Cisco is honored to be this year’s winner of the Best Next Generation Firewall Award in the SE Labs 2023 Annual Report. This industry recognition validates Cisco’s continuous push towards harmonizing network, workload, and application security across hybrid and multicloud environments. I’m incredibly proud of the Cisco Secure Firewall team and am thankful for our amazing customers who continue to trust Cisco and develop their network security around our capabilities.
SE Labs, a cybersecurity testing and evaluation firm, provides impartial and independent assessments of various cybersecurity products and solutions. In their 2023 Annual Report, SE Labs states:
“Our Annual Security Awards recognizes security vendors that notonly do well in our tests, but perform well in the real world withreal customers. These awards are the only in the industry thatrecognize strong lab work combined with practical success.”
SE Labs performs tests on behalf of customers seeking independent proof-of-value assistance, as well as security vendors. At Cisco, we use third-party evaluations from multiple sources, including SE Labs, to augment our internal testing and to drive product improvement.
Winners were determined after months of in-depth testing, based on a combination of continual public testing, private assessments and feedback from corporate clients who use SE Labs to help choose security products and services. The award further validates that our customers can expect superior threat protection and performance with Cisco Secure Firewall.
SE Labs’ reports use the MITRE ATT&CK framework, employing both common “commodity” malware samples and sophisticated, targeted attacks. Their network security testing uses full attack chains to assess the detection and protection abilities of network devices and combinations of network and endpoint solutions. SE Labs publishes its testing methodologies and is BS EN ISO 9001: 2015 certified for The Provision of IT Security Product Testing.
As a worldwide leader in networking and security, Cisco is better positioned than any other security vendor to incorporate effective firewall controls into our customers’ infrastructure — anywhere data and applications reside. We offer a comprehensive threat defense with industry-leading Snort 3 IPS to protect users, applications, and data from continuously evolving threats. Our solutions also leverage machine learning and advanced threat intelligence from Cisco Talos, one of the world’s largest commercial threat intelligence teams.
In the constantly evolving world of cybersecurity, it is important to have access to the latest and most advanced technologies to stay ahead of threats. Whether you are an enterprise, government, healthcare, or a service provider organization, Cisco Secure Firewall provides top-ranked security.
When you invest in Cisco Secure Firewall, you are investing in award-winning threat defense with capabilities that are built for the real world. Learn more about SE Labs 2023 Annual Report, Cisco Secure Firewall and how you can refresh your firewall.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Cisco Live is the premier destination for Cisco customers and partners to gain knowledge and build community. Our teams work hard to deliver education and inspiration, ignite creativity, deliver practical know-how, and accelerate the connections that fuel your digital future.
The Cisco Secure team is excited to share our expertise to help power the strategies – and safety – of your organization.
In 2023, the threat landscape will evolve to one that sees attacks on every surface, from criminals who are opportunistic, yet laser-focused on their goal. The attacks themselves could be email-borne, directly targeted, socially based, or a mix of all three.
Criminals will target vulnerabilities, operational deficiencies, suppliers, and business partners, as a means of accomplishing their goals. They will use the target’s own environment and take advantage of existing people and technology problems, including alert fatigue and staffing shortages.
To face this reality and address the needs of organizations both large and small, Cisco will continue to focus on education and innovation in the areas of preventing insider threats, providing consistent and informed alerts, enabling actionable intelligence, and delivering solutions to implement a zero-trust security framework.
As the organization that pioneered networking, we are driven to secure every connection, providing end-to-end protection for users and devices across multiple clouds and networks with a seamless experience.
As our vision for the integrated Cisco Security Cloud evolves, we’re continuing to challenge existing models and unify security and networking, with foundational elements that execute on this vision. From verified push – which protects organizations from MFA-focused phishing attacks – to Wi-Fi Fingerprint, and Remembered Devices, the performance enhancements with Enterprise Single Sign-on and Cisco+ Secure Connect, we continue to meet our customers where they are, offering true zero trust, with frictionless experiences for the hybrid workforce.
We’re excited to celebrate the following innovations and updates announced at Cisco Live EMEA:
Finding the balance between usability and security is now easier than ever. With Risk-Based Authentication, users have the access they need, secured by real-time contextual signals. Organizations can increase security efficacy by dynamically adjusting authentication requirements based on risk levels and by enabling safer end-user behavior. Risk-based authentication now includes wi-fi fingerprint, remembered device, and verified push features, which work together to reduce risk while preserving user experience by only requesting additional interaction for suspicious logins or a change in risk.
Our Enterprise Ready Single Sign-on expands Duo SSO with three new capabilities to easily connect single sign-on to modern apps and empower end users. By adding major protocol support, improved admin tooling, and SSO on demand password resets, organizations enable easier and more secure access from anywhere.
Cisco SD-WAN customers can now enjoy all the benefits of a turnkey, single-vendor SASE solution that brings together industry-leading networking with security: Cisco+ Secure Connect. This new integration gives Cisco SD-WAN (powered by Viptela) customers fast, secure private application and internet access, enabling them to deliver a secure experience, anywhere work happens.
We are also announcing the introduction of industry-first Business Risk Observability, an enhancement of our Full-Stack Observability application security solution. Available through Cisco Secure Application, which is integrated into Cisco AppDynamics, it provides a business risk scoring solution which brings together Kenna Risk Meter score distribution and Business Transactions from Cisco AppDynamics and integrates with Panoptica for API security and Talos for threat intelligence.
The initial findings from our first Cybersecurity Readiness Index reveal that while technology to devices is widely adopted, more progress is needed to protect identity, networks and applications. The report assessed the preparedness of companies around the world to safeguard against cyber threats in the current environment. See our key findings and security readiness trends, with the full report launching in the coming weeks.
As we navigate 2023, we will continue to face uncertainties and challenges. We are fully committed to our customers and partners in the journey to provide security resilience, supporting a frictionless user experience, and solutions threat intelligence that work to continually minimize risk.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
The use of unmanaged and IoT devices in enterprises is growing exponentially, and will account for 55.7 billion connected devices by the end of 2025. A critical concern is deploying IoT devices without requisite security controls.
While these numbers are numbing, their reality is undeniable. 90% of customers believe digitization has accelerated the importance placed upon security. The World Economic Forum now lists cybersecurity failure as a critical threat, and estimates a gap of more than 3 million security experts worldwide, hindering secure deployments at scale. Furthermore, 83% of IoT-based transactions happen over plaintext channels and not SSL, making them especially risky.
Securing an IoT device can be achieved either through securing the IoT device itself, or hardening the network it accesses. Securing devices can be cumbersome, requiring complex manufacturing partnerships and increasing unit prices, thereby reducing adoption. On the other hand, securing the network is always desirable as it helps secure access, encrypt traffic, and ease management.
Being a leader in both security and networking, Cisco continues to bring security closer to networking, providing the network with built-in security, and enabling the network to act both as sensor and as an enforcer. The convergence of security and networking leverages the network’s intelligence and visibility to enable more-informed decisions on policy and threats.
Cisco uniquely integrates security and networking, for instance we recently integrated Cisco Secure Firewall to operate on Cisco Catalyst 9000 Series switches. Additionally, Secure Firewall can be deployed in a containerized form, on-premises and in clouds. Cisco Secure Firewall classifies traffic and protects applications while stopping exploitation of vulnerable systems. Additionally, we offer Identity Services Engine with AI Endpoint Analytics to passively identify IoT devices and apply segmentation policies. Furthermore, Cisco offers management flexibility by integrating with Cisco Defense Orchestrator and DNA Center and with existing customer tools like SIEMs and XDRs.
Let’s look at three use cases where the addition of Secure Firewall capability on Catalyst 9000 Series switches solves real world problems:
Use case 1: Securing the Smart Building: This solution is ideal to secure smart buildings, converging various IoT systems into a single IT-managed network infrastructure. Smart buildings lower the operational and energy costs. Smarter building systems, however, pose serious security risks as these include so many unmanaged devices such as window shades, lighting, tailored HVAC, and more. One of the methods to secure smart buildings is to control access to avoid manipulation of sensors. Such control is attained with a networking switch with enhanced firewall capability. The firewall ensures granular segmentation, directing policies for traffic generated out of IoT devices, providing access to the right users. This integration also brings security closer to endpoints, making policy orchestration simpler.
Use Case 2: Centrally manage isolated IoT network clusters: IoT devices which communicate with each other in the same subnet typically cannot be routed, which is a challenge. By default, most IoT networks are configured in the same subnet, making it difficult to manage them centrally. Administrators are forced to physically connect to the IoT network to manage and collect telemetry. Furthermore, IoT vendors often charge hefty amounts to update IP addresses of devices. Cisco Secure Firewall, hosted on the Catalyst switch, solves this problem and not only inspects traffic from the IoT network but also translates duplicate IoT IP addresses to unique global IP addresses using NAT for centralized management of isolated IoT networks.
Use Case 3: Securely encrypt IoT traffic passing through a shared IT network: At airports, for example, multiple vendors manage unique systems such as baggage, air quality, biometric access control, etc, which share a common network. IoT traffic is usually in plain text, making it susceptible to packet sniffing, eavesdropping, man-in-the-middle attacks, and other such exploits. The IPSec capability on Cisco Secure Firewall encrypts IoT traffic, securing data transfer and reducing risk.
Cisco’s IoT initiatives join the once disconnected worlds of IT and IoT, unifying networking and security. For further details refer to the At-A Glance and see how and an Australian oil company, Ampol, fortified its retail IoT with Cisco Secure!
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
For Cisco engineers working on Duo, having a remote-first workplace has helped them reach life goals, connect with colleagues around the world, and be intentional communicators. We understand that working remotely can be an adjustment — that’s why we’ve compiled the 10 parts of remote work that surprised our team members most and their advice for navigating the nuances. If you’re interested in being part of a remote-first workplace, check out our open positions.
Senior Engineering Leader David Rines has worked remotely for the past seven years. He’s found that Cisco’s approach to distributed teams has “enabled us to pick up the right talent, and not necessarily local talent. We are moving towards a global, follow the sun environment,” he said.
One of the aspects Rines appreciates most of this structure is getting “a widely varied set of perspectives and experiences that help build a more reliable, more robust product, which is why we’re here.”

Another benefit to having colleagues across the globe is the sharing of recipes, a perk Senior Site Reliability Engineer Bernard Ting particularly enjoys. Proactively communicating with colleagues virtually “helps you to form bonds with people from other teams. You can always learn something new about cultures elsewhere. I talk to people about food and so I’m always gathering recipes from people from all over the world,” Ting shared.
While some may fear that working remotely could lead to feelings of isolation and loneliness, a different camaraderie can flourish in the structure of our distributed teams. With colleagues across time zones, “there’s always someone there who you can reach out to help solve your problem,” Rines said.
Collaboration hours are another way Site Reliability Engineering Manager Jaya Sistla has cultivated virtual community and problem-solving. These hours are blocked off for team members to talk about what they’re working on. “The main thing is being able to ask for help so you don’t go into the rabbit hole debugging things,” Sistla said.
Ting points out that working in a distributed model allows you to really engage in virtual events and conversations. Given that the team mainly communicates through online chat, Ting has found that “forces you to see everyone as equally approachable, which has made me more comfortable reaching out to people from anywhere in the world.”
For folks sharing an office, collaboration can happen through casual chats over coffee. When facing a challenge, you can ask your neighbor for support. While ideally virtual communication could have a similar cadence and spontaneity, the logistics of remote and distributed work require intentionality and being proactive in connecting with colleagues as people and as co-workers.
When Ting first started working remotely, he felt that every meeting needed to be formal and have a business objective. By sharing his feelings with his manager, he was reassured that “socializing is a very important part of teamwork, because if you don’t have a good relationship with your colleagues you’re not going to be able to have healthy discussions, healthy conflict or be able to critique each other when the situation arises.”
Since that conversation, Ting has been more proactive about catching up with colleagues, which can include sharing a coffee over video chat. Duo’s “coffee roulette” formalizes the process as every month, employees who opt in can be randomly paired up for a quick half-hour chat focused exclusively on socializing. Ting has found being proactive about socializing virtually helpful. “It’s made me more intentional with my time and really treasure the social experience you can get,” he said.
Some folks may be concerned that without a manager observing their efforts and work ethic day in and day out, it may be harder to recognize accomplishments and challenges. Ting found that within his team “when you work on projects and in your one-on-ones with your managers, they’re always very intentional about learning what you’ve been doing and seeing what your progress is like on certain projects. I’ve been asked, ‘How do you think you can improve? What are some of the things you’ve been doing outside of the team work?’”

To cultivate cross-team collaboration and education, there are thoughtfully planned virtual lunch and learns. “We schedule training sessions and common meetings at times that are flexible for everyone. If it has to be repeated, we do it so people can comfortably attend rather than stretching themselves and attending at odd hours,” Sistla said.
For Software Engineer Nick Aspinall, an important and fun part of working remotely is keeping in touch with virtual messaging. One unique perk has been getting to create and customize emojis with team members including a few of himself in “various ridiculous states,” he said.
Connecting with colleagues on themed channels focused on personal and professional interests from coffee to pets “makes it really cool because you can meet people across different teams and still get some of the feeling of rubbing elbows that you get when you’re in the office,” Aspinall said. Participating in these virtual conversations boosts morale while also providing an endless supply of cute animal pics.
Given the multi-faceted nature of our work and the importance of consistent information sharing, having different communication channels and formats to communicate data with varying degrees of complexity is vital. Having information readily accessible, accurate and updated is particularly necessary in a field like cybersecurity.
Senior Software Engineer Mario Lopez finds that the variety of information sources contributes to an easeful remote working experience. For instance, for complex architecture decisions or detailing, Duo’s Wiki is the best source.
Software Engineer Hanna Fernandez has benefited from chat channels dedicated to design and engineering topics to “see what everyone’s up to and what thoughts people have,” she said. Sista pointed out these are great places to ask questions and open up dialogue to solve problems.
Our culture is “video-on,” meaning that it is preferred that during video meetings, as much as possible, attendees have their cameras on. Lopez loves this because “you get a bit of that personal human element.”
“We’re all people behind these screens. You definitely get some of people’s personality through text, but you get it more when you actually see them. It’s infectious when you see someone smiling. You’ve got to smile back,” he shared (while we both smiled).
When Fernandez started at Cisco, she was advised to schedule individual meetings with everyone she would be working with on every team that she joined. That suggestion is one she’s applied even virtually.

“It’s a great strategy because I already know that my team is super talented and very smart, but this way I also get to know them as humans beyond their roles,” Fernandez said. Fernandez also finds it important to check in with co-workers and ask how they’re feeling and how their time off was. “I know a lot of people hate small talk, but it’s not just small talk. I’m genuinely interested in how my co-workers are doing.”
One of Ting’s biggest goals was buying his first house in the countryside outside of London. By working remotely, Ting has flexibility in his location which allowed him to achieve his goal of buying a house and settling down with his partner, while giving their dogs the space they need to be dogs.

When transitioning from fully remote to hybrid, it’s important to recognize that there will be some shifts to get accustomed to. As the structures of remote, distributed and hybrid work evolve, it’s important to stay flexible and notice what’s possible through multiple modalities of team building. Many teams have enjoyed in-person gatherings and connecting through virtual lunches and team games when remote.
Fernandez has had multiple roles with multiple structures at Cisco. As an intern, she was fully in person and shared desk space with other interns who collaborated on full stack engineering. While working in finance IT, Fernandez was hybrid and many of her colleagues were distributed among multiple offices. The pandemic began while she was in a DevOps role, forcing her to maintain boundaries around her work time while working fully remotely. In her current role working on Duo, Fernandez is completely remote but advocates for in-person events if possible, because “humans are social creatures who want to see each other’s faces in real life once in a while.”
For Aspinall, “when we did come back to the office, there was a bit of an adjustment period where you were overstimulated from the office.” He also wanted to ensure team members who were 100% remote were fully included. Now he sees that while half his team is fully remote and the other half is hybrid, “that doesn’t stop anyone from doing anything. All of our meetings feel the same. They’re all seamless.”
If you’re interested in joining our team from wherever you are in the world, check out our open roles.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Cybersecurity professionals are often perceived as sole practitioners, plying their craft in dimly lit rooms. Nothing could be further from the truth, as one of the keys to being a successful cybersecurity professional is the ability to collaborate and, more importantly, to share knowledge as far and wide as possible.
At Cisco, we have formed the Cisco Insider Advocacy program, which consists of a global community of professionals passionate about working and spreading their knowledge with others. We celebrate these individuals’ efforts with annual awards in various disciplines and locales. In 2023, Cisco will recognize top advocates by region for the Global Advocate Awards. Our first event – highlighting Cisco customers from across the EMEA region – is around the corner. It all happens at Cisco Live in Amsterdam, in a live ceremony on February 8!
I am joined on the Advocate Awards judges’ panel by my colleagues, Cindy Valladares, Director of Brand Strategy and Customer Advocacy at Cisco Secure, Caroline Surujpaul, EMEA and European Marketing Director at Cisco Secure and Sarah Stephens, Senior Security Marketing Leader for EMEA at Cisco Secure. We are pleased to introduce the nominees for the Cybersecurity Defender of the Year Award in EMEA.
We have five distinguished nominees, and while we have yet to select a winner, you will see how each of their contributions to Cisco’s cybersecurity community raised our attention.
Alessandro was featured in a recent successful case study about the Future of Work with Umbrella, as well as an earlier piece about simplified security using Cisco Meraki in Talent Garden.
Alessandro also authored a book about digital transformation long before it was a common buzzword. That is typical of Alessandro’s foresight, the ability to be proactive to changes before they are commonplace. He is indeed on the cutting edge.
Alessandro considers his involvement in the Advocacy community as “a very easy goal for me. First, because I’m very passionate about cybersecurity, and second because here I can find very valuable peers and professionals to share information with.” Alessandro’s abilities are borne from passion, drive, and adherence to a personal code of excellence; he learned security in a strictly hands-on style. He is also a member of Cisco’s “League of Cybersecurity Heroes.”
Christoffer, the newest Cisco Insider Advocacy community member, has gotten off to a brisk involvement with the group. He was recently featured in the case study “NTNU Supports a Diverse Academic and Research Community with Proactive Security,” which detailed how the Norwegian University of Science and Technology tackled the management of a dizzying 110,000 endpoints connecting to the university’s VPN.
Christoffer fully embraces the ideology of collaboration, mentioning that when he was seeking a security solution, “We didn’t want a vendor. We didn’t want a product. We wanted a partner to help us attack this large problem of cybersecurity.” He also demonstrates a fervent dedication to sharing by authoring half a dozen works in the cybersecurity realm, ranging from scientific to academic articles. His involvement in the Insider Advocacy community has earned him a spot in Cisco’s “League of Cybersecurity Heroes.”
Mark is one of the most erudite cybersecurity professionals one could meet. He has extensive educational credentials and enjoys sharing his knowledge, making him one of the Top 10 most engaged advocates of the Cybersecurity Channel within the Cisco Insider Advocates community.
Mark’s professional involvement extends beyond his local precinct, offering his knowledge of security best practices across the UK Policing community. In completing his most recent university degree, he authored a dissertation that “has led to an initiative to improve the security posture of my workplace.” Mark’s support to other Cisco customers has also led to his election as Vice-Chair of the Internet Society Cybersecurity Special Interest Group. He is also a member of Cisco’s “League of Cybersecurity Heroes.”
Luigi is a valuable member of the Insider Advocacy group and was recently featured in a video and written success story about Zero Trust and XDR.
Luigi is an agent of change who embraces the collaborative spirit of a true cybersecurity expert, as exemplified in his entire professional approach: “Since the infrastructure is now cloud-based, we had to change our mindset regarding cybersecurity as well. It was important to have the people, the process, the organisation, and the technology under the same security umbrella.”
When not working to ensure the security of the Sara Assicurazioni environment, Luigi has dedicated time to speaking at events, such as the “Experts Learning from Experts” global virtual session, a special virtual roundtable dedicated to Zero Trust and, last but not least, his presentation at Cisco Live Emea in Amsterdam about XDR and Zero Trust. His contributions to the Insider Advocacy platform reflect a tireless commitment to the cybersecurity community. Luigi is also a member of Cisco’s “League of Cybersecurity Heroes.”
Last year, Diego participated as speaker at the Tech Forum: Convergencia entre redes y seguridad. He will also be featured in a future ThreatWise TV – Cisco episode
Diego recognised early on that remote work would place his organisation outside the scope of their security and took proactive measures to meet the challenge. Part of his proactive approach is to freely communicate his ideas, leading to his involvement in the Insider Advocacy community. This has also earned him a place within Cisco’s “League of Cybersecurity Heroes.”
Diego’s view of working with Cisco’s products is summed up in a catchy phrase: “If it’s connected, it’s protected.” His involvement within the Insider Advocacy community makes us echo that sentiment by stating that he is connected, helping to keep everyone protected.
One point of note is the absence of women from the list of nominees. This was not the result of bias, as Cisco has a history of substantial diversity, equity, and inclusion. As you can see from the activities of the current nominees, the selection was based strictly on contributions to the community. We would love to see more engagement and membership in the Insider Advocacy program, not only from women but from a broader geographic area. This would increase the choices of possible nominees and add an even wider palette of inclusion to the entire nomination process.
We know that there is an entire population of cybersecurity professionals who seek more connection with like-minded individuals, and we welcome you to join this cohesive community.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Speaking to many CISOs, it’s clear that many security executives view zero trust as a journey that can be difficult to start, and one that even makes identifying successful outcomes a challenge. Simultaneously, the topic of security resilience has risen up the C-level agenda and is now another focus for security teams. So, are these complementary? Or will they present conflicting demands that will disrupt rather than assist the CISO in their role?
One of the most striking results coming from Cisco’s latest Security Outcomes Report is that organizations with a mature zero trust implementation – those with basic controls, constant validation and automated workflows – experience a 30% improvement in security resilience compared to those who have not started their zero trust journey. So, these two initiatives – implementing zero trust and working to achieve security resilience – appear to complement each other while supporting the CISO when a cyber black swan swims in.
Security resilience is the ability to withstand an incident and recover more strongly. In other words, ride out the storm and come back better. Meanwhile, zero trust is best known as a “never trust, always verify” principle. The idea is to check before you provide access, and authenticate identity based on a risk profile of assets and users. This starts to explain why the two are complementary.
The Security Outcomes Report summarizes the results of a survey of more than 4,700 security professionals. Among the insights that emerge are nine security resilience outcomes they consider most important. The top three outcomes for resilience are prevention, mitigation and adaptation. In other words, they prioritize first the ability to avoid an incident by having the right controls in place, then the ability to reduce and reverse the overall impact when an incident occurs, and then the ability to pivot rapidly without being bound by too rigid a set of systems. Zero trust will support these outcomes.
Preventing, or reducing the likelihood of a cybersecurity incident, is an obvious first step and no surprise as the most important outcome. Pursuing programs that identify users and monitor the health of devices is a crucial a preventative step. In fact, simply ensuring that multifactor authentication (MFA) is ubiquitous across the organization can bring an 11% improvement in security resilience.
When incidents occur, security teams will need a clear picture of the incident they are having to manage. This will help in them respond quickly, with a proactive determination of recovery requirements. Previous studies show that once a team achieves 80% coverage of critical systems, the ability to maintain continuity increases measurably. This knowledge will also help teams develop more focused incident response processes. A mature zero trust environment has also been found to almost double a team’s ability to streamline these processes when compared to a limited zero trust implementation.
When talking to CISOs about successful implementation programs, communication within the business emerges as a recurring theme. Security teams must inform and guide users through the phases of zero trust implementation, while emphasizing the benefits to them. When users are aware of their responsibility to keep the organization secure, they take a participatory role in an important aspect of the business. So, when an incident occurs, they can support the company’s response. This increases resilience. Research has shown that a mature program will more than double the effect of efforts to improve the security culture. Additionally, the same communication channels established to spread the word of zero trust now can be called upon when an incident requires immediate action.
Mature implementations have also been seen to help increase cost effectiveness and reduce unplanned work. This releases more resource to cope with the unexpected – another important driver of resilience surfaced in Volume 3 of the Security Outcomes Report. Having more efficient resources enables the security function to reallocate teams when needed. Reviewing and updating resource processes and procedures, along with all other important processes, is a vital part of any of any change initiative. Mature zero trust environments reflect this commitment continuous assessment and improvement.
Inherent in organizational resilience is the ability to adapt and innovate. The corporate landscape is littered with examples of those who failed to do those two things. A zero trust environment enables organizations to lower their risk of incidents while adapting their security posture to fit the ongoing changes of the business. Think of developing new partners, supporting new products remotely, securing a changing supply chain. The basic tenets of MFA – including continuous validation, segmentation and automation – sets a foundation that accommodates those changes without compromising security. The view that security makes change difficult is becoming obsolete. With zero trust and other keys to achieving security resilience, security now is a partner in business change. And for those CISOs who fear even starting this journey, understanding the benefits should help them take that first step.
Download the Security Outcomes Report, Vol. 3: Achieving Security Resilience today.
Learn more about cybersecurity research and security resilience:
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Oh, the scammers online are frightful, and the deals they offer seem delightful. No matter what you think you know, let it go, let it go, let it go (to the tune of 1945’s Let it Snow by Vaughn Monroe with the Norton Sisters).
‘Tis the season to find ourselves awash in good tidings and, well, consumerism. While it’s only partly tongue in cheek, we must be honest with ourselves. We spend a lot of money online. Often, we find ourselves leaving things to the last minute and hope that the delivery folks can make the magic happen and send us all the widgets and grapple grommets while we surf the Internet from the safety of our sofas with coffee in hand.
But, not every deal is what it appears to be. Scammers are always lurking in the void of the Internet waiting for a chance to fleece the unexpecting from their hard-earned money. This can manifest itself to the unsuspecting in many ways. There are shipping frauds, gift card giveaways and vishing (phone-based scams).
Scams tend to rely on generating a false sense of urgency. The shipping scam emails often show up in our inboxes as a warning about a missed or delayed package that will be sent back to the point of origin if we don’t answer quickly. Of course, this requires a payment to receive the fictitious package.
These types of shipping scam emails are quite effective this time of year when more often than naught many people have enough orders coming to their house to make a fort with the empty boxes.
The other kinds of attacks are the gift card scams and vishing. The first of which taps into the sense of excitement that a person might receive something for free. “Fill out this form with your credit card information for a chance to win a $200 gift card.” Sadly, this attack works well for older generations for which giveaways were more common and they aren’t as accustomed to spotting digital swindlers.
The last scam that we will tackle here is often labeled as vishing or voice phishing. This is a method whereby the attackers call a victim and attempt to convince their target that they need to do something which will lead to the exposure of financial information while pressuring the victim to think if they don’t act quickly that they will miss an opportunity for personal gain.
Unfortunately, the aforementioned scams really bring in a lot of return for the criminal element. In 2021, over 92,000 victims over the age of 60 reported losses of $1.7 billion. This represents a 74 percent increase in losses over losses reported in 2020.
One additional scam that plays on the heart strings is the romance scams. A lot of single people find themselves lonely during the holidays and can be manipulated into thinking that they’ve found a romantic match. But this can drain the bank accounts as well.
In 2021, the IC3 received reports from 7,658 victims who experienced over $432 million in losses to Confidence Fraud/Romance scams. This type of fraud accounts for the highest losses reported by victims over the age of 60.
All these attacks prey on people’s emotional responses. So, how do we prepare ourselves? We need to make knowledge a capability and arm ourselves with information that will help us avoid being taken advantage of by criminals.
Passwords are a significant exposure. They are the digital equivalent of a house key. A password will work for anyone that has access to it. We need to utilize technologies such as multi-factor authentication (MFA) on websites where it is possible to do so. So even if bad actors have our password, the victim still needs to approve the login.
If we don’t have the option to use MFA it would be an excellent idea to make use of a password manager. This is a way to safely store passwords and not fall into the trap of reusing passwords on multiple sites. Attackers bank on human nature and if we use the same credentials on multiple sites there is a high possibility that the criminals could gain access to other sites if they compromise just one.
I’m usually one to eschew the practice of New Year’s resolutions but I’ll make an exception. Keep a keen sense about yourselves whenever you receive an email or SMS that you were not expecting. If a deal is too good to be true then, well, it most likely is a scam. If you’re in doubt, try to look up the phone number, email address, person or “organization” offering the “deal.” More often than not, you’ll find lots of people reporting that it’s a scam.
Rather than being visited by the three ghosts of holiday scams, make sure you and your loved ones are prepared for a happy holiday and a prosperous New Year.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
In our last blog, we gave a rundown of what the Telecommunications (Security) Act (TSA) is, why it’s been introduced, who it affects, when it starts, and how firms can prepare. Here, we take a closer look into the themes introduced by the Act, explore how the telecoms industry can explore zero trust to further improve its security posture, and outline the benefits that can be gained when complying.
When the Telecoms Security Act (TSA) was introduced, it was labelled as ‘one of the strongest telecoms security regimes in the world, a rise in standards across the board, set by the government rather than the industry’ by Matt Warman, former Minister of State at the Department for Digital, Culture, Media, and Sport. The industry is certainly feeling the impending impact of the act – with one industry pundit at an event we ran recently describing it as a ‘multi-generational change’ for the sector.
One of the headline grabbers stemming from the Act are the associated fines. With the new powers granted to it by the Act, Ofcom now has the responsibility to oversee operators’ security policies and impose fines of up to 10 percent of turnover or £100,000 a day in case operators don’t comply or the blanket ban of telecoms vendors such as Huawei. Sounds like the typical ‘stick’-based costly compliance messaging that no-one particularly wants to hear, right? But what if the TSA had some ‘carrot’-based business benefits that are much less discussed?
The TSA introduces a new security framework for the UK telecoms sector to ensure that public telecommunications providers operate secure and resilient networks and services and manage their supply chains appropriately. ny of the themes introduced in the code of practice can be aligned with the themes in a zero trust security model, which are also a focus for CISOs.
Zero trust security is a concept (also known as ‘never trust, always verify’) which establishes trust in users and devices through authentication and continuous monitoring of each access attempt, with custom security policies that protect every application. At Duo, our approach to zero trust is:
A crucial point to note here: much like a solution that claims to help with all aspects of the TSA, telecom providers should be wary of any vendor who claims to have a zero-trust product. Both are far much bigger than any ‘silver bullet’ solution purports to offer. But there is a good reason a zero-trust framework has been mandated by the US White House for all federal agencies, and recommended by the Australian Cyber Security Centre (ACSC) and the UK’s National Cyber Security Centre (NCSC).
As well as helping to mitigate the significant cyber risks presented to the telecoms industry, a zero-trust strategy provides many business benefits. Our recent Guide to Zero Trust Maturity shows that:
A robust zero-trust security program includes phishing-resistant multi factor authentication (MFA), access controls for devices and applications, risk-signalling, dynamic authentication, firewalls, analytics, web monitoring and more. As I said previously there is no one answer to zero trust, or indeed the TSA, but getting the basics right like strong MFA, single sign on (SSO) and device trust are an easy and effective way to get started.
The TSA will be a huge undertaking for industry, but it is important to focus on the benefits such a wide-reaching set of regulatory rules will inevitably result in. As another guest from our recent event put it: ‘the TSA is full of the latest and modern best practice around security, so the aim really is to raise the tide and all ships, which can only be a good thing.’
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Cyber security implies protecting the confidentiality, availability and integrity of computer systems and networks. Often security researchers and security teams focus on threats to software and the risks associated with authenticating and managing users. However, computing systems are built upon a tall stack of computing resources.
Each layer within the stack is exposed to specific threats which need to be considered as part of a cyber security strategy. As the threat landscape evolves and exposure to risk changes, organizations need to review their threat exposure and consider if current mitigations are sufficient for their needs.
The recent disruption of the Nord Stream submarine gas pipeline in the Baltic Sea by an apparent act of sabotage highlights the risks to infrastructure located beneath the waves. The telecommunications infrastructure that carries internet traffic between countries and continents is often provided by submarine cables. These cables are relatively few in number but carry vast amounts of internet and enterprise traffic, potentially from many different service providers.
The seabed is a challenging environment for infrastructure. Sea water is corrosive, the pressure on the ocean floor can be extreme, while earthquakes, ship’s anchors and dredging provide additional risks to may result in the severing of a cable. Submarine cables are only expected to achieve a lifespan in the region of 25 years before failure.
Repairing or replacing a submarine cable is expensive and time consuming. It may be many months before a failed cable can be repaired or replaced. In the absence of a functioning cable, internet connections must be rerouted to avoid disruption. However, this risks saturating the remaining infrastructure and adversely affecting the quality of connections.
Organizations that require high availability international or intercontinental network connections should review their exposure to the risk of submarine cables failure. The nature of this risk will depend on how services are currently delivered.
At the time of writing there is no specific threat to undersea infrastructure. Other than attacks against terrestrial cables, no cable damage has been shown to be due to sabotage. Nevertheless, the Secretary General of NATO has stressed the importance of undersea cables to civilian society and military capability [1]. The British Chief of Defense Staff has warned how seriously intentional damage to telecommunications cables would be taken [2].
Physical infrastructure can not be taken for granted. Organizations would do well to review the impact of one or more submarine cables being taken out of service. Preparing response plans and contingencies in advance ensures that disruption is kept to a minimum in the event that such a scenario occurs.
[1]. Press Conference (22 Oct 2020), NATO Secretary General Jens Stoltenberg.
https://www.nato.int/cps/en/natohq/opinions_178946.htm?selectedLocale=en
[2]. “Chief of Defence Staff: Russia cutting underwater cables could be ‘an act of war’” (8 Jan 2022), Forces.net.
https://www.forces.net/news/chief-defence-staff-russia-cutting-underwater-cables-could-be-act-war
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
SaaS Security Marketing Manager Laura O’Melia has always been interested in living and working internationally. After living in Austin, Texas for twenty years, O’Melia was ready for a new adventure and decided to move to Sydney, Australia with the support and encouragement of her manager and Cisco. The pandemic delayed her plans, but now that O’Melia’s settling into life and work in Australia, she shared how she made the move to work from anywhere and how you can, too.

What do you do?
O’Melia: I am on the Security Marketing team and focus on driving demand for our Zero Trust solution in the Asia-Pacific, Japan and China (APJC) region. I work closely with the Sales teams to do activities that will generate pipeline and educate prospects on our security solutions. I spend time finding new leads and trying new ways to engage with our top prospects while having fun along the way.
What do you like most about working at Cisco?
O’Melia: What I love most about working at Cisco is the amount of positive contributions we get to have on the world, from solving some of the world’s biggest problems around cybersecurity to giving money and resources to others in need. I also love the feeling of empowerment to create my own work/life balance as Cisco allows me the opportunity to have a flexible schedule.
What has been your career journey within Cisco?
O’Melia: I started at Duo Security in 2017. While working in Field Marketing, I was able to gain experience across many different teams. For example, I worked closely with a region in the U.S. as well as the Managed Service Provider team, which is a global team with a completely different business model. The needs differ greatly, from how we report and track metrics to the messaging and offers from one team to the next. I am now working in a very different market that is much larger and includes many more languages, so that brings a new level of understanding to how we show up in the market to achieve business goals.

“Stepping outside of my comfort zone is one of my favorite things to do.”
– Laura O’Melia
What prompted you to relocate from Austin, Texas to Sydney, Australia?
O’Melia: Austin is great and was my home for 20 years, but I still wanted to gain international work experience to learn what it would be like somewhere else and compare it to what I know.
Stepping outside of my comfort zone is one of my favorite things to do, so when I heard Duo was expanding internationally and there was an opportunity in Australia, I was immediately interested. Everyone I know that has visited Australia always has absolutely wonderful things to say, so without ever having visited I agreed to take a long-term international two-year assignment.
How has Cisco supported your relocation?
O’Melia: I worked closely with my manager on the process from start to finish. We had the support of Cisco’s Mobility Services team, a group of Cisco employees that help with relocation services. We worked with immigration to obtain my work visa. I was planning to relocate in March 2020 but as we know, the borders were closed and visas were not being processed for nearly two years. I was already in-role, so continued to support the APJC team from Austin.
When the time came, Cisco had a team of experts that I worked with to pack and ship my belongings and help get set up with an overseas bank. I also worked with a realtor to help me find a place to live, and the team even assists with my U.S. and Australian tax returns while I am away.
How has your work changed since relocating?
O’Melia: My role has expanded from doing lead-gen events for Duo in Australia and New Zealand to now being responsible for driving demand across the APJC region through digital campaigns and other marketing channels. I still strive to provide qualified leads to Sales and educate the market on our offerings. My goal is to help get Cisco Secure solutions into more doors to ultimately give users a better experience and stop the bad actors from doing harm.
What advice do you have for others who want to work from anywhere?
O’Melia: If you get the opportunity, take it. Everyone has their own path, but if you feel your career could benefit, even slightly, from the experience you will gain moving to another country and figuring things out far from what you know today, why not give it a try? You can learn so much from meeting and working with people that have a very different experience than you might know.
Ready for an adventure? If you want to solve global challenges through cybersecurity with the potential to work anywhere, check out our open roles.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Welcome back! In our last article, you cleared out your extraneous digital footprints by removing unnecessary accounts and opting-out of data broker services, and have finished a dedicated review of your online history. In this final section, we will answer the natural question encountered at the end of any journey: What’s next?
Before becoming the series you’ve just read, I presented a version of this many times as a live talk at conferences and training sessions. After the first few talks, I noticed a consistent trend in the feedback when I was approached afterwards: people who said they felt anxious about how their online activity going forward might share more than they want. So I went back and added a final section to the talk, one that we’re going to cover together now: risk acceptance and the value of routine in good security.
Some people think that the goal of good security is to eliminate risk. One of the first lessons you learn in this industry, though, is that eradicating every possible risk is very rarely practical, whether we’re talking about the individual or organizational level. This is because there are few choices one can make with zero possibility of a negative outcome, and because human beings are… human, and even with excellent discipline and good intent the best of us can mess up.
The goal of good security strategy is instead to assess risk and find a healthy balance: to decide what is more or less important and valuable, to determine how damaging the worst-case scenario might be and weigh that against the potential benefits, and figuring out how much you can reasonably do to tip the balance and increase your odds of success.
That’s fairly abstract, so let’s use a couple quick practical examples at both levels:
I don’t know about you, but I grew up as a child of the internet, and the thought of never going online again isn’t one I’m likely to seriously consider. So rather than logging off forever, let’s focus on how we can both stay safe and stay connected. We’ve completed the “3 R’s” of the self-dox process: Review, Restrict, and Remove. But now, a surprise more shocking than the Spanish Inquisition itself: we’re going to add two final steps-Repeat and Refine.
Every good security plan includes a plan for routine follow-up. We know that staying offline forever isn’t practical, so the next best thing is to set up a reminder to go through an easier version of this checklist on a regular schedule. Why is it easier? In this review, you had to look back on your entire life up to the present, and next time you’ll just need to look back from then to… well… now! Depending on how active you are online and how likely you are to be doxxed, this might make sense to do on an annual basis, or split into abbreviated and more frequent quarterly reviews.
There is no one-size-fits-all approach to this review, but here are some typical checks you may want to consider:
Before we move on to our final (final, I promise!) step, let’s talk one more kind of repeating. A wifi repeater is a gadget that can connect to and boost the signal from a wireless network, helping to expand the network’s reach and keep a strong connection. In the same way, by sharing the lessons you’ve learned with your family and friends you will expand the reach of that security knowledge. Not only does that help keep the people you care about safer… but since we’ve seen how information shared about us by others can also be discovered by doxxers, it helps to increase your own safety as well!
My goal in writing this series was to give a straightforward introduction and broadly-useful walkthrough of how to figure out what’s out there about you online. In the beginning of this series, I talked about how the level of risk for doxxing is not the same for everyone. You may want to go significantly further than we’ve covered in this guide if you are:
This can cover a wide range of additional steps like placing a freeze on your credit report, requesting a privacy removal from search engines, or even setting up dedicated secure devices/apps for communication online. The full scope of these additional protections is beyond what we can cover here, but I will again recommend the Self-Doxxing Guide from AccessNow and the Gender and Tech Safety Resource guide linked in the first post of this series as an excellent reference for where else you might want to check.
Thank you for following along with me on this journey, and I hope that you found this guide and the resources shared have been helpful for you. Still have questions, or have you discovered any of the links/tools here are no longer available? Please let me know! Life comes at you fast on the web, and I want to make sure this guide continues to be relevant and helpful for a long time to come. You can drop me a line at zoe@duo.com, or find me on Twitter. Until then, happy trails and stay safe out there!
If you can’t get enough security content and care deeply about making the web safer for everyone, we’d also love to hear from you. Please check out our open positions and how your passion can contribute to keeping people safe online.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Lots of exciting things happening at Cisco, and for our customers, all to help them better prepare for what’s next. Case in point, we just returned from a very successful Cisco Partner Summit where the spotlight shined on cyber security. When our executives were on stage talking about solutions, the attendees heard a very catchy phrase; “if it’s connected, it’s protected.” A cool phrase, but there is more to that phrase and much more behind it.
To tie both connected and protected together, it’s good to note that Cisco is uniquely positioned as a security vendor with 80% of the worldwide internet traffic running through our network hardware and secured by our open platform, with hundreds of thousands of customers benefitting from automation, and from enriched and prioritized threat intel via our Extended Detection and Response (XDR) capabilities. That means a vast amount of unique insights for our customers to become more resilient, stay ahead of threats, be more confident, and benefit from less risk.
As examples of these questions above:
(1) what about proof points on the above?
(2) and do Cisco’s capabilities align with what customers want and need?
Let’s find out on the first by bringing the XDR aspect of security into the discussion, and the second by observing responses from a Forrester Total Economic Impact 
(TEI) study commissioned by Cisco, both points utilizing our Secure Endpoint solution.
First off, in simple terms, XDR provides the benefit of integrating threat intel from all control points of the security platform and combines that into actionable insights for better, faster, and where appropriate, prioritized remediation of the most critical threats, i.e. XDR helps security teams to identify the threats that can do the most damage and enables the workflows to neutralize those threats first.
And here is where the proof point comes in. One of the most critical components of XDR is endpoint security. And in the case of Cisco, it’s our Secure Endpoint solution. Cisco recently participated in the AV-Comparatives’ Endpoint Prevention and Response (EPR) Test. The AV-C test is described by that independent test organization as “… the most comprehensive test of EPR products ever performed.” Secure Endpoint was one of the 10 endpoint security products in the test that were subjected to 50 separate targeted attack scenarios, which used a variety of different techniques.
Here are the highlights of the AV-C EPR report where Cisco Secure Endpoint:
Stunning results and confidence building for our customers that Cisco is effective in endpoint security. Read the complete AV-C EPR Test Report here.
And then, what about the second proof point – is Cisco providing what customers want & need?
Cisco commissioned Forrester Consulting to perform an unbiased cost-benefit analysis of our Cisco Secure Endpoint product. The report yielded the highlights below, based upon a composite organization, and also includes 20+ outstanding customer quotes.
Here’s the Forrester TEI Study bottom line for the composite organization:
Very good results and again, confidence building for our customers that Cisco is effective in endpoint security. Read the Forrester “The Total Economic Impact Of Cisco Secure Endpoint” Study here.
Of Cisco Secure Endpoint” Study here.
One last thing, what about those customer quotes? Here are a couple of examples:
Director of IT security, logistics
Director of IT security, logistics
To find out more, read Forrester’s “The Total Economic Impact Of Cisco Secure Endpoint” Study here. And if you are not familiar with Secure Endpoint, or would like to sign up for a free trial, check it out here.
Of Cisco Secure Endpoint” Study here. And if you are not familiar with Secure Endpoint, or would like to sign up for a free trial, check it out here.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Welcome back! Previously in our Go Dox Yourself series, we walked through reviewing what information is available about you online, prioritizing those accounts that are most important or still active, and then restricting how much we share through those accounts and who gets to see it. That’s two out of our three steps — maybe good enough for Meatloaf, but not for us! You’re in the home stretch now, and this is the most straightforward-if-slow portion of the process — so let’s dive right in.
In the review step , along with the top accounts that you wrote out in your initial brain dump, we used some email search tricks and the free services NameCheckup.com and NameChk.com to dig up any unused, forgotten, or now obsolete accounts you might have previously registered under your email address or favorite username (or, as us ʼ80s kids used to say, your “handle.”)

We set those old accounts to the side to focus on your active and sensitive data first, but now it’s time to make Marie Kondo proud and clean out the junk drawers of our online life – if it doesn’t still serve you or spark joy, let’s kiss it goodbye!
In a perfect world, this would be as simple as logging in, going to your account settings and clicking a big ol’ “Cancel My Account” button. However, many sites opt to bury the cancelation settings behind a series of smokescreen menus, sometimes even including a half dozen unskippable “are you SURE you want to leave?” and “but we’ll give you a super good deal to stay!” surveys to click through first.
If you find yourself thwarted and your first search of “[Unwanted Service] cancel” doesn’t take you where you need to go, try checking out AccountKiller. This collaborative resource takes submissions of step-by-step deletion instructions and direct links to cancel for a tremendous number of sites, and even includes phone tree options and direct support numbers for canceling offline accounts as well.
The first pass of your delete list might well be longer than a CVS receipt, because these days the average person has 100 password-protected accounts to manage, but don’t worry! You don’t have to sprint to the finish line, and slow progress checking off a few accounts in short sessions over a few weeks will serve you better than a several-hour slog of trying to clear them all at once and burning out.
An important lesson in security is that operating at max capacity isn’t sustainable all the time, and planning for rest and overflow in our personal security planning is no different. Remember that the work you’re doing is cumulative, each small step is one more forward, and every account you clear now is one less that you’ll need to revisit later.
You might notice that we’ve checked off most of the information from our initial brainstorm: emails, usernames, phone numbers, profile pictures… but so far, we haven’t done much with your location history: the cities you lived in and live now, the cities where you worked or went to school, and the city of your birth. Now that we’re going to see how much information on you is available through data brokers and public record sites, these details will be important to have handy.
For the unfamiliar, data brokers are companies which collect and bundle personal information for everything from ad customization to individual investigation. Brokers collect their data through a wide variety of methods, including:
These metrics and details are bundled and sold, either directly through lookup sites like we’ll review in just a moment, or in demographic bundles (for example, “Resilient Renters” or “Living on Loans: Young Urban Single Parents”). If you’ve ever walked through a car dealership window-shopping and suddenly found sponsored content for that car company in your feed, data brokers are the most likely reason.
For this step you should reference the previously-mentioned Personal Data Removal Workbook provided by Michael Bazzell through his company, IntelTechniques. Bazzell has maintained and updated this workbook for many years now, and it is by far the most comprehensive resource for keeping a handle on who is buying and selling your data.
One of the first things you’ll notice on opening the workbook is the sheer volume of businesses out there buying and selling your data: at time of writing, the current edition includes 220 separate brokers. But much like your initial account inventory likely included a select set of important accounts and a longer list of less-relevant ones, there are less than a dozen brokers who dominate most of the market and should be at the top of your list – and fortunately, they’re also at the top of the workbook! These sites are:
Aside from covering most of the market for data and analytics intelligence, these primary sites often act as “feeders” for smaller providers that are either directly affiliated or collect information for their own databases from the largest providers. Which means that as you remove your data from these sites, you’ll not only check off another box on your list, but you may also reduce the number of hits you find for your information on smaller sites as you work your way down.
Congratulations: if you’ve been following along, you’ve just made it through your self-doxxing! Hopefully you’re feeling much better informed and aware of what tracks you’ve left online, and addressed who you do and do not want to have your… addresses. Join us soon for our wrap-up post where we’ll recap with takeaway lessons, as well as good habits and check-ins to keep you safe going forward.
Care about keeping people and their data safe online? Check out our open roles.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Going beyond the hype, passwordless authentication is now a reality. Cisco Duo’s passwordless authentication is now generally available across all Duo Editions.
“Cisco Duo simplifies the passwordless journey for organizations that want to implement phishing-resistant authentication and adopt a zero trust security strategy.”
—Jack Poller, Senior Analyst, ESG
We received tremendous participation and feedback during our public preview, and we are now excited to bring this capability to our customers and prospects.
“Over the last few years, we have increased our password complexities and required 2FA wherever possible. With this approach, employees had more password lock outs, password fatigue, and forgetting their longer passwords due to password rotations. With Duo Passwordless, we are excited to introduce this feature to our employees to keep our password complexities in place and leverage different Biometric options whether that is using their mobile device, Windows Hello, or a provided FIDO security key.
The Duo Push for passwordless authentication feature is simple and easy and introduces a more pleasant experience overall. Using Duo’s device insight and application policies, we are able to leverage and verify the security of the mobile devices before the device is allowed to be used. To top it off, Duo is connected to our SIEM and our InfoSec team is able to review detailed logs and setup alerts to be able to keep everything secure.”
—Vice President of IT, Banking and Financial Services Customer
As with any new technology, getting to a completely passwordless state will be a journey for many organizations. We see customers typically starting their passwordless journey with web-based applications that support modern authentication. To that effect, Duo’s passwordless authentication is enabled through Duo Single Sign-On (SSO) for federated applications. Customers can choose to integrate their existing SAML Identity provider such as Microsoft (ADFS, Azure), Okta or Ping Identity; or choose to use Duo SSO (Available across all Duo editions).
“Password management is a challenging proposition for many enterprises, especially in light of BYOD and ever increasing sophistication of phishing schemes. Cisco aims to simplify the process with its Duo passwordless authentication that offers out-of-box integrations with popular single sign-on solutions.”
—Will Townsend, Vice President & Principal Analyst, Networking & Security, Moor Insights & Strategy
Duo offers a flexible choice of passwordless authentication options to meet the needs of businesses and their use cases. This includes:
No matter which authentication option you choose, it is secure and inherently multi-factor authentication. We are eliminating the need for the weak knowledge factor (something you know – passwords) which are shared during authentication and can be easily compromised. Instead, we are relying on stronger factors, which are the inherence factor (something you are – biometrics) and possession factor (something you have – a registered device). A user completes this authentication in a single gesture without having to remember a complex string of characters. This significantly improves the user experience and mitigates the risk of stolen credentials and man-in-the-middle (MiTM) attacks.
FIDO2 authentication is regarded as phishing-resistant authentication because it:
Using Duo with FIDO2 authenticators enables organizations to enforce phishing-resistant MFA in their environment. It also complies with the Office of Management and Budget (OMB) guidance issued earlier this year in a memo titled “Moving the U.S. Government Towards Zero Trust Cybersecurity Principles”. The memo specifically requires agencies to use phishing-resistant authentication method.
We understand that getting the IT infrastructure ready to support FIDO2 can be expensive and is typically a long-term project for organizations. In addition, deploying and managing 3rd party security keys creates IT overhead that some organizations are not able to undertake immediately.
Alternatively, using Duo Push for passwordless authentication is an easy, cost effective to get started on a passwordless journey for many organizations, without compromising on security.
We have incorporated security into the login workflow to bind the browser session and the device being used. So, organizations get the same benefits of eliminating use of stolen credentials and mitigation of phishing attacks. To learn more about passwordless authentication with Duo Push, check out our post: Available Now! Passwordless Authentication Is Just a Tap Away.
In addition to going passwordless, many organizations are looking to implement zero trust access in their IT environment. This environment typically is a mix of modern and legacy applications, meaning passwordless cannot be universally adopted. At least not until all applications can support modern authentication.
Additionally, organizations need to support a broad range of use cases to allow access from both managed and unmanaged (personal or 3rd party contractor) devices. And IT security teams need visibility into these devices and the ability to enforce compliance to meet the organization’s security policies such as ensuring that the operating system (OS) and web browser versions are up to date. The importance of verifying device posture at the time of authentication is emphasized in the guidance provided by OMB’s zero trust memorandum – “authorization systems should work to incorporate at least one device-level signal alongside identity information about the authenticated user.”
Duo can help organizations adopt a zero trust security model by enforcing strong user authentication across the board either through passwordless authentication where applicable or thought password + MFA where necessary, while providing a consistent user experience. Further, with capabilities such as device trust and granular adaptive policies, and with our vision for Continuous Trusted Access, organizations get a trusted security partner they can rely on for implementing zero trust access in their environment.
To learn more, check out the eBook – Passwordless: The Future of Authentication, which outlines a 5-step path to get started. And watch the passwordless product demo in this on-demand webinar .
Many of our customers have already begun their passwordless journey. If you are looking to get started as well, sign-up for a free trial and reach out to our amazing representatives.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
With passwords and MFA out of the way, let’s next look at connected apps or services that are tied to our priority accounts. When you log into other sites on the web through Facebook, Google, or another social account, as well as when you install social media apps or games, you are sharing information about those accounts with those services. This may be as limited as the email address and username on file, or may include much more information like your friends list, contacts, likes/subscriptions, or more.
A well-known example of this data-harvesting method is the Cambridge Analytica story, where installing a social media app opened up access to much more information than users realized. (Note: as mentioned in the linked article, Facebook added protective measures to limit the amount of data available to app developers, but connected accounts can still present a liability if misused.)
With this in mind, look under the Security or Privacy section of each of your account’s settings, and review where you have either used this account to log into a third-party website or allowed access when installing an app. Here are some handy links to some of the most common services to check:
If you aren’t going to use the app again or don’t want to share any details, remove them. Once you’ve checked your accounts, repeat this process with all the apps installed on your phone.
Just like connecting a social account to a third-party game can share information like your contact info and friend’s list, installing an app on your mobile device can share information including your contacts, camera roll and more. Fortunately, mobile OSes have gotten much better at notifying users before installation on what information is shared, so you should be able to see which apps might be nosier than you’re comfortable with.
Finally — and this is really for the nerds and techies out there — check if you have any API (short for “application programming interface”) keys or browser extensions connected to your accounts. API keys are commonly used to let different apps or services “talk” between one another. They let you use services like Zapier or IFTTT to do things like have your Spotify favorites automatically saved to a Google Sheet, or check Weather Underground to send a daily email with the forecast.
Browser extensions let you customize a web browser and integrate services, like quickly clicking to save an article for review on a “read it later” service like Instapaper. Even if you trust the developer when installing these apps, they may pose a risk later on if they are recovered or taken over by an attacker. These “zombie extensions” rely on a broad install base from a legitimate service which can later be misused to gather information or launch attacks by a malicious developer.
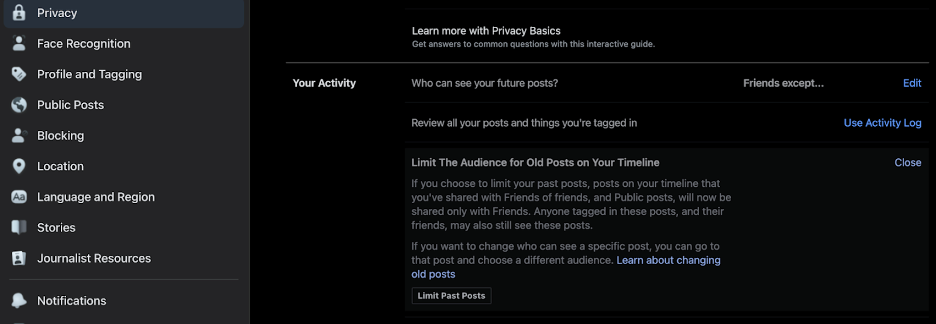
We’ve made great progress already, and taken steps to help defend your accounts from prying eyes going forward – now it’s time to lock down your previous activities on social media. Rather than enumerate every option on every service, I’ll highlight some common tools and privacy settings you’ll want to check:
Before moving on to email, I’ll add another plug for the NYT Social Media Security and Privacy Checklists if you, like me, would rather have a series of boxes to mark off while going through each step above.
Security experts know that you can’t erase the possibility of risk, and it can be counterproductive to build a plan to that expectation. What is realistic and achievable is identifying risk so you know what you’re up against, mitigating risk by following security best practices, and isolating risk where possible so that in the event of an incident, one failure doesn’t have a domino effect affecting other resources. If that seems a bit abstract, let’s take a look at a practical example.
Tech journalist Mat Honan was the unlucky victim of a targeted hack, which resulted in a near-complete lockout from his digital life requiring a Herculean effort to recover. Fortunately for us, Mat documented his experience in the Wired story, “How Apple and Amazon Security Flaws Led to My Epic Hacking,” which offers an excellent summary of exactly the type of domino effect I described. I encourage you to read the full article, but for a CliffsNotes version sufficient for our needs here:
Honan’s article goes into much more detail, including some of the changes made by the services exploited to prevent similar incidents in the future. The key takeaway is that having a couple of emails without strong authentication tied to all his most important accounts, including the recovery of these email accounts themselves, meant that the compromise of his Amazon account quickly snowballed into something much bigger.
We’re going to learn from that painful lesson, and do some segmentation on our email channels based on the priority and how public we want that account to be. (“Segmentation” is an industry term that can be mostly boiled down to “don’t put all your eggs in one basket”, and keep critical or vulnerable resources separate from each other.) I would suggest setting up a few different emails, listed here from least- to most-public:
For all of the above, of course, we’ll create strong passwords and set up 2FA. And speaking of 2FA, you can use the same split-channel approach we followed for email to set up a dedicated verification number (using a VOIP service or something like Google Voice) when sending a passcode by SMS is the only option supported. Keeping these recovery numbers separate from your main phone number reduces the risk of them being leaked, sold, or captured in an unrelated breach.
Good news: We’re almost done with doxxing ourselves! In the next section, we’ll sweep out those unused accounts to avoid leaving data-filled loose ends and take a look at how data brokers profit off of your personal information and what you can do to opt-out.
You’ve made it this far so maybe you’re passionate like we are about developing innovative ways to make security accessible. We’d love for you to join our mission.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
The concept of zero trust is not a new one, and some may even argue that the term is overused. In reality, however, its criticality is growing with each passing day. Why? Because many of today’s attacks begin with the user. According to Verizon’s Data Breach Investigations Report, 82% of breaches involve the human element — whether it’s stolen credentials, phishing, misuse or error.
Additionally, today’s businesses are hyper-connected, meaning that — in addition to your employees — customers, partners and suppliers are all part of your ecosystem. Couple that with hybrid work, IoT, the move to the cloud, and more emboldened attackers, and organizational risk increases exponentially.
Adopting a zero trust model can dramatically reduce this risk by eliminating implicit trust. It has become so crucial, in fact, that several governments including the U.S., UK and Australia have released mandates and guidance for how organizations should deploy zero trust to improve national security.
However, because zero trust is more of a concept than a technology, and so many vendors use the term, organizations struggle with the best way to implement it. At Cisco, we believe you should take a holistic approach to zero trust, starting with what you have and adding on as you identify gaps in your defenses. And while layers of protection are necessary for powerful security, so is ease of use.
Zero trust plays a major role in building security resilience, or the ability to withstand unpredictable threats or changes and emerge stronger. Through zero trust, the identity and security posture of users, devices and applications are continuously checked and verified to prevent network intrusions — and to also limit impact if an unauthorized entity does gain access.
Organizations with high zero trust maturity are twice as likely to achieve business resilience.
– Cisco’s Guide to Zero Trust Maturity
Eliminating trust, however, doesn’t really conjure up images of user-friendly technology. No matter how necessary they are for the business, employees are unlikely to embrace security measures that make their jobs more cumbersome and time-consuming. Instead, they want fast, consistent access to any application no matter where they are or which device they are using.
That’s why Cisco is taking a different approach to zero trust — one that removes friction for the user. For example, with Cisco Secure Access by Duo, organizations can provide those connecting to their network with several quick, easy authentication options. This way, they can put in place multi-factor authentication (MFA) that frustrates attackers, not users.
Cisco Secure Access by Duo is a key pillar of zero trust security, providing industry-leading features for secure access, authentication and device monitoring. Duo is customizable, straightforward to use, and simple to set up. It enables the use of modern authentication methods including biometrics, passwordless and single sign-on (SSO) to help organizations advance zero trust without sacrificing user experience. Duo also provides the flexibility organizations need to enable secure remote access with or without a VPN connection.
During Cisco’s own roll-out of Duo to over 100,000 people, less than 1% of users contacted the help desk for assistance. On an annual basis, Duo is saving Cisco $3.4 million in employee productivity and $500,000 in IT help desk support costs. Furthermore, 86,000 potential compromises are averted by Duo each month.
La-Z-Boy, one of the world’s leading residential furniture producers, also wanted to defend its employees against cybersecurity breaches through MFA and zero trust. It needed a data security solution that worked agnostically, could grow with the company, and that was easy to roll out and implement.
“When COVID first hit and people were sent home to work remotely, we started seeing more hacking activity…” said Craig Vincent, director of IT infrastructure and operations at La-Z-Boy. “We were looking for opportunities to secure our environment with a second factor…. We knew that even post-pandemic we would need a hybrid solution.”
“It was very quick and easy to see where Duo fit into our environment quite well, and worked with any application or legacy app, while deploying quickly.” – Craig Vincent, Director of IT Infrastructure and Operations, La-Z-Boy
Today, Duo helps La-Z-Boy maintain a zero trust framework, stay compliant, and get clear visibility into what is connecting to its network and VPN. Zero trust helps La-Z-Boy secure its organization against threats such as phishing, stolen credentials and out-of-date devices that may be vulnerable to known exploits and malware.
As mentioned, zero trust is a framework, not a single product or technology. For zero trust to be truly effective, it must do four things:
Many technology companies may offer a single component of zero trust, or one aspect of protection, but Cisco’s robust networking and security expertise enables us to provide a holistic zero trust solution. Not only can we support all the steps above, but we can do so across your whole IT ecosystem.
Modern organizations are operating multi-environment ecosystems that include a mix of on-premises and cloud technologies from various vendors. Zero trust solutions should be able to protect across all this infrastructure, no matter which providers are in use. Protections should also extend from the network and cloud to users, devices, applications and data. With Cisco’s extensive security portfolio, operating on multiple clouds and platforms, zero trust controls can be embedded at every layer.
Depending on where you are in your security journey, embedding zero trust at every layer of your infrastructure may sound like a lofty endeavor. That’s why we meet customers where they are on their path to zero trust. Whether your first priority is to meet regulatory requirements, secure hybrid work, protect the cloud, or something else, we have the expertise to help you get started. We provide clear guidance and technologies for zero trust security mapped to established frameworks from organizations like CISA and NIST.
Much of our Cisco Secure portfolio can be used to build a successful zero trust framework, but some examples of what we offer include:
All of our technologies and services are backed by the unparalleled intelligence of Cisco Talos — so you always have up-to-date protection as you build your zero trust architecture. Additionally, our open, integrated security platform — Cisco SecureX — makes it simple to expand and scale your security controls, knowing they will work with your other technologies for more unified defenses.
As Italy’s leading insurance company, Sara Assicurazioni requires complete visibility into its extended network, including a multi-cloud architecture and hybrid workforce. The company has adopted a comprehensive zero trust strategy through Cisco Secure.
“Our decentralized users, endpoints, and cloud-based servers and workloads contribute to a large attack surface,” says Paolo Perrucci, director of information and communications technology architectures and operations at Sara Assicurazioni. “With Cisco, we have the right level of visibility on this surface.”
“The main reason we chose Cisco is that only Cisco can offer a global security solution rather than covering one specific point…. Thanks to Cisco Secure, I’m quite confident that our security posture is now many times better because we are leveraging more scalable, state-of-the-art security solutions.” – Luigi Vassallo, COO & CTO, Sara Assicurazioni
To learn more, explore our zero trust page and sign up for one of our free zero trust workshops.
Watch video: How Cisco implemented zero trust in just five months
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
In the first step of our doxxing research, we collected a list of our online footprint, digging out the most important accounts that you want to protect and obsolete or forgotten accounts you no longer use. Because the most recent and relevant data is likely to live in the accounts you use regularly, our next step will be to review the full scope of what’s visible from these accounts and to set more intentional boundaries on what is shared.
It’s important to note here that the goal isn’t to eliminate every trace of yourself from the internet and never go online again. That’s not realistic for the vast majority of people in our connected world (and I don’t know about you, but even if it was I wouldn’t want to!) And whether it’s planning for an individual or a giant organization, security built to an impossible standard is destined to fail. Instead, we are shifting you from default to intentional sharing, and improving visibility and control over what you do want to share.
Before making changes to the settings and permissions for each of these accounts, we’re going to make sure that access to the account itself is secure. You can start with your email accounts (especially any that you use as a recovery email for forgotten passwords, or use for financial, medical, or other sensitive communications). This shouldn’t take very long for each site, and involves a few straightforward steps:
The best way to prevent a breached password from exposing another account to attack is to use a unique password for for every website you visit. And while you may have heard previous advice on strong passwords (along the lines of “eight or more characters, with a mix of upper/lower case letters, numbers, and special characters”), more recent standards emphasize the importance of longer passwords. For a great explanation of why longer passwords work better than shorter, multi-character type passwords, check out this excellent XKCD strip:
A password manager will make this process much easier, as most have the ability to generate unique passwords and allow you to tailor their length and complexity. While we’re on the topic of what makes a good password, make sure that the password to access your password manager is both long and memorable.
You don’t want to save or auto-fill that password because it acts as the “keys to the kingdom” for everything else, so I recommend following a process like the one outlined in the comic above, or another mnemonic device, to help you remember that password. Once you’ve reset the password, check for a “log out of active devices” option to make sure the new password is used.
MFA uses two or more “factors” verifying something you know, something you have, or something you are. A password is an example of “something you know”, and here are a few of the most common methods used for an additional layer of security:
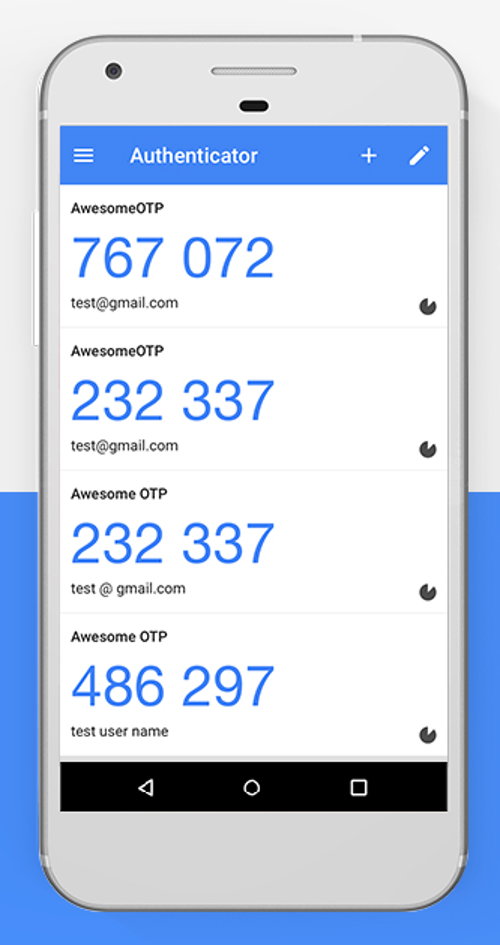

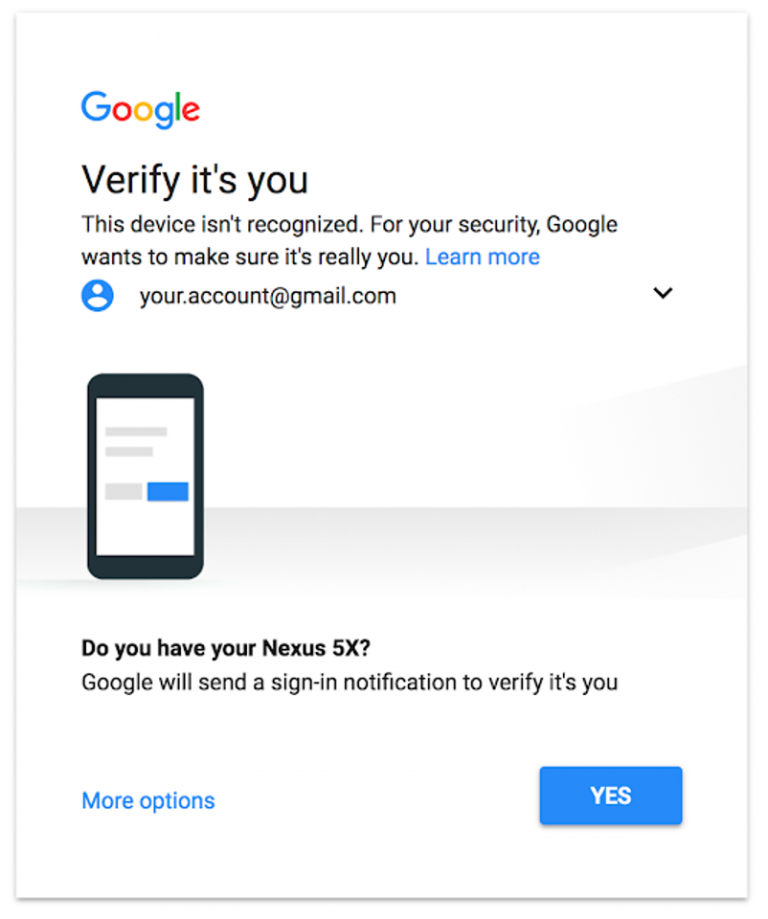
If you want to know more about the different ways you can log in with strong authentication and how they vary in effectiveness, check out the Google Security Team blog post “Understanding the Root Cause of Account Takeover.”
Before we move on from passwords and 2FA, I want to highlight a second step to log in that doesn’t meet the standard of strong authentication: password questions. These are usually either a secondary prompt after entering username and password, or used to verify your identity before sending a password reset link. The problem is that many of the most commonly-used questions rely on semi-public information and, like passcodes, are entered on the same device used to log in.
Another common practice is leveraging common social media quizzes/questionnaires that people post on their social media account. If you’ve seen your friends post their “stage name” by taking the name of their first pet and the street they grew up on, you may notice that’s a combination of two pretty common password questions! While not a very targeted or precise method of attack, the casual sharing of these surveys can have consequences beyond their momentary diversion.
One of the first widely-publicized doxxings happened when Paris Hilton’s contact list, notes, and photos were accessed by resetting her password using the password question, “what is your favorite pet’s name?”. Because Hilton had previously discussed her beloved chihuahua, Tinkerbell, the attacker was able to use this information to access the account.
Sometimes, though, you’ll be required to use these password questions, and in those cases I’ve got a simple rule to keep you safe: lie! That’s right, you won’t be punished if you fib when entering the answers to your password questions so that the answers can’t be researched, and most password managers also include a secure note field that will let you save your questions and answers in case you need to recall them later.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Sharing is caring… but on the internet, sharing can also be tricky! When we post something, we have to look at the forest and not just the trees. Doxxers usually start with one or two pieces of relatively innocent or public information, but by connecting the dots between those pieces they can build a frighteningly detailed picture of an individual.
Seemingly innocuous details can be pieced together into a much more personal profile when collected and leveraged to learn more. As one example, your wish list/wedding registry makes it easy for friends and family to get you gifts that you actually want, but could also be used to find out products/services you’re interested in as pretext (setting the scene) of a conversation or phishing email trying to gather more. You may have Google Alerts set up for your name (a great idea!), but this may not flag text in scanned documents such as school yearbooks, newspapers and other digitized paper records available online.

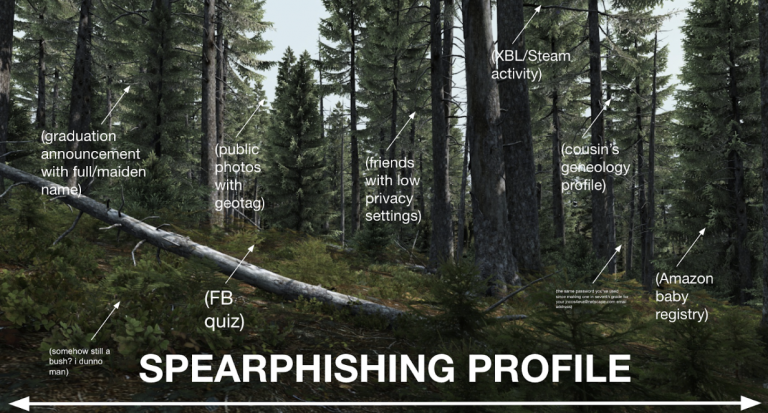
If the above sounds scary – don’t panic! Your first step in this auto-dox is going to be brainstorming as much personally identifying information (PII) shared online as possible. I suggest doing this either in a secure note or longhand. The goal is to write down all of the accounts/addresses/phone numbers that come to mind, as these are some of the top things that attackers will try to gather in their search. Start your list here:
Email addresses are an especially juicy target for someone trying to locate you, because most people only use one personal and maaaybe a second school or work email account. Those accounts are tied to all our other online identities and often double as our username for logging in.
When you finish this process, you will likely have dozens or even hundreds of “breadcrumbs” between your account list and search results. Read through your list again, and we’re going to sort it into three categories:
Great job! You’ve already got a much better idea of what people can learn about you than most folks ever do, and are well on your way to cleaning up your online footprint. In our next step, we’ll start locking down everything that you want to keep!
P.S. If you’re enjoying this process and value keeping people safe online, please check out our open roles at Cisco Secure.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
How do organizations earn and build trust when it comes to the personal data that customers share with them? Customers certainly expect these organizations to comply with all privacy laws that are now in place in more than 130 countries. Customers also expect them not to sell personal data without consent and to try to avoid data breaches that could expose personal data. While these actions are necessary, organizations still need to do more when it comes to customer trust. According to our latest research, consumers’ top priority is, in fact, for organizations to be more transparent about how they use personal data.
The Cisco 2022 Consumer Privacy Survey, released today, explores what organizations can do to earn and build trust with customers, the actions individuals are taking to protect their data, the impact of privacy laws around the world, and some of the benefits and costs of Artificial Intelligence (AI) and data localization requirements. The report, our fourth annual look at consumer privacy issues, draws on anonymous responses from 2600 adults in 12 countries.
Here are some highlights from the survey:
Check out the associated infographic that provides visual and easily consumable descriptions of the key data.
At Cisco, we believe that privacy is a fundamental human right. Privacy continues to be a high priority for consumers, and organizations need to do their part to protect personal data and build consumer confidence in how this data is being used. Some recommendations for organizations include:
Privacy remains a critical element of trust. Consumers want more transparency and control of their personal data, especially as we continue to see innovations in technology. As we are now in the midst of Cybersecurity Awareness Month in the US and other countries around the world, it’s a great time to learn more and join in activities and discussions that advance cybersecurity.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Whether or not you’ve heard the term “doxxing” before, you’re probably familiar with the problem it names: collecting personal information about someone online to track down and reveal their real-life identity. The motivations for doxxing are many, and mostly malicious: for some doxxers, the goal in tracking someone is identity theft. For others, it’s part of a pattern of stalking or online harassment to intimidate, silence or punish their victim – and overwhelmingly, victims are youth and young adults, women, and LGBTQ+ people. The truth is, most of us have information online that we don’t realize can put us at risk, and that’s why I’ve written this series: to inform readers about how doxxing happens, and how you can protect yourself from this very real and growing problem by doxxing yourself.
In computer security, we talk about the idea of a “security mindset”: understanding how someone with bad intentions would cause harm, and being able to think like they would to find weak spots. In this series, you will learn by doing. By understanding the tools and methods used by those with ill intent, you’ll be better prepared to keep yourself safe and your information secure.
Your mission, should you choose to accept it, is to follow along and find out everything the internet knows about… you!
This series will provide simple steps for you to follow as you begin your investigation. Along the way, as you get familiar with the tools and tactics of internet sleuths, you’ll get a better idea of your current internet footprint as well as know what tracks you leave in the future. Our process will be split into three main sections:

Information is power. And in the case of doxxing, most people don’t realize how much of their power they’re giving up! My goal in this series is to demystify the methods used for doxxing, so in the spirit of “showing my work,” here are some of the best resources and collected checklists I referenced when planning these exercises, along with how to best use each:
If this looks like a whole lot of homework… don’t worry! We’ll cover most of the core tools and tips mentioned in these resources through the course of this series, and we’ll revisit these links at the end of the series when you’ve gotten more context on what they cover. In the next article, we’ll take on the review step of our process, getting a holistic inventory of what personal information is currently available online so you can prioritize the most important fixes. See you soon!
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
In November 2020, the Telecommunications (Security) Bill was formally introduced to the UK’s House of Commons by the department for Digital, Culture, Media & Sport. Now, after several readings, debates, committee hearings, and periods of consultation, the Telecommunications (Security) Act is quickly becoming reality for providers of public telecoms networks and services in the UK, going live on 1 October 2022. Here, we outline what exactly the requirements mean for these firms, and what they can do to prepare.
The Act outlines new legal duties on telecoms firms to increase the security of the entire UK network and introduces new regulatory powers to the UK Telecoms regulator OFCOM to regulate Public Telecommunications Providers in the area of cyber security. It place obligations on operators to put in place more measures around the security of their supply chains, which includes the security of the products they procure. The Act grants powers to the Secretary of State to introduce a so-called Code of Practice. It is this Code of Practice which contains the bulk of the technical requirements that operators must comply with. Those not in compliance face large fines (up to 10% of company turnover for one year).
Following the UK Telecoms Supply Chain review in 2018, the government identified three areas of concern that needed addressing:
Following the review, little did we know a major resilience test for the telecoms industry was about to face significant challenges brought on by the Covid-19 pandemic. Data released by Openreach – the UK’s largest broadband network, used by customers of BT, Plusnet, Sky, TalkTalk, Vodafone and Zen – showed that broadband usage more than doubled in 2020 with 50,000 Petabytes (PB) of data being consumed across the country, compared to around 22,000 in 2019.
There is no question the security resilience of the UK telecoms sector is becoming ever more crucial — especially as the government intends to bring gigabit capable broadband to every home and business across the UK by 2025. As outlined in the National Cyber Security Centre’s Security analysis for the UK telecoms sector, ‘As technologies grow and evolve, we must have a security framework that is fit for purpose and ensures the UK’s Critical National Telecoms Infrastructure remains online and secure both now and in the future’.
The legislation will apply to public telecoms providers (including large companies such as BT and Vodafone and smaller companies that offer telecoms networks or services to the public). More specifically to quote the Act itself:
As the requirements are long and varied and so the timelines to comply have been broken down to help organisations comply. The current Code of Practice expects Tier 1 providers to implement ‘the most straightforward and least resource intensive measures’ by 31 March 2024, and the more complex and resource intensive measures by 31 March 2025.
Tier 2 firms have been given an extra two years on top of the dates outlined above to reflect the relative sizes of providers. Tier 3 providers aren’t in scope of the regulatory changes currently but are strongly encouraged to use the Code of Practice as best practice. The Code of Practice also expects that these firms ‘must continue to take appropriate and proportionate measures to comply with their new duties under the Act and the regulations’.
The TSA introduces a range of new requirements for those in the telecoms industry to understand and follow. These will require a multi-year programme for affected organisations. An area of high focus for example will be on Third Party controls and managing the relationship with them.
However there are more common security requirements as well. From our work with many companies across many different industries, we know that establishing that users accessing corporate systems, data and applications are who they say they are is a key aspect of reducing risk by limiting the possibility of attacks coming in through the front door. This is a very real risk highlighted in Verizon’s 2022 Data Breaches Investigations Report, which states that around 82% of data breaches involved a human element, including incidents in which employees expose information directly or making a mistake that enables cyber criminals to access the organisation’s systems.
Therefore, one area to start to try and protect the organisation and take a step on the way to compliance is to build up authentication and secure access to systems, data and applications. However even this can take time to implement over large complex environments. It means gaining an understanding of all devices and ensuring there is a solid profile around them, so they can be reported on, attacks can be blocked and prevented, and access to applications can be controlled as needed.
We will be creating more information around the Act as we move closer to the deadlines, including part two of this blog where we will take a deeper dive into themes introduced by the bill, how it compare with other industries’ and jurisdictions’ cyber security initiatives, and explore what else the telecoms industry can do to improve its security posture.
We are also running an event in London on 13 October: ‘Are you ready for TSA?’ which will include peer discussions where participation is welcome on the TSA. If you are interested in attending, please register here.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Self-awareness goes a long way in determining your next professional steps. While job searching, it’s critical to identify how to leverage your transferable skills and network, while also evaluating what environmental factors of work and work culture matter to you most. Learn what it’s like to work at Cisco and the top 10 ways to suss out a workplace that suits your needs from leaders at Cisco Secure, Cisco Talos and Duo Security.
First things first. Emily Reid, the newly appointed director of employee experience at Cisco Secure who came from Duo Security, advises, “Do your own research to see how the company and their employees describe the culture publicly — on the company’s website and through other sites, articles and resources. For tech companies specifically I always think, “What else do you have beyond the ping-pong table?”’
The interview process is the next key opportunity to find out what culture is like beyond amenities. To gain multiple perspectives, Reid recommends asking about company culture in every interview you have.
The question at the top of Reid’s list: Do you have programs and resources to support the development and success of your employees? “I want to know how a company will be investing in my career growth and if I will feel welcome and included as part of the team. Seeing what a company chooses to center and highlight when describing their culture is usually very telling,” she said.
Interning at a company is another way to get firsthand knowledge and can lead to full-time employment. “several former interns are now people leaders managing their own teams — and their own interns — coming full circle,” Reid said.
Knowing that there is safety and support in bringing your whole self to work is vital. What policies, programs and initiatives are in place that demonstrate an organization’s commitment to diversity, equity, inclusion and belonging?
Cisco’s ongoing commitments to social justice and pay parity include twelve action steps as part of Cisco’s Social Justice Blueprint. Cultivating a conscious culture includes on-going dialogue, programs and events meant to increase equality. Employee Resource Organizations and mentorship programs provide more opportunities to build community and share knowledge, resources and advocacy.
What environment allows you to do your best work? Also consider what perks and processes an employer offers to enhance flexibility and adaptability. During the pandemic, Duo and Cisco transitioned all global events, training and professional development workshops to fully virtual. As in person options resumed following the pandemic, all events are designed to ensure an inclusive experience no matter where you’re joining from.
“We don’t want to go back to a world where people not based in an office feel like they are getting a lesser experience,” Reid said.
Considering how to make programs and information accessible to employees regardless of where they work is also important to Sammi Seaman, team lead of employee experience at Cisco Talos. She’s currently spearheading a new hire program that is “more inclusive of folks whether they’re office based, remote or somewhere across the world.”
It’s essential to consider how you want your life and work to intersect, particularly as hybrid work becomes more popular. How important is paid time off, flexible work options or a consistent structure?
Cisco Secure offers “Days for Me,” days off for employees to decompress and do something to fill their cups. Monthly “Focus Days” are days without meetings, so employees can prioritize the projects that need attention.
Curran recalls one candidate who, despite multiple offers from competitors, chose Cisco Secure because of the flexible work environment: “This person has a young child and felt that the “Days for Me” and flexibility to work from home in a hybrid situation would work best for his career long-term.”
As Reid’s team helps lead the transition to hybrid work, the book Out of Office: The Big Problem and Bigger Promise of Working From Home by Charlie Warzel and Anne Helen Petersen has been inspiring. The book “does an amazing job of sharing a vision for an inclusive future that empowers employees to be successful and have a ‘work/life balance’ that truly works,” Reid said.
Currently Cisco Secure offers a hybrid model while many employees still work remotely. In terms of maintaining accessibility through this transition, Marketing Specialist Julie Kramer advocated for more accessibility and saw changes at Cisco as a result.
“Webex pre-COVID didn’t have any closed captioning. So, another deaf person and I reached out and closed captioning and the transcript option got added,” Kramer shared.
Kramer prefers to have high-quality and frequently the same interpreters who “know the terminology for my job, marketing and technology. In business, the security and marketing industry can really talk fast, so you need a high-quality interpreter that can keep up and one that is qualified and certified,” she said.
Consider what pace of your specific role and within an industry is needed for you to feel engaged without overwhelmed. While different roles within the same organization and industry may run at different paces, it’s important to tune into what might be expected on your potential new team.
Seaman finds that the fast pace of cybersecurity can be “delightful and challenging. There’s a lot of fast-paced pivoting that happens, which makes for an interesting workplace because two days are never the same,” she said.
Do you prefer a hierarchical structure, or one that is more flat? Are you most effective and fulfilled riding solo, or while consistently connecting with coworkers? Does contributing your ideas make you feel empowered?
At Cisco Secure, there is space to join conversations. “No matter where you sit in the company, you have a voice and can speak up and collaborate and self-organize on a project. It feels like a bunch of really hard working, humble, smart people who are trying to solve problems together,” said Manager of Duo’s Global Knowledge and Communities Team Kelly Davenport.
To enhance communication and knowledge among distributed teams, Seaman started a dialogue series called “The More You Know.” Questions include: What do you do? How do you do it? How can that help other parts of Cisco Talos? The conversations lead to future collaboration and resource sharing.
Do you want to grow professionally and increase your skills and knowledge? A culture of teaching and learning within an organization can help hone and expand your skills and connections.
Lead of Strategic Business Intelligence Ashlee Benge finds the security world “very dynamic. You really can never stop learning. Within Cisco Talos, the people around me are such smart, dedicated people that there’s really a lot that you can gain from just being involved in the group as a whole.”
For Seaman, who didn’t come from a technical background, Cisco Talos offered opportunities to expand her technical knowledge, including from colleagues. “Coming into Cisco Talos, people are like, “Here, let me teach you. You can totally do this. Just because you didn’t know how to do it doesn’t mean you can’t learn. Let’s go,” Seaman shared. Seaman’s colleagues have also learned from her expertise in information and knowledge management given her background as a librarian.
More formally, the Learning and Development team recently launched a comprehensive talent development program with enablement resources and support for people leaders. Aspects include: “really thoughtful templates for employees to use with their manager to talk through career goals, development areas, and to define an actionable investment plan. These resources are fueling great career conversations, strong alignment, and thoughtful development plans,” Reid said.
Do you want to refine your skills within your wheelhouse? Or are you driven to try new tasks and potentially change roles within your next organization?
Benge, whose background is in computational astrophysics, has found her interests shift from technical security research to business strategy and data science. At Cisco Talos, she’s been involved in everything from detection research and threat hunting, to community outreach, conference talks and traveling to support sales engagements. Currently, she’s helping to lead threat hunting in Ukraine.
“My leaders have always made it very clear that if there’s an interest, it’s okay to pursue it and it doesn’t have to necessarily be within the scope of my role. Having that freedom to pursue interests within the industry has been really engaging,” Benge said.
In addition to company values and mission statements, leaders and employees contribute to an organization’s culture every day. If you want to enhance your company’s culture, participate.
“Feedback on what employees want to see is crucial,” Reid said. “The easiest way to contribute to developing culture and a positive employee experience in your workplace is to add to what’s already happening! Culture takes participation and ownership from all employees.”
Reid shared that in performance reviews at Cisco, “‘Team Impact” is equally as important as “Results.” Contributing positively to company culture should contribute to performance reviews and promotion justification,” she said.
To learn more about Cisco’s company culture and how you can contribute to it, check out our open roles.

We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Just like the myriad expanding galaxies seen in the latest images from the James Webb space telescope, the cybersecurity landscape consists of a growing number of security technology vendors, each with the goal of addressing the continually evolving threats faced by customers today. In order to be effective, cybersecurity tools have to be collaborative—be it sharing relevant threat intelligence, device & user insights, acting on detection and remediation workflows, and more.
We at Cisco Secure have embraced this concept for a while now with our continually growing ecosystem of multi-vendor technology integrations. At the RSA Conference 2022 earlier this year, Jeetu Patel, Cisco’s Executive Vice President and General Manager of Security and Collaboration, spoke of how the ‘cybersecurity poverty line’ is widening and how malicious actors are taking advantage of this gaping hole to unleash persistent attacks. It is imperative that cybersecurity vendors interact with and collaborate with each other to lower this gap. To do this, security vendors must adopt open ecosystems of APIs to easily integrate with each other to provide effective ways for mutual customers to defend and react to cybersecurity attacks.
Like in prior years, this fiscal year 2022 saw us growing to include new ecosystem partners and integrations. With 22 new partners and 51 new integrations in our ecosystem, Cisco Secure Technical Alliance (CSTA) now boasts over 450 integrations, including technical integrations with Cisco Duo and Cisco Kenna. This allows our mutual customers the freedom to implement the cybersecurity tools of their choice with the knowledge that these tools can integrate with each other if they need to, thus realizing a better return on investment in their cybersecurity spending and improving cybersecurity posture.
In this annual round-up of our ecosystem, we congratulate our new partners in CSTA and existing partners as well, who have either created new integrations across our portfolio or augmented existing ones. For more details on each partner integration in this announcement, please read through the individual partner highlights below.
Happy integrating!
The AlienApp for Cisco Secure Endpoint enables you to automate threat detection and response activities between USM Anywhere and Cisco Secure Endpoint. It also enhances the threat response capabilities of USM Anywhere by providing orchestration and response actions to isolate or un-isolate hosts based on risks identified in USM Anywhere. In addition, it allows you to collect hourly events from Cisco Secure Endpoint through the USM Anywhere Job Scheduler. Read more here.
![]() AttackIQ automates the evaluation of Cisco Secure Endpoint against the tactic categories as outlined by MITRE ATT&CK
AttackIQ automates the evaluation of Cisco Secure Endpoint against the tactic categories as outlined by MITRE ATT&CK . The AttackIQ and Cisco partnership and technical integration enables organizations to validate that the Cisco Secure Endpoint is deployed correctly and configured optimally, ensuring protection for your endpoints against the latest threats. Read more here.
. The AttackIQ and Cisco partnership and technical integration enables organizations to validate that the Cisco Secure Endpoint is deployed correctly and configured optimally, ensuring protection for your endpoints against the latest threats. Read more here.
 With Certego Tactical Response for Cisco Secure Endpoint, monitored endpoints are monitored by the Certego PanOptikon SOAR platform. When Certego IRT detects malicious activities on a specific host in the customer’s network, it can isolate compromised hosts to block the attack, even without requiring the user to access the Cisco Secure Endpoint Console. Read more about the Certego here.
With Certego Tactical Response for Cisco Secure Endpoint, monitored endpoints are monitored by the Certego PanOptikon SOAR platform. When Certego IRT detects malicious activities on a specific host in the customer’s network, it can isolate compromised hosts to block the attack, even without requiring the user to access the Cisco Secure Endpoint Console. Read more about the Certego here.
![]() Cisco Secure Endpoint is now certified for the ServiceNow ITSM San Diego release. The Cisco Secure Endpoint App on ServiceNow provides users with the ability to integrate event data from the Cisco Secure Endpoint into ServiceNow by creating ITSM incidents. The app automates the collection of events from Cisco Secure Endpoint and groups them into single incidents. Read more here.
Cisco Secure Endpoint is now certified for the ServiceNow ITSM San Diego release. The Cisco Secure Endpoint App on ServiceNow provides users with the ability to integrate event data from the Cisco Secure Endpoint into ServiceNow by creating ITSM incidents. The app automates the collection of events from Cisco Secure Endpoint and groups them into single incidents. Read more here.
FAMOC manage from Techstep, a Gartner-recognized MMS provider, is an MDM designed to give IT a complete view and absolute control over mobile devices used by the workforce, so that people can work more effectively and securely. With the Cisco Security Connector for iOS integration, FAMOC MDM extends its enterprise mobility management with an extra layer of network security and traffic analysis tool, giving IT admins tools to make actionable decisions and design access control policies. Read more here.
Elastic Security now supports event ingestion from Cisco Umbrella, providing visibility into user activity and attempts to access potentially malicious domains. This new integration supports Umbrella proxy, cloud firewall, IP, and DNS logs. This integration enables security analysts to detect threats and visualize Cisco Umbrella data, and also correlate Umbrella events with other data sources including endpoint, cloud, and network. This integration expands on Elastic’s on-going expansion of Cisco integrations including ASA, Nexus, Meraki, Duo and Secure Firewall Threat Defense. Read more here.
FortiSIEM brings together visibility, correlation, automated response, and remediation in a single, scalable solution. It reduces the complexity of managing network and security operations to effectively free resources, improve breach detection, and even prevent breaches. Read more here.
Hunters ingests Cisco Umbrella log and alert information into our SOC Platform; the Platform then correlates that information with all of the other (vendor agnostic) customer security telemetry, including EDR, Identity and Cloud/Network log data, in the customer’s infrastructure to synthesize and detect incidents with a higher fidelity than any single tool alone can produce. Read more here.
LearnSafe equips school leaders (K-12) with evidence-based information to better understand which students are exhibiting behavioral issues and in need of help based on what they are using, saying, and doing on the school-owned computer. With Cisco Umbrella, LearnSafe administrators are able to block access to domains their students should not be accessing. Read more here.
The Cisco Umbrella solution for Microsoft Azure Sentinel is now live! This integration enables your customers to ingest Cisco Umbrella events stored in Amazon S3 into Microsoft Sentinel using the Amazon S3 REST API. Read more here.
Sumo Logic’s cloud-native collector supports automatic ingestion of logs from Cisco Umbrella’s hosted AWS S3 buckets. Data collected from Umbrella can then be routed to Sumo’s Cloud SIEM, where it is then automatically normalized and applied to our rule’s engine. Several built-in rules for Umbrella have been created that, when triggered, will generate security signals in the platform. These and other security signals are then clustered together based on related entities (IP, email, domain name, URL, etc.) to create insights for review by the SOC. Read more here.
The Secure Firewall team and Alkira have validated Secure Firewall (Virtual) Version 7.1 to run on Alkira’s cloud network as-a-service (CNaaS) platform. The solution offers on-demand hybrid and multi-cloud connectivity, integrated network and security services, end-to-end visibility, controls and governance. Read more here.
The Secure Firewall team has validated Cyware’s STIX 1.2 threat intelligence feed for interoperability with Secure Firewall’s Threat Intelligence Director. Customers can quickly operationalize the inbound data to protect the network from the latest threats. Read more here.
Dragos protects critical infrastructure and has joined the CSTA program. Dragos inventories assets, determines risk and vulnerabilities and generates firewall policy objects that administrators can apply to their Cisco Secure Firewall deployment through its REST API. Read more here.
The Secure Firewall team and Equinix have validated Secure Firewall (Virtual) to run on Equinix’s Network Edge as a Service platform. Equinix Fabric allows you to connect digital infrastructure and services on demand via secure, software-defined interconnection (Ecosystem). Read more here.
Fastvue has joined the CSTA program. The Fastvue Site Clean engine intelligently interprets Cisco Secure Firewall log data so that non-technical employees can easily see what people are actually doing online. The data use to keep companies compliant with workplace and school policies. Read more here.
Alef Nula has developed a new integration with ISE. The Alef Nula Identity Bridge consumes identity updates published by pxGrid and serves them to ASA firewalls using the CDA/Radius protocol. Using pxGrid v2.0, it replaces unsupported Cisco CDA and allows ASA firewalls to become an identity consumer of ISE context. It can read the full identity database and can update registered ASA firewalls in Full Download mode. Read more here.
Forescout’s pxGrid Plugin integrates with existing Cisco ISE deployments so that you can benefit from Forescout visibility and assessment for policy decisions, while continuing to use ISE as an enforcement point. The pxGrid Plugin enables Forescout platform policies to detect ISE-related properties on endpoints, and to apply Cisco ISE ANC policies, including policies that assign Security Groups to devices. Read more here.
FortiManager provides automation-driven centralized management of Fortinet devices from a single console, enabling full administration and visibility of your network devices through streamlined provisioning and innovative automation tools. FortiManager dynamically collects updates from Cisco ISE with pxGrid and forwards them to FortiGate using the Fortinet Single Sign On (FSSO) protocol. This enables the use of session information collected by Cisco ISE to be leveraged in FortiOS security policies. Read more here.
Radiflow provides OT ICS policy creation and enforcement with the Radiflow iSID IDS. They recently completed a new integration with ISE leveraging pxGrid. With this integration Cisco ISE receives enriched data of OT devices from Radiflow iSID and will process it according to the profiles and policies which have been configured. Enriching ISE with OT specific insights available with iSID’s DPI engine enables better decision making within ISE by providing additional context to categorize devices by their type/function within the OT environment. Read more here.
XTENDISE is a simple web application connected to Cisco ISE. It is designed for administrators, helpdesk, operators or anyone who needs to work with ISE and helps them with everyday routine tasks related to 802.1X without the need to train them in Cisco ISE. XTENDISE saves administrators’ time, prevents errors and increases network security. Read more here.
The Cisco Secure Malware Analytics Add-On for Splunk leverages the Threat Grid API to enrich events within Splunk. The add-on is now updated for Splunk 8 and is available on Splunkbase. Read more here.
Censys now has an integration with SecureX threat response, which returns Sightings of IP and IPv6 Observables (IOCs) in an investigation. Read more about the Censys relay module here.
The new Exabeam integration empowers users to investigate an observable and determine if it is contained in a log message stored in Exabeam Fusion SIEM Data Lake. It provides users with the date and time the observable was seen in the log, the forwarder that sent the log, and the raw log messages. When you pivot into Exabeam and search for an observable in all the log messages, the results of the search are displayed in the Exabeam UI. This integration allows you to query IPv4, IPv6, SHA-1, SHA-256, MD5, domain, URL, file path, user and email data types and it returns sightings of an observable from each log message. Read more here.
The LogRhythm integration empowers users to investigate an observable and determine if it is contained in an event stored in LogRhythm. It provides users with the date and time the observable was seen in the event and the raw event data. This integration allows you to query IPv4 and IPv6 data types and it returns sightings of an observable from each event. Read more here.
A proof-of-concept integration with RSA NetWitness SIEM was built for the RSAC SOC and Black Hat NOCs. The SecureX Concrete Relay implementation using NetWitness as a third-party Cyber Threat Intelligence service provider. The Relay itself is just a simple application written in Python that can be easily packaged and deployed. Read more here.
Cisco SecureX threat response integration with SecOps is now certified for the ServiceNow San Diego release. The module allows ServiceNow SecOps to leverage the Verdicts, Refer and Response capabilities provided by SecureX threat response to assist the security analyst in their investigation workflow. Read more here.
The Sumo Logic Cloud SIEM integration provides security analysts with enhanced visibility across the enterprise to thoroughly understand the impact and context of an attack. Streamlined workflows automatically triage alerts to maximize security analyst efficiency and focus. This integration indicates to users that the observable in an investigation is contained in an insight and/or signal within Sumo Logic Cloud SIEM. It allows you to query IPv4, IPv6, SHA-1, SHA-256, MD5, domain, and URL data types. It also returns sightings and indicators of an observable from each insight and signal retrieved from Sumo Logic Cloud SIEM. Read more here.
APIVoid provides JSON APIs useful for cyber threat analysis, threat detection and threat prevention. The following APIVoid atomic actions for SecureX Orchestration Workflows are now available: Get Domain Reputation, Get IP Reputation, Get URL Reputation, Get URL Status. Access the workflows here.
Censys is a company that allows users to discover the devices, networks, and infrastructure on the Internet and monitor how it changes over time. SecureX orchestration atomic actions for Censys is now available and includes: Basic Search. Access the workflows here.
This integration radically reduces the time and resources enterprises spend to detect, investigate, and remediate ransomware threats to data. It empowers SecOps, ITOps and NetOps with visibility and automation to collaborate in countering ransomware — regardless of whether data resides on-premises or in the cloud — delivering enterprise-wide confidence in deterring, detecting, and recovering fast from cyberattacks. Cohesity’s next-gen data management enhances Cisco SecureX by adding visibility and context to data, complementing Cisco’s existing capabilities for networks, endpoints, clouds, and apps. Read more here.
SecureX orchestration atomic actions for workflows are now available for Farsight Security DNSDB. They include various items like DKIM key inspections, DNS Resource Records and more. Access the workflows here.
SecureX orchestration workflows for Fortinet FortiGate are now available: Block URL, IP and Domain Threat Containment. Access the workflows here.
SecureX orchestration workflows for Jamf Pro include: Lock Computer, Lock Mobile Device. Access the workflows here.
SecureX orchestration workflows for Palo Alto Networks Panorama are now available: Block URL, IP, Domain Threat Containment. Access the workflows here.
A new Orchestration action provides top MacOS IR Indicators to ServiceNow This workflow runs multiple Orbital queries on the endpoint provided to look for top incident response indicators of compromise. The results are then posted to a ServiceNow incident. Supported observables: ip, mac_address, amp_computer_guid, hostname. Access the workflow here.
Shodan is a database of billions of publicly available IP addresses, and it’s used by security experts to analyze network security. SecureX orchestration atomic actions for Shodan include: Basic Search. Access the workflows here.
Earlier this year we announced SecureX Device Insights which provides comprehensive endpoint inventory in a single unified view. Endpoint searching and reporting allows you to assess device security configuration on employee-owned, contractor-owned, company owned, and IoT/OT devices—without risking business disruption. With Device Insights you can
Device insights supports the following third-party sources in its initial release: Jamf Pro, Microsoft Intune, Ivanti MobileIron and VMware Workspace ONE (formerly AirWatch).
Bitglass’ Next-Gen CASB provides data protection, threat protection, access management, and visibility, while Duo offers identity verification options like SSO and MFA. The Duo and Bitglass integration provide a synergistic solution that funnels traffic through Duo’s SSO and verifies users via its MFA so Bitglass can deliver real-time data loss prevention and granular adaptive access control. Because of Bitglass’ agentless architecture, the joint solution can secure any app, any device, anywhere. Read more about the integration here. A joint solution brief is also available here.
Cmd helps companies authenticate and manage user security in Linux production environments without slowing down teams — you don’t need to individually configure identities and devices. Cmd integrates with Duo to put 2FA checkpoints into Linux-based data centers and cloud infrastructure. The combination of Cmd and Duo enables development teams to run at the modern, agile pace they are accustomed to without any security-induced slowdowns. Read more here.
Darktrace is an AI-native platform that delivers self-learning cyber defense and AI investigations and seamlessly integrates with other tools via an open and extensible architecture. Darktrace’s Security Module for Duo provides coverage over access, user sessions and platform administration within the Duo platform. Read more here.
Dashlane is a password manager that now supports Duo using Duo SSO. The integration lets IT Administrators easily deploy Duo + Dashlane and set up access policies. End users can easily access Dashlane and their passwords with SSO from Duo. Read more here.
HashiCorp Vault is an identity-based secrets and encryption management system. A secret is anything that you want to tightly control access to, such as API encryption keys, passwords, and certificates. Add another layer of protection and protect access to secrets within HashiCorp Vault with Duo Security MFA. Read more here. A recording of the Cisco Duo + HashiCorp webinar is available to view here.
Oort discovers vulnerabilities across an entire user population (or a segment of it). Trigger notifications related to behavioral anomalies or best practices, or policies not being followed. Oort integrates with Duo for identity analytics and threat detection to provide a complete picture of the user behavior and highlight any anomalous activity or identify risks. Read more here.
Perimeter 81 simplifies cyber and network security for the hybrid workforce, ensuring secure access to local networks, applications, and cloud infrastructure. Their integration with Duo provides protection for administrators and end-users who need to log in to Perimeter 81. Read more here.
Specops Software, a leading provider of password management and authentication solutions, protects businesses by securing user authentication across high-risk tasks including account unlocks and password recovery via self-service or the IT service desk. Organizations can extend Duo authentication to secure user verification across these use cases. Read about the integration here. A blog on the integration is also available here.
Sectona is a Privileged Access Management company that delivers integrated privilege management components for securing dynamic remote workforce access across on-premises or cloud workloads, endpoints, and machine-to-machine communication. Duo’s secure access multi-factor authentication can be used to ensure that each user authenticates using multiple methods (factors) while accessing Sectona Privileged Access Management. Read more here.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Over her 25-year-plus career, Saleema Syed has seen the information security industry from a variety of vantage points, all while championing women in technology. Syed worked as director of business systems and data management for Duo Security before rising to vice president of information technology. Later, after Duo was acquired by Cisco, she transitioned to new roles within the larger organization and now heads up operations for Webex Marketing. In this position Syed brings structure across different functions of marketing including brand, events and technology while also serving as chief operating officer for Chief Marketing Officer Aruna Ravichandran.
“I fell in love with the culture, the kindness, the heart of this company,” Syed said.
Recently, she shared her passion for problem solving and inclusion with the Duo Blog, along with the advice she gives mentees navigating their own career paths.
Saleema Syed: I like chaos and I love putting a method to the madness. With marketing we have to react to the market, react to the business, react internally. What energizes me is there’s never a dull day and there is always this ability to bring some overall end to end process.

I love running towards a burning car and figuring out how to put it out. I love change. I know change is the only constant and rather than running away from it, I thrive in it. I like to look at it and ask, “What can we do to break it down and figure out what we need to do?”
My brain works in terms of boxes and flows and charts and spreadsheets so when I look at something I’m like, “Okay, what is a box? What is a process? How do I untangle it?” I like sitting in the discomfort and understanding what to do to get out of it.
Saleema Syed: There are three things I always keep in mind when I look at what I’m doing and where I want to be. One is, at the core of it, does it fill my cup of empathy and allow me to be true to who I am in how I treat people or how I build a team?
The second thing is, will I have the opportunity to influence and impact the people on the team or my family? How do I show myself to my daughter who is growing and seeing how to become who she is as a career person?
The third thing is, is it something new and am I learning something? Continuous learning is a huge part of who I am, so that drives me to get out of my comfort zone constantly.

When I’m changing jobs people usually say, “You’ve set up this team, you’re so comfortable. Now all you have to do is sit back and execute.” And my answer is, “That’s exactly why I am moving.”
If I am comfortable I’m not learning, and I don’t know if I’m adding any more value than I’ve set up. That means it’s time for me to move on and elevate somebody. What I’m doing is sending the elevator down to somebody on the team to grow.
That’s why I’ve had people who work for me for many years follow me through multiple organizations, which as a leader has been my pinnacle of what I call my success. Success is not my role; it is how many people I have impacted and influenced.
Saleema Syed: I keep going back to Duo because working at that organization and meeting those people defined me as a human being. One of the strategic pillars of that organization is to be kinder than necessary.

However complicated the work challenges are, those around me must be aligned with what my integral values are and who I am. They have to have empathy and kindness in their heart. If that is not there, no matter how much I love solving challenges and know I can solve them, I’m not going to go for it. I’ve been extremely lucky at Duo, Cisco and Webex that I’ve been around those kinds of people.
If you look at Webex, I love the core of what we are, the journey we are on, the inclusivity. We are not just selling Webex messaging or other products. At the heart of it we are looking at how we are influencing people and things around us by making sure that there is inclusivity in the collaboration tools that we are launching.
Saleema Syed: My leadership style is pretty simple: nobody works for me; people work with me. I lead with making sure that people know this is the problem you’re trying to solve, here is the context of what we are trying to do. Now, let’s figure out how we solve it. That is something that has helped my team be part of the problem solving that I love to do.
When I interview people my first questions are, “What does the job bring to you? How would this job fill your cup?” That throws people off every time. You can teach any technology, you can teach any skill set, but if you don’t have the basic passion, the attitude to be able to do this job, then everything else can just go out the door.
Saleema Syed: I have a very diverse background. I am an Indian by birth and grew up in the Middle East. When I went into engineering, finished my education and started my career, one of the things I realized was that as a woman of color, I always wanted to apply for positions that I was fully qualified for. I wanted to make sure I knew everything about the job because a very big fear was being asked a question in the interview I didn’t know. LinkedIn’s Gender Insights Report found that women apply for 20% fewer jobs than men despite similar job search behaviors. That has been a very challenging mental barrier for me to break.
Trey Boynton, who was at Duo and now she’s leading Cisco in a beautiful journey of diversity as the senior director of inclusion and collaboration strategy always said, “We have to have that bicycle lane on the road, whether it is for females, whether it is for people of color or any LGBTQIA+ community members. That is how we get people to bring that confidence in to learn, grow and then they can merge easily.”
“Passion is a part of who I am and is contributing to my growth.” – Saleema Syed
Whatever I faced as I was growing up, whether it was my dark skin, whether it was my accent, whether it was, “Oh, you’re way too passionate” has been some of the feedback that I’ve gotten. In my career if I’m told I’m way too passionate I turn that around and say, “Passion is a part of who I am and is contributing to my growth.”
Saleema Syed: Within Webex, within Cisco, I try to be part of anything that I can do in terms of giving back to the community. I’m definitely a big proponent of women in technology. In the local Dallas area I run a program by myself and go into schools and advocate for girls in STEM. Cisco is amazing in how it gives us time to volunteer. I love that educating kids is part of my journey of giving back. That’s the generation you can influence.
How do we enable children and women to be more open to technology and being part of the technology field? Let’s look at the percentage of diversity in the technology field and be aware of it. It’s not only about the diversity numbers, but are we bringing in candidates at the leadership level and giving them not just a seat at the table but a voice at the table, too?
You also have to talk about what you do and with passion and energy because if you don’t, people get intimidated. If you can influence one person who comes from an underrepresented community, imagine what you are doing, not just for that person, but for his household, for his family, for his extended community. I have a lot more to do, but as I get into the next decade of my life and my career, that is something that is a huge focus for me.
Saleema Syed: First and foremost it’s very important to spend time and understand the business and the products in whatever industry you’re going into. It is key to your growth. Especially if it’s a security industry, take time to understand the products, the technology or the function that you’re trying to get into. Contextual understanding and product understanding are extremely important.
The second piece is to keep learning. Cisco is amazing in trying to help you learn and support you financially to be able to do it. I went back and got my executive MBA four years ago. Give yourself a goal of learning a new something, whether it is a new function, new technology or new leadership skill.
The third piece is to create a spreadsheet of where you want to be in two years. Put that out there and then work back just like you would do a project plan. Work back month by month, quarter by quarter. What are the skill sets you need to learn to get there?
The last part is: Do the job you want versus the job you are in. Of course, you have to do the job you are in, but do the job you want to get to. Don’t wait for a title, don’t wait for a promotion to act. No. What do you want to be? Show that to your leaders and yourself. The title will come, money will come, everything will come, but am I doing the job that I want and enjoy and I want to get to?
To learn more about Webex, Cisco and Duo Security and how you can apply your passion, advocacy and problem solving to make a difference in cybersecurity, browse our open roles.

We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
We have entered a world where uncertainty has become the normal operating mode for everyone. Within this new frontier, cybersecurity has become even more challenging. However, some cybersecurity professionals have stood out, using their unique skills and resourcefulness to protect the integrity of their businesses, and to withstand unpredictable and dynamically changing threats. In the end, they, and their businesses have emerged even stronger.
These accomplishments have lead them to be selected from over more than 700 Cisco Cybersecurity Advocates – who are also members of Cisco Insider Advocates – to join the League of Cybersecurity Heroes.
Cisco Insider Advocates is a peer networking community developed several years ago for Cisco customers around the globe. Currently, over 14,000 customers are using it to share technology insights, feedback, and best practices, and also to make meaningful connections with others in the industry. We at Cisco believe that when we connect, anything is possible, and the Insider Advocacy program is a great example of the great things that can happen when people come together.
As the global CISO of Mediapro, Roberto has deployed Cisco SecureX together with Umbrella, Secure Endpoint, Secure Firewall, ISE, NGIP, Threat Response, AnyConnect, and Web security. With this partnership, Mediapro has reduced its threat detection time by 90%. In addition, they have seen no false positives in their threat detection alerts. It is rare to boast of a 100% success rate, but they can boldly make that pronouncement. All of this has also benefitted Mediapro financially by incurring zero fines for any compliance issues
What do music, cybersecurity, and teaching all have in common? They all culminate in a readiness to perform. Equally, they all require collaboration, comfort with the unexpected, and a passion for the job. Blair exemplifies the best of these traits, and in doing so, he provides inspiration and excellence to all with whom he interacts. Watching Blair at work makes one wonder if there are more hours granted to him during a day than the average person. He is a time-maximizer, spending most of that time in the service of others.
Too often, cybersecurity certifications are treated derisively by some of the very professionals who need them most. This is not the case with Kevin, who can list the many benefits of attaining certifications. Kevin’s desire to improve his knowledge doesn’t stop with technology and cybersecurity. He is an avid reader of anything that can raise him up to be better than he was the day before. With a career that started in the US Marine Corps, Kevin continues to learn and grow, all the while remaining as masterful at a computer keyboard as he is his with his traditional 55-gallon-barrel BBQ smoker and grill.
Steve is a Senior Cybersecurity and Network Architect at Lake Trust Credit Union. Like most organizations, Lake Trust has had to transition to a completely remote workforce quickly, and thanks to Secure Network Analytics, they were able to transition the employees to work remotely while maintaining the same high level of visibility and protection in place. Steve was the subject of a case study about the benefits that Cisco products have brought to Lake Trust Credit Unions’ customers. He is currently collaborating to update that information to share more of his knowledge.
Being the Head of Information Technology is never an easy job. However, when food manufacturer, Leng-d’Or, was faced with a challenge during the pandemic that could have interrupted its production line, quick thinking, skilled leadership, and a close partnership with Cisco all lead to positive outcomes, and helped them to pull through stronger than before. Part of this success comes from Enric’s distinct understanding of the threats, solutions, and processes needed to bring security to a higher level for the Leng-d’Or organization. Enric also shares his success story very freely, adding immeasurable benefits to the security community.
Cybersecurity is truly a global discipline. Tony Dous proves this by practicing his craft as a Senior Network Security Engineer in Cairo, Egypt. Tony’s involvement with the Cisco community shows how no distance is too far for a motivated cybersecurity professional.
When John Patrick is on the job, there is no longer any feeling that the criminals are one-step ahead of the good guys. He adopted Umbrella together with Meraki to develop a proactive security approach inside his organization. John Patrick created a more unified network from a patchwork of disparate entities. In doing so, he reduced the complexity within the environment. Complexity is so often responsible for security gaps, and John Patrick’s work not only corrected those gaps, but he brought people together in the process. He and his team received great feedback from the employees, who enjoyed a consistent network experience.
We often hear stories about teenagers who become enamored with technology, leading to the fulfillment of a dream. Amit Gumber became interested in cybersecurity at an early age, pursued his passion and has worked in the field ever since. His sense of advocacy is best described in his own words: “I’m quite passionate about sharing knowledge and ideas with peers and participating in collaborative activities.” Amit’s use of Cisco technologies has helped HCL Technologies to stabilize and secure their environment.
One of the most important factors for success is insatiable curiosity. Mark Healey is a continuous learner, and he is an example of someone who enthusiastically shares his knowledge. Whether it is on a personal level, or through his high engagement as part of the Cisco Insider Advocates community, or as an active member of the Internet Society, Mark is an evangelist and a positive voice for cybersecurity.
Wouter holds a special designation, not only as a member of the League of Cybersecurity Heroes, but also as the recipient of the “Cybersecurity Defender of the Year” award. Wouter is an active participant in the cybersecurity community, working with an almost evangelical zeal towards sharing the importance of holistic cybersecurity. His contributions stand out towards making the cyber realm a safer place.
It is often said that the job of a cybersecurity professional in an educational facility is especially challenging. When that facility happens to be the largest in an entire country, with over 4,000 schools and universities, the job of protecting it can seem insurmountable. At AzEduNet, in Azerbaijan, Bahruz and his team is tasked with securing the network for its 1.5 Million students. With Cisco Secure, the security team reduced security incidents by 80%. This not only ensures access for the students, but also keeps the data safe.
Many people want to enter the cybersecurity profession, but few have the dedication and perseverance to fully embrace the skillset required to meet that goal. Walther Noel not only had the desire to refocus his career, but he proved it by earning the CyberOps Associate Certification. His accomplishment is a prime example of how one can step outside of their comfort zone to grow and thrive.
Pascual demonstrates how important it is to make the most of the learning opportunities in Cisco Insiders Advocates. While already a successful NOC engineer, he sought to advance his professional development by studying cybersecurity. He passed the CCNA CyberOps 200-201 exam, moving him closer to propelling his career to even higher achievements.
One of the noblest expressions of knowledge is the desire to freely share that information. Inderdeep lives up to this ideal, offering his expertise to all with no expectations of reciprocity. His charitable spirit has not gone unnoticed, as he has been a previous award winner for Cisco IT Blogs, as well as a designation on the Feedspot top 100 Networking Blog.
Being the first to try a new technology can be a risky proposition. However, as a COO, risk calculations are in one’s blood. Luigi, along with the Sara Assicurazioni organization, hails as the first company in Italy to embrace cloud technology. As a company with more than one million customers, this was a bold initiative that required careful planning, keen insight, and above all, collaboration. In the end, this has resulted not only in a digital transformation, but a business transformation.
Whether it is a technical achievement, a personal triumph, or a spirit of helping others, each member of our League of Cybersecurity Heroes proves how technology and humanity can work together to accomplish the impossible. Congratulations to all of them!
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Instagram
Facebook
Twitter
LinkedIn
Few security career paths are linear. For Stephanie Frankel the journey to Cisco Secure was circuitous. The Ann Arbor, Michigan native studied journalism at the University of Michigan before managing communications for the Washington Capitals and NBC Sports. But after several stints at communications agencies, she charted a new path for herself in cybersecurity. Not only has her diverse background served as a strength in her current role as senior manager for strategy and operations, but it’s also informed her management philosophy.
After doing project management and account direction at consulting agencies, Frankel was interested in honing her skills and expertise on the client side. She had heard amazing things about Duo and wanted to stay in Ann Arbor and work for a company with local roots. After interviewing, Frankel realized that “working at Duo was a cool, exciting opportunity with a really awesome group of people.”
Frankel was on the ground running working as a technical project manager in research and development overseeing the Multi-Factor Authentication, applications and mobile engineering teams despite not having worked in information security before.
Duo’s security education allowed Frankel to understand the industry and is something she values for getting more people into the cybersecurity field. At Duo and Cisco Secure, employees come from a variety of backgrounds and some don’t have much (or any) experience with cybersecurity.
Robust educational programs build knowledge about security and specific products which empower new team members to grow and learn. Every team also has a learning and development budget for employees to quench their curiosity and enhance their knowledge through courses, books or other programs Manager of Global Employee Programs Anndrea Boris shared.
“People are open to having conversations and open to ideas and ways to solve those ideas. If you have an idea of how to solve a problem, no matter whether it’s your job or not, people are open and willing to listen to you.” – Stephanie Frankel
Something Frankel also appreciates most is that ideas are valued at Duo and Cisco Secure: “Even in my first job, I would have ideas and go to my boss or our head of engineering and say, ‘Hey, I think this could be a really cool opportunity, and I think it needs this.’ People are open to having conversations and open to ideas and ways to solve those ideas. If you have an idea of how to solve a problem, no matter whether it’s your job or not, people are willing to listen to you.”
After a year, Frankel moved from engineering to marketing to run operations for Duo’s in-house brand team, leading the team through a rebrand. “The team really rallied behind this new brand and it was amazing to see their pride and hard work when sharing it,” she said. With Frankel’s leadership, the team showcased not only the new look and feel of the brand but also the customer research that went into understanding the need for the change.

“Our amazing team knew that for it to catch on internally we needed to help people understand the why. The team put together an amazing training and went around the company to help people understand the security buyer, the industry overall and our differentiators and how we could do all of this within the umbrella of Cisco,” she said.
Recognizing that she most enjoys and feels best suited for a strategic operations role, she had open conversations with her manager. “I told my boss, ‘It’s just not a great fit.’” Her manager was very supportive, and they worked through potential options. “You’ll find a lot of that at Cisco,” she said.
Now as senior manager in the Strategy and Operations Group within Cisco’s Security and Collaboration division, Frankel runs key initiatives for business operations that drive business growth. She is empowered to creatively solve problems and collaborate “with all the stakeholders within each group to move these programs forward, to understand the problems we’re looking to solve, create objectives, a program plan, and continue to track metrics and progress towards those ultimate goals,” she said.
A self-described “over communicator,” Frankel believes that as a leader, “the more you communicate and the more transparent you are, the better.” Frankel loves leading people who are experts in their fields and letting them do what they do best.
On the brand team, for example, she trusted her team’s expertise in producing stories, videos and animations to demystify Cisco’s security products.
“All I needed to do was give them the objective and the goals and they were able to come up with the solutions,” Frankel said.
She fondly remembers the boss at one of her first jobs out of college. In that job Frankel wrote press releases and wanted her boss to fully approve the final versions before sending them to the media. Once her boss told her, “Stephanie, if you keep giving it back to me, I will keep finding things to change. I trust you to know when it is ready to go.” That confidence in her so early in her career “gave me so much confidence in myself,” she said.
Frankel emulates his approach to management by recognizing that each employee has different needs in their lives, in their careers, and in how they like to receive feedback. From that boss Frankel first learned that for every piece of negative feedback, you must give four pieces of positive feedback for “someone to actually hear it because that’s how you balance things out in your mind.”

Frankel believes feedback is crucial for growth. “I don’t see how you can improve or grow without it, no matter what level of your career you’re at. Feedback shouldn’t be taken as negative, as much as it is a way for you to improve,” she said.
One of the most helpful things Frankel learned in a Cisco class for managers was the importance of asking a person if they are in a good place to receive critical feedback. “You might not be in the mindset to accept the feedback and to do something constructive with it,” she said. ”If you’re having a bad day or struggling, you could say, ‘You know what, I’m not going to be able to take it today, but let’s talk tomorrow and I’ll be in a better place to receive it.’’’
Frankel has spent the last year thriving in a role she never anticipated in an industry her college training in journalism didn’t fully prepare her for. The secret, she says, is keeping an open mind to new possibilities and a willingness to take on new challenges, even if you don’t feel 100% ready.
“A lot of it is getting real world experience and learning your way through it and knowing that there’s a lot of opportunities and a lot of people that are willing to teach you,” she said.

To pivot professionally Frankel advises not feeling pigeonholed just because you studied a particular topic or have been in a certain industry for a long time. Take what you can from where you started such as storytelling and communications skills in the case of journalism for Frankel. While trying something new may require taking a different level or type of job “sometimes it’s worth it because you have that opportunity to grow and you might find you’re happier somewhere else,” she said.
When discerning professional steps Frankel recommends having open and honest conversations with yourself and others such as mentors.
“Cisco has so many mentorship programs and so many people that are knowledgeable about a lot of things,” she said. ”Just because your current role isn’t a great fit doesn’t mean that there’s not another good fit within the corporation, or it doesn’t mean that you can’t create your own good fit.”
Did you know that Cisco offers cybersecurity trainings and certifications? Start developing your cybersecurity skills today! And if you’re ready to jump into an exciting new career in security, check out the open roles at Cisco Secure and Duo Security.

We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
No, ransomware attacks are not random. From extortion to data breaches, ransomware is always evolving, and is becoming very lucrative with ransomware-as-a-service kit making it easier to target organizations. The days of just a single bad actor searching for vulnerabilities in your security stack are over. Security Operations Centers (SOCs) and the security analyst community are dealing with a sophisticated global network of adversaries who can do irreversible damage. The conversation must shift from how we can prevent a breach to how do we prepare for the inevitable breach.
Recently I found out that the small private college I attended right out of high school closed their doors permanently, falling victim to a targeted ransomware attack. This institution not only provided an education but also contributed to the local economy in this rural town for over 150 years.
The cyberattack occurred during the pandemic when most educational institutions had suddenly shifted to remote learning. Adversaries knew that the shift to remote learning would expose the college’s lack of acceptable tools for monitoring and managing applications, frequently from unsecure locations.
Unfortunately, the hackers were able to halt all admission activities, locked the administrators out from accessing critical data pertaining to the upcoming school year and ultimately, forced the school to close their doors – even after they paid the hackers the ransom.
And this is not an isolated case – Comparitech published a story ‘Ransomware attacks on US schools and colleges cost $3.56bn in 2021’ and outlined how threat actors have evolved with their ransomware attacks on schools and colleges. This is particularly concerning as many of these institutions do not have the skillsets or resources to protect their students or organization from these attacks. Below you can review their findings from a study done between 2018 – 2022:

In 2021:
Just having a firewall alone will not stop all of the attacks, it’s just a matter of time before you experience a breach. Once the breach happens, you need a security system that will quickly detect and remediate the threat .
Resiliency must be a critical outcome for any security solution and Cisco Secure Endpoint is built to stop hackers at the point of entry. Our cloud native solution allows your security operations team to quickly detect and respond to threats minutes after a breach occurs.
Small to medium size businesses, hospitals, and educational institutions internal network will rely on cyber insurance in-lieu of a fully staffed, skilled cyber-security team. In today’s climate of ever-increasing sophisticated cyber threats this won’t cut it. You will need an agent that quickly detects, responds, and has visibility across your different security solutions.
With Cisco Secure Endpoint Pro we are equipped to assist with the responsibility of monitoring your endpoints for cyberattacks. With 24/7/365 monitoring capabilities, our SOC will quickly detect and remediate any threats that targets your organization. Secure endpoint pro provides flexibility and the option of letting our SOC team do the heavy lifting while you focus on your core business.
Tangible outcomes provided by Secure Endpoint and Secure Endpoint Pro:
An effective managed endpoint detection and response solution frees up time for your SOC team along with accelerating detection and response time. Cisco Secure Endpoint can reduce incident response time by as much as 97%, which limits the damage threat actors can cause after you have been breached.
Cisco Security has launched a solution geared towards protecting your school’s network by blocking malicious threats before they enter the endpoint and compromising your data. The secure endpoint agent is deployed, sits on the school endpoint freeing up time from a stretched thin IT department.
Don’t know where to get started? Check out how our EDR solution got you covered below and how to contact us to learn more.
Interested? Reach out to grantsquestions@cisco.com to learn about public funding options available in your state.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels