it safe involves asking yourself a question: what could happen if someone got their hands on this info? Further realizing that even little snippets of unsecured info can lead to fraud or theft in your name helps—even that un-shredded bill or innocuous refund check for a couple of bucks could give a crook the puzzle piece they need. You can keep your digital identity safe by keeping those pieces of info out of other people’s hands.
The post Guide: Protecting Your Digital Identity appeared first on McAfee Blog.

Depending on where your travels take you, you might need a new passport—a COVID-19 vaccine passport.
In an effort to kickstart travel and local economies, these so-called vaccine passports are more accurately a certificate. Such a “passport” can offer proof that the holder has been fully vaccinated against the virus, and there are several of these passports developing in the wings. With all of this in motion, I wanted to give families a look at what’s happening so that they can protect their privacy and identity online.
Broadly speaking, a vaccine passport works like this: information such as name, date of birth, date of vaccination, vaccination type, and vaccination lot number are used to create a digital certificate stored in a smartphone or a physical card. The holder can then offer up that proof of vaccination (or a recent negative test result) to businesses, travel authorities, and the like.
The notion of a vaccine passport has actually been around for a while now, such as the “Yellow Card” issued by the World Health Organization (WHO), which documents vaccination against diseases like cholera and yellow fever for travelers. Note that currently there’s no widely accepted standard for COVID-19 vaccine passports. What’s more, conversations continue around the concerns that come with documenting and sharing vaccine information securely. Understandably, it’s a complex topic.
As of this writing, the European Union has started issuing the “EU Digital Covid Certificate,” which allows its holders to travel throughout the EU freely without quarantine restrictions. The UK has its own version in the works, as do other nations in Asia, along with airline carriers too. In the U.S., “passports” appear to be in development on the state level, rather than on the federal level. For example, the state of New York has its Excelsior Pass program and California has its Digital COVID-19 Vaccine Record available to residents. Private airlines and air travel industry groups have launched their own efforts as well, such as the International Air Travel Association’s IATA Travel Pass.
How these passports are rolled out and how they get used will vary, yet vaccine passports may have an impact on the way people can travel as we recover globally from the pandemic. In some cases, they may even determine if people can attend large events that can help localities reboot their economies and public life in general (i.e., concerts, sporting events, and so on).
The development of vaccine passports and all the rules businesses and local authorities set around them may feel a bit out of our hands. However, in terms of your privacy and your family’s privacy, plenty is still very much in your hands. The common denominator across all these vaccine passports is the exchange of personal information—you and your family’s personal information. And where personal information is shared, hackers are sure to follow. This presents a perfect opportunity for you and your family to review your online privacy practices and close any gaps, whether you plan on traveling or not.
I put together a few things you can do to make sure that you and your family can navigate the future use of these passports with your privacy in mind:
What seems like an innocent celebration of your vaccination could put your personal information at risk. The information captured on these cards varies by nation, region, and locality, with some of the cards containing more information than others. However, even basic info such as birthday, vaccine manufacturer and lot number, location of immunization, or doctor’s name can provide the basis of a scam, such as a phishing email or phishing text message. Likewise, such information could get scooped up by a hacker and used to create phony vaccination credentials. Instead of posting that pic of you and your vaccine card, go with a happy selfie instead. And if you’ve already posted, go ahead and delete the image, better to remove it now and stay safe.
As mentioned above, the uncertainty around vaccine passports, and the general uncertainty around the latter days of the pandemic overall, creates opportunities for hackers and cybercrooks. Just as the early pandemic saw phony offers around miracle cures and today we’re seeing offers for phony vaccination cards, you can bet that scams revolving around vaccine passports will follow. The best advice here is to go to a trusted source for information, like the NHS in the UK or the American Medical Association in the U.S. Granted, cybercrooks will launch their phishing campaigns regardless. Here’s what to do if one heads your way:
In all, if someone is asking for any kind of personal or financial information via an email, text, instant message, or the like, chances are it’s a scam. For more, check out this article on how to spot the warning signs of a phishing attack.
In a time of data breaches large and small, checking your credit regularly is a wise move. Doing so will help you quickly spot issues and help you address them, as companies typically have a clear-cut process for dealing with fraud. You can get a free credit report in the U.S. via the Federal Trade Commission (FTC) and other nations like the UK have similar free offerings as well.
Do the same for your children. They’re targets too. High-value targets at that. Their credit reports are clean, which gives cybercrooks a blank slate to work with. Even more attractive is that child identity theft often goes long unnoticed until years later when the child gets older and rents an apartment or applies for their first credit card.
It’s that simple. Given that these vaccine passports will likely involve a digital certificate stored on a smartphone, app, or possibly other devices, protect them so you can protect yourself. Select comprehensive security software that will protect multiple devices so that everyone in your home is covered.
You can bet that rumors will abound as to who is issuing what “passport”, under what restrictions, and with what implications for traveling, dining out, and visiting shops. All of that amounts to plenty of falsehoods and scams that attempt to rob you of your privacy, identity, and even your money. Turn to trusted news sources known for their even-handed reporting, such as Reuters or the Associated Press, and get your information from there. Knowing what the facts about vaccine passports are in your locality will arm you against fear-based attacks.
A few months back, the FTC posted its own blog about sharing vaccine card photos. It’s a great read, in part because they used a helpful analogy to discuss privacy and identity theft:
Think of it this way — identity theft works like a puzzle, made up of pieces of personal information. You don’t want to give identity thieves the pieces they need to finish the picture.
Likewise, any vaccine passport you acquire will become yet another puzzle piece that you have to protect.
In all, with post-pandemic recovery measures evolving before our eyes, keep an eye on your family’s security. Don’t give away any snippets of info that could be used against you and stay on the lookout for the scams hitting the internet that play on people’s uncertainty and fears. COVID-19 passports may be entirely new, yet they give cybercrooks one more way they can play their old tricks.
The post COVID-19 Vaccine Passports: 5 Security Tips for You and Your Family appeared first on McAfee Blogs.

Among the many major shifts in lifestyle during the COVID-19 pandemic, the way we used healthcare was one of the most significant. Providers limited in-person visits, elective procedures were delayed, and we avoided hospitals. In response, we went online and started using telehealth and other virtual solutions in ways we never had before.
Our latest consumer mindset survey confirms this was more than a passing trend, showing an almost 50% rise since the beginning of the pandemic in the use of PCs and Mobile devices to access health information, meet virtually with health care providers, and manage prescriptions. Survey respondents also showed they adapted by increasing their usage of smart fitness devices, like Fitbits, to track their personal health.
Navigating the healthcare system and accessing more of our services through the web means more of our personal information is now online. From patient intake forms to test results, a great deal of data about our health, including confidential information like vaccination records, is potentially available. Survey respondents confirmed that they shared and accessed their personal health information across the internet, despite 1/3 or more of respondents having concerns for their privacy and security of their personal information.
This trend hasn’t gone unnoticed by cybercriminals. In fact, the US Department of Health and Human Services is currently investigating nearly 800 health-related data breaches impacting nearly 60 million individuals. All of which is to say that telehealth advances may help us avoid sitting in a doctor’s office, but we need to be more mindful about our security when using these new online services.
Despite the adoption of many telehealth and online health services, security was still a concern for many of our survey respondents. A majority said the primary reason they do not use smart devices for their personal health was because of privacy and security concerns. Fortunately, just as there is preventive medicine, there are also preventive cybersecurity measures we can take to keep our personal data safer online. Here are a few we recommend:
The shift to managing our health online comes with a few safety considerations, but by following the steps above, we can enjoy convenience and access to a healthier life online and off.
The post How to Make Telehealth Safer for a More Convenient Life Online appeared first on McAfee Blogs.

I’m about to tell you an extraordinary fact about cybercrime. Some of the most significant data breaches in internet history weren’t after bank account numbers, cryptocurrency, or even credit card numbers. They were, in fact, after YOU. That’s right, the most valuable data on the internet is the data that comprises your identity. Let’s take a look at what that data is, how it gets leveraged by cybercriminals, and how you can get the online identity monitoring you deserve.
1 billion is a big number. In the case of a recent CVS database leak, that’s how many user records were accidentally released online, including details like email addresses and even searches about Covid vaccines. This is just one of the dozens of breaches that have occurred recently and will continue to happen as personally, identifiable information becomes more valuable to cybercriminals. Just as remarkable as the huge volume of user data being exposed online is the speed with which compromised data is used by hackers online. Cybersecurity researchers recently discovered that cybercriminals access leaked or stolen credentials within 12 hours to exploit them as soon as possible. These circumstances beg the question, why has your personally identifiable information has become so valuable lately?
While the value of some information, like a credit card number, is obvious, you may think your name and date of birth aren’t that big of a deal. After all, it wasn’t so long ago that you could find all that information in a phone book. In fact, personally identifiable information (PII), also known as data used to identify a specific individual, is what many data breaches are after.
Armed with just a mailing address, a phone number, and a date of birth, a cybercriminal can begin constructing a fake identity to take out loans and disguise many kinds of criminal activities. With a social security number and a few personal details from a social media account, they could take over a bank account. When it comes to your PII, any information is as good as gold to cybercriminals.
If our PII were treated like actual gold and held in a safe location like Fort Knox, I wouldn’t be writing this post. But in fact, it’s the currency we use to obtain many services in our connected lives. Social media sites are massive repositories of PII, and their access to our most personal details and the ability to sell it to marketers is the reason the service remains free. Free email services are the same. Now consider all the other accounts we may have created to, say, try out a streaming service for free, or even old accounts we no longer use. From that perspective, you can see how much of your data is being used by companies, may not be very well protected, and is a tempting target for cybercriminals. Fortunately, there are many things you can do to keep your identity safer online.
When it comes to protecting your PII, knowledge is power. Let’s start by identifying if you’ve been the target of a data breach. Here are a few tell-tale signs:
Okay, now that you know the signs of a data breach, let’s look at how you can take action to protect yourself. The best way to avoid being the victim of identity theft is by limiting the amount of PII you provide. There are some easy ways to do this.
Only a few types of organizations legitimately need your social security number. These include employers or when contracting with a business, group health insurance, financial and real estate transactions, applying for credit cards, car loans, and so forth.
Quizzes, social media games, and other kinds of interactive clickbait are often grifting pieces of your PII in a seemingly playful way. While you’re not giving up your SSN, you may be giving up things like your birthday, your pet’s name, your first car … things that people often use to compose their passwords or use as answers to common security questions on banking and financial sites.
A phishing email poses as a real email from known or trusted brands and financial institutions. These emails attempt to trick you into sharing important information like your logins, account numbers, credit card numbers, and so on under the guise of providing customer service. Here are some more ways to spot a phishing email.
Clearly, we’re in a new era when it comes to securing our identities online. In response, McAfee has created a new kind of identity monitoring.
We knew from the outset Identity monitoring had to be proactive, holistic, and accessible. We also wanted it to follow the timeline for how cybercrime actually affects your identity. When it comes to PII, the breach is just the first step for cybercriminals. The 10 months following a breach is when cybercriminals will use your PII to commit fraudulent acts using your data.
To address this, your identity monitoring looks after more personally identifiable information than other leading competitors. It will also alert you of stolen personal info an average of 10 months ahead of other monitoring services. And it’s accessible anywhere via mobile app, browser, and the web.
In practice, McAfee’s identity monitoring protects all your online accounts by doing the following:
As we spend more of our lives online, we need an approach to security that reflects this new reality. Identity monitoring is part of it. VPN is part of it. Antivirus is part of it. They are all pieces of a puzzle that we solve with products like McAfee Total Protection. Our premier security service is comprehensive, affordable, and, with identity monitoring, an indispensable part of your life online.
The post Identity Protection Service: The Best Solution to a Growing Problem appeared first on McAfee Blog.

Across the country, Canadians are moving out of cities in droves to stretch their legs and call a larger plot of land home. For those embracing the work-from-home lifestyle, they no longer need to live near metro-area offices in expensive shoebox apartments and condos. According to Statistics Canada, 50,000 people moved out of Toronto and nearly 25,000 people migrated from Montréal to suburban areas from July 2019 to July 2020.
The increased demand for suburban housing is making the Canadian real estate market a mad dash for limited supply. Additionally, some families who are out of work are struggling to keep their homes and are resorting to unsafe measures to keep a roof over their heads.
Leave it to scammers and identity thieves to pounce on a vulnerable situation. Scammers and identity thieves are increasingly taking advantage of unsuspecting homeowners, and in some cases, selling homes without the rightful owners even realizing it.
Be on the lookout for these three Canadian real estate scams.
Foreclosure occurs when a homeowner can no longer afford to pay their mortgage, so the lending institution takes over homeownership with the right to sell it. When homeowners are facing the prospect of having to move out, they may seek dubious loans to help them bridge the gap. Loan fraud is when a scammer pretends to extend a gracious loan. In exchange for the loan, the scammer may ask for the title of the home. With the title in hand, the thief may stop sending loan payments to the homeowner and instead resell or remortgage the property.
Not being able to make mortgage payments is a desperate situation, which causes struggling homeowners to make dramatic decisions. Before agreeing to any type of loan, homeowners must ask themselves if the terms of the loan are too good to be true. In cases of fake loans, they often advertise an incredibly low-interest rate. It is best to trust your financial matters to accredited institutions.
Title fraud is when someone steals the title of the home, usually by impersonating the homeowner. Once they have the title, the thief may attempt to sell the home or apply for a mortgage against it. In March 2021, the Times Colonist reported that a thief impersonated a British Columbian homeowner in order to transfer the home’s title to someone else’s name. Then, the thief tried to sell the home behind the rightful homeowner’s back. It was only when a neighbor alerted the real homeowner about the for-sale sign that they realized that their home could have been sold without their permission.
The best way to defend against title fraud is to keep your personal information as private as possible. Title fraud is closely related to identity theft, and fraudsters may gain access to your personal information through phishing methods. Phishing is a tactic where cybercriminals trick people into giving up personal details, including full names, birthdays, and financial information. Statistics Canada calculates that 34% of Canadians have experienced a phishing attempt since the beginning of the pandemic. This statistic emphasizes the importance of constant vigilance concerning your most sensitive personal information.
Mortgage fraud is a term that can apply to untruthful lenders who attempt to swindle cash from unsuspecting buyers or pitch mortgage terms that fall outside of the buyer’s means. The Financial Services Commission of Ontario lists several warning signs of mortgage fraud. For example, lenders who do not have your best interests in mind may ask for cash fees and upfront payments.
Again, it is best to only trust accredited financial institutions with your mortgages and loans. Research the institution before signing any contract. If the mortgage terms are too good to be true, it probably is. There are several online mortgage calculators that can give you an idea of the type of mortgage you can afford. Before entering any talks with a lender, conduct some research beforehand so you can spot unreasonable terms.
Also, an unscrupulous lender may try to hurry you along but also take a long time responding to your calls and emails. If you feel pressured or unsure at any point, remember that there are plenty of fish in the sea. Ask your friends or family for lender recommendations to make sure that you are not tricked into mortgage fraud, the consequences of which could follow you for years.
The post 3 Canadian Real Estate Scams You Should Know About appeared first on McAfee Blogs.

Every day you place your personal information in the hands of companies and trust that it will remain safe. However, what happens when external threats jeopardize your personal data security, especially while working remotely?
The transition to remote work environments and consumers’ online habits have made it more difficult for Canadian employees and consumers to protect their personal information. This challenge is primarily due to ransomware. To protect yourself, you need to first understand how cybercriminals take advantage of users’ online behaviors to launch strategic attacks against employees and consumers through the information they glean from stolen company data.
Ransomware has been on the rise this past year with attacks increasing 62% in 2020 according to Statista. In fact, 78% of Canadian cybersecurity professionals said that attacks increased due to employees working remotely in a recent VMware report. Cybercriminals target remote workers primarily through malicious links sent through phishing emails — in fact, over one third of Canadian respondents in a recent survey said they experienced at least one phishing attempt in the last year.
Hackers pose as legitimate organizations and prompt individuals to take action: say you decide to check your personal email on your work laptop during your lunch break. You open a message that claims to be from one of your favorite retailers claiming that you just won $500 in shopping credit – all you need to do is click on the link and fill out your banking information. This is an example of a phishing attack that could not only wreak havoc on your personal security, but your company’s as well. If the link in the message downloads a credential-stealing malware on your work laptop, there is a good chance that your organization’s private data or network could be compromised.
Knowing that many employees will be communicating virtually instead of face-to-face, hackers can take advantage of the remote work environment by posing as employees from finance departments and sending fake invoices for products or services. The goal of these fake invoices is for employees to call a support phone number to investigate, whereby hackers attain credit card numbers or other information they can leverage in spear-phishing scams. Hackers can also spoof phone calls to make it look like it is coming from a legitimate number within the organization. Revealing too much information to an unverified contact is a risk that remote workers must learn to identify and avoid.
Ransomware is always evolving, making it critical to understand the nature of these threats so you can better avoid them.
Cybercriminals are constantly finding new ways to automate their attacks and increase their profits. Here is a look at five active ransomware variants cybercriminals use today—and how they deploy them.
By the end of 2020, McAfee Labs observed a 69% increase in new ransomware, which Cryptodefense largely drove. This virus is similar to CryptoLocker, a trojan virus that spreads through email phishing to infiltrate hard drives and files. Both spread ransomware, use high levels of encryption to compromise users’ files, and claim that these files cannot be decrypted without a decryption key.
Maze ransomware has been active since November of 2019 and is operated by hackers notorious for leaking victim data upon non-payment. Maze operators first gain access to a network by using valid credentials. It will then scan the network for user devices, check these devices for additional credentials, and compromise user files.
In a Ransomware Task Force interview with an affiliate of the REvil/Sodinokibi syndicate, the interviewee revealed that companies with cyber insurance are prime targets since the chances of a payout are high. This ransomware spreads through software vulnerabilities, phishing scams, and exploit kits. Once it infiltrates a device, it spreads through escalated privilege to compromise user files and systems.
Ryuk has been around since August of 2018 and targets large companies, critical infrastructure, and hospitals. This ransomware is almost always spread through a banking trojan called Trickbot, used by hackers to steal financial and banking credentials. The operators behind this ransomware demand higher ransoms compared to other groups. They also use opensource tools and manual hacking techniques to bypass detection and infiltrate private networks.
The operators behind SamSam ransomware gain access through Windows servers using a Microsoft protocol that allows remote connections to other computers. Operators will then elevate their privilege to include admin rights once inside a network to infect servers with malware, requiring no action or authorization on the victim’s part.
Ransomware can affect anyone, regardless of whether you are an employee or a customer of a targeted company. Keep these tips in mind to reduce your risk of a ransomware attack and know what steps to take if you fall victim.
Phishing emails are one of the most common methods a hacker will use to infect devices and spread ransomware. They will send links through seemingly legitimate emails to trick users into clicking on them and downloading malicious files. Knowing how to spot one is the first step to prevent infection. If you receive an email you suspect is a phishing scam, start by analyzing its structure: common indicators of a phishing scam may include:
Once you identify a phishing email, don’t click on any links or download attachments. Simply delete it and carry on with your day.
Keep in mind that the cybercriminals behind Maze ransomware gained access to private networks through valid credentials. Hackers typically obtain these credentials through a “password spray” technique where they attempt to log in to accounts using a list of commonly used passwords. However, hackers have a higher chance of guessing valid passwords if they are too short or not complex enough. Additionally, a hacker is more likely to infiltrate multiple accounts if they share the same password.
Strong passwords help ensure that a hacker cannot access your private network, gain administrative rights to your device, or infect another device you are connected to. Create a password that is strong enough to withstand simple guess-and-check attempts by making them long, difficult, and unique. Multi-phrased passwords or passphrases also help to prevent hackers from breaking into your accounts, such as “P3anutbutter&J3lly.” Avoid reusing passwords across multiple accounts and change them periodically, especially after an account has been breached. Even if a hacker does steal your credentials, multi-factor authentication adds an extra validation layer to prohibit unauthorized sign-in attempts.
Your device is more susceptible to ransomware and viruses without the right security tools to help mitigate the chances of infection. Avoid the risk of a ransomware attack by employing a quality security solution like McAfee Total Protection. A holistic security solution can help you stay vigilant of cyber threats by monitoring for ransomware viruses in addition to malware and spyware. Security software can also monitor your internet connection and network traffic through regular scans to flag malicious activity and provide guidance on how to sidestep these threats. If a hacker attempts to launch an attack on your device, you can rest assured your security software will promptly alert you of the intrusion.
In addition to social engineering tactics, hackers will leverage vulnerabilities in software to create a back door through which they can infiltrate user devices. A way to keep cyber criminals out is to keep your software applications and devices up to date. This includes the apps on your mobile device as well as apps on your desktop. Regular updates ensure that the proper security patches are implemented, the right bugs are fixed and that hackers cannot exploit these vulnerabilities.
If worse comes to worst and your device is infected with ransomware, the first thing to do is isolate the device and disconnect from shared networks. Disconnecting the infected device ensures that ransomware cannot spread to other devices on that same network.
Immediately gather evidence on what type of malware you are dealing with so you can accurately report it to authorities and determine what your options are for remediation. You can then choose to remove it or wipe your system completely which is the most assured way to eliminate ransomware from your device. Afterwards you can reinstall your operating system and, provided you perform regular backups, restore your files to a previous version.
No one is truly out of the danger zone when hackers strike. Ransomware is on the rise, and online users must understand how to bypass these viruses to avoid the ramifications of a compromised device. By understanding online security best practices, users can safeguard their online presence and defend against ransomware threats.
To stay updated on all things McAfee and on top of the latest consumer and mobile security threats, follow @McAfee_Home on Twitter, subscribe to our newsletter, listen to our podcast Hackable?, and ‘Like’ us on Facebook.
The post 5 Ransomware Threats Canadians Need to Know appeared first on McAfee Blogs.

If you have a tween or teen, you’ve likely heard a lot of excited chatter about Roblox. With a reported 150 million users, there’s a good chance your child has the Roblox site on their phone, tablet, PC, or Xbox. In fact, in 2020, Roblox estimated that over half of kids in the U.S. under 16 had used the forum. However, as with all digital destinations, the fun of Roblox is not without some safety concerns.
Roblox is an online gaming forum (not an app or game as one might assume) where users can create and share games or just play games. Kids can play Roblox games with friends they know or join games with unknown players. Roblox hosts an infinite number of games (about 20 million), which makes it a fun place to build and share creations, chat, and make friends. Game creators can also make significant money if their games take off.
A huge component of Roblox is its social network element that allows users to chat and have meetups. During quarantine, Roblox added its own private space for users to host virtual private birthday parties and social gatherings.
Like any site or app, Roblox is safe if you take the time to optimize parental controls (both in-forum and personal software), monitor your child’s use, and taking basic precautions you’re your child starts using the forum. Especially with kids drawn to gaming communities, it’s important to monitor conversations they can be having with anyone, anywhere.
Roblox security tip: Adjust settings to prohibit strangers’ from friending an account. Consider watching your child play a few games and how he or she interacts or wanders through the app. Pay close attention to the chat feature. Keep the conversation open, so your child feels comfortable sharing online concerns with you.
If you have your child’s login information, you can easily view their activity history in a few vulnerable areas including private and group chats, friends list, games played, games created, and items purchased. It’s also a good idea to make sure their birthdate is correct since Roblox automatically filters chats and game content for users under 13. Roblox has a separate login for parents of younger kids that allows you to go in and view all activities.
As always, the best way to keep your child safe on Roblox or any other site or app is to take every opportunity for open, honest conversation about personal choices and potential risks online. Oh, and sitting down to play their favorite games with them — is always the best seat in the house.
The post What is Roblox and is It Safe for Kids? appeared first on McAfee Blogs.

What do Burger King and the popular “Doge” meme have in common? They both have cryptocurrencies named after their likeliness. WhopperCoin and Dogecoin are just two examples of the thousands of types of cryptocurrencies that have caught users’ attention over the past few years. Cryptocurrencies are digital tokens generated by a computer after solving complex mathematical functions. These functions are used to verify the authenticity of a ledger, or blockchain.
Bitcoin is the most popular cryptocurrency today, increasing its value by almost 300% in 2020. Today, almost 46 million Americans own at least one share of Bitcoin, illustrating how these cryptocurrencies are the future of tomorrow’s digital payment system — or are they? The same benefits that make them a popular choice with online users have also made them popular amongst online thieves, sparking a wave of ransomware attacks and other cyberattacks more recently. This begs the question: do the benefits of Bitcoin outweigh the risks?
Every rose has its thorn, and several Bitcoin benefits seem to be hitched to online security risks. Here are some cryptocurrency characteristics that may seem appealing to users, but also provide cybercriminals with an opportunity to exploit:
As previously mentioned, cryptocurrency exchanges take place on an online public ledger, or blockchain, to secure online transactions. This means that anybody can observe the exchange online. However, the parties making the transactions are anonymous, disguised with a random number. Bitcoin users can make purchases that are never associated with their identity, similar to a cash transaction.
While the purchase discretion provided by Bitcoin may be appealing to users who want to remain private, this characteristic could also aid cybercriminals in malicious activity. Due to the anonymity of Bitcoin transactions, there is no way for someone to associate a person with a certain cryptocurrency wallet. Furthermore, a user could have multiple wallets, allowing them to spread their currency from one address to another.
For a cybercriminal looking to target an individual with ransomware, the purchase discretion and anonymity of Bitcoin provide a favorable solution. In fact, Bitcoin accounts for approximately 98% of ransomware payments today. Say a hacker carries out a ransomware attack and demands that the user pay a large sum in Bitcoin. If the user completes the payment, the hacker can keep moving the currency from one anonymous account to another. That makes it very difficult — though not impossible — to trace if the individual decides to investigate the case and tries to get their money back.
Another characteristic that Bitcoin users find appealing is the autonomy offered by digital currencies. In theory, they allow users more autonomy over their own money than government-regulated currencies do. With Bitcoin, users can control how they spend their money without dealing with an intermediary authority like a bank or government.
This lack of intermediary authority also opens a door for hackers to exploit. Say a user decides that they want to manage their finances using Bitcoin to bypass banking fees and send money to friends and family in different parts of the world. As previously mentioned, a Bitcoin user is assigned an anonymous private key that acts as their security credential. This key is generated and maintained by the user instead of a third-party agency. But what happens if the key isn’t random enough? An attacker could steal the user’s private key, and they will not be able to recover it since the Bitcoin blockchain is not dependent on any centralized third-party institutions. Therefore, it will be very difficult to track the attacker’s behaviors and recover lost funds.
It is safe to say that Bitcoin has caused a lot of buzz. But do the benefits outweigh the risks? Due to the nature of Bitcoin and most other public blockchains, anyone in the world can perform transactions or cryptographic computations — including cybercriminals. That’s why it is crucial for current cryptocurrency users and those considering cryptocurrency investment to do their research and know what vulnerabilities lie within the world of Bitcoin.
Follow these tips to help protect yourself from common threats that leverage cryptocurrency:
With blockchain, cryptocurrency, and any new and emerging technology, make sure you always remain a bit skeptical. Do your homework before you embrace the technology — research your options and make note of any known security issues and what you can do to mitigate known risks.
If a hacker does target you with ransomware demanding Bitcoin payment, it’s best not to pay the ransom. Although you may feel in the moment that this is the only way to get your encrypted files back, there is no guarantee that the ransomware developers will send a decryption tool once they receive the payment. Paying the ransom also contributes to the development of more ransomware families, so it is best to hold off on making any payments. Furthermore, a recent study found that 80% of businesses that choose to pay a ransom experience a subsequent ransomware attack. While it may feel like your only option in the moment, paying a ransom could show attackers that you’re willing to make the payment, therefore positioning you as an ideal target for yet another attack.
If you are targeted with ransomware, it’s crucial that you always have backup copies of your files, preferably in the cloud and on an external hard drive. This way, if you do get a ransomware infection, you can wipe your computer or device and reinstall your files from the backup. Backups protect your data, and you won’t be tempted to reward the hackers by paying a ransom. Backups won’t prevent ransomware, but they can mitigate the risks.
Large organizations often fall prey to ransomware attacks, so take necessary precautions if a company you’ve interacted with becomes compromised from a data leak or a ransomware attack. Immediately change your passwords for all your accounts, ensuring they are strong and unique. You can also employ a password manager to keep track of your credentials and generate secure login keys.
Add an extra layer of security with a solution such as McAfee® Total Protection, which includes Ransom Guard, to help protect your devices from these cyberthreats and ensure your digital wellness online.
The emergence of Bitcoin has indeed facilitated a wave of cybercrime that was previously difficult to perceive. In this new age of digital payments, blockchain, and cryptocurrencies, make sure that you do your research and stay vigilant when it comes to protecting your online safety. Remember: Bitcoin worth will continue to fluctuate, but your personal security will always remain invaluable.
To stay updated on all things McAfee and on top of the latest consumer and mobile security threats, follow @McAfee_Home on Twitter, subscribe to our newsletter, listen to our podcast Hackable?, and ‘Like’ us on Facebook.
The post Do the Benefits of Bitcoin Outweigh the Risks? appeared first on McAfee Blogs.

Over the past year, you may have seen the term ransomware popping up frequently. There’s good reason for that as ransomware is responsible for 21% of all cyberattacks, according to a new report. For enterprising hackers, this tactic has become standard operating procedure because it’s effective and organizations are willing to pay. But what does that mean for you and living a confident life online? Fortunately, there are a number of things individuals can do to avoid ransomware. But first, let’s start with the basics.
Ransomware is malware that employs encryption to hold a victim’s information at ransom. The hacker uses it to encrypt a user or organization’s critical data so that they cannot access files, databases, or applications. A ransom is then demanded to provide access. It is a growing threat, generating billions of dollars in payments to cybercriminals and inflicting significant damage and expenses for businesses and governmental organizations.
McAfee Labs counted a 60% increase in attacks from Q4 2019 to Q1 2020 in the United States alone. Unfortunately, the attacks targeting organizations also impact the consumers who buy from them, as the company’s data consists of its customers’ personal and financial information. That means your data if you’ve done business with the affected company. Fortunately, there are many ways you can protect yourself from ransomware attacks.
When a company is hit with a ransomware attack, they typically are quick to report the incident, even though a full analysis of what was affected and how extensive the breach may have been may take much longer. Once they have the necessary details they may reach out to their customers via email, through updates on their site, social media, or even the press to report what customer data may be at risk. Paying attention to official communications through these various channels is the best way to know if you’ve been affected by a ransomware attack.
The top ransomware infection vectors – a fancy term for the way you get ransomware on your device – are phishing and vulnerability exploits. Of these two, phishing is responsible for a full 41% of ransomware infections. Ironically, this is good news, because phishing is something we can learn to spot and avoid by educating ourselves about how scammers work. Before we get into specific tips, know that phishing can take the form of many types of communications including emails, texts, and voicemails. Also know that scammers are convincingly imitating some of the biggest brands in the world to get you to surrender your credentials or install malware on your device. With that in mind, here are several tips to avoid getting phished.
If you receive an email, call, or text asking you to download software or pay a certain amount of money, don’t click on anything or take any direct action from the message. Instead, go straight to the organization’s website. This will prevent you from downloading malicious content from phishing links or forking over money unnecessarily.
If someone sends you a message with a link, hover over the link without clicking on it. This will allow you to see a link preview. If the URL looks suspicious, don’t interact with it and delete the message altogether.
Instead of clicking on a link in an email or text message, it’s always best to check directly with the source to verify an offer, request, or link.
McAfee offers the free McAfee WebAdvisor, which can help identify malicious websites and suspect links that may be associated with phishing schemes.
If you do get ransomware, the story isn’t over. Below are 8 remediation tips that can help get your data back, along with your peace of mind.
If you get ransomware, you’ll want to immediately disconnect any infected devices from your networks to prevent the spread of it. This means you’ll be locked out of your files by ransomware and be unable to move the infected files. Therefore, it’s crucial that you always have backup copies of them, preferably in the cloud and on an external hard drive. This way, if you do get a ransomware infection, you can wipe your computer or device free and reinstall your files from backup. Backups protect your data, and you won’t be tempted to reward the malware authors by paying a ransom. Backups won’t prevent ransomware, but they can mitigate the risks.
If you discover that a data leak or a ransomware attack has compromised a company you’ve interacted with, act immediately and change your passwords for all your accounts. And while you’re at it, go the extra mile and create passwords that are seriously hard to crack with this next tip.
When updating your credentials, you should always ensure that your password is strong and unique. Many users utilize the same password or variations of it across all their accounts. Therefore, be sure to diversify your passcodes to ensure hackers cannot obtain access to all your accounts at once, should one password be compromised. You can also employ a password manager to keep track of your credentials and generate secure login keys.
Two or multi-factor authentication provides an extra layer of security, as it requires multiple forms of verification. For instance, you’ll be asked to verify your identity through another device, such as a phone. This reduces the risk of successful impersonation by hackers.
Be careful where you click. Don’t respond to emails and text messages from people you don’t know, and only download applications from trusted sources. This is important since malware authors often use social engineering to get you to install dangerous files. Using a security extension on your web browser is one way to browse more safely.
Avoid using public Wi-Fi networks, since many of them are not secure, and cybercriminals can snoop on your internet usage. Instead, consider installing a VPN, which provides you with a secure connection to the internet no matter where you go.
While it is often large organizations that fall prey to ransomware attacks, you can also be targeted by a ransomware campaign. If this happens, don’t pay the ransom. Although you may feel that this is the only way to get your encrypted files back, there is no guarantee that the ransomware developers will send a decryption tool once they receive the payment. Paying the ransom also contributes to the development of more ransomware families, so it’s best to hold off on making any payments. Thankfully there are free resources devoted to helping you like McAfee’s No More Ransomware initiative McAfee, along with other organizations, created www.nomoreransom.org/ to educate the public about ransomware and, more importantly, to provide decryption tools to help people recover files that have been locked by ransomware. On the site you’ll find decryption tools for many types of ransomware, including the Shade ransomware.
Adding an extra layer of security with a solution such as McAfee® Total Protection, which includes Ransom Guard, can help protect your devices from these cyber threats. In addition, make sure you update your devices’ software (including security software!) early and often, as patches for flaws are typically included in each update. Comprehensive security solutions also include many of the tools we mentioned above and are simply the easiest way to ensure digital wellness online.
The post 8 Tips for Staying Safe from Ransomware Attacks appeared first on McAfee Blog.