Throughout my career, I have noticed the way we “futurize” technology. Often, we are thinking of technology in five-to-ten-year increments. But the fact of the matter is – technology is moving faster than we can keep up. The minute we think we understand it, it’s already onto something new. That’s why here at Cisco, we’re focused on what’s NEXT. We all know technology will continue to grow at a rapid pace, our goal is to remain at the forefront of these changes.
After much anticipation, it’s finally here! I am excited to present the first episode of “NEXT” by Cisco Secure! “NEXT” is a video series illuminating simple conversations about complex topics. Our mission is twofold: First, we want to humanize cybersecurity. Second, we want to build a bridge between Cisco Secure and the ideas of the future.
CTO of Cisco Secure, TK Keanini and I sit down with Michael Ebel, CEO of Atmosfy. If you saw our preview, then you know Atmosfy is on a mission to help inspire others and support local restaurants through live videos.
Want to learn what’s NEXT for Michael Ebel and Atmosfy? Check out our episode!
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Welcome back! In our last article, you cleared out your extraneous digital footprints by removing unnecessary accounts and opting-out of data broker services, and have finished a dedicated review of your online history. In this final section, we will answer the natural question encountered at the end of any journey: What’s next?
Before becoming the series you’ve just read, I presented a version of this many times as a live talk at conferences and training sessions. After the first few talks, I noticed a consistent trend in the feedback when I was approached afterwards: people who said they felt anxious about how their online activity going forward might share more than they want. So I went back and added a final section to the talk, one that we’re going to cover together now: risk acceptance and the value of routine in good security.
Some people think that the goal of good security is to eliminate risk. One of the first lessons you learn in this industry, though, is that eradicating every possible risk is very rarely practical, whether we’re talking about the individual or organizational level. This is because there are few choices one can make with zero possibility of a negative outcome, and because human beings are… human, and even with excellent discipline and good intent the best of us can mess up.
The goal of good security strategy is instead to assess risk and find a healthy balance: to decide what is more or less important and valuable, to determine how damaging the worst-case scenario might be and weigh that against the potential benefits, and figuring out how much you can reasonably do to tip the balance and increase your odds of success.
That’s fairly abstract, so let’s use a couple quick practical examples at both levels:
I don’t know about you, but I grew up as a child of the internet, and the thought of never going online again isn’t one I’m likely to seriously consider. So rather than logging off forever, let’s focus on how we can both stay safe and stay connected. We’ve completed the “3 R’s” of the self-dox process: Review, Restrict, and Remove. But now, a surprise more shocking than the Spanish Inquisition itself: we’re going to add two final steps-Repeat and Refine.
Every good security plan includes a plan for routine follow-up. We know that staying offline forever isn’t practical, so the next best thing is to set up a reminder to go through an easier version of this checklist on a regular schedule. Why is it easier? In this review, you had to look back on your entire life up to the present, and next time you’ll just need to look back from then to… well… now! Depending on how active you are online and how likely you are to be doxxed, this might make sense to do on an annual basis, or split into abbreviated and more frequent quarterly reviews.
There is no one-size-fits-all approach to this review, but here are some typical checks you may want to consider:
Before we move on to our final (final, I promise!) step, let’s talk one more kind of repeating. A wifi repeater is a gadget that can connect to and boost the signal from a wireless network, helping to expand the network’s reach and keep a strong connection. In the same way, by sharing the lessons you’ve learned with your family and friends you will expand the reach of that security knowledge. Not only does that help keep the people you care about safer… but since we’ve seen how information shared about us by others can also be discovered by doxxers, it helps to increase your own safety as well!
My goal in writing this series was to give a straightforward introduction and broadly-useful walkthrough of how to figure out what’s out there about you online. In the beginning of this series, I talked about how the level of risk for doxxing is not the same for everyone. You may want to go significantly further than we’ve covered in this guide if you are:
This can cover a wide range of additional steps like placing a freeze on your credit report, requesting a privacy removal from search engines, or even setting up dedicated secure devices/apps for communication online. The full scope of these additional protections is beyond what we can cover here, but I will again recommend the Self-Doxxing Guide from AccessNow and the Gender and Tech Safety Resource guide linked in the first post of this series as an excellent reference for where else you might want to check.
Thank you for following along with me on this journey, and I hope that you found this guide and the resources shared have been helpful for you. Still have questions, or have you discovered any of the links/tools here are no longer available? Please let me know! Life comes at you fast on the web, and I want to make sure this guide continues to be relevant and helpful for a long time to come. You can drop me a line at zoe@duo.com, or find me on Twitter. Until then, happy trails and stay safe out there!
If you can’t get enough security content and care deeply about making the web safer for everyone, we’d also love to hear from you. Please check out our open positions and how your passion can contribute to keeping people safe online.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Welcome back! Previously in our Go Dox Yourself series, we walked through reviewing what information is available about you online, prioritizing those accounts that are most important or still active, and then restricting how much we share through those accounts and who gets to see it. That’s two out of our three steps — maybe good enough for Meatloaf, but not for us! You’re in the home stretch now, and this is the most straightforward-if-slow portion of the process — so let’s dive right in.
In the review step , along with the top accounts that you wrote out in your initial brain dump, we used some email search tricks and the free services NameCheckup.com and NameChk.com to dig up any unused, forgotten, or now obsolete accounts you might have previously registered under your email address or favorite username (or, as us ʼ80s kids used to say, your “handle.”)

We set those old accounts to the side to focus on your active and sensitive data first, but now it’s time to make Marie Kondo proud and clean out the junk drawers of our online life – if it doesn’t still serve you or spark joy, let’s kiss it goodbye!
In a perfect world, this would be as simple as logging in, going to your account settings and clicking a big ol’ “Cancel My Account” button. However, many sites opt to bury the cancelation settings behind a series of smokescreen menus, sometimes even including a half dozen unskippable “are you SURE you want to leave?” and “but we’ll give you a super good deal to stay!” surveys to click through first.
If you find yourself thwarted and your first search of “[Unwanted Service] cancel” doesn’t take you where you need to go, try checking out AccountKiller. This collaborative resource takes submissions of step-by-step deletion instructions and direct links to cancel for a tremendous number of sites, and even includes phone tree options and direct support numbers for canceling offline accounts as well.
The first pass of your delete list might well be longer than a CVS receipt, because these days the average person has 100 password-protected accounts to manage, but don’t worry! You don’t have to sprint to the finish line, and slow progress checking off a few accounts in short sessions over a few weeks will serve you better than a several-hour slog of trying to clear them all at once and burning out.
An important lesson in security is that operating at max capacity isn’t sustainable all the time, and planning for rest and overflow in our personal security planning is no different. Remember that the work you’re doing is cumulative, each small step is one more forward, and every account you clear now is one less that you’ll need to revisit later.
You might notice that we’ve checked off most of the information from our initial brainstorm: emails, usernames, phone numbers, profile pictures… but so far, we haven’t done much with your location history: the cities you lived in and live now, the cities where you worked or went to school, and the city of your birth. Now that we’re going to see how much information on you is available through data brokers and public record sites, these details will be important to have handy.
For the unfamiliar, data brokers are companies which collect and bundle personal information for everything from ad customization to individual investigation. Brokers collect their data through a wide variety of methods, including:
These metrics and details are bundled and sold, either directly through lookup sites like we’ll review in just a moment, or in demographic bundles (for example, “Resilient Renters” or “Living on Loans: Young Urban Single Parents”). If you’ve ever walked through a car dealership window-shopping and suddenly found sponsored content for that car company in your feed, data brokers are the most likely reason.
For this step you should reference the previously-mentioned Personal Data Removal Workbook provided by Michael Bazzell through his company, IntelTechniques. Bazzell has maintained and updated this workbook for many years now, and it is by far the most comprehensive resource for keeping a handle on who is buying and selling your data.
One of the first things you’ll notice on opening the workbook is the sheer volume of businesses out there buying and selling your data: at time of writing, the current edition includes 220 separate brokers. But much like your initial account inventory likely included a select set of important accounts and a longer list of less-relevant ones, there are less than a dozen brokers who dominate most of the market and should be at the top of your list – and fortunately, they’re also at the top of the workbook! These sites are:
Aside from covering most of the market for data and analytics intelligence, these primary sites often act as “feeders” for smaller providers that are either directly affiliated or collect information for their own databases from the largest providers. Which means that as you remove your data from these sites, you’ll not only check off another box on your list, but you may also reduce the number of hits you find for your information on smaller sites as you work your way down.
Congratulations: if you’ve been following along, you’ve just made it through your self-doxxing! Hopefully you’re feeling much better informed and aware of what tracks you’ve left online, and addressed who you do and do not want to have your… addresses. Join us soon for our wrap-up post where we’ll recap with takeaway lessons, as well as good habits and check-ins to keep you safe going forward.
Care about keeping people and their data safe online? Check out our open roles.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
NetWitness and Cisco released the third annual Findings Report from the RSA Conference® 2022 Security Operations Center (SOC).
The RSA Conference® SOC analyzes the Moscone Center wireless traffic, which is an open network during the week of the Conference.
The role of the SOC at RSA Conference is an educational exhibit sponsored by NetWitness and Cisco. It has elements of a SOC like you would create to protect an organization. The RSAC SOC coordinated with the Moscone Center Network Operation Center for a SPAN of the network traffic from the Moscone Center wireless network. In the SOC, NetWitness had real time visibility of the traffic traversing the wireless network. Cisco provided automated malware analysis, threat intelligence, DNS visibility and Intrusion Detection; brought together with SecureX.
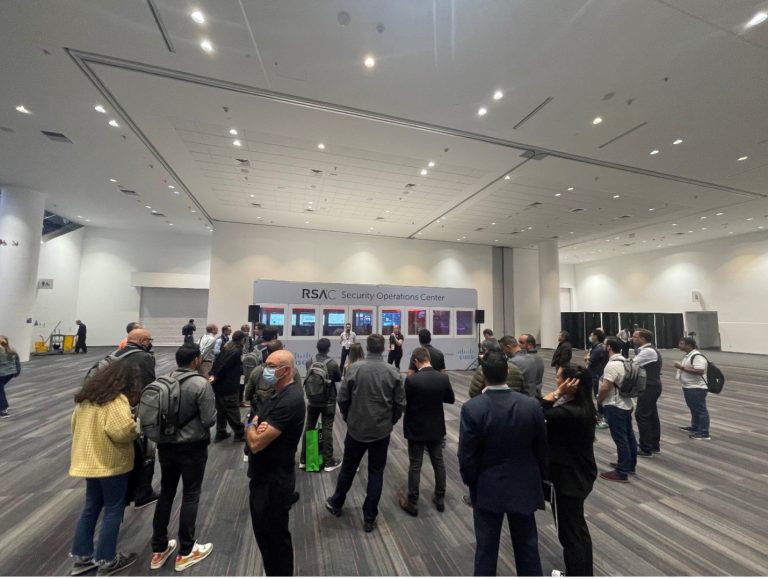
The goal of the RSAC SOC is to use technology to educate conference attendees about what happens on a typical wireless network. The education comes in the form of daily SOC tours and an RSA Conference® session. You can watch the replay of the ‘EXPOSURE: The 3rd Annual RSAC SOC Report’ session here.
The findings report addresses several security topics, including:

Look forward to seeing you in 2023!
Download the RSA Conference® 2022 Security Operations Center Findings Report here.
Acknowledgements: Our appreciation to those who made the RSAC SOC possible.
Percy Tucker
Steve Fink
Bart Stump
Dave Glover
Jessica Bair Oppenheimer – Cisco SOC Manager
Ian Redden – Team Lead & Integrations
Aditya Sankar / Ben Greenbaum – SecureX & Malware Analytics
Alejo Calaoagan / Christian Clasen – Cisco Umbrella
Dinkar Sharma / Seyed Khadem-Djahaghi – Cisco Secure Firewall
Matt Vander Horst – SecureX Orchestration
Doug Hurd – Partnerships
Eric Kostlan
Navin Sinha
Zohreh Khezri
Eric Goodwin
Gabe Gilligan and the amazing staff at XPO Digital!
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
With passwords and MFA out of the way, let’s next look at connected apps or services that are tied to our priority accounts. When you log into other sites on the web through Facebook, Google, or another social account, as well as when you install social media apps or games, you are sharing information about those accounts with those services. This may be as limited as the email address and username on file, or may include much more information like your friends list, contacts, likes/subscriptions, or more.
A well-known example of this data-harvesting method is the Cambridge Analytica story, where installing a social media app opened up access to much more information than users realized. (Note: as mentioned in the linked article, Facebook added protective measures to limit the amount of data available to app developers, but connected accounts can still present a liability if misused.)
With this in mind, look under the Security or Privacy section of each of your account’s settings, and review where you have either used this account to log into a third-party website or allowed access when installing an app. Here are some handy links to some of the most common services to check:
If you aren’t going to use the app again or don’t want to share any details, remove them. Once you’ve checked your accounts, repeat this process with all the apps installed on your phone.
Just like connecting a social account to a third-party game can share information like your contact info and friend’s list, installing an app on your mobile device can share information including your contacts, camera roll and more. Fortunately, mobile OSes have gotten much better at notifying users before installation on what information is shared, so you should be able to see which apps might be nosier than you’re comfortable with.
Finally — and this is really for the nerds and techies out there — check if you have any API (short for “application programming interface”) keys or browser extensions connected to your accounts. API keys are commonly used to let different apps or services “talk” between one another. They let you use services like Zapier or IFTTT to do things like have your Spotify favorites automatically saved to a Google Sheet, or check Weather Underground to send a daily email with the forecast.
Browser extensions let you customize a web browser and integrate services, like quickly clicking to save an article for review on a “read it later” service like Instapaper. Even if you trust the developer when installing these apps, they may pose a risk later on if they are recovered or taken over by an attacker. These “zombie extensions” rely on a broad install base from a legitimate service which can later be misused to gather information or launch attacks by a malicious developer.
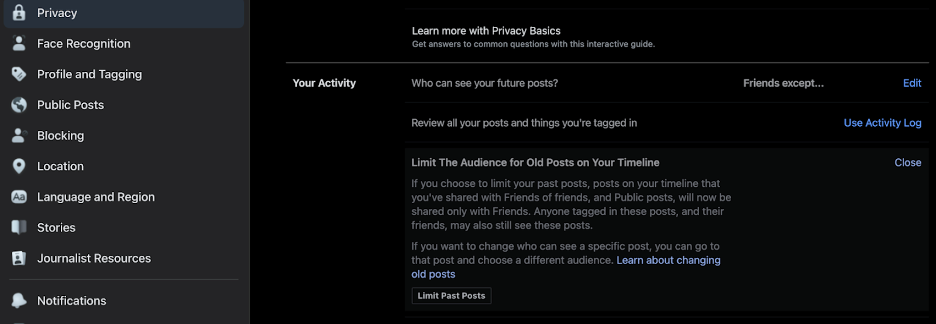
We’ve made great progress already, and taken steps to help defend your accounts from prying eyes going forward – now it’s time to lock down your previous activities on social media. Rather than enumerate every option on every service, I’ll highlight some common tools and privacy settings you’ll want to check:
Before moving on to email, I’ll add another plug for the NYT Social Media Security and Privacy Checklists if you, like me, would rather have a series of boxes to mark off while going through each step above.
Security experts know that you can’t erase the possibility of risk, and it can be counterproductive to build a plan to that expectation. What is realistic and achievable is identifying risk so you know what you’re up against, mitigating risk by following security best practices, and isolating risk where possible so that in the event of an incident, one failure doesn’t have a domino effect affecting other resources. If that seems a bit abstract, let’s take a look at a practical example.
Tech journalist Mat Honan was the unlucky victim of a targeted hack, which resulted in a near-complete lockout from his digital life requiring a Herculean effort to recover. Fortunately for us, Mat documented his experience in the Wired story, “How Apple and Amazon Security Flaws Led to My Epic Hacking,” which offers an excellent summary of exactly the type of domino effect I described. I encourage you to read the full article, but for a CliffsNotes version sufficient for our needs here:
Honan’s article goes into much more detail, including some of the changes made by the services exploited to prevent similar incidents in the future. The key takeaway is that having a couple of emails without strong authentication tied to all his most important accounts, including the recovery of these email accounts themselves, meant that the compromise of his Amazon account quickly snowballed into something much bigger.
We’re going to learn from that painful lesson, and do some segmentation on our email channels based on the priority and how public we want that account to be. (“Segmentation” is an industry term that can be mostly boiled down to “don’t put all your eggs in one basket”, and keep critical or vulnerable resources separate from each other.) I would suggest setting up a few different emails, listed here from least- to most-public:
For all of the above, of course, we’ll create strong passwords and set up 2FA. And speaking of 2FA, you can use the same split-channel approach we followed for email to set up a dedicated verification number (using a VOIP service or something like Google Voice) when sending a passcode by SMS is the only option supported. Keeping these recovery numbers separate from your main phone number reduces the risk of them being leaked, sold, or captured in an unrelated breach.
Good news: We’re almost done with doxxing ourselves! In the next section, we’ll sweep out those unused accounts to avoid leaving data-filled loose ends and take a look at how data brokers profit off of your personal information and what you can do to opt-out.
You’ve made it this far so maybe you’re passionate like we are about developing innovative ways to make security accessible. We’d love for you to join our mission.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
In the first step of our doxxing research, we collected a list of our online footprint, digging out the most important accounts that you want to protect and obsolete or forgotten accounts you no longer use. Because the most recent and relevant data is likely to live in the accounts you use regularly, our next step will be to review the full scope of what’s visible from these accounts and to set more intentional boundaries on what is shared.
It’s important to note here that the goal isn’t to eliminate every trace of yourself from the internet and never go online again. That’s not realistic for the vast majority of people in our connected world (and I don’t know about you, but even if it was I wouldn’t want to!) And whether it’s planning for an individual or a giant organization, security built to an impossible standard is destined to fail. Instead, we are shifting you from default to intentional sharing, and improving visibility and control over what you do want to share.
Before making changes to the settings and permissions for each of these accounts, we’re going to make sure that access to the account itself is secure. You can start with your email accounts (especially any that you use as a recovery email for forgotten passwords, or use for financial, medical, or other sensitive communications). This shouldn’t take very long for each site, and involves a few straightforward steps:
The best way to prevent a breached password from exposing another account to attack is to use a unique password for for every website you visit. And while you may have heard previous advice on strong passwords (along the lines of “eight or more characters, with a mix of upper/lower case letters, numbers, and special characters”), more recent standards emphasize the importance of longer passwords. For a great explanation of why longer passwords work better than shorter, multi-character type passwords, check out this excellent XKCD strip:
A password manager will make this process much easier, as most have the ability to generate unique passwords and allow you to tailor their length and complexity. While we’re on the topic of what makes a good password, make sure that the password to access your password manager is both long and memorable.
You don’t want to save or auto-fill that password because it acts as the “keys to the kingdom” for everything else, so I recommend following a process like the one outlined in the comic above, or another mnemonic device, to help you remember that password. Once you’ve reset the password, check for a “log out of active devices” option to make sure the new password is used.
MFA uses two or more “factors” verifying something you know, something you have, or something you are. A password is an example of “something you know”, and here are a few of the most common methods used for an additional layer of security:
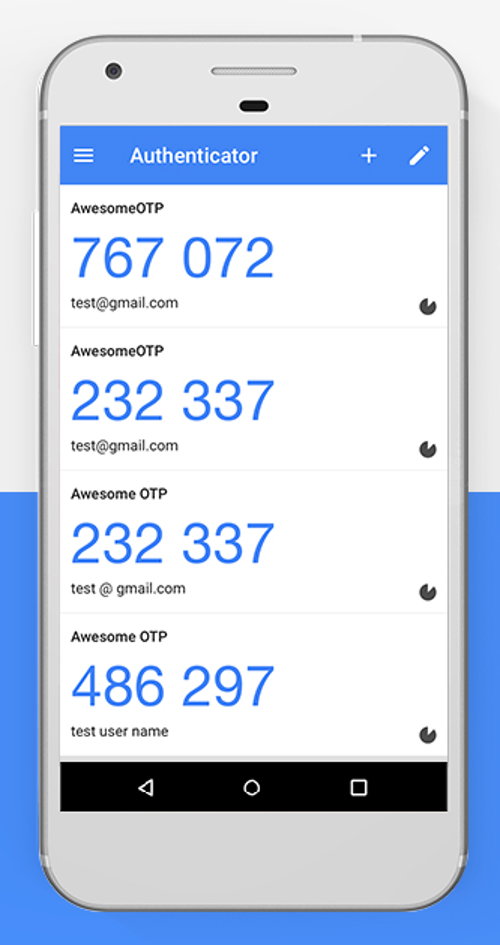

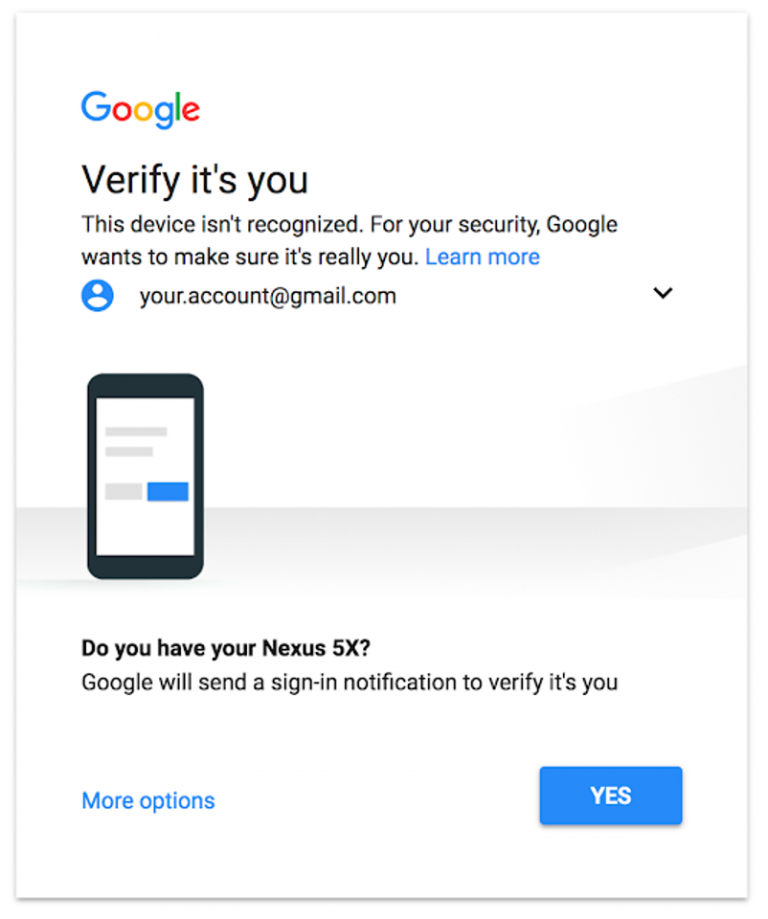
If you want to know more about the different ways you can log in with strong authentication and how they vary in effectiveness, check out the Google Security Team blog post “Understanding the Root Cause of Account Takeover.”
Before we move on from passwords and 2FA, I want to highlight a second step to log in that doesn’t meet the standard of strong authentication: password questions. These are usually either a secondary prompt after entering username and password, or used to verify your identity before sending a password reset link. The problem is that many of the most commonly-used questions rely on semi-public information and, like passcodes, are entered on the same device used to log in.
Another common practice is leveraging common social media quizzes/questionnaires that people post on their social media account. If you’ve seen your friends post their “stage name” by taking the name of their first pet and the street they grew up on, you may notice that’s a combination of two pretty common password questions! While not a very targeted or precise method of attack, the casual sharing of these surveys can have consequences beyond their momentary diversion.
One of the first widely-publicized doxxings happened when Paris Hilton’s contact list, notes, and photos were accessed by resetting her password using the password question, “what is your favorite pet’s name?”. Because Hilton had previously discussed her beloved chihuahua, Tinkerbell, the attacker was able to use this information to access the account.
Sometimes, though, you’ll be required to use these password questions, and in those cases I’ve got a simple rule to keep you safe: lie! That’s right, you won’t be punished if you fib when entering the answers to your password questions so that the answers can’t be researched, and most password managers also include a secure note field that will let you save your questions and answers in case you need to recall them later.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Technology has typically had a reputation for being exciting and inventive. Unfortunately, this hasn’t always been the case for security. But times have changed. We are now recognizing the crucial role security plays in any groundbreaking technology. Without strong defenses, even the most visionary app is likely to crash and burn. So it’s imperative that big security players like Cisco stay on top of what’s next.
I am thrilled to announce that in November, we will be launching our new video series, “NEXT” by Cisco Secure. In the series, my esteemed co-host TK Keanini and I will interview some of the brightest new minds in tech to find out more about the future of the industry and how we can best secure it. Watch the series preview below!
As the CTO of Cisco Secure, TK has over 25 years of networking and security expertise, as well as a penchant for driving technical innovation. As for me, I’m a cybersecurity specialist of 10 years with an obsession for communication and empathy. Together, TK and I will bring new cyber pioneers to the forefront and highlight the criticality of digital protection and privacy for everyone.
Whether we’re discussing Web3, the metaverse, or next-generation healthcare, we’ll learn and laugh a lot. Through simple conversations about complex topics, we’re building a bridge between leading-edge tech and how Cisco is helping to safeguard what’s on the horizon.
And what better time to preview this series than during Cybersecurity Awareness Month? A time when we focus on the reality that security belongs to everyone — not just the threat hunter, or the product engineer, or the incident responder — but everyone.
We all have a responsibility to protect the world’s data and infrastructure, and should all have a seat at the table for important security conversations. We hope you’ll join us as we dive into what’s making waves out there, and how we can keep it safe.
Follow our Cisco Secure social channels to catch our first episode in November, when we will speak with Michael Ebel, CEO of Atmosfy. Atmosfy is revolutionizing restaurant reviews by incorporating engaging live video that inspires others and supports local businesses. TK and I will chat with Michael about the origin of Atmosfy, and how the company keeps its content authentic and organization resilient.
In the meantime, explore our other Cybersecurity Awareness Month resources.
Who do you want to hear from next? Tell us your ideas for future guests in the comments.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
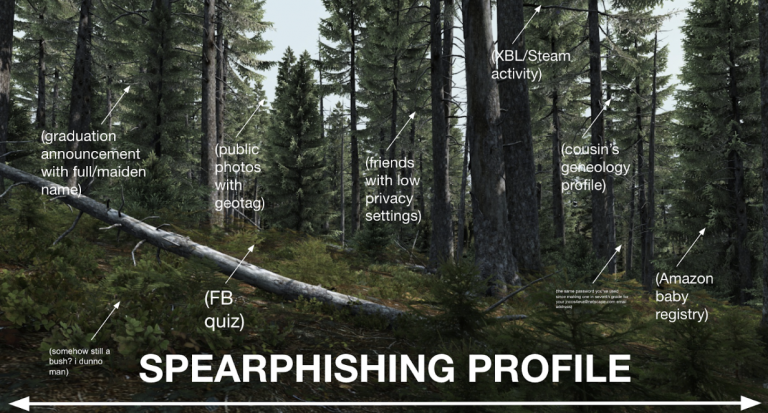
Sharing is caring… but on the internet, sharing can also be tricky! When we post something, we have to look at the forest and not just the trees. Doxxers usually start with one or two pieces of relatively innocent or public information, but by connecting the dots between those pieces they can build a frighteningly detailed picture of an individual.
Seemingly innocuous details can be pieced together into a much more personal profile when collected and leveraged to learn more. As one example, your wish list/wedding registry makes it easy for friends and family to get you gifts that you actually want, but could also be used to find out products/services you’re interested in as pretext (setting the scene) of a conversation or phishing email trying to gather more. You may have Google Alerts set up for your name (a great idea!), but this may not flag text in scanned documents such as school yearbooks, newspapers and other digitized paper records available online.

If the above sounds scary – don’t panic! Your first step in this auto-dox is going to be brainstorming as much personally identifying information (PII) shared online as possible. I suggest doing this either in a secure note or longhand. The goal is to write down all of the accounts/addresses/phone numbers that come to mind, as these are some of the top things that attackers will try to gather in their search. Start your list here:
Email addresses are an especially juicy target for someone trying to locate you, because most people only use one personal and maaaybe a second school or work email account. Those accounts are tied to all our other online identities and often double as our username for logging in.
When you finish this process, you will likely have dozens or even hundreds of “breadcrumbs” between your account list and search results. Read through your list again, and we’re going to sort it into three categories:
Great job! You’ve already got a much better idea of what people can learn about you than most folks ever do, and are well on your way to cleaning up your online footprint. In our next step, we’ll start locking down everything that you want to keep!
P.S. If you’re enjoying this process and value keeping people safe online, please check out our open roles at Cisco Secure.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Whether or not you’ve heard the term “doxxing” before, you’re probably familiar with the problem it names: collecting personal information about someone online to track down and reveal their real-life identity. The motivations for doxxing are many, and mostly malicious: for some doxxers, the goal in tracking someone is identity theft. For others, it’s part of a pattern of stalking or online harassment to intimidate, silence or punish their victim – and overwhelmingly, victims are youth and young adults, women, and LGBTQ+ people. The truth is, most of us have information online that we don’t realize can put us at risk, and that’s why I’ve written this series: to inform readers about how doxxing happens, and how you can protect yourself from this very real and growing problem by doxxing yourself.
In computer security, we talk about the idea of a “security mindset”: understanding how someone with bad intentions would cause harm, and being able to think like they would to find weak spots. In this series, you will learn by doing. By understanding the tools and methods used by those with ill intent, you’ll be better prepared to keep yourself safe and your information secure.
Your mission, should you choose to accept it, is to follow along and find out everything the internet knows about… you!
This series will provide simple steps for you to follow as you begin your investigation. Along the way, as you get familiar with the tools and tactics of internet sleuths, you’ll get a better idea of your current internet footprint as well as know what tracks you leave in the future. Our process will be split into three main sections:

Information is power. And in the case of doxxing, most people don’t realize how much of their power they’re giving up! My goal in this series is to demystify the methods used for doxxing, so in the spirit of “showing my work,” here are some of the best resources and collected checklists I referenced when planning these exercises, along with how to best use each:
If this looks like a whole lot of homework… don’t worry! We’ll cover most of the core tools and tips mentioned in these resources through the course of this series, and we’ll revisit these links at the end of the series when you’ve gotten more context on what they cover. In the next article, we’ll take on the review step of our process, getting a holistic inventory of what personal information is currently available online so you can prioritize the most important fixes. See you soon!
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Self-awareness goes a long way in determining your next professional steps. While job searching, it’s critical to identify how to leverage your transferable skills and network, while also evaluating what environmental factors of work and work culture matter to you most. Learn what it’s like to work at Cisco and the top 10 ways to suss out a workplace that suits your needs from leaders at Cisco Secure, Cisco Talos and Duo Security.
First things first. Emily Reid, the newly appointed director of employee experience at Cisco Secure who came from Duo Security, advises, “Do your own research to see how the company and their employees describe the culture publicly — on the company’s website and through other sites, articles and resources. For tech companies specifically I always think, “What else do you have beyond the ping-pong table?”’
The interview process is the next key opportunity to find out what culture is like beyond amenities. To gain multiple perspectives, Reid recommends asking about company culture in every interview you have.
The question at the top of Reid’s list: Do you have programs and resources to support the development and success of your employees? “I want to know how a company will be investing in my career growth and if I will feel welcome and included as part of the team. Seeing what a company chooses to center and highlight when describing their culture is usually very telling,” she said.
Interning at a company is another way to get firsthand knowledge and can lead to full-time employment. “several former interns are now people leaders managing their own teams — and their own interns — coming full circle,” Reid said.
Knowing that there is safety and support in bringing your whole self to work is vital. What policies, programs and initiatives are in place that demonstrate an organization’s commitment to diversity, equity, inclusion and belonging?
Cisco’s ongoing commitments to social justice and pay parity include twelve action steps as part of Cisco’s Social Justice Blueprint. Cultivating a conscious culture includes on-going dialogue, programs and events meant to increase equality. Employee Resource Organizations and mentorship programs provide more opportunities to build community and share knowledge, resources and advocacy.
What environment allows you to do your best work? Also consider what perks and processes an employer offers to enhance flexibility and adaptability. During the pandemic, Duo and Cisco transitioned all global events, training and professional development workshops to fully virtual. As in person options resumed following the pandemic, all events are designed to ensure an inclusive experience no matter where you’re joining from.
“We don’t want to go back to a world where people not based in an office feel like they are getting a lesser experience,” Reid said.
Considering how to make programs and information accessible to employees regardless of where they work is also important to Sammi Seaman, team lead of employee experience at Cisco Talos. She’s currently spearheading a new hire program that is “more inclusive of folks whether they’re office based, remote or somewhere across the world.”
It’s essential to consider how you want your life and work to intersect, particularly as hybrid work becomes more popular. How important is paid time off, flexible work options or a consistent structure?
Cisco Secure offers “Days for Me,” days off for employees to decompress and do something to fill their cups. Monthly “Focus Days” are days without meetings, so employees can prioritize the projects that need attention.
Curran recalls one candidate who, despite multiple offers from competitors, chose Cisco Secure because of the flexible work environment: “This person has a young child and felt that the “Days for Me” and flexibility to work from home in a hybrid situation would work best for his career long-term.”
As Reid’s team helps lead the transition to hybrid work, the book Out of Office: The Big Problem and Bigger Promise of Working From Home by Charlie Warzel and Anne Helen Petersen has been inspiring. The book “does an amazing job of sharing a vision for an inclusive future that empowers employees to be successful and have a ‘work/life balance’ that truly works,” Reid said.
Currently Cisco Secure offers a hybrid model while many employees still work remotely. In terms of maintaining accessibility through this transition, Marketing Specialist Julie Kramer advocated for more accessibility and saw changes at Cisco as a result.
“Webex pre-COVID didn’t have any closed captioning. So, another deaf person and I reached out and closed captioning and the transcript option got added,” Kramer shared.
Kramer prefers to have high-quality and frequently the same interpreters who “know the terminology for my job, marketing and technology. In business, the security and marketing industry can really talk fast, so you need a high-quality interpreter that can keep up and one that is qualified and certified,” she said.
Consider what pace of your specific role and within an industry is needed for you to feel engaged without overwhelmed. While different roles within the same organization and industry may run at different paces, it’s important to tune into what might be expected on your potential new team.
Seaman finds that the fast pace of cybersecurity can be “delightful and challenging. There’s a lot of fast-paced pivoting that happens, which makes for an interesting workplace because two days are never the same,” she said.
Do you prefer a hierarchical structure, or one that is more flat? Are you most effective and fulfilled riding solo, or while consistently connecting with coworkers? Does contributing your ideas make you feel empowered?
At Cisco Secure, there is space to join conversations. “No matter where you sit in the company, you have a voice and can speak up and collaborate and self-organize on a project. It feels like a bunch of really hard working, humble, smart people who are trying to solve problems together,” said Manager of Duo’s Global Knowledge and Communities Team Kelly Davenport.
To enhance communication and knowledge among distributed teams, Seaman started a dialogue series called “The More You Know.” Questions include: What do you do? How do you do it? How can that help other parts of Cisco Talos? The conversations lead to future collaboration and resource sharing.
Do you want to grow professionally and increase your skills and knowledge? A culture of teaching and learning within an organization can help hone and expand your skills and connections.
Lead of Strategic Business Intelligence Ashlee Benge finds the security world “very dynamic. You really can never stop learning. Within Cisco Talos, the people around me are such smart, dedicated people that there’s really a lot that you can gain from just being involved in the group as a whole.”
For Seaman, who didn’t come from a technical background, Cisco Talos offered opportunities to expand her technical knowledge, including from colleagues. “Coming into Cisco Talos, people are like, “Here, let me teach you. You can totally do this. Just because you didn’t know how to do it doesn’t mean you can’t learn. Let’s go,” Seaman shared. Seaman’s colleagues have also learned from her expertise in information and knowledge management given her background as a librarian.
More formally, the Learning and Development team recently launched a comprehensive talent development program with enablement resources and support for people leaders. Aspects include: “really thoughtful templates for employees to use with their manager to talk through career goals, development areas, and to define an actionable investment plan. These resources are fueling great career conversations, strong alignment, and thoughtful development plans,” Reid said.
Do you want to refine your skills within your wheelhouse? Or are you driven to try new tasks and potentially change roles within your next organization?
Benge, whose background is in computational astrophysics, has found her interests shift from technical security research to business strategy and data science. At Cisco Talos, she’s been involved in everything from detection research and threat hunting, to community outreach, conference talks and traveling to support sales engagements. Currently, she’s helping to lead threat hunting in Ukraine.
“My leaders have always made it very clear that if there’s an interest, it’s okay to pursue it and it doesn’t have to necessarily be within the scope of my role. Having that freedom to pursue interests within the industry has been really engaging,” Benge said.
In addition to company values and mission statements, leaders and employees contribute to an organization’s culture every day. If you want to enhance your company’s culture, participate.
“Feedback on what employees want to see is crucial,” Reid said. “The easiest way to contribute to developing culture and a positive employee experience in your workplace is to add to what’s already happening! Culture takes participation and ownership from all employees.”
Reid shared that in performance reviews at Cisco, “‘Team Impact” is equally as important as “Results.” Contributing positively to company culture should contribute to performance reviews and promotion justification,” she said.
To learn more about Cisco’s company culture and how you can contribute to it, check out our open roles.

We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Over her 25-year-plus career, Saleema Syed has seen the information security industry from a variety of vantage points, all while championing women in technology. Syed worked as director of business systems and data management for Duo Security before rising to vice president of information technology. Later, after Duo was acquired by Cisco, she transitioned to new roles within the larger organization and now heads up operations for Webex Marketing. In this position Syed brings structure across different functions of marketing including brand, events and technology while also serving as chief operating officer for Chief Marketing Officer Aruna Ravichandran.
“I fell in love with the culture, the kindness, the heart of this company,” Syed said.
Recently, she shared her passion for problem solving and inclusion with the Duo Blog, along with the advice she gives mentees navigating their own career paths.
Saleema Syed: I like chaos and I love putting a method to the madness. With marketing we have to react to the market, react to the business, react internally. What energizes me is there’s never a dull day and there is always this ability to bring some overall end to end process.

I love running towards a burning car and figuring out how to put it out. I love change. I know change is the only constant and rather than running away from it, I thrive in it. I like to look at it and ask, “What can we do to break it down and figure out what we need to do?”
My brain works in terms of boxes and flows and charts and spreadsheets so when I look at something I’m like, “Okay, what is a box? What is a process? How do I untangle it?” I like sitting in the discomfort and understanding what to do to get out of it.
Saleema Syed: There are three things I always keep in mind when I look at what I’m doing and where I want to be. One is, at the core of it, does it fill my cup of empathy and allow me to be true to who I am in how I treat people or how I build a team?
The second thing is, will I have the opportunity to influence and impact the people on the team or my family? How do I show myself to my daughter who is growing and seeing how to become who she is as a career person?
The third thing is, is it something new and am I learning something? Continuous learning is a huge part of who I am, so that drives me to get out of my comfort zone constantly.

When I’m changing jobs people usually say, “You’ve set up this team, you’re so comfortable. Now all you have to do is sit back and execute.” And my answer is, “That’s exactly why I am moving.”
If I am comfortable I’m not learning, and I don’t know if I’m adding any more value than I’ve set up. That means it’s time for me to move on and elevate somebody. What I’m doing is sending the elevator down to somebody on the team to grow.
That’s why I’ve had people who work for me for many years follow me through multiple organizations, which as a leader has been my pinnacle of what I call my success. Success is not my role; it is how many people I have impacted and influenced.
Saleema Syed: I keep going back to Duo because working at that organization and meeting those people defined me as a human being. One of the strategic pillars of that organization is to be kinder than necessary.

However complicated the work challenges are, those around me must be aligned with what my integral values are and who I am. They have to have empathy and kindness in their heart. If that is not there, no matter how much I love solving challenges and know I can solve them, I’m not going to go for it. I’ve been extremely lucky at Duo, Cisco and Webex that I’ve been around those kinds of people.
If you look at Webex, I love the core of what we are, the journey we are on, the inclusivity. We are not just selling Webex messaging or other products. At the heart of it we are looking at how we are influencing people and things around us by making sure that there is inclusivity in the collaboration tools that we are launching.
Saleema Syed: My leadership style is pretty simple: nobody works for me; people work with me. I lead with making sure that people know this is the problem you’re trying to solve, here is the context of what we are trying to do. Now, let’s figure out how we solve it. That is something that has helped my team be part of the problem solving that I love to do.
When I interview people my first questions are, “What does the job bring to you? How would this job fill your cup?” That throws people off every time. You can teach any technology, you can teach any skill set, but if you don’t have the basic passion, the attitude to be able to do this job, then everything else can just go out the door.
Saleema Syed: I have a very diverse background. I am an Indian by birth and grew up in the Middle East. When I went into engineering, finished my education and started my career, one of the things I realized was that as a woman of color, I always wanted to apply for positions that I was fully qualified for. I wanted to make sure I knew everything about the job because a very big fear was being asked a question in the interview I didn’t know. LinkedIn’s Gender Insights Report found that women apply for 20% fewer jobs than men despite similar job search behaviors. That has been a very challenging mental barrier for me to break.
Trey Boynton, who was at Duo and now she’s leading Cisco in a beautiful journey of diversity as the senior director of inclusion and collaboration strategy always said, “We have to have that bicycle lane on the road, whether it is for females, whether it is for people of color or any LGBTQIA+ community members. That is how we get people to bring that confidence in to learn, grow and then they can merge easily.”
“Passion is a part of who I am and is contributing to my growth.” – Saleema Syed
Whatever I faced as I was growing up, whether it was my dark skin, whether it was my accent, whether it was, “Oh, you’re way too passionate” has been some of the feedback that I’ve gotten. In my career if I’m told I’m way too passionate I turn that around and say, “Passion is a part of who I am and is contributing to my growth.”
Saleema Syed: Within Webex, within Cisco, I try to be part of anything that I can do in terms of giving back to the community. I’m definitely a big proponent of women in technology. In the local Dallas area I run a program by myself and go into schools and advocate for girls in STEM. Cisco is amazing in how it gives us time to volunteer. I love that educating kids is part of my journey of giving back. That’s the generation you can influence.
How do we enable children and women to be more open to technology and being part of the technology field? Let’s look at the percentage of diversity in the technology field and be aware of it. It’s not only about the diversity numbers, but are we bringing in candidates at the leadership level and giving them not just a seat at the table but a voice at the table, too?
You also have to talk about what you do and with passion and energy because if you don’t, people get intimidated. If you can influence one person who comes from an underrepresented community, imagine what you are doing, not just for that person, but for his household, for his family, for his extended community. I have a lot more to do, but as I get into the next decade of my life and my career, that is something that is a huge focus for me.
Saleema Syed: First and foremost it’s very important to spend time and understand the business and the products in whatever industry you’re going into. It is key to your growth. Especially if it’s a security industry, take time to understand the products, the technology or the function that you’re trying to get into. Contextual understanding and product understanding are extremely important.
The second piece is to keep learning. Cisco is amazing in trying to help you learn and support you financially to be able to do it. I went back and got my executive MBA four years ago. Give yourself a goal of learning a new something, whether it is a new function, new technology or new leadership skill.
The third piece is to create a spreadsheet of where you want to be in two years. Put that out there and then work back just like you would do a project plan. Work back month by month, quarter by quarter. What are the skill sets you need to learn to get there?
The last part is: Do the job you want versus the job you are in. Of course, you have to do the job you are in, but do the job you want to get to. Don’t wait for a title, don’t wait for a promotion to act. No. What do you want to be? Show that to your leaders and yourself. The title will come, money will come, everything will come, but am I doing the job that I want and enjoy and I want to get to?
To learn more about Webex, Cisco and Duo Security and how you can apply your passion, advocacy and problem solving to make a difference in cybersecurity, browse our open roles.

We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Few security career paths are linear. For Stephanie Frankel the journey to Cisco Secure was circuitous. The Ann Arbor, Michigan native studied journalism at the University of Michigan before managing communications for the Washington Capitals and NBC Sports. But after several stints at communications agencies, she charted a new path for herself in cybersecurity. Not only has her diverse background served as a strength in her current role as senior manager for strategy and operations, but it’s also informed her management philosophy.
After doing project management and account direction at consulting agencies, Frankel was interested in honing her skills and expertise on the client side. She had heard amazing things about Duo and wanted to stay in Ann Arbor and work for a company with local roots. After interviewing, Frankel realized that “working at Duo was a cool, exciting opportunity with a really awesome group of people.”
Frankel was on the ground running working as a technical project manager in research and development overseeing the Multi-Factor Authentication, applications and mobile engineering teams despite not having worked in information security before.
Duo’s security education allowed Frankel to understand the industry and is something she values for getting more people into the cybersecurity field. At Duo and Cisco Secure, employees come from a variety of backgrounds and some don’t have much (or any) experience with cybersecurity.
Robust educational programs build knowledge about security and specific products which empower new team members to grow and learn. Every team also has a learning and development budget for employees to quench their curiosity and enhance their knowledge through courses, books or other programs Manager of Global Employee Programs Anndrea Boris shared.
“People are open to having conversations and open to ideas and ways to solve those ideas. If you have an idea of how to solve a problem, no matter whether it’s your job or not, people are open and willing to listen to you.” – Stephanie Frankel
Something Frankel also appreciates most is that ideas are valued at Duo and Cisco Secure: “Even in my first job, I would have ideas and go to my boss or our head of engineering and say, ‘Hey, I think this could be a really cool opportunity, and I think it needs this.’ People are open to having conversations and open to ideas and ways to solve those ideas. If you have an idea of how to solve a problem, no matter whether it’s your job or not, people are willing to listen to you.”
After a year, Frankel moved from engineering to marketing to run operations for Duo’s in-house brand team, leading the team through a rebrand. “The team really rallied behind this new brand and it was amazing to see their pride and hard work when sharing it,” she said. With Frankel’s leadership, the team showcased not only the new look and feel of the brand but also the customer research that went into understanding the need for the change.

“Our amazing team knew that for it to catch on internally we needed to help people understand the why. The team put together an amazing training and went around the company to help people understand the security buyer, the industry overall and our differentiators and how we could do all of this within the umbrella of Cisco,” she said.
Recognizing that she most enjoys and feels best suited for a strategic operations role, she had open conversations with her manager. “I told my boss, ‘It’s just not a great fit.’” Her manager was very supportive, and they worked through potential options. “You’ll find a lot of that at Cisco,” she said.
Now as senior manager in the Strategy and Operations Group within Cisco’s Security and Collaboration division, Frankel runs key initiatives for business operations that drive business growth. She is empowered to creatively solve problems and collaborate “with all the stakeholders within each group to move these programs forward, to understand the problems we’re looking to solve, create objectives, a program plan, and continue to track metrics and progress towards those ultimate goals,” she said.
A self-described “over communicator,” Frankel believes that as a leader, “the more you communicate and the more transparent you are, the better.” Frankel loves leading people who are experts in their fields and letting them do what they do best.
On the brand team, for example, she trusted her team’s expertise in producing stories, videos and animations to demystify Cisco’s security products.
“All I needed to do was give them the objective and the goals and they were able to come up with the solutions,” Frankel said.
She fondly remembers the boss at one of her first jobs out of college. In that job Frankel wrote press releases and wanted her boss to fully approve the final versions before sending them to the media. Once her boss told her, “Stephanie, if you keep giving it back to me, I will keep finding things to change. I trust you to know when it is ready to go.” That confidence in her so early in her career “gave me so much confidence in myself,” she said.
Frankel emulates his approach to management by recognizing that each employee has different needs in their lives, in their careers, and in how they like to receive feedback. From that boss Frankel first learned that for every piece of negative feedback, you must give four pieces of positive feedback for “someone to actually hear it because that’s how you balance things out in your mind.”

Frankel believes feedback is crucial for growth. “I don’t see how you can improve or grow without it, no matter what level of your career you’re at. Feedback shouldn’t be taken as negative, as much as it is a way for you to improve,” she said.
One of the most helpful things Frankel learned in a Cisco class for managers was the importance of asking a person if they are in a good place to receive critical feedback. “You might not be in the mindset to accept the feedback and to do something constructive with it,” she said. ”If you’re having a bad day or struggling, you could say, ‘You know what, I’m not going to be able to take it today, but let’s talk tomorrow and I’ll be in a better place to receive it.’’’
Frankel has spent the last year thriving in a role she never anticipated in an industry her college training in journalism didn’t fully prepare her for. The secret, she says, is keeping an open mind to new possibilities and a willingness to take on new challenges, even if you don’t feel 100% ready.
“A lot of it is getting real world experience and learning your way through it and knowing that there’s a lot of opportunities and a lot of people that are willing to teach you,” she said.

To pivot professionally Frankel advises not feeling pigeonholed just because you studied a particular topic or have been in a certain industry for a long time. Take what you can from where you started such as storytelling and communications skills in the case of journalism for Frankel. While trying something new may require taking a different level or type of job “sometimes it’s worth it because you have that opportunity to grow and you might find you’re happier somewhere else,” she said.
When discerning professional steps Frankel recommends having open and honest conversations with yourself and others such as mentors.
“Cisco has so many mentorship programs and so many people that are knowledgeable about a lot of things,” she said. ”Just because your current role isn’t a great fit doesn’t mean that there’s not another good fit within the corporation, or it doesn’t mean that you can’t create your own good fit.”
Did you know that Cisco offers cybersecurity trainings and certifications? Start developing your cybersecurity skills today! And if you’re ready to jump into an exciting new career in security, check out the open roles at Cisco Secure and Duo Security.

We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels