AI models, the subject of ongoing safety concerns about harmful and biased output, pose a risk beyond content emission. When wedded with tools that enable automated interaction with other systems, they can act on their own as malicious agents.…
Google has open sourced Magika, an in-house machine-learning-powered file identifier, as part of its AI Cyber Defense Initiative, which aims to give IT network defenders and others better automated tools.…
A Ukrainian cybercrime kingpin who ran some of the most pervasive malware operations faces 40 years in prison after spending nearly a decade on the FBI's Cyber Most Wanted List.…
The murder of 16-year-old schoolgirl Brianna Ghey has kickstarted a debate around limiting children's access to the dark web in the UK, with experts highlighting the difficulty in achieving this.…
Quest Diagnostics has agreed to pay almost $5 million to settle allegations it illegally dumped protected health information – and hazardous waste – at its facilities across California.…
The US government today said it disrupted a botnet that Russia's GRU military intelligence unit used for phishing expeditions, spying, credential harvesting, and data theft against American and foreign governments and other strategic targets.…
Updated Last night's launch of six Pentagon missile-detection satellites was well timed as fears mount that Russia is considering putting nuclear weapons into space.…
Webinar It has become possible to swiftly and inexpensively train, validate and deploy AI models and applications, yet while we embrace innovation, are we aware of the security risks?…
Video conferencing giant Zoom today opened up about a fresh batch of security vulnerabilities affecting its products, including a critical privilege escalation flaw.…
Cybercriminals are targeting iOS users with malware that steals face scans from the users of Apple devices to break into and pilfer money from bank accounts – thought to be a world first.…

Today, the latest issue of The Domain Name Industry Brief Quarterly Report was released by DNIB.com, showing the fourth quarter of 2023 closed with 359.8 million domain name registrations across all top-level domains (TLDs), an increase of 0.6 million domain name registrations, or 0.2%, compared to the third quarter of 2023. Domain name registrations also increased by 8.9 million, or 2.5%, year over year.
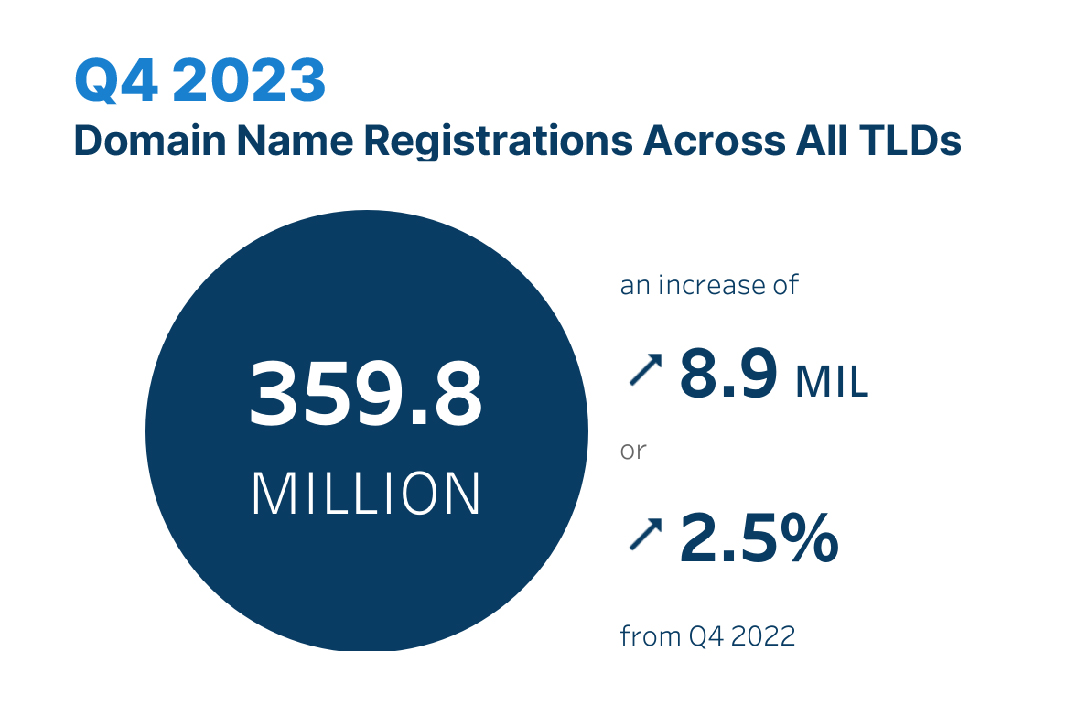
Check out the latest issue of The Domain Name Industry Brief Quarterly Report to see domain name stats from the fourth quarter of 2023, including:
DNIB.com and The Domain Name Industry Brief Quarterly Report are sponsored by Verisign. To see past issues of the quarterly report, interactive dashboards and learn about DNIB.com’s statistical methodology, please visit DNIB.com.
The post Domain Name Industry Brief Quarterly Report: DNIB.com Announces 359.8 Million Domain Name Registrations in the Fourth Quarter of 2023 appeared first on Verisign Blog.
Cyber baddies have turned to ad networks to measure malware deployment and to avoid detection, according to HP Wolf Security.…
The European Court of Human Rights (ECHR) has ruled that laws requiring crippled encryption and extensive data retention violate the European Convention on Human Rights – a decision that may derail European data surveillance legislation known as Chat Control.…
North Korea's latest money-making venture is the production and sale of gambling websites that come pre-infected with malware, according to South Korea's National Intelligence Service (NIS).…
OpenAI has shut down five accounts it asserts were used by government agents to generate phishing emails and malicious software scripts as well as research ways to evade malware detection.…
The Chinese government's Volt Typhoon spy team has apparently already compromised a large US city's emergency services network and has been spotted snooping around America's telecommunications' providers as well.…
Skilled IT professionals considering a career change have a new option, as the US Air Force is reintroducing warrant officer ranks exclusively "within the cyber and information technology professions." …
Prudential Financial, the second largest life insurance company in the US and eight largest worldwide, is dealing with a digital break-in that exposed some internal company and customer records to a criminal group.…
The Minnesota-based Internet provider U.S. Internet Corp. has a business unit called Securence, which specializes in providing filtered, secure email services to businesses, educational institutions and government agencies worldwide. But until it was notified last week, U.S. Internet was publishing more than a decade’s worth of its internal email — and that of thousands of Securence clients — in plain text out on the Internet and just a click away for anyone with a Web browser.
Headquartered in Minnetonka, Minn., U.S. Internet is a regional ISP that provides fiber and wireless Internet service. The ISP’s Securence division bills itself “a leading provider of email filtering and management software that includes email protection and security services for small business, enterprise, educational and government institutions worldwide.”

U.S. Internet/Securence says your email is secure. Nothing could be further from the truth.
Roughly a week ago, KrebsOnSecurity was contacted by Hold Security, a Milwaukee-based cybersecurity firm. Hold Security founder Alex Holden said his researchers had unearthed a public link to a U.S. Internet email server listing more than 6,500 domain names, each with its own clickable link.
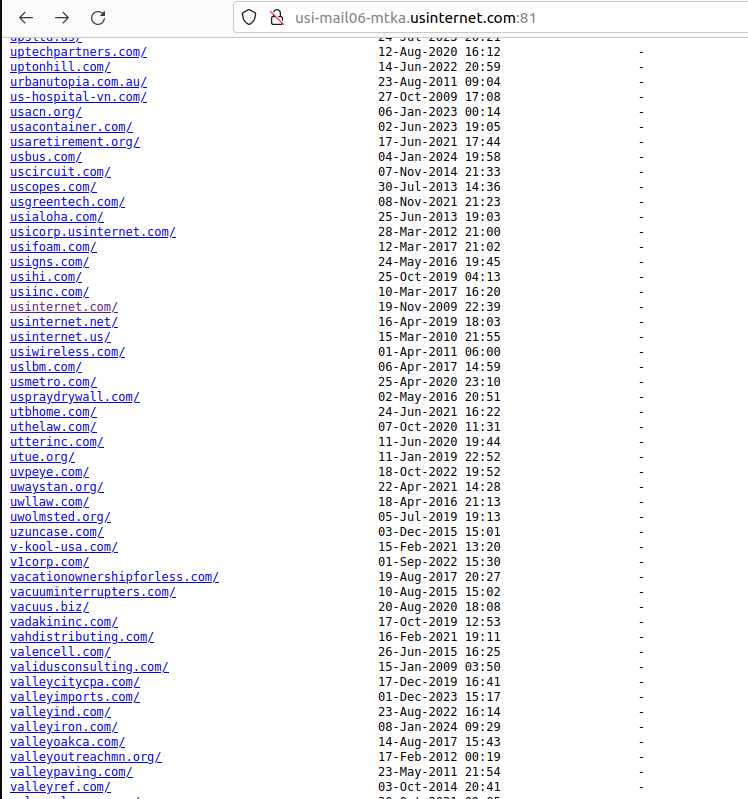
A tiny portion of the more than 6,500 customers who trusted U.S. Internet with their email.
Drilling down into those individual domain links revealed inboxes for each employee or user of these exposed host names. Some of the emails dated back to 2008; others were as recent as the present day.
Securence counts among its customers dozens of state and local governments, including: nc.gov — the official website of North Carolina; stillwatermn.gov, the website for the city of Stillwater, Minn.; and cityoffrederickmd.gov, the website for the government of Frederick, Md.
Incredibly, included in this giant index of U.S. Internet customer emails were the internal messages for every current and former employee of U.S. Internet and its subsidiary USI Wireless. Since that index also included the messages of U.S. Internet’s CEO Travis Carter, KrebsOnSecurity forwarded one of Mr. Carter’s own recent emails to him, along with a request to understand how exactly the company managed to screw things up so spectacularly.
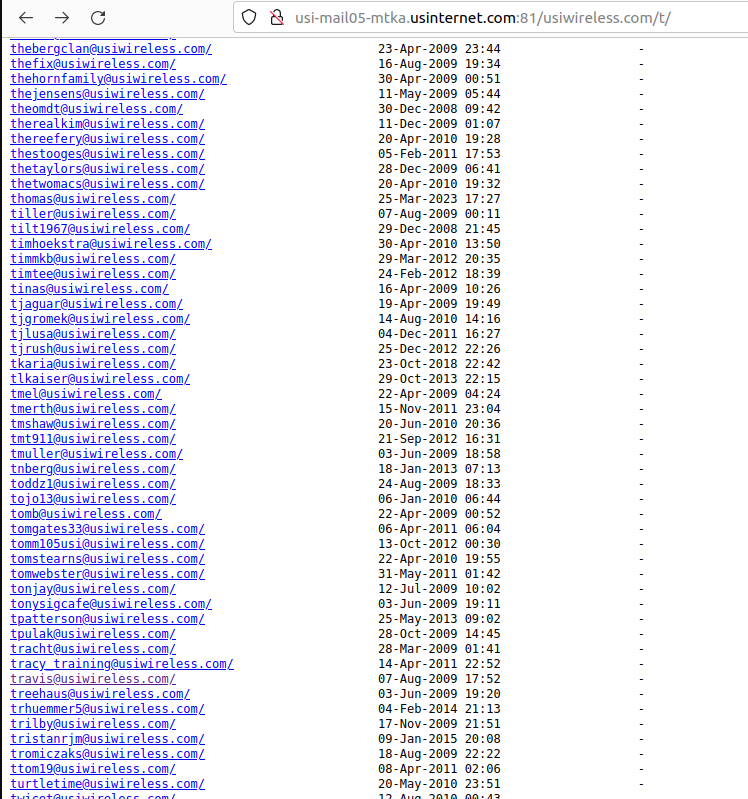
Individual inboxes of U.S. Wireless employees were published in clear text on the Internet.
Within minutes of that notification, U.S. Internet pulled all of the published inboxes offline. Mr. Carter responded and said his team was investigating how it happened. In the same breath, the CEO asked if KrebsOnSecurity does security consulting for hire (I do not).
[Author’s note: Perhaps Mr. Carter was frantically casting about for any expertise he could find in a tough moment. But I found the request personally offensive, because I couldn’t shake the notion that maybe the company was hoping it could buy my silence.]
Earlier this week, Mr. Carter replied with a highly technical explanation that ultimately did little to explain why or how so many internal and customer inboxes were published in plain text on the Internet.
“The feedback from my team was a issue with the Ansible playbook that controls the Nginx configuration for our IMAP servers,” Carter said, noting that this incorrect configuration was put in place by a former employee and never caught. U.S. Internet has not shared how long these messages were exposed.
“The rest of the platform and other backend services are being audited to verify the Ansible playbooks are correct,” Carter said.
Holden said he also discovered that hackers have been abusing a Securence link scrubbing and anti-spam service called Url-Shield to create links that look benign but instead redirect visitors to hacked and malicious websites.
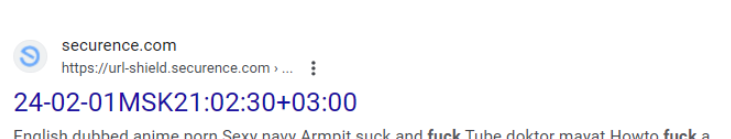
“The bad guys modify the malicious link reporting into redirects to their own malicious sites,” Holden said. “That’s how the bad guys drive traffic to their sites and increase search engine rankings.”
For example, clicking the Securence link shown in the screenshot directly above leads one to a website that tries to trick visitors into allowing site notifications by couching the request as a CAPTCHA request designed to separate humans from bots. After approving the deceptive CAPTCHA/notification request, the link forwards the visitor to a Russian internationalized domain name (рпроаг[.]рф).
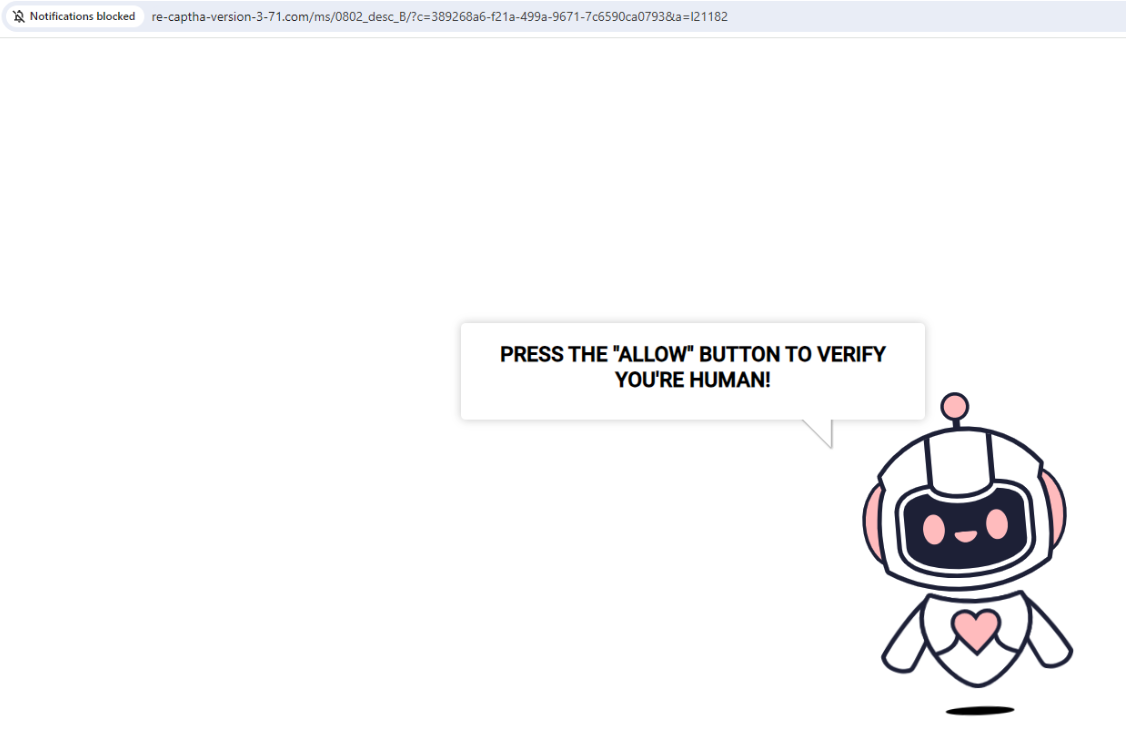
The link to this malicious and deceptive website was created using Securence’s link-scrubbing service. Notification pop-ups were blocked when this site tried to disguise a prompt for accepting notifications as a form of CAPTCHA.
U.S. Internet has not responded to questions about how long it has been exposing all of its internal and customer emails, or when the errant configuration changes were made. The company also still has not disclosed the incident on its website. The last press release on the site dates back to March 2020.
KrebsOnSecurity has been writing about data breaches for nearly two decades, but this one easily takes the cake in terms of the level of incompetence needed to make such a huge mistake unnoticed. I’m not sure what the proper response from authorities or regulators should be to this incident, but it’s clear that U.S. Internet should not be allowed to manage anyone’s email unless and until it can demonstrate more transparency, and prove that it has radically revamped its security.