Sponsored Feature The steady migration of applications and infrastructure out of in-house data centres and server farms and into the cloud looks unstoppable at this moment in time. Research firm Gartner has estimated that by 2025, 51 percent of IT spending on application and infrastructure software, business process services and system infrastructure will have shifted to the public cloud, up from 41 percent in 2022. And you can bet that large volumes of the data that those applications and systems host and process will go with them.…
Organizations hit earlier by the HermeticWiper malware have reportedly been menaced by ransomware unleashed this month against transportation and logistics industries in Ukraine and Poland.…
Japanese industrial giants NTT Communications Corporation and Denso Corporation have decided to start a business “to respond to the threat of increasingly sophisticated cyber-attacks against vehicles.”…
Europol this week said it has arrested 31 people in a crackdown on a car-theft ring that developed and used a technique to steal keyless vehicles.…
A former Wall Street Journal reporter has sued a multinational law firm, some of its attorneys, and others for allegedly stealing his emails and spreading the messages to wrongly discredit him, leading to his firing.…



Interpol arrested 75 suspected members of the Black Axe West African crime syndicate, and intercepted over $1 million in various bank accounts as part of a wide-ranging multi-country operation aimed at thwarting the group's cyber-fraud efforts that fund its criminal operations.…
In brief Advanced persistent threat group (APT) Budworm has shifted targets after hitting the Middle East, Europe and Asia, and was caught this week trying to break into the systems of an unnamed US state legislature.…
Dan Burke is the director of strategy, risk, and compliance for AppDynamics, a company acquired by Cisco in 2017. Burke and his team are a vital part of the Cisco acquisition process in helping acquired companies adhere to a higher level of cybersecurity. This blog is the fourth in a series focused on M&A cybersecurity, following Shiva Persaud’s post on When It Comes to M&A, Security Is a Journey.
Part of the secret to Cisco’s success is its ability to acquire companies that strengthen its technology portfolio and securely integrate them into the larger organization. From the outside, that process might appear seamless—consider Webex or Duo Security, for instance—but a fruitful acquisition takes tremendous work by multiple cross-functional teams, mainly to ensure the acquired company’s solutions and products meet Cisco’s rigorous security requirements.
“My team is responsible for aligning new acquisitions to Cisco controls to maintain our compliance with SOC2 and FedRAMP, as well as other required certifications,” says Burke.
When Cisco acquires a new company, it conducts an assessment and produces a security readiness plan (SRP) document. The SRP details the identified weaknesses and risks within that company and what they need to fix to meet Cisco standards.
“In the past, my team wouldn’t find out about an acquisition until they received a completed SRP. The downside of this approach was that the assessments and negotiations had been done without input from our group of experts, and target dates for resolution had already been decided on,” shares Burke.
“We needed to be involved in the process before the SRP was created to understand all risks and compliance issues in advance. Now we have a partnership with the Cisco Security and Trust M&A team and know about an acquisition months before we can start working to address risks and other issues—before the SRP is completed and the due dates have been assigned,” Burke adds.
“Another issue resolved in this process change is that Cisco can gain earlier access to the people in the acquired company who know the security risks of their solutions. During acquisitions, people will often leave the company, taking with them their institutional knowledge, resulting in Cisco having to start from scratch to identify and assess the risks and determine how best to resolve them as quickly as possible,” says Burke. “It could be vulnerabilities in physical infrastructure or software code or both. It could be that the company isn’t scanning often enough, or they don’t have SOC 2 or FedRAMP certification yet—or they’re not using Cisco’s tools.”
“Third-party vendors and suppliers can also present an issue,” he adds. “One of the biggest risk areas of any company is outside vendors who have access to a company’s data. It’s vital to identify who these vendors are and understand the level of access they have to data and applications. The earlier we know all these things, the more time we must devise solutions to solve them.”
“Now that I’m in the process earlier, I can build a relationship with the people who have the security knowledge—before they leave. If I can understand their mindset and how all these issues came about, I can help them assimilate more easily into the bigger Cisco family,” says Burke.
The additional benefits of bringing teams in earlier are reduced risk and compliance requirements can be met earlier. It also provides a smoother transition for the company being acquired and ensures they meet the security requirements that customers expect when using their technology solutions.
“Without that early involvement, we might treat a low-risk issue as high risk, or vice versa. The misclassification of risk is extremely dangerous. If you’re treating something as high risk, that’s low risk, and you’re wasting people’s time and money. But if something’s high risk and you’re treating it as low risk, then you’re in danger of harming your company,” Burke shares.
“The key is to involve their risk, compliance, and security professionals from the beginning. I think other companies keep the M&A process so closely guarded, to their detriment. I understand the need for privacy and to make sure deals are confidential but bringing us in earlier was an advantage for the M&A team and us,” Burke adds.
When asked what he thinks makes Cisco successful in M&A, Burke says, “Cisco does an excellent job of assimilating everyone into the larger organization. I have worked at other companies where they kept their acquisitions separate, which means you have people operating separately with different controls for different companies. That’s not only a financial burden but also a compliance headache.”
“That’s why Cisco tries to drive all its acquisitions through our main programs and controls. It makes life easier for everyone in terms of compliance. With Cisco, you have that security confidence knowing that all these companies are brought up to their already very high standards, and you can rely on the fact that they don’t treat them separately. And when an acquisition has vulnerabilities, we identify them, set out a remediation path, and manage the process until those risks are resolved,” Burke concludes.
Managing Cybersecurity Risk in M&A
Demonstrating Trust and Transparency in Mergers and Acquisitions
When It Comes to M&A, Security Is a Journey
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
What can schools, which all too often make easy prey for cybercriminals, do to bolster their defenses and keep threats at bay?
The post 5 steps to protect your school from cyberattacks appeared first on WeLiveSecurity
Panic over the risk of deepfake scams is completely overblown, according to a senior security adviser for UK-based infosec company Sophos.…
Asia In Brief Chinese president Xi Jinping has opened the 20th Congress of the Chinese Communist Party with a call for the nation he leads to win the race for development of “core technologies” and to become self-reliant in strategic tech.…

I decided to do something a bit different this week and mostly just answer questions from my talk at GOTO Copenhagen last week. I wasn't actually in Denmark this time, but a heap of really good questions came through and as I started reading them, I thought "this would actually make for a really good weekly update". So here we are, and those questions then spurned on a whole heap more from the live audience too so this week's video became one large Q&A. I hope you enjoy this one, let me know if I should do more of these in the future.

Feature The infosec industry remains mostly a boys club. And while there are some indications that it's becoming more diverse, bringing women into the room continues to move at a glacial pace.…
AMLBot, a service that helps businesses avoid transacting with cryptocurrency wallets that have been sanctioned for cybercrime activity, said an investigation published by KrebsOnSecurity last year helped it shut down three dark web services that secretly resold its technology to help cybercrooks avoid detection by anti-money laundering systems.
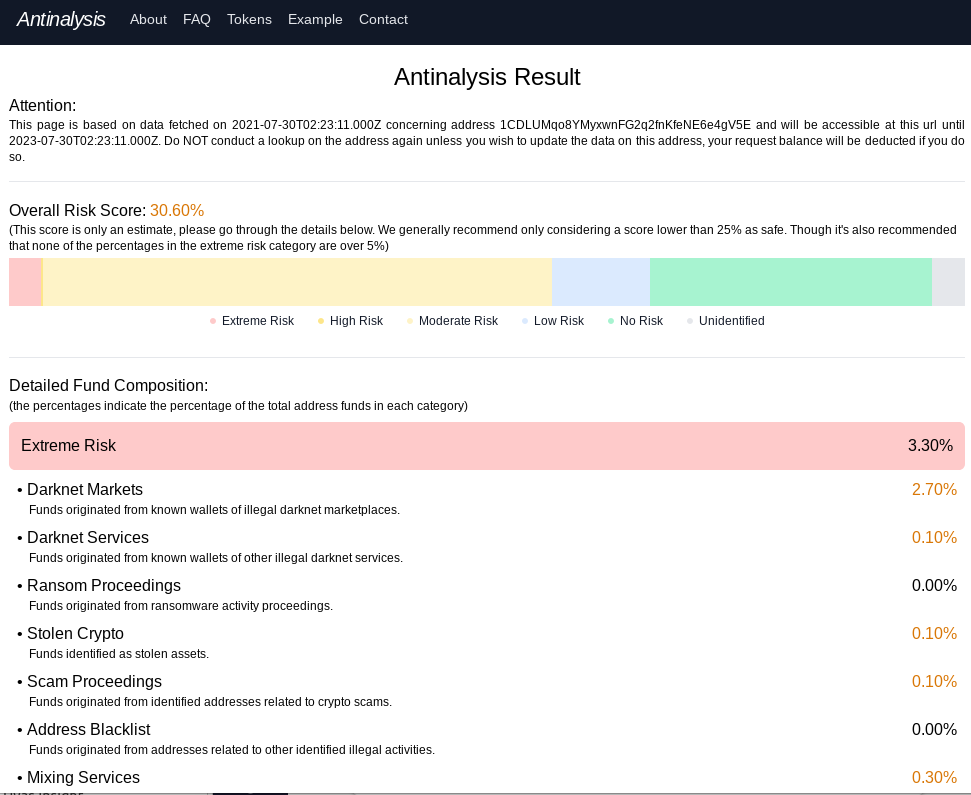
Antinalysis, as it existed in 2021.
In August 2021, KrebsOnSecurity published “New Anti Anti-Money Laundering Services for Crooks,” which examined Antinalysis, a service marketed on cybercrime forums that purported to offer a glimpse of how one’s payment activity might be flagged by law enforcement agencies and private companies that track and trace cryptocurrency transactions.
“Worried about dirty funds in your BTC address? Come check out Antinalysis, the new address risk analyzer,” read the service’s opening announcement. “This service is dedicated to individuals that have the need to possess complete privacy on the blockchain, offering a perspective from the opponent’s point of view in order for the user to comprehend the possibility of his/her funds getting flagged down under autocratic illegal charges.”
Antinalysis allows free lookups, but anyone wishing to conduct bulk look-ups has to pay at least USD $3, with a minimum $30 purchase. Other plans go for as high as $6,000 for 5,000 requests. Nick Bax, a security researcher who specializes in tracing cryptocurrency transactions, told KrebsOnSecurity at the time that Antinalysis was likely a clone of AMLBot because the two services generated near-identical results.
AMLBot shut down Antinalysis’s access just hours after last year’s story went live. However, Antinalysis[.]org remains online and accepting requests, as does the service’s Tor-based domain, and it is unclear how those services are sourcing their information.
AMLBot spokesperson Polina Smoliar said the company undertook a thorough review after that discovery, and in the process found two other services similar to Antinalysis that were reselling their application programming interface (API) access to cybercrooks.
Smoliar said that following the revelations about Antinalysis, AMLBot audited its entire client base, and implemented the ability to provide APIs only after a contract is signed and the client has been fully audited. AMLBot said it also instituted 24/7 monitoring of all client transactions.
“As a result of these actions, two more services with the name AML (the same as AMLBot has) were found to be involved in fraudulent schemes,” Smoliar said. “Information about the fraudsters was also sent to key market participants, and their transaction data was added to the tracking database to better combat money laundering.”
The Antinalysis homepage and chatter on the cybercrime forums indicates the service was created by a group of coders known as the Incognito Team. Tom Robinson, co-founder of the blockchain intelligence firm Elliptic, said the creator of Antinalysis is also one of the developers of Incognito Market, a darknet marketplace specializing in the sale of narcotics.
“Incognito was launched in late 2020, and accepts payments in both Bitcoin and Monero, a cryptoasset offering heightened anonymity,” Robinson said. “The launch of Antinalysis likely reflects the difficulties faced by the market and its vendors in cashing out their Bitcoin proceeds.”
A man who lost $24 million in cryptocurrency in an elaborate SIM swapping scam has won a multi-million-dollar judgment against the thief, who was 15 at the time of the hustle.…
Microsoft Office 365 Message Encryption claims to offer a way "to send and receive encrypted email messages between people inside and outside your organization."…
Online retailer Zoetop will fork out $1.9 million after account data belonging to 46 million customers was stolen in 2018.…





Technology has typically had a reputation for being exciting and inventive. Unfortunately, this hasn’t always been the case for security. But times have changed. We are now recognizing the crucial role security plays in any groundbreaking technology. Without strong defenses, even the most visionary app is likely to crash and burn. So it’s imperative that big security players like Cisco stay on top of what’s next.
I am thrilled to announce that in November, we will be launching our new video series, “NEXT” by Cisco Secure. In the series, my esteemed co-host TK Keanini and I will interview some of the brightest new minds in tech to find out more about the future of the industry and how we can best secure it. Watch the series preview below!
As the CTO of Cisco Secure, TK has over 25 years of networking and security expertise, as well as a penchant for driving technical innovation. As for me, I’m a cybersecurity specialist of 10 years with an obsession for communication and empathy. Together, TK and I will bring new cyber pioneers to the forefront and highlight the criticality of digital protection and privacy for everyone.
Whether we’re discussing Web3, the metaverse, or next-generation healthcare, we’ll learn and laugh a lot. Through simple conversations about complex topics, we’re building a bridge between leading-edge tech and how Cisco is helping to safeguard what’s on the horizon.
And what better time to preview this series than during Cybersecurity Awareness Month? A time when we focus on the reality that security belongs to everyone — not just the threat hunter, or the product engineer, or the incident responder — but everyone.
We all have a responsibility to protect the world’s data and infrastructure, and should all have a seat at the table for important security conversations. We hope you’ll join us as we dive into what’s making waves out there, and how we can keep it safe.
Follow our Cisco Secure social channels to catch our first episode in November, when we will speak with Michael Ebel, CEO of Atmosfy. Atmosfy is revolutionizing restaurant reviews by incorporating engaging live video that inspires others and supports local businesses. TK and I will chat with Michael about the origin of Atmosfy, and how the company keeps its content authentic and organization resilient.
In the meantime, explore our other Cybersecurity Awareness Month resources.
Who do you want to hear from next? Tell us your ideas for future guests in the comments.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Sponsored Feature We hear the term data sovereignty more and more these days. That's strange in some ways because the rules for flinging data around the world have been a challenge for decades – particularly since the internet hit critical mass in the late 1990s and early 2000s and international data transfers went from being a rarity to the norm.…
More than a dozen organizations operating in various verticals were attacked by the threat actor
The post ESET research into POLONIUM’s arsenal – Week in security with Tony Anscombe appeared first on WeLiveSecurity
Advanced, a managed software provider to the UK National Health Service, has confirmed that customer data was indeed lifted as part of the attack by cyber baddies that has disrupted operations for months.…
From a little girl financially helping her family in Jerusalem to a Nobel Prize laureate. That is the exceptional life of Ada Yonath in a nutshell.
The post Life in pursuit of answers: In the words of Ada Yonath appeared first on WeLiveSecurity
India's minister of state for electronics and information technology, Rajeev Chandrasekhar, has hinted strongly that he will again extend the deadline to comply with sweeping new information security reporting rules that were imposed as an essential national defence mechanism.…
Miscreants broke into the Church of Jesus Christ of Latter-day Saints' computer systems and stole personal data belonging to "some" members, employees, contractors and friends, the church has confirmed.…
Interview Crimeware targeting banks and other financial-services organizations today features sophisticated capabilities and evasion tools, according to Kaspersky's lead security researcher Sergey Lozhkin.…


