Feature Two US intelligence bigwigs last week issued stark warnings about foreign threats to American election integrity and security – and the nation's ability to counter these adversaries.…
Don't worry this isn't some sort of stealer that I grabbed from GitHub, nope it's actually my very own framework, it's open source, easy to understand, easy for beginners to learn from the code, easy to run and over all just great at everything one does for recon! Dont worry I'll be updating it continuously fore the framework is on its first little legs but I'll be releasing SubSeekerPro V.2 soon!
Stay tuned and as always, keep grinding my dudes ☝🏻✨

How on earth are we still here? You know, that place where breached companies stand up and go all Iraqi information minister on the incident as if somehow, flatly denying the blatantly obvious will make it all go away. It's the ease of debunking the "no breach here" claim that I find particularly fascinating; the truth is always sitting there in the data and it doesn't take much to bring it to the surface. Ah well, as I always end up lamenting, with behaviour like this it's a good time to be in the industry 🤷♂️

Updated Jack Teixeira, the Air National Guardsman accused of leaking dozens of classified Pentagon documents, is expected to plead guilty in a US court on Monday.…
NSO Group, the Israel-based maker of super-charged snoopware Pegasus, has been ordered by a federal judge in California to share the source code for "all relevant spyware" with Meta's WhatsApp.…
The US Department of Justice has unsealed an indictment accusing an Iranian national of a years-long campaign that compromised hundreds of thousands of accounts and attempting to infiltrate US defense contractors and multiple government agencies.…
Webinar The quantum threat might seem futuristic, more like something you'd encounter in a science fiction film. But it's arguably already a danger to real cyber security defences.…
The UK's Information Commissioner's Office has put the West Midlands Police (WMP) on the naughty step after the force was found to have repeatedly mixed up two people's personal data for years.…
Webinar Dealing with cyber security incidents is an expensive business. Each data breach costs an estimated $4.35 million on average and it's not as if the volume of cyber attacks is falling - last year, they rose by 38 percent according to Google Cloud.…
NTT West president Masaaki Moribayashi announced his resignation on Thursday, effective at the end of March, in atonement for the leak of data pertaining to 9.28 million customers that came to light last October.…
A malware distribution campaign that began last May with a handful of malicious software packages uploaded to the Python Package Index (PyPI) has spread to GitHub and expanded to reach at least 100,000 compromised repositories.…
More than 130 petitions seeking access to push notification metadata have been filed in US courts, according to a Washington Post investigation – a finding that underscores the lack of privacy protection available to users of mobile devices.…
The ransomware group LockBit told officials with Fulton County, Ga. they could expect to see their internal documents published online this morning unless the county paid a ransom demand. LockBit removed Fulton County’s listing from its victim shaming website this morning, claiming the county had paid. But county officials said they did not pay, nor did anyone make payment on their behalf. Security experts say LockBit was likely bluffing and probably lost most of the data when the gang’s servers were seized this month by U.S. and U.K. law enforcement.
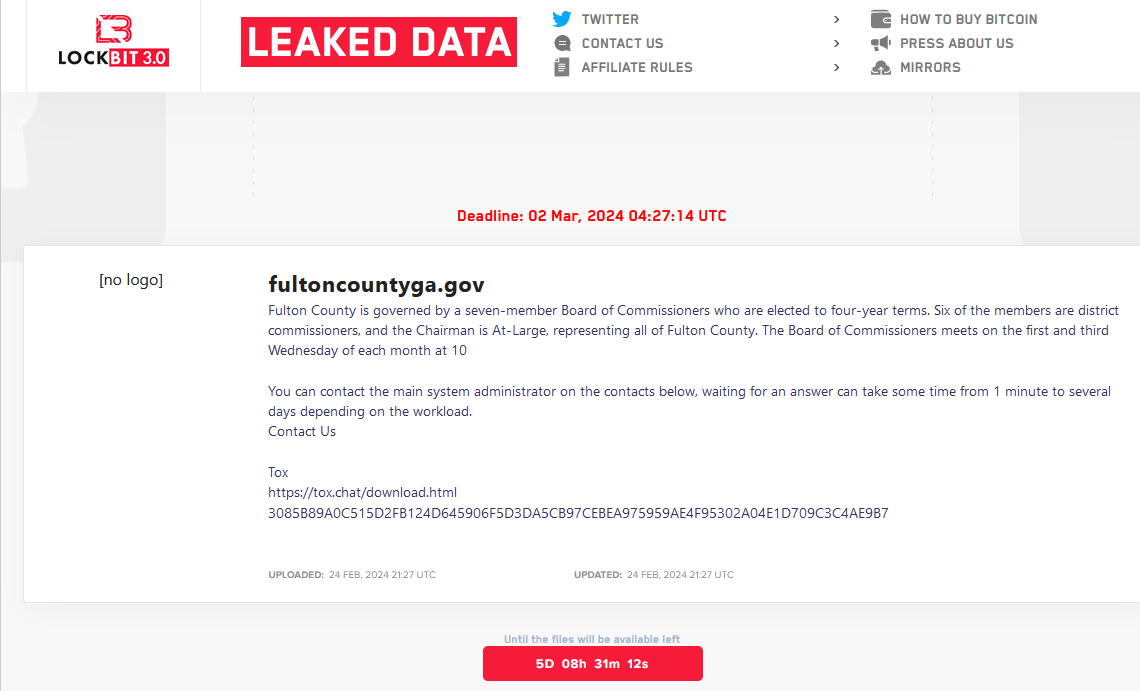
The LockBit website included a countdown timer until the promised release of data stolen from Fulton County, Ga. LockBit would later move this deadline up to Feb. 29, 2024.
LockBit listed Fulton County as a victim on Feb. 13, saying that unless it was paid a ransom the group would publish files stolen in a breach at the county last month. That attack disrupted county phones, Internet access and even their court system. LockBit leaked a small number of the county’s files as a teaser, which appeared to include sensitive and sealed court records in current and past criminal trials.
On Feb. 16, Fulton County’s entry — along with a countdown timer until the data would be published — was removed from the LockBit website without explanation. The leader of LockBit told KrebsOnSecurity this was because Fulton County officials had engaged in last-minute negotiations with the group.
But on Feb. 19, investigators with the FBI and the U.K.’s National Crime Agency (NCA) took over LockBit’s online infrastructure, replacing the group’s homepage with a seizure notice and links to LockBit ransomware decryption tools.
In a press briefing on Feb. 20, Fulton County Commission Chairman Robb Pitts told reporters the county did not pay a ransom demand, noting that the board “could not in good conscience use Fulton County taxpayer funds to make a payment.”
Three days later, LockBit reemerged with new domains on the dark web, and with Fulton County listed among a half-dozen other victims whose data was about to be leaked if they refused to pay. As it does with all victims, LockBit assigned Fulton County a countdown timer, saying officials had until late in the evening on March 1 until their data was published.
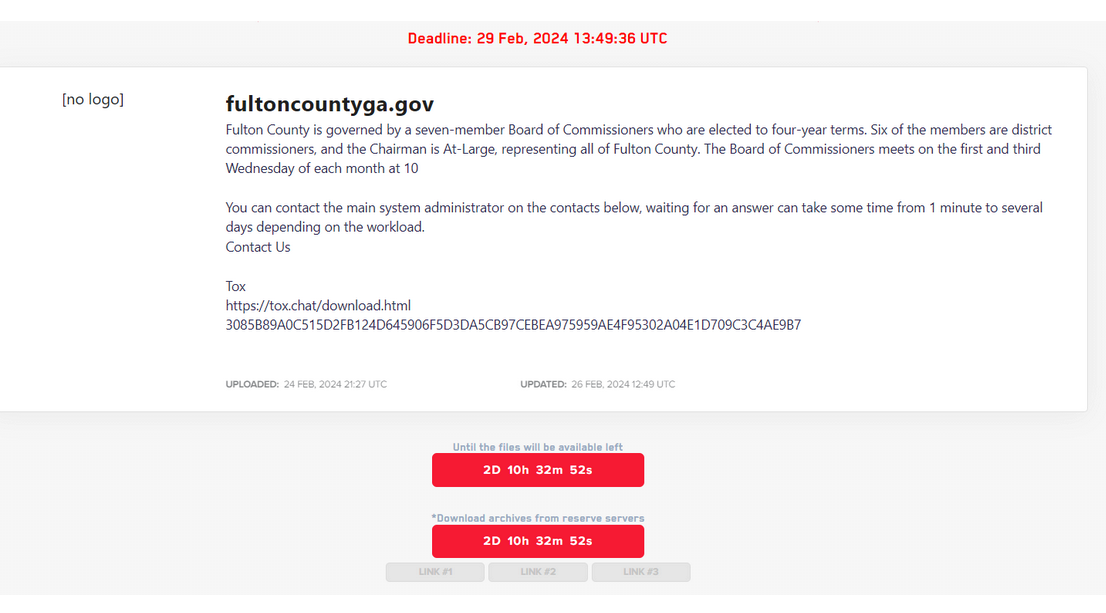
LockBit revised its deadline for Fulton County to Feb. 29.
LockBit soon moved up the deadline to the morning of Feb. 29. As Fulton County’s LockBit timer was counting down to zero this morning, its listing disappeared from LockBit’s site. LockBit’s leader and spokesperson, who goes by the handle “LockBitSupp,” told KrebsOnSecurity today that Fulton County’s data disappeared from their site because county officials paid a ransom.
“Fulton paid,” LockBitSupp said. When asked for evidence of payment, LockBitSupp claimed. “The proof is that we deleted their data and did not publish it.”
But at a press conference today, Fulton County Chairman Robb Pitts said the county does not know why its data was removed from LockBit’s site.
“As I stand here at 4:08 p.m., we are not aware of any data being released today so far,” Pitts said. “That does not mean the threat is over. They could release whatever data they have at any time. We have no control over that. We have not paid any ransom. Nor has any ransom been paid on our behalf.”
Brett Callow, a threat analyst with the security firm Emsisoft, said LockBit likely lost all of the victim data it stole before the FBI/NCA seizure, and that it has been trying madly since then to save face within the cybercrime community.
“I think it was a case of them trying to convince their affiliates that they were still in good shape,” Callow said of LockBit’s recent activities. “I strongly suspect this will be the end of the LockBit brand.”
Others have come to a similar conclusion. The security firm RedSense posted an analysis to Twitter/X that after the takedown, LockBit published several “new” victim profiles for companies that it had listed weeks earlier on its victim shaming site. Those victim firms — a healthcare provider and major securities lending platform — also were unceremoniously removed from LockBit’s new shaming website, despite LockBit claiming their data would be leaked.
“We are 99% sure the rest of their ‘new victims’ are also fake claims (old data for new breaches),” RedSense posted. “So the best thing for them to do would be to delete all other entries from their blog and stop defrauding honest people.”
Callow said there certainly have been plenty of cases in the past where ransomware gangs exaggerated their plunder from a victim organization. But this time feels different, he said.
“It is a bit unusual,” Callow said. “This is about trying to still affiliates’ nerves, and saying, ‘All is well, we weren’t as badly compromised as law enforcement suggested.’ But I think you’d have to be a fool to work with an organization that has been so thoroughly hacked as LockBit has.”
The Biden Administration has asked a court, rather than Congress, to renew controversial warrantless surveillance powers used by American intelligence and due to expire within weeks. It's a move that is either business as usual or an end-run around spying reforms, depending on who in Washington you believe.…
Concerned over the chance that Chinese-made cars could pose a future threat to national security, Biden's administration is proposing plans to probe potential threats posed by "connected" vehicles made in the Middle Kingdom.…
There appears to be an uptick in interest among cybercriminals in infostealers – malware designed to swipe online account passwords, financial info, and other sensitive data from infected PCs – as a relatively cheap and easy way to get a foothold in organizations' IT environments to deploy devastating ransomware.…
Consumer groups are filing legal complaints in the EU in a coordinated attempt to use data protection law to stop Meta from giving local users a "fake choice" between paying up and consenting to being profiled and tracked via data collection.…