This month’s Patch Tuesday offers a little something for everyone, including security updates for a zero-day flaw in Microsoft Windows that is under active attack, and another Windows weakness experts say could be used to power a fast-spreading computer worm. Also, Apple has also quashed a pair of zero-day bugs affecting certain macOS and iOS users, and released iOS 16, which offers a new privacy and security feature called “Lockdown Mode.” And Adobe axed 63 vulnerabilities in a range of products.
Microsoft today released software patches to plug at least 64 security holes in Windows and related products. Worst in terms of outright scariness is CVE-2022-37969, which is a “privilege escalation” weakness in the Windows Common Log File System Driver that allows attackers to gain SYSTEM-level privileges on a vulnerable host. Microsoft says this flaw is already being exploited in the wild.
Kevin Breen, director of cyber threat research at Immersive Labs, said any vulnerability that is actively targeted by attackers in the wild must be put to the top of any patching list.
“Not to be fooled by its relatively low CVSS score of 7.8, privilege escalation vulnerabilities are often highly sought after by cyber attackers,” Breen said. “Once an attacker has managed to gain a foothold on a victim’s system, one of their first actions will be to gain a higher level of permissions, allowing the attacker to disable security applications and any device monitoring. There is no known workaround to date, so patching is the only effective mitigation.”
Satnam Narang at Tenable said CVE-2022-24521 — a similar vulnerability in the same Windows log file component — was patched earlier this year as part of Microsoft’s April Patch Tuesday release and was also exploited in the wild.
“CVE-2022-37969 was disclosed by several groups, though it’s unclear if CVE-2022-37969 is a patch-bypass for CVE-2022-24521 at this point,” Narang said.
Another vulnerability Microsoft patched this month — CVE-2022-35803 — also seems to be related to the same Windows log file component. While there are no indications CVE-2022-35803 is being actively exploited, Microsoft suggests that exploitation of this flaw is more likely than not.
Trend Micro’s Dustin Childs called attention to CVE-2022-34718, a remote code execution flaw in the Windows TCP/IP service that could allow an unauthenticated attacker to execute code with elevated privileges on affected systems without user interaction.
“That officially puts it into the ‘wormable’ category and earns it a CVSS rating of 9.8,” Childs said. “However, only systems with IPv6 enabled and IPSec configured are vulnerable. While good news for some, if you’re using IPv6 (as many are), you’re probably running IPSec as well. Definitely test and deploy this update quickly.”
Cisco Talos warns about four critical vulnerabilities fixed this month — CVE-2022-34721 and CVE-2022-34722 — which have severity scores of 9.8, though they are “less likely” to be exploited, according to Microsoft.
“These are remote code execution vulnerabilities in the Windows Internet Key Exchange protocol that could be triggered if an attacker sends a specially crafted IP packet,” wrote Jon Munshaw and Asheer Malhotra. “Two other critical vulnerabilities, CVE-2022-35805 and CVE-2022-34700 exist in on-premises instances of Microsoft Dynamics 365. An authenticated attacker could exploit these vulnerabilities to run a specially crafted trusted solution package and execute arbitrary SQL commands. The attacker could escalate their privileges further and execute commands as the database owner.”
 Not to be outdone, Apple fixed at least two zero-day vulnerabilities when it released updates for iOS, iPadOS, macOS and Safari. CVE-2022-32984 is a problem in the deepest recesses of the operating system (the kernel). Apple pushed an emergency update for a related zero-day last month in CVE-2022-32983, which could be used to foist malware on iPhones, iPads and Macs that visited a booby-trapped website.
Not to be outdone, Apple fixed at least two zero-day vulnerabilities when it released updates for iOS, iPadOS, macOS and Safari. CVE-2022-32984 is a problem in the deepest recesses of the operating system (the kernel). Apple pushed an emergency update for a related zero-day last month in CVE-2022-32983, which could be used to foist malware on iPhones, iPads and Macs that visited a booby-trapped website.
Also listed under active attack is CVE-2022-32817, which has been fixed on macOS 12.6 (Monterey), macOS 11.7 (Big Sur), iOS 15.7 and iPadOS 15.7, and iOS 16. The same vulnerability was fixed in Apple Watch in July 2022, and credits Xinru Chi of Japanese cybersecurity firm Pangu Lab.
“Interestingly, this CVE is also listed in the advisory for iOS 16, but it is not called out as being under active exploit for that flavor of the OS,” Trend Micro’s Childs noted. “Apple does state in its iOS 16 advisory that ‘Additional CVE entries to be added soon.’ It’s possible other bugs could also impact this version of the OS. Either way, it’s time to update your Apple devices.”
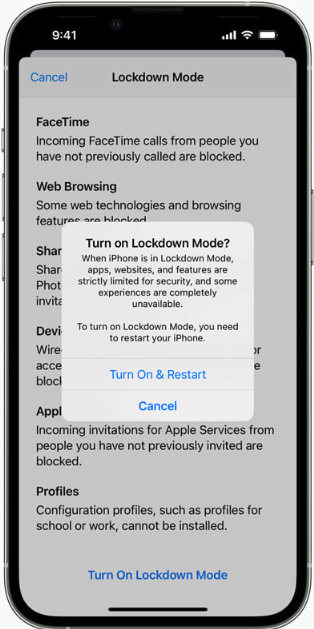
Apple’s iOS 16 includes two new security and privacy features — Lockdown Mode and Safety Check. Wired.com describes Safety Check as a feature for users who are at risk for, or currently experiencing, domestic abuse.
“The tool centralizes a number of controls in one place to make it easier for users to manage and revoke access to their location data and reset privacy-related permissions,” wrote Lily Hay Newman.
“Lockdown Mode, on the other hand, is meant for users who potentially face targeted spyware attacks and aggressive state-backed hacking. The feature comprehensively restricts any nonessential iOS features so there are as few potential points of entry to a device as possible. As more governments and repressive entities around the world have begun purchasing powerful commodity spyware to target individuals of particular importance or interest, iOS’s general security defenses haven’t been able to keep pace with these specialized threats.”
To turn on Lockdown Mode in iOS 16, go to Settings, then Privacy and Security, then Lockdown Mode. Safety Check is located in the same area.
Finally, Adobe released seven patches addressing 63 security holes in Adobe Experience Manager, Bridge, InDesign, Photoshop, InCopy, Animate, and Illustrator. More on those updates is here.
Don’t forget to back up your data and/or system before applying any security updates. If you experience glitches or problems installing any of these patches this month, please consider leaving a comment about it below; there’s a decent chance other readers have experienced the same and may chime in here with useful tips.
Twitter's former head of security Peiter "Mudge" Zatko on Tuesday told the US Senate Judiciary Committee that the social media company's lax data handling and inability to present problems to its board of directors threaten the privacy, security, and democracy for Americans.…
Patch Tuesday September's Patch Tuesday is here and it brings, among other things, fixes from Microsoft for one security bug that miscreants have used to fully take over Windows systems along with details of a second vulnerability that, while not yet under attack, has already been publicly disclosed.…






pipe-light-not-1200











The Lorenz ransomware gang is exploiting a vulnerability in Mitel VoIP appliances to break corporate networks.…

Sponsored Post No matter how hard organizations in Latin America try to stop malicious attackers from infiltrating their IT systems, breaches are inevitable – as recent events demonstrate. …






Has your Wi-Fi speed slowed down to a crawl? Here are some of the possible reasons along with a few quick fixes to speed things up.
The post Why is my Wi‑Fi slow and how do I make it faster? appeared first on WeLiveSecurity
Elon Musk has come up with a new reason to get out of his acquisition of Twitter - a severance payment.…
Multiple high-severity firmware bugs in HP's business computers remain unpatched, some more than a year after Binarly security researchers disclosed the vulnerabilities to HP and then discussed them at the Black Hat security conference last month.…
The Yanluowang ransomware group behind the May attack on Cisco Systems has publicly leaked the stolen files on the dark web over the weekend, but the networking giant says there's nothing to worry about.…
Chinese scammers have reportedly stolen a whopping $529 million dollars from Indian residents using instant lending apps, lures of part-time jobs, and bogus cryptocurrency trading schemes, according to the cyber crime unit in the state of Uttar Pradesh.…
Apple has pushed out five security fixes including two vulnerabilities in its iPhones, iPads and Mac operating systems that are already being exploited.…



apple-plus-16-1200








Google closed its $5.4 billion Mandiant acquisition today in a move that brings the threat intel and incident response giant under the Google Cloud umbrella. …
The hybrid work environment has been around for years, albeit not common but it existed. I can recall my first job where I was able to split my time working in an office and working from my makeshift home office. This was many moons ago as I will call it… pre-COVID-19.
Job seekers are certainly looking to have the flexibility of working from anywhere at any time – preferably in an environment of their choosing. Even though a hybrid workforce will provide people with the option to work from anywhere, those remote locations are sometimes in unsecured locations. Organizations must now reimagine a workforce that will need access to your internal collaboration tools along with access to your network from both on- and off-premises.
Cisco, a leader in equipping organizations with the right products for a hybrid workforce, provides the tools & services to protect your organization from bad threat actors.
With pervasive ransomware attacks, malware attacks, and email attacks, you must be ready and have not only a security solution but also a security analyst team ready to respond when an attack happens.
Securing access to your endpoint must be a top priority and your security analysts must be agile and have the right telemetry to provide around-the-clock monitoring and the ability to quickly respond to threats.
Cisco Secure Endpoint provides you with the visibility and ability to respond to threats by blocking them before they compromise your network. Combined with global, proactive threat hunting, leading-edge forensic/analytic capabilities, and reduced leading Mean Time To Detection (MTTD)/Mean Time To Resolution (MTTR) across the supply chain that no other vendor can parallel; why would you partner with any other company to secure and scale your unique hybrid workforce or workplace clients?
Click here to listen to my fireside chat on how we at Cisco would define 5 Best Practices Security Analysts Can Use to Secure Their Hybrid Workforce:
I am joined by Cisco Talos global Senior Threat Defense and Response Analyst, William (Bill) Largent who has over 20 plus years of infosec experience, specifically in network intrusion detection, traffic analysis, and signature/rule writing.
I will also be speaking with Eric Howard, Cisco Secure Technical Marketing Engineer Leader for the Security Platform and Response Group. Eric is a seasoned team leader in both Information Security Sales, and Product Management. He has built and led teams that apply deep technical understanding to business needs, initiatives, and strategies in both start-ups and established companies.
This is a conversation you do not want to skip! There were a lot of gems shared by these gentlemen that will get you where you need to be as a Security Analyst.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
In an IT world that is increasingly automated, there are still occasions when manual operations are necessary. According to Microsoft, one of these times is when security events are reported to enterprise security operation centers (SOCs).…
Webinar Keeping data secure from ransomware attacks requires dedicated attention to constantly evolving risks. Zero Trust security is one of the many rungs on the IT team's Jacob's Ladder to data asset security heaven. But there are other steps you can take, not least making assured data recovery integral to an organization's cyber security.…

.jpg)
Worok takes aim at various high-profile organizations that operate in multiple sectors and are located primarily in Asia
The post ESET Research uncovers new APT group Worok – Week in security with Tony Anscombe appeared first on WeLiveSecurity