








This blog was also published by APNIC.
With so much traffic on the global internet day after day, it’s not always easy to spot the occasional irregularity. After all, there are numerous layers of complexity that go into the serving of webpages, with multiple companies, agencies and organizations each playing a role.
That’s why when something does catch our attention, it’s important that the various entities work together to explore the cause and, more importantly, try to identify whether it’s a malicious actor at work, a glitch in the process or maybe even something entirely intentional.
That’s what occurred last year when Internet Corporation for Assigned Names and Numbers staff and contractors were analyzing names in Domain Name System queries seen at the ICANN Managed Root Server, and the analysis program ran out of memory for one of their data files. After some investigating, they found the cause to be a very large number of mysterious queries for unique names such as f863zvv1xy2qf.surgery, bp639i-3nirf.hiphop, qo35jjk419gfm.net and yyif0aijr21gn.com.
While these were queries for names in existing top-level domains, the first label consisted of 12 or 13 random-looking characters. After ICANN shared their discovery with the other root server operators, Verisign took a closer look to help understand the situation.
One of the first things we noticed was that all of these mysterious queries were of type NS and came from one autonomous system network, AS 15169, assigned to Google LLC. Additionally, we confirmed that it was occurring consistently for numerous TLDs. (See Fig. 1)
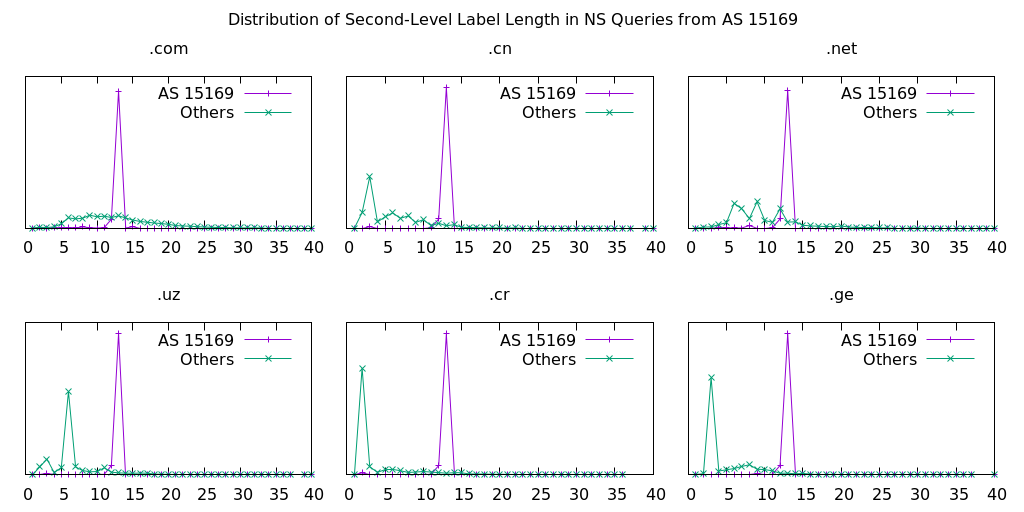
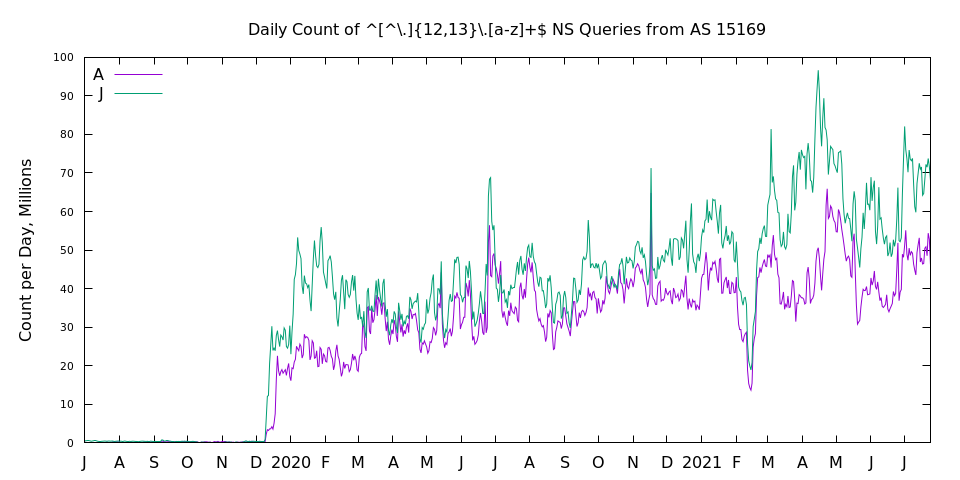
Although this phenomenon was newly uncovered, analysis of historical data showed these traffic patterns actually began in late 2019. (See Fig. 2)
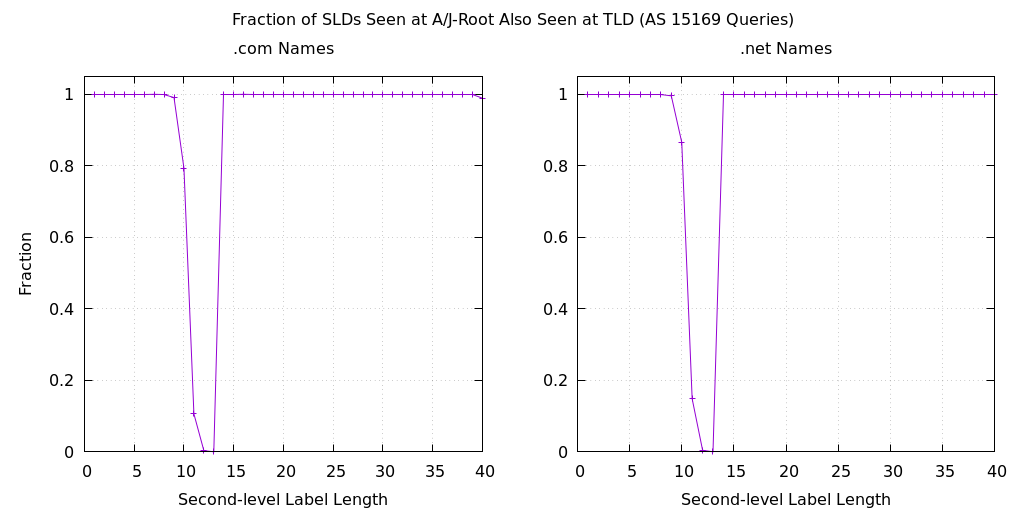
Perhaps the most interesting discovery, however, was that these specific query names were not also seen at the .com and .net name servers operated by Verisign. The data in Figure 3 shows the fraction of queried names that appear at A-root and J-root and also appear on the .com and .net name servers. For second-level labels of 12 and 13 characters, this fraction is essentially zero. The graphs also show that there appears to be queries for names with second-level label lengths of 10 and 11 characters, which are also absent from the TLD data.
The final mysterious aspect to this traffic is that it deviated from our normal expectation of caching. Remember that these are queries to a root name server, which returns a referral to the delegated name servers for a TLD. For example, when a root name server receives a query for yyif0aijr21gn.com, the response is a list of the name servers that are authoritative for the .com zone. The records in this response have a time to live of two days, meaning that the recursive name server can cache and reuse this data for that amount of time.
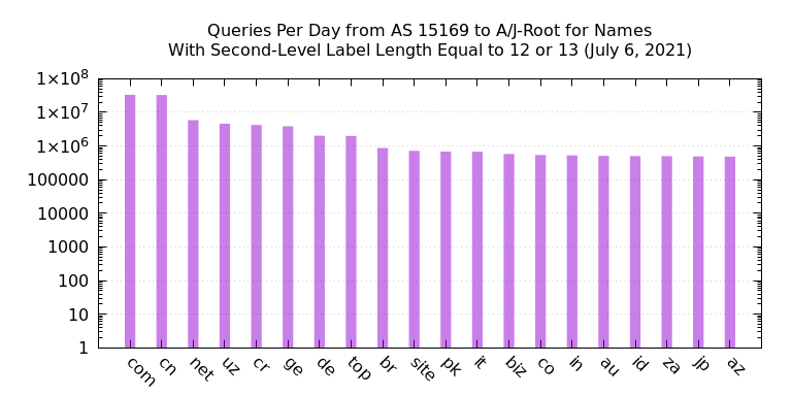
However, in this traffic we see queries for .com domain names from AS 15169 at the rate of about 30 million per day. (See Fig. 4) It is well known that Google Public DNS has thousands of backend servers and limits TTLs to a maximum of six hours. Assuming 4,000 backend servers each cached a .com referral for six hours, we might expect about 16,000 queries over a 24-hour period. The observed count is about 2,000 times higher by this back-of-the-envelope calculation.
From our initial analysis, it was unclear if these queries represented legitimate end-user activity, though we were confident that source IP address spoofing was not involved. However, since the query names shared some similarities to those used by botnets, we could not rule out malicious activity.
These findings were presented last year at the DNS-OARC 35a virtual meeting. In the conference chat room after the talk, the missing piece of this puzzle was mentioned by a conference participant. There is a Google webpage describing its public DNS service that talks about prepending nonce (i.e., random) labels for cache misses to increase entropy. In what came to be known as “the Kaminsky Attack,” an attacker can cause a recursive name server to emit queries for names chosen by the attacker. Prepending a nonce label adds unpredictability to the queries, making it very difficult to spoof a response. Note, however, that nonce prepending only works for queries where the reply is a referral.
In addition, Google DNS has implemented a form of query name minimization (see RFC 7816 and RFC 9156). As such, if a user requests the IP address of www.example.com and Google DNS decides this warrants a query to a root name server, it takes the name, strips all labels except for the TLD and then prepends a nonce string, resulting in something like u5vmt7xanb6rf.com. A root server’s response to that query is identical to one using the original query name.
Now, we are able to explain nearly all of the mysterious aspects of this query traffic from Google. We see random second-level labels because of the nonce strings that are designed to prevent spoofing. The 12- and 13-character-long labels are most likely the result of converting a 64-bit random value into an unpadded ASCII label with encoding similar to Base32. We don’t observe the same queries at TLD name servers because of both the nonce prepending and query name minimization. The query type is always NS because of query name minimization.
With that said, there’s still one aspect that eludes explanation: the high query rate (2000x for .com) and apparent lack of caching. And so, this aspect of the mystery continues.
Even though we haven’t fully closed the books on this case, one thing is certain: without the community’s teamwork to put the pieces of the puzzle together, explanations for this strange traffic may have remained unknown today. The case of the mysterious DNS root query traffic is a perfect example of the collaboration that’s required to navigate today’s ever-changing cyber environment. We’re grateful and humbled to be part of such a dedicated community that is intent on ensuring the security, stability and resiliency of the internet, and we look forward to more productive teamwork in the future.
The post More Mysterious DNS Root Query Traffic from a Large Cloud/DNS Operator appeared first on Verisign Blog.

Whether you think you might have a virus on your computer or devices, or just want to keep them running smoothly, it’s easy to do a virus scan. How to check for viruses depends on the software and device you have, so we’ll go through everything you need to know to run a scan effectively and keep your computers, phones and tablets in tip-top shape.
First, let’s cover a few of the telltale signs your device might have a virus. Is your computer or device acting sluggish or having a hard time booting up? Have you noticed missing files or a lack of storage space? Have you noticed emails or messages sent from your account that you did not write? Perhaps you’ve noticed changes to your browser homepage or settings? Or maybe, you’re seeing unexpected pop-up windows, or experiencing crashes and other program errors. These are all examples of signs that you may have a virus, but don’t get too worried yet, because many of these issues can be resolved with a virus scan.
Each antivirus program works a little differently, but in general the software will look for known malware that meets a specific set of characteristics. It may also look for variants of these known threats that have a similar code base. Some antivirus software even checks for suspicious behavior. If the software comes across a dangerous program or piece of code, it removes it. In some cases, a dangerous program can be replaced with a clean one from the manufacturer.
The process of checking for viruses depends on the device type and its operating system. Check out these tips to help you scan your computers, phones and tablets.
If you use Windows 10, go into “Settings” and look for the “Updates & Security” tab. From there you can locate a “Scan Now” button.
Of course, many people have invested in more robust antivirus software that has a high accuracy rate and causes less drain on their system resources, such as McAfee Total Protection. To learn how to run a virus scan using your particular antivirus software, search the software’s help menu or look online for instructions.
Mac computers don’t have a built-in antivirus program, so you will have to download security software to do a virus scan. There are some free antivirus applications available online, but we recommend investing in trusted software that can protect you from a variety of threats. Downloading free software and free online virus scans can be risky, since cybercriminals know that this is a good way to spread malware.
Whichever program you choose, follow their step-by-step instructions on how to perform a virus scan, either by searching under “help” or looking it up on their website.
Yes, you can get a virus on your phone or tablet, although they are less common than on computers. However, the wider category of mobile malware is on the rise and your device can get infected if you download a risky app, click on an attachment in a text message, visit a dangerous webpage, or connect to another device that has malware on it.
Fortunately, you can protect your devices with mobile security software. It doesn’t usually come installed, so you will have to download an application and follow the instructions.
Because the Android platform is an open operating system, there are a number of antivirus products for Android devices, that allows you to do a virus scan.
Apple devices are a little different because they have a closed operating system that doesn’t allow third parties to see their code. Although Apple has taken other security precautions to reduce malware risks, such as only allowing the installation of apps from Apple’s official app store, these measures aren’t the same as an antivirus program.
For more robust protection on your Apple devices, you can install mobile security software to protect the private data you have stored on your phone or tablet, such as contacts, photos and messages.
If safeguarding all your computers and devices individually sounds overwhelming, you can opt for a comprehensive security product that protects computers, smartphones and tablets from a central control center, making virus prevention a breeze.
New online threats emerge every day, putting our personal information, money and devices at risk. In the first quarter of 2019 alone McAfee detected 504 new threats per minute, as cybercriminals employed new tactics. That’s why it is essential to stay ahead of these threats by using security software that is constantly monitoring and checking for new known threats, while safeguarding all of your sensitive information. Virus scans are an essential part of this process when it comes to identifying and removing dangerous code.
Most antivirus products are regularly scanning your computer or device in the background, so you will only need to start a manual scan if you notice something suspicious, like crashes or excessive pop-ups. You can also program regular scans on your schedule.
Of course, the best protection is to avoid getting infected in the first place. Here are a few smart tips to sidestep viruses and other malware:
The post How To Do A Virus Scan appeared first on McAfee Blog.


apple-1200


I can remember so clearly the day I got my first mobile phone. I was 21, had just finished university and was beyond excited at the idea of driving around in my red Mazda 121 (bubble car) making calls on my new fancy phone! The fact that it was the size of a brick, didn’t bother me a bit – I was connected!!
Without a doubt, mobile phones have completely changed our expectations of being connected and contactable. If calls or texts are not promptly returned in 2022, the lack of reply may be interpreted as rude or, worst case – the sender may feel that they’ve been ghosted!
So, in our super-connected society, it’s inevitable that our kids want to get in on the action. But when is the right time to give them a phone of their own? And how can you keep them safe?
In 2020, the Australian Communications and Media Authority released a report, entitled Kids and Mobiles: how Australian children are using mobile phones, which found that in 2020, just under half (46%) of Aussie children aged 6 to 13 used a mobile phone. 33% of children owned the phone they used while the remaining 14% used a device that didn’t belong to them.
The research also showed that playing games, taking photos/videos, and using apps were the most common activities undertaken on a mobile phone. Using the phone to communicate via text messages and calling a parent or family member was also a common activity – and actually increased in the three years prior.
And if your tweens and teens are telling you that “everyone has a phone” then it looks like they are on the money, with the report revealing that 76% of 12- and 13-year-olds own their own devices.
In my opinion, there are many factors that need to be considered when making this big decision. You need to take into account your child’s maturity, their technology habits, and most importantly, your gut instinct – one of the most powerful parenting tools, in my opinion!
And please, don’t think that is a one size fits all answer here because there absolutely isn’t. If there is one thing parenting 4 boys has taught me is that not only does each child have different strengths, but they mature at their own pace. So, when considering whether your child is ready, don’t think about their age. Instead, ask yourself whether they can handle the technology properly and robust enough to navigate the tricky stuff. A naïve 14-year-old with low social awareness may not be as ready as a savvy 12-year-old who has previously demonstrated successful problem-solving skills.
Here are some things to consider:
Let me share my biggest piece of advice – before you put that phone into your child’s hand, PLEASE set the ground rules. Their willingness to co-operate will be vastly reduced once the phone is theirs! Some families choose to outline the ground rules for any device (including a phone) in a family technology agreement. And it’s not a bad idea: you develop the rules and the boundaries and then have them sign it – just like a contract. I love this agreement from America’s Family Online Safety Institute (FOSI) which you can find here. But why not develop your own one? Here are some points to consider including:
In my opinion, starting high school seems to be a logical time to start thinking about phone ownership, if you haven’t gone down that road before. Many kids will need to catch public transport to get to high school and having a phone in their pocket, in case plans go awry can make everyone feel more comfortable.
I realize that there is so much to consider so take some time to weigh up all factors.
But don’t forget – you’re the parent. Regardless of how much pressure your super keen tween is applying – this is your decision. You are the best judge of your child’s maturity and readiness. Giving your child a phone is in effect, giving them access to the adult world. So, only say yes if you are convinced the time is right
Good luck!
Alex x
The post My Child Wants a Phone. Should I Say ‘Yes’? appeared first on McAfee Blog.






apple-1200




apple-1200















Something’s not right. Maybe your phone is losing its charge way too quickly. Or one day it suddenly starts turning itself off and on again. Perhaps it’s running hot, so hot it’s hard to hold. Likewise, you might see outgoing calls that you never dialed or strange spikes in your data usage. Signs like these could mean that your smartphone’s been hacked. Learn how to protect your smartphone with McAfee Mobile Security
Several signs of a potential smartphone hack can look like a technical issue, at least on the surface. Yet the fact is that these issues may be a symptom of a deeper problem, such as malware installed on your smartphone. Malware can eat up system resources or conflict with other apps and your operating system, all of which can cause your phone to act sluggish or erratically.
Yet, in a way, that’s good news. Because malware can run inefficiently on your phone and create hiccups both large and small, it can tip you off to its presence. And with all the important information we carry in the palms of our hands nowadays, that’s good news twice over. Knowing the signs, subtle or otherwise can alert you to an otherwise largely invisible problem.
Whether hackers physically sneak it onto your phone or by tricking you into installing it via a phony app, a sketchy website, or a phishing attack, hacking software can create problems for you in a couple of ways:
Some possible signs of hacking software on your phone include:
Maybe you’ve seen some of the signs we mentioned earlier. Is your device operating slower, are web pages and apps harder to load, or does your battery never seem to keep a charge? These are all signs that you could have malware running in the background, zapping your phone’s resources.
Like the performance issues above, malware or mining apps running in the background can burn extra computing power (and data). Aside from sapping performance, malware and mining apps can cause your phone to run hot or even overheat.
If you find apps you haven’t downloaded, or calls, texts, and emails that you didn’t send, that’s a red flag. A hacker may have hijacked your phone to send premium-rate calls or messages or to spread malware to your contacts. Similarly, if you see spikes in your data usage, that could be a sign of a hack as well.
Malware can also be behind spammy pop-ups, changes to your home screen, or bookmarks to suspicious websites. In fact, if you see any configuration changes you didn’t personally make, this is another big clue that your smartphone has been hacked.
While there are several ways a hacker can get into your phone and steal personal and critical information, here are a few tips to keep that from happening:
The post How To Tell If Your Smartphone Has Been Hacked appeared first on McAfee Blog.




Can thieves steal identities with only a name and address?
In short, the answer is “no.” Which is a good thing, as your name and address are in fact part of the public record. Anyone can get a hold of them. However, because they are public information, they are still tools that identity thieves can use.
If you think of your identity as a jigsaw puzzle, your name and address are the first two pieces that they can use to build a bigger picture and ultimately put your identity at risk.
With that, let’s look at some other key pieces of your identity that are associated with your name and address—and what you can do to protect them.
For starters, this information is so general that it is of little value in of itself to an identity thief. Yet a determined identity thief can do a bit of legwork and take a few extra steps to use them as a springboard for other scams.
For example, with your name and address a thief could:
There are volumes of public information that are readily available should someone want to add some more pieces to your identity jigsaw puzzle, such as:
In the U.S., the availability of such information will vary from state-to-state and different levels of government may have different regulations about what information gets filed—in addition to whether and how those reports are made public. Globally, different nations and regions will collect varying amounts of public information and have their own regulations in place as well. More broadly, though, many of these public databases are now online. Consequently, accessing them is easier than the days when getting a hold of that information required an in-person visit a library or public office.
Thieves can gain additional information about you from other online sources, such as data brokers. And data brokerage is a big business, a global economy estimated at $200 billion U.S. dollars a year. What fuels it? Personal information, representing thousands of data points on billions of people scraped from public records, social media, smartphone apps, shopper loyalty cards, third-party sources, and sometimes other data broker sites as well.
The above-the-board legal intent of data broker sites is to sell that information to advertisers so that they can create highly targeted campaigns based on people’s behaviors, travels, interests, and even political leanings. Others such as law enforcement officials, journalists, and others who are conducting background checks will use them too.
On the dark side, hackers, scammers, and thieves will buy this information as well, which they can use to commit identity theft and fraud. The thing is, data brokers will sell to anyone. They don’t discriminate.
Phishing attacks aren’t just for email, texts, and direct messages. In fact, thieves are turning to old tricks via old-fashioned physical mail. That includes sending phony offers or by impersonating officials of government institutions, all designed to trick you into giving up your personally identifiable information (PII).
What might that look like in your mailbox? They can take the form of bogus lottery prizes that request bank information for routing (non-existent) winnings. Another favorite of scammers are bogus tax notifications that demand immediate payment. In all, many can look quite convincing at first blush, yet there are ready ways you can spot them. In fact, many of the tips for avoiding these physical mail phishing attacks are the same for avoiding phishing attacks online, which we outline in detail here.
Recently, I’ve seen a few news stories like this where thieves reportedly abuse the change-of-address system with the U.S. Postal Service. Thieves will simply forward your mail to an address of their choosing, which can drop sensitive information like bank and credit card statements in their mailbox. From there, they could potentially have new checks sent to them or perhaps an additional credit card—both of which they can use to drain your accounts and run up your bills.
The Postal Service has mechanisms in place to prevent this, however. Among which, the Postal Service will send you a physical piece of mail to confirm the forwarding. So, if you ever receive mail from the Postal Service, open it and give it a close look. If you get such a notice and didn’t order the forwarding, visit your local post office to get things straightened out. Likewise, if it seems like you’re missing bills in the mail, that’s another good reason to follow up with your post office and the business in question to see if there have been any changes made in your mail forwarding.
So while your name and address are out there for practically all to see, they’re largely of little value to an identity thief on their own. But as mentioned above, they are key puzzle pieces to your overall identity. With enough of those other pieces in hand, that’s where an identity thief can cause trouble.
Other crucial pieces of your identity include:
Let’s start with the biggest one. This is the master key to your identity, as it is one of the most unique identifiers you have. As I covered in my earlier blog on Social Security fraud, a thief can unlock everything from credit history and credit line to tax refunds and medical care with your Social Security or tax ID number. In extreme cases, they can use it to impersonate you for employment, healthcare, and even in the event of an arrest.
You can protect your Social Security Number by keeping it locked in a safe place (rather than in your wallet) and by providing your number only when absolutely necessary. For more tips on keeping your number safe, drop by that blog on Social Security fraud I mentioned.
Thieves have figured out ways of getting around the fact that IDs like these include a photo. They may be able to modify or emulate these documents “well enough” to pull off certain types of fraud, particularly if the people requesting their bogus documents don’t review them with a critical eye.
Protecting yourself in this case means knowing where these documents are at any time. (With passports, you may want to store those securely like your Social Security or tax ID number.) Also be careful when you share this information, as the identifiers on these documents are highly unique. If you’re uncomfortable with sharing this information, you can ask if other forms of ID might work—or if this information is really needed at all. Also, take a moment to make copies of these documents and store them in a secure place. This can help you provide important info to the proper authorities if they’re lost or stolen.
With data breaches large and small making the news (and many more that do not), keeping a sharp eye on your accounts is a major part of identity theft prevention. We talk about this topic quite often, and it’s worth another mention because protecting these means protecting yourself from thieves who’re after direct access to your finances and more.
Secure your digital accounts for banking, credit cards, financials, and shopping by using strong, unique passwords for each of your accounts that you change every 60 days. Sound like a lot of work? Let a password manager do it for you, which you can find in comprehensive online protection software. By changing your strong passwords and keeping them unique can help prevent you from becoming a victim if your account information is part of a breach—by the time a crook attempts to use it, you may have changed it and made it out of date.
In addition to protecting the core forms of identity mentioned above, a few other good habits go a long way toward keeping your identity secure.
By protecting your devices, you protect what’s on them, like your personal information. Comprehensive online protection software can protect your identity in several ways, like creating and managing the strong, unique passwords we talked about and providing further services that monitor and protect your identity—in addition to digital shredders that can permanently remove sensitive documents (simply deleting them won’t do that alone.) Further, it can monitor your identity and monitor your credit, further protecting you from theft and fraud.
Identity theft where thieves dig through trash or go “dumpster diving” for literal scraps of personal info in bills and statements, has been an issue for some time. You can prevent it by shredding up any paper medical bills, tax documents, and checks once you’re through with them. Paper shredders are inexpensive, and let’s face it, kind of fun too. Also, if you’re traveling, have a trusted someone collects your mail or have the post office put a temporary hold on your mail. Thieves still poach mail from mailboxes too.
Getting statements online cuts the paper out of the equation and thus removes another thing that a thief can physically steal and possibly use against you. Whether you use electronic statements through your bank, credit card company, medical provider, or insurance company, use a secure password and a secure connection provided by a VPN. Both will make theft of your personal info far tougher on identity thieves.
A VPN is a Virtual Private Network, a service that protects your data and privacy online. It creates an encrypted tunnel to keep you more anonymous online by masking your IP address, device information, and the data you’re passing along that connection. In this way, it makes if far more difficult for advertisers, data brokers, and bad actors to skim your private information—in addition to shielding your information from crooks and snoops while you’re banking, shopping, or handling any kind of sensitive information online.
Give your statements a close look each time they come around. While many companies and institutions have fraud detection mechanisms in place, they don’t always catch every instance of fraud. Look out for strange purchases or charges and follow up with your bank or credit card company if you suspect fraud. Even the smallest charge could be a sign that something shady is afoot.
This is a powerful tool for spotting identity theft. And in many cases, it’s free to do so. In the U.S., the Fair Credit Reporting Act (FCRA) requires the major credit agencies to provide you with a free credit check at least once every 12 months. Canada provides this service, and the UK has options to receive free reports as well, along with several other nations. It’s a great idea to check your credit report, even if you don’t suspect a problem.
If the thought of your personal info being bought and sold puts you off, there’s something you can do about it. Our Personal Data Cleanup service can scan some of the riskiest data broker sites and show you which ones are selling your personal info. It also provides guidance on how you can remove your data from those sites, and with select products, it can even manage the removal for you.
While thieves need more than just your name and address to commit the overwhelming majority of fraud, your name and address are centerpieces of the larger jigsaw puzzle that is your overall identity.
And the interesting thing is your puzzle gets larger and larger as time goes on. With each new account you create and service that you sign into, that’s one more piece added to the puzzle. Thieves love getting their hands on any pieces they can because with enough of them in place they can try and pull a fast one in your name. By looking after each piece and knowing what your larger jigsaw puzzle looks like, you can help keep identity thieves out of your business and your life.
The post Can Thieves Steal Identities With Only a Name and Address? appeared first on McAfee Blog.




A good time to check if someone is using your identity is before it even happens.
One of identity theft’s several downsides is how people discover they’ve become a victim in the first place—by surprise. They go to rent an apartment, open a line of credit, or apply for financing, only to discover that their finances or reputation has taken a hit because of identity thief.
And those hits add up, particularly when you look at the dollars involved. In 2020, the Federal Trade Commission (FTC) reported $3.3 billion in financial losses from 4.7 million reported cases of fraud, a 45% increase over the year prior. Of those reports, identity theft was the leading fraud category, accounting for 29% of fraud incidents.
Plenty. Depending on the type and amount of information an identity thief gets their hands on, they can harm your finances and reputation in several ways, including:
Rather than ending up with a rude and potentially costly surprise of your own, you can get ahead of thieves by checking to see if someone is using your identity before it’s a problem or before it really takes root.
Major data breaches that expose personal information seem to hit the headlines with some regularity, not to mention the many, many more that don’t get national or international press coverage. Most recently we have the Neiman Marcus breach, where this major retailer alerted 4.6 million customers that “an unauthorized party obtained personal information associated with certain Neiman Marcus customers’ online accounts.”
And as it is with many such breaches, it took quite some time before the theft of information was discovered. Per Neiman Marcus, it’s believed that the breach occurred in May 2020 and only discovered in September of 2021. Potentially compromised information included:
Whether or not you have reason to suspect that your information got caught up in this recent large-scale breach, it serves as a good reminder that any time is the right time to check up on your identity. Acting now can save headaches, potentially big headaches, later.
Quite a bit of identity theft prevention begins with taking stock of the accounts and services you have in your name. This ranges anywhere from bank accounts to public utilities and from credit cards to loans, all of which contain varying degrees of personal information about you. With a sense of where your personal identity is being used, you can better look for instances where it’s being misused.
Ways you can spot for possible identity theft include:
If you stop receiving a bill that normally comes to you, such as a utility bill or for a department store credit card, that could be a sign that a thief has changed the mailing address and has potentially hijacked your identity.
This is rather straightforward, yet it reminds us how important it is to look at our statements closely. Charges that you didn’t ring up or that seem slightly higher than normal are a surefire sign that you should follow up with the bank or company involved and let them know of possible fraud.
In the U.S., you have annual access to free credit reports from the major credit reporting agencies. Not only will this give you a sense of your credit score, but it will also show the credit that’s open in your name, along with addresses associated with your identity. Spotting an account that you haven’t signed up for or seeing an address of a residence that you’re not renting are other common signs that your identity may have been compromised.
With the number of accounts many of us have these days, a credit monitoring service can help you stay on top of what’s happening in your name. Often offered through banks, credit unions, and even insurance providers, credit monitoring can alert you in several instances, including:
Overall, credit monitoring can act as another set of eyes for you and spot potential identity issues. Different services provide different levels of monitoring, so consider reviewing a few options to find the one that works best for you.
One like our own Identity Protection Service will monitor several types of personally identifiable information, alert you of potentially stolen personal info, and offer guided help to neutralize the threat—in addition to offering several preventative steps to help keep theft from happening in the first place. With this set up on your computers and smartphone you can stay in the know and address issues immediately.
Along with keeping an eye on what’s happening with your identity online and elsewhere, there are a few more things you can do to make it tougher for thieves to steal your identity.
Given all the banking and shopping we do on our computers and phones, installing and using comprehensive online protection software is a must these days. It puts several layers of security in place, such as creating complex passwords automatically, shielding credit card info from prying eyes, and protecting your privacy and data online by connecting with a VPN. In short, online protection software acts as a solid first line of defense.
As mentioned above, comprehensive online protection software often includes a password manager that can generate strong, unique passwords for each of your accounts and remember them for you. It’s extra protection that makes life a lot easier for you by managing all the accounts you’re juggling. Also, use MFA (multi-factor authentication) on the accounts that give you the option, which makes it harder for a thief to crack your accounts with a password alone.
Sensitive documents come in all forms. Top-of-the-line examples include things like tax returns, bank statements, and financial records. Yet there are also things like your phone and utility bills, statements from your doctor’s office, and offers that come to you via mail. Together, these things can contain personal information such as account numbers, your full Social Security Number, the last four digits of your Social Security Number (which can still be useful to thieves), and other information that may uniquely identify you. You’ll want to dispose of sensitive documents like these so that they can’t be harvested by hackers.
For physical documents, consider the low-cost investment of a paper shredder to help ensure they don’t fall into the wrong hands when you are done with them. (And let’s face it, they’re fun to use!) For digital documents, simply deleting a file is not enough – online protection software is a great resource that often includes a digital document shredder, designed to render the data practically unusable when you’re ready to trash the file.
Your Social Security Number is one of the most prized possessions a thief can run away with because it is so closely associated with you and things like your tax returns, employment, and so on. Keep it stored in a safe location rather than on your person or in your wallet. Likewise, be careful about giving out your SSN. While organizations like the IRS, your bank, and employer require it, there are other organizations who do not—but may ask for it anyway. (Doctor’s offices are a prime example.) If you get such a request, ask them what they intend to use it for and then ask if another form of identification will work instead.
Phishing attacks are one of the primary ways identity thieves steal personal information. Whether they come via a direct message, on social media, or through email, text, or phone calls, thieves use them to harvest your personal info by posing as a legitimate organization—such as in this recent IRS phishing scam. Phishing is a topic all unto itself, and you can check out this quick read to see how you can spot phishing scams and protect yourself from them.
Like any criminal, identity thieves do their dirtiest work in the shadows—quietly stealing money under your nose, or worse, as we outlined above. By shining a light on your identity and keeping regular track of what’s happening with it, you can spot unusual activity right away. Even the small stuff is important. A co-worker of mine once saw an incorrect address listed on his credit report. Turned out, that address was used to rack up several large charges at a retailer, which he was able to fix with the aid of the credit reporting agency and the retailer in question.
No doubt about it. Identity theft is indeed on the rise, and your best bet to avoid such a nasty surprise is to keep an eye on your digital identity the same way you keep an eye on your actual wallet.
The post How to Check if Someone is Using Your Identity appeared first on McAfee Blog.

Some scams can make a telltale sound—rinnng, rinnng! Yup, the dreaded robocall. Not only are they annoying, but they can also hit you in the pocketbook.
In the U.S., unwanted calls rank as the top consumer complaint reported to the Federal Communications Commission (FCC), partly because scammers have made good use of spoofing technologies that serve up phony caller ID numbers. As a result, that innocent-looking phone number may not be innocent at all.
Whether the voice on the other end of the smartphone is recorded or an actual person, the intent behind the call is likely the same—to scam you out of your personal information, money, or both. Callers such as these may impersonate banks, government agencies, insurance companies, along with any number of other organizations that give them an excuse to demand payment, financial information, or ID numbers.
And some of those callers can sound rather convincing. Others, well, they’ll just get downright aggressive or threatening. One of the most effective tools these scam calls use is a sense of urgency and fear, telling you that there’s a problem right now and they need your information immediately to resolve whatever bogus issue they’ve come up with. That right there is a sign you should take pause and determine what’s really happening before responding or taking any action.
Whatever form these unwanted calls take, there are things you can do to protect yourself and even keep you from getting them in the first place. These five tips will get you started:
Okay, maybe you can file this one under “obviously.” Yet be aware that scammers excel at spoofing. They can make a call look like it’s local or just familiar enough. If you get caught off guard and answer a spammy call, hang up immediately. If you’re unsure about the number, you’re better off letting your voicemail screen the call for you. Picking up the phone to determine if a call is legit or not could help a scammer verify that you have a valid line, which could lead to more nuisance calls down the road.
So, let’s say you let an unknown call go through to voicemail. The call sounds like it’s from a bank or business with news of an urgent matter. If you feel the need to follow up, get a legitimate customer service number from a statement, bill, or website of the bank or business in question so you can verify the situation for yourself. Calling back the number captured by your phone or left in voicemail could play right into the hands of a scammer.
As you can see, scammers love to play the role of an imposter and will tell you there’s something wrong with your taxes, your account, or your bank statement. Some of them can be quite convincing, so if you find yourself in a conversation where you don’t feel comfortable with what’s being said or how it’s being said, hang up and follow up bank or business as called out above. In all, look out for pressure or scare tactics and keep your info to yourself.
Several nations provide such a service, effectively a list that legitimate telemarketers will reference before making their calls. While this may not prevent scammers from ringing you up, it can cut down on unsolicited calls in general. For example, the U.S., Canada, and the UK each offer do not call registries.
Many mobile carriers provide additional apps and services that can block unwanted calls, often as part of your smartphone’s service plan. There are third-party apps that do this as well. Yet do your research. You’ll want to see if those apps are legitimate and if they can effectively let “good” calls through without blocking them.
While security software and apps won’t block robocalls, they increase the security of your phone overall, which can protect both you and your data. You have a couple of options here. You can grab comprehensive security software that protects all of your devices or pick up an app in Google Play or Apple’s App Store. This way, you’ll have malware, web, and device security that’ll help you stay safe on your phone in general.
Taken together, these steps can help you beat or outright block unwanted calls like robocalls—and be safer (and maybe less annoyed) as a result.
The post Smartphone Security: Five Steps Beating and Blocking Robocalls appeared first on McAfee Blog.

“My phone’s been hacked!” Words you probably don’t want to hear or say. Ever.
Your phone gets to be like an old friend after a while. You have things laid out the way you like, your favorite apps are at the ready, and you have the perfect home screen and wallpaper all loaded up. So, if you unlock your phone one day and notice that something is a little … off, you’ll know pretty quickly. And it could be a sign that your phone may be hacked.
It’s often pretty easy to tell when a piece of your tech isn’t working quite right. The performance is off, things crash, and so on. While there are several cases where there’s a legitimate technical issue behind that, it could also be the sign of a hacked device.
Many hacks and attacks involve the installation of malware on the device, which eats up system resources, creates conflicts with other apps, and uses your data or internet connection to pass along your personal information—all of which can make your smartphone feel a little off.
A few examples follow. Note that these may be signs of a hacked phone, yet not always.
A suddenly sluggish phone or one that simply can’t hold a charge anymore are often attributed to phones that are getting a little old (these things happen). Yet, those same behaviors can also be signs of a compromised phone. For example, malicious bitcoin miners can run in the background and cause all types of performance issues because they eat up battery life and take up resources that your phone could otherwise normally use. In a way, it’s like having a second person using your phone at the same time you are.
Similar to the performance issues mentioned above, malware or mining apps running in the background can burn extra computing power, battery life, and data. Aside from a performance hit, they can cause your phone to physically run hot or even overheat. So if your phone feels like it’s been sitting in the sun, this could be a sign that malware is present.
If you’re seeing more popup ads than usual or seeing them for the first time, it could be a sign that your phone has been hit with adware—a type of malicious app that hackers use to generate revenue by distributing ads without the consent of the user. Furthermore, those ads may be malicious in nature as well (which is a good reminder to never click on them). Such ads may lead to bogus products and services or pages designed to steal personal information. All in all, malicious adware is what hackers prop up to make money off unsuspecting people.
A potential telltale sign that your phone has been hacked is the appearance of new apps that you didn’t download, along with spikes in data usage that you can’t account for. Likewise, if you see calls in your phone bill that you didn’t make, that’s a warning as well.
Big red flag here. Like seeing an unknown charge or payment in your bank statement, this is a possible sign that a hacker has hijacked your phone and is using it to transfer data, make purchases, send messages, or make calls via your phone.
To help keep your phone from getting hacked in the first place, there are a few relatively easy steps you can take. Inside of a few minutes, you can find yourself much safer than you were before.
1. Use comprehensive security software on your phone. Over the years, we’ve gotten into the good habit of using this on our computers and laptops. Our phones? Not so much. Installing security software on your smartphone gives you the first line of defense against attacks, plus several of the additional security features mentioned below.
2. Stay safer on the go with a VPN. One way that crooks can hack their way into your phone is via public Wi-Fi, such as at airports, hotels, and even libraries. These networks are public, meaning that your activities are exposed to others on the network—your banking, your password usage, all of it. One way to make a public network private is with a VPN, which can keep you and all you do protected from others on that Wi-Fi hotspot.
3. Use a password manager. Strong, unique passwords offer another primary line of defense. Yet with all the accounts we have floating around, juggling dozens of strong and unique passwords can feel like a task—thus the temptation to use (and re-use) simpler passwords. Hackers love this because one password can be the key to several accounts. Instead, try a password manager that can create those passwords for you and safely store them as well. Comprehensive security software will include one.
4. Avoid public charging stations. Charging up at a public station seems so simple and safe. However, some hackers have been known to “juice jack” by installing malware into the charging station. While you “juice up,” they “jack” your passwords and personal info. So what to do about power on the road? You can look into a portable power pack that you can charge up ahead of time or run on AA batteries. They’re pretty inexpensive and can prevent malware from a public charging station.
5. Keep your eyes on your phone. Preventing the actual theft of your phone is important too, as some hacks happen simply because a phone falls into the wrong hands. This is a good case for password or PIN protecting your phone, as well as turning on device tracking so that you can locate your phone or even wipe it remotely if you need to. Apple provides iOS users with a step-by-step guide for remotely wiping devices and Google offers up a guide for Android users as well.
A phone that’s acting a little funny may indicate a run-of-the-mill tech issue, yet it could also be a tell-tale sign of a hack. At a minimum, following up on your gut instinct that something isn’t quite right can take care of a nagging tech issue. But in the event of a possible hack, it can save you the far greater headache of unauthorized charges and purchases, and even identity theft. If you spot a problem, it absolutely pays to take a closer look. Follow up with tech support for help, whether that’s through your device manufacturer, retailer, or your antivirus providers. They’ll help pinpoint the issue and get you on your way.
The post Help! I Think My Phone’s Been Hacked appeared first on McAfee Blog.

Mobile phones have gone through an incredible transformation since their inception in the 1970s. Now, the sheer number of applications is dizzying, as are their privacy policies; however, smartphone apps can bring hours of fun and belly laughs, and occasionally, a viral app captures the world’s attention. Don’t let potential risks to your personal information safety ruin all smartphone apps for you. All you need to share and play safely is a few tips to help you identify which apps are OK to use and how to navigate them intelligently.
Check out these four viral apps that may be putting your personal information at risk, plus a few tips that’ll help you enjoy smartphone apps safely.
Voilà AI Artist is a trending app that reimagines your face as a cartoon, caricature, or model of fine Renaissance art. Users can snap a selfie with the app or allow the app to access their photo library. According to WIRED, the app says it deletes users’ photos from its database in 24 to 48 hours, though it’s difficult to confirm that they aren’t stored.
Approach any app that could potentially use and store your likeness with caution. Deepfake technology is becoming more sophisticated and common by the day. Deepfakes are fabricated videos, images, or sound clips of every day or famous people based on real videos and images. Fake media impacts the victims whose likenesses are used because often the media is demeaning or incendiary. Voilà AI Artist hasn’t been suspected of any wrongdoing, but it’s best to be aware of how your face could be used to endorse something you don’t agree with.
Another face-altering app that could pose a risk to users’ privacy is FaceApp. Similar to Voilà AI Artist, it’s unclear what the app does with your likeness once you allow it to take your picture. FaceApp’s terms of use agreement outline that the selfies uploaded to the app belong to the app. From there, the app is free “to use, reproduce, modify, adapt, create derivative works from, distribute, perform, and display your User Content.” This line of fine print should make users pause. Again, users’ faces could be used in ways they wouldn’t normally agree to.
While the Pokémon Go craze of 2016 has greatly subsided, the next viral app that sweeps the world could replicate the security vulnerabilities the premise presents. Pokémon Go uses augmented reality, which is the kind of technology that makes it look like a Pokémon is strolling across your living room. The app can access your camera, as well as your contacts, pictures, chats, and location. It’s a blast exploring your neighborhood looking for animated critters and seeing nearby strangers’ profiles pop up on your map; however, be wary of sharing location data and images of the inside of your home with people you don’t know in real life.
TikTok may pose a risk to users’ data privacy. TikTok is under suspicion for using data mining tactics. Data mining is a practice where corporations harvest personal details from user-profiles and share them with advertising, marketing, and analytics companies. According to Business Insider, TikTok collects more than 50 kinds of data from users as young as 13 years old, including age, gender, location, and online habits. These facts are often used to create targeted ads that sometimes border on an invasion of privacy.
Check out these tips to make sure you’re prepared to use apps safely or help you decide to skip trends entirely.
The post 4 Viral Apps Risking Your Personal & Smartphone Security appeared first on McAfee Blog.

Equipping and guiding your digitally connected child is one of the toughest challenges you will face as a parent. As your child grows and changes, so too will their online activities. Friend groups, favorite apps, and online interests can shift from one month to the next, which is why parental controls can be a parent’s best friend.
According to a report from Common Sense Media, teens spend an average of seven hours and 22 minutes on their phones a day. Tweens (ages 8 to 12) spend four hours and 44 minutes daily. This is time outside of schoolwork.
That is a lot of time to stroll the streets of cyberspace for entertainment purposes, and it’s only increased since the pandemic.
Striking a balance between screen time and healthy device use is an always-evolving challenge. On the one hand, your child’s device is an essential channel connecting them to their self-identity, peer acceptance, and emotional well-being. On the other hand, that same device is also the door that can bring issues such as cyberbullying, predators, risky behavior, and self-image struggles into your child’s life.
Parental controls are tools that allow parents to set controls on their children’s internet use. Controls include content filters (inappropriate content), usage limits (time controls), and monitoring (tracking activity).
Many of the technology your family already owns or sites your kids visit have basic parental controls (i.e., built-in controls for android and iPhone and social networks such as YouTube). However, another level of parental control comes in software specifically engineered to filter, limit, and track digital activity. These consumer-designed parental controls offer families a higher, more powerful form of protection.
If you are like many parents who land on this blog, you’ve hit a rough patch. You have concerns about your child’s online activity but aren’t sure how to begin restoring balance. Rightly, you want to find the best parental control software and put digital safeguards in place.
Every family dynamic is different, as is every family’s approach to online monitoring. However, most parents can agree that when a negative influence begins to impact the family’s emotional and physical health, exploring new solutions can help get you back on track.
Depending on your child’s age, you may need to consider parental controls if:
1. They don’t respond when you talk to them
If your child is increasingly engrossed in their phone and it’s causing communication issues in your family, you may want to consider software that includes time limits. Connecting with your child during device-free time can improve communication.
2. They’ve started ignoring homework and family responsibilities
There are a lot of reasons grades can plummet, or interests can fade. However, if your child is spending more and more time online, limiting or monitoring what goes on in that time can help restore emotional balance and self-discipline to meet responsibilities.
3. Their browser history shows access to risky content
Innocent online searches can lead to not so innocent results or children may go looking for content simply because they’re curious. Parental controls automatically block age-inappropriate sites and filter websites, apps, and web searches.
4. They won’t give you their device without a fight
If the phone has become the center of your child’s world at the cost of parental respect and family rules, they may be engaged in inappropriate behavior online, connecting with the wrong friends, or struggling with tech balance. With the proper parental controls, a parent can block risky content, view daily activity, and set healthy time limits.
5. They’re losing interest in family outings and other non-digital activities
Poor habits form quietly over time. If your child has dramatically changed their focus in the past three to six months, consider zooming in on why. It may not be technology use, but you may consider an additional layer of protection if it is.
6. They go into another room to respond to a text
While everyone deserves privacy, if constantly sneaking away to communicate with a friend is your child’s new norm, you may consider making some screen time adjustments.
7. They are exhausted
Unbeknownst to parents, kids might be exchanging sleep for screen time. Parental controls can help you nip this unhealthy habit. Setting time limits can help kids experience deeper sleep, better moods, more focus, and more energy.
8. They overshare online
If you browse through your child’s social media and notice their profiles are public instead of private, or if your child tends to overshare personal information, parental controls can help you monitor future activity.
Ideally, we’d all prefer to live in a world where we didn’t need parental controls at all. Unfortunately, that is neither a present nor future reality. So, we recalibrate, keep learning, and keep adding to our parenting skills. As always, we believe the first go-to digital safety tool is investing in consistent open and honest conversation with your child. And the second tool? Yup, reach for the parental controls. While you may hear some hemming and hawing from your kids at first, the peace of mind you gain from having parental controls in place will be worth it.
The post 8 Signs It May Be Time for Parental Controls appeared first on McAfee Blog.

There’s little rest for your hard-working smartphone. If you’re like many professionals today, you use it for work, play, and a mix of personal business in between. Now, what if something went wrong with that phone, like loss or theft? Worse yet, what if your smartphone got hacked? Let’s try and keep that from happening to you.
Globally, plenty of people pull double duty with their smartphones. In Spain, one survey found that 55% of people use the same phone for a mix of personal and and work activity. The same survey showed that up to half of people interviewed in Japan, Australia, and the U.S. do so as well, while nations like the UK and Germany trailed at 31% and 23% respectively.
Whether these figures trend on the low or high end, the security implications remain constant. A smartphone loaded with business and personal data makes for a desirable target. Hackers target smartphones because they’re often unprotected, which gives hackers an easy “in” to your personal information and to any corporate networks you may use. It’s like two hacks with one stone.
Put simply, as a working professional with a smartphone, you’re a high-value target.
As both a parent and a professional, I put together a few things you can do to protect your smartphone from hacks so that you can keep your personal and work life safe:
First up, the basics. Locking your phone with facial ID, a fingerprint, pattern or a pin is your most basic form of protection, particularly in the event of loss or theft. (Your options will vary depending on the device, operating system, and manufacturer.) Take it a step further for even more protection. Secure the accounts on your phone with strong passwords and use two-factor authentication on the apps that offer it, which doubles your line of defense.
Or, put another way, don’t hop onto public Wi-Fi networks without protection. A VPN masks your connection from hackers allowing you to connect privately when you are on unsecure public networks at airports, cafes, hotels, and the like. With a VPN connection, you’ll know that your sensitive data, documents, and activities you do are protected from snooping, which is definitely a great feeling given the amount of personal and professional business we manage with our smartphones.
Both Google Play and Apple’s App Store have measures in place to help prevent potentially dangerous apps from making it into their stores. Malicious apps are often found outside of the app stores, which can run in the background and compromise your personal data like passwords, credit card numbers, and more—practically everything that you keep on your phone. Further, when you are in the app stores, look closely at the descriptions and reviews for apps before you download them. Malicious apps and counterfeits can still find their way into stores, and here are a few ways you can keep those bad apps from getting onto your phone.
Backing up your phone is always a good idea for two reasons:
Both iPhones and Android phones have straightforward ways of backing up your phone regularly.
Worst case scenario—your phone is gone. Really gone. Either it’s hopelessly lost or got stolen. What now? Lock it remotely or even wipe its data entirely. While that last bit about wiping the phone seems like a drastic move, if you maintain regular backups as mentioned above, your data is secure in the cloud—ready for you to restore. In all, this means that hackers won’t be able to access you, or your company’s, sensitive information—which can keep you out of trouble and your professional business safe. Apple provides iOS users with a step-by-step guide for remotely wiping devices, and Google offers up a guide for Android users as well.
We all download apps, use them once, and then forget they are on our phone. Take a few moments to swipe through your screen and see which ones you’re truly done with and delete them along with their data. Some apps have an account associated with them that may store data off your phone as well. Take the extra step and delete those accounts so any off-phone data is deleted.
The reason for this is that every extra app is another app that needs updating or that may have a security issue associated with it. In a time of data breaches and vulnerabilities, deleting old apps is a smart move. As for the ones you keep, update them regularly and turn on auto-updates if that’s an option. Updates not only introduce new features to apps, but they also often address security issues too.
With so much of your life on your phone, getting security software installed on it can protect you and the things you keep on your phone. Whether you’re an Android owner or iOS owner, mobile security software can keep your data, your shopping, and payments secure.
The post 7 Tips to Protect Your Smartphone from Getting Hacked appeared first on McAfee Blog.

If only more things in life came with training wheels; a child’s first smartphone could certainly use some.
Like taking off the training wheels and riding out into the neighborhood for the first time, a smartphone opens an entirely new world for children. There are apps, social media, group chats with friends, TikTok stars, and the joy of simply being “in” with their classmates and friends through the shared experience of the internet.
For parents, the similarities between first bike rides and first phones continue. You love the growing independence that this moment brings, yet you also wonder what your child will encounter out there when you’re not around. The good and the bad. How have you prepared them for this? Are they really ready?
That’s the question, isn’t it—when is my child ready for that first smartphone?
For years, your child has dabbled on the internet, whether that was playing on your phone while they were little, letting them spend time on a tablet, or using a computer for school. Along the way, there have been teaching moments, little lessons you’ve imparted about staying safe, how to treat others online, and so forth. In other words, you’ve introduced the internet to your child in steps. Giving them their own phone is yet another step, but a big one.
Yet those teaching moments and little lessons are things that they’ll lean on when they’re on their own phone—whether those were about “stranger dangers” online, proper online etiquette, and the difference between safe and unsafe websites. Understanding if your child has a firm foundation for navigating all the highs and lows of the internet is a strong indication of their readiness. After all, safely entering the always-online world of having a smartphone demands a level of intellectual and emotional maturity.
Good question. We do know that smartphone usage by children is on the rise. For example, research from Common Sense Media indicates that 53% of 11-year-olds have a smartphone, a number that jumps to 69% at age 12. That’s quite a bit of smartphone use by tweens, use which may be lightly monitored or not monitored at all. Note the percentage of ownership by age and the volume of screen time that follows in the infographic below:

Source: Common Sense Media
Why the rise, particularly in very young owners? However, does that mean 26% of nine-year-olds should have unfettered and all-day access to the internet in the palm of their hands? That’s a topic for you to decide for yourself and for the good of your family. However, if the notion of a third grader with a smartphone seems a little on the young side to you, there are alternatives to smartphones.
If keeping in touch is the primary reason for considering a smartphone, you have internet-free options that you can consider:
In all, for a younger child, one of these options may be your best bet. They’ll help you and your child keep in touch, develop good habits, and simply learn the basic responsibilities and behaviors that come with using a device to communicate with others.
Now’s a perfect time to prepare yourself for the day when your child indeed gets that first proper smartphone. That entails a little research and a little conversation on your part. Topics such as cyberbullying, digital literacy, social media etiquette, and so on will be important to get an understanding on. And those are just the first few.
A good place to start is your circle of family and friends. There, you can find out how they handled smartphone ownership with their children. You’ll likely hear a range of strategies and approaches, along with a few stories too, all of which can prepare you and your child.
I also suggest carving out a few minutes a week to read up on our McAfee blog safety topics so that you can have all the knowledge and tools you need. We blog on topics related to parenting and children quite regularly, and you can get a quick view of them here:
Having a smartphone will change not only their life, but yours as well. Relationships will evolve as your child navigates their new online life with their middle school and high school peers. (Remember those days? They weren’t always easy. Now throw smartphones into the mix.)
With that, give you and your child one last checkpoint. The following family talking points for owning a smartphone offer a solid framework for conversation and a way to assess if your child, and you, are truly ready for what’s ahead.
Once smartphone day arrives, it’s time to put two things in place—mobile security and parental controls:
Plenty. And as a mom myself, I rely heavily on those parental controls I put into place, but I also stay close to what they are doing online. It’s a bit of a mix. I simply ask them what’s going on and do a little, monitoring too. That could be asking them what their favorite games and apps are right now or talking about what playlists they’re listening to. This keeps communication open and normalizes talking about the phone/ their internet usage and what’s happening on it. Communication like this can come in handy later on should they need your help with something that’s occurred online. By talking now, the both of you will have an established place to start.
In all, take children’s smartphone ownership in steps and prepare them for the day those training wheels come off so the both of you can fully enjoy that newfound independence of life with a smartphone.
The post How to Prepare for Your Child’s First Smartphone appeared first on McAfee Blogs.

In an earlier article, we took a look at smartphone alternatives for free-ranging kids. Next up is the follow-on conversation … the time you give them their first, fully functional smartphone—and how to manage having it in your lives.
For children, learning to use a first smartphone is just like learning to ride a bike. And that’s just as true for you just as it is for them.
When a child learns to ride a bike, they take it in steps and stages. Maybe they start tooling around on little kick-bikes, a tricycle, scooter, or so on, just to get their feet under them so to speak. Next, it’s that first bike with training wheels, and then the big day that they come off (complete with a few scrapes and bruises too). They’re on two wheels, and a whole new world has opened up for them—one that you have to monitor and parent as you give them increasing freedom to roam—from the block, to the neighborhood, to your town—as they grow older and more responsible.
Now, apply that same progression to the day your child finally gets their first smartphone. Plenty has led up to that moment: the times when they first tapped around your phone as a toddler, when as a preschooler they watched cartoons on a tablet, and maybe when they got a little older they had some other device, like a smartphone alternative designed just for kids.
Then comes along that first smartphone. And for parents it’s a game-changer, because it opens up yet another new world to them. The entire internet.
As you can see, your child doesn’t enter the world of smartphones entirely cold. They’ve already been on the internet and had the chance to experience selective slices of it under your supervision. But a smartphone—well, that’s another story entirely. A smartphone, out of the box, is a key to the broader internet. And just as you likely wouldn’t let your brand-new cyclist ride five miles to go and buy ice cream in town, there are plenty of places you wouldn’t let your new internet user go.
What follows here are a few words of advice that can ease your child into that new world, and ease you into it as well, so that you can all get the tremendous benefits of smartphone ownership with more confidence and care.
Whether you go with an Android device or iPhone, make sure you protect it. You can get mobile security for Android phones and mobile security for iPhones that’ll give you basic protection, like system scans, along with further protection that steers your child clear of suspicious websites and links. While I recommend protection for both types of phones, I strongly recommend it for Android phones given the differences in the way Apple and Android handle the code that runs their operating systems.
Apple is a “closed platform,” meaning that they do not release their source code to the public and partners. Meanwhile, Android is “open-source” code, which makes it easier for people to modify the code—hackers included. So while Apple phones have been historically less prone to attacks than Android phones, any device you own is inherently a potential target, simply because its connected to the internet. Protect it. (Also, for more on the differences between the security on Android phones and iPhones, check out this article from How-To Geek. It’s worth the quick read.)
Next up on your list is to establish a set of parental controls for the smartphone. You’ll absolutely want these as well. After all, you won’t be able to look over their shoulder while they’re using their phone like you could when they were little. Think of it as the next line of protection you can provide as a parent. A good set of parental controls will allow you to:
• Monitor their activity on their phone—what they’re doing and how much they’re doing it.
• Limit their screen time—allowing you to restrict access during school hours or select times at home.
• Block apps and filter websites—a must for keeping your children away from distractions or inappropriate content.
The great thing about parental controls is that they’re not set in stone. They give you the flexibility to parent as you need to parent, whether that’s putting the phone in a temporary time out to encourage time away from the screen or expanding access to more apps and sites as they get older and show you that they’re ready for the responsibility. Again, think about that first bike and the day you eventually allowed your child ride beyond the block. They’ll grow and become more independent on their phone too.
Unlike those rotisserie ovens sold on late-night infomercials, a smartphone isn’t a “set it and forget it” proposition. Moreover, you won’t find the best monitoring, safety, and guidance software in an app store. That’s because it’s you.
As a parent, you already have a strong sense of what does and does not work for your household. Those rules, those expectations, need to make the jump from your household to your child’s smartphone and your child’s behavior on that smartphone. Obviously, there’s no software for that. Here’s the thing, though: they’ve established some of those behaviors already, simply by looking at you. Over the years, your child has seen your behavior with the phone. And let’s face it, none of us have been perfect here. We’ll sneak a peek at our phones while waiting for the food to show up to the table at a restaurant or cracked open our phones right as we’ve cracked open our eyes at the start of the day.
So, for starters, establishing the rules you want your child to follow may mean making some fresh rules for yourself and the entire household. For example, you may establish that the dinner table is a phone-free zone or set a time in the evening when phones are away before bedtime. (On a side note, research shows that even dim light from a smartphone can impact a person’s sleep patterns and their health overall, so you’ll want to consider that for your kids—and yourself!)
Whatever the rules you set in place end up being, make them as part of a conversation. Children of smartphone age will benefit from knowing not only what the rules are but why they’re important. Aside from wanting them to be safe and well, part of the goal here is to prepare them for the online world. Understanding “the why” is vital to that.
And that leads us to “The Internet Talk.”. In a recent McAfee blog on “What Security Means to Families,” we referred to the internet as a city, the biggest one there is. And if we think about letting our children head into town on their bikes, the following excerpt from that blog extends that idea to the internet:
For all its libraries, playgrounds, movie theaters, and shopping centers, there are dark alleys and derelict lots as well. Not to mention places that are simply age appropriate for some and not for others. Just as we give our children freer rein to explore their world on their own as they get older, the same holds true for the internet. There are some things we don’t want them to see and do.
There are multiple facets to “The Talk,” ranging anywhere from “stranger danger” to cyberbullying, and just general internet etiquette—not to mention the basics of keeping safe from things like malware, bad links, and scams. That’s a lot! Right? It sure is.
The challenge is this: while we’ve grown up with or grown into the internet over the course of our lives, the majority of children are amongst the first waves of children who were “born into” the internet. As parents, that means we’re learning much, if not all, of what we know about digital parenting from scratch.
The good news is that you’re far from alone. Indeed, a good portion of our blog is dedicated entirely to family safety. And with that, I’ve pulled out a few select articles below that can give you some information and inspiration for when it’s time to have “The Internet Talk.”
• Stranger Danger
• Keeping Your Kids Safe from Predators Online
• Building Digital Literacy
• Screen Time and Sleep Deprivation in Kids
• Lessons Learned: A Decade of Digital Parenting
• Social Influencers and Your Kids
• Getting Kids to Care About Their Safety Online
And those are just a few for starters. We have plenty more, and a quick search will keep them coming. Meanwhile, know that once you have The Internet Talk, keep talking. Making sure your child is safe and happy on the internet is an ongoing process—and conversation, which will cover more in a moment.
One reason parents often cite for giving their child a smartphone is its location tracking capabilities that allow parents to see where their children are ranging about with a quick glance. And whether or not you choose to use such tracking features, that’s a decision you’ll have to make. However, consider your child’s privacy when you do. That’s not to say that you’re not in charge or that you shouldn’t track your child. Rather, it’s a reminder that your child is in fact getting older. Their sense of space and privacy is growing. Thus, if you choose to monitor their location, let them know you’re doing it. Be above the board with the intent that if you don’t hide anything from them, they’ll be less inclined to hide anything from you.
The same applies to parental controls software. Many of them will issue a report of app usage and time spent using the app, along with surfing habits too. Go ahead, monitor those early on and then adjust as them as it feels right to you. Let your child know that you’re doing it and why.
Another thing I’ve seen many of the parents I know do is share the credentials to any social media account their child sets up. Doing this openly lets your child take those first steps into social media (when you feel they’re ready) while giving you the opportunity to monitor, correct, and even cheer on certain behaviors you see. Granted, it’s not unusual for kids to work around this by setting up alternate accounts that they hide from their parents. With parental controls in place, you can mitigate some of that behavior, yet vigilance and openness on your part will be the greatest tool you have in that instance.
While you’re at it, go ahead and have conversations with your kid about what they’re doing online. Next time you’re in the car, ask what’s the latest app their friends are using. Take a peek at what games they’re playing. Download that game yourself, give it a try, and play it online with them if you can. This kind of engagement makes it normal to talk about the internet and what’s happening on it. Should the time come to discuss more serious topics or pressing matters (like a cyberbullying event, for instance), you have a conversational foundation already built.
So, as we’ve discussed, technology is only part of the answer when managing that first smartphone in your child’s life. The other part is you. No solution works without your engagement, care, consistent application of rules, and clear expectations for behavior.
So, as you once looked on proudly as those training wheels came off your child’s first bike, you’ll want to consider doing the digital equivalent in those first months of that first smartphone. Keep your eyes and ears open as they use it. Have conversations about where their digital travels have taken them—the games they’re playing, the friends they’re chatting with. While you do, keep a sharp eye on their moods and feelings. Any changes could be a sign that you need to step in and catch them before they fall or pick them up right after they’ve fallen.
In all, your child’s first smartphone is a wonderful moment for any family, as it represents another big step in growing up. Celebrate it, have fun with it, and play your role in making sure your child gets the very best out of it.
To stay updated on all things McAfee and for more resources on staying secure from home, follow @McAfee_Home on Twitter, listen to our podcast Hackable?, and ‘Like’ us on Facebook.
The post The First Smartphone for Free-Ranging Kids appeared first on McAfee Blogs.